Professional Documents
Culture Documents
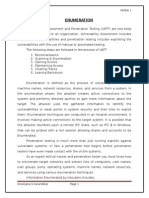
Name Service Vulnerable Platforms Mechanism Time To Implement Effect
Name Service Vulnerable Platforms Mechanism Time To Implement Effect
Uploaded by
blinking02Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Name Service Vulnerable Platforms Mechanism Time To Implement Effect
Name Service Vulnerable Platforms Mechanism Time To Implement Effect
Uploaded by
blinking02Copyright:
Available Formats
Name
Service
telnet,
Dictionary rlogin, pop,
imap, ftp
Ftp-write
ftp
Guest
telnet,
rlogin
Imap
imap
Named
dns
Phf
http
Sendmail
smtp
Xlock
Xsnoop
Vulnerable
Platforms
Mechanism
Time to
Implement
Effect
Abuse of Feature
Medium
User-level access
Misconfiguration
Short
User-level access
Misconfiguration
Short
User-level access
Bug
Short
Root Shell
Bug
Short
Root Shell
Bug
Short
Bug
Long
Misconfiguration
Medium
Misconfiguration
Short
All
All
All
Linux
Linux
All
Linux
All
All
Execute commands as
user http
Execute commands as
root
Spoof user to obtain
password
Monitor Keystrokes
remotely
Figure 8-1: Summary of Remote to Local Attacks
Users typically do not choose good passwords, so an attacker who knows the
username of a particular user (or the names of all users) will attempt to gain access to this
users account by making guesses at possible passwords. Dictionary guessing can be
done with many services; telnet, ftp, pop, rlogin, and imap are the most prominent
services that support authentication using usernames and passwords. Figure 8-2 is a plot
of the connections made to the pop3 port of a victim machine during a dictionary attack
that is using the pop service to check for valid login/password combinations.
The
horizontal axis of this plot represents time in minutes, and each line segment in the plot is
a single connection to the pop3 service.
Lines representing succesive sessions are
71
You might also like
- GMAT Ir 50题 (官方详解版)Document64 pagesGMAT Ir 50题 (官方详解版)blinking02No ratings yet
- How To Hack Remote Computer Using Ip AddressDocument4 pagesHow To Hack Remote Computer Using Ip AddressJeandelaSagesseNo ratings yet
- Network CommandsDocument36 pagesNetwork CommandsR B SHARANNo ratings yet
- Utilities CommandDocument14 pagesUtilities Commandmanishbhardwaj8131No ratings yet
- Section 10 Understanding Common Endpoint Attacks LabDocument25 pagesSection 10 Understanding Common Endpoint Attacks LabritaNo ratings yet
- CH 05Document12 pagesCH 05andrewiles88No ratings yet
- Telnet and Remote LoginDocument5 pagesTelnet and Remote LoginBoobalan RNo ratings yet
- Lab - Exploring Endpoint Attacks: RequirementsDocument16 pagesLab - Exploring Endpoint Attacks: RequirementsMohcine OubadiNo ratings yet
- The Inetd Daemon and Inetd ServicesDocument21 pagesThe Inetd Daemon and Inetd ServicesSonata912No ratings yet
- Hacking Unix: Last Modified 2-27-09Document80 pagesHacking Unix: Last Modified 2-27-09andrewiles88No ratings yet
- How To Hack Remote Computer Using Ip AddressDocument4 pagesHow To Hack Remote Computer Using Ip AddressJeandelaSagesseNo ratings yet
- How To Hack Remote Computer Using Ip AddressDocument4 pagesHow To Hack Remote Computer Using Ip AddressJeandelaSagesseNo ratings yet
- ImpersonationDocument6 pagesImpersonationdanesvNo ratings yet
- Phase3: Gaining Access Using Network AttacksDocument70 pagesPhase3: Gaining Access Using Network AttackspermasaNo ratings yet
- PenetrationTestReport SaDocument5 pagesPenetrationTestReport Sapratik khadkaNo ratings yet
- Big Ultra HackDocument6 pagesBig Ultra Hackruwan555100% (2)
- 22MCAR0033 CF Activity2Document11 pages22MCAR0033 CF Activity2Fatema TahaNo ratings yet
- Chapter 3Document49 pagesChapter 3Jeff MaynardNo ratings yet
- Chapter 5 Linux System AdminDocument48 pagesChapter 5 Linux System AdminMohammed HusenNo ratings yet
- Lec 04Document24 pagesLec 04death wishNo ratings yet
- How To Use FTP in A Shell ScriptDocument5 pagesHow To Use FTP in A Shell ScriptSwaroop VanteruNo ratings yet
- TCP Wrapper Network Monitoring, Access Control, and Booby TrapsDocument7 pagesTCP Wrapper Network Monitoring, Access Control, and Booby Trapsdelta craiovaNo ratings yet
- Application Layer ProtocolDocument4 pagesApplication Layer Protocolhassan IQNo ratings yet
- Experiment 9Document8 pagesExperiment 9Javeed AhamedNo ratings yet
- Exploits: Dalia SolomonDocument39 pagesExploits: Dalia SolomonnickNo ratings yet
- Enumeration: MSC 2 Sem 3 Paper 1Document13 pagesEnumeration: MSC 2 Sem 3 Paper 1Niranjana KarandikarNo ratings yet
- Notes On Computer Networks Unit5Document9 pagesNotes On Computer Networks Unit5Rohit Chaudhary100% (2)
- Protocols in Application Layer 17.01.2024Document4 pagesProtocols in Application Layer 17.01.2024Aloysius DsouzaNo ratings yet
- CCNA Cyber Ops Version 11 Chapter 3 Exam Answers FullDocument11 pagesCCNA Cyber Ops Version 11 Chapter 3 Exam Answers FullMetasploitNo ratings yet
- Linux Overview and Introduction To Socket Programming: Lab InstructorDocument35 pagesLinux Overview and Introduction To Socket Programming: Lab InstructorUmar RiazNo ratings yet
- VulnVoIP (Vulnerable VoIP) SolutionsDocument10 pagesVulnVoIP (Vulnerable VoIP) SolutionsFelipe MeraNo ratings yet
- PHP File InclusionDocument11 pagesPHP File InclusionAhmed SolimanNo ratings yet
- Lab1 - Kali Linux Overview: 1. ReconnaissanceDocument6 pagesLab1 - Kali Linux Overview: 1. ReconnaissanceNguyễn Hữu VĩnhNo ratings yet
- 7 2 Malware BehaviorDocument28 pages7 2 Malware BehaviorJayesh ShindeNo ratings yet
- Client Gibraltar Server Comparison (Microsoft Design Document)Document24 pagesClient Gibraltar Server Comparison (Microsoft Design Document)illegal-manualsNo ratings yet
- Cs155 Pp3 SectionDocument30 pagesCs155 Pp3 SectionXozanNo ratings yet
- Remote Monitoring System For Cyber ForensicDocument9 pagesRemote Monitoring System For Cyber ForensicpagalfakirNo ratings yet
- Finger Protocol Wiki PDFDocument3 pagesFinger Protocol Wiki PDFSalman AlfarisiNo ratings yet
- VAPT Mooc Course NotesDocument10 pagesVAPT Mooc Course NotesFatema TahaNo ratings yet
- Enumeration TestingDocument38 pagesEnumeration TestingYusifsuleimanNo ratings yet
- Lifecycle of An AttackDocument9 pagesLifecycle of An AttackDhritiman BasuNo ratings yet
- TCP IP VulnerabilitiesDocument17 pagesTCP IP VulnerabilitiesHemant Sudhir WavhalNo ratings yet
- MSF IiDocument12 pagesMSF IiGlowing StarNo ratings yet
- Trojan Port ListDocument13 pagesTrojan Port ListWahyu HidayatNo ratings yet
- The Arsenal, The Armorty and The LibraryDocument51 pagesThe Arsenal, The Armorty and The LibraryD Chris100% (1)
- Anatomy of A Pass-Back-Attack - Intercepting Authentication Credentials Stored in Multi Function PrintersDocument7 pagesAnatomy of A Pass-Back-Attack - Intercepting Authentication Credentials Stored in Multi Function PrinterskurapixNo ratings yet
- Malware DeveopmentDocument435 pagesMalware Deveopmentjjjabriyel jabriNo ratings yet
- 1.4 Basic Network UtilitiesDocument4 pages1.4 Basic Network UtilitiesmeeeNo ratings yet
- Hacking Primer: BY Intramantra Global Solution PVT LTD, IndoreDocument34 pagesHacking Primer: BY Intramantra Global Solution PVT LTD, IndoreDeepak RathoreNo ratings yet
- EnumerationDocument12 pagesEnumerationNiranjana KarandikarNo ratings yet
- Honeypots: Hands-On SessionDocument34 pagesHoneypots: Hands-On SessionakhileshNo ratings yet
- It 429 - Week 12&13Document35 pagesIt 429 - Week 12&13mjdcan_563730775No ratings yet
- Ettercap: FunctionalityDocument2 pagesEttercap: FunctionalityMaduka ChukwuNo ratings yet
- How Do SSH, Telnet and Rlogin Differ?Document11 pagesHow Do SSH, Telnet and Rlogin Differ?Saorabh KumarNo ratings yet
- CS155: Computer and Network Security: Programming Project 3 - Spring 2004Document30 pagesCS155: Computer and Network Security: Programming Project 3 - Spring 2004ashishbhangeNo ratings yet
- Ip Multimedia Sub SystemDocument50 pagesIp Multimedia Sub SystemSatyanarayan MishraNo ratings yet
- Week-2 Lab DNS FTPDocument7 pagesWeek-2 Lab DNS FTPMIHIKA PARAG DESHPANDENo ratings yet
- PuTTY User ManualDocument579 pagesPuTTY User Manualder ApfelNo ratings yet
- Important DocumentDocument5 pagesImportant Documenttasnim tamannaNo ratings yet
- LAB5 - CSE3501 - 19BEC1289 ReferenceDocument11 pagesLAB5 - CSE3501 - 19BEC1289 ReferencepranavNo ratings yet
- Reading Comprehension For GRE and GMATDocument120 pagesReading Comprehension For GRE and GMATThe RockNo ratings yet
- Chess Life 2018 12 PDFDocument76 pagesChess Life 2018 12 PDFblinking02100% (2)
- 27 Ways To Clean With Baking Soda: Friday: Clean and OrganizedDocument4 pages27 Ways To Clean With Baking Soda: Friday: Clean and Organizedblinking02No ratings yet
- Grade 7/8 Math Circles Sets - Solutions Exercises I: February 4/5, 2014Document18 pagesGrade 7/8 Math Circles Sets - Solutions Exercises I: February 4/5, 2014blinking02No ratings yet
- WHICH THAT的就近修饰和跳跃修饰整理Document18 pagesWHICH THAT的就近修饰和跳跃修饰整理blinking02No ratings yet
- Farm ParticipantsDocument9 pagesFarm Participantsblinking02No ratings yet
- 附:答案Document1 page附:答案blinking02No ratings yet
- Practice Test #1 Sentence Correction (171-258)Document26 pagesPractice Test #1 Sentence Correction (171-258)blinking02No ratings yet
- Oracle®: SOA Suite 11 Hands-On Workshop Lab 7Document18 pagesOracle®: SOA Suite 11 Hands-On Workshop Lab 7blinking02No ratings yet
- Exploring Excel Functions Goal Seek: Learnit InstructionDocument3 pagesExploring Excel Functions Goal Seek: Learnit Instructionblinking02No ratings yet
- SOA Suite 11 Hands-On Workshop VM Intro / Demo / Deployment: Oracle®Document35 pagesSOA Suite 11 Hands-On Workshop VM Intro / Demo / Deployment: Oracle®blinking02No ratings yet
- Relative Resource ManagerDocument26 pagesRelative Resource Managerblinking02No ratings yet
- Oracle®: SOA Suite 11.1.1.2 Hands-On Workshop OSB Lab 2bDocument23 pagesOracle®: SOA Suite 11.1.1.2 Hands-On Workshop OSB Lab 2bblinking02No ratings yet
- Exploring Excel Functions Statistical Functions: Learnit InstructionDocument2 pagesExploring Excel Functions Statistical Functions: Learnit Instructionblinking02No ratings yet