Professional Documents
Culture Documents
Z08 Lecture 1 - 2
Z08 Lecture 1 - 2
Uploaded by
Veeresh BaligeriOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Z08 Lecture 1 - 2
Z08 Lecture 1 - 2
Uploaded by
Veeresh BaligeriCopyright:
Available Formats
DS DCN
Distributed Systems Security Authentication Principles - 1
Prof. Steve Wilbur s.wilbur@cs.ucl.ac.uk
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
DS DCN
Lecture Objectives
u u u u Define authentication Identify types of protocols needed Identify threats Examine classic protocols based on SKC and identify weaknesses
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1-2
Page 1
1
DS DCN
Authentication
u Assurance that messages are from claimed originator u Generally implies that original message has not been tampered with - message integrity u Does not necessarily imply secrecy Mutual authentication: Two parties satisfy themselves of each others identity usually for long term (session or transaction) interaction u One-way Authentication: One party is authenticated, eg. your login to Unix u
1-3
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
DS DCN
Cryptography
u Use cryptography to achieve these functions u Need keys to be distributed u Key distribution different for PKC and SKC u Need Key Distribution Protocols u Need PKC and SKC protocols u Also, need message oriented (single-ended) protocols and stream oriented (two-way) protocols
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1-4
Page 2
2
DS DCN
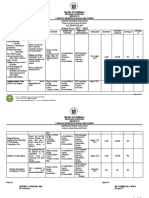
Basic Protocol Map
u We will use the following map to keep our bearings as we explore the various protocols
Shared Key (SKC) Key Distribution One-way Authentication Two-way Authentication
Shared Key Distribution One-way SKC
Public Key (PKC)
Public Key Distribution One-way PKC
Two-way SKC
Two-way PKC
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1-5
DS DCN
Notation
A, B U, V E S Kx Ks {Data}K Principals - good guys eg. Alice, Bob Domains - organisations eg. UCL, IBM Eavesdropper - bad guys, eg. Eve Security server/service Personal key of x Session key Data encrypted with key K
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1-6
Page 3
3
DS DCN
SKC Key Distribution
u For A, B to communicate securely they need to share a key u This could be achieved by:
1. Providing pair-wise keys for all possible communications to all relevant parties 2. Shared key selected by A and physically transmitted to B 3. Third party selects key and physically delivers it to A and B 4. If A and B already have secure communication, one party can select a new key and transmit using old key 5. If A and B have secure communication to third party S. S can provide shared key via these secure connections
1-7
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
DS DCN
SKC Key Distribution - 2
u For a population of N users, approach 1 requires N(N-1)/2 keys u May be just about feasible for small populations, but e.g. N=1,000 needs about 500,000 keys and N=10,000 needs about 50M keys u Also, keys used for long periods become more vulnerable to cryptanalysis, so would need to change them periodically/frequently u Physical delivery is generally inappropriate for routine key distribution in distributed systems, 2 and 3 are not suitable
1-8
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
Page 4
4
DS DCN
SKC Key Distribution - 3
u Approach 4 can be used, but needs an existing secure session u Approach 5 is attractive. It requires that S shares a key with each member of population u Thus, need to distribute N-1 keys, not N(N-1)/2 u Hierarchy of keys:
o Session keys o End user/application personal keys shared with first level KDC o Repeated for higher level KDCs
1-9
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
DS DCN
Two-way SKC Authentication
u Assume A, B already have their own personal keys, Ka and Kb (do not know each others key) u Each key is shared with trusted third party, S, such that S knows private keys of both A and B u S known as Authentication Server (AS) or Key Distribution Centre (KDC) u Protocol needed to distribute session key securely and mutually authenticate A and B u Note: A and B both trust S, since S holds their personal keys
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 10
Page 5
5
DS DCN
Two-Way Authentication
Protocol is broadly of form below Ka, Kb are Personal Keys Ks is the Session Key
1 2 Authentication Server - S
Ka
Kb
Ka
Client - A Ks 3 4
Server - B Ks
Kb
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 11
DS DCN
Needham & Schroeder SKC Protocol
S A B
u A, B are parties involved u S is Authentication Server u Ka, Kb are personal keys of A, B known only to owner and S u I is nonce used once only u Ks is conversation key or session key generated by S u , indicates message composition or concatenation
Authentication with SKC 1. 2. 3. 4. 5. 6. A->S: S->A: A->B: B->A: A->B: A<->B: A, B, Ia1 {Ia1, B, Ks, {Ks, A}Kb }Ka {Ks, A}Kb {Ib}Ks {f(Ib)}Ks {Data}Ks
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 12
Page 6
6
DS DCN
Needham & Schroeder SKC Protocol - 2
u Steps 1 to 3 are used to distribute session key to A and B u Step 3 also indicates to B that S has only distributed this key to A (and B) u Steps 3 to 5 deal with mutual authentication and live-ness indicating to both parties that message 3 was not a replay u Can extend it to deal with multiple domains (see over) u KDCs use similar protocol with a super-KDC they all trust
1 - 13
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
DS DCN
Needham & Schroeder Multiple Domains
Su Sv A B
Authentication with Secret Keys 1. A->Su: A, B, Ia1 {Ks, B, A, Ia1}Ksas {{Ks, A}Kb, Ia1, A}Ksas {Ia1, B, Ks, {Ks, A}Kb }Ka {Ks, A}Kb {Ib}Ks {f(Ib)}Ks
u As before, plus: u Su, Sv are Authentication Servers u Ka, Kb are secret keys of A, B known only to owner & Su, Sv resp. u Ksas is conversation key between authentication servers
1a. Su->Sv: 1b. Sv->Su: 2. 3. 4. 5. Su->A: A->B: B->A: A->B:
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 14
Page 7
7
DS DCN
Needham & Schroeder Protocol Issues
u What is purpose of nonce? u What forms of attack are possible?
o Simple replay o Backward replay o Nonce attacks
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 15
DS DCN
Needham & Schroeder Weakness
u Simple replay of msg 3 to B by E may cause confusion at A if session has closed, but otherwise is relatively harmless u However, if an old session key has been compromised and E can suppress selected messages to A, then replay of msg 3 will cause B to have session with E thinking it is A u Denning suggested use of timestamps to overcome this u Because nonces give no indication of freshness of message
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 16
Page 8
8
DS DCN
Denning SKC Protocol
S A B
u A, B are parties involved u S is Authentication Server u Ka, Kb are personal keys of A, B known only to owner and S u T is timestamp u Ks is conversation key or session key generated by S u , indicates message composition or concatenation
Authentication with SKC 1. A->S: 2. S->A: 3. A->B: 4. B->A: 5. A->B: 6. A<->B: A, B {T, B, Ks, {Ks, A, T}Kb }Ka {Ks, A, T}Kb {Ib}Ks {f(Ib)}Ks {Data}Ks
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 17
DS DCN
Denning SKC Protocol - 2
u Basically same protocol as Needham &Schroeder, except timestamp generated by S used instead of nonce u Message considered valid if on receipt: Clock - T< t1 + t2 where
o t1 is max. allowed discrepancy between KDC and local clock o t2 is max. network delay
Z08
u Provided Bs personal key not compromised, only replay of message 3 is possible and timestamp thwarts this attack
1 - 18
MSc in Data Communications Networks and Distributed Systems, UCL
Page 9
9
DS DCN
Denning Protocol Issues
u Clocks must be synchronised, so need secure clock synchronisation protocol u If recipient clock can be advanced, accidentally or by sabotage, protocol messages could be replayed again at a valid time u Frequent clock synchronisation with KDC is one solution u Neuman and Stubblebine [1993] proposed protocol to remove this requirement using nonces again
1 - 19
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
DS DCN
Neuman and Stubblebine SKC Protocol
S A B
Z08
u A, B are parties involved u S is Authentication Server u Ka, Kb are personal keys of A, B known only to owner and S u Tb is time limit for session key u Ia, Ib are nonces u Ks is conversation key or session key generated by S u , indicates message composition or concatenation
Authentication with SKC 1. A->B: 2. B->S: 3. S->A: A, Ia B, Ib, {A, Ia, Tb}Kb {B, Ia, Ks, Tb}Ka, {A, Ks, Tb}Kb, Ib 4. A->B: 5. A<->B: {A, Ks, Tb}Kb, {Ib}Ks {Data}Ks
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 20
Page 10
10
DS DCN
Neuman and Stubblebine SKC Protocol - 2
u Impervious to clock sabotage or session key cracking u Assumes Ka and Kb not compromised u Nonce Ia is bound to Ks within short space of time via protocol synchronisation not clock sync. u Similarly, Ib is bound to Ks u Tb provides a validity period for the session key u {A, Ks, Tb}Kb acts as a ticket or authenticator for A with B, indicating session key and validity period
1 - 21
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
DS DCN
Neuman and Stubblebine SKC Protocol - 3
A B
u Can avoid repeated KDC exchanges by use of ticket within validity period u Tb is relative to Bs clock so no clock sync. issue Z08
Creation of new session 1. A->B: 2. B->A: 3. A->B: 4. A<->B: {A, Ks, Tb}Kb, Ia Ib, {Ia}Ks {Ib}Ks {Data}Ks
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 22
Page 11
11
DS DCN
Single-ended Authentication
u In some applications parties are not necessarily available simultaneously, e.g. e-mail u Ideally, we would like to have mutual authentication so that A knows only B can read message and B knows that it could only have come from A u If not possible to have 2-way dialogue, assurances may be weaker u Note: this is not strictly one-way authentication
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 23
DS DCN
Needham & Schroeder Single-ended Authentication
S A B
u Single-ended system, e.g. email u As before, plus: u TS is senders timestamp u Sn is serial number of message fragment u Recipient must check for possible replays (via max. clock asynchrony and estimated delivery delay)
Authentication with Secret Keys 1. A->S: 2. S->A: 3. A->B: A, B, Ia1 {Ia1, B, Ks, {Ks, A}Kb }Ka {Ks, A}Kb, {TS,S1, Mess1}Ks, {S2,Mess2}Ks, ..
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 24
Page 12
12
DS DCN
E-mail Protocols
u This can form the basis of secure e-mail protocols u However, e-mail is often distributed by the originator to several recipients so there are additional threats and additional service requirements u What might they be? u See Pretty Good Privacy (PGP) and Privacy Enhanced Mail (PEM) for more details
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 25
DS DCN
Further Reading
u W Stallings, Cryptography and Network Security: Principles and Practice, 2ed, Prentice Hall, 1999, 0-13869017-0 o Key Distribution: pp 141-149 o Authentication: pp 303-311 o Pretty Good Privacy: pp 356-374 C Pfleeger, Security in Computing, 2ed, Prentice Hall, 1997, 0-13-185794-0 o Privacy Enhanced Mail: pp 422-426
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 26
Page 13
13
DS DCN
Further Reading - 2
u R Needham & M Schroeder, Using Encryption for Authentication in Large Networks of Computers, CACM, Dec 1978 D Denning, Cryptography and Data Security, AddisonWesley, 1982 B Neuman & S Stubblebine, A Note on the use of Timestamps as Nonces, ACM Operating Systems Review, 1993
Z08
MSc in Data Communications Networks and Distributed Systems, UCL
1 - 27
Page 14
14
You might also like
- 7230 Repaso Exam 2Document10 pages7230 Repaso Exam 2iuser1900100% (1)
- I Will Do b2b Lead Generation, Prospect List Building and Web ScrapingDocument7 pagesI Will Do b2b Lead Generation, Prospect List Building and Web Scrapingshymal_No ratings yet
- CISSP Exam Prep Questions, Answers & Explanations: 1500+ CISSP Practice Questions with SolutionsFrom EverandCISSP Exam Prep Questions, Answers & Explanations: 1500+ CISSP Practice Questions with SolutionsRating: 3 out of 5 stars3/5 (7)
- The CIPP Model For EvaluationDocument15 pagesThe CIPP Model For Evaluationfangg100% (1)
- Network Security UNIT 2Document30 pagesNetwork Security UNIT 2smitcse2021No ratings yet
- Key Management and DistributionDocument32 pagesKey Management and DistributionsansureNo ratings yet
- Module 3-2ND Half NotesDocument24 pagesModule 3-2ND Half NotesSrinidhi MNo ratings yet
- IGNOU Mca Network Solved AssignmentDocument15 pagesIGNOU Mca Network Solved AssignmentKamal TiwariNo ratings yet
- Key ManagementDocument24 pagesKey ManagementSubhiAlkourdeNo ratings yet
- Lecture 5Document41 pagesLecture 5yeabsiramulualemNo ratings yet
- Key Management and DistributionDocument38 pagesKey Management and Distributionabb acNo ratings yet
- cns4 1Document12 pagescns4 1gadidheerajreddy.20.itNo ratings yet
- UNIT-4 Key Distribution & ManagementDocument53 pagesUNIT-4 Key Distribution & ManagementBharath Kumar T VNo ratings yet
- UNIT 7 - S - P Key DistributionDocument36 pagesUNIT 7 - S - P Key DistributionCool BoyNo ratings yet
- Osi Seven Layers Model Explained With ExamplesDocument11 pagesOsi Seven Layers Model Explained With ExamplesbarkatwaganNo ratings yet
- Quantum Password Sharing Scheme Using Trusted Servers: International Journal of Information & Network Security (IJINS)Document4 pagesQuantum Password Sharing Scheme Using Trusted Servers: International Journal of Information & Network Security (IJINS)stephenlim7986No ratings yet
- CCN 2021 (Final A Part)Document8 pagesCCN 2021 (Final A Part)farhad.hossain.hstu43No ratings yet
- Cryptography and Network SecurityDocument23 pagesCryptography and Network SecurityJunaid MalikNo ratings yet
- Notes 3 5Document60 pagesNotes 3 5sangee20039No ratings yet
- Key Management and Distribution: UNIT-4Document36 pagesKey Management and Distribution: UNIT-4jyoshna yenamalaNo ratings yet
- 1 Topics Covered: Lecture 5: September 18, 1997Document5 pages1 Topics Covered: Lecture 5: September 18, 1997Lorena StrechieNo ratings yet
- Ijesat 2012 02 Si 01 16Document7 pagesIjesat 2012 02 Si 01 16Ijesat JournalNo ratings yet
- NSP CST434 Sample QP SolvedDocument27 pagesNSP CST434 Sample QP SolvedASHNA ANo ratings yet
- AnaValid-ProtocSécurité V3.1Document15 pagesAnaValid-ProtocSécurité V3.1nyamsi claude bernardNo ratings yet
- ST Mary Security AnswerDocument7 pagesST Mary Security AnswerBehaylu ByaNo ratings yet
- (IJCT-V2I2P10) Authors :E.Mukundhan, R.VeeramaniDocument4 pages(IJCT-V2I2P10) Authors :E.Mukundhan, R.VeeramaniIjctJournalsNo ratings yet
- Advanced 2 13Document62 pagesAdvanced 2 13MichelleNo ratings yet
- OSI Seven Layers Model Explained With ExamplesDocument10 pagesOSI Seven Layers Model Explained With ExamplesHammad Nisar100% (1)
- CN Manual SocketDocument4 pagesCN Manual SocketSneha KanwadeNo ratings yet
- Study of Socket Programming and Client SDocument4 pagesStudy of Socket Programming and Client Snkprannesh12No ratings yet
- SPINS: Security Protocols For Sensor Networks: Adrian Perrig, Robert Szewczyk, Victor Wen, David Culler, J.D. TygarDocument18 pagesSPINS: Security Protocols For Sensor Networks: Adrian Perrig, Robert Szewczyk, Victor Wen, David Culler, J.D. TygarSalah EddineNo ratings yet
- Secure Transmission Services in Wireless Networks Using Key TreesDocument7 pagesSecure Transmission Services in Wireless Networks Using Key Treessurendiran123No ratings yet
- Unit-5 Part-1Document7 pagesUnit-5 Part-1sachinchoudhary1610No ratings yet
- Practical WLAN SecurityDocument7 pagesPractical WLAN SecurityArsène CAKPONo ratings yet
- Detailed Narration Script SOC Analyst 11 15Document3 pagesDetailed Narration Script SOC Analyst 11 152022mt13231No ratings yet
- Lecture 12: Public-Key Cryptography and The RSA Algorithm Lecture Notes On "Computer and Network Security"Document90 pagesLecture 12: Public-Key Cryptography and The RSA Algorithm Lecture Notes On "Computer and Network Security"Anshu MittalNo ratings yet
- Computer Systems Security (Cs-426)Document2 pagesComputer Systems Security (Cs-426)Jehangir Adil VakilNo ratings yet
- Part 0Document29 pagesPart 0Shivansh PundirNo ratings yet
- Transport Layer Security (TLS) : DSL AdslDocument4 pagesTransport Layer Security (TLS) : DSL AdslSohaib QaisarNo ratings yet
- Authenticated Key Exchange in Dtns Using Public Key ExchangeDocument3 pagesAuthenticated Key Exchange in Dtns Using Public Key ExchangeInternational Journal of Scientific Research in Science, Engineering and Technology ( IJSRSET )No ratings yet
- Case Studies: Needham - Schroeder, Kerberos, TLS, 802.11 WifiDocument2 pagesCase Studies: Needham - Schroeder, Kerberos, TLS, 802.11 WifiJoy BagdiNo ratings yet
- Lecture 13-14 Digital Signature ApplicationsDocument31 pagesLecture 13-14 Digital Signature ApplicationsAmr HatemNo ratings yet
- (Bluebee Uet - Com) 1472960712dethiso1 k53khmtDocument3 pages(Bluebee Uet - Com) 1472960712dethiso1 k53khmtZhu Ghe LiangNo ratings yet
- Combined Efficient WSN Key Protocol For Internet of ThingsDocument20 pagesCombined Efficient WSN Key Protocol For Internet of ThingsK Asif RiadNo ratings yet
- NC Sem 4Document8 pagesNC Sem 4divyasharmade98No ratings yet
- NIS Slide 6Document21 pagesNIS Slide 6Soumak PoddarNo ratings yet
- Rsa 1Document94 pagesRsa 1llcoolj11413No ratings yet
- Anonymous Routing in Wireless Networks: Onion Routing: Priyanka BanerjeeDocument36 pagesAnonymous Routing in Wireless Networks: Onion Routing: Priyanka BanerjeeJatin VyasNo ratings yet
- Sem in A RioDocument77 pagesSem in A RioVehap CurriNo ratings yet
- Osi ModelDocument11 pagesOsi ModelMu Asif KhNo ratings yet
- Unit 8Document87 pagesUnit 8testNo ratings yet
- CNS Unit 4Document11 pagesCNS Unit 4Arti DwivediNo ratings yet
- Cryptography and The Smart GridDocument21 pagesCryptography and The Smart GridJoseph_NuamahNo ratings yet
- PeDocument46 pagesPehieucybNo ratings yet
- Final Synopsis Sem 4new-HarshadDocument6 pagesFinal Synopsis Sem 4new-HarshadsuvarnbhushanNo ratings yet
- Cloud Multidomain Access Control Based On Role Access: AbstractDocument6 pagesCloud Multidomain Access Control Based On Role Access: AbstractManoj BabuNo ratings yet
- Computer Network 1Document17 pagesComputer Network 1Surendra Singh ChauhanNo ratings yet
- Quality of Service in A Software-Defined Network: Dennis Chan University of California, Los AngelesDocument14 pagesQuality of Service in A Software-Defined Network: Dennis Chan University of California, Los AngelesBob BobboNo ratings yet
- Chap 05 PDFDocument21 pagesChap 05 PDFSidney100% (1)
- Computer Security EITA25: Final Exam inDocument6 pagesComputer Security EITA25: Final Exam inGeorges karamNo ratings yet
- REPORTED SPEECH: Present Simple: Grammar QuizDocument1 pageREPORTED SPEECH: Present Simple: Grammar QuizCINTHYA AIDA ESPINOZA AYALANo ratings yet
- Clean and Simple - ResumUP - SampleDocument3 pagesClean and Simple - ResumUP - SampleVineethKurnalaNo ratings yet
- Module 7 21st Century LiteratureDocument26 pagesModule 7 21st Century LiteratureAmelyn Goco Mañoso87% (31)
- MEchanics and CriteriaDocument1 pageMEchanics and CriteriaAlexander Bermejo Avila100% (1)
- Year 2 English Yearly PlanDocument16 pagesYear 2 English Yearly Planகவியரசு முனுசாமிNo ratings yet
- Learning Styles Self AssessmentDocument6 pagesLearning Styles Self Assessmentedrian de leonNo ratings yet
- SYNCTAG - Listed Products PDFDocument3 pagesSYNCTAG - Listed Products PDFKumar Kaushish M.No ratings yet
- Guidelines in Career Guidance PortfolioDocument3 pagesGuidelines in Career Guidance PortfolioMa Quin Cio100% (1)
- Law School Study TipsDocument4 pagesLaw School Study TipsHanna MapandiNo ratings yet
- Action Plan School Year: 2022 - 2023Document6 pagesAction Plan School Year: 2022 - 2023Mark GutangNo ratings yet
- Nepal Telecom History Book 1973-2072Document409 pagesNepal Telecom History Book 1973-2072mkg_just4u8932No ratings yet
- Observation Checklist For Annie and KierstenDocument3 pagesObservation Checklist For Annie and Kierstenapi-462727619No ratings yet
- 36212-910 - Multiplexing and Channel CodingDocument60 pages36212-910 - Multiplexing and Channel CodingumtsrfNo ratings yet
- Profile of Tele Phone IndustryDocument5 pagesProfile of Tele Phone IndustryRavi JoshiNo ratings yet
- Brie Gutzmans ResumeDocument1 pageBrie Gutzmans Resumeapi-242723472No ratings yet
- QCM TelecomDocument3 pagesQCM TelecomChhengmean SimNo ratings yet
- CISB 412 Social and Professional IssuesDocument28 pagesCISB 412 Social and Professional IssuesRonald SuritaNo ratings yet
- Personal and Social Development: Children DevelopDocument21 pagesPersonal and Social Development: Children DevelopMark TiongsonNo ratings yet
- 1st Quarter Exam EAPPDocument5 pages1st Quarter Exam EAPPedzil almogueraNo ratings yet
- 7 DomainsDocument10 pages7 Domainsmarinel franciscoNo ratings yet
- PLC Survey - 14-15 - Google FormsDocument39 pagesPLC Survey - 14-15 - Google Forms5cr1bdedNo ratings yet
- Case Study 8 10 AJ TeforaDocument9 pagesCase Study 8 10 AJ TeforaHannah EdañoNo ratings yet
- Unit Title Reading and Use of English WritingDocument1 pageUnit Title Reading and Use of English WritingAOCNo ratings yet
- The Use of Debate in English Writing Class: Noriko IWAMOTODocument12 pagesThe Use of Debate in English Writing Class: Noriko IWAMOTOScarletRoseNo ratings yet
- Nagbalaye High School: Directions: Listen To The Song "WHAT A WONDERFUL WORLD" by LOUIS ARMSTRONGDocument4 pagesNagbalaye High School: Directions: Listen To The Song "WHAT A WONDERFUL WORLD" by LOUIS ARMSTRONGArnel EsongNo ratings yet
- UTIHP UTSC Executive Committee Applications !Document3 pagesUTIHP UTSC Executive Committee Applications !YoserAl-ArashiNo ratings yet
- Five Ways Technology Is Changing Human Behavior: Teknologi Komunikasi Dan Perubahan PerilakuDocument2 pagesFive Ways Technology Is Changing Human Behavior: Teknologi Komunikasi Dan Perubahan Perilakuentah siapaNo ratings yet
- Teaching Eng VovabularyDocument22 pagesTeaching Eng VovabularyMAAZNo ratings yet