Professional Documents
Culture Documents
Logical Design 3.1 File Design: Agency Customer
Logical Design 3.1 File Design: Agency Customer
Uploaded by
nklharish1Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Logical Design 3.1 File Design: Agency Customer
Logical Design 3.1 File Design: Agency Customer
Uploaded by
nklharish1Copyright:
Available Formats
LOGICAL DESIGN
3.1 FILE DESIGN
The files are been protected using the username and password as key and by using the
transposition cipher technique where the content of the file will be changed into cipher data
which cannot be understood even by the administrator. By doing this the data is completely
secured. Only after decrypting the file the data can be understood by the administrator by
using the same key and password.
3.2INPUT DESIGN
Various forms of project collaboration exist, e.g. business-to-consumer (b2c) between
companies and clients, business-to-business (b2b) among companies organized, for example,
as virtual enterprises, and vertical hierarchic b2b between a prime contractor and its legally
independent subcontractors.
The pure act of commercial transaction in typical b2c markets is short.
Communication is usually reduced to filling out online forms. In the context of projects,
where the product is particularly designed for the client, the need for exchange of information
is considerably higher. Possible fields of applications in this area include all forms of digital
products. The clients can be interactively integrated in the product development cycle via the
Internet, due to its foremost characteristics like availability, low costs, speed, audio and visual
capabilities and ease of use. The agency will publish its work to their clients, whereas the
clients just contribute to the process by giving comments and proposals, see Fig. 1. Agencies
state that they do not want the clients to change drafts by themselves, but rather want the
clients to submit change proposals.
1st Draft,
Proposal
Comment
Agency Customer
2nd Draft,
Final
Figure 1: Customer Integration
This form of interaction between agency and customer enhances and
simultaneously documents the creation process of the desired product. Incoming drafts and
comments as well as the complete history and progress of the development process are being
documented. Thus, we not only have collaborative CRM by using a communication center
and communication 7
bridges between company and customer. We additionally have integrated the customer in the
production process, which further enhances analytical CRM providing crucial customer data.
The model of collaboration among companies differs from the client integrated case in
such a way that the participants are meant to agitate with equal rights. Therefore, all actors are
equipped with equivalent access rights and contribute to the project by developing parts of the
project, see Fig. 2. They do not necessarily interact in all segments of the project. As in the
previously mentioned b2c case, project participants have the latest information and the history
of the ongoing project at their fingertips, at any time and at any place, as long as there is an
Internet connection available.
Company 2
Drafts, Comments
Proposals,
Finals Customer
Drafts, Comments
Proposals,
Finals
Comments
Company 1
Drafts,
Proposals,
Finals Comments
Company 3
Figure 2: Collaboration among Companies
At first sight, a b2b collaboration setting does not require any customer-relationship
management, because there are no customers involved. However, if both the virtual enterprise
and its customers use the same Internet platform, individual companies can access CRM data
both about the customers and about other participating companies.
Hierarchical b2b is characterized by precisely defined contracts with definite
structures of responsibilities and dependencies. Tasks are passed on top-down. The flow of
execution reports from the bottom up. This arrangement usually occurs in the context of
proposal requests, e.g., for the planning of construction projects. In the example in Fig. 3, a
prime contractor initiates an invitation to bid for several possible subcontracts. Potential
subcontractors have the possibility to submit their proposal or pass a complete or part of the
requested workload to further subcontractors. The prime contractor does not have insight into
the complete process. After receiving all proposals from potential direct subcontractors, the
prime contractor accepts favored proposals and the contracts may be signed. It is important to
ensure that all contractors are just exposed to the part of the process and the project structure
that they are responsible for. This is achieved by security mechanisms and the distribution of
different access rights. Due to reasons of acceptance it is appropriate to store project
information at independent service providers or a superordinate association which may
provide the needed infrastructure.
8
Prime
1
Request PC Contractor
7 2
3
Proposal SC1
Sub
6
Proposal SC2 Contractors I
3
5
4
Proposal SC21 Sub
Proposal
4
SC Contractors II
22
Figure 3: Collaboration with Subcontractors
In this scenario, we have a net of company-client relationships, where none of the
participants may have full information about the entire setting. Communication to and
information about the client is restricted to the prime contractor. Any subcontractors are only
involved in communication with their subcontractors, of which they are the clients, and with
their prime contractor, which is their client. CRM is complex in this scenario with nobody
having full view to the complete project structure and to the complete CRM information that
is available. In this case CRM principles can be applied on any stage, as any company, except
the ones residing on the bottom, can act as a client for a subordinated company in the
hierarchy.
3.4 DATABASE DESIGN
All operations relating to database is carried out in this module Including:
Create company
Edit/ Delete company
Back up
Restore
The module in which initial details needed are stored
Including:
Account group
Account ledger
Shelf
Generic name
Product group
Product batch
Unit
Product
Manufacture
Vendor
Sales man
Daily customer
Greeting text
You might also like
- Low-Code/No-Code: Citizen Developers and the Surprising Future of Business ApplicationsFrom EverandLow-Code/No-Code: Citizen Developers and the Surprising Future of Business ApplicationsRating: 2.5 out of 5 stars2.5/5 (2)
- Day Trading 4 Dummies PDFDocument47 pagesDay Trading 4 Dummies PDFPeterVUSA100% (1)
- A Comparison Between Silver Book and The Enaa Model FormDocument8 pagesA Comparison Between Silver Book and The Enaa Model FormMdms Payoe100% (1)
- CCDC Documents DescriptionsDocument6 pagesCCDC Documents Descriptionsmynalawal100% (1)
- Corporate Venture Studios DirectoryDocument12 pagesCorporate Venture Studios Directorymoctapka0880% (1)
- Pam ContractDocument21 pagesPam Contractteeyuan100% (6)
- One Island East: Hong KongDocument11 pagesOne Island East: Hong KongKashyap Patel100% (1)
- Media Planning and Buying: Notes and PPT by Prof - Chahat HargunaniDocument35 pagesMedia Planning and Buying: Notes and PPT by Prof - Chahat HargunaniHarsha Bulani Chahat Hargunani100% (1)
- Jacksonville Jaguars Media PlanDocument14 pagesJacksonville Jaguars Media PlanOakenshield1100% (1)
- Bidding Documents For Procurement of WorksDocument209 pagesBidding Documents For Procurement of Worksggvn adminNo ratings yet
- Cpix On Line: Pre-Contract Building Information Modelling (Bim) Execution Plan (Bep)Document11 pagesCpix On Line: Pre-Contract Building Information Modelling (Bim) Execution Plan (Bep)Himang JainNo ratings yet
- NBIMS-US V3 5.8 Practical BIM Contract RequirementsDocument15 pagesNBIMS-US V3 5.8 Practical BIM Contract Requirementsmahmoud mokhtarNo ratings yet
- Bim Protocol 2nd Edition 2Document24 pagesBim Protocol 2nd Edition 2Nadia Dyorota Magdalena AdyamcyzkovnaNo ratings yet
- 7projdelivery 2010 (Web)Document16 pages7projdelivery 2010 (Web)N.a. M. TandayagNo ratings yet
- TML - PS Manual Version 0.1Document76 pagesTML - PS Manual Version 0.1prithviNo ratings yet
- Mosey, David. PPC 2000 - The First Standard Form of Contract For Project PartneringDocument18 pagesMosey, David. PPC 2000 - The First Standard Form of Contract For Project Partnering1NFORMA2 1nforma2No ratings yet
- Project Name Business Requirements Document: VersionDocument7 pagesProject Name Business Requirements Document: VersionTulasi MNo ratings yet
- Framework - For - Assessment - and - Recognition - of - Competencies - 2012 - 04 - 26Document90 pagesFramework - For - Assessment - and - Recognition - of - Competencies - 2012 - 04 - 26Mohammad Mohsin BaigNo ratings yet
- SCM in Construction Industry: Deepak Ojha Roll No. 5 Div II (E)Document20 pagesSCM in Construction Industry: Deepak Ojha Roll No. 5 Div II (E)Deepak D OjhaNo ratings yet
- Article On ECI Under NECDocument11 pagesArticle On ECI Under NECPvvg PrasadNo ratings yet
- e-D&B Works - Single Tage Without Prequalification (One EnvelopeDocument140 pagese-D&B Works - Single Tage Without Prequalification (One EnvelopeVIKASH PEERTHYNo ratings yet
- Municipal Corporation of Greater Mumbai: User Manual of Sewerage NOC Application For Licensed ArchitectDocument16 pagesMunicipal Corporation of Greater Mumbai: User Manual of Sewerage NOC Application For Licensed ArchitectMrigank AggarwalNo ratings yet
- ContracttypesDocument4 pagesContracttypesAhmed FaresNo ratings yet
- e-D&B Works - Single Stage Without Prequaliifcation (Two Envelopes)Document144 pagese-D&B Works - Single Stage Without Prequaliifcation (Two Envelopes)VIKASH PEERTHYNo ratings yet
- Procurement Manual - FinalDocument23 pagesProcurement Manual - FinalThushara BandaraNo ratings yet
- Sample Bidding Documents Under Japanese ODA Loans (Design Build)Document291 pagesSample Bidding Documents Under Japanese ODA Loans (Design Build)lwin_oo2435No ratings yet
- Page 1 of 32Document32 pagesPage 1 of 32Abhay KumarNo ratings yet
- FIDIC, NEC & JCT Disputes Clauses - Muhammad Anamul HoqueDocument20 pagesFIDIC, NEC & JCT Disputes Clauses - Muhammad Anamul HoqueMuhammad Anamul HoqueNo ratings yet
- FIDIC, NEC & JCT Disputes Clauses - Muhammad Anamul HoqueDocument20 pagesFIDIC, NEC & JCT Disputes Clauses - Muhammad Anamul HoqueMuhammad Anamul HoqueNo ratings yet
- Capital Programs User Guide:: Massachusetts Bay Transportation AuthorityDocument9 pagesCapital Programs User Guide:: Massachusetts Bay Transportation AuthorityYared YitbarekNo ratings yet
- Process of Matching Work Items Between Bim Model and Cost Estimating Software2018Document9 pagesProcess of Matching Work Items Between Bim Model and Cost Estimating Software2018Anita GutierrezNo ratings yet
- Green and Sustainable Design: Rating System - IgbcDocument14 pagesGreen and Sustainable Design: Rating System - IgbcMADHU MITHANo ratings yet
- 01-Contracts and The SurveyorDocument48 pages01-Contracts and The SurveyorJoanne TanNo ratings yet
- Comperative Analysis of Three Major Type of Contracts With Case StudyDocument4 pagesComperative Analysis of Three Major Type of Contracts With Case StudyGroot AvengerNo ratings yet
- Application of BIM in Arbitration and Its Legal PerspectiveDocument4 pagesApplication of BIM in Arbitration and Its Legal PerspectiveFrancisco VeraNo ratings yet
- Cic/Bim Pro Building Information Model (BIM) Protocol University of CambridgeDocument21 pagesCic/Bim Pro Building Information Model (BIM) Protocol University of Cambridgeخالد هراسNo ratings yet
- Cic Bim Protocol PDFDocument3 pagesCic Bim Protocol PDFFacundo ContrerasNo ratings yet
- BIM Execution Plan: Phase II - ConstructionDocument26 pagesBIM Execution Plan: Phase II - ConstructionFayyazAhmadNo ratings yet
- Bac 1Document2 pagesBac 1KE GOH CHEWNo ratings yet
- Capstone ReportDocument14 pagesCapstone Reportapi-497949503No ratings yet
- Dan Stroescu - Module 2 - The EIRDocument10 pagesDan Stroescu - Module 2 - The EIRDan StroescuNo ratings yet
- 2017 08 02 18 47 18 SRFP - PS12 - 85Document100 pages2017 08 02 18 47 18 SRFP - PS12 - 85HumayunNo ratings yet
- BIM Execution Planning (BEP) TranscriptDocument5 pagesBIM Execution Planning (BEP) Transcriptxpipespipescom100% (1)
- Business Requirements Document (BRD) Template: Tech Comm TemplatesDocument9 pagesBusiness Requirements Document (BRD) Template: Tech Comm TemplatesHuyền KikukaiNo ratings yet
- BRD Template TechDocument10 pagesBRD Template TechNghiêm Đức Hiếu - B19DCAT067No ratings yet
- CIC BIM Protocol University of CambridgeDocument21 pagesCIC BIM Protocol University of CambridgeLuis Fernando RodriguezNo ratings yet
- Chapter-2 Pre-Planning PhaseDocument24 pagesChapter-2 Pre-Planning PhaseAmanuel AlemayehuNo ratings yet
- 1st Step of Tendering Process-Decision To Tender Quantity Surveyor BlogDocument3 pages1st Step of Tendering Process-Decision To Tender Quantity Surveyor BlogShashank BahiratNo ratings yet
- IEM Vs PAM Form-COCDocument25 pagesIEM Vs PAM Form-COCNadia Izzati100% (1)
- Articulo Del CMDocument11 pagesArticulo Del CMCarlos Alberto Ayvar GonzalesNo ratings yet
- Auto Deals ProposalDocument30 pagesAuto Deals Proposalsaqib_dNo ratings yet
- Design Build Project - QS Practice 1 Sergio RevDocument13 pagesDesign Build Project - QS Practice 1 Sergio RevSérgio FariaNo ratings yet
- Chun Wo - Technical Note 005Document3 pagesChun Wo - Technical Note 005Paul KwongNo ratings yet
- Project Monitoring System: in NTPCDocument38 pagesProject Monitoring System: in NTPCTrilok Singh TakuliNo ratings yet
- 2011 - Design Bid Build (Web)Document4 pages2011 - Design Bid Build (Web)Assa SafitriNo ratings yet
- Comperative Analysis of Three Major Type of Contracts With Case StudyDocument5 pagesComperative Analysis of Three Major Type of Contracts With Case StudyGroot AvengerNo ratings yet
- Building Information Modelling Its Impact On Design Liability, Insurance and Intellectual Property RightsDocument17 pagesBuilding Information Modelling Its Impact On Design Liability, Insurance and Intellectual Property RightsNOUNo ratings yet
- Basic Things You Should Know About Bill of Quantity (BOQ) - Basic Civil EngineeringDocument3 pagesBasic Things You Should Know About Bill of Quantity (BOQ) - Basic Civil Engineeringaldeto71No ratings yet
- Commercial Building Proposal - Rev2Document6 pagesCommercial Building Proposal - Rev2Joel BautistaNo ratings yet
- Ictpmg613 - At2 ProjectDocument21 pagesIctpmg613 - At2 Projectkinsgyel11No ratings yet
- Contract: Frequently Asked QuestionsDocument52 pagesContract: Frequently Asked QuestionsMilan UljarevicNo ratings yet
- 35 EnglishDocument37 pages35 Englisholga.a.manyakinaNo ratings yet
- Difference Between PMC & Engineering ContractorDocument2 pagesDifference Between PMC & Engineering ContractorMustafa AhsanNo ratings yet
- MMC Guidance NoteDocument22 pagesMMC Guidance NoteMILL3482No ratings yet
- Arduino Based Automatic Pneumatic SystemDocument31 pagesArduino Based Automatic Pneumatic Systemnklharish1No ratings yet
- Connection of Converters To A Low and Medium Power DC Network Using An Inductor CircuitDocument3 pagesConnection of Converters To A Low and Medium Power DC Network Using An Inductor Circuitnklharish1No ratings yet
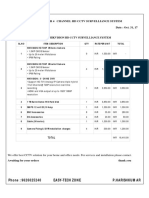
- Product: Hikvision HD CCTV Survelliance System: Phone: 9626025240 Easy-Tech Zone P.HarishkumarDocument2 pagesProduct: Hikvision HD CCTV Survelliance System: Phone: 9626025240 Easy-Tech Zone P.Harishkumarnklharish1No ratings yet
- HyperText Markup LanguageDocument3 pagesHyperText Markup Languagenklharish1No ratings yet
- HR ManageDocument47 pagesHR Managenklharish1No ratings yet
- Ijsrp p35101 PDFDocument24 pagesIjsrp p35101 PDFnklharish1No ratings yet
- Quotation No: 304 Date: 07/06/2016: Quotation For HD CCTV Survelliance SystemDocument2 pagesQuotation No: 304 Date: 07/06/2016: Quotation For HD CCTV Survelliance Systemnklharish1No ratings yet
- 10-11-2016 - The Hindu - Shashi ThakurDocument26 pages10-11-2016 - The Hindu - Shashi ThakurSunilSainiNo ratings yet
- Asia Pacific Shopping Center Definition Standard Proposal PDFDocument18 pagesAsia Pacific Shopping Center Definition Standard Proposal PDFwitanti nur utamiNo ratings yet
- SOA TemplateDocument1 pageSOA TemplateNoorasyaLya RozikinNo ratings yet
- Commissioner of Internal Revenue Vs TMX Sales Inc Et Al 205 SCRA 184 PDFDocument6 pagesCommissioner of Internal Revenue Vs TMX Sales Inc Et Al 205 SCRA 184 PDFTAU MU OFFICIALNo ratings yet
- 02 & 12 - Anup & Hitesh - Jubilant FoodWorks LTDDocument10 pages02 & 12 - Anup & Hitesh - Jubilant FoodWorks LTDasitbhatiaNo ratings yet
- New Look Warrenty LetterDocument4 pagesNew Look Warrenty Lettersujata1013No ratings yet
- Björn Raake AccentureConsultingDocument2 pagesBjörn Raake AccentureConsultingbjörnNo ratings yet
- Inb 372 Course OutlineDocument4 pagesInb 372 Course OutlineMd SabirNo ratings yet
- Tender No. SH/013/2017-2019 For Supply of Cleaning Materials, Detergents and DisinfectantDocument37 pagesTender No. SH/013/2017-2019 For Supply of Cleaning Materials, Detergents and DisinfectantState House Kenya100% (4)
- My Value Trade Equity DP NSDL FormDocument56 pagesMy Value Trade Equity DP NSDL FormchetanjecNo ratings yet
- Marketing Final ReportDocument70 pagesMarketing Final Reportsatya0% (1)
- MGMT627 - Project Management Midterm MCQ'S: 1.1 True/FalseDocument39 pagesMGMT627 - Project Management Midterm MCQ'S: 1.1 True/FalsePravir SinghNo ratings yet
- Accounts Payable: Oracle Fusion FinancialsDocument20 pagesAccounts Payable: Oracle Fusion Financialsmaha AhmedNo ratings yet
- Decision Science Project Report On "Big Data"Document9 pagesDecision Science Project Report On "Big Data"Satyajit ChatterjeeNo ratings yet
- SachinDocument43 pagesSachinsachin patraNo ratings yet
- Asia Lighterage & Shipping Vs CA - G.R. No. 147246. August 19, 2003Document6 pagesAsia Lighterage & Shipping Vs CA - G.R. No. 147246. August 19, 2003Ebbe DyNo ratings yet
- City of Paranaque Ordinance No. 31 Series of 2011 2Document3 pagesCity of Paranaque Ordinance No. 31 Series of 2011 2Jo Mary LudovicoNo ratings yet
- Day 1 Employee Quickstart Equinix Template v11Document13 pagesDay 1 Employee Quickstart Equinix Template v11Anonymous IFc0l5DLNo ratings yet
- Receiving Inspection ProcedureDocument2 pagesReceiving Inspection ProcedureErwin SantosoNo ratings yet
- The Anjuman Wazifa DIRECTOARY1Document25 pagesThe Anjuman Wazifa DIRECTOARY1Shoaib Raza JafriNo ratings yet
- As 3565.4-2007 Meters For Water Supply In-Service Compliance TestingDocument8 pagesAs 3565.4-2007 Meters For Water Supply In-Service Compliance TestingSAI Global - APACNo ratings yet
- tmpD7DE TMPDocument167 pagestmpD7DE TMPFrontiers100% (1)
- Stst3002 Op EdDocument3 pagesStst3002 Op EdEmma ChenNo ratings yet
- Class 8 Profit and LossDocument1 pageClass 8 Profit and LossPoojitha PottiNo ratings yet
- IBM Cognos 8 4 1 Administration and Security GuideDocument841 pagesIBM Cognos 8 4 1 Administration and Security GuidecoolcapsiNo ratings yet
- Introduction To AuditingDocument24 pagesIntroduction To AuditingVinayak SaxenaNo ratings yet