Professional Documents
Culture Documents
0 ratings0% found this document useful (0 votes)
50 viewsInformation Security Officer Role Within Community Banks
Information Security Officer Role Within Community Banks
Uploaded by
Saroj KafleRole of ISO
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5834)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (350)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (824)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (405)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Bid-No Bid Assessment and Checklist FormDocument1 pageBid-No Bid Assessment and Checklist FormSaad Al-Subaie100% (3)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- How To Integrate Micro and Macro Management For Organization Evolution?Document4 pagesHow To Integrate Micro and Macro Management For Organization Evolution?Alaa Din AL-khwarizmiNo ratings yet
- Strategic Foresight PlatformDocument575 pagesStrategic Foresight Platformtestato123No ratings yet
- Procurement and TenderingDocument68 pagesProcurement and TenderingBUKENYA BEEE-2026No ratings yet
- Statement of Work PDFDocument7 pagesStatement of Work PDFJairo Castro FlorianNo ratings yet
- Embrace The Inevitable - Six Imperatives To Prepare Your Company For Cloud ComputingDocument4 pagesEmbrace The Inevitable - Six Imperatives To Prepare Your Company For Cloud ComputingswainanjanNo ratings yet
- Assignment 1Document17 pagesAssignment 1ShammimBegumNo ratings yet
- AMC Process in SAP PM PDFDocument12 pagesAMC Process in SAP PM PDFPiyush BoseNo ratings yet
- DATAVERSITY Erwin State of Data Governance 2020 Final 012420Document16 pagesDATAVERSITY Erwin State of Data Governance 2020 Final 012420Jorge GarzaNo ratings yet
- Case Analysis Tip-Hrdm 423Document5 pagesCase Analysis Tip-Hrdm 423EhmzyDegacoBacsafra0% (1)
- Session 4: Supply Chain IntegrationDocument32 pagesSession 4: Supply Chain IntegrationWonderkid YHHNo ratings yet
- AssignmentDocument7 pagesAssignmentmian577938No ratings yet
- Objective of CostingDocument2 pagesObjective of CostingAshik Uz ZamanNo ratings yet
- GAMP 5 Quality Risk Management Approach: by Kevin C. Martin and Dr. Arthur (Randy) PerezDocument7 pagesGAMP 5 Quality Risk Management Approach: by Kevin C. Martin and Dr. Arthur (Randy) PerezSaurabh VijNo ratings yet
- Chapter 31 Computer-Aided Software EngineeringDocument6 pagesChapter 31 Computer-Aided Software EngineeringRoshan KCNo ratings yet
- Corporate FinanceDocument4 pagesCorporate FinanceNeerajNo ratings yet
- SSW Nom20Document72 pagesSSW Nom20Brian RamphisaNo ratings yet
- Why KPA Is Important in Performance ManagemantDocument2 pagesWhy KPA Is Important in Performance ManagemantbbarpdNo ratings yet
- MMFIDocument3 pagesMMFImayoorNo ratings yet
- Literature Review On Inventory Management TechniquesDocument5 pagesLiterature Review On Inventory Management Techniquesea44a6t7No ratings yet
- ETL Vs ELTDocument7 pagesETL Vs ELTMiguel Angel PiñonNo ratings yet
- Week 001-003 BPODocument5 pagesWeek 001-003 BPOkitaNo ratings yet
- Quality Service in Tourism and Hospitality: Prepared By: Jaymee Ara E. CatchillarDocument43 pagesQuality Service in Tourism and Hospitality: Prepared By: Jaymee Ara E. CatchillarEfaith1256No ratings yet
- Sartaj Alam Sales & Marketing ManagerDocument4 pagesSartaj Alam Sales & Marketing ManagerZubair AhmedNo ratings yet
- Job Descriptions: Writing Job Descriptions and Examples, Job Descriptions DutiesDocument22 pagesJob Descriptions: Writing Job Descriptions and Examples, Job Descriptions DutiesSurjit SinghNo ratings yet
- OSCM Merge @vickyDocument183 pagesOSCM Merge @vickySanjay sadafule100% (1)
- My Cloud Power BriefDocument6 pagesMy Cloud Power BriefChiTownITNo ratings yet
- Successfully Utilizing CMMSEAM Systems Maintenance Strategy Series by WiremanDocument133 pagesSuccessfully Utilizing CMMSEAM Systems Maintenance Strategy Series by WiremanLuis Daniel RodríguezNo ratings yet
- Question 13 - Draft - Shortened 7COO3Document3 pagesQuestion 13 - Draft - Shortened 7COO3Flora InnehNo ratings yet
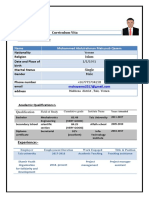
- Curriculum Vita: Mohammed Abdulrahman Mahyoub Qasem NameDocument2 pagesCurriculum Vita: Mohammed Abdulrahman Mahyoub Qasem Namerahbi malekNo ratings yet
Information Security Officer Role Within Community Banks
Information Security Officer Role Within Community Banks
Uploaded by
Saroj Kafle0 ratings0% found this document useful (0 votes)
50 views3 pagesRole of ISO
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentRole of ISO
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
50 views3 pagesInformation Security Officer Role Within Community Banks
Information Security Officer Role Within Community Banks
Uploaded by
Saroj KafleRole of ISO
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 3
Filling the Information Security Officer Role within Community Banks
By, John J. DeMauro, President, Practical Security Solutions, LLC and
Thomas W. Grottke, President, NEBSG, LLC
Banking has been significantly impacted by technology. Maybe more than any other business,
but that may be an insular view. Technologies that came to the industry during the 1960s through
most of the 90s emphasized and impacted operations and financial systems. Technologies
impacting banking today and for the past decade have transitioned to those that connect a
financial institutions operations with customers or other third-parties. In other words, such
technologies have had an outside orientation.
This absolutely revolutionary orientation has increased dependency on technology and also
reliance on technology for operating procedures that we used to rely on heavily to be performed
by our human resources.
These new technology changes coupled with the ever increasing power and use of the Internet
has changed the nature of major aspects of the business of banking. Most of us believe we are
only at the tipping point in this transformation and some of our clients are preparing for nearly
complete transformation to this automated business model. Technology, once relegated to the
backroom is now a focus of the boardroom as evidenced by comments from some of our CEO
and their directors, people dont want to come into the branch anymore, ...the next
generation wont even know what a bank is.. or there are not enough deposits available here
(in our branch markets) and we cant afford to open new branches so we must use the Internet to
gather deposits.
This growth and expected continued growth of technology based products, services and front and
back-office automation may be why regulators stopped just short of requiring that banks appoint
an Information Security Officer (ISO) as they drafted the GLBA data protection provisions back
in 2001 and 2002. But, by 2003, the FFIEC issued guidance that states: Senior management
should designate one or more individuals as information security officers.
1
. For some time, we
have seen regulatory examinations strongly recommend to their banks that are in excess of $1
billion in assets that they established the ISO position and see regular comments where it has
been established on the quality and structure of the position. With increasing regularity we are
seeing similar regulatory commentary at smaller banks.
This is a costly and, we have witnessed firsthand with a number of banks, politically charged
position that the regulatory agencies are requiring all banks to address. Now certainly it is not a
full-time job, in our experience, not even at a bank with an in-house core data processing system
with over $2 billion in assets.
1 http://www.ffiec.gov/ffiecinfobase/booklets/information_security/01_security_process.htm
Before options are discussed it is important to consider the responsibilities that make up the ISO
role. First and foremost the ISO should be responsible and accountable for the administration of
the information security program. At a minimum, they should directly manage or oversee the
information technology (IT) risk assessment process, development of IT security policies,
standards, and procedures, testing, and the information security reporting processes.
To ensure appropriate segregation of duties, the information security officer should report
directly to the board or to a senior officer with sufficient independence to perform their assigned
tasks. It is not uncommon or completely out of the question for the position to report to the CIO.
However, such a circumstance can raise questions with regards to adequate levels of
independence. Typically, security officers should be risk managers and not a resource assigned
operational responsibilities within the information technology (IT) department. They should have
sufficient knowledge, background, and training, as well as a level of authority that enables them
to adequately and effectively perform their assigned tasks.
With these points in mind the following options are worthy of your consideration:
1. Hire an individual that has the necessary blended background in technology, information
security, banking and risk management. This person should also have the capability to
understand the business implications of this responsibility. You need someone who understands
technology and information security risks and can clearly articulate such risks to management
and the Board. They need to be able to convert complicated technical issues into plain language
and help others to understand its potential impact on the business.
The main potential issue with this option is that these resources are in short supply and typically
command salaries that will likely burden most financial institutions.
2. Assign the responsibility to an existing bank employee. It is important that this person have
many of the skills described above and that they are given sufficient time outside their normal set
of responsibilities to effectively carry the additional ISO responsibilities.
The main potential issue here is that the likelihood that a person with such skills exists within
most banks is remote. If such a resource does exist they probably work in the IT Department and
therefore lack the independence necessary to act as ISO. It is very likely that a resource selected
from the existing ranks would result in compromised effectives of the position.
3. Outsource this role to a qualified professional. Hiring a full-time staff position as described in
option 1 can be capital intensive. Outsourcing can provide you the same type of resource but at a
significant cost savings. This option may be the most cost effective for many small to midsize
community banks.
The main potential issue with this option is vendor management, scope of services and ability to
understand banking.
In all three scenarios, cost and skill are key issues. Clearly option 2 is the lowest cost, as the bank
is basically taking on opportunity cost assuming they do not add an FTE to the persons unit who
is acting as the ISO. Out-sourcing certainly will add hard dollar expense, but outside of cost there
are other benefits related to this option. One is that the outside entity is completely independent
of IT operations. Another is that an outsourced ISO role can be made to be flexible and may be
tailored to meet specific business requirements of your organization. In addition, using an out-
side ISO can reduce the annual IT audit costs.
Other issues to keep in mind when considering outsourcing the ISO role:
Outsourced professionals should have deep technical, IT security and banking industry
experience.
Consider the importance of IT security certifications such as CISM (Certified Information
Security Manager), CISSP (Certified Information Systems Security Professional) or
CISA (Certified Information Systems Auditor).
Outsourced service options should be consistent with FFIEC guidance.
Banks should consider their options in filling this increasingly critical role whether they are
being forced to by examiners or auditors. Whichever option works best for your institution, you
need to ensure that this new role has a direct line of reporting to the Board or its delegated
executive committee.
January 2, 2008
John DeMauro can be reached at 508-614-0719, or at
JDemauro@.practicalsecuritysolutions.com and Tom Grottke can be reached at 860-798-7107
or tgrottke@nebsg.com
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5834)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (350)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (824)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (405)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Bid-No Bid Assessment and Checklist FormDocument1 pageBid-No Bid Assessment and Checklist FormSaad Al-Subaie100% (3)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- How To Integrate Micro and Macro Management For Organization Evolution?Document4 pagesHow To Integrate Micro and Macro Management For Organization Evolution?Alaa Din AL-khwarizmiNo ratings yet
- Strategic Foresight PlatformDocument575 pagesStrategic Foresight Platformtestato123No ratings yet
- Procurement and TenderingDocument68 pagesProcurement and TenderingBUKENYA BEEE-2026No ratings yet
- Statement of Work PDFDocument7 pagesStatement of Work PDFJairo Castro FlorianNo ratings yet
- Embrace The Inevitable - Six Imperatives To Prepare Your Company For Cloud ComputingDocument4 pagesEmbrace The Inevitable - Six Imperatives To Prepare Your Company For Cloud ComputingswainanjanNo ratings yet
- Assignment 1Document17 pagesAssignment 1ShammimBegumNo ratings yet
- AMC Process in SAP PM PDFDocument12 pagesAMC Process in SAP PM PDFPiyush BoseNo ratings yet
- DATAVERSITY Erwin State of Data Governance 2020 Final 012420Document16 pagesDATAVERSITY Erwin State of Data Governance 2020 Final 012420Jorge GarzaNo ratings yet
- Case Analysis Tip-Hrdm 423Document5 pagesCase Analysis Tip-Hrdm 423EhmzyDegacoBacsafra0% (1)
- Session 4: Supply Chain IntegrationDocument32 pagesSession 4: Supply Chain IntegrationWonderkid YHHNo ratings yet
- AssignmentDocument7 pagesAssignmentmian577938No ratings yet
- Objective of CostingDocument2 pagesObjective of CostingAshik Uz ZamanNo ratings yet
- GAMP 5 Quality Risk Management Approach: by Kevin C. Martin and Dr. Arthur (Randy) PerezDocument7 pagesGAMP 5 Quality Risk Management Approach: by Kevin C. Martin and Dr. Arthur (Randy) PerezSaurabh VijNo ratings yet
- Chapter 31 Computer-Aided Software EngineeringDocument6 pagesChapter 31 Computer-Aided Software EngineeringRoshan KCNo ratings yet
- Corporate FinanceDocument4 pagesCorporate FinanceNeerajNo ratings yet
- SSW Nom20Document72 pagesSSW Nom20Brian RamphisaNo ratings yet
- Why KPA Is Important in Performance ManagemantDocument2 pagesWhy KPA Is Important in Performance ManagemantbbarpdNo ratings yet
- MMFIDocument3 pagesMMFImayoorNo ratings yet
- Literature Review On Inventory Management TechniquesDocument5 pagesLiterature Review On Inventory Management Techniquesea44a6t7No ratings yet
- ETL Vs ELTDocument7 pagesETL Vs ELTMiguel Angel PiñonNo ratings yet
- Week 001-003 BPODocument5 pagesWeek 001-003 BPOkitaNo ratings yet
- Quality Service in Tourism and Hospitality: Prepared By: Jaymee Ara E. CatchillarDocument43 pagesQuality Service in Tourism and Hospitality: Prepared By: Jaymee Ara E. CatchillarEfaith1256No ratings yet
- Sartaj Alam Sales & Marketing ManagerDocument4 pagesSartaj Alam Sales & Marketing ManagerZubair AhmedNo ratings yet
- Job Descriptions: Writing Job Descriptions and Examples, Job Descriptions DutiesDocument22 pagesJob Descriptions: Writing Job Descriptions and Examples, Job Descriptions DutiesSurjit SinghNo ratings yet
- OSCM Merge @vickyDocument183 pagesOSCM Merge @vickySanjay sadafule100% (1)
- My Cloud Power BriefDocument6 pagesMy Cloud Power BriefChiTownITNo ratings yet
- Successfully Utilizing CMMSEAM Systems Maintenance Strategy Series by WiremanDocument133 pagesSuccessfully Utilizing CMMSEAM Systems Maintenance Strategy Series by WiremanLuis Daniel RodríguezNo ratings yet
- Question 13 - Draft - Shortened 7COO3Document3 pagesQuestion 13 - Draft - Shortened 7COO3Flora InnehNo ratings yet
- Curriculum Vita: Mohammed Abdulrahman Mahyoub Qasem NameDocument2 pagesCurriculum Vita: Mohammed Abdulrahman Mahyoub Qasem Namerahbi malekNo ratings yet