Professional Documents
Culture Documents
CS 010 803 Security in Computing
CS 010 803 Security in Computing
Uploaded by
Celex Varghese0 ratings0% found this document useful (0 votes)
9 views2 pages1. The document is a model question paper for the eighth semester course "Security in Computing" for the Computer Science and Engineering branch.
2. It contains three parts - Part A contains 5 multiple choice questions carrying 3 marks each. Part B contains 5 questions carrying 5 marks each requiring short explanations. Part C contains 5 questions carrying 12 marks each that require longer explanations of security concepts and algorithms.
3. The questions cover a wide range of security topics including ciphers, encryption algorithms like DES and RSA, digital signatures, Kerberos, intrusion detection, viruses and security services.
Original Description:
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Document1. The document is a model question paper for the eighth semester course "Security in Computing" for the Computer Science and Engineering branch.
2. It contains three parts - Part A contains 5 multiple choice questions carrying 3 marks each. Part B contains 5 questions carrying 5 marks each requiring short explanations. Part C contains 5 questions carrying 12 marks each that require longer explanations of security concepts and algorithms.
3. The questions cover a wide range of security topics including ciphers, encryption algorithms like DES and RSA, digital signatures, Kerberos, intrusion detection, viruses and security services.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
9 views2 pagesCS 010 803 Security in Computing
CS 010 803 Security in Computing
Uploaded by
Celex Varghese1. The document is a model question paper for the eighth semester course "Security in Computing" for the Computer Science and Engineering branch.
2. It contains three parts - Part A contains 5 multiple choice questions carrying 3 marks each. Part B contains 5 questions carrying 5 marks each requiring short explanations. Part C contains 5 questions carrying 12 marks each that require longer explanations of security concepts and algorithms.
3. The questions cover a wide range of security topics including ciphers, encryption algorithms like DES and RSA, digital signatures, Kerberos, intrusion detection, viruses and security services.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 2
1
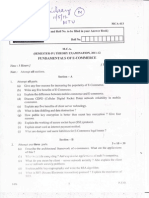
MODEL QUESTION PAPER B.Tech Degree Examination
Eighth Semester
Branch : Computer Science and Engineering
CS 010 803 - SECURITY IN COMPUTING (CS)
(New Scheme - Regular)
Time : Three Hours
Maximum : 100 Marks
Answer all questions.
Part A
Each question carries 3 marks.
1. What is meant by denial of service attack?
2. Differentiate between stream cipher and block cipher?
3. List the functions used to produce authenticator?
4. What are limitations of firewalls?
5. What are the different types of intruders?
(5 x 3 = 15 marks)
Part B
Each question carries 5 marks.
6. With an example, explain Playfair Cipher ?
7. Write a note on Diffie Hellman key exchange?
8. With a neat diagram, explain the general format of X.509 certificate?
9. What do you mean by Transport mode and Tunnel mode? Differentiate between them.
10. Briefly explain techniques used to avoid guessable passwords?
(5 x 5 = 25 marks)
Part C
Each question carries 12 marks.
Module 1
11. Briefly explain different security mechanisms and security services.
Or
12. Explain transposition and substitution ciphers in detail.
Module 2
13. Explain about DES algorithm and its avalanche effect.
Or
14. Explain RSA algorithm. Discuss the three possible approaches to attack RSA algorithm.
Module 3
15. Explain how to generate and verify digital signatures.
Or
16. Explain about Kerberos version 4. Differentiate Kerberos version 4 and version 5.
Module 4
17. Explain about S/MIME.
Or
18. Explain about Pretty Good Privacy.
Module 5
19. Explain different approaches on intrusion detection?
Or
20. Explain about viruses and its related threats?
(5 x 12 = 60 marks)
You might also like
- Name: ID:: End ExamDocument3 pagesName: ID:: End ExamRamesh Babu BattulaNo ratings yet
- It010 802 Cryptography and Network Security: B.Tech Degree Examination, May 2014Document3 pagesIt010 802 Cryptography and Network Security: B.Tech Degree Examination, May 2014GeorgeStenNo ratings yet
- Cryptography Model Question Paper Mca 5th SemDocument4 pagesCryptography Model Question Paper Mca 5th SemSanthosh B Acharya100% (1)
- CSS Paper 2nd YearDocument1 pageCSS Paper 2nd YearlalitmguptaamuNo ratings yet
- Diploma Board Examination - December 2020Document2 pagesDiploma Board Examination - December 2020kathirdcnNo ratings yet
- Information Security June 2010Document2 pagesInformation Security June 2010Suganya PeriasamyNo ratings yet
- Jntuworld: Network Security and CryptographyDocument1 pageJntuworld: Network Security and CryptographycomputerstudentNo ratings yet
- Network Security QuestionDocument1 pageNetwork Security QuestionathirayanNo ratings yet
- Fundamental of E - Commerce4Document2 pagesFundamental of E - Commerce4Ayush GargNo ratings yet
- Sathyabama-IIIsem-Network Security-783301Document2 pagesSathyabama-IIIsem-Network Security-783301ShankarNo ratings yet
- IV-I-Reg-NETWORK SECURITY & CRYPTOGRAPHYDocument2 pagesIV-I-Reg-NETWORK SECURITY & CRYPTOGRAPHYbodhu varunNo ratings yet
- Question BankDocument5 pagesQuestion BankNavneeth GnlNo ratings yet
- Mca 501 Computer Security: Each Question Carries 3 MarksDocument2 pagesMca 501 Computer Security: Each Question Carries 3 MarksToby ThomasNo ratings yet
- Data Communication Networks Nec 702B PDFDocument2 pagesData Communication Networks Nec 702B PDFomenderNo ratings yet
- NSC 2Document2 pagesNSC 2raju rama raj kumarNo ratings yet
- Questionbank CryptoDocument4 pagesQuestionbank CryptoSantoshNo ratings yet
- Neural Networks-Question PaperDocument2 pagesNeural Networks-Question PaperSanjanaNo ratings yet
- T215B - MTA - Spring 2014-2015 AKDocument7 pagesT215B - MTA - Spring 2014-2015 AKChristina FingtonNo ratings yet
- B. Tech. Examination: Roll No. ........................Document2 pagesB. Tech. Examination: Roll No. ........................Pawan KumarNo ratings yet
- B. Tech. Examination: Roll No. ........................Document2 pagesB. Tech. Examination: Roll No. ........................Monu PareekNo ratings yet
- Ilovepdf MergedDocument21 pagesIlovepdf Mergedd.soniNo ratings yet
- 07TE762Document2 pages07TE762Shiva ShankarNo ratings yet
- Network and Information SecurityDocument2 pagesNetwork and Information SecuritySuveetha SuviNo ratings yet
- Computer Communication & Networking (Ec602) : Group ADocument3 pagesComputer Communication & Networking (Ec602) : Group Asg1983No ratings yet
- Computer NetworksDocument4 pagesComputer NetworksSavari RajNo ratings yet
- Cryptography Question-BankDocument5 pagesCryptography Question-BankTriveni KulkarniNo ratings yet
- (CS6701 PTCS6701)Document3 pages(CS6701 PTCS6701)Russian CarxgameNo ratings yet
- CRYPTOGAPHYDocument4 pagesCRYPTOGAPHYVivek ShuklaNo ratings yet
- WWW - Manaresults.Co - In: (Computer Science and Engineering)Document2 pagesWWW - Manaresults.Co - In: (Computer Science and Engineering)Ravikumar BhimavarapuNo ratings yet
- Information Systems SecurityDocument4 pagesInformation Systems SecurityShakti SriNo ratings yet
- MCS 042Document3 pagesMCS 042shivshankar shahNo ratings yet
- MCS 042Document3 pagesMCS 042shivshankar shahNo ratings yet
- Model Question Paper Two Year M.Tech Degree End Examinations Computer Science & Engineering Third Semester Network Security & Cryptography (NSC)Document1 pageModel Question Paper Two Year M.Tech Degree End Examinations Computer Science & Engineering Third Semester Network Security & Cryptography (NSC)api-279049687No ratings yet
- Mid Sem CNS FAQDocument3 pagesMid Sem CNS FAQmayurikasoni0No ratings yet
- CNS Question BankDocument3 pagesCNS Question BankNitya JaniNo ratings yet
- 54115-mt - Network Security & CryptographyDocument1 page54115-mt - Network Security & CryptographySRINIVASA RAO GANTA100% (1)
- Crypto Question BankDocument2 pagesCrypto Question Bankjohnabrahim1010No ratings yet
- Apollo Group of Colleges: Cs 2354 - Advanced Computer ArchitectureDocument2 pagesApollo Group of Colleges: Cs 2354 - Advanced Computer ArchitectureJagan NathanNo ratings yet
- B.Tech IV Year I Semester (R15) Regular Examinations November/December 2018Document5 pagesB.Tech IV Year I Semester (R15) Regular Examinations November/December 2018pruthviNo ratings yet
- Final 06Document2 pagesFinal 06Moudi MouhamadouNo ratings yet
- MTA Makeup Spring 2014 PDFDocument8 pagesMTA Makeup Spring 2014 PDFChristina FingtonNo ratings yet
- Write The Examination Using Blue or Black Pen Draw Neat Sketch With Pencil (If Necessary) Use Tables or Charts (If Necessary) Answer All QuestionsDocument1 pageWrite The Examination Using Blue or Black Pen Draw Neat Sketch With Pencil (If Necessary) Use Tables or Charts (If Necessary) Answer All QuestionsJanarish Saju CNo ratings yet
- MODEL QUESTION PAPER - B.Tech Degree Examination: CS010 804L01: E-COMMERCEDocument2 pagesMODEL QUESTION PAPER - B.Tech Degree Examination: CS010 804L01: E-COMMERCEsaranya pugazhenthiNo ratings yet
- Assignment Final Term NetworksDocument4 pagesAssignment Final Term NetworksMuhammad AliNo ratings yet
- (B) Write The Algorithm of RSA and Explain With An ExampleDocument2 pages(B) Write The Algorithm of RSA and Explain With An ExampleShanmugapriyaVinodkumarNo ratings yet
- (Sem. Vi) Even Theory Examination 2012-13: PAPER ID: 2474Document2 pages(Sem. Vi) Even Theory Examination 2012-13: PAPER ID: 2474123vidyaNo ratings yet
- 2018 Advanced Computer Network and Security CSEM-204: Time Allotted: 3 Hours Full Marks: 70Document2 pages2018 Advanced Computer Network and Security CSEM-204: Time Allotted: 3 Hours Full Marks: 70SAFIKURESHI MONDALNo ratings yet
- Testing of Vlsi Circuits: Answer All Questions Each Question Carries 25 MarksDocument2 pagesTesting of Vlsi Circuits: Answer All Questions Each Question Carries 25 MarksAnonymous gwdxvOcoqNo ratings yet
- Cryptography and System SecurityDocument1 pageCryptography and System Securitygowona4117No ratings yet
- Networking Sample Exam Questions - 2003-4 Semester 2Document4 pagesNetworking Sample Exam Questions - 2003-4 Semester 2abraha gebruNo ratings yet
- 6.CNS Unit Wise Question BankDocument2 pages6.CNS Unit Wise Question BankRajNo ratings yet
- MCS 042 Previous Year Question Papers by IgnouassignmentguruDocument58 pagesMCS 042 Previous Year Question Papers by IgnouassignmentguruAbhi kumarNo ratings yet
- 153 - Embedded Systems (Sem - II) (Main)Document1 page153 - Embedded Systems (Sem - II) (Main)Sangeetha BajanthriNo ratings yet
- ISE Question PapersDocument21 pagesISE Question Papersd.soniNo ratings yet
- Cryptography Quest Bank 02Document7 pagesCryptography Quest Bank 02Gurpreet SinghNo ratings yet
- MCA-505 (E) : M.C.A. V Semester Network SecurityDocument2 pagesMCA-505 (E) : M.C.A. V Semester Network Securityabhinavgiri17No ratings yet
- 3.nov 2011 PDFDocument2 pages3.nov 2011 PDFkarthickamsecNo ratings yet
- Networking Sample Exam Questions Marking Scheme - 2003-4 Semester 2Document9 pagesNetworking Sample Exam Questions Marking Scheme - 2003-4 Semester 2abraha gebruNo ratings yet
- M. Tech. Semester - I: Data Mining and Data Warehousing (MCSSE 104)Document10 pagesM. Tech. Semester - I: Data Mining and Data Warehousing (MCSSE 104)saurabh1116No ratings yet
- Analytical Modeling of Wireless Communication SystemsFrom EverandAnalytical Modeling of Wireless Communication SystemsNo ratings yet
- St. Joseph's College of Engineering & Technology PalaiDocument12 pagesSt. Joseph's College of Engineering & Technology PalaiCelex VargheseNo ratings yet
- Dap Guang Xiang - 1458611671284 PDFDocument32 pagesDap Guang Xiang - 1458611671284 PDFCelex VargheseNo ratings yet
- HPC Question Bank From SNGCE, KadayirippuDocument3 pagesHPC Question Bank From SNGCE, KadayirippuCelex VargheseNo ratings yet
- HhiolDocument39 pagesHhiolCelex VargheseNo ratings yet
- Depth First SearchDocument1 pageDepth First SearchCelex VargheseNo ratings yet
- CS010 804 L06 Advanced Networking TrendsDocument2 pagesCS010 804 L06 Advanced Networking TrendsCelex VargheseNo ratings yet