Professional Documents
Culture Documents
Rajalakshmi Engineering College: Signature of Faculty Signature of HOD
Rajalakshmi Engineering College: Signature of Faculty Signature of HOD
Uploaded by
suganya0040 ratings0% found this document useful (0 votes)
11 views1 pageThis document contains the lesson plan for a Cryptography and Network Security course taught over 5 units covering various topics in cryptography. The lesson plan lists 50 topics that will be covered across the 5 units, including conventional encryption techniques, public key cryptography, authentication, hash functions, and network and system level security tools and applications. It also lists the textbook and references that will be used for the course.
Original Description:
COMPUTER AND NETWORK SECURITY NOTES
Original Title
IT1352
Copyright
© © All Rights Reserved
Available Formats
DOC, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document contains the lesson plan for a Cryptography and Network Security course taught over 5 units covering various topics in cryptography. The lesson plan lists 50 topics that will be covered across the 5 units, including conventional encryption techniques, public key cryptography, authentication, hash functions, and network and system level security tools and applications. It also lists the textbook and references that will be used for the course.
Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
Download as doc, pdf, or txt
0 ratings0% found this document useful (0 votes)
11 views1 pageRajalakshmi Engineering College: Signature of Faculty Signature of HOD
Rajalakshmi Engineering College: Signature of Faculty Signature of HOD
Uploaded by
suganya004This document contains the lesson plan for a Cryptography and Network Security course taught over 5 units covering various topics in cryptography. The lesson plan lists 50 topics that will be covered across the 5 units, including conventional encryption techniques, public key cryptography, authentication, hash functions, and network and system level security tools and applications. It also lists the textbook and references that will be used for the course.
Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
Download as doc, pdf, or txt
You are on page 1of 1
RAJALAKSHMI ENGINEERING COLLEGE 21 Random Number Generation T220-T227
LESSON PLAN 22 Public key cryptography principles of Public T259-T268
Faculty Name J.CHITRA Faculty Code IT37 key cryptosystems
Subject Name Cryptography and Network Security Subject code IT1352 23 The RSA Algorithm. T268-T278
Class III Year IT A & B Sec Date of Compilation 16/11/2007 UNIT-III AUTHENTICATION AND HASH FUNCTION Actual 9 hrs. Planned 11 hrs.
DEFINITION 24 Authentication Requirements T312- T313
25 Authentication functions T313- T324
To understand the principles of encryption algorithms; conventional and public key cryptography. To
26 Message Authentication codes T324- T328
have a detailed knowledge about authentication, hash functions and application level security 27 Hash functions T328- T334
mechanisms. 28 Security of Hash Functions and MACs T335- T338
29 MD5 Message Digest Algorithm T348- T357
OBJECTIVES
To know the methods of conventional encryption. 30 Secure Hash Algorithm. T357- T364
To understand the concepts of public key encryption and number theory 31 RIPEMD T365- T372
To understand authentication and Hash functions. 32 HMAC Digital Signature T372- T376
To know the network security tools and applications. 33 Authentication Protocols T384- T391
To understand the system level security used. 34 Digital Signatures Standard T392- T395
UNIT-IV NETWORK SECURITY Actual 8 hrs. Planned 8 hrs.
S.No Date Period Topic Page No 35 Authentication Applications: Kerberos T402- T419
UNIT- I INTRODUCTION Actual 10 hrs. Planned-11hrs. 36 X.509 Authentication Services T419- T428
1 OSI Security Architecture T7- T14 37 Electronic Mail Security-PGP T436- T455
2 Classical Encryption Techniques T23-T30 38 S/MIME T455- T472
Symmetric cipher model 39 IP Security Overview-Architecture T482- T491
Substitution Techniques 40 Authentication Header-ESP T491-T501
3 Transportation Techniques T44- T47 41 Combining Security Payload-Key mgmt. T501-T515
Rotar Machines Steganography
42 Web Security T528- T560
4 Cipher principles T63- T72
UNIT V SYSTEM LEVEL SECURITY Actual 8 hrs. Planned 8 hrs.
5 Data encryption standard T72- T81
43 Intrusion Detection T569- T581
6 Block Cipher Design Principles and T63
44 Intrusion Detection Techniques T569- T581
Modes of operation T91- T98
45 Password Management T581- T591
7 Evaluation criteria for AES T140- T143
46 Viruses and related Threats T598- T609
8 AES cipher T143- T167 47 Virus counter measures T609- T613
48 Firewall Design Principles T616- T628
9 Triple DES T174- T179 49 Firewall Design Principles T616- T628
10 Placement of Encryption Function T202- T210 50 Trusted Systems. T628- T634
11 Traffic confidentiality T210- T211 TEXT BOOK
UNIT-II PUBLIC KEY CRYPTOGRAPHY Actual 10 hrs. Planned 12 hrs. 1. William Stallings, Cryptography And Network Security Principles and
12 Key Management T286- T293 Practices, Prentice Hall of India, Third Edition, 2003.
13 Diffie Hellman key Exchange T293- T296 REFERENCES
14 Elliptic Curve Architecture and Cryptography T304- T308
1. Atul Kahate, Cryptography and Network Security, Tata McGraw-Hill, 2003.
15 Introduction to Number theory Prime T236-T239 2. Bruce Schneier, Applied Cryptography, John Wiley & Sons Inc, 2001.
numbers 3. Charles B. Pfleeger, Shari Lawrence Pfleeger, Security in Computing, Third
16 Fermats and Eulers Theorems T239- T243 Edition, Pearson Education, 2003.
17 Testing for Primality T243-T245
18 The Chinese Remainder Theorem-Discrete T245-T252
Logarithms
19 Confidentiality using symmetric Encryption T202-T211
20 20 Ke Key distribution T2 T211-T220
Signature of Faculty Signature of HOD
You might also like
- 2021 Threat Detection ReportDocument122 pages2021 Threat Detection Reportprueba prueba3No ratings yet
- Simply Supported BeamDocument9 pagesSimply Supported BeamcukkNo ratings yet
- InDesign and XML Tech RefDocument28 pagesInDesign and XML Tech RefMarius TNo ratings yet
- CNS Course Plan - Iv CDocument9 pagesCNS Course Plan - Iv CMohana SubbuNo ratings yet
- Cryptography and Network SecurityDocument4 pagesCryptography and Network SecurityMary HelenNo ratings yet
- US Govt Report On Cryptocurrencies and BlockchainDocument59 pagesUS Govt Report On Cryptocurrencies and BlockchainSyndicated NewsNo ratings yet
- Cns Lecture PlanDocument6 pagesCns Lecture PlanAnonymous nT5gwPNo ratings yet
- iOS AttackDocument1 pageiOS AttackrakivanatanNo ratings yet
- Pune - University - Vlsi Book - Study - Plan XeroxDocument4 pagesPune - University - Vlsi Book - Study - Plan Xeroxanshu4u06No ratings yet
- 6696 LessonsLearned DD 20150422 WebDocument10 pages6696 LessonsLearned DD 20150422 Webiam@scribd123No ratings yet
- Lecture Plan - CS801DDocument3 pagesLecture Plan - CS801DAvishek GhoshNo ratings yet
- Guidelines For The Selection, Configuration, and Use of Transport Layer Security (TLS) ImplementationsDocument73 pagesGuidelines For The Selection, Configuration, and Use of Transport Layer Security (TLS) ImplementationshumdilNo ratings yet
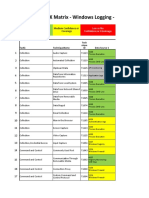
- Mitre ATT@CK Matrix - Windows Logging - Basic: High Confidence or Covereage Medium Confidence or CoverageDocument27 pagesMitre ATT@CK Matrix - Windows Logging - Basic: High Confidence or Covereage Medium Confidence or CoverageTuba ŞengünNo ratings yet
- Profile of Computer Engineering ProgramDocument4 pagesProfile of Computer Engineering ProgramMelwin SyafrizalNo ratings yet
- M. Sc. CS Draft Syllabus 13.12.2021Document73 pagesM. Sc. CS Draft Syllabus 13.12.2021ಭರತ್ಕುಮಾರಒಂಟಿಬಾನಾಡಿNo ratings yet
- SEEL4343 - Chapter 3-Part1Document18 pagesSEEL4343 - Chapter 3-Part1farhatulNo ratings yet
- Tortuga Logic Security Verification of Rambus CMRTDocument5 pagesTortuga Logic Security Verification of Rambus CMRTPhil UrichNo ratings yet
- Making Mitre Att&Ck Framework New Hunting Standard: January 2020 SentineloneDocument14 pagesMaking Mitre Att&Ck Framework New Hunting Standard: January 2020 SentineloneShreekanth MuraliNo ratings yet
- TEACHING AND EVALUATION SCHEME FOR 6th Semester (CSE) (Wef 2020-21)Document25 pagesTEACHING AND EVALUATION SCHEME FOR 6th Semester (CSE) (Wef 2020-21)SWARNA LATANo ratings yet
- Iscf pg2013 14 PDFDocument34 pagesIscf pg2013 14 PDFSumanNo ratings yet
- Tyco Fire Catalogue Iss 7 29Document207 pagesTyco Fire Catalogue Iss 7 29ishaq100% (1)
- TD15 TC LI Presentation JointDocument17 pagesTD15 TC LI Presentation JointMac KioNo ratings yet
- Mxcat 3Document49 pagesMxcat 3Mon MontejoNo ratings yet
- ECE 6th Sem SyllabusDocument7 pagesECE 6th Sem SyllabusHarsh KumarNo ratings yet
- OPEN UNIVERSITY - NonStop Virtual Courses - Study Guide, MetropoliaDocument6 pagesOPEN UNIVERSITY - NonStop Virtual Courses - Study Guide, Metropoliaworld.of.ledgersNo ratings yet
- Mod 2 ISO OSI Reference Model IDATOSI001Document90 pagesMod 2 ISO OSI Reference Model IDATOSI001Mao BourichaNo ratings yet
- Fire Alarm BookDocument196 pagesFire Alarm Bookprasanth_kb100% (5)
- B.tech-I.T 7 & 8 Semester Course WorkDocument16 pagesB.tech-I.T 7 & 8 Semester Course WorkRocker byNo ratings yet
- 1 s2.0 S2590005622000777 MainDocument27 pages1 s2.0 S2590005622000777 MainMila Datul MuharromahNo ratings yet
- A Thesis Report On Optimized Encryption Algorithm Using Dynamic KeysDocument58 pagesA Thesis Report On Optimized Encryption Algorithm Using Dynamic KeysMajid KhanNo ratings yet
- Syllabus Cse 5-8 (Regulation 2001)Document25 pagesSyllabus Cse 5-8 (Regulation 2001)Jaganathan K100% (19)
- Tricon Safety Instrumented System (SIL3) : Ensuring Operational Continuity and Managing Operational RisksDocument4 pagesTricon Safety Instrumented System (SIL3) : Ensuring Operational Continuity and Managing Operational RisksROAMEN ENGINEERINGNo ratings yet
- Mobile Attack Cheat Sheet 1708115239Document1 pageMobile Attack Cheat Sheet 1708115239Joash MacentonNo ratings yet
- R 2008 It CurriculumDocument4 pagesR 2008 It CurriculumKarti SubramanianNo ratings yet
- NetworkSecurityISO Lesson Plan1Document3 pagesNetworkSecurityISO Lesson Plan1KarpagamSivakumarNo ratings yet
- EST3 History Reports.Document2 pagesEST3 History Reports.Pedro100% (1)
- GettingstartedDocument43 pagesGettingstartedJulio Cesar Tapia ReyesNo ratings yet
- lesson_plan-CCS-PO-2021Document2 pageslesson_plan-CCS-PO-2021prakash.omprakash.om1No ratings yet
- Up & Uc - LessonPlanDocument2 pagesUp & Uc - LessonPlanKannan AlagumuthiahNo ratings yet
- IT Courses Data Analysis of Inter Continental Submitiom by Asia Bureo of Indian National ScienceDocument2 pagesIT Courses Data Analysis of Inter Continental Submitiom by Asia Bureo of Indian National SciencedetroitopftwNo ratings yet
- Fire Catalogue Iss 7 24Document210 pagesFire Catalogue Iss 7 24prasanth_kb100% (2)
- Security Analysis of TETRADocument102 pagesSecurity Analysis of TETRAkondorosNo ratings yet
- Cat 3 PPTDocument10 pagesCat 3 PPTSATYAM ANAND 20SCSE1010341No ratings yet
- Technicolor Td5130 Admin Password E-PUBDocument5 pagesTechnicolor Td5130 Admin Password E-PUBLabodedexterNo ratings yet
- Digital Communication: Department of EceDocument4 pagesDigital Communication: Department of EceJefferson ThompsonNo ratings yet
- Automated Symbolic Verification of Telegram'S Mtproto 2.0: Marino MiculanDocument16 pagesAutomated Symbolic Verification of Telegram'S Mtproto 2.0: Marino MiculanVũ Đăng HoàngNo ratings yet
- TYCO-Fire Detection Catalog-Issue 5Document157 pagesTYCO-Fire Detection Catalog-Issue 5woawoaNo ratings yet
- Department of Electronics and Communication Engineering Course DescriptionDocument7 pagesDepartment of Electronics and Communication Engineering Course DescriptionDurga SravanthiNo ratings yet
- Code No.: ETIT 412 L T C Paper: Network Security 3 1 4: Instructions To Paper Setters: Maximum Marks: 75Document2 pagesCode No.: ETIT 412 L T C Paper: Network Security 3 1 4: Instructions To Paper Setters: Maximum Marks: 75Mohit SinglaNo ratings yet
- Minors HonorsDocument2 pagesMinors Honorschokkagnapikasri.21.itNo ratings yet
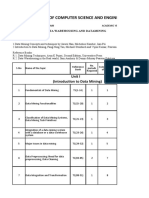
- Department of Computer Science and Engineering: Unit I (Introduction To Data Mining)Document10 pagesDepartment of Computer Science and Engineering: Unit I (Introduction To Data Mining)K VENKATA SRAVANINo ratings yet
- Information Security and Cryptography Updated SyllabusDocument4 pagesInformation Security and Cryptography Updated SyllabusShivani DimriNo ratings yet
- 2023-1866Document24 pages2023-1866张泽楷No ratings yet
- Datasheet Triconex TofinoFirewall 04-10 Rev 2Document4 pagesDatasheet Triconex TofinoFirewall 04-10 Rev 2Obinna Benedict ObiojiNo ratings yet
- Third Semester MCADocument22 pagesThird Semester MCAVaiSh CHNo ratings yet
- Approved Telecoms Degree CurriculumDocument15 pagesApproved Telecoms Degree CurriculumMunya ChiksNo ratings yet
- E&C - JUNE-JULY 2019-MinDocument90 pagesE&C - JUNE-JULY 2019-Minkvxrw7201No ratings yet
- B.E Computer Science and EngineeringDocument70 pagesB.E Computer Science and Engineeringapi-3838221No ratings yet
- Mitre ATT&CK Top TecnicasDocument4 pagesMitre ATT&CK Top TecnicasInfonet MundoNo ratings yet
- Virtual Private Networking: A Construction, Operation and Utilization GuideFrom EverandVirtual Private Networking: A Construction, Operation and Utilization GuideNo ratings yet
- Apps ShortutsDocument8 pagesApps Shortutssuganya004No ratings yet
- Tcs-Mock Test Paper Tatcs5Document4 pagesTcs-Mock Test Paper Tatcs5suganya004No ratings yet
- Tcs-Mock Test Paper Tatcs5Document4 pagesTcs-Mock Test Paper Tatcs5suganya004No ratings yet
- TATCS3 - Detailed SolutionDocument4 pagesTATCS3 - Detailed Solutionsuganya004No ratings yet
- Tatcs3 FinalDocument4 pagesTatcs3 Finalsuganya004No ratings yet
- TCS A and B Answer KeyDocument5 pagesTCS A and B Answer Keysuganya004No ratings yet
- Wipro 1Document4 pagesWipro 1suganya004No ratings yet
- Tcs Verbal Ability Prep - Answer KeyDocument2 pagesTcs Verbal Ability Prep - Answer Keysuganya004No ratings yet
- WiproDocument41 pagesWiprosuganya004No ratings yet
- Dacj 2 2BDocument30 pagesDacj 2 2Bsuganya004No ratings yet
- Citizen Instruction Manual C651Document38 pagesCitizen Instruction Manual C651vbadsNo ratings yet
- CPAR Lesson1 Three Major TraditionsDocument28 pagesCPAR Lesson1 Three Major TraditionsShyra Mae PonceNo ratings yet
- Contemporary Philippine Arts From The Regions MODULE 5Document5 pagesContemporary Philippine Arts From The Regions MODULE 5JOHN RULF OMAYAN100% (1)
- The Ultimate Electrical Engineering Book List With Emphasis On ElectromagneticsDocument15 pagesThe Ultimate Electrical Engineering Book List With Emphasis On ElectromagneticsAsdf FdsaNo ratings yet
- TechRef StationControllerDocument28 pagesTechRef StationControllerАлишер ГалиевNo ratings yet
- QD StudentsDocument14 pagesQD StudentsBimboy CuenoNo ratings yet
- New Holland LB90B, LB95B, LB110B, LB115B Loader Backhoe Service Repair ManualDocument21 pagesNew Holland LB90B, LB95B, LB110B, LB115B Loader Backhoe Service Repair ManualggjjjjotonesNo ratings yet
- Annex A. SHS Learning Activity Plan Career Guidance ProgramDocument11 pagesAnnex A. SHS Learning Activity Plan Career Guidance ProgramDoone Heart Santander CabuguasNo ratings yet
- CHAP 2 - Diode Applications-Clippers ClampersDocument33 pagesCHAP 2 - Diode Applications-Clippers Clampersksreddy2002No ratings yet
- Four TemperamentsDocument11 pagesFour TemperamentsVũ Hằng GiangNo ratings yet
- Application Form NNT EFDocument5 pagesApplication Form NNT EFRizky Aulya AkbarNo ratings yet
- Night Vision Technology: Seminars Electronics & Communication EngineeringDocument2 pagesNight Vision Technology: Seminars Electronics & Communication Engineeringphani98No ratings yet
- Allison Serie 9800Document2 pagesAllison Serie 9800Anonymous TEbcqw5RbT100% (2)
- How LPG Industry Operates Its Marketing OperationsDocument7 pagesHow LPG Industry Operates Its Marketing OperationsShakir AhmadNo ratings yet
- Indian Maritime University: Section-A (12x 1 12 Marks) (Answer All Questions) Choose The Correct AnswerDocument4 pagesIndian Maritime University: Section-A (12x 1 12 Marks) (Answer All Questions) Choose The Correct AnswerAmitrajeet kumarNo ratings yet
- 4 - Web Enabled Business Processes AssignmentDocument16 pages4 - Web Enabled Business Processes Assignmentrahulsanas0% (1)
- 1-Sentence-Summary: The Unexpected Joy of Being Sober Will Help You Have ADocument4 pages1-Sentence-Summary: The Unexpected Joy of Being Sober Will Help You Have ASainolzii GanboldNo ratings yet
- Multi Touch TrademarkDocument18 pagesMulti Touch TrademarkJordan GolsonNo ratings yet
- 5-6 Chapter QSTN AnswerDocument28 pages5-6 Chapter QSTN Answer02 - CM Ankita AdamNo ratings yet
- Chapter 7-User Defined PrimitivesDocument19 pagesChapter 7-User Defined PrimitivesDanh ZEUS49No ratings yet
- Board Composition and Corporate Social RespomsibilityDocument22 pagesBoard Composition and Corporate Social RespomsibilityJohnNo ratings yet
- MMC Questions For Division Finals Grade 5 - 2Document2 pagesMMC Questions For Division Finals Grade 5 - 2Rocelia Abelardo100% (1)
- Evaluation Exercise Nov 17Document3 pagesEvaluation Exercise Nov 17Isa GuerreroNo ratings yet
- Daftar Pustaka DownloadDocument4 pagesDaftar Pustaka DownloadSulaksNo ratings yet
- Binding The Strongman in Jesus NameDocument5 pagesBinding The Strongman in Jesus NamePat Ruth HollidayNo ratings yet
- 2nd Dispatch DLPD - IIT JEE - Class XI - English - PC (Physics) PDFDocument162 pages2nd Dispatch DLPD - IIT JEE - Class XI - English - PC (Physics) PDFRaja Bisht50% (8)
- Do's & Don'Ts For TurbochargersDocument7 pagesDo's & Don'Ts For Turbochargersvikrant GarudNo ratings yet
- Writing HWDocument5 pagesWriting HWMinh LêNo ratings yet