Professional Documents
Culture Documents
0 ratings0% found this document useful (0 votes)
17 viewsg42GSM Security
g42GSM Security
Uploaded by
Manoj KumarCopyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5825)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (349)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (823)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (403)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Sales SopDocument19 pagesSales SopFelix Mwanduka100% (1)
- 1 Report Jan 2014 - June 2014Document1 page1 Report Jan 2014 - June 2014Manoj KumarNo ratings yet
- IpaddressDocument46 pagesIpaddressManoj KumarNo ratings yet
- UPS BatteryDocument1 pageUPS BatteryManoj KumarNo ratings yet
- Nokia Flasher Dejan 1.00 ManualDocument5 pagesNokia Flasher Dejan 1.00 ManualManoj KumarNo ratings yet
- Back To The BibleDocument2 pagesBack To The BibleManoj KumarNo ratings yet
- NodeB MML&Alarm VerDocument24 pagesNodeB MML&Alarm Verhi_demirel118978% (9)
- A Hand Book ON Billing and Customer Care System IN GSM NetworkDocument19 pagesA Hand Book ON Billing and Customer Care System IN GSM NetworkGuna SekarNo ratings yet
- Common Service Spares For U-Power and Omega 01012015Document1 pageCommon Service Spares For U-Power and Omega 01012015smartechengineering.infoNo ratings yet
- Business Marketing Management-WDDocument81 pagesBusiness Marketing Management-WDMaruko ChanNo ratings yet
- Exercise 4aDocument7 pagesExercise 4aMinh Thư Lưu NguyễnNo ratings yet
- Catalina DQDocument49 pagesCatalina DQecho chenNo ratings yet
- Project Activity 3 - Social CodingDocument3 pagesProject Activity 3 - Social CodingJoel DolotNo ratings yet
- Ug 146 PDFDocument36 pagesUg 146 PDFTrần LinhNo ratings yet
- CT122 6987062 enUS Om 05-12Document218 pagesCT122 6987062 enUS Om 05-12Henry HuayhuaNo ratings yet
- The Design of Garment Enterprise Data Warehouse Using TOGAFDocument9 pagesThe Design of Garment Enterprise Data Warehouse Using TOGAFsentyNo ratings yet
- Machine Learning Dev Ops Engineer Nanodegree Program SyllabusDocument16 pagesMachine Learning Dev Ops Engineer Nanodegree Program Syllabuskerlos ZakryNo ratings yet
- Determination of Natural Gas Recovery Factors: JC.p/66:"'D3Document15 pagesDetermination of Natural Gas Recovery Factors: JC.p/66:"'D3Hector MarzanaNo ratings yet
- A Course On Geographic Data Science: Dani Arribas-BelDocument4 pagesA Course On Geographic Data Science: Dani Arribas-BelKrishna LodhaNo ratings yet
- Subject: ACI-ICAO Implementing Annex 14 Course: (Cairo, Egypt, 28 June - 2 July 2020)Document2 pagesSubject: ACI-ICAO Implementing Annex 14 Course: (Cairo, Egypt, 28 June - 2 July 2020)Osama SharafNo ratings yet
- Acer Aspire 3610 - Wistron Morar - Rev SBDocument40 pagesAcer Aspire 3610 - Wistron Morar - Rev SBPer JensenNo ratings yet
- Chapter 4 Three Phase Uncontrolled Rectifier (Compatibility Mode)Document17 pagesChapter 4 Three Phase Uncontrolled Rectifier (Compatibility Mode)Apry PermatasariNo ratings yet
- Micronta VoxClock 3 - Owners Manual & Schematic - Cat. 63-906Document11 pagesMicronta VoxClock 3 - Owners Manual & Schematic - Cat. 63-906HoeiNo ratings yet
- 25NB To 65NB Duplex Basket StrainerDocument1 page25NB To 65NB Duplex Basket Straineraloke2mondalNo ratings yet
- Şelale, Çevik Ve Yalin Alti Sigma Proje Yönetimi Metodolojilerinin Başari Faktörlerinin Bulanik Bilişsel Haritalama Yöntemi İle DeğerlendirilmesiDocument70 pagesŞelale, Çevik Ve Yalin Alti Sigma Proje Yönetimi Metodolojilerinin Başari Faktörlerinin Bulanik Bilişsel Haritalama Yöntemi İle DeğerlendirilmesiAhmet Emre EĞRİNo ratings yet
- Domain Name Registration Data Lookup: DatesDocument1 pageDomain Name Registration Data Lookup: DatesBrad JohnsonNo ratings yet
- KC 60335-2-98Document17 pagesKC 60335-2-98le duc huynhNo ratings yet
- Context Diagram of Proposed Hotel Reservation Management SystemDocument8 pagesContext Diagram of Proposed Hotel Reservation Management SystemJoffrey Montalla67% (3)
- Suresh AadharDocument1 pageSuresh AadharApcare14No ratings yet
- Chap6 - Engineering Measurements and EstimationsDocument36 pagesChap6 - Engineering Measurements and EstimationsalsinanhananNo ratings yet
- Cable-Catalogue BR enDocument72 pagesCable-Catalogue BR enmuhammedNo ratings yet
- BSCADocument39 pagesBSCAROOMA SALEEMNo ratings yet
- RWC 2: Jetblue Airways, Westjet Airlines, and OthersDocument9 pagesRWC 2: Jetblue Airways, Westjet Airlines, and Othersriya7sen67% (3)
- Simularea Reţelei În Cisco Packet TracerDocument6 pagesSimularea Reţelei În Cisco Packet TracerFlorin AlexandruNo ratings yet
- App 001 PresentationDocument23 pagesApp 001 PresentationReign Crizzelle BarridNo ratings yet
- Synopsis Project Title E-Health Care Management System: College of Management and Computer Sicnece, YavatmalDocument6 pagesSynopsis Project Title E-Health Care Management System: College of Management and Computer Sicnece, YavatmalAshish MOHARENo ratings yet
g42GSM Security
g42GSM Security
Uploaded by
Manoj Kumar0 ratings0% found this document useful (0 votes)
17 views17 pagesCopyright
© Attribution Non-Commercial (BY-NC)
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
17 views17 pagesg42GSM Security
g42GSM Security
Uploaded by
Manoj KumarCopyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 17
GSM Security
Helsinki University of Technology
S-38.153 Security of Communication Protocols
Mikko.Suominen@hut.fi
15.4.2003
Contents
Introduction
GSM security mechanisms
GSM security concerns
Conclusion
15.4.2003 GSM Security - Mikko Suominen 2
Introduction
Global System for Mobile communications
Specified by ETSI
Digital cellular communications system
High mobility (international roaming)
Services
Voice communication, Short Messaging Service,
call waiting, call forwarding, calling line identity,
circuit-switched data (packet-switched data with
GPRS)
15.4.2003 GSM Security - Mikko Suominen 3
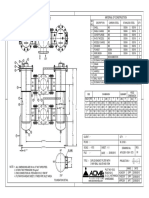
GSM Architecture
15.4.2003 GSM Security - Mikko Suominen 4
Network Databases (1)
The network subsystem uses the following
databases for the authentication and security
purposes
The HLR database contains all administrative
information about each registered user of a GSM
network along with the current location of the MS
The VLR tracks mobiles that are out of their home
network, so that the network will know where to find
them
15.4.2003 GSM Security - Mikko Suominen 5
Network Databases (2)
The EIR contains a list of each MS IMEI allowed on
the network
White listed – Allowed to connect to the network
Grey listed – Under observation for possible problems
Black listed – Not allowed to connect to the network
The AUC database contains:
IMSI: International Mobile Subscriber Identity
TMSI: Temporary Mobile Subscriber Identity
LAI: Location Area Identity
Ki: Authentication Key
15.4.2003 GSM Security - Mikko Suominen 6
Security Measures in GSM
PIN code (authentication of SIM = local security
measure, network not involved)
User authentication (performed by network)
Ciphering of information sent over air interface
Usage of TMSI (instead of IMSI) over air
interface
15.4.2003 GSM Security - Mikko Suominen 7
PIN Code
Personal Identification Number
Stored in SIM card
Asked when phone is switched on
If 3 faulty PIN inputs Æ longer Personal
Unblocking Key (PUK) code is asked
If 10 faulty PUK inputs Æ SIM card is locked
Æ new card from operator
15.4.2003 GSM Security - Mikko Suominen 8
User Authentication
Authentication key (Ki) is never sent over radio interface!
15.4.2003 GSM Security - Mikko Suominen 9
Ciphering in GSM
For each call a new ciphering key (Kc) is generated
during authentication!
15.4.2003 GSM Security - Mikko Suominen 10
Summary of Algorithms Used
15.4.2003 GSM Security - Mikko Suominen 11
Usage of TMSI (1)
IMSI uniquely identifies the subscriber
Rather than sending IMSI, TMSI is sent
This prevents the intruder from
gaining information on the resources the user
is using
tracing the location of the user
matching the user and the transmitted signal
15.4.2003 GSM Security - Mikko Suominen 12
Usage of TMSI (2)
TMSI is sent to MS after the authentication
procedure has taken place
Mapping of the TMSI to the IMSI is done by the
network and is typically handled by the VLR
IMSI is sent only when necessary, for example
when the SIM is used for the first time
when there is data loss at VLR
15.4.2003 GSM Security - Mikko Suominen 13
Security through Obscurity
Authentication and encryption algorithms
were never made public
Whole security model developed in secret
Suspicion that cryptographic algorithms are
weak
Although never published, ciphering algorithm
A5 has been reverse engineered!
15.4.2003 GSM Security - Mikko Suominen 14
SIM Wars: Attack of the Clones
Cloning of SIM cards is possible
Extract Ki from SIM by means of side-channel
attack
Can retrieve Ki with as little as 8 adaptively
chosen plaintexts within a minute
Needs physical access to SIM and equipment
that is not found from people’s garages (at
least at the moment)
15.4.2003 GSM Security - Mikko Suominen 15
Other Concerns
Only air interface transmission is
encrypted
Ciphering key (Kc) used for encryption is
only 54 bits long
MS is authenticated to the BS, but the BS
is not authenticated to the MS Æ false
base stations (man-in-the-middle attack)
15.4.2003 GSM Security - Mikko Suominen 16
Conclusion
GSM still is a reasonably secure cellular
telecommunications system
However there are some concerns
End-to-end security is not provided
No open algorithms tested by engineering
community
SIM cloning is a real threat
15.4.2003 GSM Security - Mikko Suominen 17
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5825)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (349)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (823)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (403)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Sales SopDocument19 pagesSales SopFelix Mwanduka100% (1)
- 1 Report Jan 2014 - June 2014Document1 page1 Report Jan 2014 - June 2014Manoj KumarNo ratings yet
- IpaddressDocument46 pagesIpaddressManoj KumarNo ratings yet
- UPS BatteryDocument1 pageUPS BatteryManoj KumarNo ratings yet
- Nokia Flasher Dejan 1.00 ManualDocument5 pagesNokia Flasher Dejan 1.00 ManualManoj KumarNo ratings yet
- Back To The BibleDocument2 pagesBack To The BibleManoj KumarNo ratings yet
- NodeB MML&Alarm VerDocument24 pagesNodeB MML&Alarm Verhi_demirel118978% (9)
- A Hand Book ON Billing and Customer Care System IN GSM NetworkDocument19 pagesA Hand Book ON Billing and Customer Care System IN GSM NetworkGuna SekarNo ratings yet
- Common Service Spares For U-Power and Omega 01012015Document1 pageCommon Service Spares For U-Power and Omega 01012015smartechengineering.infoNo ratings yet
- Business Marketing Management-WDDocument81 pagesBusiness Marketing Management-WDMaruko ChanNo ratings yet
- Exercise 4aDocument7 pagesExercise 4aMinh Thư Lưu NguyễnNo ratings yet
- Catalina DQDocument49 pagesCatalina DQecho chenNo ratings yet
- Project Activity 3 - Social CodingDocument3 pagesProject Activity 3 - Social CodingJoel DolotNo ratings yet
- Ug 146 PDFDocument36 pagesUg 146 PDFTrần LinhNo ratings yet
- CT122 6987062 enUS Om 05-12Document218 pagesCT122 6987062 enUS Om 05-12Henry HuayhuaNo ratings yet
- The Design of Garment Enterprise Data Warehouse Using TOGAFDocument9 pagesThe Design of Garment Enterprise Data Warehouse Using TOGAFsentyNo ratings yet
- Machine Learning Dev Ops Engineer Nanodegree Program SyllabusDocument16 pagesMachine Learning Dev Ops Engineer Nanodegree Program Syllabuskerlos ZakryNo ratings yet
- Determination of Natural Gas Recovery Factors: JC.p/66:"'D3Document15 pagesDetermination of Natural Gas Recovery Factors: JC.p/66:"'D3Hector MarzanaNo ratings yet
- A Course On Geographic Data Science: Dani Arribas-BelDocument4 pagesA Course On Geographic Data Science: Dani Arribas-BelKrishna LodhaNo ratings yet
- Subject: ACI-ICAO Implementing Annex 14 Course: (Cairo, Egypt, 28 June - 2 July 2020)Document2 pagesSubject: ACI-ICAO Implementing Annex 14 Course: (Cairo, Egypt, 28 June - 2 July 2020)Osama SharafNo ratings yet
- Acer Aspire 3610 - Wistron Morar - Rev SBDocument40 pagesAcer Aspire 3610 - Wistron Morar - Rev SBPer JensenNo ratings yet
- Chapter 4 Three Phase Uncontrolled Rectifier (Compatibility Mode)Document17 pagesChapter 4 Three Phase Uncontrolled Rectifier (Compatibility Mode)Apry PermatasariNo ratings yet
- Micronta VoxClock 3 - Owners Manual & Schematic - Cat. 63-906Document11 pagesMicronta VoxClock 3 - Owners Manual & Schematic - Cat. 63-906HoeiNo ratings yet
- 25NB To 65NB Duplex Basket StrainerDocument1 page25NB To 65NB Duplex Basket Straineraloke2mondalNo ratings yet
- Şelale, Çevik Ve Yalin Alti Sigma Proje Yönetimi Metodolojilerinin Başari Faktörlerinin Bulanik Bilişsel Haritalama Yöntemi İle DeğerlendirilmesiDocument70 pagesŞelale, Çevik Ve Yalin Alti Sigma Proje Yönetimi Metodolojilerinin Başari Faktörlerinin Bulanik Bilişsel Haritalama Yöntemi İle DeğerlendirilmesiAhmet Emre EĞRİNo ratings yet
- Domain Name Registration Data Lookup: DatesDocument1 pageDomain Name Registration Data Lookup: DatesBrad JohnsonNo ratings yet
- KC 60335-2-98Document17 pagesKC 60335-2-98le duc huynhNo ratings yet
- Context Diagram of Proposed Hotel Reservation Management SystemDocument8 pagesContext Diagram of Proposed Hotel Reservation Management SystemJoffrey Montalla67% (3)
- Suresh AadharDocument1 pageSuresh AadharApcare14No ratings yet
- Chap6 - Engineering Measurements and EstimationsDocument36 pagesChap6 - Engineering Measurements and EstimationsalsinanhananNo ratings yet
- Cable-Catalogue BR enDocument72 pagesCable-Catalogue BR enmuhammedNo ratings yet
- BSCADocument39 pagesBSCAROOMA SALEEMNo ratings yet
- RWC 2: Jetblue Airways, Westjet Airlines, and OthersDocument9 pagesRWC 2: Jetblue Airways, Westjet Airlines, and Othersriya7sen67% (3)
- Simularea Reţelei În Cisco Packet TracerDocument6 pagesSimularea Reţelei În Cisco Packet TracerFlorin AlexandruNo ratings yet
- App 001 PresentationDocument23 pagesApp 001 PresentationReign Crizzelle BarridNo ratings yet
- Synopsis Project Title E-Health Care Management System: College of Management and Computer Sicnece, YavatmalDocument6 pagesSynopsis Project Title E-Health Care Management System: College of Management and Computer Sicnece, YavatmalAshish MOHARENo ratings yet