Professional Documents
Culture Documents
Hipaa Risk Analysis
Hipaa Risk Analysis
Uploaded by
Bayu Bacharuddin YahyaOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Hipaa Risk Analysis
Hipaa Risk Analysis
Uploaded by
Bayu Bacharuddin YahyaCopyright:
Available Formats
UCSC HIPAA Security Rule Risk Analysis
Date:
Unit:
Contact (name and email):
Purpose:
This template provides an approach for assessing risk to Electronic Protected Health Information (ePHI) in your department. This template is
based on:
Office for Civil Rights (OCR) HIPAA Security Standards: Guidance on Risk Analysis Requirements under the HIPAA Security Rule -
http://www.hhs.gov/ocr/privacy/hipaa/administrative/securityrule/rafinalguidancepdf.pdf
Dept. of Health and Human Service (HHS) HIPAA Security Series: Basics of Risk Analysis and Risk Management
-http://www.hhs.gov/ocr/privacy/hipaa/administrative/securityrule/riskassessment.pdf
UCSC's Practices for HIPAA Security Rule Compliance: http://its.ucsc.edu/policies/hipaa-practices.html
Each UCSC unit that works with ePHI is required to complete a risk analysis for that data. This template is a suggested way to complete that risk
analysis and begin the process of risk management. Completed risk analyses are to be maintained by the unit and also submitted to the campus
HIPAA Security Official for review.
Disclaimer:
This template has been developed for UCSC HIPAA entities as a tool in the process of analyzing and documenting risk to ePHI, as required
under HIPAA. It is based on industry best practice, and has been targeted for our environment. UCSC makes no guarantee of compliance based
on completion of this form.
Any data collected as a result of using this template, including the completed analysis, itself, should be considered sensitive and confidential and
must be safeguarded as such.
Please direct questions to the office of the campus HIPAA Security Official: itpolicy@ucsc.edu
Template Rev. 12/19/13 Page 1 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Inventory:
Identify where ePHI is created, stored, received, or transmitted. This includes identifying external sources of ePHI, such as vendors or
consultants who create, receive, maintain or transmit ePHI. Also indicate whether there is a documented process for updating the inventory.
Template Rev. 12/19/13 Page 2 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Access:
Identify who can access ePHI (intentional and risk of unintentional). Identification by role is acceptable.
Template Rev. 12/19/13 Page 3 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Definitions:
Maturity Levels (from IS-3 Assessment) from CobIT, v 4.1
0 Non-Existent: Complete lack of any recognizable processes. The institution has not even recognized that there is an issue to be
addressed.
1 Initial/Ad-Hoc: There is evidence that the institution has recognized that the issues exist and need to be addressed. There are,
however, no standardized processes; instead, there are ad hoc approaches that tend to be applied on an individual or case-by-case basis.
The overall approach to management is disorganized.
2 Repeatable but Intuitive: Processes have developed to the stage where similar procedures are followed by different people
undertaking the same task. There is no formal training or communication of standard procedures, and responsibility is left to the
individual. There is a high degree of reliance on the knowledge of individuals and, therefore, errors are likely.
3 Defined Process: Procedures have been standardized and documented, and communicated through training. It is mandated that these
processes should be followed; however, it is unlikely that deviations will be detected. The procedures themselves are not sophisticated
but are the formalization of existing practices.
4 Managed and Measurable: Management monitors and measures compliance with procedures and takes action where processes
appear not to be working effectively. Processes are under constant improvement and provide good practice. Automation and tools are
used in a limited or fragmented way.
5 Optimized: Processes have been refined to a level of good practice, based on the results of continuous improvement and maturity
modeling with other enterprises. IT is used in an integrated way to automate the workflow, providing tools to improve quality and
effectiveness, making the enterprise quick to adapt.
Template Rev. 12/19/13 Page 4 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Definitions (cont.)
Likelihood Level Likelihood Definition Magnitude of Impact Impact Definition
High (1.0) The threat-source is highly motivated and High (100) Exercise of the vulnerability (1) may result in the very
sufficiently capable, and controls to costly loss of major tangible assets or resources; (2)
prevent the vulnerability from being may significantly violate, harm, or impede an
exercised are ineffective. organizations function, reputation, or interest; or (3)
may result in human death or serious injury.
Medium (0.5) The threat-source is motivated and Medium (50-90) Exercise of the vulnerability (1) may result in the costly
capable, but controls are in place that loss of tangible assets or resources; (2) may violate,
may impede successful exercise of the harm, or impede an organizations function, reputation,
vulnerability. or interest; or (3) may result in human injury.
Low (0.1) The threat-source lacks motivation or Low (10-40) Exercise of the vulnerability (1) may result in the loss of
capability, or controls are in place to some tangible assets or resources or (2) may
prevent, or at least significantly impede, noticeably affect an organizations function, reputation,
the vulnerability from being exercised. or interest.
Risk Calculation Table and Examples:
Threat Impact if Threat Occurs
Likelihood of Occurrence
Given Existing Controls Low (10-40) Medium (50-90) High (100)
High (1.0) 10 x 1.0 = 10 50 x 1.0 = 50 100 x 1.0 = 100
Medium (0.5) 10 x 0.5 = 5 50 x 0.5 = 25 100 x 0.5 = 50
Low (0.1) 10 x 0.1 = 1 50 x 0.1 = 5 100 x 0.1 = 10
Risk Levels:
Risk = Likelihood x Impact
0-9 = Low
10-49 = Medium
50-100 = High
Template Rev. 12/19/13 Page 5 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Template Rev. 12/19/13 Page 6 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Security Risk Matrix
Instructions:
1. Assess whether each security concern in the matrix below applies to your unit or not. For items that aren't applicable, indicate N/A and a
reason. Leave everything else blank for the N/A items.
2. For each security concern that applies to your unit:
a) Identify the existing mitigations/controls
Please note that the questions in italics in the "Existing Mitigations/Controls" boxes of the template are examples of
possible controls, not a list of requirements for HIPAA compliance. Replace the questions with actual, existing
mitigations/controls.
Although the questions are examples, they should all be considered. If the answer to any of the questions is "no,"
consider whether that implies a risk that should be addressed in the "Next Steps" column (see e, below).
b) Indicate the Maturity Level of each existing mitigation/control (see page 4)
c) Indicate the Likelihood and Impact (high/med/low see page 5) of each concern actually happening given the controls currently in place
d) Calculate the residual risk level by multiplying Likelihood x Impact (see page 5)
e) Next Steps: If the residual risk (if any) is not accepted as-is, identify any next steps (action items and owners) needed to further
mitigate the risk to an acceptable level, along with the effort/cost associated with each action item.
3. Add any unit-specific security concerns in the available boxes at the end.
Template Rev. 12/19/13 Page 7 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
1. [System] 1. Are patches current?* 1. 1. HML/HML
Data accessed or
2. Have default passwords been 2. 2. 1.
corrupted by hacker
changed? 3. 3. 2.
through exploiting OS or
application/ database 3. Are unnecessary services disabled?* 4. 3.
weaknesses. 4. Are firewalls installed/enabled?* 5.
5. Is access to databases/applications 6.
Summary: [Is residual technically limited based on IP
7.
risk accepted?] address, domain, or VPN?
8. High/ High/ High/
6. Are proper software development/ Med/ Med/ Med/
coding practices used for in-house Low Low Low
apps?
7. Is a host-based intrusion detection/
prevention system (HIDS/HIPS)1
used?
8. Are DB/file access monitoring/
alerting applications used (e.g.
Imperva, IBM Guardium, etc.)?
9. Is printer software kept up to date?
1
Host-based intrusion detection/prevention system (HIDS/HIPS): Host based intrusion prevention system (HIDS)/host based intrusion prevention system (HIPS). These are software packages
installed on a host system that detect attacks against the host and take action against such attacks, such as tuning host based firewall rules to shunt/block attacking IPs. Tools such as Blackice
Defender, Verisys, Tripwire, and OSSEC (which is what IT Security uses) would be considered HIDS/HIPS apps.
Template Rev. 12/19/13 Page 8 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
2. [System/Human] 1. Does the server have anti-phishing 1. 1. HML/HML
Disclosure due to controls? 2. 2. 1.
unauthorized account
2. Is instant messaging (IM) 3. 3. 2.
access (shared, stolen,
controlled?
hacked, phished 4. 3.
credentials) 3. Are users educated about IM &
5.
email safety, phishing, phone
scams, other social engineering, 6.
Summary: [Is residual
password policy? 7.
risk accepted?]
4. Are individuals issued unique 8.
accounts for access to ePHI? 9.
5. Are strong passwords technically 10.
enforced where possible? 11.
6. Are apps set not to remember
High/ High/ High/
passwords?
Med/ Med/ Med/
7. Is anti-virus/anti-malware Low Low Low
current?*
8. Is installation of unauthorized
applications disallowed (technically
or procedurally)?
9. Are session timeouts/screen locking
administratively and technically
enforced including for
workstations with shared or
generic logins, if any?*
10. Is HIDS/HIPS1 used?
11. Are authentication systems
periodically tested and upgraded
when upgrades are available?
Template Rev. 12/19/13 Page 9 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
3. [System] 1. Is anti-virus/anti-malware 1. 1. HML/HML
Data loss, disclosure, or current?* 2. 2. 1.
inability to access data
2. Is more than one anti-virus being 3. 3. 2.
due to malware. Includes
run?
remote access by a 4. 3.
hacker due to malware. 3. Are patches current?*
5.
4. Is web surfing to known malware
6.
Summary: [Is residual sites blocked technically?
7.
risk accepted?] 5. Are appropriate and inappropriate
uses of workstations, including 8.
shared-access workstations, 9.
defined? 10.
6. Is installation of unauthorized 11.
applications disallowed (technically 12.
or procedurally)? High/ High/ High/
13.
7. Is user education in place? Med/ Med/ Med/
14. Low Low Low
8. Are browser security standards
15.
implemented?
9. Have default logins/passwords
been changed or removed?
10.Are unnecessary services disabled?*
11.Have proper file/directory
ownership/permissions been set?
12. Is email malicious code filtering
implemented?
13. Are firewalls installed/enabled?*
14. Are periodic network
vulnerability scans performed?
15. Is HIDS/HIPS1 used?
Template Rev. 12/19/13 Page 10 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
4. [System/Human] 1. Are patches current?* 1. 1. HML/HML
Disclosure or data loss
2. Is anti-virus/anti-malware 2. 2. 1.
due to application or OS
current?* 3. 3. 2.
weaknesses introduced
by users on workstations 3. Is education about safe computing 4. 3.
/ laptops/portable practices in place?
5.
devices/electronic media 4. Is web surfing to known malware
6. High/ High/ High/
sites blocked technically?
7. Med/ Med/ Med/
Summary: [Is residual 5. Is installation of unauthorized Low Low Low
risk accepted?] applications disallowed (technically
or procedurally)?
6. Are users set not to run as admin?
7. Are appropriate controls in place to
restrict remote system access, or is
remote access disabled?
5. [System] 1. Is anti-virus/anti-malware 1. 1. HML/HML
Unauthorized access to a current?* 2. 2. 1.
system via 0-day exploit
2. Is access to databases/applications 3. High/ High/ High/ 3. 2.
technically limited based on IP Med/ Med/ Med/
Summary: [Is residual 4. 3.
address, domain, or VPN? Low Low Low
risk accepted?]
3. Are users set not to run as admin?
4. Is HIDS/HIPS1 used?
Template Rev. 12/19/13 Page 11 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
6. [System] 1. Is stored ePHI encrypted? 1. 1. HML/HML
Disclosure due to theft of
2. Are workstations and laptops 2. 2. 1.
workstation/
containing ePHI physically 3. 3. 2.
laptop/portable
secured?*
device/electronic media 4. 3.
3. Is ePHI not stored on portable
5.
Summary: [Is residual devices?
6.
risk accepted?] 4. Are portable devices and electronic High/ High/ High/
media containing ePHI physically Med/ Med/ Med/
secured when unattended?* Low Low Low
5. Is there a policy against leaving
portable devices containing ePHI
in vehicles?
6. Are systems and electronic media
containing ePHI in physically
secure locations?
Template Rev. 12/19/13 Page 12 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
7. [System] 1. Are applications configured not to 1. 1. HML/HML
Disclosure due to remember passwords? 2. 2. 1.
physical access of a
2. Are screen locks or session 3. 3. 2.
workstation /
timeouts in place including for
laptop/portable 4. 3.
workstations with shared or
device/electronic media 5.
generic logins, if any?*
(use, not theft) 6.
3. Is ePHI not stored?
4. Is stored ePHI encrypted? 7.
Summary: [Is residual
risk accepted?] 5. Are strong passwords required to 8.
access system or resume session?* 9.
6. Is installation of unauthorized 10.
applications disallowed High/ High/ High/
technically? Med/ Med/ Med/
7. Do typical users not have admin Low Low Low
access?
8. Are workstations and other devices
containing ePHI housed in
physically secure facilities?
9. Are workstations and other devices
that may display ePHI positioned
to only allow viewing by
authorized individuals?
10. Are workstations physically
restricted to limit access to only
authorized personnel?
Template Rev. 12/19/13 Page 13 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
8. [System] 1. Is ePHI not stored on non- 1. 1. HML/HML
Disclosure due to storage University equipment (except by a 2. 1.
of ePHI on non- third party with a HIPAA BAA)? High/ High/ High/
University devices 3. 2.
Med/ Med/ Med/
Low Low Low 3.
Summary: [Is residual
risk accepted?]
9. [System] 1. Is management approval required 1. 1. HML/HML
Disclosure/unauthorized for accessing ePHI from a non- 2. 2. 1.
access due to inadequate University device?
security controls on non- 3. 3. 2.
2. Are all required HIPAA
University workstations / 4. 3.
protections applied to non-
laptops/portable 5.
University devices used to
devices/electronic media 6.
remotely access ePHI, and are they
used for remote access of
verified periodically?
ePHI
3. Are non-University devices used to
Summary: [Is residual remotely access ePHI not shared High/ High/ High/
risk accepted?] with others, including family Med/ Med/ Med/
members? Low Low Low
4. Are procedures in place to log out
of programs and remove all
viewable ePHI before leaving the
device unattended?
5. Are non-University devices
configured not to save passwords
that provide access to ePHI?
6. Is ePHI never accessed from a
public, non-University device?
Template Rev. 12/19/13 Page 14 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
10. [Network] 1. Are switches hardened? (This is a 1. 1. HML/HML
Disclosure due to an question for ITS.) 2. 2. 1.
attacker re-routing
2. Is all traffic encrypted, including 3. 2.
network traffic to their
remote access? High/ High/ High/
system (ARP spoofing / 3.
Med/ Med/ Med/
man-in-the-middle
Low Low Low
attack)
Summary: [Is residual
risk accepted?]
11. [Network] 1. Is all traffic encrypted, including 1. 1. HML/HML
Disclosure due to traffic remote access? 2. 2. 1.
sniffer
2. Are Network Interface Cards 3. 3. 2.
High/ High/ High/
(NICs) controlled? (This is a
Summary: [Is residual Med/ Med/ Med/ 3.
question for ITS.)
risk accepted?] Low Low Low
3. Are sniffer detectors used (e.g.
some AV detects activity associated
with this)?
12. [System] 1. Are computers regularly examined 1. 1. HML/HML
Disclosure due to for foreign devices? 2. High/ High/ High/ 2. 1.
physical keylogger
2. Does Desktop Support do #1 when 3. Med/ Med/ Med/ 3. 2.
they work on a system in person? Low Low Low
Summary: [Is residual 3.
risk accepted?] 3. Are USB ports disabled?
Template Rev. 12/19/13 Page 15 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
13. [System] 1. Is anti-virus/anti-malware 1. 1. HML/HML
Disclosure due to current?* 2. 2. 1.
software keylogger
2. Is user education in place? 3. 3. 2.
Summary: [Is residual 3. Is web surfing to known malware 4. High/ High/ High/ 3.
risk accepted?] sites blocked technically? Med/ Med/ Med/
5.
4. Is installation of unauthorized Low Low Low
applications disallowed
(technically or procedurally)?
5. Is HIDS/HIPS1 used?
14. [Network] 1. Is all traffic encrypted, including 1. 1. HML/HML
Unauthorized device on remote access? 2. 2. 1.
network used to capture
2. Are there port based restrictions on 3. 3. 2.
traffic or credentials
who/what can connect to network?
3.
(This is a questions for ITS.)
Summary: [Is residual High/ High/ High/
risk accepted?] 3. Is Network Access Control/ Med/ Med/ Med/
Protection (NAC/NAP) Low Low Low
implemented? (This technically
enforces requiring host systems to
meet a specified security standard
before being granted full network
access.)
Template Rev. 12/19/13 Page 16 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
15. [System] 1. Is there a policy against installing 1. 1. HML/HML
Unauthorized access unapproved modems? 2. 2. 1.
through modem
2. Are computers regularly examined 3. 3. 2.
connection from a
for foreign devices?
networked PC. 4. 3.
3. Is auto-answer disabled on
5. High/ High/ High/
Summary: [Is residual modems?
Med/ Med/ Med/
risk accepted?] 4. Does the modem application Low Low Low
require authentication when
answering?
5. Are strong passwords used for
modem access, and have default
passwords been changed?
Template Rev. 12/19/13 Page 17 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
16. [Human] 1. Are accounts & access terminated 1. 1. HML/HML
Unauthorized access to or disabled ASAP upon separation 2. 2. 1.
workstation / laptop or or leave, including security codes
application/database/ 3. 3. 2.
& admin access?
server/media by former 4. 3.
2. Are passwords to shared accounts
employees, employees 5.
changed?
on leave or disability, 6.
employees whose job 3. Are shared or generic accounts
known and documented? 7.
duties no longer include
authorized access to 4. Are passwords to shared or generic 8.
ePHI; includes data accounts/logins changed when 9.
corruption by these someone leaves the group? 10.
employees. 5. Are keys/access cards collected, 11.
lock codes cancelled, and shared
Summary: [Is residual codes changed?
risk accepted?] 6. Is log monitoring proactive?
High/ High/ High/
7. Is a Data Loss Protection (DLP) Med/ Med/ Med/
system implemented (to identify Low Low Low
sensitive cleartext information
leaving the network)?
8. Is HIDS/HIPS1 used?
9. Are DB/file access monitoring/
alerting applications used (e.g.
Imperva, IBM Guardium, etc.)?
10.Is there a periodic review of
individuals with accounts/
codes/keys that provide access to
ePHI or to secure facilities that
house ePHI?
11.Are there separate procedures for
Template Rev. 12/19/13 Page 18 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
17. [Human] 1. Is log monitoring proactive? 1. 1. HML/HML
Unauthorized access to
2. Are employees educated about 2. 2. 1.
or corruption of data by High/ High/ High/
appropriate and inappropriate 3. 3. 2.
authorized employees Med/ Med/ Med/
access?
Low Low Low 3.
Summary: [Is residual 3. Is a DLP system implemented? (see
risk accepted?] above)
18. [Environmental] 1. Is data backed up regularly? 1. 1. HML/HML
Data loss or data access
2. Is there spare hardware? 2. 2. 1.
loss due to non-Data
Center SHS, SHR, or 3. Are data recovery procedures 3. 3. 2.
County Health server(s) documented? 4. High/ High/ High/ 3.
outage by failure or 4. Are data restoration procedures 5. Med/ Med/ Med/
environmental causes tested periodically? Low Low Low
6.
5. Are there backups and redundant
Summary: [Is residual systems in an alternate location?
risk accepted?] 6. Are UPSs & UPS alerts in place?
19. [Environmental] 1. Is data backed up regularly? 1. 1. HML/HML
Data loss or data access
2. Is there spare hardware? 2. 2. 1.
loss due to Data Center
server(s) outage by 3. Are data recovery procedures 3. 3. 2.
failure or environmental documented? 4. High/ High/ High/ 3.
causes. 4. Are data restoration procedures 5. Med/ Med/ Med/
tested periodically? Low Low Low
6.
Summary: [Is residual 5. Are there backups and redundant
risk accepted?] systems in an alternate location?
6. Are UPSs & UPS alerts in place?
Template Rev. 12/19/13 Page 19 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
20. [Environmental] 1. Is data backed up regularly? 1. 1. HML/HML
Data access loss due to
2. Are there backups and redundant 2. 2. 1.
SHS, SHR, Fire Dept High/ High/ High/
systems in an alternate location? 3. 3. 2.
building closure. Med/ Med/ Med/
3. Are alternate work or data access 3.
Low Low Low
Summary: [Is residual procedures documented?
risk accepted?]
21. [Environmental] 1. Is data backed up regularly? 1. 1. HML/HML
Data access loss due to
2. Are there backups and redundant 2. 2. 1.
Data Center building
systems in an alternate location? 3. High/ High/ High/ 3. 2.
closure.
3. Can Data Center systems be 4. Med/ Med/ Med/ 3.
administered remotely? Low Low Low
Summary: [Is residual
risk accepted?] 4. Are alternate work or data access
procedures documented?
22. [Human] 1. Are physical access controls in 1. 1. HML/HML
Data loss or data access place? 2. 2. 1.
loss due to non-Data
2. Is data backed up regularly? 3. 3. 2.
Center SHS, SHR, or
County Health server(s) 3. Is there spare hardware? 4. 3.
failure from physical 4. Are there backups and redundant 5. High/ High/ High/
sabotage systems in an alternate location? Med/ Med/ Med/
6.
5. Are alternate work or data access Low Low Low
7.
Summary: [Is residual procedures documented?
risk accepted?] 6. Are data restoration procedures
tested periodically?
7. Are UPSs & UPS alerts in place?
Template Rev. 12/19/13 Page 20 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
23. [Human] 1. Are physical access controls in 1. 1. HML/HML
Data loss or data access place? 2. 2. 1.
loss due to Data Center
2. Is data backed up regularly? 3. 3. 2.
server(s) failure from
physical sabotage 3. Is there spare hardware? 4. 3.
4. Are there backups and redundant 5. High/ High/ High/
Summary: [Is residual systems in an alternate location? Med/ Med/ Med/
6.
risk accepted?] 5. Are alternate work or data access Low Low Low
7.
procedures documented?
6. Are data restoration procedures
tested periodically?
7. Are UPSs & UPS alerts in place?
24. [Network] 1. Is there spare hardware? 1. 1. HML/HML
Data access loss due to
2. Are data recovery procedures 2. 2. 1.
network interruption
documented? 3. 3. 2.
from a
hacker/virus/worm 3. Are data restoration procedures 4. 3.
exploiting network tested periodically?
5.
insecurities 4. Are there backups and redundant High/ High/ High/
6.
systems in an alternate location? Med/ Med/ Med/
7. Low Low Low
Summary: [Is residual 5. Are alternate work or data access
risk accepted?] procedures documented?
6. Are UPSs & UPS alerts in place?
7. Are there redundant pathways
w/automatic switching? (This is a
question for ITS.)
Template Rev. 12/19/13 Page 21 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
25. [Network] 1. Is there spare hardware? 1. 1. HML/HML
Data access loss due to
2. Are data recovery procedures 2. 2. 1.
network interruption
documented? 3. 3. 2.
from environmental
factors or sabotage 3. Are data restoration procedures 4. 3.
tested periodically?
5.
Summary: [Is residual 4. Are there backups and redundant High/ High/ High/
6.
risk accepted?] systems in an alternate location? Med/ Med/ Med/
7. Low Low Low
5. Are alternate work or data access
procedures documented?
6. Are UPSs & UPS alerts in place?
7. Are there redundant pathways
w/automatic switching? (This is a
question for ITS.)
26. [Human] 1. Is education in place? 1. 1. HML/HML
Disclosure due to
2. Is automatic monitoring and 2. 2. 1.
inadvertent transmission
blocking in place for unencrypted 3. 2.
of data (includes High/ High/ High/
traffic?
misdirected data Med/ Med/ Med/ 3.
transmissions) Low Low Low
Summary: [Is residual
risk accepted?]
Template Rev. 12/19/13 Page 22 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
27. [Human] 1. Is education in place? 1. 1. HML/HML
Disclosure due to
2. Is automatic monitoring and 2. 2. 1.
intentional transmission
blocking in place for unencrypted 3. High/ High/ High/ 3. 2.
of data (malicious or out
traffic? Med/ Med/ Med/
of ignorance) 3.
3. Are background checks performed? Low Low Low
Summary: [Is residual
risk accepted?]
28. [Human] 1. Is all emailed ePHI encrypted? 1. 1. HML/HML
Disclosure due to email
2. Is ePHI never sent via email? 2. 2. 1.
being hijacked or stolen High/ High/ High/
by hackers 3. 2.
Med/ Med/ Med/
Low Low Low 3.
Summary: [Is residual
risk accepted?]
29. [Human] 1. Is education to double-check prior 1. 1. HML/HML
Disclosure due to to sending in place? 2. 2. 1.
printing to unintended
2. Are procedures in place to confirm 3. 3. 2.
printer, faxing to
receipt of documents?
unintended fax machine, 3.
emailing to unintended 3. Are available printers limited?
High/ High/ High/
recipient, leaving Med/ Med/ Med/
material in copy Low Low Low
machine, misaddressed
paper mail
Summary: [Is residual
risk accepted?]
Template Rev. 12/19/13 Page 23 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
30. [Human] 1. Does everyone receive HIPAA 1. 1. HML/HML
Disclosure due to training prior to obtaining access 2. 2. 1.
authorized employee to ePHI?
lack of knowledge 3. 3. 2.
2. Does training include UCSC
regarding ePHI security 4. 3.
Password Standards and the
requirements
importance of protecting against High/ High/ High/
malicious software and exploitation Med/ Med/ Med/
Summary: [Is residual
of vulnerabilities? Low Low Low
risk accepted?]
3. Are there periodic training updates
and reminders?
4. Are there periodic tests for
understanding of HIPAA security
requirements?
31. [Human] 1. Do HIPAA training and training 1. 1. HML/HML
Delay in detection of updates include incident response 2. 2. 1.
disclosure due to and reporting procedures? High/ High/ High/
improper or lack of 3. 2.
2. Are there periodic tests for Med/ Med/ Med/
incident reporting 3.
understanding of HIPAA incident Low Low Low
response and reporting
procedures?
Template Rev. 12/19/13 Page 24 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
32. [System] 1. Is education in place? 1. 1. HML/HML
Disclosure due to
2. Are procedures to destroy or 2. 2. 1.
improper disposal of
securely wipe prior to disposal, re- 3. 3. 2.
equipment
use, return to vendor, including for
4. 3.
copiers, faxes, printers, etc.,
Summary: [Is residual
documented? High/ High/ High/
risk accepted?]
3. Does management verify that Med/ Med/ Med/
disposal policies are being carried Low Low Low
out (e.g. spot checks that devices
have been wiped)?
4. Is stored ePHI encrypted,
including on copiers, faxes,
printers, etc.
33. [System] 1. Are alternate work procedures 1. 1. HML/HML
Loss of access to External documented? 2. 2. 1.
Service Provider from a
2. Are troubleshooting procedures High/ High/ High/ 3. 2.
system failure on the
with external service provider Med/ Med/ Med/
remote end. 3.
documented? Low Low Low
Summary: [Is residual
risk accepted?]
Template Rev. 12/19/13 Page 25 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
34. [Network] 1. Are alternate work procedures 1. 1. HML/HML
Loss of access to External documented? 2. 2. 1.
Service Provider system
2. Are troubleshooting procedures 3. 2.
from a connection failure
with external service provider High/ High/ High/
caused by hacker, virus 3.
documented? Med/ Med/ Med/
or worm, or network
Low Low Low
outage.
Summary: [Is residual
risk accepted?]
35. [System] 1. See #1-4 1. 1. HML/HML
Loss of access to External
2. Are alternate work procedures 2. 2. 1.
Service Provider system
documented? 3. 2.
from a local workstation High/ High/ High/
failure caused by hacker, Med/ Med/ Med/ 3.
virus or worm. Low Low Low
Summary: [Is residual
risk accepted?]
Template Rev. 12/19/13 Page 26 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
36. [System] 1. Is the data backup and recovery 1. 1. HML/HML
Disclosure or lack of plan for all original sources of 2. 2. 1.
availability due to an essential ePHI documented and
inadequate data backup 3. 3. 2.
implemented, including restoration
and recovery plan priorities? 4. 3.
2. Do backup procedures include 5.
Summary: [Is residual
steps to ensure that all protections
risk accepted?]
are re-applied and restored before
ePHI is restored to a system?
3. Are data backups and recovery High/ High/ High/
tested periodically? Med/ Med/ Med/
4. Are any additional authorities or Low Low Low
procedures necessary to ensure the
continuation of security
protections for ePHI during
emergency operations mode
documented and implemented?
5. Is a copy of original sources of
essential ePHI created before
moving equipment containing
them?
Template Rev. 12/19/13 Page 27 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
37. [Human] 1. Are backups containing ePHI 1. 1. HML/HML
Disclosure due to stored securely? 2. 2. 1.
improper handling of
2. Are backups stored temporarily 3. 3. 2.
backups containing ePHI
before transporting to a permanent
4. 3.
facility stored in a secure manner?
Summary: [Is residual 5. High/ High/ High/
risk accepted?] 3. Is the method of transportation of
Med/ Med/ Med/
backups, if any, secure?
Low Low Low
4. Do only authorized, HIPAA-
trained personnel handle backups
containing ePHI?
5. Is a HIPAA BAA is in place for all
non-UC offsite storage?
38. [Human] 1. Are movements of hardware and 1. 1. HML/HML
Disclosure due to electronic media containing ePHI 2. 2. 1.
inadequate tracking of formally tracked?
the movements of 3. 2.
2. Is hardware and electronic media High/ High/ High/
hardware and electronic Med/ Med/ Med/ 3.
containing ePHI transported by
media containing ePHI Low Low Low
secure methods and authorized
personnel only?
Summary: [Is residual
risk accepted?]
Template Rev. 12/19/13 Page 28 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
39. [System] 1. Is there proactive log review/ 1. 1. HML/HML
Lack of discovery of monitoring, including of activities 2. 2. 1.
disclosure or performed with elevated privileges
unauthorized data 3. 2.
or by authorized users?
modification/ destruction 3.
2. If there is shared or generic access High/ High/ High/
due to inadequate
to a workstation, are other controls Med/ Med/ Med/
information system
in place to tie activity on the Low Low Low
activity review/log
workstation to an individual?
monitoring
Summary: [Is residual
risk accepted?]
40. [Human] 1. Are HIPAA BAAs are in place 1. 1. HML/HML
Disclosure due to where required? High/ High/ High/
2. 1.
improper protection of Med/ Med/ Med/
ePHI by third -parties 3. 2.
Low Low Low
3.
41. [Servers] 1. Is ePHI stored on servers 1. 1. HML/HML
Disclosure due to theft of encrypted? 2. 2. 1.
server or a server drive,
2. Are systems and electronic media 3. 2.
including printers, High/ High/ High/
containing ePHI in physically
copiers, fax machines, Med/ Med/ Med/ 3.
secure locations with physical
etc. Low Low Low
access controls?*
Summary: [Is residual
risk accepted?]
Template Rev. 12/19/13 Page 29 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
42. [Servers] 1. Are systems and electronic media 1. 1. HML/HML
Disclosure due to containing ePHI in physically 2. 2. 1.
physical access to servers secure locations with physical
(to pull data, mirror 3. 3. 2.
access controls?*
drive, install a malicious 4. 3.
2. Are there technical access controls? High/ High/ High/
device) 5.
3. Is ePHI stored on servers Med/ Med/ Med/
Summary: [Is residual encrypted? Low Low Low
risk accepted?] 4. Are unauthorized apps technically
disallowed on servers?
5. Is periodic visual inspection of
servers performed?
Template Rev. 12/19/13 Page 30 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
43. [Servers] 1. Is OS & application patching 1. 1. HML/HML
Disclosure or data current?* 2. 2. 1.
corruption due to server
2. Are unnecessary services disabled* 3. 3. 2.
OS or application
on servers?
weaknesses or malware 4. 3.
on servers 3. Is anti-virus on Windows servers
5.
current?*
6.
Summary: [Is residual 4. Are there physical access controls?
7.
risk accepted?] 5. Are there technical access controls?
8. High/ High/ High/
6. Do sessions time out?*
9. Med/ Med/ Med/
7. Is installation of unauthorized Low Low Low
applications disallowed (technically 10.
or procedurally)?
8. Are all default passwords changed?
9. Are strong passwords required to
access system or resume session?*
10. Are authentication systems
periodically tested and upgraded
when upgrades are available?
Template Rev. 12/19/13 Page 31 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
44. [Servers] 1. Are background checks performed? 1. 1. HML/HML
Disclosure, loss of data
2. Is access limited to the least 2. 2. 1.
access or data corruption
necessary to perform job functions? 3. 3. 2.
due to corrupt admins
3. Is there separation of duties 4. 3.
High/ High/ High/
Summary: [Is residual wherever possible?
5. Med/ Med/ Med/
risk accepted?] 4. Is there proactive log review/ Low Low Low
monitoring, including of activities
performed with elevated privileges?
5. Is stored and transmitted data
(ePHI) encrypted?
45. [Servers] 1. Are stored passwords encrypted? 1. 1. HML/HML
Disclosure due to use of
2. Are there physical access controls? 2. 2. 1.
stored passwords
3. Are session timeouts/screen locking 3. High/ High/ High/ 3. 2.
Summary: [Is residual in place?* 4. Med/ Med/ Med/ 3.
risk accepted?] 4. Is a master password used for Low Low Low
5.
access to any stored passwords?
5. Is a password vault used?
46. Unit-Specific Risk #1 1. 1. 1. HML/HML
High/ High/ High/ 2. 1.
Med/ Med/ Med/
Summary: [Is residual 3. 2.
Low Low Low
risk accepted?] 3.
47. Unit-Specific Risk #2 1. 1. 1. HML/HML
High/ High/ High/ 2. 1.
Med/ Med/ Med/
Summary: [Is residual 3. 2.
Low Low Low
risk accepted?] 3.
Template Rev. 12/19/13 Page 32 of 33 itpolicy@ucsc.edu
UCSC HIPAA Security Rule Risk Analysis
Existing Mitigations/Controls Maturity
(possible controls/suggestions in Level (0-5) Next Steps: Effort/Cost to
Security Concern/ Likeli-
italics; Impact Risk Identified Action Items Mitigate Risk
Threat/Vulnerability hood
* = part of UCSCs Minimum Network for each and Owners (High/Med/Low)
Connectivity Requirements) Mitigation
48. Unit-Specific Risk #3 1. 1. 1. HML/HML
High/ High/ High/ 2. 1.
Med/ Med/ Med/
Summary: [Is residual 3. 2.
Low Low Low
risk accepted?] 3.
49. Unit-Specific Risk #4 1. 1. 1. HML/HML
High/ High/ High/ 2. 1.
Med/ Med/ Med/
Summary: [Is residual 3. 2.
Low Low Low
risk accepted?] 3.
50. Unit-Specific Risk #5 1. 1. 1. HML/HML
High/ High/ High/ 2. 1.
Med/ Med/ Med/
Summary: [Is residual 3. 2.
Low Low Low
risk accepted?] 3.
Template Rev. 12/19/13 Page 33 of 33 itpolicy@ucsc.edu
You might also like
- Quiz - Introduction To Cybersecurity - Attempt ReviewDocument2 pagesQuiz - Introduction To Cybersecurity - Attempt ReviewPonce100% (1)
- Presentation - CrowdStrike Falcon InsightDocument24 pagesPresentation - CrowdStrike Falcon InsightAlbert gonzalez fuentesNo ratings yet
- CISSP - 1 Information Security & Risk ManagementDocument60 pagesCISSP - 1 Information Security & Risk ManagementlebenikosNo ratings yet
- Csol530 Final Assignment Re-FormattedDocument7 pagesCsol530 Final Assignment Re-Formattedapi-360051483No ratings yet
- Phishing Attacks and SolutionsDocument22 pagesPhishing Attacks and SolutionsMadhuri DollNo ratings yet
- Hipaa Risk AnalysisDocument33 pagesHipaa Risk AnalysisKalpana KalpanaNo ratings yet
- SOPRFA SecurityManagementProcedure 120722 1005 6274Document7 pagesSOPRFA SecurityManagementProcedure 120722 1005 6274Siti Aishah Umairah Naser Binti Abdul RahmanNo ratings yet
- NSM IvDocument17 pagesNSM IvVignesh ShettyNo ratings yet
- Risk Management ProcessDocument40 pagesRisk Management Processfatimabbajwa27No ratings yet
- Risk Management ProcessDocument40 pagesRisk Management ProcessAliAdnan AliAdnan100% (1)
- 3600 Lecture6 Risk ManagementDocument37 pages3600 Lecture6 Risk ManagementGNo ratings yet
- Risk Assessment Process Nist 80030 7383Document20 pagesRisk Assessment Process Nist 80030 7383datadinkNo ratings yet
- Risk ManagementDocument34 pagesRisk Managementsumrun sahabNo ratings yet
- CISSP - 1 Information Security & Risk ManagementDocument60 pagesCISSP - 1 Information Security & Risk Managementjonty509No ratings yet
- Employee Security Awareness SurveyDocument7 pagesEmployee Security Awareness Surveyrazan essaNo ratings yet
- Risk Analysis Template 05Document20 pagesRisk Analysis Template 05analysis of packaging materials department responsible quality control managementNo ratings yet
- NIST SP800-30 Approach To Risk AssessmentDocument6 pagesNIST SP800-30 Approach To Risk AssessmentBabby BossNo ratings yet
- DoD HFACS 8.0 Guide - 20230927 Corrected smDocument33 pagesDoD HFACS 8.0 Guide - 20230927 Corrected smJose A. HerreraNo ratings yet
- Hipaa Risk AnalysisDocument20 pagesHipaa Risk AnalysisnabilNo ratings yet
- 3 - 2. Risk Identification and ClassificationDocument35 pages3 - 2. Risk Identification and Classification23Mochammad DwikyNo ratings yet
- Assignment Risk ManagementDocument5 pagesAssignment Risk ManagementHimanshu JainNo ratings yet
- Topic 2 - Information RisksDocument43 pagesTopic 2 - Information RisksMOAWYA Al JAYOUSINo ratings yet
- Risk Analysis NotesDocument26 pagesRisk Analysis NotesJosh TuibeoNo ratings yet
- GS102 GuideDocument21 pagesGS102 GuideAbel PodaNo ratings yet
- 6 Steps To A What You Should Know About PoliticsDocument11 pages6 Steps To A What You Should Know About PoliticsKEBESHERNo ratings yet
- Security ProjectDocument14 pagesSecurity ProjectjagritiNo ratings yet
- 3600 Lecture4 Risk ManagementDocument36 pages3600 Lecture4 Risk ManagementJoel CuasayNo ratings yet
- National Infrastructure Protection Center: Risk Management: An Essential Guide To Protecting Critical AssetsDocument11 pagesNational Infrastructure Protection Center: Risk Management: An Essential Guide To Protecting Critical AssetslazioromaNo ratings yet
- Lec 4Document30 pagesLec 4Misbah IrumNo ratings yet
- Guide To Risk Opportunity Assessment ResponseDocument17 pagesGuide To Risk Opportunity Assessment ResponseNina AzizNo ratings yet
- Risk Management - Concepts and ApplicationsDocument20 pagesRisk Management - Concepts and ApplicationsStephen EmmanuelNo ratings yet
- Iowa State University: Business Impact Analysis and Risk Assessment For Information ResourcesDocument12 pagesIowa State University: Business Impact Analysis and Risk Assessment For Information ResourcesHomerKhanNo ratings yet
- Why Should A Risk Analysis Be Conducted?: Security Management PracticesDocument2 pagesWhy Should A Risk Analysis Be Conducted?: Security Management PracticesZayaan RnbNo ratings yet
- Security Risk Management: COSC 454Document7 pagesSecurity Risk Management: COSC 454Silver LisingNo ratings yet
- IT Risk Management Based On COBIT 5 For Risk at Deutsche Telekom AG Joa Eng 0518Document7 pagesIT Risk Management Based On COBIT 5 For Risk at Deutsche Telekom AG Joa Eng 0518toanquoc.doanNo ratings yet
- Risk ManagementDocument8 pagesRisk ManagementSylviaNo ratings yet
- SsprocdscrpDocument3 pagesSsprocdscrpmazen_229No ratings yet
- Risk Assessment: ChallengeDocument8 pagesRisk Assessment: ChallengeApoloTrevinoNo ratings yet
- SMSCRM - Handout Day 1Document6 pagesSMSCRM - Handout Day 1astroNOTNo ratings yet
- Infosec RisksDocument15 pagesInfosec RisksJOENo ratings yet
- RiskDocument51 pagesRisknyavee373No ratings yet
- CSSLP 2016 NotesDocument26 pagesCSSLP 2016 Notesparul154No ratings yet
- Unit 5 - Assignment 2 Frontsheet - SecurityDocument28 pagesUnit 5 - Assignment 2 Frontsheet - SecurityTran Van KhoiNo ratings yet
- Upon Completion of This Chapter, You Should Be Able To:: - Identify The Categories That Can Be Used To Classify ControlsDocument30 pagesUpon Completion of This Chapter, You Should Be Able To:: - Identify The Categories That Can Be Used To Classify ControlsabegazNo ratings yet
- Risk Managementin InformatizationDocument12 pagesRisk Managementin InformatizationcherifdjNo ratings yet
- White Paper: Building An Application Vulnerability Management ProgramDocument32 pagesWhite Paper: Building An Application Vulnerability Management Programhai TrầnNo ratings yet
- Running Head: Stages To Demeanor A Risk Assessment 1Document7 pagesRunning Head: Stages To Demeanor A Risk Assessment 1guntupally shiridi saiNo ratings yet
- Risk ProfilingDocument6 pagesRisk ProfilingIsaac TapfumaneyiNo ratings yet
- 3-HIRARC (Hazard Identification, Risk Assessment and Risk Control)Document7 pages3-HIRARC (Hazard Identification, Risk Assessment and Risk Control)A. RAHMAD BIN NGAH / UPM100% (1)
- Threat and Risk and Gaps AssessmentDocument8 pagesThreat and Risk and Gaps Assessments14301370No ratings yet
- How To Perform An IT Cyber Security Risk Assessment 1595802501Document11 pagesHow To Perform An IT Cyber Security Risk Assessment 1595802501Florick Le MahamatNo ratings yet
- Lecture 3Document29 pagesLecture 3seham alshehhiNo ratings yet
- IT Security ManagementDocument7 pagesIT Security ManagementNamata Racheal SsempijjaNo ratings yet
- How To Analyze Process RiskDocument5 pagesHow To Analyze Process RiskMustafa GhaleiwNo ratings yet
- Likelihood-Exposure Level, Ease of Breaking, Data Value Quantity $, Quality ScenarioDocument11 pagesLikelihood-Exposure Level, Ease of Breaking, Data Value Quantity $, Quality ScenariosibinsukumaranPsibi3No ratings yet
- Evaluation Report 1Document6 pagesEvaluation Report 1tsepoNo ratings yet
- MSIS 4253 Exam 1-Chapters 1-5 Lecture NotesDocument19 pagesMSIS 4253 Exam 1-Chapters 1-5 Lecture Notesnightmonkey215No ratings yet
- Risk Assessment Report TemplateDocument7 pagesRisk Assessment Report Templateguylevy855No ratings yet
- ICT Lesson 2 - Data Security and ControlDocument61 pagesICT Lesson 2 - Data Security and ControlOTIENO ELIJAHNo ratings yet
- Session 5 Cyber Security Risks and VulnerabilitiesDocument14 pagesSession 5 Cyber Security Risks and Vulnerabilitiesdrelm7399No ratings yet
- Information Technology Risk Management in Enterprise Environments: A Review of Industry Practices and a Practical Guide to Risk Management TeamsFrom EverandInformation Technology Risk Management in Enterprise Environments: A Review of Industry Practices and a Practical Guide to Risk Management TeamsRating: 5 out of 5 stars5/5 (1)
- Asset Attack Vectors: Building Effective Vulnerability Management Strategies to Protect OrganizationsFrom EverandAsset Attack Vectors: Building Effective Vulnerability Management Strategies to Protect OrganizationsNo ratings yet
- CompTIA CASP+ Certification The Ultimate Study Guide To Master the Advanced Security Practitioner ExamFrom EverandCompTIA CASP+ Certification The Ultimate Study Guide To Master the Advanced Security Practitioner ExamNo ratings yet
- Computer Security Solved MCQs (Set-1)Document6 pagesComputer Security Solved MCQs (Set-1)nzellemary99No ratings yet
- Lecture - 1 - What Is Information SecurityDocument8 pagesLecture - 1 - What Is Information SecurityvaishaliguptaNo ratings yet
- AJ Lab 8 & 9Document2 pagesAJ Lab 8 & 9Shilpa SannamaniNo ratings yet
- PR3 Rail Fence Cipher FinalDocument8 pagesPR3 Rail Fence Cipher FinalprafullaNo ratings yet
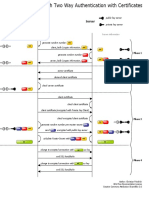
- SSL Handshake With Two-Way Authentication With CertificatesDocument1 pageSSL Handshake With Two-Way Authentication With CertificatesShailendra PandeyNo ratings yet
- An Introduction To PKI (Public Key Infrastructure)Document8 pagesAn Introduction To PKI (Public Key Infrastructure)Rama SubramaniamNo ratings yet
- Gtu Computer 3170720 Winter 2022Document1 pageGtu Computer 3170720 Winter 2022Farhan MansuriNo ratings yet
- Key Distribution ProblemDocument1 pageKey Distribution ProblemDeepa SainiNo ratings yet
- What Is 802.1X - How Does It WorkDocument13 pagesWhat Is 802.1X - How Does It WorkvatcheNo ratings yet
- WpaDocument39 pagesWpaAbraham NdongNo ratings yet
- Burp Suite Help - Using Burp SuiteDocument4 pagesBurp Suite Help - Using Burp SuiteNidhin DineshNo ratings yet
- DBMS PresentationDocument17 pagesDBMS Presentationsantoshmahato2481832No ratings yet
- 9 - 13 - 22 - (3) - Network Perimeter Security DesignDocument10 pages9 - 13 - 22 - (3) - Network Perimeter Security DesignArun SharmaNo ratings yet
- Huntmetrics Deck v3Document15 pagesHuntmetrics Deck v3Sarah KhanNo ratings yet
- Third Party Public Auditing Scheme For Cloud Storage: SciencedirectDocument8 pagesThird Party Public Auditing Scheme For Cloud Storage: SciencedirectjyoshnaNo ratings yet
- Try Ini Utk CR PasswordDocument3 pagesTry Ini Utk CR PasswordHarjit Ranjit KumarNo ratings yet
- IT Security - HashDocument30 pagesIT Security - HashpupuNo ratings yet
- What Is Information Security: Confidentiality Integrity AvailabilityDocument23 pagesWhat Is Information Security: Confidentiality Integrity AvailabilityFLEXCODEC TECHNo ratings yet
- Practical Cryptology, IT754A, 7,5hp: InstructionDocument3 pagesPractical Cryptology, IT754A, 7,5hp: Instructionsaeed khanNo ratings yet
- Unit 5Document45 pagesUnit 5埃蘭戈萬(Elangovan)No ratings yet
- Shree Swaminarayan Institute of Technology, Bhat: Computer Engineering Department Subject: Information Security (3170720)Document3 pagesShree Swaminarayan Institute of Technology, Bhat: Computer Engineering Department Subject: Information Security (3170720)Herry MahetaNo ratings yet
- Cloud Computing Chapter 09Document27 pagesCloud Computing Chapter 09ghar_dashNo ratings yet
- Chapters 1 2Document36 pagesChapters 1 2radhe shamNo ratings yet
- Hillstone SA Firewall Series & GreenBow IPSec VPN Client Software Configuration (English)Document15 pagesHillstone SA Firewall Series & GreenBow IPSec VPN Client Software Configuration (English)greenbowNo ratings yet
- 8.1 Cyber SecurityDocument6 pages8.1 Cyber Securityamit_post2000No ratings yet
- Information SecurityDocument2 pagesInformation Security3qtrtymNo ratings yet
- Tony Dick Dropbox02 7/10/2021 Information Systems Security Ccis 391 AdeDocument2 pagesTony Dick Dropbox02 7/10/2021 Information Systems Security Ccis 391 AdeTony DickNo ratings yet