Professional Documents
Culture Documents
(IJCST-V2I1P3) :K.Devika, M.Jawahar
(IJCST-V2I1P3) :K.Devika, M.Jawahar
Uploaded by
IJETA - EighthSenseGroupOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
(IJCST-V2I1P3) :K.Devika, M.Jawahar
(IJCST-V2I1P3) :K.Devika, M.Jawahar
Uploaded by
IJETA - EighthSenseGroupCopyright:
Available Formats
International Journal of Engineering Trends and Applications (IJETA) Volume 2 Issue 1, Jan-Feb 2015
RESEARCH ARTICLE
OPEN ACCESS
Review On: Cryptographic Algorithms for Data Integrity
Proofs in Cloud Storage
K.Devika1, M.Jawahar2
Department of Computer Science and Engineering
K.S.R Institute for Engineering and Technology K.S.R Kalvi Nagar,
Tiruchengode Namakkal-637215,
Tamilnadu, India
ABSTRACT
In cloud computing , there are many cryptographic algorithm for storing and retrieving data , the cryptographic
algorithm is more secure and highly well organized and successful in the field of authenticate information and keep
the information private. This paper discusses cryptographic algorithms for data integrity proofs in cloud storage. Data
integrity has been proved in cloud by enhancing the scheme known as proof of irretrievability (POR) using
cryptographic algorithms. Here various cryptographic algorithms are compared. Those are different from one another
based on its features. The important concerns that need to be addressed is to assure the customer of the integrity i.e.
correctness of his data in the cloud. As the data is physically not accessible to the user the cloud should provide a way
for the user to check if the integrity of his data is maintained or is compromised. In this paper a scheme provided
which gives a proof of data integrity in the cloud which the customer can employ to check the correctness of his data
in the cloud. This proof can be agreed upon by both the cloud and the customer and can be incorporated in the
Service level agreement (SLA) and this scheme ensures that the storage at the client side is minimal which will be
beneficial for thin clients.
Keywords:- Cloud Storage, Proof Of Retreivability (POR), Service Level Agreement(SLA), Data Integrity,
Cryptographic Algorithm.
I.
INTRODUCTION
II.
Cloud storage moves the users
data to large data centres, which are
remotely located, on which user does not
have any control. However, this unique
feature of the cloud posses many new
security challenges which need to be
clearly understood and resolved
The importance of cloud storage is
reflected by the convenience of accessing
the data from anywhere at any time
through internet. For example, user store
their data using gmail, ticket reservation
etc. the data integrity to be proved by
using the cryptographic algorithm. It use
different cryptographic algorithm such as
AES, DES, RSA,SHA,HASH .
ISSN: 2393 - 9516
RELATED WORK
Different studies are performing for
proving data integrity, it based on file or
data
retrieval.
It
use
Different
cryptographic algorithm to retrieve the file
or data.
A.
AES Algorithm
The
Advanced
Encryption
Standard (AES) is a symmetric-key
algorithm approved by NIST which means
same key is used for both encrypting and
decrypting the data.
AES is based on the Rijndael
cipher developed by two Belgian
cryptographers, Joan Daemen and Vincent
Rijmen Rijndael is a family of ciphers with
different key and block sizes each with a
www.ijetajournal.org
Page 14
International Journal of Engineering Trends and Applications (IJETA) Volume 2 Issue 1, Jan-Feb 2015
block size of 128 bits, but three different
key lengths are used as 128, 192 and 256
bits. The input to the encryption and
decryption algorithm is a single 128 bits
block, this block is depicted as a 4x4
square matrix of bytes and copied into the
State array, which is modified at each
stage of encryption and decryption. After
the final stage, State is copied to an output
matrix. Similarly the key is depicted as a
square matrix of bytes. This key is
expanded into an array of key schedule
words. In AES each word is four bytes,
and the total key schedule is 44 words for
the 128 bit key. The ordering of bytes
within a matrix is by column. The cipher
consists of number(N) of rounds depends
on the key length as 10 rounds for a 16 bit
key, 12 rounds for a 24 bit key, and 14
rounds for a 32 bit key. The first N-1
round consists of four transformation
functions Known as SubBytes, ShiftRows,
MixColumns, and AddRoundKey. The
final
round
contains
only
three
transformations, and there is a initial single
transformation (AddRoundKey) before the
first round. Only the AddRoundKey stage
makes use of the key. Therefore the cipher
begins and ends with an AddRoundKey.
SubBytes is a non-linear substitution step
where each byte is replaced with another
according to a lookup table. ShiftRows is a
transposition step where the last three rows
of the state are shifted cyclically a certain
number of steps. MixColumns is a mixing
operation which operates on the columns
of the state, combining the four bytes in
each column.
AES algorithm is more reliable and
secure and provides various key lengths to
process the input files. By using this
algorithm, the amount of control that an
attacker can have on encrypted data
ISSN: 2393 - 9516
depends on the encryption type and some
specific details of some encryption modes
can make the life a bit harder for the
attacker if he wants to make surgical
modifications.
B.
DES Algorithm
Data Encryption Standard (DES)
is a symmetric block cipher developed by
IBM. This algorithm uses a 56-bit key to
encipher/decipher a 64-bit block of data.
The key is always presented as a 64-bit
block, every 8th bit of which is ignored.
However, it is usual to set each 8th bit so
that each group of 8 bits has an odd
number of bits set to 1.
The processing of plain text
proceeds in three phases. First, the 64-bit
plain text passes through an Initial
Permutation (IP) that rearranges the bits to
produce the permutated input. This is
followed by the phase consisting of sixteen
rounds of the same function, which
involves both permutation and substitution
functions. The output of the last (sixteenth)
round consists of 64 bits that are a function
of the input plain text and the key. The left
and right halves of the output are swapped
to produce the pre output. Finally the pre
output is passed through a permutation
[IP-1]that is the inverse of the initial
permutation function, to produce the 64 bit
ciphertext. With the exception of the initial
and final permutation, DES has the exact
structure of a Fiestel cipher and it has key
length as too short.
The substitution consists of a set of
eight s boxes each of which accepts 6 bits
as input and produce 4 bits as output. The
key length argument goes like this.
Assuming that the only feasible attack on
DES is to try each key in turn until the
www.ijetajournal.org
Page 15
International Journal of Engineering Trends and Applications (IJETA) Volume 2 Issue 1, Jan-Feb 2015
right one is found, then
testing keys per second
average) one key every
reasonable people might
comforting and a good
strength of the algorithm.
C.
each capable of
would find (on
12 hours. Most
find this rather
measure of the
RSA algorithm
RSA is a public key algorithm
invented by Rivest, Shamir and Adleman.
It uses different keys for encryption and
decryption. Therefore it is called as
asymmetric. RSA based on modular
exponentiation. Numbers e, d and N are
chosen with the property that if A is a
number less than N, then (Ae mod N)d
mod N = A. This means that we can
encrypt A with e and decrypt using d.
Conversely we can encrypt using d and
decrypt using e.
The pair of numbers (e,N) is known as
the public key and can be published.
The pair of numbers (d,N) is known as
the private key and must be kept secret.
The number e is known as the public
exponent, the number d is known as the
private exponent, and N is known as the
modulus. The concerns on the Key length,
Anybody knowing the public key and they
can use it to create encrypted messages,
but only the owner of the secret key can
decrypt them. Conversely the owner of the
secret key can encrypt messages that can
be decrypted by anybody with the public
key. RSA also used for digital signature.
Anybody successfully decrypting such
messages can be sure that only the owner
of the secret key could have encrypted
them. This fact is the basis of the digital
signature technique.
In digital signature technique, the
RSA algorithm uses the public key to
ISSN: 2393 - 9516
encrypt and the private key to decrypt in
the encryption/decryption process. The
private key is used to encrypt and the
public key is used to decrypt in the digital
signature. The sender using HASH
algorithm to calculate the hash value of the
file M, then generate the digital signature
C from using the key to encrypt digital
abstract and then M C together and sent to
the receiver. The receiver receives the file
M1 and digital signature C1, needs to
verify that M and M1 are identical.
RSA is very slow with the problem
of choosing the long keys when compared
with a symmetric block cipher such as
DES. The best solution is to use RSA for
digital signatures and for protecting DES
keys. When used in practice, RSA must be
combined with some form of padding
scheme, so that no values of M result in
insecure cipher texts. RSA used without
padding may have some problems. RSA
also has a particular mathematical
structure that can potentially be exploited
without solving the RSA problem directly.
To achieve the full strength of the RSA
problem, an RSA-based cryptosystem
must also use a padding scheme like
Optimal Asymmetric Encryption Padding
(OAEP), to protect against such structural
problems in RSA.
D.
SHA Algorithm
The Secure Hash Algorithm is the
most widely used hash function developed
by the National Institute of Standards and
Technology (NIST) and published as a U.S
Federal Information Processing Standard
(FIPS). A prime motivation for the
publication of the SHA was the Digital
Signature Standard, in which it is
incorporated. The four SHA algorithms are
www.ijetajournal.org
Page 16
International Journal of Engineering Trends and Applications (IJETA) Volume 2 Issue 1, Jan-Feb 2015
structured differently and are named as
SHA-0, SHA-1, SHA-2, andSHA-3.
SHA-0:
This is the original
version of Secure Hash Algorithm. SHA-0
produces the 160-bit hash function
published in 1993 under the name "SHA".
It was withdrawn shortly after publication
due to an undisclosed "significant flaw"
and replaced by the slightly revised
version SHA-1.
SHA-1: A 160-bit hash function
which resembles the earlier MD5
algorithm. This was designed by the
National Security Agency (NSA) to be part
of the Digital Signature Algorithm. In
SHA-1, the cryptographic weaknesses
were discovered and the standard was no
longer approved for most cryptographic
uses after 2010. SHA-1 is the most widely
used of the existing SHA hash functions,
and is employed in several widely used
applications and protocols.
SHA-1 is very similar to SHA-0,
but alters the original SHA hash
specification
to
correct
alleged
weaknesses. It produces a 160-bit (20byte) hash value that is typically rendered
as a hexadecimal number, 40 digits long
and differs from SHA-0 only by a single
bitwise rotation in the message schedule of
its compression function, this was done,
according to the NSA, to correct a flaw in
the original algorithm which reduced its
cryptographic security. SHA-1 appears to
provide greater resistance to attacks
supporting the NSAs assertion that the
change increased the security.
In Data integrity, Source control
management systems such as Git and
Mercurial use SHA-1 not for security but
for ensuring that the data has not changed
due to accidental corruption.
ISSN: 2393 - 9516
SHA-2: published in 2001, is
significantly different from the SHA-1
hash function. A family of two similar
hash functions, with different block sizes,
known as SHA-256 and SHA-512. They
differ in the word size. SHA-256 uses 32bit words where SHA-512 uses 64-bit
words. There are also truncated versions of
each standard designed by the NSA known
as SHA-224 and SHA-384. SHA-1 and
SHA-2 are the secure hash algorithms
required by law for use in certain U.S.
Government applications, including use
within other cryptographic algorithms and
protocols, for the protection of sensitive
unclassified information.
SHA-3: In 2012, NIST selected an
additional
algorithm,
Keccak,
for
standardization under SHA-3. It supports
the same hash lengths as SHA-2, and its
internal structure differs significantly from
the rest of the SHA family.
E.
HASH Algorithm
A Hash algorithm is used for
computing a condensed representation of a
fixed length message/file. This is
sometimes known as a message digest or a
fingerprint. Some programs need a one
way cryptographic hash algorithm, that is,
a function that takes an arbitrary amount of
data and generates a fixed-length number
that hard for an attacker to invert, this
stated as it is difficult for an attacker to
create a different set of data to generate
that same value. Hashing (or digest)
algorithm should be computationally
infeasible to construct a different message
with the same digest.
The hash algorithm is a
development of the MD4 algorithm
invented by Ronald
Rivest and
www.ijetajournal.org
Page 17
International Journal of Engineering Trends and Applications (IJETA) Volume 2 Issue 1, Jan-Feb 2015
announced in 1990. Unfortunately, MD4
was flawed, so Rivest made some
revisions, and the resulting algorithm was
christened MD5. MD5 is a hashing
algorithm that takes a message of up to
264 bits and reduces it to a digest of 128
bits (16 bytes). Instead of MD5 The new
code to be written by using SHA-1. The
SHA-256, SHA-384, or SHA-512 was
used when more bits are needed in hash
algorithm.
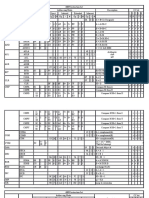
III.
Algorithms
Functions
Drawbacks
used
AES
DES
i)SubBytes
AES
decryption
ii) ShiftRows
cipher
iii)MixColumns
identical
iv)AddRoundKey
encryption cipher.
i)Expansion D-box,
ii)Whitener(XOR),
iii)S-Boxes and
iv)Straight D-Box.
i) Key length is
too short.
ii)Guarantees the
is
to
integrity
authenticity
not
the
or
(but
not security of the
COMPARATIVE ANALYSIS
message).
RSA
i)Encrypting
messages,
ii)Decrypting
messages,
iii)Padding schemes
ivSigning
messages.
SHA
Compression
function
HASH
Message Digest
i)
Must
use
a padding scheme
to protect against
such
structural
problems
ii) It has no
random
component.
Therefore,
an
attacker
can
successfully
launch a chosen
plaintext
attack
against
the
cryptosystem.
Functions
are
vulnerable
to
length-extension
and
partialmessage collision
attacks.
i)Worst behavior
cause of excessive
collisions
ii)Results in poor
performance
IV. CONCLUSION
This paper presents an extensive
survey on data integrity proofs in cloud
storage using cryptographic algorithm.
Many new approaches are proposed in the
field of data integrity proofs in cloud
ISSN: 2393 - 9516
www.ijetajournal.org
Page 18
International Journal of Engineering Trends and Applications (IJETA) Volume 2 Issue 1, Jan-Feb 2015
storage. Many research issues have been
highlighted and direction for future work
has been suggested. Many open issues
have been highlighted by the researchers
such as dealing with data integrity proofs
in cloud by different techniques future
work will done.
REFERENCES
[1]
[2]
[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
Behrouz
A.
Forouzan,
Debdeep
Mukhopadhya,
Cryptography
and
Network Security Second Edition,2011.
William Stallings , Cryptography and
Network Security, Fifth Edition.
Miles E. Smid and Dennis K. Branstad,
Data Encryption Standard past and
furure may-1998
Dr Reinhard Wobst, The Advanced
Encryption Standard(AES): The Successor
of DES 2001.
Douglas Stinson, Chapman & Hall/CRC,
Cryptography: Theory and Practice.
Charles Kaufman et al, Network
Security: Private Communication in a
public word.
Dr. Prerna Mahajan and Abhishek
Sachdeva, A Study of encryption
Algorithms AES,DES and RSA for
security, 2013.
Hamdan.O.Alan azi et al, New
comparative study between DES,3DES
and AES within Nine Factors, 2010.
Sunitra, Comparative Analysis of AES
and DES security Algorithms,2013.
Krunal Suthar et al, Analytical
Comparison of Symmetric Encryption and
Encoding
Techniques
for
Cloud
Environment, 2012.
Cetin Kaya Koc , Cryptographic
Algorithms and Key Size Issues.
ISSN: 2393 - 9516
www.ijetajournal.org
Page 19
You might also like
- AI For HCI - BOOK PDFDocument602 pagesAI For HCI - BOOK PDFAnn DanickNo ratings yet
- Film Scanner Slide ManualDocument30 pagesFilm Scanner Slide Manualhtcstech67% (6)
- Hash Functions: - Dr. Sanjay H ADocument125 pagesHash Functions: - Dr. Sanjay H ARiddhi SinghalNo ratings yet
- Encryption and Decryption Algorithms 1Document5 pagesEncryption and Decryption Algorithms 1Jolina Joy B. BayacaNo ratings yet
- Research Paper 2Document6 pagesResearch Paper 2Suraj ShindeNo ratings yet
- Comparative Study of Different Cryptographic Algorithms For Data Security in Cloud ComputingDocument5 pagesComparative Study of Different Cryptographic Algorithms For Data Security in Cloud ComputingAsaba BrianNo ratings yet
- Encryption Algorithms and Digital SignaturesDocument11 pagesEncryption Algorithms and Digital SignaturesPrateek MahajanNo ratings yet
- (Delfs and Knebl 2015) : Individual Assignment - Im41103 Network SecurityDocument6 pages(Delfs and Knebl 2015) : Individual Assignment - Im41103 Network SecurityNaue J.No ratings yet
- Pec ItDocument9 pagesPec ItPratham RaiNo ratings yet
- Cis Unit2 NotesDocument35 pagesCis Unit2 NotesAAMENA SUZZANNENo ratings yet
- Cryptography inDocument97 pagesCryptography inDhanraj DSNo ratings yet
- Cryptography: Software SectionDocument5 pagesCryptography: Software SectionJaymin PatelNo ratings yet
- Pec ItDocument9 pagesPec ItPratham RaiNo ratings yet
- 4 A Study of Encryption AlgorithmsDocument9 pages4 A Study of Encryption AlgorithmsVivekNo ratings yet
- Using Cryptography Algorithms To Secure Cloud Computing Data and ServicesDocument4 pagesUsing Cryptography Algorithms To Secure Cloud Computing Data and ServicesRareş T. BogdanNo ratings yet
- AES PaperDocument5 pagesAES PaperAmitPrakashSinghNo ratings yet
- AES Seminar ReportDocument17 pagesAES Seminar ReportAbinash AgrawalNo ratings yet
- Compusoft, 3 (8), 1059-1064 PDFDocument6 pagesCompusoft, 3 (8), 1059-1064 PDFIjact EditorNo ratings yet
- Study of Cloud Computing Security Methods: Cryptography: Maryann Thomas, S. V. AthawaleDocument5 pagesStudy of Cloud Computing Security Methods: Cryptography: Maryann Thomas, S. V. AthawalejecamargNo ratings yet
- Des PDFDocument11 pagesDes PDFHenock urgessaNo ratings yet
- Net Security Chap 2Document20 pagesNet Security Chap 2Asif KoujaganurNo ratings yet
- Transform Operator Random Generator Delimiter Based Encryption Standard (TORDES)Document4 pagesTransform Operator Random Generator Delimiter Based Encryption Standard (TORDES)Ajay ChaudharyNo ratings yet
- Unit Ii - Block Ciphers & Public Key CryptographyDocument60 pagesUnit Ii - Block Ciphers & Public Key CryptographyAadilNo ratings yet
- Final DocumentDocument60 pagesFinal DocumentRitul RaiNo ratings yet
- Encryption and Decryption Using AES in The Field of Network Communication Based On ConfidentialityDocument3 pagesEncryption and Decryption Using AES in The Field of Network Communication Based On ConfidentialityUjjwal KumarNo ratings yet
- Secure and Improved Approach For 3-Des Algorithm Against Cryptographic AttacksDocument8 pagesSecure and Improved Approach For 3-Des Algorithm Against Cryptographic AttacksBiancaNo ratings yet
- Security 4Document15 pagesSecurity 4علي الورفليNo ratings yet
- Topic 7 - CryptographyDocument22 pagesTopic 7 - Cryptographyrojaluteshi28No ratings yet
- Chapter8 OverviewDocument10 pagesChapter8 OverviewEuber ChaiaNo ratings yet
- Review IDocument17 pagesReview I20PCS509 S.AbithaNo ratings yet
- International Journal of Engineering Research and DevelopmentDocument8 pagesInternational Journal of Engineering Research and DevelopmentIJERDNo ratings yet
- Crypto SystemsDocument36 pagesCrypto SystemsDitty KunnathNo ratings yet
- Sravani 2018Document5 pagesSravani 2018viralsddNo ratings yet
- Doubble EncriptionDocument60 pagesDoubble Encriptiondeepak kumarNo ratings yet
- CSS Lab ManualDocument32 pagesCSS Lab ManualQaif AmzNo ratings yet
- Main Project SlidesDocument26 pagesMain Project SlidesHari Harul VullangiNo ratings yet
- Mini Project ReportDocument11 pagesMini Project ReportKiran BogamNo ratings yet
- Implementation of Aes Algorithm Using Verilog: Gireesh Kumar P, P. Mahesh KumarDocument4 pagesImplementation of Aes Algorithm Using Verilog: Gireesh Kumar P, P. Mahesh KumarVasanth VasuNo ratings yet
- Comparative Study of Different Cryptographic Algorithms For Data Security in Cloud ComputingDocument7 pagesComparative Study of Different Cryptographic Algorithms For Data Security in Cloud ComputingPathan MehemudNo ratings yet
- Eliptic Curve Cryptography 2Document7 pagesEliptic Curve Cryptography 2Yashashri NaikNo ratings yet
- AES-128 Performance in Tinyos With CBC Algorithm (WSN) : Ankit Srivastava, Dr. N. Revathi VenkataramanDocument10 pagesAES-128 Performance in Tinyos With CBC Algorithm (WSN) : Ankit Srivastava, Dr. N. Revathi VenkataramanIJERDNo ratings yet
- MCQ & Subjective 707Document15 pagesMCQ & Subjective 707Shahid Azeem0% (2)
- NSC Module II PptsDocument32 pagesNSC Module II PptssamNo ratings yet
- Internet of Things Encryption James Ballance Developing The Industrial Internet of Things I 3/11/2019Document8 pagesInternet of Things Encryption James Ballance Developing The Industrial Internet of Things I 3/11/2019Ahmed Mahamed Mustafa GomaaNo ratings yet
- NSC Unit 2 Zoom Cls (15-04-2020)Document20 pagesNSC Unit 2 Zoom Cls (15-04-2020)yuvaraaj aletiNo ratings yet
- Simulation of Image EncryptionDocument92 pagesSimulation of Image EncryptionBodhankar Santosh KumarNo ratings yet
- Survey Paper Comparing ECC With RSA, AES and Blowfish AlgorithmsDocument4 pagesSurvey Paper Comparing ECC With RSA, AES and Blowfish AlgorithmsEditor IJRITCCNo ratings yet
- Basics: Cryptology Is The Study of Cryptography and CryptanalysisDocument7 pagesBasics: Cryptology Is The Study of Cryptography and CryptanalysisPrakash ThalaNo ratings yet
- Unit-2 - Part-IDocument24 pagesUnit-2 - Part-IRam Prasad Reddy SadiNo ratings yet
- Unit 8Document42 pagesUnit 8Tin SiocoNo ratings yet
- Combination of The "Data Encryption Standard" Algorithm (DES) and The "Public-Key Encryption" Algorithm (RSA) On The Key - Generation StageDocument3 pagesCombination of The "Data Encryption Standard" Algorithm (DES) and The "Public-Key Encryption" Algorithm (RSA) On The Key - Generation StageInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Comparison of Symmetric and Asymmetric Cryptography With Existing Vulnerabilities and CountermeasuresDocument4 pagesComparison of Symmetric and Asymmetric Cryptography With Existing Vulnerabilities and CountermeasuresLaine VenâncioNo ratings yet
- UNIT2Document29 pagesUNIT2Evy LawNo ratings yet
- Cryptography and Network Security HandoutDocument79 pagesCryptography and Network Security HandoutDr Narayana Swamy RamaiahNo ratings yet
- High Efficient Complex Parallelism For CryptographyDocument7 pagesHigh Efficient Complex Parallelism For CryptographyInternational Organization of Scientific Research (IOSR)No ratings yet
- Numeric To Numeric Encryption of Databases Using 3kDES AlgorithmDocument5 pagesNumeric To Numeric Encryption of Databases Using 3kDES AlgorithmSwathi VasudevanNo ratings yet
- Topic 2 Highlights - Cryptographic ToolsDocument5 pagesTopic 2 Highlights - Cryptographic ToolsOlivia RadaNo ratings yet
- Unit - 2 Two Marks CNSDocument6 pagesUnit - 2 Two Marks CNSanandhacNo ratings yet
- Advanced Encryption Standard (AES) Algorithm To Encrypt and Decrypt DataDocument12 pagesAdvanced Encryption Standard (AES) Algorithm To Encrypt and Decrypt Datatatigutla thulasammaNo ratings yet
- RSA Algorithm - Simple English Wikipedia, The Free EncyclopediaDocument27 pagesRSA Algorithm - Simple English Wikipedia, The Free EncyclopediaPragyan NayakNo ratings yet
- (IJETA-V11I1P4) :manoj Kumar Sharma, Hemant Kumar SainDocument5 pages(IJETA-V11I1P4) :manoj Kumar Sharma, Hemant Kumar SainIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V11I1P8) :pushpendra Kumar Balotia, Anil Kumar SharmaDocument3 pages(IJETA-V11I1P8) :pushpendra Kumar Balotia, Anil Kumar SharmaIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V10I1P1) :M.Thachayani, G.RubavaniDocument3 pages(IJETA-V10I1P1) :M.Thachayani, G.RubavaniIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V11I1P1) :gaurav Singh Raghav, Mohsin Khan AgwanDocument10 pages(IJETA-V11I1P1) :gaurav Singh Raghav, Mohsin Khan AgwanIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V11I1P7) :shubham Mishra, Vikas KumarDocument5 pages(IJETA-V11I1P7) :shubham Mishra, Vikas KumarIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V10I6P9) :yogesh Ajmera, Anil Kumar SharmaDocument6 pages(IJETA-V10I6P9) :yogesh Ajmera, Anil Kumar SharmaIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V10I3P1) :abdullah Al Hasan, Md. Shamim RayhanDocument7 pages(IJETA-V10I3P1) :abdullah Al Hasan, Md. Shamim RayhanIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I6P3) :mehtab Alam, Hemant Kumar SainDocument7 pages(IJETA-V8I6P3) :mehtab Alam, Hemant Kumar SainIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V9I5P1) :gasana James Madson, Habumugisha Fulgence, Uwimana Josephine, Munyaneza Midas Adolphe, Uwantege Stellah Prossy, Niyonsaba MaximilienDocument6 pages(IJETA-V9I5P1) :gasana James Madson, Habumugisha Fulgence, Uwimana Josephine, Munyaneza Midas Adolphe, Uwantege Stellah Prossy, Niyonsaba MaximilienIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V10I6P6) :tabssum Bano, Mohsin Khan AgwanDocument8 pages(IJETA-V10I6P6) :tabssum Bano, Mohsin Khan AgwanIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V9I3P1) :yew Kee WongDocument7 pages(IJETA-V9I3P1) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V10I6P1) :yogesh Ajmera, Anil Kumar SharmaDocument4 pages(IJETA-V10I6P1) :yogesh Ajmera, Anil Kumar SharmaIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V10I2P1) :dr. A. Manjula, D. Kalpana, M. Sai Prasad, G. Sanjana, B. Mahender, D. Manisha, M. AbhishekDocument10 pages(IJETA-V10I2P1) :dr. A. Manjula, D. Kalpana, M. Sai Prasad, G. Sanjana, B. Mahender, D. Manisha, M. AbhishekIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V10I5P1) :rakesh K BumatariaDocument12 pages(IJETA-V10I5P1) :rakesh K BumatariaIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V9I1P2) :yew Kee WongDocument7 pages(IJETA-V9I1P2) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V9I1P5) :kavitha RDocument6 pages(IJETA-V9I1P5) :kavitha RIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I5P3) :sujith Krishna B, Priyanka BasavaDocument3 pages(IJETA-V8I5P3) :sujith Krishna B, Priyanka BasavaIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V921P1) :yew Kee WongDocument5 pages(IJETA-V921P1) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V9I2P2) :yew Kee WongDocument6 pages(IJETA-V9I2P2) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V9I1P1) :yew Kee WongDocument7 pages(IJETA-V9I1P1) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I6P2) :yew Kee WongDocument5 pages(IJETA-V8I6P2) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I4P6) :hari Om Choumal, Hitesh Bhagnani, Deepansu Soni, Dr. Manish MukhijaDocument5 pages(IJETA-V8I4P6) :hari Om Choumal, Hitesh Bhagnani, Deepansu Soni, Dr. Manish MukhijaIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I5P8) :simiran Kuwera, Sunil Agarwal, Rajkumar KaushikDocument6 pages(IJETA-V8I5P8) :simiran Kuwera, Sunil Agarwal, Rajkumar KaushikIJETA - EighthSenseGroup100% (1)
- (IJETA-V8I5P1) :yew Kee WongDocument5 pages(IJETA-V8I5P1) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I6P1) :yew Kee WongDocument7 pages(IJETA-V8I6P1) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I5P2) :yew Kee WongDocument7 pages(IJETA-V8I5P2) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (Ijeta-V8i5p4) :anupama UshaDocument3 pages(Ijeta-V8i5p4) :anupama UshaIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I4P8) :nisha Rani, Kiran Ahuja, Gaurav Patel, Kushagra JangidDocument8 pages(IJETA-V8I4P8) :nisha Rani, Kiran Ahuja, Gaurav Patel, Kushagra JangidIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I4P11) :yew Kee WongDocument6 pages(IJETA-V8I4P11) :yew Kee WongIJETA - EighthSenseGroupNo ratings yet
- (IJETA-V8I4P7) :zaid Ahmed, Akash Rawat, Pankaj KumariDocument6 pages(IJETA-V8I4P7) :zaid Ahmed, Akash Rawat, Pankaj KumariIJETA - EighthSenseGroupNo ratings yet
- Atmel 8011 8 Bit Avr Microcontroller Atmega164p 324p 644p DatasheetDocument505 pagesAtmel 8011 8 Bit Avr Microcontroller Atmega164p 324p 644p DatasheetDhaiana VillarNo ratings yet
- 0818 Gearsolutions PDFDocument76 pages0818 Gearsolutions PDFdesetekNo ratings yet
- 3D Pipe ModellingDocument21 pages3D Pipe ModellingMuhamadSadiqNo ratings yet
- Batch 10 - AdvtDocument24 pagesBatch 10 - AdvtsumitNo ratings yet
- Expression Language (EL) in JSPDocument25 pagesExpression Language (EL) in JSPAnkit AgrawalNo ratings yet
- 5 Steps To Designing An Embedded Software Architecture, Step 3Document7 pages5 Steps To Designing An Embedded Software Architecture, Step 3sclu2000No ratings yet
- Image DetectionDocument5 pagesImage Detectionbruno.lopezgNo ratings yet
- Log FileDocument39 pagesLog FileConnor RoweNo ratings yet
- PE3308 - Technical Summary For Cable1632 Rev DDocument2 pagesPE3308 - Technical Summary For Cable1632 Rev DJohn HallowsNo ratings yet
- Sponsorship OpportunitesDocument9 pagesSponsorship OpportuniteshadihadihaNo ratings yet
- Introduction To STM32 Before 2 ExpDocument36 pagesIntroduction To STM32 Before 2 Expsaira isratNo ratings yet
- Epson RC PL 60 Users Guide-Rc620 (v62r5)Document382 pagesEpson RC PL 60 Users Guide-Rc620 (v62r5)Produccion TAMNo ratings yet
- Check FeaturesDocument4 pagesCheck FeaturesAnkit GuptaNo ratings yet
- Task 2 - Job Roles and Freelance 2022-23Document6 pagesTask 2 - Job Roles and Freelance 2022-23api-632047644No ratings yet
- Spec Hotel Load Conv P4 - Rev 0 - Aug 12Document35 pagesSpec Hotel Load Conv P4 - Rev 0 - Aug 12divisional electrical enggNo ratings yet
- Visa Processing Information SystemDocument4 pagesVisa Processing Information SystemKpsmurugesan KpsmNo ratings yet
- UT Dallas Syllabus For cs1335.001.11f Taught by Jeyakesavan Veerasamy (Veerasam)Document8 pagesUT Dallas Syllabus For cs1335.001.11f Taught by Jeyakesavan Veerasamy (Veerasam)UT Dallas Provost's Technology GroupNo ratings yet
- 6809 Instruction SetDocument8 pages6809 Instruction Setزهر الدين ضيفNo ratings yet
- Business Case For New Bug Tracking - SampleDocument2 pagesBusiness Case For New Bug Tracking - SampleShar MayNo ratings yet
- 2020-21 M.C.A. (Affiliated Colleges and Instituite)Document58 pages2020-21 M.C.A. (Affiliated Colleges and Instituite)Brothers CreationNo ratings yet
- The Digital School PDFDocument15 pagesThe Digital School PDFramNo ratings yet
- Seminar - Sty: AL TEX Style For Slides and Notes User's GuideDocument45 pagesSeminar - Sty: AL TEX Style For Slides and Notes User's GuideNPNo ratings yet
- Chapter Three The Research Methodology 3.1. Seismic Fragility Research DesignDocument14 pagesChapter Three The Research Methodology 3.1. Seismic Fragility Research DesignJholo BuctonNo ratings yet
- The One-Watt Server Linux Magazine2Document14 pagesThe One-Watt Server Linux Magazine2lee richardsNo ratings yet
- Ai Notes Unit-1Document22 pagesAi Notes Unit-13009 AiswaryaNo ratings yet
- BR1000 Operators Manual A PDFDocument49 pagesBR1000 Operators Manual A PDFJHGHJGJJNo ratings yet
- ITDataManagement PDFDocument208 pagesITDataManagement PDFBräyanAdriänNo ratings yet
- BS Lab Manual NewDocument36 pagesBS Lab Manual NewShameer PhyNo ratings yet