Professional Documents
Culture Documents
Ethics and Professionalism PDF
Ethics and Professionalism PDF
Uploaded by
Suada Bőw Wéěžý0 ratings0% found this document useful (0 votes)
157 views11 pagesHJK
Original Title
Ethics and Professionalism.pdf
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentHJK
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
157 views11 pagesEthics and Professionalism PDF
Ethics and Professionalism PDF
Uploaded by
Suada Bőw WéěžýHJK
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 11
Chapter 6: I CT Ethics and Professionalism Page 1
Impact of ICT in Business and Society
Chapter 6: ICT Ethics and Professionalism
Understanding Ethical and Social issues related to systems
6.1. Ethics
Ethics are moral standards that help guide behaviour, actions, and choices.
Ethics: the study of principles that individuals and organizations can use to determine right and wrong
courses of action.
Ethics are grounded in the notion of responsibility (as free moral agents, individuals, organizations, and
societies are responsible for the actions that they take) and accountability (individuals, organizations, and
society should be held accountable to others for the consequences of their actions). In most societies, a
system of laws codifies the most significant ethical standards and provides a mechanism for holding
people, organizations, and even governments accountable. (Laudon, et al, 1996)
Ethics refers to the principles of right and wrong that individuals, acting as free moral agents, use to make
choices to guide their behaviours. Ethics has to do with making a principle-based choice between
competing alternatives. In the simplest ethical dilemmas, the choice is between right and wrong.
Information systems raise new ethical questions for both individuals and societies because they create
opportunities for intense social change, and thus threaten existing distribution of power, money, rights and
obligations. Information technology can be used to achieve social progress, but is can also be used to
commit crimes and threaten cherished social values.
6.2. Ethics in An Information Society
Basic Concepts: Responsibility, Accountability, And Liability
Ethical choices are decisions made by individuals who are responsible for the consequences of their
actions.
Responsibility is a key element of ethical action. Responsibility means that you accept the potential
costs, duties, and obligations for the decisions you make.
Accountability is a feature of systems and social institutions: It means that mechanisms are in place
to determine who took responsible action, who is responsible. Systems and institutions in which it is
impossible to find out who took what action are inherently incapable of ethical analysis or ethical
action.
Liability is a feature of political systems in which a body of laws is in place that permits individuals
to recover the damages done to them by other actors, systems, or organizations.
Due process is a related feature of law-governed societies and is a process in which laws are known
and understood and there is an ability to appeal to higher authorities to ensure that the laws are applied
correctly.
The following are the basic concepts that form the underpinning ethical analysis of information systems
and those who manage them: -
1. Information technologies are filtered through social institutions, organizations, and individuals.
Systems do not have impacts by themselves.
2. Responsibility for the consequences of technology falls clearly on the institutions, organizations,
and individual managers who choose to use the technology.
3. In an ethical, political society, individuals and others can recover damages done to them through a
set of laws characterized by due process.
Chapter 6: I CT Ethics and Professionalism Page 2
6.4. Features of ICT and their potential Ethical, Legal, Social and /or Political implications
E-Commerce Technology Dimension Potential ethical, Social and Political significance
Ubiquity internet/Web technology is
available everywhere; at work, at home and
elsewhere via mobile devices
Work and shopping can invade family life, shopping
can distract workers at work, lowering productivity,
use of mobile devices can lead to automobile and
industrial accidents. Presents confusing issues of
nexus to taxation authorities
Global reach: The technology reaches across
national boundaries around the Earth
Reduces cultural diversity in products, weakens local
small firms while strengthening large global firms;
moves manufacturing production to low-wage areas
of the world; weakens the ability of all nations large
and small to control their information density
Universal standards: there is one set of
technology standards, namely internet
standards
Increases vulnerability to viruses and hacking attacks
worldwide affecting millions of people at once.
Increases the likelihood of information crime,
crimes against systems and deception.
Richness: Video, audio, and text messages
are possible
A screen technology that reduces use of text and
potentially the ability to read by focusing instead on
video and audio messages. Potentially very persuasive
messages that may reduce reliance on multiple
independent sources of information
Interactivity: The technology works through
interaction with the user
The nature of interactivity at commercial sites can be
shallow and meaningless. Customers e-mails are
frequently not read by human beings. Customers do
not really co-produce the product as much as they
co-produce the sale. The amount of customization
of products that occurs is minimal, occurring within
predefined platforms and plug-in options.
Information density: The technology reduces
information costs, raises quality
While the total amount of information available to all
parties increases, so does the possibility of false and
misleading information, unwanted information and
invasion of solitude, trust, authenticity, accuracy,
completeness and other quality features of
information can be degraded. The ability of
individuals and organizations to make sense out of
this plethora of information is limited.
Personalization /Customization: The
technology allows personalized messages to
be delivered to individuals as well as groups
Opens up the possibility of intensive invasion of
privacy for commercial and governmental purposes
that is unprecedented.
Social Technology: The technology enables
user content generation and social
networking.
Creates opportunities for cyber-bullying, abusive
language, and predation; challenges concepts of
privacy, fair use and consent to use posted
information; creates new opportunities for
surveillance by authorities and corporations into
private lives
Chapter 6: I CT Ethics and Professionalism Page 3
6.5. Moral Dimensions of Information Age
Globalization and digital convergence in the emerging knowledge society has raised complex ethical, legal
and societal issues. We are faced with complex and difficult questions regarding the freedom of
expression, access to information, the right to privacy, intellectual property rights, and cultural diversity.
ICT is an instrumental need of all humans for the gathering of information and knowledge, and as such,
should be guaranteed as a basic right to all human beings. All over the world, rights that are already legally
recognised are daily being violated, whether in the name of economic advancement, political stability,
religious causes, the campaign against terrorism, or for personal greed and interests.
Violations of these rights have created new problems in human social systems, such as;
The digital divide: refers to any inequalities between groups, broadly construed, in terms of access to,
use of, or knowledge of information and communication technologies (ICT).
Cybercrime; Offences that are committed against individuals or groups of individuals with a criminal
motive to intentionally harm the reputation of the victim or cause physical or mental harm to the victim
directly or indirectly, using modern telecommunication networks such as Internet (Chat rooms, emails,
notice boards and groups) and mobile phones (SMS/MMS)".
Digital security and privacy concerns,
'Digital Security' gives individuals the freedom to embrace the digital lifestyle to confidently engage
in everyday interactions across all digital devices.
All of which have affected peoples lives either directly or indirectly.
It is important that the countries come up with an assessment of the situation, followed by guidelines for
action to combat the incidence of malicious attacks on the confidentiality, integrity and availability of
electronic data and systems, computer-related crimes, such as forgery and fraud, content related offenses,
such as those related to child pornography, and violations of intellectual property rights (IPRs). Further,
threats to critical infrastructure and national interests arising from the use of the internet for criminal and
terrorist activities are of growing concern after the September 11 incident.
The harm incurred to businesses, governments and individuals in those countries in which the internet is
used widely, is gaining in scope and importance, while in other countries, cybercrime threatens the
application of information and communication technology for government services, health care, trade, and
banking. As users start losing confidence in transactions and business, the opportunity costs may become
substantial.
Ethical, Social, and Political issues Raised by information systems include the following five (5) moral
dimensions: -
1. Information Rights and Obligations
2. Property Rights and Obligations
3. Accountability and Control
4. System Quality
5. Quality of life
Ethical, Social and political issues are closely linked as shown in the Fig 1. Society is a delicate ecosystem
in partial equilibrium with individuals and with social and political institutions. Individuals know how to
act in the society because social institutions (family, Education, Organisations) have developed well honed
behaviour, and these are supported by the laws developed in the political sector that prescribe behaviour
and promise sanctions for violations. When the information technology is adopted in the society it
Chapter 6: I CT Ethics and Professionalism Page 4
destabilises the existing harmony in the society. Suddenly, individual actors are confronted with new
situations often not covered by the old rules. Social institutions cannot respond overnight to these changes
and it may take years to develop etiquette, expectations, social responsibility, political correct attitudes or
approved rules.
FIG: 1 The Relationship between Ethical, Social and Political issues in an Information Society
1. Information Rights: Privacy and freedom in the internet age
Privacy is the claim of individuals to be left alone, free from surveillance or interference from other
individuals or organisations, including the state. Information Technology threaten individual claims to
privacy by making the invasion of privacy cheap, Profitable and effective. In some countries privacy is
protect by the laws.
Issue;
What rights to their own personal information do individuals have in a public marketplace or in
their private homes, when internet technologies make information collection so pervasive and
efficient
What rights do individuals have to access information about business firms and other
organizations.
The basic concepts of privacy;
Privacy: The right to be left alone and free from surveillance or interference from other individuals or
organizations including the state.
Information privacy;
the claim that certain information should not be collected at all by the government or business
firms
the claims that individuals to control the use of whatever information that is collected about them
Fair Information Practices (FIP) Was developed by the US federal government advisory committee
to set principles governing the collection and use of information about individuals. FIP principles are
based on the notion of a mutuality of interest between the record holder and the individual. The
individual has an interest in engaging in a transaction, and the record keep usually an organisation or
Chapter 6: I CT Ethics and Professionalism Page 5
government requires information about the individual to support the transaction. Once the
information is gathered, the individual maintains an interest in the record, and the record may not be
used support other activities without the individuals consent. In 1998, the Federal Trade Commission
(FTC) restated and extended the original FIP to provide guidelines for protecting online privacy. Table
1 describes the FTCs Fair Information Practice principles.
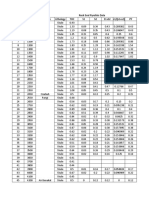
Table 1: federal trade commission fair information practice principles
1 Notice/awareness
(core principle).
Web sites must disclose their information practices before collecting
data. Includes identification of collector; uses of data; other
recipients of data; nature of collection (active/inactive); voluntary or
required status; consequences of refusal; and steps taken to protect
confidentiality, integrity, and quality of the data.
2 Choice/consent
(core principle).
There must be a choice regime in place allowing consumers to
choose how their information will be used for secondary purposes
other than supporting the transaction, including internal use and
transfer to third parties.
3 Access/participation. Consumers should be able to review and contest the accuracy and
completeness of data collected about them in a timely, inexpensive
process.
4 Security. Data collectors must take responsible steps to assure that consumer
information is accurate and secure from unauthorized use.
5 Enforcement. There must be in place a mechanism to enforce FIP principles. This
can involve self-regulation, legislation giving consumers legal
remedies for violations, or federal statutes and regulations.
Internet Challenges to Privacy - Internet technology has posed new challenges for the protection of
individual privacy. Information sent over this vast network of networks may pass through many
different computer systems before it reaches its final destination. Each of these systems is capable of
monitoring, capturing, and storing communications that pass through it. Companies can also collect
their site users information without the site users knowing or giving consent for such information to
be collected. This is done using Cookies (are tiny files deposited on a computer hard drive when a user
visits certain Web sites) or Web bugs (are tiny graphic files embedded in e-mail messages and Web
pages that are designed to monitor who is reading the e-mail message or Web page and transmit that
information to another computer).
2. Property rights: intellectual property
Issue;
How can traditional intellectual property rights be enforced in an Internet world where perfect
copies of protected works can be made and easily distributed worldwide in seconds
Intellectual property: Creations of the mind, such as inventions, literary and artistic works, and
symbols, names, images and designs used in commerce.
Intellectual property is considered to be intangible property created by individuals or corporations.
Information technology has made it difficult to protect intellectual property because computerized
information can be so easily copied or distributed on networks.
Chapter 6: I CT Ethics and Professionalism Page 6
Intellectual property is subject to a variety of protections under three different legal traditions: trade
secrets / marks, copyright, and patent law
Trade secrets: Any intellectual work producta formula, device, pattern, or compilation of data-used
for a business purpose can be classified as a trade secret, provided it is not based on information in
the public domain
Trademark: A symbol used by businesses to identify their goods and services; government
registration of the trademark confers exclusive legal rights to its use.
Copyright - is a statutory grant that protects creators of intellectual property from having their work
copied by others for any purpose during the life of the author plus an additional 70 years after the
authors death. It is an exclusive right of the author or creator of a book, movie, musical composition
or other artistic property to print, copy, sell, license, distribute, transform to another medium, translate,
record, perform or otherwise use.
For corporate-owned works, copyright protection lasts for 95 years after their initial creation.
Copyright protection is extended to books, periodicals, lectures, dramas, musical compositions, maps,
drawings, artwork of any kind, and motion pictures. The intent behind copyright laws has been to
encourage creativity and authorship by ensuring that creative people receive the financial and other
benefits of their work.
A patent grants the owner an exclusive monopoly on the ideas behind an invention (fixed number of
years (for 20 years). The intent behind patent law is to ensure that inventors of new machines, devices,
or methods receive the full financial and other rewards of their labour and yet still makes widespread
use of the invention possible by providing detailed diagrams for those wishing to use the idea under
license from the patents owner.
Challenges to Intellectual Property Rights - Digital media differ from physical media like books,
periodicals, CDs, and newspapers in terms of ease of replication; ease of transmission; ease of alteration;
difficulty in classifying a software work as a program, book, or even music; compactnessmaking theft
easy; and difficulties in establishing uniqueness. The proliferation of electronic networks, including the
Internet, has made it even more difficult to protect intellectual property. Using networks, information can
be more widely reproduced and distributed.
3. Responsibility and Control: Who is responsible and who controls the use and abuse of information
from the People.
Who can and will be held accountable and liable for the harm done to individual and collective
information and property rights?
Computer-related liability problems: If software fails, who is responsible?
The new information technologies are challenging existing laws regarding liability and social
practices, to force individuals and institutions accountable for their actions.
4. System quality: data quality and system errors
What data standards, information processing programs should be required (or demanded) to ensure the
protection of individual rights and safety of society?
System quality is very important in the sense that the errors arising from these systems can cause
injuries to someone either physically or economically which the company can be held accountable.
The gray area is that some system errors are foreseeable and correctable only at very great expense, an
Chapter 6: I CT Ethics and Professionalism Page 7
expense so great that pursuing this level of perfection is not feasible economicallyno one could
afford the product.
Three principal sources of poor system performance are (1) software bugs and errors, (2) hardware or
facility failures caused by natural or other causes, and (3) poor input data quality.
5. Quality of life: equity, access, and boundaries
What values should be preserved and protected in a society based on information and knowledge?
What institutions should be protect from violation? What cultural values and practices are
supported by the new information technology?.
The negative social costs of introducing information technologies and systems are growing along
with the power of technology. Computers and information technologies can destroy valuable
elements of culture and society, while providing benefits.
Negative Consequences of ICT
The following are some of the negative social consequences of information systems, considering
individual, social, and political responses: -
Balancing Power: Center Versus Periphery - Lower-level employees may be empowered to make
minor decisions, but the key policy decisions may be as centralized as in the past.
Rapidity of Change: Reduced Response Time to Competition - Time-based competition has an
ugly side: The businesses may not have enough time to respond to global competitors and may be
wiped out in a year, along with employees job.
Maintaining Boundaries: Family, Work, and Leisure - Time spent on the computer threatens these
close social relationships. Workers can be able to do their work from home thus reducing the time
they are interacting with their families.
Dependence and Vulnerability - Today, our businesses, governments, schools, and private
associations, are incredibly dependent on information systems and are, therefore, highly vulnerable
if these systems fail.
Computer Crime and Abuse - Computer crime is the commission of illegal acts through the use
of a computer or against a computer system. Computer abuse is the commission of acts involving
a computer that may not be illegal but that are considered unethical such as Spamming.
Employment: Trickle-Down Technology and Reengineering Job Loss - redesigning business
processes could potentially cause millions of mid-level managers and clerical workers to lose their
jobs.
Equity and Access: Increasing Racial and Social Class Cleavages - digital divide is a situation
where distribution of ICT resources is depended on social classes. The families with the higher
income will be able to afford more ICT devices while those with lower income will just have a few
of these devices.
Health Risks: RSI, CVS, and Technostress - Repetitive stress injury (RSI) occurs when muscle
groups are forced through repetitive actions often with high-impact loads (such as tennis) or tens of
thousands of repetitions under low-impact loads (such as working at a computer keyboard).
Computer vision syndrome (CVS) refers to any eyestrain condition related to computer display
screen use. Its symptoms, which are usually temporary, include headaches, blurred vision, and dry
and irritated eyes. Technostress is the stress induced by computer use. Its symptoms include
aggravation, hostility toward humans, impatience, and fatigue. According to experts, humans
working continuously with computers come to expect other humans and human institutions to
behave like computers, providing instant responses, attentiveness, and an absence of emotion.
Chapter 6: I CT Ethics and Professionalism Page 8
6.6. Key technology trends that raise ethical issues
There are four key technological trends responsible for these ethical stresses and they are summarized in
Table 2.
TREND IMPACT
Computing power doubles every 18 months More organizations depend on computer systems for
critical operations.
Data storage costs rapidly declining Organizations can easily maintain detailed databases on
individuals.
Data analysis advances Companies can analyze vast quantities of data gathered
on individuals to develop detailed profiles of individual
behaviour.
Networking advances and the Internet Copying data from one location to another and
accessing personal data from remote locations are much
easier.
Table 2: technology trends that raise ethical issues
The use of computers to combine data from multiple sources and create electronic dossiers of detailed
information on individuals is called profiling.
Example: A new data analysis technology called nonobvious relationship awareness (NORA) has given
both the government and the private sector even more powerful profiling capabilities. NORA can take
information about people from many disparate sources, such as employment applications, telephone
records, customer listings, and wanted lists, and correlate relationships to find obscure hidden
connections that might help identify criminals or terrorists
6.7. Analyzing an Ethical Dilemma
When confronted with a situation that seems to present ethical issues, how should you analyze it?
Dilemma: a situation in which there are at least two diametrically opposed actions, each of which supports a
desirable outcome.
The following five-step process should help you to confront a situation that seems to present ethical issues:
1. Identify and describe clearly the facts - The facts will help you understand the situation at hand better.
2. Define the conflict or dilemma and identify the higher-order values involved - Ethical, social, and
political issues always reference higher values. The parties to a dispute all claim to be pursuing higher
values (e.g., freedom, privacy, protection of property, and the free enterprise system). Typically, an
ethical issue involves a dilemma: two diametrically opposed courses of action that support worthwhile
values.
3. Identify the stakeholders - Every ethical, social, and political issue has stakeholders: players in the
game who have an interest in the outcome, who have invested in the situation, and usually who have
vocal opinions. Find out the identity of these groups and what they want.
4. Identify the options that you can reasonably take - You may find that none of the options satisfy all the
interests involved, but that some options do a better job than others.
5. Identify the potential consequences of your options - Some options may be ethically correct but
disastrous from other points of view. Other options may work in one instance but not in other similar
instances.
Chapter 6: I CT Ethics and Professionalism Page 9
6.8. Ethical Principles
The following are the ethical principles with deep roots in many cultures that have survived throughout
recorded history.
1. Do unto others as you would have them do unto you (the Golden Rule). Putting yourself into the place
of others, and thinking of yourself as the object of the decision, can help you think about fairness in
decision making.
2. If an action is not right for everyone to take, it is not right for anyone (Immanuel Kants Categorical
Imperative). Ask yourself, If everyone did this, could the organization, or society, survive?
3. If an action cannot be taken repeatedly, it is not right to take at all (Descartes rule of change). This is
the slippery-slope rule: An action may bring about a small change now that is acceptable, but if it is
repeated, it would bring unacceptable changes in the long run. It might be stated as once started down
a slippery path, you may not be able to stop.
4. Take the action that achieves the higher or greater value (the Utilitarian Principle). This rule assumes
you can prioritize values in a rank order and understand the consequences of various courses of action.
5. Take the action that produces the least harm or the least potential cost (Risk Aversion Principle). Some
actions have extremely high failure costs of very low probability (e.g., building a nuclear generating
facility in an urban area) or extremely high failure costs of moderate probability (speeding and
automobile accidents). Avoid these high-failure-cost actions, paying greater attention obviously to
high-failure-cost potential of moderate to high probability.
6. Assume that virtually all tangible and intangible objects are owned by someone else unless there is a
specific declaration otherwise. (This is the ethical no free lunch rule.) If something someone else has
created is useful to you, it has value, and you should assume the creator wants compensation for this
work.
6.9. IT Profession and Ethical Issues?
For the purpose of this discourse, the key areas are those that relate to the Attitude, Skill and Knowledge of
the IT professional. Interestingly these are the same areas of change that training focuses on. Training
seeks to close or fill any gaps that an individual has in these areas.
Professional codes of conduct
When groups of people claim to be professionals, they take on special rights and obligations because of
their special claims to knowledge, wisdom, and respect. Professional codes of conduct are promulgated by
associations of professionals, the Association of Information Technology Professionals (AITP), and the
Association of Computing Machinery (ACM). These professional groups take responsibility for the partial
regulation of their professions by determining entrance qualifications and competence. Codes of ethics are
promises by professions to regulate themselves in the general interest of society.
However, does having superior IT skills, knowledge and certification make you a true professional
What is your attitude towards business ethics? In today's fast and slick business environment, how
relevant is ethics when you can take the easy way out?
The right attitude also extends to how you treat your clients or employers. Are you dependable and
trustworthy?
Is it truly ethical, for example, for a professional to take longer than necessary to perform a job? To say
that he/she is sick in order to take a day off for leisure? To fail to report rule violations by a co-worker?
The public expects the IT professional to be socially responsible and disciplined and should be a role
model for the youth.
Chapter 6: I CT Ethics and Professionalism Page 10
Some real-world ethical dilemmas
Information systems have created new ethical dilemmas in which one set of interests is pitted against
another. For example, many of the large telephone companies are using information technology to reduce
the sizes of their workforces. Voice recognition software reduces the need for human operators by enabling
computers to recognize a customers responses to a series of computerized questions. Many companies
monitor what their employees are doing on the Internet to prevent them from wasting company resources
on non business activities
In each instance, you can find competing values at work, with groups lined up on either side of a debate. A
company may argue, for example, that it has a right to use information systems to increase productivity and
reduce the size of its workforce to lower costs and stay in business. Employees displaced by information
systems may argue that employers have some responsibility for their welfare. Business owners might feel
obligated to monitor employee e-mail and Internet use to minimize drains on productivity. Employees
might believe they should be able to use the Internet for short personal tasks in place of the telephone. A
close analysis of the facts can sometimes produce compromised solutions that give each side half a loaf.
Ethical Issues and ICT Profession.
These are common unethical and unprofessional business habits and serves as current challenges of most
companies:
1. Plagiarism - Plagiarism is where the work of others is copied, but the author presents it as his or her
own work. This is a highly unethical practice, but happens quite frequently, and with all the
information that is now available on the Internet it is much easier to do and is happening more often.
2. Hacking - Unauthorized used or access of networked computer systems. Hackers break into, or hack
into a system. Hacking can be undertaken for a variety of reasons, such as the wish to damage a system
or the wish to understand how a system works, so that money can be made out of it. Alternatively,
there might be a desire to alert people to the fact that a system is insecure and needs improving.
3. Viruses - Clearly writing and spreading virus programs are unethical acts, they have very serious
consequences, and cause systems to crash and organisations to cease operating for certain periods.
4. Spamming sending unsolicited email to many users and usually for commercial purposes.
5. Flaming sending grave and offensive email or posting offensive messages to social / group bulletins.
6. Forwardi ng non- busi ness emai l s
7. Moonlighting - doing side jobs or personal business using companys network and computer system
8. Sharing of password, data and access to other users
9. Internet hijacking unauthorized use of another users email account and information.
10. Use of internet for personal use such as online shopping, browsing, social networking etc.
11. Acts which threatens the security of companys information.
12. Ergonomics/health issues - Responsible/ethically-minded employers will, hopefully, give due
consideration to this. This includes issues such as the importance of taking adequate breaks from using
the computer and ensuring that the screens comply with the regulations. Also, ensuring that the
positioning of the chair and the computer is appropriate for the user and providing foot rests, when
required.
13. Nanotechnology - Nanotechnology presents a new set of ethical dilemmas. Nanotechnology could
help humankind and help to provide adequate food and shelter. On the other hand, it could be very
dangerous. There are also various environmental issues to consider, such as the effect that
nanomaterials have on living systems.
14. Netiquette - There are also ethical/moral codes that should be adhered to, in the use of networks and
email correspondence. The setting up of such codes has become necessary as people have not always
Chapter 6: I CT Ethics and Professionalism Page 11
addressed each other in an appropriate manner through this means of communication, and in this way
they have behaved unethically.
15. Speed of computers - The pure speed at which computers operate can cause ethical problems in
themselves. It can allow people to perform unethical issues quickly, or perform operations that it was
difficult or impossible to perform before, such as browsing through files that one is not authorised to. It
can also mean that people do not give enough consideration before performing various actions.
16. Vendor-client issues - Ethical issues also arise in regard to vendor-client relationships, the vendor
being the computer supplier and the client being the person that is buying the computer system,
whether this be the hardware or software or both. If the user continually changes the system
specification, for example, to what extent should the vendor be prepared to adjust the system
specification accordingly? Other unethical acts include, for example, consultants selling the program to
the second client, after being paid to develop the program for the first client only. Also, the vendor
might provide hardware maintenance according to a written contract and for hardware to be repaired in
a timely manner, but the client might not believe that the repairs have been timely. Drawing up more
precise contracts might help here, but in some instances the outcome can probably only depend on
peoples individual moral consciences.
17. Wardriving it is the act of searching for Wi-Fi networks by moving vehicle. The tools used to locate
open networks are now freely available on the Internet and they are allowing people to liberally search
for free connections. Many are using GPS devices to measure the locations of networks and then log
these locations onto websites for others to use.
Reference
Ken Laudon et al..., Management of Information system, Elevenths Edition, Pearson, 2010
You might also like
- The Digital Republic: On Freedom and Democracy in the 21st CenturyFrom EverandThe Digital Republic: On Freedom and Democracy in the 21st CenturyNo ratings yet
- Legal, Social and Ethical Issues in MisDocument4 pagesLegal, Social and Ethical Issues in MisAmiani 'Amio' DavidNo ratings yet
- Pco 3 For Close Control Units 201728a02Document72 pagesPco 3 For Close Control Units 201728a02Laurentiu Lapusescu50% (2)
- Ethical and Social Issues in Information SystemDocument25 pagesEthical and Social Issues in Information SystemfrankrivNo ratings yet
- UNIT - I Part - VIDocument16 pagesUNIT - I Part - VIRam MohanreddyNo ratings yet
- Grade 12 Unit OneDocument27 pagesGrade 12 Unit OnetewodrosbayisaNo ratings yet
- IctDocument4 pagesIctabebeb967No ratings yet
- Ethical and Social Issues of Information SystemDocument14 pagesEthical and Social Issues of Information SystemTejas BhavsarNo ratings yet
- HR AssignmentDocument23 pagesHR Assignmentabdul imran rasheedNo ratings yet
- What Are Issues That Consumers Have To Be Conscious in Social MediaDocument7 pagesWhat Are Issues That Consumers Have To Be Conscious in Social Mediataurusphammie99No ratings yet
- Social Challenges For Information TechnologyDocument12 pagesSocial Challenges For Information TechnologyAli HaqNo ratings yet
- Management Information Systems - Chapter 4Document3 pagesManagement Information Systems - Chapter 4Salsa ArdilaNo ratings yet
- CHH 1Document32 pagesCHH 1beki.ad10No ratings yet
- Ethical Issues and Social Issues Related To SystemsDocument11 pagesEthical Issues and Social Issues Related To SystemsWaivorchih Waibochi GiterhihNo ratings yet
- Part 55Document36 pagesPart 55fuhghjkmNo ratings yet
- Draft PPT.. Assignment ITDocument64 pagesDraft PPT.. Assignment ITDevendra SainiNo ratings yet
- Ethics and Social Impacts of ISDocument5 pagesEthics and Social Impacts of ISFredrick IshengomaNo ratings yet
- Define Computer EthicsDocument13 pagesDefine Computer EthicsPiyush PriyankNo ratings yet
- Ethical Legal and Social Aspects of Information AnDocument7 pagesEthical Legal and Social Aspects of Information Antristan araoNo ratings yet
- Lesson 6 TranscriptDocument6 pagesLesson 6 TranscriptJaytee TaquisoNo ratings yet
- Unite One:-Information Systems and Their ApplicationsDocument47 pagesUnite One:-Information Systems and Their ApplicationsbeleteasfawmezigebuNo ratings yet
- For ReviewDocument13 pagesFor ReviewanastaciahayaNo ratings yet
- Ethics in Digital FirmDocument60 pagesEthics in Digital FirmWycton Ombachi CliffNo ratings yet
- Digital Space and Human LibraryDocument20 pagesDigital Space and Human Librarymitalirakhecha19.solNo ratings yet
- Ethical Issues Cyberspace & ITDocument8 pagesEthical Issues Cyberspace & ITDrHarman Preet SinghNo ratings yet
- Ethical Issues in Information TechnologyDocument4 pagesEthical Issues in Information Technologyjustin naitira100% (1)
- Understanding Ethical and Social Issues Related To SystemsDocument20 pagesUnderstanding Ethical and Social Issues Related To Systemsnormie.fieldguy132xNo ratings yet
- Essay 4Document2 pagesEssay 4sandramankore3No ratings yet
- 4TH Inclar 2023Document4 pages4TH Inclar 2023Kantor AdvokatNo ratings yet
- 2 of 3 - Computer Internet and Information EthicsDocument5 pages2 of 3 - Computer Internet and Information EthicsSparsh JainNo ratings yet
- Unit 3 NotesDocument49 pagesUnit 3 NotesSmNo ratings yet
- Chapter 4 SummaryDocument2 pagesChapter 4 SummaryGraciella AudreyNo ratings yet
- Ethics and The LawDocument28 pagesEthics and The Lawthukralyash256No ratings yet
- CDI6-weeak 1-4Document20 pagesCDI6-weeak 1-4Kaneki KenNo ratings yet
- Docs Ibale, Abelardo, AntonioDocument15 pagesDocs Ibale, Abelardo, AntonioIbale, Arjay D.No ratings yet
- Moral Issues of Information TechnologyDocument18 pagesMoral Issues of Information TechnologyHope WanjeriNo ratings yet
- STS Reflection PaperDocument2 pagesSTS Reflection PapersrslytrdNo ratings yet
- LegalDocument7 pagesLegalChescaNo ratings yet
- Barrientos AchoDocument27 pagesBarrientos Achojuvelyn.aclaoNo ratings yet
- Ethics of IctDocument6 pagesEthics of IctBal QisNo ratings yet
- FRB Im Dict3 Icte 10083 Lesson-4-Lesson-6Document36 pagesFRB Im Dict3 Icte 10083 Lesson-4-Lesson-6benceldominguez2No ratings yet
- Digital EthicsDocument5 pagesDigital Ethicsapi-558431836No ratings yet
- 10 Advantages of Social Media For The SocietyDocument7 pages10 Advantages of Social Media For The SocietyPol AsuncionNo ratings yet
- Topic 12 EthicsDocument5 pagesTopic 12 EthicsBENSON NGARINo ratings yet
- Somya Gupta TechnoDocument14 pagesSomya Gupta TechnodkgodaraNo ratings yet
- Week 16-17Document23 pagesWeek 16-17Brennan Roi DuagNo ratings yet
- Q:2 Draw and Explain A Model For Thinking About Ethical, Social and Political Issues?Document5 pagesQ:2 Draw and Explain A Model For Thinking About Ethical, Social and Political Issues?Shahbaz ArtsNo ratings yet
- Phyassingment 104Document3 pagesPhyassingment 104Shi SirNo ratings yet
- BSIT-64 (Computer Ethics & Cyber Laws)Document8 pagesBSIT-64 (Computer Ethics & Cyber Laws)SiddhArth JAinNo ratings yet
- Ethical AssignmentDocument8 pagesEthical AssignmentronicaNo ratings yet
- Ethical and Social Issues in Information SystemDocument5 pagesEthical and Social Issues in Information Systemcopy smart100% (2)
- Ethical and Social Issues in The Digital FirmDocument7 pagesEthical and Social Issues in The Digital FirmJolinaBaybayNo ratings yet
- Can Cyber Security and Cyber Crimes InfringeDocument4 pagesCan Cyber Security and Cyber Crimes InfringeGauthamNo ratings yet
- Topic 2-EthicsDocument37 pagesTopic 2-EthicsZobia Bukhari100% (1)
- (HS 21201 Essay) Importance of Computer Ethics and Morality in SocietyDocument7 pages(HS 21201 Essay) Importance of Computer Ethics and Morality in SocietycoolinkenanatamNo ratings yet
- Cyber EthicsDocument1 pageCyber EthicsVarsha KhandelwalNo ratings yet
- Condominium Management System For ADAMA TownDocument8 pagesCondominium Management System For ADAMA TownHabtamu MollaNo ratings yet
- INTERNET & DEMOCRACY in BharatDocument5 pagesINTERNET & DEMOCRACY in Bharatsrikanthboiwar88shreeNo ratings yet
- Legal and Ethical Issues of EcommerceDocument15 pagesLegal and Ethical Issues of EcommerceRavi JindalNo ratings yet
- Digital Dilemmas: Navigating Ethics in the Age of AI and SurveillanceFrom EverandDigital Dilemmas: Navigating Ethics in the Age of AI and SurveillanceNo ratings yet
- Architectural Design: ©ian Sommerville 2000 Software Engineering. Chapter 11 Slide 1Document65 pagesArchitectural Design: ©ian Sommerville 2000 Software Engineering. Chapter 11 Slide 1Suada Bőw WéěžýNo ratings yet
- Uncertainty in KBSDocument5 pagesUncertainty in KBSSuada Bőw WéěžýNo ratings yet
- 340 IntroductionDocument25 pages340 IntroductionSuada Bőw WéěžýNo ratings yet
- Excel Assessment Tests Standard Seven Excel Exam A3 2013 Marking Scheme S/StudiesDocument2 pagesExcel Assessment Tests Standard Seven Excel Exam A3 2013 Marking Scheme S/StudiesSuada Bőw WéěžýNo ratings yet
- Bit 4202 Distributed Multimedia SystemsDocument157 pagesBit 4202 Distributed Multimedia SystemsSuada Bőw WéěžýNo ratings yet
- Case Based ReasoningDocument35 pagesCase Based ReasoningSuada Bőw WéěžýNo ratings yet
- SaoFM HghygDocument111 pagesSaoFM HghygSuada Bőw WéěžýNo ratings yet
- CHAP13Document30 pagesCHAP13Suada Bőw WéěžýNo ratings yet
- Database Fundamentals Distributed DatabasesDocument18 pagesDatabase Fundamentals Distributed DatabasesSuada Bőw WéěžýNo ratings yet
- Database System Concepts and Architecture: Basic Client/server DBMS ArchitectureDocument44 pagesDatabase System Concepts and Architecture: Basic Client/server DBMS ArchitectureSuada Bőw WéěžýNo ratings yet
- Databases Review IntroDocument50 pagesDatabases Review IntroSuada Bőw WéěžýNo ratings yet
- Knowledge Acquisition and Expert SystemsDocument11 pagesKnowledge Acquisition and Expert SystemsSuada Bőw WéěžýNo ratings yet
- Data World: Represents A Real World Which Is Changing ContinuouslyDocument40 pagesData World: Represents A Real World Which Is Changing ContinuouslySuada Bőw WéěžýNo ratings yet
- Knowledge Representation and InferenceDocument15 pagesKnowledge Representation and InferenceSuada Bőw WéěžýNo ratings yet
- Intro To KBS and Knowledge RepresentationDocument18 pagesIntro To KBS and Knowledge RepresentationSuada Bőw Wéěžý100% (1)
- Uman Resource Management MODULEDocument132 pagesUman Resource Management MODULESuada Bőw WéěžýNo ratings yet
- Mandatory Access Control: 1 Why Need MACDocument6 pagesMandatory Access Control: 1 Why Need MACSuada Bőw WéěžýNo ratings yet
- HCI Ourse OutlineDocument2 pagesHCI Ourse OutlineSuada Bőw WéěžýNo ratings yet
- Perception & RepresentationDocument26 pagesPerception & RepresentationSuada Bőw WéěžýNo ratings yet
- Broch Samcef Mecano PDFDocument4 pagesBroch Samcef Mecano PDFTrường ĐàoNo ratings yet
- CitesteDocument3 pagesCitesteCosmin MarianNo ratings yet
- Removal of Cod and Tds From Industrial Waste Water PDFDocument12 pagesRemoval of Cod and Tds From Industrial Waste Water PDFPc typeNo ratings yet
- Fem PDFDocument3 pagesFem PDFJavedNo ratings yet
- Brookfield Viscometer AssignmentDocument4 pagesBrookfield Viscometer AssignmentRicardo VelozNo ratings yet
- Atal FDPDocument2 pagesAtal FDPnoble aNo ratings yet
- Pneumatic Conveying Assignment (Final)Document31 pagesPneumatic Conveying Assignment (Final)Joel ForbesNo ratings yet
- High Voltage Insulated Cable (B1)Document57 pagesHigh Voltage Insulated Cable (B1)amits.bhelNo ratings yet
- SA164YKDocument6 pagesSA164YKperoz_ak47No ratings yet
- CorporateDocument26 pagesCorporatesainath93No ratings yet
- Company Profile Swiss-Belinn BalikpapanDocument9 pagesCompany Profile Swiss-Belinn BalikpapansibkbalikpapanNo ratings yet
- Syllubus M TechDocument33 pagesSyllubus M TechSumit KumarNo ratings yet
- Swaged Connection SystemDocument11 pagesSwaged Connection System魏永涛No ratings yet
- QQQQ That InformationDocument30 pagesQQQQ That InformationYosian Berkat SihombingNo ratings yet
- Type 8560 Eccentric Disk Butterfly Control Valve: Bulletin 51.6:8560Document10 pagesType 8560 Eccentric Disk Butterfly Control Valve: Bulletin 51.6:8560Datt NguyenNo ratings yet
- ABB Review Fit at 50 EnglishDocument7 pagesABB Review Fit at 50 EnglishmrhomNo ratings yet
- Om WD PLDocument6 pagesOm WD PLjsojosa72_382072351No ratings yet
- AmarujalaDocument59 pagesAmarujalaroyal.faraz4u9608100% (2)
- Astm C868-02 PDFDocument4 pagesAstm C868-02 PDFIan HsuNo ratings yet
- Curriculam VitaeDocument3 pagesCurriculam VitaeSumit GroverNo ratings yet
- FDMC 8884Document7 pagesFDMC 8884Kholit LitNo ratings yet
- IPC-TM-650 Test Methods ManualDocument1 pageIPC-TM-650 Test Methods ManualWim Op 't VeldNo ratings yet
- 11 1 2019 PDFDocument2 pages11 1 2019 PDFdkNo ratings yet
- Indian Standard - Industrial Plant Layout-Code of Safe PracticeDocument29 pagesIndian Standard - Industrial Plant Layout-Code of Safe PracticeDineshKumarNo ratings yet
- Cooperative Secondary Authorization RecyclingDocument10 pagesCooperative Secondary Authorization RecyclingHariharan SaravananNo ratings yet
- Official Breakout EDU Game TemplateDocument8 pagesOfficial Breakout EDU Game Templateapi-300338370No ratings yet
- 06 Mulia Life of Mine - Andre TitaleyDocument33 pages06 Mulia Life of Mine - Andre TitaleyDwik Thesoulof VillianoNo ratings yet
- WinUSB Tutorial 5Document12 pagesWinUSB Tutorial 5quim758No ratings yet
- Klinger KGS/VD: The First Infinitely Adjustable GasketDocument4 pagesKlinger KGS/VD: The First Infinitely Adjustable Gasketperdhana2000No ratings yet