Professional Documents
Culture Documents
Ds DLP Prevent
Ds DLP Prevent
Uploaded by
Constantin Caliman0 ratings0% found this document useful (0 votes)
14 views2 pagesThe more people share information electronically, the greater the likelihood that someone will inadvertently or intentionally send sensitive data to an unauthorized individual. This creates a tremendous challenge for corporate security and compliance officers. Enforcing the right policies at the right time is essential to ensuring data security, regulatory compliance, and intellectual property protection.
Original Description:
Original Title
Ds Dlp Prevent
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe more people share information electronically, the greater the likelihood that someone will inadvertently or intentionally send sensitive data to an unauthorized individual. This creates a tremendous challenge for corporate security and compliance officers. Enforcing the right policies at the right time is essential to ensuring data security, regulatory compliance, and intellectual property protection.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
14 views2 pagesDs DLP Prevent
Ds DLP Prevent
Uploaded by
Constantin CalimanThe more people share information electronically, the greater the likelihood that someone will inadvertently or intentionally send sensitive data to an unauthorized individual. This creates a tremendous challenge for corporate security and compliance officers. Enforcing the right policies at the right time is essential to ensuring data security, regulatory compliance, and intellectual property protection.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 2
Data Sheet
McAfee DLP Prevent
Enforce policies to protect your sensitive information
The more people share information electronically, the greater the likelihood that
someone will inadvertently or intentionally send sensitive data to an unauthorized
individualand put condential corporate data at risk. Whether through email, web,
instant messaging (IM), or FTP, information can leave the company across many dif-
ferent electronic channels. This creates a tremendous challenge for corporate security
and compliance ofcers. Some messages or transactions are allowable but should
be encrypted to ensure data privacy. Other types of messages, or their recipients, are
simply unacceptable at any time, and these transmissions must be blocked. Enforcing
the right policies at the right time is essential to ensuring data security, regulatory
compliance, and intellectual property protection.
Key Advantages
Leverage existing infrastructure
Protect corporate email through
integration with MTA gateways
using SMTP with X-Headers for
blocking, bouncing, encrypting,
quarantining, and redirecting
Deliver trafc enforcement
through integration with ICAP-
compliant web proxies to block
content violations over HTTP,
HTTPS, IM, FTP, and webmail
Proactively enforce policies for all
types of information
Protect more than 300 unique
content types
Enforce policies for the infor-
mation you know is sensitive
as well as the non-obvious
information you may not know
about
Scale to support hundreds
of thousands of concurrent
connections
Classify, analyze, and address
data leaks
Filter and control sensitive
information to protect against
known and unknown risks
Index and enforce ne-grained
security policies for all types
of content
Apply policies regarding internal
le share access to prevent users
from accessing information or
repositories in an unauthorized
manner
Enforce Security Policies for Data in Motion
Across each division of every company, individuals
share data using multiple applications and a
variety of protocols. To prevent against inadvertent
or intentional data leakage, companies must be
able to proactively protect sensitive information
from leaving the network and enforce correct
business processes.
McAfee Data Loss Prevention (DLP) Prevent
enforces policies for information leaving the
network through email, webmail, Instant
Messaging, wikis, blogs, portals, HTTP/HTTPS,
and FTP transfers by integrating with Message
Transfer Agent (MTA) gateways using Simple Mail
Transfer Protocol (SMTP) or ICAP-compliant web
proxies. Upon encountering a policy violation,
McAfee DLP Prevent allows you to take a variety
of actions, including applying encryption, blocking,
redirecting, quarantining, and moreso you can
ensure compliance with regulations governing the
privacy of sensitive information and reduce the risk
of security threats.
Integrate with Web Proxies and MTAs for
Greater Protection
McAfee DLP Prevent integrates with web proxies
(using ICAP) and with MTAs (using X-Headers)
for the required action. Because it terminates
unauthorized transactions at the application layer
rather than simply dropping the TCP session,
which does nothing to modify application
behavior, McAfee DLP Prevent alerts the initiating
application that the transmission was denied
due to a policy breach. This ensures greater data
protection for your organization because McAfee
DLP Prevent learns what must be protected and
stops the application from reattempting the same
behavior.
Protect Known and Unknown Sensitive
Information
With the ability to classify more than 300 different
content types, McAfee DLP Prevent helps you
ensure that the security of the information you
know remains condentialSocial Security
numbers, credit card numbers, and nancial
dataand learn what non-obvious information
or documents require protection, such as highly
complex intellectual property. McAfee DLP Prevent
includes a wide range of built-in policies, ranging
from compliance to acceptable use to intellectual
property, enabling you to match entire and partial
documents to a comprehensive set of rules, so you
can protect all your sensitive information, both
known and unknown.
Customize Views and Incident Reports
Using the McAfee ePolicy Orchestrator
(McAfee
ePO
) management console, you can customize
summary views of security incidents and
subsequent actions based on any two contextual
pivot points. List and detail views, as well as
summary views with trending, are available at your
ngertips. McAfee DLP Prevent also includes a
2821 Mission College Boulevard
Santa Clara, CA 95054
888 847 8766
www.mcafee.com
McAfee, the McAfee logo, McAfee ePolicy Orchestrator, and McAfee ePO are registered trademarks or trademarks of McAfee, Inc. or its
subsidiaries in the United States and other countries. Other marks and brands may be claimed as the property of others. The product plans,
specications and descriptions herein are provided for information only and subject to change without notice, and are provided without
warranty of any kind, express or implied. Copyright 2011 McAfee, Inc.
39802ds_dlp_prevent_1111
large number of pre-built reports, each of which
can be viewed, saved for later use, or scheduled
for periodic delivery.
Complex Data Classication
McAfee DLP Prevent empowers your organization
to protect all kinds of sensitive datafrom
common, xed-format data to complex, highly
variable intellectual property. By combining these
object-classication mechanisms, McAfee DLP
Prevent leverages a highly accurate, detailed
classication engine that blocks sensitive
information and identies hidden or unknown
risks. Object classication mechanisms include:
Multilayer classicationCovers both contextual
information and content in a hierarchical format
Document registrationIncludes biometric
signatures of information as it changes
Grammar analysisDetects grammar or
syntax of anything from text documents to
spreadsheets to source code
Statistical analysisTracks how many times a
signature, grammar, or biometric match occurred
in a particular document or le
File classicationIdenties content types
regardless of the extension applied to the le or
compression
Specications
Capture and index capacity
Index up to 80 TB of information
and up to 50 million documents
on the McAfee DLP 4400
appliance
System throughput
Up to 150 Mbps of full content
analysis, indexing, and storage
throughput
Network integration
Integrates into the network
as an off-path appliance that
is active within the data path
using MTAs and ICAP-compliant
web proxies
Content types
Supports le classication of
more than 300 content types,
including:
Microsoft Ofce documents
Multimedia les
P2P
Source code
Design les
Archives
Encrypted les
Protocols supported
Supports HTTP, HTTPS, FTP, and
Instant Messaging protocols via
the ICAP protocol to an ICAP-
compliant proxy. Please refer to
your proxy vendor for protocols
supported by your proxy.
Supports SMTP via integration
with MTAs.
Built-in policies
Provides a wide range of built-
in policies and rules for common
requirements, including regu-
latory compliance, intellectual
property, and acceptable use.
Enables complete customization
of rules to meet business-specic
needs by leveraging the McAfee
capture database.
Specications: McAfee DLP 4400 Appliance
Component Description
Mother Board Intel TimberCreek System (S5520URR)
CPU 2 x Intel X5660 12 M Cache, 2.8 GHz
(6 cores)
Memory 24 GB P1333 DDR3 memory
Raid Controller Intel RS2MB044 raid controller
Power Supply 2 x 760 W hot-swap power supply
modules
Hard Drives 12 x Seagate Constellation ES 1T
7200 rpm 3 1/2 SATA drives
NIC Card Intel Dual Copper 1 Gbps Ethernet I/O
module
DVD Drive SATA DVD-ROM
IPMI Intel Remote Management Modules 3
(AXXRMM3)
Product Size 2 rack units (2U)
Specications: Virtual Machine
McAfee DLP Prevent is available as a virtual appliance that can
run on VMware ESX or VMware ESXI 4.1 servers. Below are the
minimum hardware requirements for running the virtual appliance.
Component Requirement
CPU Intel Quad Core
Memory 8 GB RAM
Hard disk drive(s) Drive 1: Minimum size, 128 GB for
VM software
Drive 2: Minimum size, 640 GB for
DLP virtual image
Network ports 1 port for McAfee DLP Prevent application
BIOS Enable VT thread
You might also like
- My SubmissionDocument2 pagesMy SubmissionAbdelkebir Labyad83% (6)
- Security Infrastructure Design DocumentDocument7 pagesSecurity Infrastructure Design Documentmostafa100% (1)
- Your Electronic Ticket Receipt PDFDocument2 pagesYour Electronic Ticket Receipt PDFshalini singh deo100% (3)
- Case Study On FirewallDocument4 pagesCase Study On Firewallsidhant kumarNo ratings yet
- IPPDDocument19 pagesIPPDPankaj NarvekarNo ratings yet
- Jack JK-6380 PDFDocument21 pagesJack JK-6380 PDFRolando Gonzalez SibajaNo ratings yet
- Housing Definitions and ConceptsDocument8 pagesHousing Definitions and ConceptsChitrakshi Kumar0% (1)
- Ds DLP PreventDocument2 pagesDs DLP PreventFarhan SattarNo ratings yet
- McAfee DLP Monitor DatasheetDocument2 pagesMcAfee DLP Monitor DatasheetM_BBNo ratings yet
- Ds DLP ManagerDocument2 pagesDs DLP ManagerConstantin CalimanNo ratings yet
- WG Data Loss Prevention PDFDocument2 pagesWG Data Loss Prevention PDFsalvadordali120No ratings yet
- What Are Data Encryption Solutions?Document4 pagesWhat Are Data Encryption Solutions?Shaban MahekulaNo ratings yet
- Combining Classification and DLPDocument12 pagesCombining Classification and DLPTriệuAnhTuânNo ratings yet
- Ds Email GatewayDocument4 pagesDs Email GatewayScout StNo ratings yet
- Safetica Datasheet EN 2024-01-11Document6 pagesSafetica Datasheet EN 2024-01-11Jerry LaviñaNo ratings yet
- Data Loss Prevention For Endpoint enDocument3 pagesData Loss Prevention For Endpoint enMostafaEl-sayedNo ratings yet
- Unit2CS Kulvinder PDFDocument7 pagesUnit2CS Kulvinder PDFSudhanshu KumarNo ratings yet
- LaRon Walker - Security Plan Proposal For New Electronics ProjectDocument7 pagesLaRon Walker - Security Plan Proposal For New Electronics ProjectLaRon WalkerNo ratings yet
- Symantec DLP For NetworksDocument3 pagesSymantec DLP For NetworksM_BBNo ratings yet
- Is Cie 2 Q&aDocument24 pagesIs Cie 2 Q&ait.was.spamNo ratings yet
- Top 35 MitigationsDocument2 pagesTop 35 MitigationsskyrbNo ratings yet
- Mcafee Data Loss Prevention 11.1.x Product Guide 11-23-2021Document210 pagesMcafee Data Loss Prevention 11.1.x Product Guide 11-23-2021Nguyễn ThànhNo ratings yet
- Cloud SecurityDocument6 pagesCloud Securitydivine rockyNo ratings yet
- Clearswift - Product - Solution GuideDocument20 pagesClearswift - Product - Solution Guideshako12No ratings yet
- Database Security Basics VALIDITYDocument3 pagesDatabase Security Basics VALIDITYoluyinkaa14No ratings yet
- Firewall Features Overview PDFDocument5 pagesFirewall Features Overview PDFElliott longNo ratings yet
- Cisco IronPort Web Data Security and Data Loss Prevention OverviewDocument3 pagesCisco IronPort Web Data Security and Data Loss Prevention OverviewShaili SinghalNo ratings yet
- Data Loss Prevention: Muhammad Yousuf - Shabbir Anwer KhalidiDocument13 pagesData Loss Prevention: Muhammad Yousuf - Shabbir Anwer KhalidiNaushad SiddiquiNo ratings yet
- Topic: A Comprehensive Framework For Secure Query Processing On Relational Data in The CloudDocument4 pagesTopic: A Comprehensive Framework For Secure Query Processing On Relational Data in The CloudNazim Uddin MahmudNo ratings yet
- Data Loss Prevention Solution enDocument7 pagesData Loss Prevention Solution eninayat1975No ratings yet
- Firewall-Features-Palo AltoDocument6 pagesFirewall-Features-Palo AltojoseNo ratings yet
- McAfee DLP Endpoint DatasheetDocument2 pagesMcAfee DLP Endpoint DatasheetM_BBNo ratings yet
- Data and Device SecurityDocument6 pagesData and Device SecurityHazel GasconNo ratings yet
- Analyze The Data Security in Cloud ComputingDocument6 pagesAnalyze The Data Security in Cloud Computingofficialwork054No ratings yet
- Data-Loss-Prevention 55 Us PDFDocument2 pagesData-Loss-Prevention 55 Us PDFHernan CopaNo ratings yet
- 1.cloud Data SecurityDocument4 pages1.cloud Data SecurityArteNo ratings yet
- Data MaskingDocument2 pagesData MaskingAngela MossNo ratings yet
- 20BCA1335 Ashish-Yadav AssinmentDocument4 pages20BCA1335 Ashish-Yadav AssinmentimyadashuNo ratings yet
- Cloud Security Course SummaryDocument17 pagesCloud Security Course SummaryCaptain AmericaNo ratings yet
- Chapter 3 Computer SecurityDocument17 pagesChapter 3 Computer SecurityYared AyeleNo ratings yet
- McAfee Total Protection Jun09Document17 pagesMcAfee Total Protection Jun09SShaikSShaikSSNo ratings yet
- sc900 Module1Document29 pagessc900 Module1Pasquale GarzilloNo ratings yet
- Blue Coat Data Loss PreventionDocument2 pagesBlue Coat Data Loss PreventionprsmailNo ratings yet
- Security Architecture Best Practice by Bob Panic WhitepaperDocument22 pagesSecurity Architecture Best Practice by Bob Panic Whitepaperapi-111740184No ratings yet
- Data Leakage and PreventionDocument50 pagesData Leakage and PreventionNalla SanjayNo ratings yet
- A Personal Privacy Data Protection Scheme For Encryption and Revocation of High-Dimensional Attri-1Document4 pagesA Personal Privacy Data Protection Scheme For Encryption and Revocation of High-Dimensional Attri-1DhineshNo ratings yet
- Data SecurityDocument8 pagesData SecurityBanjo GiraoNo ratings yet
- Symantec Data Loss Prevention Enforce PlatformDocument4 pagesSymantec Data Loss Prevention Enforce PlatformY.FNo ratings yet
- Cloud ComputingDocument7 pagesCloud ComputingPurva SukhwalNo ratings yet
- UNIT 3 (Mid 1)Document13 pagesUNIT 3 (Mid 1)narayanasettisailavanya.20.cseNo ratings yet
- 4-Module - 2 Security Device Management-18!01!2024Document58 pages4-Module - 2 Security Device Management-18!01!2024shreemanjulaaNo ratings yet
- Team Members: Aparna Kolli, Anupama, Lakshmi GaneshDocument5 pagesTeam Members: Aparna Kolli, Anupama, Lakshmi GaneshvinhneNo ratings yet
- Final DocumentDocument73 pagesFinal DocumentJayaramsai PanchakarlaNo ratings yet
- 7-Module 2-22-02-2024Document41 pages7-Module 2-22-02-2024theorphicarcaneNo ratings yet
- Cryptography & Network Security: Institute of Road & Transport TechnologyDocument11 pagesCryptography & Network Security: Institute of Road & Transport TechnologymaadhawNo ratings yet
- Network Fundamentals Training For XYZ Company AssignmentDocument5 pagesNetwork Fundamentals Training For XYZ Company AssignmentAdedolamu AyandeleNo ratings yet
- Final Interviw PreparDocument4 pagesFinal Interviw Preparsandeep singhNo ratings yet
- PDEnterprise VDocument2 pagesPDEnterprise VAlejandro AraqueNo ratings yet
- 18 Information Security ChecklistDocument7 pages18 Information Security ChecklistNahom DejeneNo ratings yet
- CS L03 OSSecurity Rootkits 1598712884023 PDFDocument37 pagesCS L03 OSSecurity Rootkits 1598712884023 PDFamitNo ratings yet
- Lect 7Document67 pagesLect 7shirto cubherNo ratings yet
- Network SecurityDocument7 pagesNetwork SecurityankurjeNo ratings yet
- Cryptography and Data Security Book 1: Proper Guide to Data Security in Communication Networks. Cryptography and Data Security in PracticeFrom EverandCryptography and Data Security Book 1: Proper Guide to Data Security in Communication Networks. Cryptography and Data Security in PracticeNo ratings yet
- IPR QuizDocument5 pagesIPR QuizConstantin CalimanNo ratings yet
- Intrusion DetectionDocument79 pagesIntrusion DetectionConstantin CalimanNo ratings yet
- 2005 Technology HandbookDocument93 pages2005 Technology HandbookConstantin Caliman100% (1)
- Intrusion DetectionDocument79 pagesIntrusion DetectionConstantin CalimanNo ratings yet
- Jta50 20030404 PDFDocument250 pagesJta50 20030404 PDFConstantin CalimanNo ratings yet
- Ds DLP ManagerDocument2 pagesDs DLP ManagerConstantin CalimanNo ratings yet
- Deploying A Certification Authority For Networks Security: Prof. Dr. Victor-Valeriu Patriciu Cdor - Prof. Dr. AUREL SERBDocument23 pagesDeploying A Certification Authority For Networks Security: Prof. Dr. Victor-Valeriu Patriciu Cdor - Prof. Dr. AUREL SERBConstantin CalimanNo ratings yet
- Manuel Wi700-FODU TD en Interfaces E1 & Asi-V 3Document103 pagesManuel Wi700-FODU TD en Interfaces E1 & Asi-V 3Geoffrey AlleyneNo ratings yet
- Free Live Sex Cams and Adult Chat With Naked GirlDocument5 pagesFree Live Sex Cams and Adult Chat With Naked GirlMarc Roca BOscNo ratings yet
- Sikadur Combiflex SG 2019Document12 pagesSikadur Combiflex SG 2019halo windaNo ratings yet
- Dept. of Civil Engineering, JNTUHCEH M.Tech. (SE) (FT) W.E.F. 2015-16Document4 pagesDept. of Civil Engineering, JNTUHCEH M.Tech. (SE) (FT) W.E.F. 2015-16Bindu SrirangamNo ratings yet
- Form 172Document2 pagesForm 172ibrahimclassy1No ratings yet
- Cycle 3 Probability Sheets - Copyright PDFDocument6 pagesCycle 3 Probability Sheets - Copyright PDFteresa_wirtzNo ratings yet
- Profile Advocate Vicky ShahDocument1 pageProfile Advocate Vicky ShahAdvocate Vicky ShahNo ratings yet
- Dewellvex: (Patent Pending) WRDHSV - Dual Expanding Element Pack-OffDocument4 pagesDewellvex: (Patent Pending) WRDHSV - Dual Expanding Element Pack-OffaminoNo ratings yet
- Project Health & Safety Management PlanDocument50 pagesProject Health & Safety Management PlanCarl Williams100% (1)
- 7963 Brida Ac WN 6 X 150 SCH STD SWDocument2 pages7963 Brida Ac WN 6 X 150 SCH STD SWAlejandro L MagnusNo ratings yet
- US-015 High Accuracy Ultrasonic SensorDocument5 pagesUS-015 High Accuracy Ultrasonic SensorsapesajeNo ratings yet
- Use Wildcards To Find and Replace TextDocument4 pagesUse Wildcards To Find and Replace Textc3378925100% (1)
- Implementing Guidelines For The Distribution of National Rice Program Hybrid Rice Seed Assistance For Rice Farmers - AEWs Virtual Meeting 02.21.2024Document29 pagesImplementing Guidelines For The Distribution of National Rice Program Hybrid Rice Seed Assistance For Rice Farmers - AEWs Virtual Meeting 02.21.2024Red MildNo ratings yet
- Co-Gen BidDocument556 pagesCo-Gen BidManish ThakurNo ratings yet
- Elevator PM ChecklistDocument12 pagesElevator PM ChecklistAndrew jacangNo ratings yet
- ACCX-KITCHENHOODS SPMDocument36 pagesACCX-KITCHENHOODS SPMDavina FristantryNo ratings yet
- CX4-120 Site PreparationDocument3 pagesCX4-120 Site PreparationrajenderdhingraNo ratings yet
- Tips GAMEBOYDocument7 pagesTips GAMEBOYRaphael JolonNo ratings yet
- 03 2.1 Excavator Maintenance.Document59 pages03 2.1 Excavator Maintenance.felipe capistran100% (1)
- Wa0068Document2 pagesWa0068Bola-Ogunyemi Teniola BrightNo ratings yet
- Ashirvad SSWR LeafletDocument2 pagesAshirvad SSWR LeafletgkpNo ratings yet
- Runway Beam Esdep Lecture Note (Wg14)Document19 pagesRunway Beam Esdep Lecture Note (Wg14)kayakeras3335No ratings yet
- ASDERDocument40 pagesASDERFernando GutierrezNo ratings yet
- RexoilDocument1 pageRexoilEslam MansourNo ratings yet
- Ak09940 en ProductbriefDocument3 pagesAk09940 en Productbriefjigofis102No ratings yet
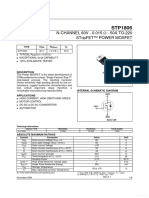
- STP 1806Document9 pagesSTP 1806David OweiNo ratings yet