Professional Documents
Culture Documents
Network Based Intrusion Detection To Detect Steganographic Communication Channels - On The Example of Images
Network Based Intrusion Detection To Detect Steganographic Communication Channels - On The Example of Images
Uploaded by
proof14Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Network Based Intrusion Detection To Detect Steganographic Communication Channels - On The Example of Images
Network Based Intrusion Detection To Detect Steganographic Communication Channels - On The Example of Images
Uploaded by
proof14Copyright:
Available Formats
Network Based Intrusion Detection to Detect Steganographic
Communication Channels - On the Example of Images
Danny Hesse, Jana Dittmann, Andreas Lang
Otto-von-Guericke University of Magdeburg, Germany
AMSL Advanced Multimedia and Security Lab
{danny.hesse, andreas.lang, jana.dittmann}@iti.cs.uni-magdeburg.de
Abstract
Today we find a wide variety of Intrusion Detection
Systems (IDS). They can detect attacks against
network services or certain hosts. These attacks often
violate integrity, availability and confidentiality of a
IT-System or its data. One attack against data is the
loss of confidentiality. With the help of stegographic
tools one can hide data in a cover media and transmit
it over the network. At this time nowadays no
Intrusion Detection System is available to detect this
security violation. In this paper we discuss the design
of an IDS that is able to detect steganographic
communication in image data. Future Intrusion
Response Systems (IRS) could be trigged by the IDS
to react in accordance to the policy.
1. Motivation and Introduction
Beside the advantage of worldwide network
connections for enabling services and communication
between people the design of the communication
protocols has some disadvantages regarding to
security. Therefore to prevent attacks Intrusion
Prevention Systems (IPS) become very popular
recently, see [21], thus Intrusion Detection Systems
[11] seem less be effective to provide security by
being re-active. On the one hand IPS offer better
ways to secure a computer system in an active
manner. One the other hand, IPS does not allow to
analyse potential security leakages effectively. For
example steganographic communication could be
used for violate a security policy. IPS systems would
need to analyze the communication online to perform
active steganalysis. As described in [22] an online
analysis is time consuming and needs the complete
Proceedings of the 30th EUROMICRO Conference (EUROMICRO04)
1089-6503/04 $ 20.00 IEEE
transmitted data to decide if there is a covered
channel initiated. Thus for detecting image or audio
steganography, an IPS would need to interrupt the
online communication to perform steganalysis and to
decide allowing or disallowing the communication.
This approach would lead in most cases to quality of
services problems or would need an expensive
scalable hardware support. Therefore in our paper we
show, how to use steganalysis within IDS to detect
steganographic communication with offline analysis.
In our paper, we discuss how to use traditional
techniques from ID (looking for attacks against the
network protocols, (network) applications or
operating systems) in combination with steganalysis
techniques in general. Beside conceptual work we
introduce a Network based Intrusion Detection
System (NIDS) that is able to capture the network
traffic on the wire and look for potential covermediums. As modularised approach different
steganalysis tools can be integrated. In our example
implementation we use the well-known Chi-SquareTest [2] to distinguish between a clean or unclean
data. In the section 2 we briefly introduce
steganographical tools and steganalysis approaches.
In section 3 we discuss our design concept for
combining IDS and steganalysis. Experimental results
are presented in section 4 and section 5 summarizes
our work.
2. Brief Overview: Steganography and
Steganalysis
Today we find a wide variety of different techniques
to prove the usage of steganographic algorithms for
digital image data, see for example in [1] or [20]. In
our first investigations we limit our system to detect
steganographic content in images. In the next two
section we briefly describe two steganalysis
approaches to motivate the general idea.
2.1 Visual Attacks
Generally, a visual attack [2] tries to visualize the
changes of a steganographic application. The Result
of a visual attack is a more or less noised picture. The
decision whether the image has an embedded
message or not, depends upon the subjectively feeling
of the observer and can therefore difficult
implemented for an automatic detection. Furthermore
the modern steganography tools like the algorithms
Jsteg [9] and F5 [4] are robust against visual attacks
and thus they are not considered in our system design.
2.2 Chi-Square-Test
The Chi-Square-Test (CST) [2] is based on the
comparison of distribution functions. The attack uses
statistical features of an image to detect hidden
messages while most used steganographic algorithms
do not pay attention to the statistical properties of the
cover image. The changes can be detected/proved for
example with Chi-Square-Tests. The result is the
likelihood that a message is embedded. For further
information we refer to [1], [4], [5] and [9].
So there are some implementations that use the ChiSquare-Test. A very famous and powerful
tool is Stegdetect [10] from Niels Provos. Stegdetect
is an automated tool for detecting steganographic
content in images. It is capable of detecting several
different steganographic methods to embed hidden
information in JPEG images. Currently, the detectable schemes are jsteg, jphide, invisible secrets,
outguess 01.3b, F5, appendX, and camouflage.
3. Design of the Intrusion Detection
System
In this section we describe our design of the Intrusion
Detection System that detect the existence of a
steganographic message in image data.
3.1 Problem Analysis and Challenges
There are many Intrusion Detection Systems
available. For example the wide used Open Source
software Snort [15] the commercial products ISS
RealSecure [16] or Cisco NetRanger [17]. There are
also steganalysis tools like Stegdetect, as introduced
in Section 2. The currently available Intrusion
Detection Systems have no methods to detect covert
channels in digital images and the steganalysis tools
have no functions to monitor network connections.
That is why we combine techniques from Intrusion
Detection and Steganalysis to a new Intrusion
Detection System.
Proceedings of the 30th EUROMICRO Conference (EUROMICRO04)
1089-6503/04 $ 20.00 IEEE
3.2 Design Concept
Generally, there are two different ways to implement
Intrusion Detection Systems [11], [14]. On the one
side there are host-based systems (HIDS). One the
other side there are network based systems. Host
based systems monitor one IT-System alternatively
they support the attack detection on application or
operating system level. Network based systems
supports the attack detection on network level [12],
[14]. In contrast to NIDS the HIDS are able to detect
attacks in the encrypted host specific network traffic.
But the main disadvantage of a host-based system is,
that it can only detect intrusions against one system,
which is observed by the host. Network based
systems are able to monitor more than one system by
using one or several sensors. In our application area
for steganography detection the goal is to capture the
whole traffic in a network and therefore networkbased monitoring becomes favored in this
implementations. Generally, the NIDS consist of five
Subsystems [14]. A component for data collection, a
component for data analysis, a storage-component, an
IDS-management and a result visualisation are also
necessary. The 5 components are described below.
The Packer Capture Engine (PCE) captures the
traffic from the wire. In promiscuous mode, the
network interface can collect the traffic address
independent. For technical background and
conditions for network based data collection, please
look at [12]. In our implementation we use this
module to process all packets on the wire. The system
supports the TCP-Protocol, at the moment.
Furthermore, it can track more than one tcpconnection by using threads. If a tcp-connection is
finished (by tcp-fin or time-out) the collected data
will be analysed in the analysis module. In the
analyses module we use the Chi-Square-Test
introduced in Section 2. So we can detect the usage of
many steganographic tools like Jsteg, Jphide or
EzStego. Due to the openness of the design we are
able to extent our system easily for example to F5 [4]
and [5] in future. In the following we explain the
modules of the IDS and whose tasks. The result of the
analysis module will be stored in the database. Also
the parameters of the communication are stored in the
database. A short description of the values that will
be stored in the database is below. All parameters for
each module are configurable in the module itself. At
the moment there is no central management module.
In future we plan to implement a central
management, so that parameters for data collection,
analysis and storage can be manipulated in one ore
extra module.
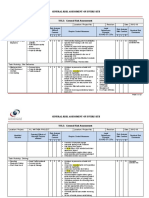
There is a HTML-Interface that is used for result
presentation or visualisation. With this interface
one can directly see the values that are stored in the
database. So one directly see when a hidden or
steganographic communication was done or not.
Please look at figure 2 for a visual representation, it
shows the basic architecture of the database.
The first value is the Unix_Timestamp, with this
value one can specify the time of the (hidden)
communication. The Source_IP, Destination_IP,
Source_Port and Destination_Port are used to
determine the kind of the communication. With the
Mime_Typ one can distinguish between the different
types e.g. JPEG, BMP, GIF. The analysis field
contains the result of the Chi-Square-Test. Possible
values are no stego message detected or !!stego
message detected!!. In this case one have all
parameters that are necessary to specify the
communication between to IT-systems.
4. Experimental Results
For testing the success and limits, we test this system
in several environments. The success of the system
can be divided into three parts. First part: The system
is successful if every image that has been transmitted
from or to the network could be captured and
analysed by the system. Second part: the system is
successful if the analysis routine classified every
collected image in a correct way. This means there
are no false positives and no false negatives. This is a
very theoretical assumption, so if we have a
minimum of false positives and false negatives the
system works successfully. The third part tries to
determine an embeding capacity limit to perform
reliable detection. For our simulations, we create a
typical web scenario (comp. figure 1) with one client,
one IDS and one webserver. For more transparency
we first explain the used hard and software
components as well as the test set. The Intrusion
Detection System is a Pentium 4 1,8 GHz with 512
MB RAM and one 3 Com 905 network interface is
installed. The IDS-operating system is Linux, kernel
2.4.19 and glibc 2.3. As database management system
(DBMS) we use MySQL-DBMS in version 4.0.15.
The client (A) is a Pentium III 800 MHz notebook
with 256 MB RAM. The operating system is a
Windows 2000 including SP3. The webserver (B) is a
IRIX 6.4 on an IP27 architecture with Apache 1.3.27.
In the following figure 2 you see the structure of the
test scenario schematically.
Figure 1 Schematical structure of the test scenario.
The client (A) visits a website on (B). The test
website consists of text and about 100 images. These
images are JPEGS with a size varying from 20 KB to
500 KB. In a predefined selection of about 20 images
we have embedded a message using Jsteg with a
message length varying from 10 to 100% of the
Proceedings of the 30th EUROMICRO Conference (EUROMICRO04)
1089-6503/04 $ 20.00 IEEE
maximum embeding capacity. The task of the IDS is
to detect the transfer of potential cover-media's (like
JPEGS). The next step is to analyse the collected data
with the Chi-Square-Test from [2]. In our scenario
the IDS was able to detect every image, so the system
was overall successful in our test environment for
both first test goals.
In regard to our third test goal due to the speed of
computation and in computing the CST the biggest
problem is that we could not detect small messages.
In this case small means messages that are less than
0.5 percent of the maximum embeding capacity.
These are the false negative results. In this case the
system works unsuccessful.
In figure 2 you see the result of the test. You see a
shortcut of the analysed database. In highperformance networks (>=100 Mbit), networks with
high packet density and bandwidth there is a packet
loss problem. In these networks the IDS cannot
process all the packets on the wire. The result is a
damaged and non-coherent image data. To minimize
these problems one can establish traffic filter that
filters the traffic to relevant data. We only analyse
TCP-connections so there is no need to look up in
UDP or ICMP-connections. The other problem
during packet processing is the performance of the
steganalysis algorithm (Chi-Square-Test). For a small
set of images the test is rather fast.
But websites usually consists of huge numbers of
images, which would have to be analysed
simultaneously. Therefore the Chi-Square-Test is
performed after storing the data in the database.
5. Conclusion
This document described very briefly a network
based Intrusion Detection System to detect
steganographic content in images. It is one of the first
IDS to detect hidden communication channel in
digital images. The extension of Intrusion Detection
Systems to steganalysis techniques will close an
existing gap. In our test environment we evaluate the
general functionality. The main problems are related
to packet processing/packet loss. In this first
approach we only monitor TCP-connections (HTTP
and FTP). In these connections we look for JPEGpictures, with the CST we can analyse these images
in case of using steganographic tools. Furthermore,
there are further programs that can embed in GIFs
(EzStego) [8] or bitmaps. Our approach is scalable
and can be extend to steganalysis algorithm that are
able detect messages in other image formats or even
other media types like audio. For example MP3-data
(MP3Stego) [18] and WAV-data (Stegowav) [19] are
used for a covert-communication and steganalysis
tools are under way to detect the hidden channels
here too, see [20]. An extension to further schemes
can be easily set up. In future we plan to monitor
connections in which sound files like WAVs or mp3
will be transmitted.
Open questions are for example: How to handle the
positive classified media data, how to protocol or
store the data, what is the impact and consequences
of positive detection and how to handle false
positives? What are useful re-actions on positive
detections? Is it possible to formulate a set of rules
with security policy languages? Is it possibly to
integrate the approach into IPS?
5. Acknowledgements
The information in this document is provided as is,
and no guarantee or warranty is given or implied that
the information is fit for any particular purpose. The
user thereof uses the information at its sole risk and
liability. The work described in this paper has been
supported in part by the European Commission
through the IST Programme under Contract IST2002-507932 ECRYPT.
6. References
[1] Stefan Katzenbeisser and Fabien A. P. Petitcolas,
Information Hiding Technics for Steganography and Digital
Watermarking, Artech House 2002.
[2] Andreas Westfeld and A. Pfitzmann, Attacks on
Steganographic Systems, 3rd International Workshop,
Lecture Notes in Computer Science, Springer Verlag Berlin
2000.
[3] Neil F. Johnson and Sushil Jajodia, Steganalysis of
Images Created Using Current Steganography Software,
Lecture Notes in Computer Science 1998.
[4] Andreas Westfeld, Steganography Software F5,
http://wwwrn.inf.tu-dresden.de/~westfeld/f5.html 2003.
[5] Jessica Fridrich and Miroslav Goljan and Dorin Hogea,
Steganalysis of JPEG Images: Breaking the F5 Algorithm,
5th Information Hiding Workshop 2002.
[6] Andreas Westfeld, F5 - Ein steganographischer
Algorithmus: Hohe Kapazitt trotz verbesserter Angriffe,
http://www.inf.tu-dresden.de/~aw4/publikationen.html
2001.
[7] Neil F. Johnson and Sushil Jajodia, Steganalysis of
Images Created Using Current Steganography Software,
Lecture Notes in Computer Science 1998.
[8] Romana Machado, Hide and recover encrypted data in
your GIF files with Steg, http://http://www.stego.com,
2003.
[9] Derek Upham, Jsteg, http://islab.oregonstate.edu/
documents/ftpsites/berkeley/jsteg, 2003.
[10] Nils Provos, Steganography Detection with Stegdetect,
http://www.outguess.org/detection.php, 2004.
[11] Ralf Spenneberg, Intrusion Detection fr LinuxServer, Markt+Technik Verlag 2003.
[12] Derek Atkins and Paul Buis and Chris Hare and Robert
Kelly, Internet Security Professional Reference, New
Riders Publishing 1997.
[13] Intrusion Detection Subgroup, Report on the NS/EP
Implications of Intrusion Detection Technology Research
Development 1997.
[14] Josef Helden and Stefan Karsch, Grundlagen
Forderungen und Marktbersicht fr Intrusion Detection
Systeme (IDS) und Intrusion Response Systeme (IRS)
1998.
[15] Brian Caswell and Marty Roesch,The Open Source
Network Intrusion Detection System, http://www.snort.org
2004.
[16] Internet Security Systems Inc. http://www.iss.net 2003.
[17] Cisco Systems, Network Security An Executive
Overview,http://www.cisco.com/warp/public/cc/so/neso/sqs
o/netsp_pl.pdf 2003.
[18] Petitcolas, Fabien, MP3Stego,
http://www.petitcolas.net/fabien/steganography/mp3steg
2004.
[19] StegoWav, http://www.jjtc.com/stegoarchive
/stego/softwaredos.html 2004.
[20] J. Fridrich, Feature-Based Steganalysis for JPEG
Images and its Implications for Future Design of
Steganographic Schemes, to appear in The 6th Information
Hiding Workshop, Toronto, CA, May 2335.
[21]DACH Security, Bestandsaufnahme, Konzepte,
Anwendungen, Perspektiven, 2004.
[22] Jana Dittmann; Stephan Klink; Andreas Lang; Martin
Steinebach:
Wasserzeichenuntersttzende
Firewalls:
Enterprise Security: Grundlagen,
Strategien, Anwendungen, Realisierungen; Patrick Horster
(Eds.) it Verlag fr Informationstechnik GmbH,
Hhenkirchen, pp. 246 257, 2002
Figure 2 Visual representation of the database.
Proceedings of the 30th EUROMICRO Conference (EUROMICRO04)
1089-6503/04 $ 20.00 IEEE
You might also like
- Privatization and Management Office v. Strategic Alliance Development CorporationDocument2 pagesPrivatization and Management Office v. Strategic Alliance Development CorporationJaypee Ortiz67% (3)
- Analysis and Design For Intrusion Detection System IDS Using Data Mining IEEE 2010Document4 pagesAnalysis and Design For Intrusion Detection System IDS Using Data Mining IEEE 2010fakeacc18No ratings yet
- Cloud 4unitDocument11 pagesCloud 4unitPriya PrakashNo ratings yet
- Network Intrusion Simulation Using OPNETDocument5 pagesNetwork Intrusion Simulation Using OPNETyzho100% (1)
- Apply Machine Learning Techniques To Detect Malicious Network Traffic in Cloud ComputingDocument24 pagesApply Machine Learning Techniques To Detect Malicious Network Traffic in Cloud ComputingMd.Mostafiz Ul IslamNo ratings yet
- Steganography and Data Loss Prevention An Overlooked RiskDocument14 pagesSteganography and Data Loss Prevention An Overlooked Riskyicesa macNo ratings yet
- Energy Efficient Hybrid Intrusion Detection System For Wireless Sensor NetworksDocument5 pagesEnergy Efficient Hybrid Intrusion Detection System For Wireless Sensor Networksram_rattleNo ratings yet
- Network Intrusion Detection SystemDocument46 pagesNetwork Intrusion Detection Systemsachin mohanNo ratings yet
- Sensors: A Deep Learning Ensemble For Network Anomaly and Cyber-Attack DetectionDocument20 pagesSensors: A Deep Learning Ensemble For Network Anomaly and Cyber-Attack Detectionmakawana janki100% (1)
- Nids STUDY PhaseDocument7 pagesNids STUDY Phaseyasir_yhNo ratings yet
- I Nternational Journal of Computational Engineering Research (Ijceronline - Com) Vol. 2 Issue. 7Document7 pagesI Nternational Journal of Computational Engineering Research (Ijceronline - Com) Vol. 2 Issue. 7International Journal of computational Engineering research (IJCER)No ratings yet
- Network Security: ARDUINO Yun Based IDSDocument5 pagesNetwork Security: ARDUINO Yun Based IDSInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- A New Technique For Wireless Sensor NetworkDocument8 pagesA New Technique For Wireless Sensor NetworkIJRASETPublicationsNo ratings yet
- Snort Alert AnalyseDocument12 pagesSnort Alert Analysepalev43287No ratings yet
- Jss Science and Technology University Department of Information Science and Engineering Computer Networks (Is610)Document8 pagesJss Science and Technology University Department of Information Science and Engineering Computer Networks (Is610)Vardhan ReddyNo ratings yet
- Network Behavior-Analysis Systems With The Use of Learning Set and Decision Rules Based On DistanceDocument12 pagesNetwork Behavior-Analysis Systems With The Use of Learning Set and Decision Rules Based On DistanceThanh Mon100% (1)
- Wendym,+04 VictorDocument24 pagesWendym,+04 VictorHeather WinNo ratings yet
- Manoj SRDocument82 pagesManoj SRMsNo ratings yet
- Rebellion 2K6: State Level Computer Science SymposiumDocument14 pagesRebellion 2K6: State Level Computer Science SymposiumgalipallidNo ratings yet
- IEEE Projects 2012-2013 Network SecurityDocument7 pagesIEEE Projects 2012-2013 Network Securitysathish20059No ratings yet
- Graph Drawing For Security Visualization: RT, Bernardo, Cpap @cs - Brown.eduDocument12 pagesGraph Drawing For Security Visualization: RT, Bernardo, Cpap @cs - Brown.eduhoaiannguyenNo ratings yet
- Machine Learning Algorithms For Spotting 6G Network Penetration For Different AttacksDocument5 pagesMachine Learning Algorithms For Spotting 6G Network Penetration For Different AttacksNabonita HalderNo ratings yet
- Approaches and Methods For Steganalysis - A Survey: IjarcceDocument6 pagesApproaches and Methods For Steganalysis - A Survey: IjarcceChethan ChethiNo ratings yet
- Network in Truss IonDocument11 pagesNetwork in Truss IonRam KumarNo ratings yet
- Towards Dynamic Self-Tuning For Intrusion Detection Systems: Sun-Il Kim, Nnamdi Nwanze and Jasen KintnerDocument8 pagesTowards Dynamic Self-Tuning For Intrusion Detection Systems: Sun-Il Kim, Nnamdi Nwanze and Jasen KintneryogendarNo ratings yet
- Crime Activity Detection Using Machine LearningDocument7 pagesCrime Activity Detection Using Machine LearningIJRASETPublicationsNo ratings yet
- Use Cases and Design of An Intelligent Intrusion Detection SystemBaltic Journal of Modern ComputingDocument21 pagesUse Cases and Design of An Intelligent Intrusion Detection SystemBaltic Journal of Modern Computingsoutien104No ratings yet
- Energy Efficient & Low Power Consuming Data Aggregation Method For Intrusion Detection in MANETDocument9 pagesEnergy Efficient & Low Power Consuming Data Aggregation Method For Intrusion Detection in MANETInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Neural Networks in Cyber Security: Issue 09, Volume 4 (September 2017)Document4 pagesNeural Networks in Cyber Security: Issue 09, Volume 4 (September 2017)Crazy MechonsNo ratings yet
- Intrusion Detection Using Geometrical StructureDocument7 pagesIntrusion Detection Using Geometrical StructureryutadragonslayerNo ratings yet
- A Novel Datamining Based Approach For Remote Intrusion DetectionDocument6 pagesA Novel Datamining Based Approach For Remote Intrusion Detectionsurendiran123No ratings yet
- An Integrated Victim-Based Approach Against IP Packet Flooding Denial of ServiceDocument11 pagesAn Integrated Victim-Based Approach Against IP Packet Flooding Denial of ServicepalashvermaNo ratings yet
- Efficient Attack Detection in Iot Devices Using Feature Engineering-Less Machine LearningDocument18 pagesEfficient Attack Detection in Iot Devices Using Feature Engineering-Less Machine LearningAnonymous Gl4IRRjzNNo ratings yet
- Forensic Analysis For Effective Combine Attack Management System Based On Cloud ComputingDocument8 pagesForensic Analysis For Effective Combine Attack Management System Based On Cloud ComputingInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Ijcet: International Journal of Computer Engineering & Technology (Ijcet)Document6 pagesIjcet: International Journal of Computer Engineering & Technology (Ijcet)IAEME PublicationNo ratings yet
- Network Monitoring and Analysis by Packet Sniffing MethodDocument3 pagesNetwork Monitoring and Analysis by Packet Sniffing MethodseventhsensegroupNo ratings yet
- MCKC: A Modified Cyber Kill Chain Model For Cognitive Apts Analysis Within Enterprise Multimedia NetworkDocument27 pagesMCKC: A Modified Cyber Kill Chain Model For Cognitive Apts Analysis Within Enterprise Multimedia NetworkPJ SANTOSNo ratings yet
- A Knowledge-Based Intrusion Detection Engine To Detect Attacks On Security ProtocolsDocument7 pagesA Knowledge-Based Intrusion Detection Engine To Detect Attacks On Security ProtocolstheijesNo ratings yet
- 1.1 MotivationDocument65 pages1.1 MotivationKalyan Reddy AnuguNo ratings yet
- RR1815514G Proposal - Internet of Things Intrusion and Wormhole Attack DetectionDocument6 pagesRR1815514G Proposal - Internet of Things Intrusion and Wormhole Attack DetectionTheophilus MaposaNo ratings yet
- Hybrid Intrusion Detection System AbstractDocument6 pagesHybrid Intrusion Detection System Abstractspeak2dasNo ratings yet
- ITA13 FinalDocument9 pagesITA13 FinalVarunKatyalNo ratings yet
- Novel High-Speed Reconfigurable FPGA Architectures For EMD-based Image SteganographyDocument30 pagesNovel High-Speed Reconfigurable FPGA Architectures For EMD-based Image Steganographyphuthuan0317No ratings yet
- Incremental Intrusion Detection System For Wireless Sensor NetworksDocument5 pagesIncremental Intrusion Detection System For Wireless Sensor NetworksInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Intrusion Detection System For CloudDocument8 pagesIntrusion Detection System For CloudInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- A User-Centric Machine LearningDocument11 pagesA User-Centric Machine LearningNaresh KanigiriNo ratings yet
- Art 22 Machine Learning Based DetectionDocument19 pagesArt 22 Machine Learning Based DetectionzhiyuyaNo ratings yet
- NIDS ReportDocument106 pagesNIDS ReportAbu ThalhathNo ratings yet
- Ntrusion D Etection S Ystem - Via F Uzzy Artmap in A Ddition With A Dvance S Emi S Upervised F Eature S ElectionDocument15 pagesNtrusion D Etection S Ystem - Via F Uzzy Artmap in A Ddition With A Dvance S Emi S Upervised F Eature S ElectionLewis TorresNo ratings yet
- School of Information Technology and Engineering: Intrusion Detection System Using Unsupervised ML AlgorithmsDocument6 pagesSchool of Information Technology and Engineering: Intrusion Detection System Using Unsupervised ML Algorithmshaggele haggeleNo ratings yet
- Towards Anomaly Detection in Smart Grids by Combining Complex Events Processing and SNMP ObjectsDocument6 pagesTowards Anomaly Detection in Smart Grids by Combining Complex Events Processing and SNMP ObjectsPedrito OrangeNo ratings yet
- IDS1Document14 pagesIDS1Akhil Jabbar MeerjaNo ratings yet
- Intrusion Detection Systems by Anamoly-Based Using Neural NetworkDocument6 pagesIntrusion Detection Systems by Anamoly-Based Using Neural NetworkInternational Organization of Scientific Research (IOSR)No ratings yet
- Ensemble Models For Intrusion Detection System ClassificationDocument15 pagesEnsemble Models For Intrusion Detection System ClassificationKurniabudi ZaimarNo ratings yet
- A Novel Evaluation Approach ToDocument13 pagesA Novel Evaluation Approach ToAIRCC - IJNSANo ratings yet
- Machine Learning Algorithms For Intrusion Detection in CybersecurityDocument9 pagesMachine Learning Algorithms For Intrusion Detection in CybersecurityIJRASETPublicationsNo ratings yet
- Intrusion Detection System For Imbalance Ratio Class Using Weighted XGBoost ClassifierDocument11 pagesIntrusion Detection System For Imbalance Ratio Class Using Weighted XGBoost ClassifierTELKOMNIKANo ratings yet
- Ids IN FUZZY LOGICDocument11 pagesIds IN FUZZY LOGICArunNo ratings yet
- Original 2Document58 pagesOriginal 2sandeep naikNo ratings yet
- Cyber Threat Detection SynopsisDocument14 pagesCyber Threat Detection SynopsisGopi KrishnaNo ratings yet
- Design and Implementation of A Secret Key Steganographic Micro-Architecture Employing FPGADocument6 pagesDesign and Implementation of A Secret Key Steganographic Micro-Architecture Employing FPGAproof14No ratings yet
- Wind Speed Model For Anantapur District, Western Andhra Pradesh, IndiaDocument7 pagesWind Speed Model For Anantapur District, Western Andhra Pradesh, Indiaproof14No ratings yet
- A Concept of Digital Picture Envelope For Internet CommunicationDocument7 pagesA Concept of Digital Picture Envelope For Internet Communicationproof14No ratings yet
- A Model of Anonymous Covert Mailing System Using Steganographic SchemeDocument5 pagesA Model of Anonymous Covert Mailing System Using Steganographic Schemeproof14No ratings yet
- Liofilchem SystemsDocument12 pagesLiofilchem SystemsDialife Medical Equipment and Supplies100% (1)
- Yajur Veda-Chapter-36Document18 pagesYajur Veda-Chapter-36Manurbhav86% (7)
- Assignment JavaDocument18 pagesAssignment Javadhruvtank06No ratings yet
- Gic Intervention Action Plan in Catch Up Friday ReadingDocument2 pagesGic Intervention Action Plan in Catch Up Friday ReadingCatherine FajardoNo ratings yet
- Present Perfect (1) (I Have Gone I Haven T Gone)Document4 pagesPresent Perfect (1) (I Have Gone I Haven T Gone)Sleyder Milla MillaNo ratings yet
- MCQs PPEDocument10 pagesMCQs PPEfrieda20093835100% (1)
- Bath Authority v. Aston Global - ComplaintDocument136 pagesBath Authority v. Aston Global - ComplaintSarah BursteinNo ratings yet
- ECB1 Tests Language Test 5ADocument2 pagesECB1 Tests Language Test 5AAlicja PodkowskaNo ratings yet
- Summary: Oedipus Rex by SophoclesDocument4 pagesSummary: Oedipus Rex by SophoclesGuilliane GallanoNo ratings yet
- Press Maintenance Troubleshooting AND "Pressroom Safety" ManualDocument45 pagesPress Maintenance Troubleshooting AND "Pressroom Safety" ManualArturo de la VegaNo ratings yet
- AssignmentDocument5 pagesAssignmentJC NicaveraNo ratings yet
- Yoga For The Modern AgeDocument22 pagesYoga For The Modern AgeSubhag SenNo ratings yet
- Bussiness Stats UNITDocument2 pagesBussiness Stats UNITsinghsaurabhh91No ratings yet
- Indian Contract Act, 1872Document112 pagesIndian Contract Act, 1872Achyuth BjNo ratings yet
- Super Food Ideas May 2017Document100 pagesSuper Food Ideas May 2017Francisco Bustos-GonzálezNo ratings yet
- DIC - Case Study (Blood 2)Document2 pagesDIC - Case Study (Blood 2)Aen BridgetteNo ratings yet
- 03.1 Implementing Users SecurityDocument89 pages03.1 Implementing Users SecurityJAN2909No ratings yet
- "CJT" Series Hydraulic Cylinders: SpecificationsDocument3 pages"CJT" Series Hydraulic Cylinders: SpecificationsWidodo Hadi PrabowoNo ratings yet
- Piping S Specificat Tion "AA1" ": CLA Ass: Ansi CS, R I 150# RFDocument4 pagesPiping S Specificat Tion "AA1" ": CLA Ass: Ansi CS, R I 150# RFJhonny Chugá MejíaNo ratings yet
- Consumer Buyer Behavior: Smartphone Industry BangladeshDocument11 pagesConsumer Buyer Behavior: Smartphone Industry BangladeshArminAhsanNo ratings yet
- History of Fashion - Indus VallyDocument3 pagesHistory of Fashion - Indus VallyShAiShahNo ratings yet
- AL - WATHBA PROJECT General - Risk - Assessment-OHSDocument27 pagesAL - WATHBA PROJECT General - Risk - Assessment-OHSMuhammad YounasNo ratings yet
- BIO270 Lab Work BookDocument7 pagesBIO270 Lab Work Booknur aqilah syafiqahNo ratings yet
- BAS AssignmentDocument1 pageBAS AssignmentElyzah EstradaNo ratings yet
- Lego Batman 3 CheatcodeDocument21 pagesLego Batman 3 CheatcodeAbir DasNo ratings yet
- 04 Mini-X-Iii and Vari-X-IiiDocument1 page04 Mini-X-Iii and Vari-X-Iiijoana ramirezNo ratings yet
- Group 2 MM Project ReportDocument31 pagesGroup 2 MM Project ReportAnkush AgarwalNo ratings yet
- Selaquischool 160904071214Document14 pagesSelaquischool 160904071214Murtaza Vanak100% (1)