Professional Documents
Culture Documents
Australian Journal of Basic and Applied Sciences: Article History
Australian Journal of Basic and Applied Sciences: Article History
Uploaded by
Rajesh ManoharanCopyright:
Available Formats
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5825)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (349)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (823)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (403)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- LTE Parameter ListDocument32 pagesLTE Parameter ListmalikmdnuraniNo ratings yet
- 4G Optimization and KPI AnalysisDocument19 pages4G Optimization and KPI AnalysisNABEEL100% (1)
- All Kpi - For Eid v.4 - Ver.aDocument6 pagesAll Kpi - For Eid v.4 - Ver.amalariamenNo ratings yet
- FortiGate-30E Familie PDFDocument4 pagesFortiGate-30E Familie PDFYuran NevesNo ratings yet
- JH016A Datasheet: Quick SpecDocument5 pagesJH016A Datasheet: Quick SpecHardi LimNo ratings yet
- 5g b2b Service Experience Standard White Paper En1Document140 pages5g b2b Service Experience Standard White Paper En1islam ezat0% (1)
- Solution Chapter 10: Exercise 10-1Document16 pagesSolution Chapter 10: Exercise 10-1AHMED MOHAMED YUSUFNo ratings yet
- Network Performance MeasuresDocument9 pagesNetwork Performance MeasuresJess David DoriaNo ratings yet
- Release Note Bianca/Brick-Xl: New System Software: Release 4.8 Revision 6Document56 pagesRelease Note Bianca/Brick-Xl: New System Software: Release 4.8 Revision 6niko67No ratings yet
- Tams 11Document33 pagesTams 11luciano0% (1)
- Product Analysis Report FormatDocument2 pagesProduct Analysis Report FormatNadiva ManopoNo ratings yet
- Datasheet - Exinda 10064Document2 pagesDatasheet - Exinda 10064rikrdo151No ratings yet
- Tibco Perfomance TuningDocument39 pagesTibco Perfomance TuningManoj Ramachandran50% (2)
- Future and Evolving Technologies - Volume 2Document132 pagesFuture and Evolving Technologies - Volume 2Bala KrishnaNo ratings yet
- Performance Analysis of IEEE 802.11ac DCF With Hidden NodesDocument5 pagesPerformance Analysis of IEEE 802.11ac DCF With Hidden NodeskhaldonNo ratings yet
- Ethernet TestDocument16 pagesEthernet TestAmjad AzeemiNo ratings yet
- Appliance BrochureDocument23 pagesAppliance BrochureJulio OliveiraNo ratings yet
- Sage 2016Document8 pagesSage 2016lazyboiNo ratings yet
- 1-16 Cisco Router ThroughputDocument3 pages1-16 Cisco Router ThroughputCassandra ShafferNo ratings yet
- Lecture 2&3 (Network Core, Delays Etc)Document27 pagesLecture 2&3 (Network Core, Delays Etc)Abdullah AnwaarNo ratings yet
- Kafka Reference ArchitectureDocument12 pagesKafka Reference ArchitecturembhangaleNo ratings yet
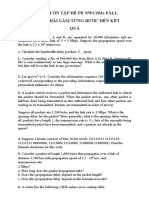
- CAU HOI ON TAP PE NWC203c FALL 2021Document4 pagesCAU HOI ON TAP PE NWC203c FALL 2021hùng cườngNo ratings yet
- FT:FG-1100E Datasheet: Quick SpecDocument5 pagesFT:FG-1100E Datasheet: Quick SpecAkram AlqadasiNo ratings yet
- Airport Capacity and Demand Calculations by Simulation - Extended AbstractDocument6 pagesAirport Capacity and Demand Calculations by Simulation - Extended AbstractbbubaloNo ratings yet
- Huawei LTE Handover EventsDocument21 pagesHuawei LTE Handover Eventsanon_297028107No ratings yet
- LTE Network Performance KPIs - ValidationDocument25 pagesLTE Network Performance KPIs - ValidationsivakumarNo ratings yet
- Low LTE Throughput Due To Inadequate Transmission BandwidthDocument4 pagesLow LTE Throughput Due To Inadequate Transmission BandwidthIschak Chaerudin100% (1)
- Als Series: Alcplus2 Idu Asn OduDocument10 pagesAls Series: Alcplus2 Idu Asn OduManoel RodriguesNo ratings yet
- 3G TOPS Formula Huawei WCDMADocument18 pages3G TOPS Formula Huawei WCDMARao DheeruNo ratings yet
- RW 2050 0100Document3 pagesRW 2050 0100mvasquez2011No ratings yet
Australian Journal of Basic and Applied Sciences: Article History
Australian Journal of Basic and Applied Sciences: Article History
Uploaded by
Rajesh ManoharanOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Australian Journal of Basic and Applied Sciences: Article History
Australian Journal of Basic and Applied Sciences: Article History
Uploaded by
Rajesh ManoharanCopyright:
Available Formats
Australian Journal of Basic and Applied Sciences, 9(7) April 2015, Pages: 698-702
ISSN:1991-8178
Australian Journal of Basic and Applied Sciences
Journal home page: www.ajbasweb.com
Congestion Control in Heterogeneous Wireless Ad hoc Network Using FRCC
1
M. Rajesh and 2J.M Gnanasekar
Research Scholar, Department of Computer Science & Engineering, St.Peter's University Chennai, India
Professor & Head Department of Computer Science & Engineering2, Karpaga Vinayaga College of Engineering & Technology, India.
ARTICLE INFO
Article history:
Received 12 February 2015
Received in revised form 17 March
2015
Accepted 28 March 2015
Available online 17 April 2015
Keywords:
Congestion control, Security, Error
control, Forward Error Correction,
Feedback and Resource based
Congestion
Control,
Encryption
Security algorithms.
ABSTRACT
Congestion control is the major problem in wireless Ad hoc network especially in
broadcasting the packet. In heterogeneous network data should be reliable and secure
the end to end delay of data transmission. So we propose to control the congestion and
error in network using Forward Error Correction (FEC) technique, which will avoid the
error. Feedback and Resource based Congestion Control (FRCC) which will reduce
congestion in transmission channels. In broadcasting, data communications is efficient
and errors are controlled caused by channel noise. The performance of local
broadcasting can be characterized by the mean number of neighbor nodes and
probability distribution of the number of neighbor nodes of broadcasting node. One of
the major challenges is that inter-system interference from different radio access
technologies operating at the same spectrum may significantly degrade the quality of
signal reception. An interesting question that can be raised is how many times a source
node should broadcast a message without the aid of acknowledgement feedback. So
that with a guaranteed probability the message will be successfully received by certain
number of nodes. Encryption Security algorithms can be used for security which
ensures that the data which is sent from the source node reaches the destination node
properly.
2015 AENSI Publisher All rights reserved.
To Cite This Article: M. Rajesh and J.M. Gnanasekar., Congestion Control in Heterogeneous Wireless Ad hoc Network Using FRCC.
Aust. J. Basic & Appl. Sci., 9(7): 698-702, 2015
INTRODUCTION
A WANET is a wireless network where the
wireless nodes can be located anywhere over the
globe. However, the underlying design is such that
the nodes believe they are part of a single-hop or
multi-hop wireless network at the PHY and MAC
layers. This is accomplished by using Software
Defined Access Points (SoDA) that are based on the
idea of Software Defined Radio (SDR). For the
uplink, each SoDA samples the down-converted
channel using an ADC (analog to-digital converter).
The sampled data is then multicast to the other
SoDAs via the Internet. At each end-point, the
received digital signals from the other SoDAs are
summed and sent through the DAC (digital-to-analog
converter) and transmitted on a designated channel
after up conversion. Then the RF environment is
mixed at geographically separate locations (albeit
with a time shift). When the number of packets
increases beyond the limit that can be handled by the
network resources, the network performance
degrades, and this situation is called congestion.
Congestion simply means overcrowding or blockage
due to overloading .It is similar to traffic jam caused
by many cars on a narrow road. Two styles of
control, proactive and reactive control, are presented.
It is shown that congestion control must happen at
several different time scales.
For WANETs where wireless channels are
shared by several motes using carrier sense multiple
access (CSMA-like) protocols, collisions could occur
when multiple active sensor motes try to seize the
channel at the same time. This can be referred to as
link-level
congestion.
Link-level
congestion
increases packet service time, and decreases both
link utilization and overall throughput, and wastes
energy of the sensor motes. There is another type of
congestion called node-level congestion which is
common in conventional networks. It is caused by
buffer overflow in the mote and can result in packet
loss, and increase latency. Packet loss in turn can
lead to retransmission and therefore wastes more
energy. Both link-level and node-level congestions
(illustrated in Figure 1) have direct impact on energy
efficiency and QoS.
Corresponding Author: M. Rajesh, Assistant Professor, The Faculty of Computer Science and Engineering, KRS College
of Engineering, Vandavasi, Tamilnadu, India.
E-mail: rajesmano@gmail.com.
699
M. Rajesh and J.M. Gnanasekar, 2015
Australian Journal of Basic and Applied Sciences, 9(7) April 2015, Pages: 698-702
Existing research is confined to the local
broadcasting in a Stand-alone wireless ad hoc
network without interference (Miorandi, D., 2008;
Haenggi, M., 2008) and with intra-system
interference (Baccelli, F. and B. Blaszczyszyn,
2009).
However,
coexistence
of
multiple
heterogeneous wireless networks emerges in the next
generation wireless networking, and several
challenges are introduced. One of the major
challenges is that inter-system interference from
different radio access technologies operating at the
same spectrum may significantly degrade the quality
of signal reception. Investigations of inter-system
interference in coexisting heterogeneous wireless
networks have focused on spectrum sharing in twotier femtocell networks (Chandrasekhar, V. and J.G.
Andrews, 2009), cellular and ad hoc networks
(Huang, K., 2009), narrowband and ultra-wideband
networks (Pinto, P.C., 2009), and cognitive radio
networks (Rabbachin, A., 2011). More details can be
found in (Haenggi, M., 2009; Weber, S., 2010).
Following this trend, in this paper we study the
performance of local broadcasting in an interferencelimited environment consisting of multiple
heterogeneous wireless ad hoc networks. We explore
the impacts of different error control techniques
(including simple retransmission, Chase combining,
and incremental redundancy (Haenggi, M. and R.K.
Ganti, 2009; Stanojev, I., 2007)) on the mean number
of neighbors and the probability distribution of the
number of neighbors in local broadcasting. With the
probability distribution of the number of neighbors,
QoS provisioning in local broadcasting can be
facilitated. An interesting question that can be raised
is how many times a source node should broadcast a
message without the aid of acknowledgment
feedback (e.g. ACK/NACK) so that with a
guaranteed probability the message will be
successfully received by more than a certain number
of nodes. Via the probability distribution, we may
answer as follows: A source node should broadcast
a message m times so that with probability more
than j nodes will receive the message successfully.
Fig. 1:
Details of the Proposed Scenarios:
The proposed (FRCC) method called error and
congestion control protocol that has two basic
functions responsible for the FEC and FRCC. The
main intention of this protocol is to be used as a
mechanism for reducing congestion in the network
by free resources to set accurate rates and priority
data needs. If two or more nodes send their packets
in the shortest path to the parent node in a crowded
place, a source node must prioritize the data and uses
data that have lower priorities of a suitable detour
nodes consisting of low or non-active consciously.
Due to the limited energy of sensor node, existing
trails will be used instead of creating new routes. The
proposed protocols are tried to increase network
lifetime and the rate of successful packet transfer by
reduction of possibility of packet loss as much as
possible. As we know there are two types of traffic at
each node, local traffic and transmitted traffic. In
fact, each node can act as a source and as routers in
the network. Source traffic is created locally and by
the node itself if the transmitted traffic is created
through other nodes and is sent to the upstream node
to be sent to the scrap. As can be inferred, the tree
structure has a kind of injustice in terms of
bandwidth allocation for sensor network nodes
located at different levels so that nodes near the sink
are given a higher priority but farther nodes have to
send data through intermediate nodes, passing
several steps with great delay.
To solve this problem, Forward Error Correction
(FEC) technique, which will avoid the error, control
the congestion using Feedback and Resource based
Congestion Control (FRCC) which will reduce
congestion in transmission channels.
First: Queuing delay is the primary congestion index.
Second: Packet loss is the next congestion index.
Congestion control strategies based on packet loss to
keep high bandwidth is employed when delay based
strategy act inefficiently.
Proposed algorithm is applied to the network
when these two indexes have been settled. In general
case, proposed algorithm is not applied in normal
case since computation is a time consumer manner.
Proposed algorithm is applied to the nodes near the
base station (which convey more traffic) after the
congestion detection mechanism detected the
congestion and resolved it.
700
M. Rajesh and J.M. Gnanasekar, 2015
Australian Journal of Basic and Applied Sciences, 9(7) April 2015, Pages: 698-702
Description:
Problem Statement:
Objective function to be maximized: s Us (Xs)
(total source utility)
Constraint 1: Xik j:(i.j) L fki,j j:(j,i)L fkj,i
(flow conservation per node-destination pair)
Constraint 2: f (rate in the rate region)
Direct variables: Xs 0 (source rate) fki,j 0
(capacity allocation per link per destination)
Dual relaxation of coupled constraints, with resultant
partial dual D(p) = maxxs 0,fk i,j 0 s Us (Xs)
pki (Xkk - fk i,j + fkj,i
iN,kD,ik
j:(i,j)L
j:(i,j)L
Scheme of the proposed congestion control protocols.
Fig. 2:
At
slower
time
scale,
update
dual
variables pki for all i and k At faster time scale, solve
the following scheduling problem Max fi.j max
(pki - pkj )
fi,j 0
i,j
k
Sub gradient update of dual variables
pki (t+1) = [pki (t) + t (xik p(t)) -( fki,j (p(t) -
fkj,i (p(t)))))]+ , j(i,j)L:(j,i)L where
is the
stepwise.
Distributed Approximate Weighted Maximum
Matching to solve the scheduling problem.
Performance Metrics and Result Analysis:
In this paper we have considered Packet
Delivery Fraction and throughput in Kilo bits per
second (Kbps) for evaluation of RCC, FCC and
FRCC Congestion Control Protocol. The simulation
results obtained with the above mentioned simulation
parameters are appended in Table-1. The graph
showing comparison between RCC, FCC and FRCC
is shown in Figure.3 Packet Delivery Fraction. It is
the ratio of the data packets delivered to the
destinations to those generated by the sources. Packet
Delivery Fraction = Total Packets Delivered to
destination / Total Packets Generated.
701
M. Rajesh and J.M. Gnanasekar, 2015
Australian Journal of Basic and Applied Sciences, 9(7) April 2015, Pages: 698-702
Throughput:
Throughput of the congestion control protocols
means that in certain time the total size of useful
packets that received at all the destination nodes. The
unit of throughput is MB/s, however we have taken
Table 1: Packet Delivery Fraction with varying number of Nodes.
Congestion Control Protocol
Total Packets sent
RCC
9812
FCC
9838
FRCC
9895
Kilo bits per second (Kb/s). The throughput values
obtained for the simulation parameters of table-1 is
tabulated in table-2. The graph shown in figure- 4
indicates the throughput comparison of congestion
control protocols, RCC, FCC and FRCC.
Total packets Received
9073
9176
9874
Packet Delivery Ratio
0.9248
0.9327
0.9979
Fig. 3: Packet Delivery Fraction.
Table 2: Throughput in speed with varying number of Nodes.
Throughput in speed with varying number of Nodes
No. of
20
50
75
.Nodes
RCC
1770.41
1600.34
1999.18
FCC
4034.64
4600.76
5002.64
FRCC
6554.53
7002.67
9979.99
100
2102.4
5454.36
8044.33
Fig. 4: No of Nodes versus Throughput.
Conclusion:
In this paper we have evaluated the performance
of FRCC congestion control protocol for ad hoc
networks. FRCC uses the proactive table-driven
congestion control strategy here as FEC uses the
reactive on demand error control strategy with
different control mechanisms. Experimental results
showed that FRCC perform better for Packet
Delivery Fraction as well as Throughput.
702
M. Rajesh and J.M. Gnanasekar, 2015
Australian Journal of Basic and Applied Sciences, 9(7) April 2015, Pages: 698-702
Due to the importance of Congestion Control for
Wireless Ad hoc network, we presented a model for
congestion control in WANETs. The main intention
of this protocol is to be used as a mechanism for
reducing congestion in the network by free resources
to set accurate rates and priority data needs. If two or
more nodes send their packets in the shortest path to
the parent node in a crowded place, a source node
must prioritize the data and uses data that have lower
priorities of a suitable detour nodes consisting of low
or non-active consciously. Proposed algorithm
(FRCC) is not applied in normal case since
computation is a time consumer manner. Proposed
algorithm (FRCC) is applied to the nodes near the
base station (which convey more traffic) after the
error and congestion detection; control the error in
network using Forward Error Correction (FEC)
technique, which will avoid the error, control the
congestion using Feedback and Resource based
Congestion Control (FRCC) which will reduce
congestion in transmission channels.
REFERENCES
Andrews, M. and L. Zhang, 2008. Satisfying
Arbitrary Delay Requirements in Multihop
Networks, Proc. IEEE 27th Conf. Computer
Comm., pp: 116-120.
Baccelli, F. and B. Blaszczyszyn, 2009.
Stochastic geometry and wireless networks volume
2: applications, Found. Trends Netw., 4(1-2): 1-312.
Badis, H. and K.A. Agha, 2005. QOLSR, QoS
Routing for Ad Hoc Wireless Networks Using
OLSR, European Trans. Telecomm., 16(5): 427442.
Chandrasekhar, V. and J.G. Andrews, 2009.
Uplink capacity and interference avoidance for twotier femtocell networks, IEEE Trans. Wireless
Commun., 8(7): 3498-3509.
Ganguly, S., V. Navda, K. Kim, A. Kashyap, D.
Niculescu, R. Izmailov, S. Hong and S. Das, 2006.
Performance Optimizations for Deploying VoIP
Services in Mesh Networks, IEEE J. Selected Areas
in Comm., 24(11): 2147-2158.
Haenggi, M. and R.K. Ganti, 2009. Interference
in large wireless networks,Found. Trends Netw., 3:
127-248.
Haenggi, M., 2008. A geometric interpretation
of fading in wireless networks: theory and
applications, IEEE Trans. Inf. Theory, 54(12):
5500-5510.
Haenggi, M., J.G. Andrews, F. Baccelli, O.
Dousse and M. Franceschetti, 2009. Stochastic
geometry and random graphs for the analysis and
design of wireless networks, IEEE J. Sel. Areas
Commun., 27(7): 1029-1046.
Huang, K., V.K.N. Lau and Y. Chen, 2009.
Spectrum sharing between cellular and mobile ad
hoc networks: transmission-capacity trade-off, IEEE
J. Sel. Areas Commun., 27(7): 1256-1267.
Hwang, Y. and P. Varshney, 2003. An
Adaptive QoS Routing Protocol with Dispersity for
Ad-Hoc Networks, Proc. 36th Ann. Hawaii Intl
Conf. System Sciences, pp: 302a.
Kim, J., H. Jin, D.K. Sung and R. Schober,
2010. Optimization of wireless multicast systems
employing hybrid-ARQ with Chase combining,
IEEETrans. Veh. Technol., 59(7): 3342-3355.
Miorandi, D., E. Altman and G. Alfano, 2008.
The impact of channel randomnesson coverage and
connectivity of ad hoc and sensor networks, IEEE
Trans. Wireless Commun., 7(3): 1062-1072.
Pinto, P.C., A. Giorgetti, M.Z. Win and M.
Chiani, 2009. A stochastic geometry approach to
coexistence in heterogeneous wireless networks,
IEEE J. Sel. Areas Commun., 27(7): 1268-1282.
Rabbachin, A., T.Q.S. Quek, H. Shin and M.Z.
Win, 2011. Cognitive network interference, IEEE
J. Sel. Areas Commun., 29(2): 480-493.
Shah, S. and K. Nahrstedt, 2002. Predictive
Location-Based QoS Routing in Mobile Ad Hoc
Networks, Proc. IEEE Intl Conf. Comm., 2: 10221027.
Shin, S. and H. Schulzrinne, 2009.
Measurement and Analysis of the VoIP Capacity in
IEEE 802.11 WLAN, IEEE Trans. Mobile
Computing, 8(9): 1265-1279.
So-In, C., R. Jain and A.K. Tamimi, 2009.
Scheduling in IEEE 802.16e Mobile WiMAX
Networks: Key Issues and a Survey, IEEE J.
Selected Areas in Comm., 27(2): 156-171.
Stanojev, I., O. Simeone, Y. Bar-Ness and D.
Kim, 2007. On the energy efficiency of hybridARQ protocols in fading channels, in Proc. IEEE
ICC.
Wang, F., A. Ghosh, C. Sankaran, P. Fleming, F.
Hsieh and S. Benes, 2008. Mobile WiMAX
Systems: Performance and Evolution,IEEE Comm.
Magazine, 46(10): 41-49.
Weber, S., J.G. Andrews and N. Jindal, 2010.
An overview of the transmission capacity of
wireless networks, IEEE Trans. Commun., 56(12):
3593-3604.
Xue, Q. and A. Ganz, 2003. Ad Hoc QoS OnDemand Routing (AQOR) in Mobile Ad Hoc
Networks, J. Parallel and Distributed Computing,
63(2): 154-165.
Zhiqiang Shi, D. Ionescu, Dongli Zhang, 2013.
A Token Based Method for Congestion and Packet
Loss Control Latin America Transactions, IEEE
(Revista IEEE America Latina) 11(2).
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5825)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (349)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (823)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (403)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- LTE Parameter ListDocument32 pagesLTE Parameter ListmalikmdnuraniNo ratings yet
- 4G Optimization and KPI AnalysisDocument19 pages4G Optimization and KPI AnalysisNABEEL100% (1)
- All Kpi - For Eid v.4 - Ver.aDocument6 pagesAll Kpi - For Eid v.4 - Ver.amalariamenNo ratings yet
- FortiGate-30E Familie PDFDocument4 pagesFortiGate-30E Familie PDFYuran NevesNo ratings yet
- JH016A Datasheet: Quick SpecDocument5 pagesJH016A Datasheet: Quick SpecHardi LimNo ratings yet
- 5g b2b Service Experience Standard White Paper En1Document140 pages5g b2b Service Experience Standard White Paper En1islam ezat0% (1)
- Solution Chapter 10: Exercise 10-1Document16 pagesSolution Chapter 10: Exercise 10-1AHMED MOHAMED YUSUFNo ratings yet
- Network Performance MeasuresDocument9 pagesNetwork Performance MeasuresJess David DoriaNo ratings yet
- Release Note Bianca/Brick-Xl: New System Software: Release 4.8 Revision 6Document56 pagesRelease Note Bianca/Brick-Xl: New System Software: Release 4.8 Revision 6niko67No ratings yet
- Tams 11Document33 pagesTams 11luciano0% (1)
- Product Analysis Report FormatDocument2 pagesProduct Analysis Report FormatNadiva ManopoNo ratings yet
- Datasheet - Exinda 10064Document2 pagesDatasheet - Exinda 10064rikrdo151No ratings yet
- Tibco Perfomance TuningDocument39 pagesTibco Perfomance TuningManoj Ramachandran50% (2)
- Future and Evolving Technologies - Volume 2Document132 pagesFuture and Evolving Technologies - Volume 2Bala KrishnaNo ratings yet
- Performance Analysis of IEEE 802.11ac DCF With Hidden NodesDocument5 pagesPerformance Analysis of IEEE 802.11ac DCF With Hidden NodeskhaldonNo ratings yet
- Ethernet TestDocument16 pagesEthernet TestAmjad AzeemiNo ratings yet
- Appliance BrochureDocument23 pagesAppliance BrochureJulio OliveiraNo ratings yet
- Sage 2016Document8 pagesSage 2016lazyboiNo ratings yet
- 1-16 Cisco Router ThroughputDocument3 pages1-16 Cisco Router ThroughputCassandra ShafferNo ratings yet
- Lecture 2&3 (Network Core, Delays Etc)Document27 pagesLecture 2&3 (Network Core, Delays Etc)Abdullah AnwaarNo ratings yet
- Kafka Reference ArchitectureDocument12 pagesKafka Reference ArchitecturembhangaleNo ratings yet
- CAU HOI ON TAP PE NWC203c FALL 2021Document4 pagesCAU HOI ON TAP PE NWC203c FALL 2021hùng cườngNo ratings yet
- FT:FG-1100E Datasheet: Quick SpecDocument5 pagesFT:FG-1100E Datasheet: Quick SpecAkram AlqadasiNo ratings yet
- Airport Capacity and Demand Calculations by Simulation - Extended AbstractDocument6 pagesAirport Capacity and Demand Calculations by Simulation - Extended AbstractbbubaloNo ratings yet
- Huawei LTE Handover EventsDocument21 pagesHuawei LTE Handover Eventsanon_297028107No ratings yet
- LTE Network Performance KPIs - ValidationDocument25 pagesLTE Network Performance KPIs - ValidationsivakumarNo ratings yet
- Low LTE Throughput Due To Inadequate Transmission BandwidthDocument4 pagesLow LTE Throughput Due To Inadequate Transmission BandwidthIschak Chaerudin100% (1)
- Als Series: Alcplus2 Idu Asn OduDocument10 pagesAls Series: Alcplus2 Idu Asn OduManoel RodriguesNo ratings yet
- 3G TOPS Formula Huawei WCDMADocument18 pages3G TOPS Formula Huawei WCDMARao DheeruNo ratings yet
- RW 2050 0100Document3 pagesRW 2050 0100mvasquez2011No ratings yet