Professional Documents
Culture Documents
12 Pubkey DH Annotated
12 Pubkey DH Annotated
Uploaded by
-Ashrant Shinh-0 ratings0% found this document useful (0 votes)
12 views42 pagesThe document discusses public-key encryption schemes based on the Diffie-Hellman protocol. It summarizes the original ElGamal encryption scheme and then describes variants like Twin ElGamal that aim to prove chosen ciphertext security based on weaker computational assumptions by modifying the original construction. The goal is to prove security without relying on random oracles and based only on the computational Diffie-Hellman assumption in suitable groups.
Original Description:
pub key
Original Title
12 Pubkey Dh Annotated
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document discusses public-key encryption schemes based on the Diffie-Hellman protocol. It summarizes the original ElGamal encryption scheme and then describes variants like Twin ElGamal that aim to prove chosen ciphertext security based on weaker computational assumptions by modifying the original construction. The goal is to prove security without relying on random oracles and based only on the computational Diffie-Hellman assumption in suitable groups.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
12 views42 pages12 Pubkey DH Annotated
12 Pubkey DH Annotated
Uploaded by
-Ashrant Shinh-The document discusses public-key encryption schemes based on the Diffie-Hellman protocol. It summarizes the original ElGamal encryption scheme and then describes variants like Twin ElGamal that aim to prove chosen ciphertext security based on weaker computational assumptions by modifying the original construction. The goal is to prove security without relying on random oracles and based only on the computational Diffie-Hellman assumption in suitable groups.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 42
uan 8oneh
ubllc key encrypuon
from ulme-Pellman
1he LlCamal
ubllc-key SysLem
Cnllne CrypLography Course uan 8oneh
uan 8oneh
8ecap: publlc key encrypuon: (Cen, L, u)
! #
$%
m c c m
&%
'()
uan 8oneh
8ecap: publlc-key encrypuon appllcauons
key exchange (e.g. ln P11S)
Lncrypuon ln non-lnLeracuve semngs:
Secure Lmall: 8ob has Allce's pub-key and sends her an emall
LncrypLed llle SysLems
8ob
wrlLe
L(k
l
, llle)
L(pk
A
, k
l
)
L(pk
8
, k
l
)
Allce
read
llle
sk
A
uan 8oneh
8ecap: publlc-key encrypuon appllcauons
key exchange (e.g. ln P11S)
Lncrypuon ln non-lnLeracuve semngs:
Secure Lmall: 8ob has Allce's pub-key and sends her an emall
LncrypLed llle SysLems
key escrow: daLa recovery wlLhouL 8ob's key
8ob
wrlLe
L(k
l
, llle)
L(pk
escrow
, k
l
)
L(pk
8
, k
l
)
Lscrow
Servlce
sk
escrow
uan 8oneh
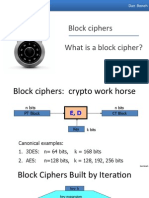
ConsLrucuons
1hls week: Lwo famllles of publlc-key encrypuon schemes
revlous lecLure: based on Lrapdoor funcuons (such as 8SA)
Schemes: lSC sLandard, CAL+, .
1hls lecLure: based on Lhe ulme-Pellman proLocol
Schemes: LlCamal encrypuon and varlanLs (e.g. used ln CC)
SecurlLy goals: chosen clpherLexL securlLy
uan 8oneh
8evlew: Lhe ulme-Pellman proLocol (1977)
llx a nlLe cycllc group C (e.g C = (Z
p
)
*
) of order n
llx a generaLor g ln C (l.e. C = [1, g, g
2
, g
3
, . , g
n-1
} )
*+,-( ./0
choose random 1 ln [1,.,n} choose random 0 ln [1,.,n}
%
*.
2 3
10
= (g
a
)
b
= *
0
.
1
= (g
b
)
a
=
A = g
a
8 = g
b
uan 8oneh
LlCamal: converung Lo pub-key enc. (1984)
llx a nlLe cycllc group C (e.g C = (Z
p
)
*
) of order n
llx a generaLor g ln C (l.e. C = [1, g, g
2
, g
3
, . , g
n-1
} )
*+,-( ./0
choose random 1 ln [1,.,n} choose random 0 ln [1,.,n}
A = g
a
8 = g
b
1reaL as a
publlc key
cL = [ , ]
compuLe g
ab
= A
b
,
derlve symmeLrlc key k ,
encrypL message m wlLh k
uan 8oneh
LlCamal: converung Lo pub-key enc. (1984)
llx a nlLe cycllc group C (e.g C = (Z
p
)
*
) of order n
llx a generaLor g ln C (l.e. C = [1, g, g
2
, g
3
, . , g
n-1
} )
*+,-( ./0
choose random 1 ln [1,.,n} choose random 0 ln [1,.,n}
A = g
a
8 = g
b
1reaL as a
publlc key
cL = [ , ]
compuLe g
ab
= A
b
,
derlve symmeLrlc key k ,
encrypL message m wlLh k
1o decrypL:
compuLe g
ab
= 8
a
,
derlve k, and decrypL
uan 8oneh
1he LlCamal sysLem (a modern vlew)
C: nlLe cycllc group of order n
(L
s
, u
s
) : symmeLrlc auLh. encrypuon dened over (k,M,C)
P: C
2
! k a hash funcuon
We consLrucL a pub-key enc. sysLem (Cen, L, u):
key generauon Cen:
choose random generaLor g ln C and random a ln Z
n
ouLpuL sk = a , pk = (g, h=g
a
)
uan 8oneh
1he LlCamal sysLem (a modern vlew)
!4 $%2435675 87 9
b " Z
n
, u " g
b
, v " h
b
k " P(u,v) , c " L
s
(k, m)
ouLpuL (u, c)
#4 &%215 4:5-7 7 9
v " u
a
k " P(u,v) , m " u
s
(k, c)
ouLpuL m
C: nlLe cycllc group of order n
(L
s
, u
s
) : symmeLrlc auLh. encrypuon dened over (k,M,C)
P: C
2
! k a hash funcuon
8
uan 8oneh
LlCamal performance
!)-;<$=/): 2 exp. (xed basls)
Can pre-compuLe [ g
(2^l)
, h
(2^l)
for l=1,.,log
2
n ]
3x speed-up (or more)
#(-;<$=/): 1 exp. (varlable basls)
!4 $%2435675 87 9
b " Z
n
, u " g
b
, v " h
b
#4 &%215 4:5-7 7 9
v " u
a
uan 8oneh
Lnd of SegmenL
nexL sLep: why ls Lhls sysLem chosen clpherLexL secure?
under whaL assumpuons?
uan 8oneh
ubllc key encrypuon
from ulme-Pellman
LlCamal SecurlLy
Cnllne CrypLography Course uan 8oneh
uan 8oneh
CompuLauonal ulme-Pellman Assumpuon
C: nlLe cycllc group of order n
Comp. uP (CuP) assumpuon holds ln C lf: g, g
a
, g
b
g
ab
for all emclenL algs. A:
r[ A(g, g
a
, g
b
) = g
ab
] < negllglble
where g " [generaLors of C} , a, b " Z
n
uan 8oneh
Pash ulme-Pellman Assumpuon
C: nlLe cycllc group of order n , P: C
2
! k a hash funcuon
#(>: Pash-uP (PuP) assumpuon holds for (C, P) lf:
(g, g
a
, g
b
, P(g
b
,g
ab
) ) =
p
(g, g
a
, g
b
, 8 )
where g " [generaLors of C} , a, b " Z
n
, 8 " k
P acLs as an exLracLor: sLrange dlsLrlbuuon on C
2
unlform on k
1emplaLe
verLLeWhlLe2
Suppose k = [0,1}
128
and
P: C
2
! k only ouLpuLs sLrlngs ln k LhaL begln wlLh 0
( l.e. for all x,y: msb(P(x,y))=0 )
Can Pash-uP hold for (C, P) ?
?es, for some groups C
no, Pash-uP ls easy Lo break ln Lhls case
?es, Pash-uP ls always Lrue for such P
uan 8oneh
LlCamal ls sem. secure under Pash-uP
?(<'(): g " [generaLors of C} , a " Z
n
ouLpuL pk = (g, h=g
a
) , sk = a
#4 &%215 4:5-7 7 9
k " P(u,u
a
) , m " u
s
(k, c)
ouLpuL m
!4 $%2435675 87 9 b " Z
n
k " P(g
b
,h
b
) , c " L
s
(k, m)
ouLpuL (g
b
, c)
uan 8oneh
LlCamal ls sem. secure under Pash-uP
=
p
=
p
=
p
chal. adv. A
pk,sk
m
0
, m
1
g
b
, L
s
(P(), 8
@
)
b'1
pk = (g,g
a
)
chal. adv. A
pk,sk
m
0
, m
1
g
b
, L
s
(P(), 8
A
)
b'1
pk = (g,g
a
)
chal. adv. A
pk,sk
m
0
, m
1
g
b
, L
s
(k, 8
@
)
b'1
pk = (g,g
a
)
k!k
chal. adv. A
pk,sk
m
0
, m
1
g
b
, L
s
(k, 8
A
)
b'1
pk = (g,g
a
)
k!k
(g
b
, g
ab
)
(g
b
, g
ab
)
=
p
uan 8oneh
LlCamal chosen clpherLexL securlLy?
1o prove chosen clpherLexL securlLy need sLronger assumpuon
B)C(;1-=D( #,E(FG(++81) (luP) ln group C:
luP holds ln C lf: (E-,()C *9 H;I * /:C$:C& 3
10
J K )(3+,3,0+(
Chal. Adv. A
(u
1
,v
1
)
g"[gen}
a,b"Z
n
g, h=g
a
, u=g
b
1 lf (u
1
)
a
= v
1
0 oLherwlse
v
wlns lf v=g
ab
uan 8oneh
LlCamal chosen clpherLexL securlLy?
L(-:;,C< M6(/;(8:
lf B#G holds ln Lhe group C, 4!
&
5 #
&
7 provldes auLh. enc.
and G9 C
2
! k ls a random oracle"
Lhen !+'181+ ls CCA
ro
secure.
Cuesuons: (1) can we prove CCA securlLy based on CuP?
(2) can we prove CCA securlLy wlLhouL random oracles?
uan 8oneh
Lnd of SegmenL
uan 8oneh
ubllc key encrypuon
from ulme-Pellman
LlCamal varlanLs
WlLh 8euer SecurlLy
Cnllne CrypLography Course uan 8oneh
uan 8oneh
8evlew: LlCamal encrypuon
?(<'(): g " [generaLors of C} , a " Z
n
ouLpuL pk = (g, h=g
a
) , sk = a
#4 &%215 4:5-7 7 9
k " P(u,u
a
) , m " u
s
(k, c)
ouLpuL m
!4 $%2435675 87 9 b " Z
n
k " P(g
b
,h
b
) , c " L
s
(k, m)
ouLpuL (g
b
, c)
uan 8oneh
LlCamal chosen clpherLexL securlLy
L(-:;,C< M6(/;(8:
lf B#G holds ln Lhe group C, 4!
&
5 #
&
7 provldes auLh. enc.
and G9 C
2
! k ls a random oracle"
Lhen !+'181+ ls CCA
ro
secure.
Can we prove CCA securlLy based on CuP (g, g
a
, g
b
g
ab
) ?
Cpuon 1: use group C where CuP = luP (a.k.a blllnear group)
Cpuon 2: change Lhe LlCamal sysLem
uan 8oneh
varlanLs: Lwln LlCamal [CkS'08]
?(<'(): g " [generaLors of C} , a1, a2 " Z
n
ouLpuL pk = (g, h
1
=g
a1
, h
2
=g
a2
) , sk = (a1, a2)
#4 &%241A51N75 4:5-7 7 9
k " P(u, u
a1
, u
a2
)
m " u
s
(k, c)
ouLpuL m
!4 $%24356
A
56
N
75 87 9 b " Z
n
k " P(g
b
, h
1
b
,
h
2
b
)
c " L
s
(k, m)
ouLpuL (g
b
, c)
uan 8oneh
Chosen clpherLexL securlLy
L(-:;,C< M6(/;(8:
lf O#G holds ln Lhe group C, 4!
&
5 #
&
7 provldes auLh. enc.
and G9 C
3
! k ls a random oracle"
Lhen CP,) !+'181+ ls CCA
ro
secure.
CosL: one more exponenuauon durlng enc/dec
ls lL worLh lL? no one knows .
uan 8oneh
LlCamal securlLy w/o random oracles?
Can we prove CCA securlLy wlLhouL random oracles?
Cpuon 1: use Pash-uP assumpuon ln blllnear groups"
Speclal elllpuc curve wlLh more sLrucLure [CPk'04 + 88'04]
Cpuon 2: use ueclslon-uP assumpuon ln any group [CS'98]
uan 8oneh
lurLher 8eadlng
1he ueclslon ulme-Pellman problem. u. 8oneh, An1S 3, 1998
unlversal hash proofs and a paradlgm for chosen clpherLexL secure publlc
key encrypuon. 8. Cramer and v. Shoup, LurocrypL 2002
Chosen-clpherLexL securlLy from ldenuLy-8ased Lncrypuon.
u. 8oneh, 8. Canem, S. Palevl, and !. kaLz, SlCCM 2007
1he 1wln ulme-Pellman problem and appllcauons.
u. Cash, L. kllLz, v. Shoup, LurocrypL 2008
LmclenL chosen-clpherLexL securlLy vla exLracLable hash proofs.
P. Wee, CrypLo 2010
uan 8oneh
ubllc key encrypuon
from ulme-Pellman
A unlfylng 1heme
Cnllne CrypLography Course uan 8oneh
uan 8oneh
Cne-way funcuons (lnformal)
A funcuon f: x ! ? ls one-way lf
1here ls an emclenL algorlLhm Lo evaluaLe f(), buL
lnverung f ls hard:
for all emclenL A and x " x :
r[ A(f(x)) ] < negllglble
luncuons LhaL are noL one-way: f(x) = x, f(x) = 0
uan 8oneh
Lx. 1: generlc one-way funcuons
LeL f: x ! ? be a secure 8C (where |?| |x| )
(e.g. f bullL uslng deL. counLer mode)
Q(881: f a secure 8C f ls one-way
roof skeLch:
A lnverLs f 8(y) = ls a dlsungulsher
Cenerlc: no speclal properues. ulmculL Lo use for key exchange.
uan 8oneh
Lx 2: 1he uLCC one-way funcuon
llx a nlLe cycllc group C (e.g C = (Z
p
)
*
) of order n
g: a random generaLor ln C (l.e. C = [1, g, g
2
, g
3
, . , g
n-1
} )
#(R)(: f: Z
n
! C as f(x) = g
x
C
Q(881: ulog hard ln C f ls one-way
H;/$(;=(&: f(x), f(y) f(x+y) = f(x) f(y)
key-exchange and publlc-key encrypuon
uan 8oneh
Lx. 3: 1he 8SA one-way funcuon
choose random prlmes p,q "1024 blLs. SeL S2$T.
choose lnLegers ( 5 U s.L. (U 2 A 48/U #4S7 7
#(R)(: f: as f(x) = x
e
ln
Q(881: f ls one-way under Lhe 8SA assumpuon
H;/$(;=(&: f(xy) = f(x) f(y) and > 61& 1 C;1$U//;
uan 8oneh
Summary
ubllc key encrypuon:
made posslble by one-way funcuons
wlLh speclal properues
homomorphlc properues and Lrapdoors
uan 8oneh
Lnd of SegmenL
uan 8oneh
larewell (for now)
Cnllne CrypLography Course uan 8oneh
uan 8oneh
Culck 8evlew: prlmluves
8C
8l, 8 MAC
CCM
C18
CMAC, PMAC
MAC
Colllslon
reslsLance
key
exchange
1rapdoor
luncuons
publlc key
encrypuon
ulme-Pellman
groups
uan 8oneh
Culck 8evlew: prlmluves
M/ $;/C(-C )/)F&(-;(C U1C1: (daLa lnLegrlLy)
uslng small read-only sLorage: use colllslon reslsLanL hash
no read-only space: use MAC . requlres secreL key
M/ $;/C(-C &()&,=D( U1C1: only use auLhenucaLed encrypuon
(eavesdropplng securlLy by lLself ls lnsumclenL)
L(&&,/) &(C:$:
lnLeracuve semngs: use auLhenucaLed key-exchange proLocol
When no-lnLeracuon allowed: use publlc-key encrypuon
uan 8oneh
8emalnlng Core 1oplcs (parL ll)
ulglLal slgnaLures and cerucaLes
AuLhenucaLed key exchange
user auLhenucauon:
passwords, one-ume passwords, challenge-response
rlvacy mechanlsms
Zero-knowledge proLocols
uan 8oneh
Many more Loplcs Lo cover .
Llllpuc Curve CrypLo
CuanLum compuung
new key managemenL paradlgms:
ldenuLy based encrypuon and funcuonal encrypuon
Anonymous dlglLal cash
rlvaLe voung and aucuon sysLems
Compuung on clpherLexLs: fully homomorphlc encrypuon
Lamce-based crypLo
1wo parLy and mulu-parLy compuLauon
uan 8oneh
llnal Words
8e careful when uslng crypLo:
A Lremendous Lool, buL lf lncorrecLly lmplemenLed:
sysLem wlll work, buL may be easlly auacked
Make sure Lo have oLhers revlew your deslgns and code
uon'L lnvenL your own clphers or modes
uan 8oneh
Lnd of parL l
You might also like
- 11 Pubkey Trapdoor AnnotatedDocument55 pages11 Pubkey Trapdoor Annotated-Ashrant Shinh-No ratings yet
- 06 Collision Resistance v2 AnnotatedDocument43 pages06 Collision Resistance v2 AnnotatedMauliawan PrimaNo ratings yet
- 03 Block v2 AnnotatedDocument65 pages03 Block v2 AnnotatedxarenwoNo ratings yet
- 04 Using Block v2 AnnotatedDocument54 pages04 Using Block v2 AnnotatedbodokidNo ratings yet
- ComplexDocument23 pagesComplexrohitmetNo ratings yet
- C++ and Root For PhysicistsDocument55 pagesC++ and Root For PhysicistsMark EdmundNo ratings yet
- Ee 241: Computer Tools For Electrical EngineersDocument24 pagesEe 241: Computer Tools For Electrical EngineersKübra ÇilingirNo ratings yet
- Sqlite Databases: Comp 355 (Muppala) Data Storage 1Document25 pagesSqlite Databases: Comp 355 (Muppala) Data Storage 1Nadilson2012No ratings yet
- HMM TutorialDocument31 pagesHMM TutorialDeetovNo ratings yet
- 08 Odds and Ends v2 AnnotatedDocument49 pages08 Odds and Ends v2 Annotated-Ashrant Shinh-No ratings yet
- On The Calculus of Smarandache FunctionDocument8 pagesOn The Calculus of Smarandache FunctionMia AmaliaNo ratings yet
- Chapter 1 Intro and Basic Concepts: Nominal: Cannot Be Ordered Ordinal: Can Be OrderedDocument40 pagesChapter 1 Intro and Basic Concepts: Nominal: Cannot Be Ordered Ordinal: Can Be OrderedMartijnKruijzenNo ratings yet
- HP-19C & 29C Solutions Mathematics 1977 B&WDocument40 pagesHP-19C & 29C Solutions Mathematics 1977 B&WjjirwinNo ratings yet
- A PASCAL Program For Fitting Non Linear Regression Models On A MicrocomputerDocument3 pagesA PASCAL Program For Fitting Non Linear Regression Models On A MicrocomputerBogdan VicolNo ratings yet
- Assignment3 Zhao ZihuiDocument8 pagesAssignment3 Zhao Zihuizhaozhaozizizi2No ratings yet
- 02.2 Stream AnnotatedDocument13 pages02.2 Stream AnnotatedStefan BalanNo ratings yet
- CCM ArdsDocument84 pagesCCM ArdsAzmachamberAzmacareNo ratings yet
- Semi Simplicial Complexes and Singular HomologyDocument16 pagesSemi Simplicial Complexes and Singular Homologyblexim100% (1)
- Free Energy Calculation in MD SimulationDocument49 pagesFree Energy Calculation in MD SimulationWilliam AgudeloNo ratings yet
- Sant Hosh NotesDocument13 pagesSant Hosh NotesNagendran RajendranNo ratings yet
- Panel Method (2-D) For NACA Four, Five, Six-Digit-Airfoil Series.Document19 pagesPanel Method (2-D) For NACA Four, Five, Six-Digit-Airfoil Series.Kivanc Ali ANILNo ratings yet
- BT3040 - BIOINFORMATICS - Assignment 4: Question 1Document9 pagesBT3040 - BIOINFORMATICS - Assignment 4: Question 1bs19b017 KartikNo ratings yet
- Materi 5 - 2Document25 pagesMateri 5 - 2murteehNo ratings yet
- Ch. 7 Worksheet - ThermochemDocument9 pagesCh. 7 Worksheet - Thermochemkjcninja13No ratings yet
- hw02 Solution PDFDocument9 pageshw02 Solution PDFsiddharth1kNo ratings yet
- Control Systems and Simulation - Prof - Kiran BabuDocument12 pagesControl Systems and Simulation - Prof - Kiran BabuWendy BrassardNo ratings yet
- Begning HTMLDocument26 pagesBegning HTMLram1178206No ratings yet
- Oscillations SHM Solutions PDFDocument2 pagesOscillations SHM Solutions PDFgitha100% (1)
- Img New 0001Document4 pagesImg New 0001amanittaNo ratings yet
- Img 0002 PDFDocument1 pageImg 0002 PDFLeslieNo ratings yet
- Applications and Benefits of Elliptic Curve CryptographyDocument11 pagesApplications and Benefits of Elliptic Curve CryptographyShahriman Dan DianaNo ratings yet
- 13 The Standard SystemDocument23 pages13 The Standard SystemgodwskyNo ratings yet
- A Tutorial On UppaalDocument40 pagesA Tutorial On Uppaaljigar ladhavaNo ratings yet
- Exam 3 SolutionsDocument11 pagesExam 3 SolutionsEarthNo ratings yet
- Conditional Logistic Regression ModelsDocument28 pagesConditional Logistic Regression Modelsds532No ratings yet
- TrigeportDocument5 pagesTrigeportapi-232312177No ratings yet
- Lead Comp en Sat orDocument11 pagesLead Comp en Sat orOscar ChaconNo ratings yet
- Cryptography Assignment SolutionDocument17 pagesCryptography Assignment SolutionWaqar AhmedNo ratings yet
- Toth PDFDocument5 pagesToth PDFCharlie PinedoNo ratings yet
- Control Systems Lab - SC4070: DR - Ir. Alessandro AbateDocument39 pagesControl Systems Lab - SC4070: DR - Ir. Alessandro AbatemakroumNo ratings yet
- Chemical Reactor Design - P. HarriottDocument115 pagesChemical Reactor Design - P. HarriottAnisa Tri HutamiNo ratings yet
- Exercises IIDocument7 pagesExercises IIhendrikNo ratings yet
- Overshoot Free Pi Controller Tuning Based On Pole AssignmentDocument5 pagesOvershoot Free Pi Controller Tuning Based On Pole AssignmentEngr Nayyer Nayyab MalikNo ratings yet
- State Feedback Controller Design: 1 The PlantDocument15 pagesState Feedback Controller Design: 1 The PlantRoberto BucherNo ratings yet
- Biomedical Signal Processing Jan 2014Document1 pageBiomedical Signal Processing Jan 2014Prasad C M100% (1)
- CSE546: Naïve Bayes: Winter 2012Document35 pagesCSE546: Naïve Bayes: Winter 2012ChrisRobyNo ratings yet
- Logic Design July 2005 OldDocument2 pagesLogic Design July 2005 OldPrasad C MNo ratings yet
- Lecture 1Document24 pagesLecture 1anantdrive2103No ratings yet
- DSPDocument15 pagesDSPbbmathiNo ratings yet
- Today's Goal: To Be Able ToDocument40 pagesToday's Goal: To Be Able ToDhanaSelvamNo ratings yet
- MATLAB Full Lab ReportDocument30 pagesMATLAB Full Lab ReportactuatorNo ratings yet
- Carnot's Process: Isothermal Expansion (T Constant, V À V)Document21 pagesCarnot's Process: Isothermal Expansion (T Constant, V À V)Robert CaseNo ratings yet
- fivelumpRB VRmodelParameterDocument5 pagesfivelumpRB VRmodelParameterSopan Ram TambekarNo ratings yet
- Task 3 PPTX KhalidDocument9 pagesTask 3 PPTX Khalidapi-240156957No ratings yet
- Statistics 512 Notes 19Document12 pagesStatistics 512 Notes 19Sandeep SinghNo ratings yet
- Commensurabilities among Lattices in PU (1,n). (AM-132), Volume 132From EverandCommensurabilities among Lattices in PU (1,n). (AM-132), Volume 132No ratings yet
- Simple Algebras, Base Change, and the Advanced Theory of the Trace Formula. (AM-120), Volume 120From EverandSimple Algebras, Base Change, and the Advanced Theory of the Trace Formula. (AM-120), Volume 120No ratings yet
- The Spectral Theory of Toeplitz Operators. (AM-99), Volume 99From EverandThe Spectral Theory of Toeplitz Operators. (AM-99), Volume 99No ratings yet