Professional Documents
Culture Documents
OSPF Version 2 (RFC 2328) : Interior Gateway Protocol (IGP)
OSPF Version 2 (RFC 2328) : Interior Gateway Protocol (IGP)
Uploaded by
sud_mishraOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
OSPF Version 2 (RFC 2328) : Interior Gateway Protocol (IGP)
OSPF Version 2 (RFC 2328) : Interior Gateway Protocol (IGP)
Uploaded by
sud_mishraCopyright:
Available Formats
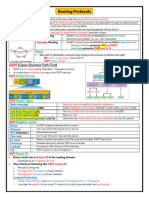
OSPF Version 2 (RFC 2328)
Interior gateway protocol (IGP). Routers maintain link-state database.
Describes Autonomous Systems (AS) topology. Propagated by ooding: Link State Advertisements (LSAs).
Router constructs tree rooted at itself. Trafc distributed equally over multiple equal-cost paths to
destination.
43
UTD, CS 6390
Ravi Prakash
OSPF Metrics
Internal metrics: cost associated with output side of router
interfaces.
External metrics: denote externally derived routing data.
Type 1: treated the same as internal metrics. Type 2: always greater than cost of any internal path.
Both external metric types can simultaneously exist in an AS. Ability to specify forwarding address in LSA to:
Reduce extra hops. Enable some routers to acts as route servers.
44
UTD, CS 6390
Ravi Prakash
OSPF Hierarchical Organization
Autonomous System split into areas. Each area has its own link-state database. Motivation for hierarchy: scalability. Area border router: router connected to multiple areas.
Stores different link-state database for each of its areas.
45
UTD, CS 6390
Ravi Prakash
Autonomous System Backbone
Special area 0 (0.0.0.0). Contains all area border routers. Logically contiguous:
Employ virtual links if physical contiguity is not possible.
46
UTD, CS 6390
Ravi Prakash
OSPF Classication of Routers
Internal routers. Area border routers. Backbone routers. AS boundary routers.
A router may belong to multiple categories. Every router in an AS knows the path to every AS boundary router.
47
UTD, CS 6390
Ravi Prakash
OSPF Adjacency Determination
Routers send and receive OSPF Hello packets to acquire
neighbors.
Hello packets sent to AllSPFRouters multicast address (224.0.0.5). Hello packets also used to elect Designated Router in
broadcast and non-broadcast multi access (NBMA) networks.
Routers form adjacencies with some newly acquired neighbors
and synchronize LS database.
In broadcast and NBMA networks, adjacencies from Designated
Router and other routers, and Backup Designated Router and other routers.
AllDRouters address (224.0.0.6) used by other routers to send
information to Designated and Backup Designated routers.
48
UTD, CS 6390
Ravi Prakash
Intra-area Routing
Routers ood LSAs in the area: periodically and on topology
change.
Reliable ooding through acknowledgments. All routers in an area have identical LS database.
49
UTD, CS 6390
Ravi Prakash
Inter-area Routing Area border router:
Summarizes topology information of its area. Sends the summary to all other area border routers in the AS. Receives summary from other area border routers and
calculates inter-area paths.
Advertises inter-area paths to its attached area.
50
UTD, CS 6390
Ravi Prakash
AS-External Routing
AS boundary routers ood their external routing information to
all routers.
Exception: not ooded into stub areas. All routers, except those in stub areas, know the path to AS
boundary routers.
51
UTD, CS 6390
Ravi Prakash
Authentication
All OSPF packets are authenticated. 64-bit authentication type eld in OSPF packet header. Authentication type congurable on per-interface basis:
0: null authentication. 1: simple password. 2: cryptographic authentication. others: reserved for future use.
52
UTD, CS 6390
Ravi Prakash
Simple Password Authentication
All OSPF packets in a network use the same password. 64-bit clear password. Guards against router inadvertently joining a routing domain. Possible to determine password if one has physical access to
network.
53
UTD, CS 6390
Ravi Prakash
Cryptographic Authentication
Shared key congured in all routers attached to a common
network.
Message digest generated using the key, and appended to packet. Implicit agreement among routers about algorithm. Cryptographic sequence number to prevent replay attacks:
Non-decreasing, 32-bit value. Initialized to zero. Rollover procedure not specied. May be used to denote seconds since reboot.
54
UTD, CS 6390
Ravi Prakash
You might also like
- OSPFDocument73 pagesOSPFlvsaruNo ratings yet
- Open Shortest Path First: State Advertisements (Lsas)Document16 pagesOpen Shortest Path First: State Advertisements (Lsas)Prabha GaranNo ratings yet
- Routing ProtocolDocument24 pagesRouting Protocolgomathisankar.v1978No ratings yet
- OSPF PresentationDocument43 pagesOSPF PresentationBehzad ZahidNo ratings yet
- CCNA 200-125: IP Routing TechnologyDocument64 pagesCCNA 200-125: IP Routing TechnologyAli Alaoui MraniNo ratings yet
- OSPF - Open Shortest Path FirstDocument28 pagesOSPF - Open Shortest Path FirstsatyamgNo ratings yet
- OSPF Summary: The Characteristics of OSPF FollowDocument7 pagesOSPF Summary: The Characteristics of OSPF FollowarubenlNo ratings yet
- OSPF Quick Review 1695007552Document8 pagesOSPF Quick Review 16950075529640515164No ratings yet
- Informal Quick Switch ReferenceDocument109 pagesInformal Quick Switch ReferenceManju DevarajNo ratings yet
- OSPF (Open Shortest Path First)Document21 pagesOSPF (Open Shortest Path First)José Luis PomaNo ratings yet
- OSPF (Open Shortest Path First)Document21 pagesOSPF (Open Shortest Path First)José Luis PomaNo ratings yet
- Lecture 10Document22 pagesLecture 10Abraham GadissaNo ratings yet
- Chapter 11 OSPFDocument53 pagesChapter 11 OSPFCao Hồng MinhNo ratings yet
- 5 - Routing ProtocolsDocument3 pages5 - Routing ProtocolsDarlin DountsNo ratings yet
- Routing Questions-Part-IIDocument6 pagesRouting Questions-Part-IIsumai BagwanNo ratings yet
- Odghspf 1Document5 pagesOdghspf 1Daniel BayodeNo ratings yet
- 100 OSPF Interview Questions and AnswersDocument15 pages100 OSPF Interview Questions and AnswersMD IRFANNo ratings yet
- Ospf Routing ProtocolDocument31 pagesOspf Routing ProtocolAbhishrkNo ratings yet
- Gregsowell Mikrotik RoutingDocument47 pagesGregsowell Mikrotik RoutingSudha GanapareddyNo ratings yet
- NB - Layer 3 - OSPFDocument53 pagesNB - Layer 3 - OSPFMohit SahaiNo ratings yet
- Distance Vector vs. Link State: A B C D X EDocument125 pagesDistance Vector vs. Link State: A B C D X EAtique RezaNo ratings yet
- CCNA-Day3 and 5 Fifth Day Start at 129 SlideDocument188 pagesCCNA-Day3 and 5 Fifth Day Start at 129 SlideAtique Reza0% (1)
- Major Routing Protocols: Submitted By: Saeed Ali Shahani (Intern)Document15 pagesMajor Routing Protocols: Submitted By: Saeed Ali Shahani (Intern)Saeed Ali ShahaniNo ratings yet
- Chapter 7 OSPFDocument35 pagesChapter 7 OSPFnuhonoNo ratings yet
- OSPFDocument3 pagesOSPFjamalnizamNo ratings yet
- Bsci OspfDocument68 pagesBsci OspfEhsan YazdaniNo ratings yet
- Chap 2Document68 pagesChap 2Vladimir NdoyouNo ratings yet
- Lesson 4 - Routing TechnologiesDocument88 pagesLesson 4 - Routing TechnologiesPhan Chi BaoNo ratings yet
- Power PointDocument10 pagesPower Pointmyat69298No ratings yet
- Link State Routing ?: Link-State Routing Protocols Are One of The Two Main Classes ofDocument6 pagesLink State Routing ?: Link-State Routing Protocols Are One of The Two Main Classes ofNikunj PatniNo ratings yet
- Lecture 10 - Routing Part IIIDocument10 pagesLecture 10 - Routing Part IIIyesmuraliNo ratings yet
- Single-Area OSPFv2 ConfigurationDocument56 pagesSingle-Area OSPFv2 Configurationmarwanosama229No ratings yet
- R@thore Interview Prep - v3Document80 pagesR@thore Interview Prep - v3naveedkuNo ratings yet
- Module 2: Single-Area Ospfv2 Configuration: Instructor MaterialsDocument76 pagesModule 2: Single-Area Ospfv2 Configuration: Instructor MaterialsHồngPhúc100% (1)
- Open Short Path Protocol - OSPFDocument78 pagesOpen Short Path Protocol - OSPFomarkhanfar2No ratings yet
- Configuring OspfDocument18 pagesConfiguring Ospfdidigamer46No ratings yet
- Link State UpdatesDocument57 pagesLink State Updatescodebreaker9199No ratings yet
- Introducing The OSPF Protocol Configuring OSPFDocument75 pagesIntroducing The OSPF Protocol Configuring OSPFTung HoangNo ratings yet
- OSPFDocument43 pagesOSPFAftab AlamNo ratings yet
- Ospf Presentation Use Exp2 - ch11Document53 pagesOspf Presentation Use Exp2 - ch11DicNo ratings yet
- Chapter 8: Single-Area OSPF: Instructor MaterialsDocument69 pagesChapter 8: Single-Area OSPF: Instructor MaterialsEdgarNo ratings yet
- Chapter 1. OSPFDocument21 pagesChapter 1. OSPFRam CNo ratings yet
- Configuring Ospf: Robert Pradeepan SrilankaDocument142 pagesConfiguring Ospf: Robert Pradeepan Srilankanvbinh2005No ratings yet
- Configuring IS-ISDocument26 pagesConfiguring IS-ISdfsfsdfsdfdsNo ratings yet
- OSPF (Open Shortest Path First)Document33 pagesOSPF (Open Shortest Path First)sachin prajapatiNo ratings yet
- Cnap 3 Mod 2Document79 pagesCnap 3 Mod 2api-3748967No ratings yet
- OspfDocument24 pagesOspfUmamaheswari KMNo ratings yet
- Ip6 Route Ospfv3Document18 pagesIp6 Route Ospfv3Господь БогNo ratings yet
- Ipv6 Routing: Ospfv3: Finding Feature InformationDocument14 pagesIpv6 Routing: Ospfv3: Finding Feature InformationMarco EspinozaNo ratings yet
- CA - Ex - S2M11 - OSPF - PPT (Compatibility Mode)Document99 pagesCA - Ex - S2M11 - OSPF - PPT (Compatibility Mode)http://heiserz.com/No ratings yet
- Answer:: Networking Interview QuestionsDocument6 pagesAnswer:: Networking Interview QuestionsnaeemNo ratings yet
- Ccna 2 Ospf PDFDocument4 pagesCcna 2 Ospf PDFmacgyver_AdonNo ratings yet
- Ccna 200-301 - 2Document52 pagesCcna 200-301 - 2Wahyudi YusufNo ratings yet
- Level 3Document191 pagesLevel 3Anonymus DeletedNo ratings yet
- OspfDocument57 pagesOspfrudyvampxNo ratings yet
- Ospf - Study: Saravanan ARDocument52 pagesOspf - Study: Saravanan ARdouglosNo ratings yet
- IP Routing Protocols All-in-one: OSPF EIGRP IS-IS BGP Hands-on LabsFrom EverandIP Routing Protocols All-in-one: OSPF EIGRP IS-IS BGP Hands-on LabsNo ratings yet
- In Depth Guide to IS-IS Routing: Learn Intermediate System to Intermediate System Routing from scratchFrom EverandIn Depth Guide to IS-IS Routing: Learn Intermediate System to Intermediate System Routing from scratchNo ratings yet
- Esiee MimoDocument52 pagesEsiee Mimosud_mishraNo ratings yet
- Feb2010 9471 MME R2 0 CPLDocument54 pagesFeb2010 9471 MME R2 0 CPLsud_mishraNo ratings yet
- RRCDocument27 pagesRRCsud_mishraNo ratings yet
- LTE RRC Connection Setup MessagingDocument10 pagesLTE RRC Connection Setup MessagingNagasravika BodapatiNo ratings yet
- LTE Protocol SignalingDocument11 pagesLTE Protocol SignalingKhåïrul Akmar TiminNo ratings yet
- Communication Systems 12: Chair of Communication Systems Department of Applied Sciences University of Freiburg 2006Document53 pagesCommunication Systems 12: Chair of Communication Systems Department of Applied Sciences University of Freiburg 2006sud_mishraNo ratings yet
- UMTS ... : 3G Technology and ConceptsDocument83 pagesUMTS ... : 3G Technology and Conceptssud_mishraNo ratings yet
- Next Generation Ip (Ipv6)Document49 pagesNext Generation Ip (Ipv6)sud_mishraNo ratings yet
- Distance-Vector Routing: Antonio CarzanigaDocument44 pagesDistance-Vector Routing: Antonio Carzanigasud_mishraNo ratings yet
- Ipv4 vs. Ipv6: Anne-Marie Ethier Andrei IoticiDocument21 pagesIpv4 vs. Ipv6: Anne-Marie Ethier Andrei Ioticisud_mishraNo ratings yet