Professional Documents
Culture Documents
01 Unit1
01 Unit1
Uploaded by
dhirkpCopyright:
Available Formats
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5834)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (350)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (824)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (405)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Cybrary CSSLP SlidesDocument246 pagesCybrary CSSLP Slidesineba100% (1)
- DA-100 - Analyzing Data With Power BIDocument7 pagesDA-100 - Analyzing Data With Power BInareshbawankarNo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Dir SellingDocument6 pagesDir SellingdhirkpNo ratings yet
- Giit Class Test - Ii: InstructionDocument6 pagesGiit Class Test - Ii: InstructiondhirkpNo ratings yet
- Remedial Coaching Class Time Table August 2014Document1 pageRemedial Coaching Class Time Table August 2014dhirkpNo ratings yet
- Su 2 Exam Prep QuestionsDocument7 pagesSu 2 Exam Prep QuestionsdhirkpNo ratings yet
- Page0001Document1 pagePage0001dhirkpNo ratings yet
- Format - A For Publication of Postpaid Tariff PlansDocument1 pageFormat - A For Publication of Postpaid Tariff PlansdhirkpNo ratings yet
- Ques W10 Math 22dec 2014Document1 pageQues W10 Math 22dec 2014dhirkpNo ratings yet
- Write Down The Time in Words: "Print Your Own Worksheets atDocument1 pageWrite Down The Time in Words: "Print Your Own Worksheets atdhirkpNo ratings yet
- Electronics Digital Circuit Addition Computers Arithmetic Logic UnitDocument1 pageElectronics Digital Circuit Addition Computers Arithmetic Logic UnitdhirkpNo ratings yet
- Unit - 6 Verification and Valuation of Assets and LiabilitiesDocument1 pageUnit - 6 Verification and Valuation of Assets and LiabilitiesdhirkpNo ratings yet
- Unit - 4 Auditing TechniquesDocument1 pageUnit - 4 Auditing TechniquesdhirkpNo ratings yet
- Unit - 8 Cost Audit: Financial Systems and Auditing Unit - 8Document1 pageUnit - 8 Cost Audit: Financial Systems and Auditing Unit - 8dhirkpNo ratings yet
- Unit - 7 Management Audit: Financial Systems and Auditing Unit - 7Document1 pageUnit - 7 Management Audit: Financial Systems and Auditing Unit - 7dhirkpNo ratings yet
- Annexure: Financial Systems and AuditingDocument1 pageAnnexure: Financial Systems and AuditingdhirkpNo ratings yet
- Financial Auditing Another MCQDocument7 pagesFinancial Auditing Another MCQdhirkpNo ratings yet
- Meet Our New MBADocument1 pageMeet Our New MBAdhirkpNo ratings yet
- Sample Answer SheetDocument1 pageSample Answer SheetdhirkpNo ratings yet
- Kolhan University, Chaibasa: Application Form For Contractual AppointmentDocument3 pagesKolhan University, Chaibasa: Application Form For Contractual AppointmentdhirkpNo ratings yet
- Vidyadeep Scholarship Terms - Fall DriveDocument4 pagesVidyadeep Scholarship Terms - Fall DrivedhirkpNo ratings yet
- 442A-MA Mathematics (Master of Arts in Mathematics)Document20 pages442A-MA Mathematics (Master of Arts in Mathematics)dhirkpNo ratings yet
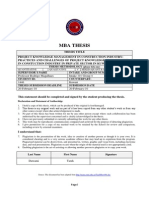
- Mba Thesis: Professor Rodrigo Magalhaes Intake 10 / Group 4 1446 Kuwait 20-February-10 20-February-10Document2 pagesMba Thesis: Professor Rodrigo Magalhaes Intake 10 / Group 4 1446 Kuwait 20-February-10 20-February-10dhirkpNo ratings yet
- MB0052 SLM Unit 02Document28 pagesMB0052 SLM Unit 02mrahul29_400215311No ratings yet
- Spirofy 4 Page Brochure - 230913 - 102119Document4 pagesSpirofy 4 Page Brochure - 230913 - 102119Amit KaradNo ratings yet
- Transaction ProcessingDocument9 pagesTransaction ProcessingJenaro WachiraNo ratings yet
- Computer TRICKS First PartDocument10 pagesComputer TRICKS First PartSantu NandiNo ratings yet
- Tef Calculator Walk ThroughDocument17 pagesTef Calculator Walk ThroughCapitus L. L. PNo ratings yet
- R GameDocument79 pagesR Gamearnav mauryaNo ratings yet
- 8 Tips For An Awesome PowerPoint PresentationDocument48 pages8 Tips For An Awesome PowerPoint PresentationTủ LạnhNo ratings yet
- Elevens Gaming HubDocument66 pagesElevens Gaming HubOrange MindedNo ratings yet
- Aster Flaash PDFDocument14 pagesAster Flaash PDFJavier Saul Salgado ParejaNo ratings yet
- 123Document2 pages123rajuNo ratings yet
- Resulticks Introduction v2Document8 pagesResulticks Introduction v2Atul SinghNo ratings yet
- Prac 8 Resistance and Heat - Using Nichrome WireDocument3 pagesPrac 8 Resistance and Heat - Using Nichrome Wireapi-357642569No ratings yet
- Introduction To Gis and Arcgis: How A Gis WorksDocument37 pagesIntroduction To Gis and Arcgis: How A Gis WorksTäð Œvê MîðNo ratings yet
- Application of SPSS in Research WritingDocument77 pagesApplication of SPSS in Research WritingKaren Joy SabladaNo ratings yet
- Updated ResumeDocument3 pagesUpdated Resumeapi-3742929No ratings yet
- Pyserial PDFDocument63 pagesPyserial PDFJayesh ShawNo ratings yet
- Editar Menu Contextual OperaDocument7 pagesEditar Menu Contextual OperaPedro José Suárez TorrealbaNo ratings yet
- Michael Kors MKT 5089 - Set-Up & InstructionsDocument21 pagesMichael Kors MKT 5089 - Set-Up & InstructionsmkorsNo ratings yet
- Lab Activitiy 3 - For ESDocument8 pagesLab Activitiy 3 - For ESHiếu ShidoNo ratings yet
- Four-Quadrant: Dynamometer/Power Supply MODEL 8960Document16 pagesFour-Quadrant: Dynamometer/Power Supply MODEL 8960Jose Angel Puente PuenteNo ratings yet
- Dv300 Service Manual Eng 120214 1Document68 pagesDv300 Service Manual Eng 120214 1rocklando777No ratings yet
- Google Strategy in 2013 - Strategic Management CaseDocument24 pagesGoogle Strategy in 2013 - Strategic Management CaseRizkySeptiandyNo ratings yet
- Sesi 15 - FinAudit - IT Audit Integration & Security MGT Ver 1Document48 pagesSesi 15 - FinAudit - IT Audit Integration & Security MGT Ver 1keishaNo ratings yet
- 2 Weeks Data Science Using Python: Days TopicsDocument2 pages2 Weeks Data Science Using Python: Days TopicsKiaraNo ratings yet
- Enerlin'X IFE Ethernet Interface For One Circuit Breaker Used GuideDocument96 pagesEnerlin'X IFE Ethernet Interface For One Circuit Breaker Used Guidelorentz franklinNo ratings yet
- Tic Tac Toe GameDocument27 pagesTic Tac Toe GameVikas KumarNo ratings yet
- Bio ChipDocument16 pagesBio ChipAnil KumarNo ratings yet
- Linksys srw208Document86 pagesLinksys srw208Ivan Ernesto MillaNo ratings yet
- 1 © Netskills Quality Internet Training, University of NewcastleDocument14 pages1 © Netskills Quality Internet Training, University of Newcastleramzi esprimsNo ratings yet
01 Unit1
01 Unit1
Uploaded by
dhirkpOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
01 Unit1
01 Unit1
Uploaded by
dhirkpCopyright:
Available Formats
Website Design
Unit 1
Unit 1
Introduction to Internet
Structure:
1.1
Introduction
Objectives
1.2
What is Internet?
Definition
Internet from practical and technical angle
Who owns and cares for the Internet?
What is TCP/IP?
Introduction to RFC
How Internet Works?
Internet Applications
1.3
Concepts of Server
Client Server Model
Servers
1.4
Getting Connected
Different Types of Connections
Requirements for Connections
1.5
Internet Service Providers
1.6
Address in Internet
The Domain Name System and DNS Servers
IP Addresses
1.6
Resource Addressing
URL (Uniform Resource Locator)
URLs and HOST Names
URLs and Port Numbers
Pathnames
1.7
Email
Email Basics
Mail protocols
How to Access the Mail System
1.8
Summary
1.9
Terminal Questions
1.10 Answers
Sikkim Manipal University
Page No. 1
Website Design
Unit 1
1.1 Introduction
We have covered the basic concepts of internet and website in the previous
semester. In addition to it we are going to cover few advance concepts in
this unit.
In this unit, we would begin with an introduction to the internet, then discuss
about the client-server model for communication and different types of
connections. We would also discuss about Internet Service Providers and
addressing in the internet. At the end we will explain about the Resource
Addressing and Electronic mail.
Objectives
After studying this unit, you should be able to:
explain the meaning, evolution, working and application of internet
discuss the client server model and various types of internet
describe how to get connected to internet
use IP addressing scheme
explain the concepts of resource addressing
describe the E-mail basics, mail protocol & methods of accessing mail
system
1.2 What is Internet?
This section covers the definition, meaning and practical & technical angle
of internet.
1.2.1 Definition
There is no single, generally agreed upon definition for internet because the
internet is a different thing to different people. We can give the following few
expressions in this context.
The Internet links are computer networks all over the world so that users
can share resources and communicate with each other.
It is the name for a vast, worldwide system consisting of people,
information and computers
It is a network of networks that spans the globe
It is an ocean of information
It is a set of computers communicating over fiber optics, phone lines,
satellite links and other media
Sikkim Manipal University
Page No. 2
Website Design
Unit 1
It is a gold mine of professionals from all fields sharing information about
their work
It is a world wide interconnected system of thousands of computer
networks, each network in turn linking thousands of computers together
The Internet is also what we call a distributed system; there is no central
archive.
The Internet thrives and develops as its many users find new ways to
create, display and retrieve the information that constitutes the Internet.
1.2.2 Internet from practical and technical angle
From the practical angle
Internet is a vast collection of globally available information which can be
accessed electronically information which is of practical use for business,
research, study and technical purposes. It is a means for electronic
commerce marketing, buying, services, economic and financial data
research. It is a collection of hundreds of libraries and archives that will open
to your fingertips. It is also a vast store of information relating to your
hobbies, travel, health, entertainment, games, software, etc.
Today the information can be in the form of Text, Images, Animation,
Sound, Video etc tomorrow it would probably be in the form of smell, touch,
taste or some energized form. If information can be put on computers, that
mean it can be digitized, it can be made available on the internet. The only
catch is, how fast? Even the future may not be able to tell.
From the Technical Angle
To be technically correct, we can say that the internet is an ever growing
wide area network of millions of computers and computer networks across
the globe, which can exchange information through standard rules
(protocols). Each computer has a unique address. Information is divided into
packets which may travel through different paths to the destination address
where it is recombined into its original form.
1.2.3 Who owns and cares for the Internet?
Owning of internet
No one owns the Internet. Any single person, corporation, university or
government does not fund it. Internet has been described as the cooperative
anarchy. Every person who makes a connection, every group whose Local
Area Network (LAN) becomes connected, owns a slice of the Internet.
Sikkim Manipal University
Page No. 3
Website Design
Unit 1
You can compare Internet model with phone companies and the electric
companies. For example, there is phone service in almost every part of the
country. With a phone company, each person who wants telephone service
contacts a local service provider. The service provides a hook-up from the
residence or office to the service network.
The person wanting service actually provides the telephone instrument and
the connections within the residence or office. As long as the calls you want
to place are restricted to your local area, you do not need anything else.
However, if you want to place a call to someone in another area, you need
to purchase services from a long-distance service provider. The local area
provider supplies the connection from the local network into the longdistance network. This model allows you to connect to the telephone almost
anywhere in the world. Moving among networks of computers works much
the same way (which is not surprising since the telephone networks that
is, the physical cables are used to connect the computers).
Who cares for Internet?
Many people care about the internet. All the people who use it, even if only
to send a note to someone on some other network that is connected into the
Internet, care about it. Someone or some enterprise owns each computer
connected. The owner of the connected equipment therefore owns a piece
of the internet. The telephone companies own the pieces that carry the
information packets. The service providers own the packet routing
equipment. So, while no one person or entity owns the internet, all who use
it or supply materials for it play a part in its existence.
Since communication between networks cannot happen without
co-operation, there are committees and groups working hard all the time to
ensure smooth functioning. Some issues related to providing standards and
identification of computers on the NET are to be cared by somebody. Some
groups have thus been formed who look after primarily about the
commonality part of internet. This body is called IAB (Internet Architecture
Board), earlier called Internet Board as named by ARPA. There are two
main wings to this board:
IETF (Internet Engineering Task Force)
IRTF (Internet Research Task Force)
Sikkim Manipal University
Page No. 4
Website Design
Unit 1
IETF does a documentation of the internet known as RFC (Request For
Comments), named so because it is a set of open-ended documents always
available to public for their comments and thus the standards keep
continuously evolving.
Apart from maintaining protocols and norms/standards, another important
function of commonality is assigning unique names and addresses to
computers connected on the Net. This function is performed by InterNIC
(Internet Network Information Center) which is a group of three
organizations.
1. General Atomics, CA : Provides Information Services
2. AT & T., NY
: Provides Directory and Database Services
3. Network Solutions, VA : Provides Registration Service
The services of InterNIC group are available on the Internet itself. Each
individually connected network maintains its own user policies and
procedures as to who can be connected, what kind of traffic the network will
carry, and so on.
1.2.4 What is TCP/IP?
As we have already discussed, the Internet is built on a collection of
networks covering the world, and obviously, these networks contain many
different types of computers. To hold the whole thing together we have
something called TCP/IP (Transmission Control Protocol/Internet Protocol).
Protocols are the rules that all networks use to understand each other. For
example, there is a protocol describing exactly what format should be used
for sending mail message. All internet mail programs follow this protocol
when they prepare a message for delivery. Collectively, more than 100
protocols are given the common name, called TCP/IP, used to organize
computers and communication devices into a network. It is glue holding it all
together.
Information within the Internet is not transmitted as a constant stream from
host to host; rather data is broken into small packages called segments. To
divide the data (or message) into number of segments is the task of TCP.
TCP marks each segment with a sequence number, the address of the
recipient, the address of the sender, and it also inserts some error control
information.
Sikkim Manipal University
Page No. 5
Website Design
Unit 1
The segments are then sent over the network, where it is the job of the IP to
transport them correctly to the remote host. TCP of the other end receives
the segments and checks for errors. If an error has occurred, TCP can ask
for that particular block to be resent. Once all the segments are received
correctly, TCP will reconstruct the original message using the sequence
number. Therefore, the job of TCP is to manage the flow and ensure the
data is correct, and for IP the job is to route the raw data the packets from
one place to another.
The technical answer of, What is TCP/IP, is: TCP/IP is a large family of
protocols used to organize computers and communication devices into a
network. The two important protocols are TCP and IP. IP transmits the data
from place to place, while TCP makes sure it all works correctly.
1.2.5 Introduction to RFC
The internet is based on a large number of protocols and conventions. Each
such protocol is explained in the technical publication called a request for
comment or RFC. An RFC is usually a detailed technical explanation of how
something is supposed to work, not an invitation for people to send in
comments. Each RFC is given a number and is made available to anyone
who wants to read it. In this manner, the technical information that supports
the internet is distributed around the world in an organized, reliable manner.
Programmers and engineers who want to design products to work with the
internet protocols can download the RFCs and use them as reference
material. This ensures that everyone is using the same specifications and
that all the internet programs are designed to follow the same set of
standards.
1.2.6 How Internet Works?
In this section, we are going to cover the concepts of Internet, sending and
receiving messages.
Working of Internet
The primary objective of any network is to exchange information between
different locations. The rules for this exchange are called Protocols. The
protocol on Internet is TCP/IP (Transmission Control Protocol/Internet
Protocol) which is actually a name for a set of many rules framed to connect
computers in a wide area network, a network which is established between
computers across cities or countries.
Sikkim Manipal University
Page No. 6
Website Design
Unit 1
Let us take a practical example of simply exchanging a message between
two persons, one at Lucknow and another at Mumbai.
Surya has an Internet account at Lucknow as Surya@lwl.vsnl.net.in
Rishaba has an Internet account at Mumbai as Rishaba@bmOl.
vsnl.net.in
When Surya wants to send a message to Rishaba at Mumbai, he dials
from his telephone to his local service provider, types out his message
and types out the address of the recipient.
Suryas message is then broken into packets, which is an easy and
reliable communicable entity.
These packets are then broadcast to various connected links along with
the destination address, say o Delhi and Kanpur. At these sites also,
there is packet forwarding facilities available based on address available
and after a while, all packets ultimately reach the destination address
that is Mumbai.
At Mumbai, all packets marked for a particular address
Rishaba@bmOl.vsnl.net.in and particular message number are
(automatically generated) are reassembled and then posted in the box
that Rishaba is supposed to access regularly.
The above example cites a case of store and forward type of message
transfer. However the on-line transfer also occurs in the same way,
provided machines at both the ends are switched on and set to
transmit/receive internet traffic.
Sending and Receiving messages
How the messages are sent and received across a network? Suppose I
send a message. It could be a simple E-mail saying Hi to tell you I am on
the network. On the other hand, it could be a file, like the text of this chapter.
Now I have to tell the system the address of your computer. It is generally
your name. Therefore, what I do is put this message in an envelope super
scribing your name on it. The actual operation is not much complicated
either. It will be relevant here to understand the mechanisms adopted in
telephones and cable networks transmitting satellite channel, to your home.
Nevertheless, keep in mind that the way communication takes place
between computers is different from both these cases.
Sikkim Manipal University
Page No. 7
Website Design
Unit 1
When your phone is off the hook, your line is engaged and you cannot
receive another call. However, your cable operator can beam so many
channels and you can surf them at will. Telephones are circuit switched. In
simple terms, it means that when you dial a number it goes to your nearest
exchange, which routes it to the nearest exchange of the called number,
and the ell rings at the end. The moment the receiver lifts his phone off the
hook, a circuit between you and him is established. This is a dedicated
circuit. The whole mechanism is called circuit switching.
Your cable operator, on the
because each channel has a
bandwidth of the cable, many
road with neatly defined lanes,
light commercial vehicles and
vehicles and you have it!
other hand, can send multiple channels
different frequency and depending on the
channels can be beamed. Imagine a wide
one for two wheelers, one for cars, one for
so on. Imagine frequency as the type of
In case of computer-to-computer communication, you cannot afford to have
circuit switching, and you cannot assign different frequencies to each
computer. The computer networks are packet switched. The different
stations send discrete blocks of data to each other. You can think of these
blocks of data as corresponding to some piece of a file, a piece of e-mail, or
an image.
The message is broken into pieces called packets. The time too is divided
and each computer gets a quota of time to send packets. Suppose many
stations want to communicate at the same time, they have to share the
network resources, especially the wires. This can be achieved through
multiplexing techniques.
Each packet has actual contents surrounded by a header and a trailer. The
packet header has information about its destination. The NIC (Network
Interface Card) transmits the packet on the network. All computers passed
by this packet get to see it but ignore it after seeing the header. The NIC at
the intended receiver copies the packet. But does it copy each packet
separately? Yes. The information at the two ends of the packets helps these
to be put together.
Sikkim Manipal University
Page No. 8
Website Design
Unit 1
1.2.7 Internet Applications
Internet is an important tool for practically everybody. The applications are
endless. Whatever information is required, it is ether already available on
the internet or it is soon going to be available. Here are some interesting
application areas:
Electronic mail, which was until recently considered only an internal
mechanism, is quickly becoming the most widely used application on
Internet. The most common of the communication methods used by the
people on the Internet is the private letter, written by one individual to
another (on any subject and in any language), and sent between any two
connected Internet sites or through an Internet e-mail gateway to or from a
service which provides an Internet gateway.
The ability to exchange visual information in readable and reusable formats
such as charts, figures, tables, images, databases, software code opens
up possibilities for collaboration at the global as well as local levels. With the
trend specialization, the ability not only to communicate but also to actually
work with colleagues in the same field scattered all over the world makes
long distance collaboration feasible.
The resources for on-line research are multiplying at an astounding rate.
Searchable databases library holdings, alerting services, pre-prints, and
other information systems are all changing the way research is done. Library
shelves are overflowing with journals and proceedings and with acquisitions
budgets receiving deep cuts, a likely scenario for the future is one in which
libraries achieve electronically, share holdings and become information
clearing houses instead of closets.
Another very important application of internet is Multimedia. Live music
concerts, radio broadcasts, live or recorded television shows, interactive
audio and web phone, and video conferencing are no more a dream on
Internet, even for a desktop PC user.
Internet provides a variety of information to everybody ranging from
entertainment to serious business application to areas of daily life such as:
Magazines and newspapers
Household shopping items
Ordering novelties from anywhere in the world
Sikkim Manipal University
Page No. 9
Website Design
Unit 1
Radio and TV broadcast schedules and sometimes the broadcast itself
Tour and travel plan guides and bookings
Health consultation
Tips for doing various things
Talking to friends and relatives in any part of the globe
Games of various kinds
Language interpreter
On-line education course material, examination conduction, advertising
on popular information sites, making payments on the net and getting an
item, Internet Banking.
Self-assessment questions
1. RFC stands for __________.
2. Internet is a network of ____________.
1.3 Concepts of Server
In this section, we are going to discuss the concepts of client server models,
mail servers and FTP servers.
1.3.1 Client Server Model
Well, some computers are more equal than others. There are more powerful
computers (not necessarily bigger) called servers. Actually they are like our
public servants, administrators to the core. These servers are connected to
other dependent (but not in all respects) computers called client, hence the
client-server model. The two are connected either through physical links
(wires, optical fibers, etc) or through microwaves using satellites or
microwave towers. When you have many computers talking and sending
and receiving an infinite number of signals traveling through these media,
there have to be traffic snarls. So there are devices to take care of these.
More detailed explanation for server and client is given below:
Server:
Many of the host computers on the Internet offer services to other
computers on the Internet. For example, your ISP probably has a host
computer that handles your incoming and outgoing mail. Computers that
provide services for other computers to use are called servers. The software
run by server computers to provide services is called server software. A
server usually runs n a computer that is connected directly to network and
Sikkim Manipal University
Page No. 10
Website Design
Unit 1
keeps running till any client login is expected. The size of that network is not
important to the client/server concept it could be a small local area
network or the global Internet. The server is designed to interact with client
programs
Client:
Conversely, many of the computers on the Internet use servers to get
information. For example, when your computer dials into an Internet
account, your e-mail program downloads your incoming messages from
your ISPs mail server.
Programs that servers for services are called clients. Your e-mail program is
more properly called an e-mail client. A client program is designed for a
particular computing platform (for example, UNIX, Macintosh, Windows) to
take advantage of the strengths of the platform. It uses environmental
elements just like the ones used in word processing or a spreadsheet, or
even in playing a computer game.
Using the familiar computer environment, the client may help you locate
servers of interest, send a query, process the query results, and display
them using familiar tools. Popular client/server software include WinGopher,
Mosaic, World Wide Web software, Netscape Navigator and Novell Netware
file server software.
The client/server model has become one of the central ideas of network
computing. Most business applications being written today use the
client/server model.
1.3.2 Servers
Mail Servers
The mail servers handle incoming and outgoing mail. Specifically, Post
Office Protocol (POP) servers (or POP3 servers) store incoming mail, while
Simple Mail Transfer Protocol (SMTP) Servers relay outgoing mail. Mail
clients get incoming message from, and send outgoing message to a mail
server, and enable you to read, write, save and print messages, store web
pages and transmit them in response to requests from web clients, which
are usually called browsers.
Sikkim Manipal University
Page No. 11
Website Design
Unit 1
FTP Servers
Stores files that you can transfer to or from your computer if you have an
FTP client
News Servers
Stores Usenet newsgroup articles that you can read and send if you have a
news client or newsreader.
IRC servers
Act as a switchboard for Internet based on-line chats. To participate, you
use an IRC client.
Self-assessment questions
3. Many of the host computers on the Internet offer services to other
computers on the Internet. (true/false)
4. SMTP stands for ___________.
1.4 Getting Connected
Since Internet is a composite network of more than thousands of discrete
networks, each having its own rules and procedures, there could be many
different ways by which you can connect to the Internet. To use the Internet
you need three things:
1. A Computer
2. Client programs to run on your computer (one client for each type of
service you want to use).
3. A way to connect your computer to the Net so your clients can service
your request.
1.4.1 Different Types of Connections
To start with, we need to go over the different types of Internet connections.
There are essentially three different types of connections for accessing the
services and resources of the Internet:
Dialup Connections
ISDN, ADSL, and Leased Line Connections
Satellite Connections
Dialup Connections
To access the Internet via a phone line, the concept is: Connect your
computer to the telephone system using either a regular phone line (with a
Sikkim Manipal University
Page No. 12
Website Design
Unit 1
modem) or an ISDN line (which requires special equipment). To start work,
you run a communication program to dial the phone and establish a
connection with a remote Internet host. Once the connection is established,
you log in to the server by typing your user name and password. At this
point, there are three possible types of dial-up connections:
a) Shell account access
b) TCP/IP account access
c) Dial-up or on-demand TCP/IP link through your LAN
a) Conventional Dial-up Shell Account: With this type of account, you
actually do your work on the remote computer. You establish an
interactive session wit another computer which is an Internet host. Your
desktop assumes the role of an ASCII terminal. With shell access, your
providers computer is considered a part of the Internet, but your
computer is not. The only program that runs on your computer is the
terminal emulator. When you connect to your provider, you type
commands to its system, which tell it what functions you want to do. The
program on your providers computer that receives and acts on the
commands is known as a shell. The shell and the programs it runs for
you send back to your computer some text that is displayed on the
screen. A terminal emulator only supports a text-based interface, not a
graphical interface. You are usually limited to running one client at a
time
b) Protocol dial-up (TCP/IP Account): A protocol dialup account lets your
computer behave like it is connected directly to another computer on the
Internet when it is really connected over a phone line whenever you
dialup and it enables you to run software, such as a graphical Web
browser like Microsoft Internet Explorer or Netscape Navigator, that
functions in your computers native environment instead of forcing you to
deal with plain text programs like the text only browser Lynx and UNIX.
This means when you have a protocol dialup (TCP/IP) account, during
the time you are connected your computer is a full fledged Internet host.
The client programs you use as many clients as you want at the same
time. For example, you could start four programs a web client, a
gopher client, a mail client, and switch back and forth from one to the
other. This type of connection is also known as TCP/IP type of account
and it uses the TCP/IP protocol to perform data transfer on the Internet.
Sikkim Manipal University
Page No. 13
Website Design
Unit 1
PPP and SLIP: The family of Internet protocols is called TCP/IP. The
connection protocol with ISPs server is known as PPP (Point to Point
Protocol), which is used in Indian context, although there are other
connection types such as SLIP or CSLIP which are available from other
Internet Service Providers in the world. But to your satisfaction you can
be sure that PPP is the most recent and advanced connection protocol.
The job of IP is to move the raw data from one place to another. Thus,
the protocol developed to support TCP/IP over a serial cable was called
SERIAL LINE IP or SLIP. SLIP dates back to the early 1980s and was
designed to be a simple, but not very powerful method of connecting two
IP devices over a serial cable. PPP is more powerful , more dependable,
more flexible, and is a lot easier to configure when you need to get it up
and running on a new system.
c) Dial-Up or On-Demand TCP/IP link through your LAN: A dial-up link
from your LAN is the intermediate step between individual dial-up and a
dedicated high speed link. It is therefore somewhat like dial-up and
somewhat like having a direct link. The main difference between this
type of connection and the one to your individual computer is that the
TCP/IP software runs on the LAN server, and your connection is to the
server. A TCP/IP connection through a LAN, either on a dial-up
connection or a direct connection, is the most common type of IP
connection, much more common than a personal dial-up IP connection.
ISDN, ADSL and Leased Line Connections: An alternative to a regular
phone line is ISDN (Integrated Services Digital Network) and Asymmetric
Digital Subscriber Line (ADSL) a type of telephone service. ISDN and
ADSL allow the user to connect to another computer at a speed which is
much faster than even the fastest modem because it is digital. Thus, if you
are using a phone line connect your computer to the Internet, you are better
off with an ISDN or ADSL (not all phone companies offer them) connection
because it is digital and it is a lot faster. These services can be run as fast
as 128 kbps.
ISDN or ADSL services are a boon for corporates that have multiple users
who need simultaneous Internet access. However, it is still a medium that
very few Internet users have tried out in India. Primary reasons for this being
delayed implementation by MTNL (Mahanagar Telephone Nigam Ltd.) and
Sikkim Manipal University
Page No. 14
Website Design
Unit 1
relatively higher costs. Mantraon-line is the first private ISP to offer the
same.
A dedicated link (or leased line) is a permanent connection over a telephone
line between a modem pointer to another modem pointer. A router is a
specialized computer that reads the address of each TCP/IP packet and
sends the packet to its destination. At higher speeds (56 kbps and above),
routers are used. With a dedicated link, your personal computer or LAN is
connected to the Internet at all times (compare it with hotlines, in which you
just pick the phone and start conversation, no dialing, no engage problem,
etc.). This type of connection is the most costly connection because it is
private (nobody else can share) to a persons computer or organization.
Leased lines come in various speeds, including T1 (1.5 Mbps, or enough for
24 voice channels) and 13 (44 Mbps, or enough for 672 voice channels). If
you do not need quite that much speed, you can ask for fractional T1 (half
or a quarter of a T1 line). You also need to connect your ISP for a leased
line account, which costs more than a dial-up account.
ISDN Advantages: To the subscriber, however, the most interesting
advantage perhaps is that via ISDN the entire services can be used with
one phone number only. One line is sufficient for telephone, telescopy,
video conference, or data transmission. A special protocol is responsible for
the fact that each incoming call will be directed to the right terminal. Thanks
to the Multiple Subscriber Number (MSN), it is now even possible to dial
each device by a central or PBX from the outside, without establishing a
connection prior to this.
1.4.2 Requirements for Connections
This section deals with shell account, TCP/IP account, TCP/IP software and
Web Browser.
For Shell Account
If you have a shell account type of access, what you all need is to become a
terminal on the computer of your ISP, thus the minimum possible PC
configuration with a VT-1 00 or equivalent type of terminal emulation
software can server your purpose well. In fact you may have a simple dumb
terminal to access such an account. The terminal emulation software on PC
is also widely available such as PROCOMM, etc. Please choose emulation
software which has KERMIT and ZMODEM file download capability. A
Sikkim Manipal University
Page No. 15
Website Design
Unit 1
modem with error correction capabilities 9.6 kbps or better, and telephone
line with capability to dial service provider Local/STD are also required.
For TCP/IP Account
It is the power of software available for TCP/IP account which has made
Internet so popular these days. It is highly desirable that you have a GUI
operating system such as Windows on your desktop, if you are a TCP/IP
account holder. Typically, you would require a TCP/IP connection
establishing software and a Web-Browser to access this type of account. A
modem which best suits your pocket and is fastest to its class is the right
choice. Typically a 28.8 kbps modem is found to perform best with Indian
ISPs.
TCP/IP Software
Such software is now bundled with new operating systems such as which
are also called TCP/IP sockets. If you do not have it along with your OS you
can have third party socket software such as Trumpet Winsock. It is
important to run this software to get connected to your ISP before you can
do the browsing part.
Web Browser
Web browsers are the Client software (your machine is a client to ISPs
server) which has various graphics capabilities to access the information
from the Internet. Modem Web Browsers are capable of browsing WWW,
Gopher sites, FTP sites and also provide facilities for e-mail. Initially NCSAs
web browser Mosaic hit the market which actually made the browsing
popular. Now web browsers from Netscape and from Microsoft are the
users choice. You can get hold of any such browser and start browsing the
Net.
Self Assessment questions
5) There are three types of dial-up connection are available. (true/false)
6) An alternative to a regular phone is ISDN. (true/false)
1.5 Internet Service Providers
An Internet Service Provider (ISP) is an organization or business offering
public access to the Internet. It is your gateway, to the Net. You have to
subscribe to a provider your Internet connection. You use your computer
and modem to access the providers system and the provider handles the
Sikkim Manipal University
Page No. 16
Website Design
Unit 1
rest of the details of connecting you to the Internet. There are many types of
Internet providers. You can, for instance, choose one of big commercial
online service providers. The primary business of an ISP is hooking people
to the Internet by giving an Internet account to subscribers, and providing
them with two different kinds of access: shell access and SLP/PPP access.
Most ISPs offer both kinds of access, some offer both with a single account
and others require that you choose one or the other. Once you register, your
provider will give you a user name (called a user id password, and a phone
number to dial). To establish the Internet connection, you have your
communications program dial the number. You then log in using your
particular user ID and password. At present it is VSNL (Videsh Sanchar
Nigam Limited) which is dominating the Internet scene in India through its
GIAS (Gateway Internet Access Service). The other service provides in
India are MTNL (Mahanagar Telephone Nigam Limited), Mantraon-line and
Satyam on-lie. Due to the new options in BSNL where the user need to
register from the telephone number and no separate account, the number of
users has increased. In this case what ever the usage of the person the
individual has to pay.
Choosing an ISP
The privatization of Internet Service Providers (ISPs) is set to give a further
fillip to the Internet boom. Central to the success of any service is the price
criterion. You will be amazed to find out how a service offered at a premium
could in effect be cheaper, considering the add-on facilities that are offered
along with the core service. Do not forget that apart from the Internet
connection, the ISP gives you an international contact address, that is, your
e-mail address. It is because of this e-mail address that you must be
discerning while choosing your ISP. The e-mail address provided by the ISP
would be all over your business and it will not be easy for you to change
your service provider if you wish to change your address. You will have to
live with the ISP as well as the e-mail address.
User ID Telephone Ratio: The first thing you must keep in mind while
zeroing in on your ISP is the user-to-line ratio it commands. That is, how
many users are using or are expected to use one single telephone line.
Ascertaining this, however, is not easy as the numbers of subscribers are
growing every day. Nevertheless, even the current user-to-line ratio will give
you an idea about the standards the ISP has set for itself. This factor is very
Sikkim Manipal University
Page No. 17
Website Design
Unit 1
critical because it determines the ease of usage whether you would be able
to connect to your ISP or not. Another way of finding this is to check out with
some of the existing users as to how much time it normally takes to dial into
a given ISP. If it takes more than 10 minutes to get through, that particular
ISP should be avoided.
Interface Simplicity: Very few organizations take into account the simplicity
of the interface while opting for an ISP. This occurs to them only when they
begin to use the Internet service across their organizations. The right kind of
interface can lead to tremendous savings in cost. There are other problems
too. How many users in an organization know about dial-up networking
under Windows? How many can remember and use passwords correctly?
To how many people would you like to give the password? Does terms like
TCP/IP sound friendly to them? Questions like these determine the success
of the Internet enabled organizations. There are some ISPs to whom these
questions do not apply. They provide an easy-to-use interface that once
installed works by simply pressing a button.
Roaming Facility: The roaming facility is particularly relevant for those who
travel a lot. Though most ISPs advertise this particular facility, there are not
many who pay heed to it. Its benefits are realized only when one reaches
another city and wants to access an urgent e-mail or the Internet. How does
one connect to the Internet when one is not an ISP subscriber in that
particular city? To overcome this problem, either you will have to use a
facility like Hotmail to access your mail from round the world or use the
roaming facility provided by your ISP. The roaming facility allows you to dialin into the local node of your ISP or of the regional ISP that your service
provider has a tie-up with. Then all you have to do is to plug in your
computer to a telephone line, find out the numbers for dial-up access, and
then using your password, access your original Internet account. A crucial
point here is the number of cities that your ISP has presence in or has tieups for the same.
Multiple Login Facility: Very few users know about this facility, mainly
because it is hardly advertised. However, it can prove to be a life-saver and
a great help for small and medium business houses. If n organization has
only one Internet connection, but more than one employee wants to access
the net simultaneously then this would be possible only if the ISP offers to
the organization the multiple login facility. In fact, this facility can even be
Sikkim Manipal University
Page No. 18
Website Design
Unit 1
availed of while being away from the Organization. For instance, one user
may be in New Delhi and the other user in Mumbai. But, with the e-mail it
would be possible for the man away in Mumbai to simultaneously access
the Internet. Some ISPs offer multiple e-mail IDs that allow you to segregate
e-mail individually. But you have to pay extra for this.
Special Packages: The private ISPs are putting out some unique usage
packages. It has launched a special package for night users. For those who
access the Net at night, some ISPs offer a dial-up account which costs
almost half compared to the regular connection. This account cannot be
used during day time. This is only the beginning as far as special packages
are concerned. Soon you will find ISPs (especially the regional ones)
coming out with packages that will fit your needs better than your cotton
trousers. So do not forget to check out each and every player before
deciding on your Internet provider.
Support: This is very crucial topic and an area of service where most of the
players have been found wanting. Try getting any help from the service
provider and the beautifully programmed EPABX system will take you
around each and every option, only to disconnect your call at the end saying
Sorry, the person handling your call is busy at the moment. In case, you
happen to be using pulse-dialing equipment, you can forget using the
telephone, and may as well go to their office and clear out the matter there
and then.
Ideally, new users should subscribe to an ISP where they can be hand-held
through the initial process, as Bill Gates Windows operating system does
try its best to support you in the exercise. An installation guide, the help
desks phone number, Windows 95 installation CD are part of the necessary
survival kit that a new user must have while undergoing this procedure.
Discounts on Renewal: Last but no the least, you must find out whether
your ISP will renew your account at the same rate or whether there are any
discounts to retain its old customers? This is a factor that can upset those
lining for their first-buy. VSNL has been very successful in playing this card.
It offers slashed rates to those subscribers ho renew their accounts.
Brochure-speak: If you can have more than a hundred different versions of
the holy Ramayana, just think what the crafty marketing people can do to
simple terms of the Internet. Hence, one must see through the exotic looking
Sikkim Manipal University
Page No. 19
Website Design
Unit 1
tariff cards of most ISPs. You must have the ability to judge beyond the
gloss and the glitter. To summarize, here is what you want from an Internet
Service Provider:
Access via a local phone call
A flat monthly fee
An ISDN or fast (28.8 kbps) connection
A PPP account
A shell account at no extra charge
The ability to use whichever Internet clients you want
Full Internet access to all resources
The capability of having your own web home page
Software support, through which you can use to connect to and use the
Internet
Technical support should be open 24 hours a day, 7 days a week
Self Aassessment Questions
7. ___________ are the examples of ISP.
8. The private ISPs are putting out some unique usage packages.
(true/false)
1.6 Address in Internet
Understanding of Internet also requires you to know a little about how the
systems connected on the network are named and identified. With these
names only you locate a computer and get connected to it. Every computer
that is on the Internet has its own unique address. On the Internet, the word
ADDRESS always refers to an electronic address. There are two kinds of
addresses in the Internet:
Domain names
IP Addresses
1.6.1 The Domain Name System and DNS Servers
On a TCP/IP network, computers know each other by their IP addresses.
But for human beings, remembering numbers is not the easiest thing to do.
Remembering names is much easier. Similarly, a way was devised to
associate IP addresses with names that can be easily remembered. In the
early days of the Internet, hosts files were used to associate machines with
names. The hosts file is simply a table of IP addresses and corresponding
names like a phone directory. Any name lookup (the process of identifying
Sikkim Manipal University
Page No. 20
Website Design
Unit 1
the IP address associated with a name) will first check the hosts file (if
present) on the machine making the query, to see whether the name can be
resolved.
Within the Internet, each separate computer is called a host. For example,
you might tell someone he can find the information he wants by connecting
to a host in Switzerland. If your computer is connected to the Internet, then it
too is a host, even though you may not be sharing any resources with the
rest of the world. If you connect to an log into a host and then use its rest of
the world. If you connect to and log into a host and then use its functions to
reach out onto the Internet, you are using your computer as a terminal to
reach another computer. Host connections are designed to use very simple
text based interactions.
Being connected to the Internet means your computer system or network is
actual a node on the Internet. It has an individually assigned Internet
address and client program to in running on the computer system that can
take full advantage of the computers capabilities. Your workstation is a peer
of every other computer on the Net. So, a node is any addressable device
attached to a computer network.
But with the number of hosts on the Internet increasing rapidly to an
unmanageable level, that soon became impossible. The way out was the
DNS: the Domain Name Server. The DNS is a distributed, scalable
database of IP addresses and their associated names. It is distributed in the
sense that unlike the hosts file, no single computer contains all the DNS
information in the world. The DNS data is distributed across many name
servers. It is scalable you can increase the volume of total DNS data and
requests from machines for the same data, without significantly increasing
the querying time. Otherwise the World Wide Web would really become the
World Wide Wait.
To understand the DNS and the way it is used, we need to understand the
Internet naming structure. Let us take, for example, the address:
http://www.trg.hclsso.hclinfosystems.com/
www: Indicates that the machine is part of the world
com: Indicates the top-level domain (TLD) that the machine is part of. Top
Level Domain include .com, .edu, .gov, .in etc
Sikkim Manipal University
Page No. 21
Website Design
Unit 1
hclinfosystems: Shows that the computer we are looking for is in a network
called hclinfosystems
hclsso: Indicates a sub-network (a group of computers with a common
function or at a common location).
trg: Is the name of the machine that we are interested in.
Let us see how the DNS aids in identifying the machines IP address, given
its name. at the top level of DNS structure are the nine root name servers of
the world, which contain pointers to the master name servers of each of the
top-level domains. To find the IP address of http://www.trg.hclsso.hclinfo
systems.com/ the DNS server will have to ask one of the root name servers
for he address of the master name server for the .com domain. This master
name server will have the addresses of the name servers for all the .com
domains. From here you get the address of the name server, for the
hclinfosystems.com/ domain. You move on to this name server, which will
give you the IP address of the machine trg.hclsso.com. If there is a name
server for the trg.hclsso.com sub-domain, then the name server for
hclinfosystems will guide you on to this name server, which will give you the
IP address of trg.
A domain name is a way by which a company can uniquely identify itself on
the Internet. Registering a domain name on the Internet is the equivalent of
registering a company name at Companies House. Based on the top level
identifications, there are basically two types of domains:
1. Non-geographic domains
2. Geographic domains
Non Geographic Domains
The top level Internet domain types those are non-geographical:
Domain
Com
Edu
Mil
Gov
Org
Net
Int
Indicates
Commercial Organizations
Educational Institutions
A (US) military setup
A (US) government setup
Other organizations
Other networks
An international organization
Sikkim Manipal University
Example
hclinfosystems.com
Stanford.edu
Nic.mil
Nasa.gov
www.bjp.org
Ns.stph.net
Tpc.int
Page No. 22
Website Design
Unit 1
Geographic Domains
The geographically based top-level domains use two-letter country
designations.
Domain
Au
Ca
Dk
Fr
Gr
In
Jp
Us
Meaning
Australia
Canada
Denmark
France
Greece
India
Japan
United States
In a complete (fully qualified) domain name, the part furthest to the right is
the top level domain, representing either a type of organization or a country.
As you read in from the right, the name gets more specific until you reach
the name of the individual host computer. For instance: rubens.anu.edu.au
is the name of a computer. It is in Australia (au), in the educational area
(edu), at the Australian National University (anu) and the host computer is
named rubens.
1.6.2 IP Addresses
Each host computer on the Internet has a unique number, called its IP
address. IP addresses identify the host computers, so that packets of
information reach the correct computer. You may have to type IP addresses
when you configure your computer for connection to the Internet. An IP
address is a 32-bit number that uniquely identifies a network interface. The
IP address is assigned to a network interface card and not a computer. So if
you have two Network Interface Cards, then each card is assigned an IP
address. The 32 bit IP addresses are normally expressed in dotted-decimal
format, with four numbers separated by periods, such as 151.202.123.132
These numbers can be the ranges of 0 to 255. The four constituent numbers
together represent the network that the computer is on and the computer
interface itself. IP addresses are organized from left to right, with the lefthand octet describing the largest network organization and the rightmost
octet describing the actual network connection. Each octet has value of 8
bits within the computer. When the four octets of the address are added
Sikkim Manipal University
Page No. 23
Website Design
Unit 1
together, the total address has a value of 32 bits. Using the various
combinations of these octets, several million unique identifiers can be
assigned.
Classes of Networks
Just as with our phone numbers, we can look at the leftmost octet and
determine something about the network. Network addresses are divided into
classes, which are assigned depending on the size of the physical network.
The value of the first octet tells us what class the network is in, and how
large the physical network that underlines the number is. The first octet is
sometimes called the network address or net number.
Class A: Over 16 million served
These are very big networks with up to 224 (16 million) nodes. Class A
networks have their network addresses from 1.0.0.0 to 126.0.0.0. The zeros
are replaced with the node addresses. NEARNET, Sprint, ANSnet, Merit
and AT&T are examples of organizations with class A network numbers.
Class B: Larger nets
Class B networks are smaller than Class A networks. They can have up to a
maximum of 65000 nodes. Network addresses range from 128.0.0.0 to
191.0.0.0. In this case only the last two zeros are replaced with the node
addresses. Class B addresses go to organizations with larger nets, such as
universities or large businesses. The first two octets in a Class B address
describe the network itself, and the second two identify the host.
Class C: Addresses
Class C networks are smaller than Class B networks. They can have up to
254 nodes. Network addresses range from 192.0.0.0 to 223.0.0.0. In this
case only the last zero are replaced with the node addresses. The first three
octets are used for the network numbers and the last octet is the host
number. This class is where most networks will be assigned. Originally,
Class C addresses were intended for small company networks, K-12
schools and single machines that were not connected to other, larger nets.
Other Classes
There are other classes of networks, Class D and Class E. They are
primarily used for experimental purposes. For a given network address, the
last node address is the broadcast address. For example, for Class C
Sikkim Manipal University
Page No. 24
Website Design
Unit 1
network with address 193.168.1.0, the address 193.168.1.255 is the
broadcast address. The IP addresses for networks on the Internet are
allocated by the InterNIC, the official body in charge of allocating domain
names and addresses.
Subnet Masks
In an IP network, every machine on the same physical network sees all the
data packets sent out on the network. As the number of computers grows,
the increase in network traffic brings down the performance. In such a
situation it is recommended to divide your network into sub-networks and
minimize the traffic across different sub-networks. Interconnectivity between
the different subnets would be provided by routers, which will only transmit
data meant for another subnet across itself. To divide the given network into
two or more subnets you use subnet masks. The default subnet mask for
Class A networks is 255.0.0.0; for Class B is 255.255.0.0; for Class C is
255.255.255.0 which signifies a network without subnets. The subnet mask
is used to identify the subnet to which an IP address belongs, by performing
a bit-wise AND operation on the mask and the IP address.
Self-assessment questions
9. Class A networks have their network addresses from __________
to _______.
10. ______________are examples of organizations with class A network
numbers.
1.7 Resource Addressing
Using the Web means having your browser act as a client program on your
behalf. In order to fulfill your requests, your browser will contact a server,
and ask for either some information or a service of some type.
1.7.1 URL (Uniform Resource Locator)
URLs provide a standard way to specify the exact location and name of just
about any Internet resource. In general, most URLs have one of two
common formats:
Scheme: //hostname/description
Scheme: description
Example 1: http://www.alan.com/afan
Sikkim Manipal University
Page No. 25
Website Design
Unit 1
This example describes a particular web page on a particular computer. The
URL begins with a name, indicating a specific type of resource.
Example 2: news.rec.human
This example describes a more general resource. The scheme is news,
which indicates a Usenet discussion group.
1.7.2 URLs and HOST Names
On the Internet, a hostname is a domain name assigned to a host computer.
This is usually a combination of the host's local name with its parent
domain's name. For example, "en.wikipedia.org" consists of a local
hostname ("en") and the domain name "wikipedia.org". This kind of
hostname is translated into an IP address via the local hosts file, or the
Domain Name System (DNS) resolver. It is possible for a single host
computer to have several hostnames; but generally the operating system of
the host prefers to have one hostname that the host uses for itself.
List of schemes used within URLs
Scheme
ftp
gopher
http
mailto
news
telnet
wais
1.7.3
Meaning
File accessed via file transfer protocol
Gopher resource
Hypertext resource
Mail
Usenet newsgroup
Interactive telnet session
Access a Wais database
URLs and Port Numbers
Each type of Internet service has its own specific port number. Within a URL
you only have to specify a port number if it is not the default for that type of
service. For example, the default port number for telnet is 23. The following
two URLs are equivalent:
telnet://locis.loc.gov/
telnet://locis.loc.gov:23/
The http service, by default, uses port 80. Similarly, the gopher service uses
port 70. For instance, the following two URLs are equivalent. They both
Sikkim Manipal University
Page No. 26
Website Design
Unit 1
point to the same hypertext resources, using port 80, on the computer
named www.wendy.com:
http://www.wendy.com/~wendy
http://www.wendy.com:80/~wendy
1.7.4 Pathnames
Here is a typical hypertext URL:
http://www.cathouse.org/cathouse/humor/tech/data
We can divide such URLs into three parts, the scheme, the host name and
the pathname. To analyze such a URL look at each of the parts:
The scheme (http) identifies this resource as being hypertext
The hostname (www.cathouse.org/) is the name of the computer
The pathname (cathouse/humor/tech/data) shows where on the host the
hypertext resource is stored
Self-assessment questions
11. URL stands for ______________.
12. ______________ is a domain name assigned to a host computer.
1.8 Email
This section covers the email concepts, definition, e-mail services and email networks.
1.8.1 Email Basics
The Internet is a valuable tool for accessing information, but it also opens a
whole new world of communications to its users. Using electronic mail
(email) a person can engage in conversations with people all over the world.
Yet, because of its convenience, it is also a powerful tool for even local
communication. With typical telephone communications you may be either
interrupted by a call, or may return a call only to find that the other person is
not available, an occurrence referred to as "telephone tag." Electronic mail
though, sits on the server computer until you are ready to read it, and when
you respond it will then wait patiently on the other person's computer until
they have time to read it. This is especially valuable for busy teachers, who
because of their duties and general working isolation in a classroom with
just their students, usually aren't able to communicate with peers on as
regular a basis as they would like.
Sikkim Manipal University
Page No. 27
Website Design
Unit 1
Meaning and definition of email
Electronic mail could be defined as the transmission of letters and memos
from one computer to another. When E-mail originated in the 1970s, it was
just the sending of messages. The capability to send various items has
rapidly become true of E-mail: users now can attach spreadsheets, business
forms, lengthy documents, scanned images, faxed images, computer
graphics, meeting schedules, sound and video to their messages.
Electronic mail or Email lets you communicate with other people on the
Internet. Email is one of the basic Internet services, and by far, the most
popular. It is used for conversation purpose, to keep in touch with friends,
get information, start relationships or express your opinion. This is called
Email because:
a) You put it into an electronic envelope and address it
b) You post it or hand the message to someone else (i.e. the network) to
be delivered
c) You may not know when the Email is read
d) You get Email back in your mailbox, if you addressed it incorrectly
e) If the recipient leaves a forwarding address, the Email system will keep
trying to route it to him/her until it runs out of forwarding locations
f) If the network is unable to deliver your Email, it will return the mail (this is
called bounced mail).
Email Services
In practice, Email usually refers to a service that includes the following
facilities:
Store and Forward: Messages are held until they are requested by the
recipient. Direct person-to-person contact is not required and the service
can be used by either party at whatever time and on whatever day that
suits them
Blind copies: Copies can be sent automatically to names on a
distribution list, including blind copies (where the principal recipient is
not notified that others have received the message).
Advise delivery: The sender an be told (by a confirming message to his
or her mailbox) when the recipient has read the message. An immediate
reply could also be demanded.
Sikkim Manipal University
Page No. 28
Website Design
Unit 1
Off-line working: Text can be prepared in advance of transmission and
incoming messages can be saved for later consideration or for use
within word-processed documents.
Email Networks
Email networks consist of Gateway and Closed user groups.
Gateways: Most electronic mail services include access to other facilities.
They include the telex system, on-line information services and electronic
typesetting bureaux which accepts Emailed text and return phototypeset
matters.
Closed user groups: These are areas of the Email service with restricted
access. In some cases they are available to anyone who pays an additional
fee; usually they will include extra gateways and more services. Other
closed user groups (CUGs) will be specific to members of a particular
profession Telecom hold hosts cues for solicitors and accountants, for
instance; and there are also cues for customers of individual companies
(handy for disseminating and sharing information or making requests) and
user groups for particular computer products.
In addition to these basic functions of electronic delivery systems, most
systems provide features related to other aspects of office work. These
features include:
Composing messages
Text editing
Message filing and retrieval
Authentication of message authorship
Broadcasting and distribution of messages as per specified addresses
Content processing of messages
Message switching
Accounting and billing
Security
Many Email services offer some or all of these:
Radiopaging: Your pager will beep when an urgent message is
received in your mailbox. Or you can beep someone by sending a
message to the services radiopaging mailbox.
Sikkim Manipal University
Page No. 29
Website Design
Unit 1
Telemessages: This is a replacement of the old style telegram, can be
sent from some Email services rather than by you calling the Post Office
yourself. Delivery on the next working day (including Saturdays, usually)
is guaranteed for messages received by a set time (which can be as late
as 10 p.m.). The Telemessage service can include special occasion
formats for birthday, anniversaries and the like; the delivery can include
a special reply envelope to encourage an immediate reply.
Message translation: Messages sent or received can be translated by
the Email service into the recipients native tongue.
Courier services: A message placed by you on the Email service can be
copied ad delivered by hand or mailed.
The basic functions involved in an Email system are the message creation,
message transfer and post delivery processing. These are provided by the
User Agent (UA) and a Message Transfer Agent (MTA). Thus, an Email
system is actually a message handling system. The user agent is
responsible for providing the text editing and proper presentation services to
the end user. It provides for other activities such as user friendly interaction,
security, priority provision, delivery notification and distribution subsets. The
message transfer agent is oriented towards the actual routing of the
electronic move. It is responsible primarily for the store-and-forward path,
channel security and the actual routing through the communication media.
Several MTAs taken together form the Message Transfer System (MTS).
1.8.2 Mail protocols
Email is instantaneous, cost effective and above all, personal. It produces
the immediate results in terms of increased productivity from reduced
turnaround time, and reduced costs. Email is one of the easiest services to
implement on your Internet. The ideal Mail System consists of Email servers
and clients that support standards. A clear understanding of popular
acronyms of Email will help the users in choosing the right Mail Systems.
SMTP
The transmission of Email message through the Internet relies on the
SMTP, which stands for Simple Mail Transfer Protocol. SMTP is part of the
TCP/IP family of protocols. The SMTP protocol is used to transport
messages between computer systems in the Internet. SMTP uses TCP,
Transmission Control Protocol, which provides a reliable means of
Sikkim Manipal University
Page No. 30
Website Design
Unit 1
communication. Throughout the Internet, there are millions of computers
using SMTP to send and receive mails.
Many of the host computers on the Internet run UNIX. Therefore, of
hundreds of thousands of transport agents scattered around the Net, are
running under UNIX. Specifically, most of these computers use a transport
agent called send mail, which runs automatically in the background and is
always ready to respond to whatever requests it may receive. In UNIX, such
a program is called a DAEMON and every UNIX system has various
daemons to provide fast services for you.
Internet mail system works only because everybodys network has at least
one computer running a transport agent, sending and receiving mail
according to the SMTP protocol. SMTP is fast and efficient. Nevertheless,
its drawback is both nodes should be on-line for communicating between
them. That is where POP comes in. SMTP governs the way; a UA (User
Agent) establishes a connection with a MTA (Message Transfer Agent) and
it transmits its Email message. MTAs also use SMTP to relay the Email from
MTA to MTA, until it reaches the appropriate MTA for delivery to the
receiving UA. The interactions that happen between two nodes on the
TCP/IP, whether a UA to an MTA or an MTA to another MTA, have similar
processes and follow a basic call-and-response procedure.
POP
Post Office Protocol (POP) is a mail collection and distribution system,
which works on the office principle with the mail server. It is designed to
allow single-user hosts to read mail from a server. POP allows creating a
mailbox for each user who has a mail account on the server.
There are three versions of POP: POP, POP2 and POP3. POP is a system
by which a mail server on the Internet lets us to grab our mails and
download them to our PCs. Like SMTP POP also uses plain ASCII and
independent platform and the Operating System. POP depends on SMTP to
send mails and it handles the access to the messages. POP3 is the latest
version of this protocol.
IMAP
Internet Mail Access Protocol (IMAP), unlike POP, allows hierarchical
storage of mail and a message retrieval system that allows selective access
Sikkim Manipal University
Page No. 31
Website Design
Unit 1
to your mailbox. While POP is used; for simply retrieving and deleting the
messages, using IMAP, we can organize our mails and read them on the
server itself. For a user getting connected over a slow dial up lines, IMAP
provides ways to download only the Header or the Body of the message that
contains a large attachment. In addition, IMAP allows one user to access
multiple mail serves and multiple users to share a single mailbox. IMAP can
work on any of the three basic models of communication, On-line, Off-line or
Disconnected Operation. In the On-line mode, the mail is processed in an
interactive fashion, that is, the client can ask the server for only the
message headers and then request only specified messages, or can even
retrieve parts of certain messages.
MIME and S/MIME
SMTP can handle only messages containing the 7 bit ASCII text and it
cannot handle other types of data such as 8-bit binary data and other
multimedia formats that nowadays we are sending both within the body of
Email messages and as attachments. However, as a solution to this
limitation, the ETF developed the Multipurpose Internet Mail Extensions
(MIME) protocol, which packs multimedia data into a format that SMTP can
handle. Stands for Secure/Multipurpose Internet Mail Extensions and was
designed to add security to Email messages in MIME format. The security
services offered are authentication (using digital signatures) and privacy
(using encryption). S/MIME is not specific to the Internet and can be used in
any electronic mail environment.
UUCP
As an Internet user, you may want to exchange mails with different types of
networks and then you should know what type of addresses they use. Same
popular networks to send mails are CompuServe, MCI Mail, America Online,
UNIX-based UUCP network, and so on.
All UNIX systems come with a built in networking system called UUCP.
Although the job of UUCP is to connect UNIX computers, it is not as
powerful as TCP/IP. For example, UUCP does not provide a remote login
facility; mail facility is slower and awkward than the TCP/IP based Internet
system. However, UUCP does have an important advantage. It is a
standard part of UNIX and it runs cheaply and reliably over dial-up or
hardwired connections.
Sikkim Manipal University
Page No. 32
Website Design
Unit 1
UUCP works by allowing UNIX systems to connect together to form a chain.
To understand this let us consider all connections in Internet are permanent
and messages are transmitted quickly, often within seconds. Therefore,
there is no comparison between Internet and UUCP connections. To send
mail to UUCP address, you must specify the route you want the message to
take. For the above example the mail command will be: Mail second! Third!
Fourth! Pant
After creating such a message, your system will start this message until a
contact is established with the computer within seconds and then the
message will be sent on its way. If the path is too long or you have no idea
about what path to use from your computer to send the mail,
UUCPMAPPING PROJECT is undertaken. This allows you to use a UUCP
address that is similar to an Internet address. Thus, on occasions, you may
see an address that uses a top-level domain of UUCP. Look at the following
example: pant@gendeau.uucp
Say you are using a computer named first. Your computer is connected to
another computer named second. This computer is connected to third,
which is, in turn connected to fourth. You decide to send the message from
your computer, first to a person having user id pant to fourth. UUCP will
pass the message from first to second to third to fourth, where it will be
delivered to user id pant.
Therefore, in our example, four computers and three connections are
involved. The system works well as it provides an economical way to send
mail from computer to computer over large distances. However, the
limitation is since many UUCP connections are made over a telephone line
at certain predefined time, mail delivery can take hours or even several
days.
1.8.3 How to Access the Mail System
As we explained in the previous section, SMTP is used to send and receive
mail behind the scenes. The question now arises, how the mail gets from
the transfer agent to you. The computer that provides the Internet
connection also acts as the mail host. Typically, this computer runs a
transport agent program which is connected to the Internet 24 hours a day.
This means, whenever your mail arrives, the transport agent available
accepts it and saves it in a file called a MAILBOX. Each person who has an
Sikkim Manipal University
Page No. 33
Website Design
Unit 1
account on the host computer is given his own mailbox file. In this way the
host computer always keep everyones mail in an organized manner and at
the same time it assures you that no one can read your messages.
Ways of Accessing Email
There are many ways to access your Email. You may use a mail client, such
as Eudora, Outlook or anyone of the popular packages that download your
incoming messages from the POP server to your computer and upload your
outgoing messages to the SMTP server. This may occur through a Local
Area Network (LAN) or through a dial-up connection.
You may use a Web based Email service
You may use a commercial provider, such as CompuServe or America
On-line which have their own Email programs
You may get your Email through a LAN, a common system at large
organization, if your organization has some sort of Internet connection,
Email arrives in the companys POP server. You then read your Email
either on the server using an Email application or on your own computer,
by downloading your Email from the server through the LAN by using an
Email application. Your company may use a POP server or some kind of
proprietary protocol.
You may have a UNIX shell account and use a UNIX Email program that
reads your POP mailbox directly.
How does Email Work?
Let us review how Email works, using an example. In this example, you are
using a PC with Windows OS, which connects to the Internet using TCP/IP.
Let us suppose you want to send a mail to two of your friends: Surya in
Washington and Rishaba in Germany. Surya uses a Macintosh and also
connects to the Net using PPP. Rishaba uses a shell account by connecting
UNIX host computer. The following steps illustrate the example.
1. First using a Windows mail client, you compose the message on your
own computer.
2. After you compose the message, address it to both Surya and
Rishaba.
3. Once the message is finished, you tell your program to send it on its
way.
Sikkim Manipal University
Page No. 34
Website Design
Unit 1
4. Now your client program contacts the mail server on your Internet host
and using the POP protocol, sends your message to the server.
5. In the next step, the server passes your message to the transport
agent.
6. Now, it is the job of transport agent to look at the addresses in your
message and connect to the appropriate computers over the Net.
7. First, the transport agent connects it on the host computer in
Washington that receives mail for Surya.
8. Once the connection is made, the two transport agents use the SMTP
to relay the message.
9. After the message is sent, your transport agent terminates the
connection and forms a new connection with the transport agent on
the appropriate computer in Germany.
10. Again, the two transport agents use SMTP to relay the message.
11. Once the message is sent, your transport agent terminates the
connection, its job is finished.
12. In Washington, Surya turns on his computer to check the mail. He tells
his Macintosh mail client to see if any new mail has arrived. Now it is
the turn of his mail client to connect to the mail server on Suryas host
computer and using the POP protocol, asks the server to check
Suryas mailbox. Since server finds your message, so using POP, it
sends the message to the client and places the message in his local
mailbox (a file on the Mac) and tells him that new mail has arrived.
Now, with the help of mail program, Surya displays the message.
13. Similarly, in Germany, Rishaba has logged into his shell account on a
UNIX host. He runs his UNIX mail program which checks his mailbox
and tells him new mail has arrived. Using appropriate command,
Rishaba tells the mail program to show him your message.
The important thing in this example is that, even though they use different
computers and different programs, the mail moves smoothly and quickly,
just because of the Internet and SMTP.
Understanding the Internet Email Addresses
In this section, we will talk a little more about how to specify addresses
when you send mail as you have now become aware that whenever we talk
Sikkim Manipal University
Page No. 35
Website Design
Unit 1
about the word mail, it always means electronic ail and the word address
always refers to an Internet address. Thus, if someone on the Net asks
What is your address? tell him or her, your electronic address.
An Email address defines the location of an individuals mailbox on the
Internet. An address consists of two parts: username and domain name,
separated by the @ symbol. Here is an example:
Username in the preceding example is Leenu. Usernames are usually pretty
straightforward; often, companies give employees usernames that use one
initial and one full name. However, usernames can also contain characters
other than letters they can contain numbers, underscores, periods and
some other special characters. They cannot contain commas, spaces or
parenthesis.
The host name provides the Internet location of the mailbox, usually the
name of a computer owned by a company or Internet service which has
been discussed in Unit 2. If the recipient is within your local network, you
can often leave out part of the address. For example, say your address is
Kapil@great.vsnl.in and you are mailing to a friend whose computer is on
the same network. Your friends address is Sachin@more.vsnl.in. So you
can leave off the part of the address you both have in common. That is, in
this case, you use sachin@more. The mail program easily recognizes it as a
local address and delivers the message properly. If you have a problem, you
may have to use the full address. it is also possible to leave out the
computer name entirely and just use the user ID if the person you are
sending mail to is surya@uptec.vsnl.in and you want to send mail to
rishaba@uptec.vsnl.in, you can use: rishaba. When you do not know
someones Email address, and you have an ides of his login name and the
name of the Internet site he uses you should be able to send Email to the
postmaster at any Internet site. That is the address to use if you have
questions about an Email to or from a specific host or site, or general
questions about a site. However, you may not get a quick response, since
the person designated as postmaster usually has lots of other duties. For
example, you have trouble finding out the address of someone who uses a
computer named great.vsnl.in; you can send a message asking for the
persons mail address to: postmaster@great.vsnl.in.
Sikkim Manipal University
Page No. 36
Website Design
Unit 1
Self-assessment questions
13. Three versions of POP are ____________.
14. _____________ allows hierarchical storage of mail and a message
retrieval system that allows selective access to your mailbox.
1.9 Summary
The Internet links are computer networks all over the world so that users
can share resources and communicate with each other.
Internet is a vast collection of globally available information which can be
accessed electronically information which is of practical use for
business, research, study and technical purposes.
No one owns the Internet. Any single person, corporation, university or
government does not fund it. Internet has been described as the
cooperative anarchy.
Protocols are the rules that all networks use to understand each other.
For example, there is a protocol describing exactly what format should
be used for sending mail message.
The internet is based on a large number of protocols and conventions.
Each such protocol is explained in the technical publication called a
request for comment or RFC.
The primary objective of any network is to exchange information
between different locations.
Many of the host computers on the Internet offer services to other
computers on the Internet.
Conversely, many of the computers on the Internet use servers to get
information.
The mail servers handle incoming and outgoing mail.
A protocol dialup account lets your computer behave like it is connected
directly to another computer on the Internet.
The family of Internet protocols is called TCP/IP.
A dedicated link (or leased line) is a permanent connection over a
telephone line between a modem pointer to another modem pointer.
Each host computer on the Internet has a unique number, called its IP
address.
Sikkim Manipal University
Page No. 37
Website Design
Unit 1
On the Internet, a hostname is a domain name assigned to a host
computer.
Internet Mail Access Protocol (IMAP), unlike POP, allows hierarchical
storage of mail and a message retrieval system that allows selective
access to your mailbox.
1.10 Terminal Questions
1. Briefly explain the Internet from practical and technical angle.
2. What are the requirements for internet connections?
3. Explain the Domain Name System and DNS servers.
4. Briefly explain the various classes of networks.
5. Explain the various mail protocols used.
1.11 Answers
Self Assessment questions:
1. Request for comment
2. Networks
3. True
4. Simple mail transfer protocol
5. True
6. True
7. Airtel, Bsnl, Tataindicom
8. True
9. 1.0.0.0 to 126.0.0.0.
10. NEARNET, Sprint, ANSnet, Merit and AT&T
11. Uniform Resource Locator
12. Hostname
13. POP, POP2 and POP3
14. POP
Sikkim Manipal University
Page No. 38
Website Design
Unit 1
Terminal Questions
1. Internet is a vast collection of globally available information which can be
accessed electronically information which is of practical use for
business, research, study and technical purposes. (Refer Section 1.2.2)
2. There are essentially three different types of connections for accessing
the services and resources of the Internet. (Refer Section 1.4.1)
3. On a TCP/IP network, computers know each other by their IP
addresses. (Refer Section 1.6.1)
4. Network addresses are divided into classes, which are assigned
depending on the size of the physical network. (Refer Section 1.6.2)
5. It produces the immediate results in terms of increased productivity from
reduced turnaround time, and reduced costs. (Refer Section 1.8.2)
Sikkim Manipal University
Page No. 39
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5834)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (350)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (824)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (405)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Cybrary CSSLP SlidesDocument246 pagesCybrary CSSLP Slidesineba100% (1)
- DA-100 - Analyzing Data With Power BIDocument7 pagesDA-100 - Analyzing Data With Power BInareshbawankarNo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Dir SellingDocument6 pagesDir SellingdhirkpNo ratings yet
- Giit Class Test - Ii: InstructionDocument6 pagesGiit Class Test - Ii: InstructiondhirkpNo ratings yet
- Remedial Coaching Class Time Table August 2014Document1 pageRemedial Coaching Class Time Table August 2014dhirkpNo ratings yet
- Su 2 Exam Prep QuestionsDocument7 pagesSu 2 Exam Prep QuestionsdhirkpNo ratings yet
- Page0001Document1 pagePage0001dhirkpNo ratings yet
- Format - A For Publication of Postpaid Tariff PlansDocument1 pageFormat - A For Publication of Postpaid Tariff PlansdhirkpNo ratings yet
- Ques W10 Math 22dec 2014Document1 pageQues W10 Math 22dec 2014dhirkpNo ratings yet
- Write Down The Time in Words: "Print Your Own Worksheets atDocument1 pageWrite Down The Time in Words: "Print Your Own Worksheets atdhirkpNo ratings yet
- Electronics Digital Circuit Addition Computers Arithmetic Logic UnitDocument1 pageElectronics Digital Circuit Addition Computers Arithmetic Logic UnitdhirkpNo ratings yet
- Unit - 6 Verification and Valuation of Assets and LiabilitiesDocument1 pageUnit - 6 Verification and Valuation of Assets and LiabilitiesdhirkpNo ratings yet
- Unit - 4 Auditing TechniquesDocument1 pageUnit - 4 Auditing TechniquesdhirkpNo ratings yet
- Unit - 8 Cost Audit: Financial Systems and Auditing Unit - 8Document1 pageUnit - 8 Cost Audit: Financial Systems and Auditing Unit - 8dhirkpNo ratings yet
- Unit - 7 Management Audit: Financial Systems and Auditing Unit - 7Document1 pageUnit - 7 Management Audit: Financial Systems and Auditing Unit - 7dhirkpNo ratings yet
- Annexure: Financial Systems and AuditingDocument1 pageAnnexure: Financial Systems and AuditingdhirkpNo ratings yet
- Financial Auditing Another MCQDocument7 pagesFinancial Auditing Another MCQdhirkpNo ratings yet
- Meet Our New MBADocument1 pageMeet Our New MBAdhirkpNo ratings yet
- Sample Answer SheetDocument1 pageSample Answer SheetdhirkpNo ratings yet
- Kolhan University, Chaibasa: Application Form For Contractual AppointmentDocument3 pagesKolhan University, Chaibasa: Application Form For Contractual AppointmentdhirkpNo ratings yet
- Vidyadeep Scholarship Terms - Fall DriveDocument4 pagesVidyadeep Scholarship Terms - Fall DrivedhirkpNo ratings yet
- 442A-MA Mathematics (Master of Arts in Mathematics)Document20 pages442A-MA Mathematics (Master of Arts in Mathematics)dhirkpNo ratings yet
- Mba Thesis: Professor Rodrigo Magalhaes Intake 10 / Group 4 1446 Kuwait 20-February-10 20-February-10Document2 pagesMba Thesis: Professor Rodrigo Magalhaes Intake 10 / Group 4 1446 Kuwait 20-February-10 20-February-10dhirkpNo ratings yet
- MB0052 SLM Unit 02Document28 pagesMB0052 SLM Unit 02mrahul29_400215311No ratings yet
- Spirofy 4 Page Brochure - 230913 - 102119Document4 pagesSpirofy 4 Page Brochure - 230913 - 102119Amit KaradNo ratings yet
- Transaction ProcessingDocument9 pagesTransaction ProcessingJenaro WachiraNo ratings yet
- Computer TRICKS First PartDocument10 pagesComputer TRICKS First PartSantu NandiNo ratings yet
- Tef Calculator Walk ThroughDocument17 pagesTef Calculator Walk ThroughCapitus L. L. PNo ratings yet
- R GameDocument79 pagesR Gamearnav mauryaNo ratings yet
- 8 Tips For An Awesome PowerPoint PresentationDocument48 pages8 Tips For An Awesome PowerPoint PresentationTủ LạnhNo ratings yet
- Elevens Gaming HubDocument66 pagesElevens Gaming HubOrange MindedNo ratings yet
- Aster Flaash PDFDocument14 pagesAster Flaash PDFJavier Saul Salgado ParejaNo ratings yet
- 123Document2 pages123rajuNo ratings yet
- Resulticks Introduction v2Document8 pagesResulticks Introduction v2Atul SinghNo ratings yet
- Prac 8 Resistance and Heat - Using Nichrome WireDocument3 pagesPrac 8 Resistance and Heat - Using Nichrome Wireapi-357642569No ratings yet
- Introduction To Gis and Arcgis: How A Gis WorksDocument37 pagesIntroduction To Gis and Arcgis: How A Gis WorksTäð Œvê MîðNo ratings yet
- Application of SPSS in Research WritingDocument77 pagesApplication of SPSS in Research WritingKaren Joy SabladaNo ratings yet
- Updated ResumeDocument3 pagesUpdated Resumeapi-3742929No ratings yet
- Pyserial PDFDocument63 pagesPyserial PDFJayesh ShawNo ratings yet
- Editar Menu Contextual OperaDocument7 pagesEditar Menu Contextual OperaPedro José Suárez TorrealbaNo ratings yet
- Michael Kors MKT 5089 - Set-Up & InstructionsDocument21 pagesMichael Kors MKT 5089 - Set-Up & InstructionsmkorsNo ratings yet
- Lab Activitiy 3 - For ESDocument8 pagesLab Activitiy 3 - For ESHiếu ShidoNo ratings yet
- Four-Quadrant: Dynamometer/Power Supply MODEL 8960Document16 pagesFour-Quadrant: Dynamometer/Power Supply MODEL 8960Jose Angel Puente PuenteNo ratings yet
- Dv300 Service Manual Eng 120214 1Document68 pagesDv300 Service Manual Eng 120214 1rocklando777No ratings yet
- Google Strategy in 2013 - Strategic Management CaseDocument24 pagesGoogle Strategy in 2013 - Strategic Management CaseRizkySeptiandyNo ratings yet
- Sesi 15 - FinAudit - IT Audit Integration & Security MGT Ver 1Document48 pagesSesi 15 - FinAudit - IT Audit Integration & Security MGT Ver 1keishaNo ratings yet
- 2 Weeks Data Science Using Python: Days TopicsDocument2 pages2 Weeks Data Science Using Python: Days TopicsKiaraNo ratings yet
- Enerlin'X IFE Ethernet Interface For One Circuit Breaker Used GuideDocument96 pagesEnerlin'X IFE Ethernet Interface For One Circuit Breaker Used Guidelorentz franklinNo ratings yet
- Tic Tac Toe GameDocument27 pagesTic Tac Toe GameVikas KumarNo ratings yet
- Bio ChipDocument16 pagesBio ChipAnil KumarNo ratings yet
- Linksys srw208Document86 pagesLinksys srw208Ivan Ernesto MillaNo ratings yet
- 1 © Netskills Quality Internet Training, University of NewcastleDocument14 pages1 © Netskills Quality Internet Training, University of Newcastleramzi esprimsNo ratings yet