Professional Documents
Culture Documents
Mobile Phone Cloning
Mobile Phone Cloning
Uploaded by
Anonymous czrvb3hOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Mobile Phone Cloning
Mobile Phone Cloning
Uploaded by
Anonymous czrvb3hCopyright:
Available Formats
Seminar Report 2012-2013
Mobile Phone Cloning
ABSTRACT
Mobile communication has been readily available for several years and is ma!or business today" #t provides a valuable service to its users $ho are $illing to pay a considerable premium over a fi%ed line phone to be able to $al& and tal& freely" 'ecause of its usefulness and the money involved in the business it is sub!ect to fraud" (nfortunately the advance of security standards has not &ept pace $ith the dissemination of mobile communication" Some of the features of mobile communication ma&e it an alluring target for criminals" #t is a relatively ne$ invention so not all people are )uite familiar $ith its possibilities in good or in bad" #ts ne$ness also means intense competition among mobile phone service providers as they are attracting customers" *he ma!or threat to mobile phone is from cloning" Cell phone cloning is a techni)ue $herein security data from one cell phone is transferred into another phone" *he other cell phone becomes the e%act replica of the original cell phone li&e a clone" +s a result $hile calls can be made from both phones only the original is billed" *hough communication channels are e)uipped $ith security algorithms yet cloners get a$ay $ith the help of loop holes in systems" So $hen one gets huge bills the chances are that the phone is being cloned" *his paper describes about the cell phone cloning $ith implementation in ,SM and C-M+ technology phones" #t gives an insight into the security mechanism in C-M+ and ,SM phones along $ith the loop holes in the systems and discusses on the different $ays of preventing this cloning" Moreover the future threat of this fraud is being elaborated"
-ept"of .lectronics .ngg" *irur
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
CONTENTS
1" #/*R0-(C*#0/ 2" 102 C.33 P10/. 20R4S5 3" 21+* #S C.33 P10/. C30/#/,5 6" 21./ -#- C.33 C30/#/, S*+R*5 7" 102 #S C.33 C30/#/, -0/.5 8" M.*10-S *0 -.*.C* C30/.- P10/. 0/ /.*20R4 9" +R. 0(R C.33 P10/.S S.C(R.-5 :" 102 *0 4/02 *1+* *1. C.33 1+S '../ C30/.-5 ;" R03. 0< S.R=#C. PR0=#-.RS *0 C0M'+* C30/#/, <R+(-5 10" 102 *0 PR.=./* C.33 C30/#>/,5 11" S0M. <+C*S +/- <#,(R.S 12" <(*(R. *1R.+*S 13" C0/C3(S#0/ 16" R.<.R./C.S
-ept"of .lectronics .ngg" *irur
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
INTRODUCTION
Cloning is the creation of an organism that is an e%act genetic copy of another" *his means that every single bit of -/+ is the same bet$een the t$o? Remember -olly the lamb cloned from a si%-year-old e$e in 1;;9 by a group of researchers at the Roslin #nstitute in Scotland5 2hile the debate on the ethics of cloning continues human race for the first time are faced $ith a more tangible and harmful version of cloning and this time it is your cell phone that is the target" Millions of cell phones users be it ,SM or C-M+ run at ris& of having their phones cloned" +s a cell phone user if you have been receiving e%orbitantly high bills for calls that $ere never placed chances are that your cell phone could be cloned" (nfortunately there is no $ay the subscriber can detect cloning" .vents li&e call dropping or anomalies in monthly bills can act as tic&ers" +ccording to media reports recently the -elhi @#ndiaA police arrested a person $ith 20 cellphones a laptop a S#M scanner and a $riter" *he accused $as running an e%change illegally $herein he cloned C-M+ based cell phones" 1e used soft$are named Patagonia for the cloning and provided cheap international calls to #ndian immigrants in 2est +sia"
-ept"of .lectronics .ngg" *irur
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
HOW CELL PHONE WORKS?
Cell phones send radio fre)uency transmissions through the air on t$o distinct channels one for voice communications and the other for control signals" 2hen a cellular phone ma&es a call it normally transmits its .lectronic Security /umber @.S/A Mobile #dentification /umber @M#/A its Station Class Mar& @SCMA and the number called in a short burst of data" *his burst is the short buBB you hear after you press the S./- button and before the to$er catches the data" *hese four things are the components the cellular provider uses to ensure that the phone is programmed to be billed and that it also has the identity of both the customer and the phone" M#/ and .S/ is collectively &no$n as the CPairD $hich is used for the cell phone identification" 2hen the cell site receives the pair signal it determines if the re)uester is a legitimate registered user by comparing the re)uestorEs pair to a cellular subscriber list" 0nce the cellular telephoneEs pair has been recogniBed the cell site emits a control signal to permit the subscriber to place calls at $ill" *his process &no$n as +nonymous Registration is carried out each time the telephone is turned on or pic&ed up by a ne$ cell site" .S/ - *he .S/ @.lectronic Serial /umberA is the serial number of your cellular telephone"*he .S/ is transmitted to the cell site and used in con!uction $ith the /+M to verify that you are a legitimate user of the cellular system" M#/ - *he M#/ @Mobile #dentification /umberA is simply the phone number of the cellular telephone"
-ept"of .lectronics .ngg" *irur
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
WHAT IS CELL PHONE CLONING?
Cell phone cloning is copying the identity of one mobile telephone to another mobile telephone" (sually this is done for the purpose of ma&ing fraudulent telephone calls" *he bills for the calls go to the legitimate subscriber" *he cloner is also able to ma&e effectively anonymous calls $hich attracts another group of interested users" Cloning is the process of ta&ing the programmed information that is stored in a legitimate mobile phone and illegally programming the identical information into another mobile phone" *he result is that the FclonedF phone can ma&e and receive calls and the charges for those calls are billed to the legitimate subscriber" *he service provider net$or& does not have a $ay to differentiate bet$een the legitimate phone and the FclonedF phone" Cloning of mobile phones is the act of copying the subscriber information from one phone onto the other for purposes of obtaining free calls" *he other cell phone becomes the e%act replica of the original cell phone li&e a clone" +s a result $hile calls can be made from both phones only the original is billed" Cloning occurs most fre)uently in areas of high cell phone usage -- valet par&ing lots airports shopping malls concert halls sports stadiums and high-congestion traffic areas in metropolitan cities"
-ept"of .lectronics .ngg" *irur
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
Figure 1. Cellular p !"e #l!"i"g
*he early 1;;0s $ere boom times for eavesdroppers" +ny curious teenager $ith a G100 *andy Scanner could listen in to nearly any analogue mobile phone call" +s a result Cabinet Ministers company chiefs and celebrities routinely found their most intimate conversations published in the ne%t dayEs tabloids Cell phone cloning started $ith Motorola FbagF phones and reached its pea& in the mid ;0Es $ith a commonly available modification for the Motorola Fbric&F phones such as the Classic the (ltra Classic and the Model :000" GS$ % ,lobal System for Mobile Communications" + digital cellular phone technology based on *-M+ ,SM phones use a Subscriber #dentity Module @S#MA card that contains user account information" +ny ,SM phone becomes immediately programmed after plugging in the S#M card thus allo$ing ,SM phones to be easily rented or borro$ed" 0perators $ho provide ,SM service are +irtel 1utch etc" CD$A - Code -ivision Multiple +ccess" + method for transmitting simultaneous signals over a shared portion of the spectrum" *here is no Subscriber #dentity Module @S#MA card unli&e in ,SM" 0perators $ho provides C-M+ service in #ndia are Reliance and *ata #ndicom" 'oth ,SM and C-M+ handsets are prone to cloning" *echnically it is easier to clone a C-M+ handset over a ,SM one though cloning a ,SM cell phone is not
-ept"of .lectronics .ngg" *irur
S"S"M" Polytechnic College
Seminar Report 2012-2013 go about hac&ing into cellphones"
Mobile Phone Cloning
impossible" *here are also #nternet sites that provide information on ho$ one could
Cl!"i"g CD$A Cell P !"e& - Cellular telephone thieves monitor the radio fre)uency spectrum and steal the cell phone pair as it is being anonymously registered $ith a cell site" *he technology uses spread-spectrum techni)ues to share bands $ith multiple conversations" Subscriber information is also encrypted and transmitted digitally" C-M+ handsets are particularly vulnerable to cloning according to e%perts" <irst generation mobile cellular net$or&s allo$ed fraudsters to pull subscription data @such as .S/ and M#/A from the analog air interface and use this data to clone phones" + device called as --i -igital -ata #nterface @$hich comes in various formats from the more e%pensive stand-alone bo% to a device $hich interfaces $ith your :00 M1B capable scanner and a PCA can be used to get pairs by simply ma&ing the device mobile and sitting in a busy traffic area @free$ay overpassA and collect all the data you need" *he stolen .S/ and .M#/ $ere then fed into a ne$ C-M+ handset $hose e%isting program $as erased $ith the help of do$nloaded soft$are" *he buyer then programs them into ne$ phones $hich $ill have the same number as that of the original subscriber" Cl!"i"g GS$ P !"e& - ,SM handsets on the contrary are safer according to e%perts" .very ,SM phone has a 17 digit electronic serial number @referred to as the #M.#A" #t is not a particularly secret bit of information and you donEt need to ta&e any care to &eep it private" *he important information is the #MS# $hich is stored on the removable S#M card that carries all your subscriber information roaming database and so on" ,SM employs a fairly sophisticated asymmetric-&ey cryptosystem for over-the-air transmission of subscriber information" Cloning a S#M using information captured over-the-air is therefore difficult though not impossible" +s long as you donEt lose your S#M card youEre safe $ith ,SM" ,SM carriers use the C0MP12: authentication algorithm for the S#M authentication center and net$or& $hich ma&e ,SM a far secure technology"
-ept"of .lectronics .ngg" *irur
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
,SM net$or&s $hich are considered to be impregnable can also be hac&ed" *he process is simpleH a S#M card is inserted into a reader" +fter connecting it to the computer using data cables the card details $ere transferred into the PC" *hen using freely available encryption soft$are on the /et the card details can be encrypted on to a blan& smart card" *he resultH + cloned cell phone is ready for misuse IS FI'ED TELEPHONE NETWORK SAFER THAN $OBILE PHONE? *he ans$er is yes" #n spite of this the security functions $hich prevent eavesdropping and unauthoriBed user are emphasiBed by the mobile phone companies" *he e%isting mobile communication net$or&s are not safer than the fi%ed *elephone net$or&s" *hey only offer protection against the ne$ forms of abuse" SECURIT( FUNCTIONS OF THE GS$ AND CD$A % +s bac&ground to a better understanding of the attac&s on the ,SM and C-M+ net$or& the follo$ing gives a brief introduction to the Security functions available in ,SM" *he follo$ing functions e%istH +ccess control by means of a personal smart card @called subscriber #dentity module S#MA and P#/ @personal identification numberA +uthentication of the users to$ards the net$or& carrier and generation of a session &ey in order to prevent abuse" .ncryption of communication on the radio interface i"e" bet$een mobile Station and base station concealing the usersD identity on the radio interface i"e" a temporary valid #dentity code @*MS#A is used for the identification of a mobile user instead 0f the #MS#"
-ept"of .lectronics .ngg" *irur
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
HOW IS CELL CLONING DONE?
Cloning involved modifying or replacing the .PR0M in the phone $ith a ne$ chip $hich $ould allo$ you to configure an .S/ @.lectronic serial numberA via soft$are" Iou $ould also have to change the M#/ @Mobile #dentification /umberA" 2hen you had successfully changed the .S/JM#/ pair your phone $as an effective clone of the other phone" Cloning re)uired access to .S/ and M#/ pairs" .S/JM#/ pairs $ere discovered in several $aysH 1" Sniffing the cellular 2" *rashing cellular companies or cellular resellers 3" 1ac&ing cellular companies or cellular resellers Cloning still $or&s under the +MPSJ/+MPS system but has fallen in popularity as older clone able phones are more difficult to find and ne$er phones have not been successfully reverse-engineered"
-ept"of .lectronics .ngg" *irur
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
Cloning has been successfully demonstrated under ,SM but the process is not easy and it currently remains in the realm of serious hobbyists and researchers" 2hen placing a call the phone transmits both the .S/ and the M#/ to the net$or&" *hese $ere ho$ever sent in the clear so anyone $ith a suitable scanner could receive them" *he eavesdropped codes $ould then be programmed into another phone effectively cloning the original subscription" +ny calls made on this cloned phone $ould be charged on the original customer" See figure2"
WHAT IS PATAGONIA?
Patagonia is soft$are available in the mar&et $hich is used to clone C-M+ phone" (sing this soft$are a cloner can ta&e over the control of a C-M+ phone i"e" cloning of phone" *here are other Soft$areDs available in the mar&et to clone ,SM phone"
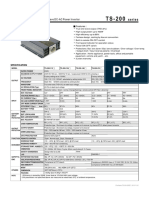
Cellular C!u")er*ei)i"g+Cl!"i"g Frau,
Figure -. Cellular #l!"i"g.
-ept"of .lectronics .ngg" *irur
10
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
*his soft$areDs are easily available in the mar&et" + S#M can be cloned again and again and they can be used at different places" Messages and calls sent by cloned phones can be trac&ed" 1o$ever if the accused manages to also clone the #M.# number of the handset for $hich soft$areDs are available there is no $ay he can be traced"
$ETHODS TO DETECT CLONED PHONES ON NETWORK
Several countermeasures $ere ta&en $ith varying success" 1ere are various methods to detect cloned phones on the net$or&H Dupli#a)e ,e)e#)i!" - *he net$or& sees the same phone in several places at the same time" Reactions include shutting them all off so that the real customer $ill contact the operator because he lost the service he is paying for or tearing do$n connections so that the clone users $ill s$itch to another clone but the real user $ill contact the operator" .el!#i)/ )rap 0 *he mobile phone seems to be moving at impossible or most unli&ely speeds" <or e%ample if a call is first made in 1elsin&i and five minutes later another call is made but this time in *ampere there must be t$o phones $ith the same identity on the net$or&" -ept"of .lectronics .ngg" *irur 11 S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
RF 1Ra,i! Fre2ue"#/3 - fingerprinting is originally a military technology" .ven nominally identical radio e)uipment has a distinguishing KKfingerprintEE so the net$or& soft$are stores and compares fingerprints for all the phones that it sees" *his $ay it $ill spot the clones $ith the same identity but different fingerprints" U&age pr!*ili"g. - Profiles of customersE phone usage are &ept and $hen discrepancies are noticed the customer is contacted" Credit card companies use the same method" <or e%ample if a customer normally ma&es only local net$or& calls but is suddenly placing calls to foreign countries for hours of airtime it indicates a possible clone" Call #!u")i"g - 'oth the phone and the net$or& &eep trac& of calls made $ith the phone and should they differ more than the usually allo$ed one call service is denied" PIN #!,e& 0 Prior to placing a call the caller unloc&s the phone by entering a P#/ code and then calls as usual" +fter the call has been completed the user loc&s the phone by entering the P#/ code again" 0perators may share P#/ information to enable safer roaming"
Figure 45 Dupli#a)e De)e#)i!"
-ept"of .lectronics .ngg" *irur
12
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
ARE OUR CELL PHONES SECURED?
*oo many users treat their mobile phones as gadgets rather than as business assets covered by corporate security policy" -id you realiBe thereEs a lucrative blac& mar&et in stolen and FclonedF Sim cards5 *his is possible because Sims are not net$or& specific and though tamper-proof their security is fla$ed" #n fact a Sim can be cloned many times and the resulting cards used in numerous phones each feeding illegally off the same bill" 'ut there are loc&ing mechanisms on the cellular phones that re)uire a P#/ to access the phone" *his $ould dissuade some attac&ers foil others but might not $or& against a $ell financed and e)uipped attac&er" +n :-digit P#/ re)uires appro%imately 70 000 000 guesses but there may be $ays for sophisticated attac&ers to bypass it"
-ept"of .lectronics .ngg" *irur
13
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
2ith the shift to ,SM digital - $hich no$ covers almost the entire (4 mobile sector - the phone companies assure us that the bad old days are over" Mobile phones they say are secure and privacy friendly" *his is not entirely true" 2hile the amateur scanner menace has been largely e%terminated there is no$ more potential than ever before for privacy invasion" *he alleged security of ,SM relies on the myth that encryption - the mathematical scrambling of our conversations - ma&es it impossible for anyone to intercept and understand our $ords" +nd $hile this claim loo&s good on paper it does not stand up to scrutiny" *he reality is that the encryption has deliberately been made insecure" Many encrypted calls can therefore be intercepted and decrypted $ith a laptop computer"
HOW TO KNOW THAT THE CELL HAS BEEN CLONED?
<re)uent $rong number phone calls to your phone or hang-ups" -ifficulty in placing outgoing calls" -ifficulty in retrieving voice mail messages" #ncoming calls constantly receiving busy signals or $rong numbers" (nusual calls appearing on your phone bills"
-ept"of .lectronics .ngg" *irur
16
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
ROLE OF SER.ICE PRO.IDER TO CO$BAT CLONING FRAUD?
*hey are using many methods such as R< <ingerprinting subscriber behavior profiling and +uthentication" R< <ingerprinting is a method to uni)uely identify mobile phones based on certain uni)ue radio fre)uency transmission characteristics that are essentially FfingerprintsF of the radio being used" Subscriber behavior profiling is used to predict possible fraudulent use of mobile service based on the types of calls previously made by the subscriber" Calls that are not typical of the subscriberEs past usage are flagged as potentially fraudulent and appropriate actions can be ta&en" -ept"of .lectronics .ngg" *irur 17 S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
+uthentication has advantages over these technologies in that it is the only industry standardiBed procedure that is transparent to the user a technology that can effectively combat roamer fraud and is a prevention system as opposed to a detection system"
HOW TO PRE.ENT CELL CLONING?
(ni)uely identifies a mobile unit $ithin a $ireless carrierEs net$or&" *he M#/ often can be dialed from other $ireless or $ire line net$or&s" *he number differs from the electronic serial number @.S/A $hich is the unit number assigned by a phone manufacturer" M#/s and .S/s can be chec&ed electronically to help prevent fraud" Mobiles should never be trusted for communicatingJstoring confidential information" +l$ays set a Pin thatEs re)uired before the phone can be used" Chec& that all mobile devices are covered by a corporate security policy" -ept"of .lectronics .ngg" *irur 18 S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
.nsure one person is responsible for &eeping tabs on $ho has $hat e)uipment and that they update the central register" 1o$ do service providers handle reports of cloned phones5 3egitimate subscribers $ho have their phones cloned $ill receive bills $ith charges for calls they didnEt ma&e" Sometimes these charges amount to several thousands of dollars in addition to the legitimate charges" *ypically the service provider $ill assume the cost of those additional fraudulent calls" 1o$ever to &eep the cloned phone from continuing to receive service the service provider $ill terminate the legitimate phone subscription" *he subscriber is then re)uired to activate a ne$ subscription $ith a different phone number re)uiring reprogramming of the phone along $ith the additional headaches that go along $ith phone number changes"
SO$E FACTS AND FIGURES
South$estern 'ell claims $ireless fraud costs the industry L870 million each year in the (S" Some federal agents in the (S have called phone cloning an especially KpopularE crime because it is hard to trace" #n one case more than 1 700 telephone calls $ere placed in a single day by cellular phone thieves using the number of a single unsuspecting o$ner" + 1ome 0ffice report in 2002 revealed that in 3ondon around 3 000 mobile phones $ere stolen in one month alone $hich $ere used for cell phone cloning"
-ept"of .lectronics .ngg" *irur
19
S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
+uthorities in the case estimated the loss at L3 000 to L6 000 for each number used in cell phone cloning" +ccording to a school of thought the *elecom Regulatory +uthority of #ndia @*R+#A should issue a directive $hich holds the operators responsible for duplications of mobile phones"
Mualcomm $hich develops C-M+ technology globally says each instance of mobile hac&ing is different and therefore there is very little an operator can do to prevent hac&ing" F#tEs li&e a virus hitting the computer" *he soft$are $hich is used to hac& into the net$or& is different so operators can only &eep upgrading their security fire$all as and $hen the hac&ers stri&e F says a Mualcomm e%ecutive"
FUTURE THREATS
Resolving subscriber fraud can be a long and difficult process for the victim" #t may ta&e time to discover that subscriber fraud has occurred and an even longer time to prove that you did not incur the debts" +s described in this article there are many $ays to abuse telecommunication system and to prevent abuse from occurring it is absolutely necessary to chec& out the $ea&ness and vulnerability of e%isting telecom systems" -ept"of .lectronics .ngg" *irur 1: S"S"M" Polytechnic College
Seminar Report 2012-2013
Mobile Phone Cloning
#f it is planned to invest in ne$ telecom e)uipment a security plan should be made and the system tested before being implemented" #t is therefore mandatory to &eep in mind that a techni)ue $hich is described as safe today can be the most unsecured techni)ue in the future"
CONCLUSION
Presently the cellular phone industry relies on common la$ @fraud and theftA and in-house counter measures to address cellular phone fraud" #s in initial stages in #ndia so preventive steps should be ta&en by the net$or& provider and the ,overnment the enactment of legislation to prosecute crimes related to cellular phones is not vie$ed as a priority ho$ever" #t is essential that intended -ept"of .lectronics .ngg" *irur 1; S"S"M" Polytechnic College
Seminar Report 2012-2013 fraud in particular Fcloning fraudF as a specific crime"
Mobile Phone Cloning
mobile crime legislation be comprehensive enough to incorporate cellular phone
.%isting cellular systems have a number of potential $ea&nesses that $ere considered" #t is crucial that businesses and staff ta&e mobile phone security seriously" +$areness and a fe$ sensible precautions as part of the overall enterprise security policy $ill deter all but the most sophisticated criminal" #t is also mandatory to &eep in mind that a techni)ue $hich is described as safe today can be the most unsecured techni)ue in the future" *herefore it is absolutely important to chec& the function of a security system once a year and if necessary update or replace it" <inally cell-phones have to go a long $ay in security before they can be used in critical applications li&e m-commerce"
REFERENCES
httpHJJ$$$"cdmasoft$are"comJeng httpHJJ$$$"victorgsm"comJproduct httpHJJ$$$"unloc&er"ruJcdmaNsoft" 20 S"S"M" Polytechnic College
httpHJJ$$$"c%otoday"com -ept"of .lectronics .ngg" *irur
Seminar Report 2012-2013 httpHJJinfotech"indiatimes"coM httpHJJ$iretap"spies"com httpHJJ$$$"hac&inthebo%"orgJ httpHJJ$$$"google"com httpHJJ$$$"$i&ipedia"com
Mobile Phone Cloning
-ept"of .lectronics .ngg" *irur
21
S"S"M" Polytechnic College
You might also like
- KLF The ManualDocument59 pagesKLF The ManualAlexander MegayNo ratings yet
- Mobile Phone CloningDocument8 pagesMobile Phone CloningVishwas N PrasadNo ratings yet
- Phishing Tutorial by DataBuster PDFDocument2 pagesPhishing Tutorial by DataBuster PDFCalebNo ratings yet
- Hackers Proofs - 2020Document33 pagesHackers Proofs - 2020jore1No ratings yet
- Continue: Fraud Bible Teejayx6 PDFDocument2 pagesContinue: Fraud Bible Teejayx6 PDFYT F1R3xS1NN3RNo ratings yet
- AT&T/Verizon/T-Mobile/Sprint/Cricket/US Cellular/C Spire Responses To Sen. Markey Re: Law Enforcement RequestsDocument80 pagesAT&T/Verizon/T-Mobile/Sprint/Cricket/US Cellular/C Spire Responses To Sen. Markey Re: Law Enforcement RequestsLeakSourceInfoNo ratings yet
- SMSDocument22 pagesSMSNaveen KumarNo ratings yet
- VanithaDocument100 pagesVanithaAnonymous czrvb3h33% (6)
- T24 Knowledge Bank - T24 Programs and RoutinesDocument9 pagesT24 Knowledge Bank - T24 Programs and RoutinesAswani MucharlaNo ratings yet
- IVV HandbookDocument390 pagesIVV HandbookkingmajorNo ratings yet
- A Presentation On "3D Printing Technology"Document19 pagesA Presentation On "3D Printing Technology"Sherry BaigNo ratings yet
- 290 Sundancer Smart Craft ManualDocument33 pages290 Sundancer Smart Craft ManualMitch Williams100% (1)
- Mobile Phone CloningDocument13 pagesMobile Phone CloningAshis Meher100% (1)
- Deeps ''MObile Cloning''Document35 pagesDeeps ''MObile Cloning''Abhiram TalluriNo ratings yet
- Mobile Phone CloningDocument12 pagesMobile Phone CloningNaveen Kamboj100% (1)
- Cell Phone Cloning by NavratnaDocument21 pagesCell Phone Cloning by NavratnaNavratna Ojha100% (1)
- Mobile Phone CloningDocument38 pagesMobile Phone CloningDevansh KumarNo ratings yet
- E SimDocument27 pagesE SimAbhiram SomanNo ratings yet
- Set Up and Get Started Your Iphone 14Document22 pagesSet Up and Get Started Your Iphone 14KevinNo ratings yet
- PhoneView ManualDocument8 pagesPhoneView ManualseefilmsNo ratings yet
- VoIP - Do It YourselfDocument10 pagesVoIP - Do It YourselfsaadsarfrazNo ratings yet
- Banking ScamsDocument27 pagesBanking Scamsmadhav kaliaNo ratings yet
- Abstract:: PhishingDocument15 pagesAbstract:: PhishingSid UpasaniNo ratings yet
- How To Hack WPA/WPA2 Wi Fi With Kali Linux: Last Updated: June 23, 2022Document7 pagesHow To Hack WPA/WPA2 Wi Fi With Kali Linux: Last Updated: June 23, 2022123456No ratings yet
- HackedDocument11 pagesHackedMkgt Hemaautomation0% (1)
- FreeRDP User Manual 4Document2 pagesFreeRDP User Manual 4vijayNo ratings yet
- Online Tracking SystemDocument87 pagesOnline Tracking SystemJaldeepNo ratings yet
- Mobile Phone CloninglDocument28 pagesMobile Phone CloninglKamal MittalNo ratings yet
- Temporary SMSDocument5 pagesTemporary SMStemp smssNo ratings yet
- FullDating TutorialDocument47 pagesFullDating Tutorialnicholasadjei1090No ratings yet
- Types of CardsDocument12 pagesTypes of CardsrodrigoelbarbaroNo ratings yet
- E SimDocument2 pagesE SimpanaxxiNo ratings yet
- Barcode Font SoftwareDocument6 pagesBarcode Font SoftwareConnectCode100% (4)
- ScammerDocument2 pagesScammerAqilah HanisNo ratings yet
- Dingtone Free Calling App Releases New Phone Numbers in 11 Countries, Reaches One Billion Calling Minutes Per YearDocument2 pagesDingtone Free Calling App Releases New Phone Numbers in 11 Countries, Reaches One Billion Calling Minutes Per YearPR.comNo ratings yet
- ¶ J¶ Hack Snapchat Account Ω Snapchathack 2021»»: Online Users: 7138Document2 pages¶ J¶ Hack Snapchat Account Ω Snapchathack 2021»»: Online Users: 7138Top Everything100% (1)
- PAYROLL TUT Smtools - LiveDocument21 pagesPAYROLL TUT Smtools - LiveGroupMae InvestmentNo ratings yet
- Scam Fraud: Prepared by S.Vinoth Martin Final - ITDocument21 pagesScam Fraud: Prepared by S.Vinoth Martin Final - ITmaakkaNo ratings yet
- Phone CodesDocument5 pagesPhone CodesElementsRookNo ratings yet
- Scam NewDocument16 pagesScam NewkrupamayekarNo ratings yet
- Law College Dehradun: Page - PAGEDocument19 pagesLaw College Dehradun: Page - PAGENancy RohillaNo ratings yet
- Article On Phishing - A New Age WeaponDocument8 pagesArticle On Phishing - A New Age WeaponAvinash SinghNo ratings yet
- Business Email Compromise FraudDocument5 pagesBusiness Email Compromise Fraudpaulinagigantone100% (1)
- What Does Spam Mean?: Spamming Is The Use of Messaging Systems To Send An Unsolicited Message (Spam)Document16 pagesWhat Does Spam Mean?: Spamming Is The Use of Messaging Systems To Send An Unsolicited Message (Spam)Daman Deep Singh ArnejaNo ratings yet
- Phishing 3371Document10 pagesPhishing 3371Syafiq RiderNo ratings yet
- Canada CC TopupDocument22 pagesCanada CC TopupFree RobuxNo ratings yet
- Advance Fee Fraud and BanksDocument10 pagesAdvance Fee Fraud and Banksbudi626No ratings yet
- How To Use A Fake IP Address & Mask Yourself OnlineDocument29 pagesHow To Use A Fake IP Address & Mask Yourself OnlineRanjeet KumarNo ratings yet
- Google Pay To Cash App 1Document6 pagesGoogle Pay To Cash App 1Charlie WillisNo ratings yet
- I'd MeDocument2 pagesI'd MeIbraheem AkoredeNo ratings yet
- Computer Hacking Related To Fraud of RecordsDocument52 pagesComputer Hacking Related To Fraud of RecordsRobin LigsayNo ratings yet
- Smart Baby SitterDocument6 pagesSmart Baby SittermohitNo ratings yet
- CitiDirect Online Banking Bank Handlowy W Warszawie S.A.Document31 pagesCitiDirect Online Banking Bank Handlowy W Warszawie S.A.César OrellanaNo ratings yet
- How To Spam Trust Wallet Account Logs Using Box SpammingDocument5 pagesHow To Spam Trust Wallet Account Logs Using Box SpammingLeeds EmileNo ratings yet
- Scams Schemes Swindles FINALDocument47 pagesScams Schemes Swindles FINALMiguelSiancas0% (1)
- Location Tracking of Android Device Based On SMS: Guided byDocument37 pagesLocation Tracking of Android Device Based On SMS: Guided bykiennaNo ratings yet
- Hack 7Document17 pagesHack 7mobilecrackersNo ratings yet
- Which Aspect of The Email Is Least Indicative of A Phishing Attack? The EmailDocument8 pagesWhich Aspect of The Email Is Least Indicative of A Phishing Attack? The EmailMirayya AidarovaNo ratings yet
- TelegramDocument5 pagesTelegramhouseNo ratings yet
- Evaluation of Some SMS Verification Services and Virtual Credit Cards Services for Online Accounts VerificationsFrom EverandEvaluation of Some SMS Verification Services and Virtual Credit Cards Services for Online Accounts VerificationsRating: 5 out of 5 stars5/5 (2)
- Mobile CloningDocument20 pagesMobile CloningBhawik100% (3)
- Cell Phone CloningDocument9 pagesCell Phone Cloningjoyjoshna0% (1)
- MObile Phone CloningDocument16 pagesMObile Phone CloningVeena ReddyNo ratings yet
- 08 - Chapter 3 The Traditional Arts of Kerala and Their Ritualistic AspectsDocument48 pages08 - Chapter 3 The Traditional Arts of Kerala and Their Ritualistic AspectsAnonymous czrvb3hNo ratings yet
- 09 - Chapter 4 PDFDocument48 pages09 - Chapter 4 PDFAnonymous czrvb3h100% (1)
- Hemiplegia Resource Book ModifiedDocument60 pagesHemiplegia Resource Book ModifiedAnonymous czrvb3hNo ratings yet
- To Whomsoever It May Concern: (Hotel Name)Document1 pageTo Whomsoever It May Concern: (Hotel Name)Anonymous czrvb3hNo ratings yet
- MT ApplicationformDocument4 pagesMT ApplicationformAnonymous czrvb3hNo ratings yet
- Bala BhumiDocument100 pagesBala BhumiAnonymous czrvb3h100% (1)
- Capacitor Voltage TransformerrDocument3 pagesCapacitor Voltage TransformerrAnonymous czrvb3hNo ratings yet
- Not 0142016 4142016Document5 pagesNot 0142016 4142016Anonymous czrvb3hNo ratings yet
- Let 171150 ScorecardDocument1 pageLet 171150 ScorecardAnonymous czrvb3hNo ratings yet
- Diploma in Computer Application: Total Time: 3 (Three) Hours Maximum: 100 MarksDocument4 pagesDiploma in Computer Application: Total Time: 3 (Three) Hours Maximum: 100 MarksAnonymous czrvb3hNo ratings yet
- Sensors: Analysis and Design of A Speed and Position System For Maglev VehiclesDocument18 pagesSensors: Analysis and Design of A Speed and Position System For Maglev VehiclesAnonymous czrvb3hNo ratings yet
- Bugatti Automobiles Road Car: Composite Technologies at AutomotiveDocument29 pagesBugatti Automobiles Road Car: Composite Technologies at AutomotiveAnonymous czrvb3hNo ratings yet
- 4Document5 pages4Anonymous czrvb3h100% (3)
- NizamDocument9 pagesNizamAnonymous czrvb3hNo ratings yet
- LET171271ScoreCard PDFDocument1 pageLET171271ScoreCard PDFAnonymous czrvb3hNo ratings yet
- Department of Technical Education: Diploma in EngineeringDocument1 pageDepartment of Technical Education: Diploma in EngineeringAnonymous czrvb3hNo ratings yet
- Government of Kerala: Community CertificateDocument1 pageGovernment of Kerala: Community CertificateAnonymous czrvb3hNo ratings yet
- Huge Document PDFDocument4 pagesHuge Document PDFAnonymous czrvb3hNo ratings yet
- Curriculum Vitae: Midhun CDocument2 pagesCurriculum Vitae: Midhun CAnonymous czrvb3hNo ratings yet
- Phone:-Director Office FAX WWW - Kerala.gov - in 0471-2305230 0471-2305193 0471-2301740Document2 pagesPhone:-Director Office FAX WWW - Kerala.gov - in 0471-2305230 0471-2305193 0471-2301740Anonymous czrvb3hNo ratings yet
- Liquid Keyboard: Govt. Women'S Polytechnic College Kottakkal - MalappuramDocument4 pagesLiquid Keyboard: Govt. Women'S Polytechnic College Kottakkal - MalappuramAnonymous czrvb3hNo ratings yet
- Mantoux TestDocument10 pagesMantoux TestAnonymous czrvb3hNo ratings yet
- Design and Assemble of Low Cost Prepaid Smart Card Energy Meter - A Novel DesignDocument9 pagesDesign and Assemble of Low Cost Prepaid Smart Card Energy Meter - A Novel DesignAnonymous czrvb3hNo ratings yet
- Detection of Lost Mobile On Android Platform: Shreya K. Patil, Bhawana D. Sarode, Prof. P.D.ChowhanDocument3 pagesDetection of Lost Mobile On Android Platform: Shreya K. Patil, Bhawana D. Sarode, Prof. P.D.ChowhanAnonymous czrvb3hNo ratings yet
- Standards of MeasurementDocument12 pagesStandards of MeasurementShubham KheraNo ratings yet
- Sakthivel Rajamani: ToolsDocument5 pagesSakthivel Rajamani: ToolsSanthanu SugumaranNo ratings yet
- 8050SDocument4 pages8050Sscr8510No ratings yet
- Fluke 971Document2 pagesFluke 971vishiNo ratings yet
- Korloy MaterialyDocument1 pageKorloy MaterialylucaNo ratings yet
- TS 200Document2 pagesTS 200Kmila ClavijoNo ratings yet
- Scan&SolveDocument24 pagesScan&SolveAtul ChauhanNo ratings yet
- Journalism, Citizens and Blogging: Debra AdamsDocument24 pagesJournalism, Citizens and Blogging: Debra AdamsMd. Abdus SamadNo ratings yet
- PMP Shortnotes For ExamDocument2 pagesPMP Shortnotes For Examatulw100% (1)
- Aibuli: Environment-Friendly Natural Grass Weaves WallcoveringDocument10 pagesAibuli: Environment-Friendly Natural Grass Weaves WallcoveringLuis MarínNo ratings yet
- Yamaha An1x DatalistDocument20 pagesYamaha An1x DatalistSal CarolloNo ratings yet
- CA Advanced Authentication - 8.1 - ENU - Collecting Device ID and DeviceDNA - 20170816Document16 pagesCA Advanced Authentication - 8.1 - ENU - Collecting Device ID and DeviceDNA - 20170816Md Aamir AliNo ratings yet
- Two Stroke AircraftDocument10 pagesTwo Stroke AircraftVinti Bhatia100% (1)
- Controlled Rectifier Single Phase Full WaveDocument7 pagesControlled Rectifier Single Phase Full WaveJesus BecerraNo ratings yet
- Practice Problems in ABSORPTION and HUMIDIFICATION - SolutionsDocument19 pagesPractice Problems in ABSORPTION and HUMIDIFICATION - SolutionsJenna Brasz100% (2)
- rsm370h1f 20169 (R20160901)Document17 pagesrsm370h1f 20169 (R20160901)bilalNo ratings yet
- GgoDocument1 pageGgodanialNo ratings yet
- Plan Reading I: Vision Properties Development Corporation Training ProgramDocument42 pagesPlan Reading I: Vision Properties Development Corporation Training ProgramOmen JettNo ratings yet
- Entrepreneurship & StrategyDocument11 pagesEntrepreneurship & StrategyRajan KumarNo ratings yet
- Highway Design With Civil 3DDocument36 pagesHighway Design With Civil 3DJeewana Meegahage100% (1)
- Nca Form Ap03aDocument5 pagesNca Form Ap03adreamtechbusiness24No ratings yet
- Abhishek SampleDocument4 pagesAbhishek SampleABHILASH KUMARNo ratings yet
- NCSC-TG-023 A Guide To Security Testing and Test Documentation in Trusted Systems (Bright Orange Book)Document124 pagesNCSC-TG-023 A Guide To Security Testing and Test Documentation in Trusted Systems (Bright Orange Book)Robert ValeNo ratings yet
- Figure-1 (A) Pendulum Oscillator: S R S S S S YDocument3 pagesFigure-1 (A) Pendulum Oscillator: S R S S S S YsaisaimmzNo ratings yet
- Daftar Layanan Khusus RSA UGMDocument6 pagesDaftar Layanan Khusus RSA UGMRiani Phara DivaNo ratings yet