Professional Documents
Culture Documents
Practical # 6 Tcp/Port Scanning Using Nmap (Use Zen Map)
Practical # 6 Tcp/Port Scanning Using Nmap (Use Zen Map)
Uploaded by
mann123456789Copyright:
Available Formats
You might also like
- Cascade Controller For DCDC Buck ConvertorDocument6 pagesCascade Controller For DCDC Buck ConvertorCristóbal Eduardo Carreño MosqueiraNo ratings yet
- What Is NmapDocument5 pagesWhat Is Nmapramya.gNo ratings yet
- Name: Pradeep Gupta Roll No: 112 Div: ADocument3 pagesName: Pradeep Gupta Roll No: 112 Div: APradeep GuptaNo ratings yet
- Lab 06 TaskDocument2 pagesLab 06 TaskZuraiz QureshiNo ratings yet
- CN - Exp-4Document4 pagesCN - Exp-4FLICKA 69No ratings yet
- Tutorial 3 - NmapDocument8 pagesTutorial 3 - Nmaplaytonchetty27No ratings yet
- VaptDocument21 pagesVaptSri GouriNo ratings yet
- Top 16 Nmap Commands To Scan Remote HostsDocument10 pagesTop 16 Nmap Commands To Scan Remote Hostsmindhackers161No ratings yet
- NmapDocument14 pagesNmapamird12No ratings yet
- Network Security Lab Manual DraftDocument29 pagesNetwork Security Lab Manual DraftShraddha PatilNo ratings yet
- Nmap Cheat Sheet From Discovery To Exploits - Part 1 Introduction To NmapDocument19 pagesNmap Cheat Sheet From Discovery To Exploits - Part 1 Introduction To Nmaparcalius7No ratings yet
- Lab Experiment #08 - Network & Host Detection ScansDocument3 pagesLab Experiment #08 - Network & Host Detection ScansAnoop DasNo ratings yet
- ED Nmap 110223 1642Document5 pagesED Nmap 110223 1642Murilo Zanardo Reis NogueiraNo ratings yet
- Lab Sheet 2Document9 pagesLab Sheet 2api-2414180090% (1)
- Networks Practical NmapDocument1 pageNetworks Practical Nmapbelkacem el kasmiNo ratings yet
- 3 NmapDocument6 pages3 NmapJohn WickNo ratings yet
- 3 NetworkSecurity LABManualDocument33 pages3 NetworkSecurity LABManualdahiyalkNo ratings yet
- NMAP - Information GatheringDocument6 pagesNMAP - Information GatheringRockstar GmailNo ratings yet
- NetworkSecurity LABManualDocument33 pagesNetworkSecurity LABManualvenkatdhanNo ratings yet
- NMAPDocument1 pageNMAPcaptnitro1No ratings yet
- 03 - Performing Security AssessmentsDocument78 pages03 - Performing Security AssessmentsDoraemonNo ratings yet
- Refresher Guide NmapDocument7 pagesRefresher Guide NmapmalinaNo ratings yet
- 03 - Performing Security AssessmentsDocument78 pages03 - Performing Security Assessmentsتيمور الجبورNo ratings yet
- Top 32 Nmap Command Examples For SysNetwork AdminsDocument16 pagesTop 32 Nmap Command Examples For SysNetwork AdminswizunuNo ratings yet
- Nmap All UsesDocument3 pagesNmap All UsesSaurabh SahuNo ratings yet
- Lab 5Document4 pagesLab 5Derick cheruyotNo ratings yet
- Lab IiiDocument14 pagesLab IiiKumar JiNo ratings yet
- NmapDocument3 pagesNmapAakanksha NNo ratings yet
- NMap - Network MappingDocument35 pagesNMap - Network MappingFaisal AR100% (4)
- IP Address and Port ScanningDocument4 pagesIP Address and Port Scanningreddy ramya sri ghantasalaNo ratings yet
- Project 7 Network Port ScanningDocument8 pagesProject 7 Network Port ScanningRahul GoyalNo ratings yet
- CIT 480: Securing Computer Systems Lab #7: Network Scanning NameDocument4 pagesCIT 480: Securing Computer Systems Lab #7: Network Scanning NameManzu PokharelNo ratings yet
- Nmap CommandDocument3 pagesNmap CommandKrishna ForuNo ratings yet
- Setup Lab Environment: MIT210 - Information Systems Security and AssuranceDocument12 pagesSetup Lab Environment: MIT210 - Information Systems Security and AssuranceJessa GalaponNo ratings yet
- Top 30 Nmap Command ExamplesDocument12 pagesTop 30 Nmap Command ExamplesvictorpetriniNo ratings yet
- Scanning NetworksDocument36 pagesScanning Networksjaya prasanna100% (2)
- Laboratory Setup: Step 1: Download Metasploitable, Which Is A Linux Machine. It Can Be Downloaded FromDocument13 pagesLaboratory Setup: Step 1: Download Metasploitable, Which Is A Linux Machine. It Can Be Downloaded FromTajria SultanaNo ratings yet
- NMAP WinDocument1 pageNMAP WinYassineNo ratings yet
- 8 24 23 NmapDocument13 pages8 24 23 NmapBALRAJ SINGHNo ratings yet
- Evaluation & Testing of Information AssetsDocument10 pagesEvaluation & Testing of Information AssetsMaksNo ratings yet
- Lab Manual CS 1-2Document23 pagesLab Manual CS 1-2Sandip MouryaNo ratings yet
- Nmap CommandsDocument17 pagesNmap CommandsAbhishekNo ratings yet
- 7 CNDocument11 pages7 CNAdfar RashidNo ratings yet
- Perform An Experiment For Port Scanning With Nmap, Superscan or Any Other Equivalent SoftwareDocument4 pagesPerform An Experiment For Port Scanning With Nmap, Superscan or Any Other Equivalent SoftwaresangeetadineshNo ratings yet
- Assignment 2Document2 pagesAssignment 2Mehul JainNo ratings yet
- Practice Exercises 4Document2 pagesPractice Exercises 4Tran TranNo ratings yet
- Foot PrintingDocument21 pagesFoot PrintingmwesigwaaNo ratings yet
- Security & Ethical Hacking p2Document29 pagesSecurity & Ethical Hacking p2Vipin NarangNo ratings yet
- MRTG NotesDocument24 pagesMRTG NotesErik Rafael Torres FernandezNo ratings yet
- NMap Tutorial For Beginners PDFDocument7 pagesNMap Tutorial For Beginners PDFzarakighostNo ratings yet
- Protecting and Port ScanningDocument3 pagesProtecting and Port ScanningShoua IqbalNo ratings yet
- NmapDocument14 pagesNmapayeshashafeeqNo ratings yet
- Craft: Top 30 Nmap Command Examples For Sys/Network AdminsDocument27 pagesCraft: Top 30 Nmap Command Examples For Sys/Network AdminsJoerdy LianuryNo ratings yet
- 4.2.2.5 Lab - Port Scanning An IoT DeviceDocument6 pages4.2.2.5 Lab - Port Scanning An IoT Devicemahin BhuiyanNo ratings yet
- Nmap Cheat SheetDocument8 pagesNmap Cheat SheetJABERO861108No ratings yet
- LAb 1Document9 pagesLAb 1Siti AisyahNo ratings yet
- Top 30 Nmap Command Examples For SysAdminsDocument8 pagesTop 30 Nmap Command Examples For SysAdminsYamabushi100% (1)
- Port ScannerDocument104 pagesPort Scannerreenasameer100% (1)
- Nmap SnortDocument63 pagesNmap SnortmibavudNo ratings yet
- Evaluation of Some Intrusion Detection and Vulnerability Assessment ToolsFrom EverandEvaluation of Some Intrusion Detection and Vulnerability Assessment ToolsNo ratings yet
- Overview of Some Windows and Linux Intrusion Detection ToolsFrom EverandOverview of Some Windows and Linux Intrusion Detection ToolsNo ratings yet
- Final CE141 CCP Practical ListDocument11 pagesFinal CE141 CCP Practical Listmann123456789No ratings yet
- Exercise 1. Fill in The BlanksDocument1 pageExercise 1. Fill in The Blanksmann123456789No ratings yet
- CBSE Practical 2016Document3 pagesCBSE Practical 2016mann123456789No ratings yet
- What Is The Ratio Between The Width and The Length of Our National Flag / Between Which Cities Does The Himasagar Express Run?Document3 pagesWhat Is The Ratio Between The Width and The Length of Our National Flag / Between Which Cities Does The Himasagar Express Run?mann123456789No ratings yet
- O Name of Student Unique ID No. DOB Class Section (Apr - Jun) (Jul - Sep) (Oct - Dec) (Jan - Mar) Admission Fee Total Quarterly Fee Payable 1 2 3 4Document1 pageO Name of Student Unique ID No. DOB Class Section (Apr - Jun) (Jul - Sep) (Oct - Dec) (Jan - Mar) Admission Fee Total Quarterly Fee Payable 1 2 3 4mann123456789No ratings yet
- Ans. The Expression For The Centripetal Acceleration. The Expression For The CentripetalDocument1 pageAns. The Expression For The Centripetal Acceleration. The Expression For The Centripetalmann123456789No ratings yet
- Solution of Triangle (MT)Document31 pagesSolution of Triangle (MT)mann123456789No ratings yet
- Final Prac Que Set1 2015Document2 pagesFinal Prac Que Set1 2015mann123456789No ratings yet
- CBSE Practical 2016Document3 pagesCBSE Practical 2016mann123456789No ratings yet
- De PDF Theory Notes 3 (MT)Document35 pagesDe PDF Theory Notes 3 (MT)mann12345678963% (8)
- Solution of Triangle (MT)Document31 pagesSolution of Triangle (MT)mann123456789No ratings yet
- Area Theory Notes (MT)Document18 pagesArea Theory Notes (MT)mann123456789No ratings yet
- TEST Paper-Math-III Ch-9, 10Document2 pagesTEST Paper-Math-III Ch-9, 10mann123456789No ratings yet
- Sahyog Mandli Jun-2016Document116 pagesSahyog Mandli Jun-2016mann123456789No ratings yet
- ORGANIC NamingDocument15 pagesORGANIC Namingapi-3835692100% (2)
- Moneytimes November07Document20 pagesMoneytimes November07ghachangfhuNo ratings yet
- Page 1 of 2 14H Motor Grader ASE00001-UP (MACHINE) POWERED BY 3176C Engine (SEB..Document2 pagesPage 1 of 2 14H Motor Grader ASE00001-UP (MACHINE) POWERED BY 3176C Engine (SEB..NovakurniawanNo ratings yet
- How To Sell Influencer Marketing To Your Clients Pitch Deck 1 1Document18 pagesHow To Sell Influencer Marketing To Your Clients Pitch Deck 1 1Hiral SoniNo ratings yet
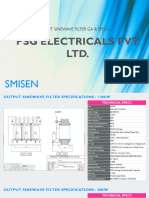
- Smisen Specs SCPL - 23-24 - SPC - PEPL - LCF - 01Document3 pagesSmisen Specs SCPL - 23-24 - SPC - PEPL - LCF - 01Glen CarterNo ratings yet
- 10 Continuous Improvement Strategies That Work 130412165110 Phpapp01Document42 pages10 Continuous Improvement Strategies That Work 130412165110 Phpapp01knabpshoNo ratings yet
- 03 2.1 Excavator Maintenance.Document59 pages03 2.1 Excavator Maintenance.felipe capistran100% (1)
- STM Lab 5,6,7Document20 pagesSTM Lab 5,6,7Kushal settulariNo ratings yet
- DunhamDocument32 pagesDunhamhjmmNo ratings yet
- Tips GAMEBOYDocument7 pagesTips GAMEBOYRaphael JolonNo ratings yet
- 2.2 & 2.3 CH 7 Creating Value Targeting & PositioningDocument4 pages2.2 & 2.3 CH 7 Creating Value Targeting & PositioningNgơTiênSinhNo ratings yet
- 101 Keyboard ShortcutDocument4 pages101 Keyboard ShortcutReney AzmiNo ratings yet
- 005056AE19D41EE99CC433064FA74A07Document1 page005056AE19D41EE99CC433064FA74A07Jan Reoven SialanaNo ratings yet
- Tubing and Fittings Quick Reference (Metric and Inch) - WebDocument9 pagesTubing and Fittings Quick Reference (Metric and Inch) - WebRajkumar MudaliarNo ratings yet
- Data Sheet, Gad, Sizing Calculation, Terminal Arrangement, Support Details of Bus Duct For New IntakeDocument2 pagesData Sheet, Gad, Sizing Calculation, Terminal Arrangement, Support Details of Bus Duct For New IntakeBasabRajNo ratings yet
- Actual Date Month Week Stage Work Parts Location Side Work To Be DoneDocument7 pagesActual Date Month Week Stage Work Parts Location Side Work To Be DoneEls YauNo ratings yet
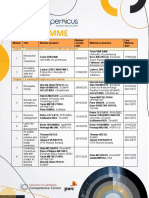
- Copernicus MOOC Programme 2nd EditionDocument2 pagesCopernicus MOOC Programme 2nd EditionGeo SpatialistNo ratings yet
- Resume Mohd Fahmi Bin AzlenDocument3 pagesResume Mohd Fahmi Bin AzlensethjihaNo ratings yet
- Form 172Document2 pagesForm 172ibrahimclassy1No ratings yet
- Ac 7 PDFDocument146 pagesAc 7 PDFMohammed Al-hewaimel100% (1)
- Daily Lesson Plan: Textbook / Activity BooksDocument1 pageDaily Lesson Plan: Textbook / Activity BooksAdri MailiNo ratings yet
- Vikas SharmaSGT Lab ManualDocument18 pagesVikas SharmaSGT Lab ManualAnand Mittal33% (3)
- Hiperfet Power Mosfets: V I R Ixfh 26N60/Ixft 26N60 600 V 26 A 0.25 Ixfk 28N60 600 V 28 A 0.25 T 250 NsDocument2 pagesHiperfet Power Mosfets: V I R Ixfh 26N60/Ixft 26N60 600 V 26 A 0.25 Ixfk 28N60 600 V 28 A 0.25 T 250 NsAmirNo ratings yet
- Fire Protection SystemsDocument20 pagesFire Protection Systemsmauco lopezNo ratings yet
- Heidenhain TNC 151 AP Service InstructionsDocument78 pagesHeidenhain TNC 151 AP Service InstructionsArtūrs CeimersNo ratings yet
- Lubrication Training - Basics of LubricationDocument35 pagesLubrication Training - Basics of LubricationFran JimenezNo ratings yet
- Civil Engineering Department: Project Management CC603Document12 pagesCivil Engineering Department: Project Management CC603shahrolhazrienNo ratings yet
- Öhlins Tools Manual: IncludingDocument32 pagesÖhlins Tools Manual: IncludingTiyok HidrolikNo ratings yet
- Starz HDTV Schedule - January, 2006Document8 pagesStarz HDTV Schedule - January, 2006Ben YoderNo ratings yet
Practical # 6 Tcp/Port Scanning Using Nmap (Use Zen Map)
Practical # 6 Tcp/Port Scanning Using Nmap (Use Zen Map)
Uploaded by
mann123456789Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Practical # 6 Tcp/Port Scanning Using Nmap (Use Zen Map)
Practical # 6 Tcp/Port Scanning Using Nmap (Use Zen Map)
Uploaded by
mann123456789Copyright:
Available Formats
Cyber Security (2150002)
Practical # 6
TCP/PORT SCANNING USING NMAP(use
Zen map)
Use of NMAP
Nmap (Network Mapper) is a security scanner originally written by Gordon
Lyon (also known by his pseudonym Fyodor Vaskovich) used to discover
hosts and services on a computer network, thus creating a "map" of the
network. To accomplish its goal, Nmap sends specially crafted packets to the
target host and then analyzes the responses.
Steps for port scan using NMAP
1. Download the Nmap installer. This can be found for free from the
developers website. It is highly recommended that you download
directly from the developer to avoid any potential viruses or fake files.
Downloading the Nmap installer includes Zenmap, the graphical
interface for Nmap which makes it easy for newcomers to perform
scans without having to learn command lines.
2. Install Nmap. Run the installer once it is finished downloading. You will
be asked which components you would like to install. In order to get
the full benefit of Nmap, keep all of these checked. Nmap will not
install any adware or spyware.
3. Run the Nmap Zenmap GUI program. If you left your settings at
default during installation, you should be able to see an icon for it on
Sumra Anish(131040109057)
Page 1
Cyber Security (2150002)
your desktop. If not, look in your Start menu. Opening Zenmap will
start the program.
4. Enter in the target for your scan. The Zenmap program makes
scanning a fairly simple process. The first step to running a scan is
choosing your target. You can enter a domain (example.com), an IP
address (127.0.0.1), a network (192.168.1.0/24), or a combination of
those. Depending on the intensity and target of your scan, running an
Nmap scan may be against the terms of your internet service provider,
and may land you in hot water. Always check your local laws and your
ISP contract before performing Nmap scans on targets other than your
own network.
5. Choose your Profile. Profiles are preset groupings of modifiers that
change what is scanned. The profiles allow you to quickly select
different types of scans without having to type in the modifiers on the
command line. Choose the profile that best fits your needs.
a. Intense scan - A comprehensive scan. Contains Operating
System (OS) detection, version detection, script scanning,
traceroute, and has aggressive scan timing. This is considered an
intrusive scan.
b. Ping scan - This scan simply detects if the targets are online, it
does not scan any ports.
c. Quick scan - This is quicker than a regular scan due to
aggressive timing and only scanning select ports.
d. Regular scan - This is the standard Nmap scan without any
modifiers. It will return ping and return open ports on the target.
6. Click Scan to start scanning. The active results of the scan will be
displayed in the Nmap Output tab. The time the scan takes will depend
Sumra Anish(131040109057)
Page 2
Cyber Security (2150002)
on the scan profile you chose, the physical distance to the target, and
the targets network configuration.
7. Read your results. Once the scan is finished, youll see the message
Nmap done at the bottom of the Nmap Output tab. You can now
check your results, depending on the type of scan you performed. All of
the results will be listed in the main Nmap Output tab, but you can use
the other tabs to get a better look at specific data.
a. Ports/Hosts - This tab will show the results of your port scan,
including the services for those ports.
b. Topology - This shows the trace route for the scan you performed. You
can see how many hops your data goes through to reach the target.
c. Host Details - This shows a summary of your target learned through
scans, such as the number of ports, IP addresses, hostnames,
operating systems, and more.
d. Scans - This tab stores the commands of your previously-run scans.
This allows you to quickly rescan with a specific set of parameters.
Sumra Anish(131040109057)
Page 3
You might also like
- Cascade Controller For DCDC Buck ConvertorDocument6 pagesCascade Controller For DCDC Buck ConvertorCristóbal Eduardo Carreño MosqueiraNo ratings yet
- What Is NmapDocument5 pagesWhat Is Nmapramya.gNo ratings yet
- Name: Pradeep Gupta Roll No: 112 Div: ADocument3 pagesName: Pradeep Gupta Roll No: 112 Div: APradeep GuptaNo ratings yet
- Lab 06 TaskDocument2 pagesLab 06 TaskZuraiz QureshiNo ratings yet
- CN - Exp-4Document4 pagesCN - Exp-4FLICKA 69No ratings yet
- Tutorial 3 - NmapDocument8 pagesTutorial 3 - Nmaplaytonchetty27No ratings yet
- VaptDocument21 pagesVaptSri GouriNo ratings yet
- Top 16 Nmap Commands To Scan Remote HostsDocument10 pagesTop 16 Nmap Commands To Scan Remote Hostsmindhackers161No ratings yet
- NmapDocument14 pagesNmapamird12No ratings yet
- Network Security Lab Manual DraftDocument29 pagesNetwork Security Lab Manual DraftShraddha PatilNo ratings yet
- Nmap Cheat Sheet From Discovery To Exploits - Part 1 Introduction To NmapDocument19 pagesNmap Cheat Sheet From Discovery To Exploits - Part 1 Introduction To Nmaparcalius7No ratings yet
- Lab Experiment #08 - Network & Host Detection ScansDocument3 pagesLab Experiment #08 - Network & Host Detection ScansAnoop DasNo ratings yet
- ED Nmap 110223 1642Document5 pagesED Nmap 110223 1642Murilo Zanardo Reis NogueiraNo ratings yet
- Lab Sheet 2Document9 pagesLab Sheet 2api-2414180090% (1)
- Networks Practical NmapDocument1 pageNetworks Practical Nmapbelkacem el kasmiNo ratings yet
- 3 NmapDocument6 pages3 NmapJohn WickNo ratings yet
- 3 NetworkSecurity LABManualDocument33 pages3 NetworkSecurity LABManualdahiyalkNo ratings yet
- NMAP - Information GatheringDocument6 pagesNMAP - Information GatheringRockstar GmailNo ratings yet
- NetworkSecurity LABManualDocument33 pagesNetworkSecurity LABManualvenkatdhanNo ratings yet
- NMAPDocument1 pageNMAPcaptnitro1No ratings yet
- 03 - Performing Security AssessmentsDocument78 pages03 - Performing Security AssessmentsDoraemonNo ratings yet
- Refresher Guide NmapDocument7 pagesRefresher Guide NmapmalinaNo ratings yet
- 03 - Performing Security AssessmentsDocument78 pages03 - Performing Security Assessmentsتيمور الجبورNo ratings yet
- Top 32 Nmap Command Examples For SysNetwork AdminsDocument16 pagesTop 32 Nmap Command Examples For SysNetwork AdminswizunuNo ratings yet
- Nmap All UsesDocument3 pagesNmap All UsesSaurabh SahuNo ratings yet
- Lab 5Document4 pagesLab 5Derick cheruyotNo ratings yet
- Lab IiiDocument14 pagesLab IiiKumar JiNo ratings yet
- NmapDocument3 pagesNmapAakanksha NNo ratings yet
- NMap - Network MappingDocument35 pagesNMap - Network MappingFaisal AR100% (4)
- IP Address and Port ScanningDocument4 pagesIP Address and Port Scanningreddy ramya sri ghantasalaNo ratings yet
- Project 7 Network Port ScanningDocument8 pagesProject 7 Network Port ScanningRahul GoyalNo ratings yet
- CIT 480: Securing Computer Systems Lab #7: Network Scanning NameDocument4 pagesCIT 480: Securing Computer Systems Lab #7: Network Scanning NameManzu PokharelNo ratings yet
- Nmap CommandDocument3 pagesNmap CommandKrishna ForuNo ratings yet
- Setup Lab Environment: MIT210 - Information Systems Security and AssuranceDocument12 pagesSetup Lab Environment: MIT210 - Information Systems Security and AssuranceJessa GalaponNo ratings yet
- Top 30 Nmap Command ExamplesDocument12 pagesTop 30 Nmap Command ExamplesvictorpetriniNo ratings yet
- Scanning NetworksDocument36 pagesScanning Networksjaya prasanna100% (2)
- Laboratory Setup: Step 1: Download Metasploitable, Which Is A Linux Machine. It Can Be Downloaded FromDocument13 pagesLaboratory Setup: Step 1: Download Metasploitable, Which Is A Linux Machine. It Can Be Downloaded FromTajria SultanaNo ratings yet
- NMAP WinDocument1 pageNMAP WinYassineNo ratings yet
- 8 24 23 NmapDocument13 pages8 24 23 NmapBALRAJ SINGHNo ratings yet
- Evaluation & Testing of Information AssetsDocument10 pagesEvaluation & Testing of Information AssetsMaksNo ratings yet
- Lab Manual CS 1-2Document23 pagesLab Manual CS 1-2Sandip MouryaNo ratings yet
- Nmap CommandsDocument17 pagesNmap CommandsAbhishekNo ratings yet
- 7 CNDocument11 pages7 CNAdfar RashidNo ratings yet
- Perform An Experiment For Port Scanning With Nmap, Superscan or Any Other Equivalent SoftwareDocument4 pagesPerform An Experiment For Port Scanning With Nmap, Superscan or Any Other Equivalent SoftwaresangeetadineshNo ratings yet
- Assignment 2Document2 pagesAssignment 2Mehul JainNo ratings yet
- Practice Exercises 4Document2 pagesPractice Exercises 4Tran TranNo ratings yet
- Foot PrintingDocument21 pagesFoot PrintingmwesigwaaNo ratings yet
- Security & Ethical Hacking p2Document29 pagesSecurity & Ethical Hacking p2Vipin NarangNo ratings yet
- MRTG NotesDocument24 pagesMRTG NotesErik Rafael Torres FernandezNo ratings yet
- NMap Tutorial For Beginners PDFDocument7 pagesNMap Tutorial For Beginners PDFzarakighostNo ratings yet
- Protecting and Port ScanningDocument3 pagesProtecting and Port ScanningShoua IqbalNo ratings yet
- NmapDocument14 pagesNmapayeshashafeeqNo ratings yet
- Craft: Top 30 Nmap Command Examples For Sys/Network AdminsDocument27 pagesCraft: Top 30 Nmap Command Examples For Sys/Network AdminsJoerdy LianuryNo ratings yet
- 4.2.2.5 Lab - Port Scanning An IoT DeviceDocument6 pages4.2.2.5 Lab - Port Scanning An IoT Devicemahin BhuiyanNo ratings yet
- Nmap Cheat SheetDocument8 pagesNmap Cheat SheetJABERO861108No ratings yet
- LAb 1Document9 pagesLAb 1Siti AisyahNo ratings yet
- Top 30 Nmap Command Examples For SysAdminsDocument8 pagesTop 30 Nmap Command Examples For SysAdminsYamabushi100% (1)
- Port ScannerDocument104 pagesPort Scannerreenasameer100% (1)
- Nmap SnortDocument63 pagesNmap SnortmibavudNo ratings yet
- Evaluation of Some Intrusion Detection and Vulnerability Assessment ToolsFrom EverandEvaluation of Some Intrusion Detection and Vulnerability Assessment ToolsNo ratings yet
- Overview of Some Windows and Linux Intrusion Detection ToolsFrom EverandOverview of Some Windows and Linux Intrusion Detection ToolsNo ratings yet
- Final CE141 CCP Practical ListDocument11 pagesFinal CE141 CCP Practical Listmann123456789No ratings yet
- Exercise 1. Fill in The BlanksDocument1 pageExercise 1. Fill in The Blanksmann123456789No ratings yet
- CBSE Practical 2016Document3 pagesCBSE Practical 2016mann123456789No ratings yet
- What Is The Ratio Between The Width and The Length of Our National Flag / Between Which Cities Does The Himasagar Express Run?Document3 pagesWhat Is The Ratio Between The Width and The Length of Our National Flag / Between Which Cities Does The Himasagar Express Run?mann123456789No ratings yet
- O Name of Student Unique ID No. DOB Class Section (Apr - Jun) (Jul - Sep) (Oct - Dec) (Jan - Mar) Admission Fee Total Quarterly Fee Payable 1 2 3 4Document1 pageO Name of Student Unique ID No. DOB Class Section (Apr - Jun) (Jul - Sep) (Oct - Dec) (Jan - Mar) Admission Fee Total Quarterly Fee Payable 1 2 3 4mann123456789No ratings yet
- Ans. The Expression For The Centripetal Acceleration. The Expression For The CentripetalDocument1 pageAns. The Expression For The Centripetal Acceleration. The Expression For The Centripetalmann123456789No ratings yet
- Solution of Triangle (MT)Document31 pagesSolution of Triangle (MT)mann123456789No ratings yet
- Final Prac Que Set1 2015Document2 pagesFinal Prac Que Set1 2015mann123456789No ratings yet
- CBSE Practical 2016Document3 pagesCBSE Practical 2016mann123456789No ratings yet
- De PDF Theory Notes 3 (MT)Document35 pagesDe PDF Theory Notes 3 (MT)mann12345678963% (8)
- Solution of Triangle (MT)Document31 pagesSolution of Triangle (MT)mann123456789No ratings yet
- Area Theory Notes (MT)Document18 pagesArea Theory Notes (MT)mann123456789No ratings yet
- TEST Paper-Math-III Ch-9, 10Document2 pagesTEST Paper-Math-III Ch-9, 10mann123456789No ratings yet
- Sahyog Mandli Jun-2016Document116 pagesSahyog Mandli Jun-2016mann123456789No ratings yet
- ORGANIC NamingDocument15 pagesORGANIC Namingapi-3835692100% (2)
- Moneytimes November07Document20 pagesMoneytimes November07ghachangfhuNo ratings yet
- Page 1 of 2 14H Motor Grader ASE00001-UP (MACHINE) POWERED BY 3176C Engine (SEB..Document2 pagesPage 1 of 2 14H Motor Grader ASE00001-UP (MACHINE) POWERED BY 3176C Engine (SEB..NovakurniawanNo ratings yet
- How To Sell Influencer Marketing To Your Clients Pitch Deck 1 1Document18 pagesHow To Sell Influencer Marketing To Your Clients Pitch Deck 1 1Hiral SoniNo ratings yet
- Smisen Specs SCPL - 23-24 - SPC - PEPL - LCF - 01Document3 pagesSmisen Specs SCPL - 23-24 - SPC - PEPL - LCF - 01Glen CarterNo ratings yet
- 10 Continuous Improvement Strategies That Work 130412165110 Phpapp01Document42 pages10 Continuous Improvement Strategies That Work 130412165110 Phpapp01knabpshoNo ratings yet
- 03 2.1 Excavator Maintenance.Document59 pages03 2.1 Excavator Maintenance.felipe capistran100% (1)
- STM Lab 5,6,7Document20 pagesSTM Lab 5,6,7Kushal settulariNo ratings yet
- DunhamDocument32 pagesDunhamhjmmNo ratings yet
- Tips GAMEBOYDocument7 pagesTips GAMEBOYRaphael JolonNo ratings yet
- 2.2 & 2.3 CH 7 Creating Value Targeting & PositioningDocument4 pages2.2 & 2.3 CH 7 Creating Value Targeting & PositioningNgơTiênSinhNo ratings yet
- 101 Keyboard ShortcutDocument4 pages101 Keyboard ShortcutReney AzmiNo ratings yet
- 005056AE19D41EE99CC433064FA74A07Document1 page005056AE19D41EE99CC433064FA74A07Jan Reoven SialanaNo ratings yet
- Tubing and Fittings Quick Reference (Metric and Inch) - WebDocument9 pagesTubing and Fittings Quick Reference (Metric and Inch) - WebRajkumar MudaliarNo ratings yet
- Data Sheet, Gad, Sizing Calculation, Terminal Arrangement, Support Details of Bus Duct For New IntakeDocument2 pagesData Sheet, Gad, Sizing Calculation, Terminal Arrangement, Support Details of Bus Duct For New IntakeBasabRajNo ratings yet
- Actual Date Month Week Stage Work Parts Location Side Work To Be DoneDocument7 pagesActual Date Month Week Stage Work Parts Location Side Work To Be DoneEls YauNo ratings yet
- Copernicus MOOC Programme 2nd EditionDocument2 pagesCopernicus MOOC Programme 2nd EditionGeo SpatialistNo ratings yet
- Resume Mohd Fahmi Bin AzlenDocument3 pagesResume Mohd Fahmi Bin AzlensethjihaNo ratings yet
- Form 172Document2 pagesForm 172ibrahimclassy1No ratings yet
- Ac 7 PDFDocument146 pagesAc 7 PDFMohammed Al-hewaimel100% (1)
- Daily Lesson Plan: Textbook / Activity BooksDocument1 pageDaily Lesson Plan: Textbook / Activity BooksAdri MailiNo ratings yet
- Vikas SharmaSGT Lab ManualDocument18 pagesVikas SharmaSGT Lab ManualAnand Mittal33% (3)
- Hiperfet Power Mosfets: V I R Ixfh 26N60/Ixft 26N60 600 V 26 A 0.25 Ixfk 28N60 600 V 28 A 0.25 T 250 NsDocument2 pagesHiperfet Power Mosfets: V I R Ixfh 26N60/Ixft 26N60 600 V 26 A 0.25 Ixfk 28N60 600 V 28 A 0.25 T 250 NsAmirNo ratings yet
- Fire Protection SystemsDocument20 pagesFire Protection Systemsmauco lopezNo ratings yet
- Heidenhain TNC 151 AP Service InstructionsDocument78 pagesHeidenhain TNC 151 AP Service InstructionsArtūrs CeimersNo ratings yet
- Lubrication Training - Basics of LubricationDocument35 pagesLubrication Training - Basics of LubricationFran JimenezNo ratings yet
- Civil Engineering Department: Project Management CC603Document12 pagesCivil Engineering Department: Project Management CC603shahrolhazrienNo ratings yet
- Öhlins Tools Manual: IncludingDocument32 pagesÖhlins Tools Manual: IncludingTiyok HidrolikNo ratings yet
- Starz HDTV Schedule - January, 2006Document8 pagesStarz HDTV Schedule - January, 2006Ben YoderNo ratings yet