Professional Documents
Culture Documents
Describe Oakley Key Determination Protocol. Explain SSL Handshake Protocol With Example
Describe Oakley Key Determination Protocol. Explain SSL Handshake Protocol With Example
Uploaded by
pramelaCopyright:
Available Formats
You might also like
- Project Report (Digital Signatures)Document33 pagesProject Report (Digital Signatures)Uzair Shakeel0% (1)
- Network Security Chapter 3 Packet Tracer Activity Answer - Invisible AlgorithmDocument6 pagesNetwork Security Chapter 3 Packet Tracer Activity Answer - Invisible AlgorithmjesusmlazNo ratings yet
- SansDocument1,013 pagesSansSajjad AkramNo ratings yet
- Assignment-5 CSSDocument1 pageAssignment-5 CSSAllo KarimNo ratings yet
- Cryptography SEE 2018Document2 pagesCryptography SEE 2018Darshan.B.C YadavNo ratings yet
- Model Exam Cloud Computing III YrDocument3 pagesModel Exam Cloud Computing III Yrsuriyakala vinothNo ratings yet
- V18ect29 SDTVDocument2 pagesV18ect29 SDTVPavansaikumar SamudrapuNo ratings yet
- SDTVQ1Document2 pagesSDTVQ1Pavansaikumar SamudrapuNo ratings yet
- NS & ST Unit 1 Test QPDocument2 pagesNS & ST Unit 1 Test QPP RANJITHKUMARNo ratings yet
- Cit3 P.GDocument1 pageCit3 P.GAnonymous c75J3yX33No ratings yet
- Question Paper ccs354Document3 pagesQuestion Paper ccs354astronaut982003No ratings yet
- CAT-2 QPset1Document2 pagesCAT-2 QPset1Marie Claude AGACE090No ratings yet
- 3 and 4 TH Unit Cloud Computing III YrDocument2 pages3 and 4 TH Unit Cloud Computing III Yrsuriyakala vinothNo ratings yet
- CNS Assignment 3Document1 pageCNS Assignment 3Aishwarya BiradarNo ratings yet
- CAT2 QP Set2Document2 pagesCAT2 QP Set2Marie Claude AGACE090No ratings yet
- Maharaja Institute of Technology, Mysore Computer Science & Engineering First Internal's Question PaperDocument1 pageMaharaja Institute of Technology, Mysore Computer Science & Engineering First Internal's Question PaperAL VarunNo ratings yet
- Big Data QpapersDocument4 pagesBig Data QpapersSushma SNo ratings yet
- Share OS Model Paper2 V18Document3 pagesShare OS Model Paper2 V18Pavansaikumar SamudrapuNo ratings yet
- IV B.tech CN Mid-IDocument1 pageIV B.tech CN Mid-IAmbica AnnavarapuNo ratings yet
- 7 Semester - EEE Duration: 90 Minutes Date: 12.09.2019 Maximum Marks: 50Document4 pages7 Semester - EEE Duration: 90 Minutes Date: 12.09.2019 Maximum Marks: 50MATHAN RAJ MNo ratings yet
- (M19RD1101) I M. Tech I Semester (R19) Regular ExaminationsDocument1 page(M19RD1101) I M. Tech I Semester (R19) Regular Examinationsbaddem jaya chandraNo ratings yet
- CT1Document1 pageCT1Nithyasri ANo ratings yet
- Fir Cat 1 QuestionsDocument3 pagesFir Cat 1 Questions5033 - John Jabes .JNo ratings yet
- Mid Sem 1Document5 pagesMid Sem 1uttkarsh singhNo ratings yet
- Assignment 02 CSS (Unit 4)Document1 pageAssignment 02 CSS (Unit 4)Gud GuyNo ratings yet
- Ec 2354 Vlsi DesignDocument144 pagesEc 2354 Vlsi DesigndivyalakshmiNo ratings yet
- Bca - Iot 2020Document126 pagesBca - Iot 2020yogesh dhamiNo ratings yet
- CSC - 202 - Security Architecture - Subjective Question PaperDocument1 pageCSC - 202 - Security Architecture - Subjective Question PaperSanjay SinghNo ratings yet
- Model QP For Cloud ComputingDocument2 pagesModel QP For Cloud ComputingMarie Claude AGACE090No ratings yet
- (M19RD1101) I M. Tech I Semester (R19) Regular ExaminationsDocument1 page(M19RD1101) I M. Tech I Semester (R19) Regular Examinationsraja raoNo ratings yet
- FRD A280420 A2141248Document1 pageFRD A280420 A2141248Balakrishna ReddyNo ratings yet
- MCS-218 AllDocument17 pagesMCS-218 Allxitere5524No ratings yet
- Amala Ajin - CNCIT2Document1 pageAmala Ajin - CNCIT2ECE DeptNo ratings yet
- Iat1 CNDocument24 pagesIat1 CNMj KumarNo ratings yet
- BCT - Subjective QBDocument2 pagesBCT - Subjective QBabhijit kateNo ratings yet
- Model Exam IVyrDocument3 pagesModel Exam IVyrsuriyakala vinothNo ratings yet
- IoT Basics and Smart Sensors IA-II Paper - Ruchira PatoleDocument1 pageIoT Basics and Smart Sensors IA-II Paper - Ruchira PatoleAvishkar [IIT BOMBAY]No ratings yet
- Internal - 2 IV YrDocument3 pagesInternal - 2 IV Yrsuriyakala vinothNo ratings yet
- 29 Cryptography and Network Security May June 2019Document2 pages29 Cryptography and Network Security May June 2019KeerthanaNo ratings yet
- Complete AssignmentDocument5 pagesComplete AssignmentYogita PalNo ratings yet
- ISS Assi 1-5 QuesDocument5 pagesISS Assi 1-5 QuesNupoor BombNo ratings yet
- Computer Network QBDocument6 pagesComputer Network QBmonish anandNo ratings yet
- CN (18) 3rd IADocument1 pageCN (18) 3rd IASuhan BNo ratings yet
- Assignment-4 CSSDocument1 pageAssignment-4 CSSAllo KarimNo ratings yet
- 6th Sem Pyq'sDocument17 pages6th Sem Pyq'sManeeshMahajanNo ratings yet
- Is Question BankDocument4 pagesIs Question BankShaik UbedNo ratings yet
- Cns QPDocument2 pagesCns QPsridharchandrasekarNo ratings yet
- BCT - Subjective QBDocument2 pagesBCT - Subjective QBHimanshu SahuNo ratings yet
- 1.2b Timing - Sense - Timing Arc inDocument5 pages1.2b Timing - Sense - Timing Arc inSudheer GangisettyNo ratings yet
- Assignment CS801-IoT-Assignment No 3Document1 pageAssignment CS801-IoT-Assignment No 3Radheshyam ShahNo ratings yet
- Lecture Plan: Goel Institute of Technology and Management Department of Computer Science & EngineeringDocument2 pagesLecture Plan: Goel Institute of Technology and Management Department of Computer Science & EngineeringAbcNo ratings yet
- VLSI Design Assignment-1Document1 pageVLSI Design Assignment-1educational9hubNo ratings yet
- IoT 2020-21 CIE 2 SchemeDocument6 pagesIoT 2020-21 CIE 2 SchemephalanetraNo ratings yet
- Quasi-Cyclic Low-Density Parity-Check Codes in The McEliece CryptosystemDocument6 pagesQuasi-Cyclic Low-Density Parity-Check Codes in The McEliece Cryptosystemgauarv vermaNo ratings yet
- DCN III-I Mid-2 PaperDocument1 pageDCN III-I Mid-2 PaperHari KethanNo ratings yet
- Put QP MP KCS 403Document2 pagesPut QP MP KCS 403LakshitNo ratings yet
- NM 18CS742 Ia3 QPDocument1 pageNM 18CS742 Ia3 QPGeetha A LNo ratings yet
- WSN Question Bank For Mid 2Document6 pagesWSN Question Bank For Mid 2praneetha ChowdaryNo ratings yet
- 19eec431 Mid Iii QPDocument1 page19eec431 Mid Iii QPkarthickpandianeieNo ratings yet
- RDBMS(1)Document2 pagesRDBMS(1)Shubhanka ANo ratings yet
- Department of Computer Science and Engineering Internal Assessment Test-IiiDocument2 pagesDepartment of Computer Science and Engineering Internal Assessment Test-IiiOmeshwarNo ratings yet
- Multiplexed Networks for Embedded Systems: CAN, LIN, FlexRay, Safe-by-Wire...From EverandMultiplexed Networks for Embedded Systems: CAN, LIN, FlexRay, Safe-by-Wire...No ratings yet
- Internet Security: Cryptographic Principles, Algorithms and ProtocolsFrom EverandInternet Security: Cryptographic Principles, Algorithms and ProtocolsNo ratings yet
- Nee Indri Naan IllaiDocument120 pagesNee Indri Naan IllaipramelaNo ratings yet
- Neela Nayanangalil PDFDocument161 pagesNeela Nayanangalil PDFSangeetha61% (18)
- Nee Indri Naan Illai PDFDocument36 pagesNee Indri Naan Illai PDFpramelaNo ratings yet
- Kaalai Nera Katru PDFDocument152 pagesKaalai Nera Katru PDFAnonymous VZL5ZzEm83% (6)
- 15CS32 SyllabusDocument2 pages15CS32 SyllabuspramelaNo ratings yet
- 10CS661 Ia2 QBDocument3 pages10CS661 Ia2 QBpramelaNo ratings yet
- Eap Auth Protocols Leap Eap Peap1 PDFDocument4 pagesEap Auth Protocols Leap Eap Peap1 PDFHafeez MohammedNo ratings yet
- Security ProcedureDocument8 pagesSecurity ProcedureBoobalan RNo ratings yet
- Self Paced / Online Web Application Security Testing Certification CoursesDocument4 pagesSelf Paced / Online Web Application Security Testing Certification CoursesSharmila SubbarajuNo ratings yet
- Comtrend AR-5389 Default Login, Password and IP PDFDocument4 pagesComtrend AR-5389 Default Login, Password and IP PDFHTMNo ratings yet
- ECMA-386 NFC PDFDocument26 pagesECMA-386 NFC PDFLazar IvanicNo ratings yet
- Unit 1: The Importance of Computer SecurityDocument11 pagesUnit 1: The Importance of Computer SecurityATULNo ratings yet
- Vulnerabilities of IEEE 802.11i Wireless LAN CCMP ProtocolDocument6 pagesVulnerabilities of IEEE 802.11i Wireless LAN CCMP ProtocolasNo ratings yet
- FGTS: Fine-Grained Time-Sensitive Data Publishing in Attribute Based Encryption For Cloud EnvironmentDocument3 pagesFGTS: Fine-Grained Time-Sensitive Data Publishing in Attribute Based Encryption For Cloud EnvironmentHarikrishnan ShunmugamNo ratings yet
- Certified List of Candidates: Rizal - Rodriguez Rizal - RodriguezDocument4 pagesCertified List of Candidates: Rizal - Rodriguez Rizal - RodriguezLuis LacsonNo ratings yet
- PKI and Digital SignaturesWA.1Document10 pagesPKI and Digital SignaturesWA.1wasirifieNo ratings yet
- Executive Summary - Documentation Iso 27k - Implementation PlanDocument3 pagesExecutive Summary - Documentation Iso 27k - Implementation PlanGVS RaoNo ratings yet
- IT-552 Executive SummaryDocument12 pagesIT-552 Executive SummaryRoland BeauchesneNo ratings yet
- CNS MCQ QuizDocument2 pagesCNS MCQ QuizHaarish TomarNo ratings yet
- Certified List of Candidates: Tarlac - Camiling Tarlac - CamilingDocument2 pagesCertified List of Candidates: Tarlac - Camiling Tarlac - Camilingjoey bustamanteNo ratings yet
- Ulangan Mandarin Kelas 5Document8 pagesUlangan Mandarin Kelas 5Maya HeryantoNo ratings yet
- Data Protection R-1742Document12 pagesData Protection R-1742Вадим ДикийNo ratings yet
- Scanning Ike and Ipsec Based VPN With IkescanDocument9 pagesScanning Ike and Ipsec Based VPN With IkescanCristian BujorNo ratings yet
- How To Configure SSL VPN in Cyber o AmDocument13 pagesHow To Configure SSL VPN in Cyber o Amolfa0No ratings yet
- Legal and Ethical Considerations in Nursing InformaticsDocument29 pagesLegal and Ethical Considerations in Nursing InformaticsReita Ryuzaki100% (3)
- Office 365 Secure Configuration AlignmentDocument82 pagesOffice 365 Secure Configuration AlignmentGarry Martin100% (1)
- CEH Practice ExamDocument170 pagesCEH Practice Examseshahbaz100% (4)
- And Electronic Commerce (Boston: Kluwer Law International, 1998), XVDocument1 pageAnd Electronic Commerce (Boston: Kluwer Law International, 1998), XVSandra RodriguezNo ratings yet
- 5 LD Registration FormDocument4 pages5 LD Registration FormGener Taña AntonioNo ratings yet
- Network Security DesignDocument5 pagesNetwork Security DesignMahbubur RahmanNo ratings yet
- Public Key CertificateDocument9 pagesPublic Key CertificaterahulsmbjNo ratings yet
- It-Essentials Chapter 12 Exam v6.0 2016Document9 pagesIt-Essentials Chapter 12 Exam v6.0 2016Prayudha LazuardiNo ratings yet
- 117dy - Information Security PDFDocument8 pages117dy - Information Security PDFvenkiscribd444No ratings yet
Describe Oakley Key Determination Protocol. Explain SSL Handshake Protocol With Example
Describe Oakley Key Determination Protocol. Explain SSL Handshake Protocol With Example
Uploaded by
pramelaOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Describe Oakley Key Determination Protocol. Explain SSL Handshake Protocol With Example
Describe Oakley Key Determination Protocol. Explain SSL Handshake Protocol With Example
Uploaded by
pramelaCopyright:
Available Formats
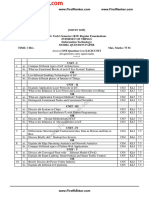
MVJ COLLEGE OF ENGINEERING
DEPARTMENT OF COMPUTER SCIENCE AND ENGINEERING
INTERNAL ASSESSMENT III
Sem VIII Duration 1.5 Hr
Subject Subject INFORMATION AND
10CS835 Max.
Date 26.05.2017 Code Name NETWORK SECURITY 25
Marks
ANSWER ANY TWO QUESTIONS. ALL THE QUESTIONS CARRY EQUAL MARKS.
Course Outcomes
CO411.5.3: Differentiate various cryptography methods, Cryptographic tools and attacks.
CO411.5.5: Describe overall process of IP security, Secure Socket Layer, Transport Layer Security, Secure
Electronic Transaction.
The following are the knowledge levels according Blooms taxonomy
K1 Remember K2- Understand K3-Apply K4-Analyze K5-Evaluate K6-Create
SL. Knowledge
Question Marks CO Code
NO Level
Explain two methods of encrypting plain text into cipher text with 6.5M CO411.5.3 K2
1 a
diagram.
Define the following terms (i)cryptography
6M CO411.5.3 K2
b (ii)Steganography
(iii)Work factor
CO411.5.5 K2
2 a Describe Oakley key determination protocol. 12.5M
CO411.5.5 K2
3 a Explain SSL Handshake protocol with example. 12.5M
IA PAPER SETTER PRINCIPAL
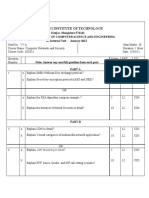
MVJ COLLEGE OF ENGINEERING
DEPARTMENT OF COMPUTER SCIENCE AND ENGINEERING
INTERNAL ASSESSMENT III
Sem VIII Duration 1.5 Hr
Subject Subject INFORMATION AND
10CS835 Max.
Date 26.05.2017 Code Name NETWORK SECURITY 25
Marks
ANSWER ANY TWO QUESTIONS. ALL THE QUESTIONS CARRY EQUAL MARKS .
Course Outcomes
CO411.5.3: Differentiate various cryptography methods, Cryptographic tools and attacks.
CO411.5.5: Describe overall process of IP security, Secure Socket Layer, Transport Layer Security, Secure
Electronic Transaction.
The following are the knowledge levels according Blooms taxonomy
K1 Remember K2- Understand K3-Apply K4-Analyze K5-Evaluate K6-Create
SL. Knowledge
Question Marks CO Code
NO Level
Explain two methods of encrypting plain text into cipher text with 6.5M CO411.5.3 K2
1 a
diagram.
Define the following terms (i)cryptography
6M CO411.5.3 K2
b (ii)Steganography
(iii)Work factor
CO411.5.5 K2
2 a Describe Oakley key determination protocol. 12.5M
CO411.5.5 K2
3 a Explain SSL Handshake protocol with example. 12.5M
IA PAPER SETTER PRINCIPAL
You might also like
- Project Report (Digital Signatures)Document33 pagesProject Report (Digital Signatures)Uzair Shakeel0% (1)
- Network Security Chapter 3 Packet Tracer Activity Answer - Invisible AlgorithmDocument6 pagesNetwork Security Chapter 3 Packet Tracer Activity Answer - Invisible AlgorithmjesusmlazNo ratings yet
- SansDocument1,013 pagesSansSajjad AkramNo ratings yet
- Assignment-5 CSSDocument1 pageAssignment-5 CSSAllo KarimNo ratings yet
- Cryptography SEE 2018Document2 pagesCryptography SEE 2018Darshan.B.C YadavNo ratings yet
- Model Exam Cloud Computing III YrDocument3 pagesModel Exam Cloud Computing III Yrsuriyakala vinothNo ratings yet
- V18ect29 SDTVDocument2 pagesV18ect29 SDTVPavansaikumar SamudrapuNo ratings yet
- SDTVQ1Document2 pagesSDTVQ1Pavansaikumar SamudrapuNo ratings yet
- NS & ST Unit 1 Test QPDocument2 pagesNS & ST Unit 1 Test QPP RANJITHKUMARNo ratings yet
- Cit3 P.GDocument1 pageCit3 P.GAnonymous c75J3yX33No ratings yet
- Question Paper ccs354Document3 pagesQuestion Paper ccs354astronaut982003No ratings yet
- CAT-2 QPset1Document2 pagesCAT-2 QPset1Marie Claude AGACE090No ratings yet
- 3 and 4 TH Unit Cloud Computing III YrDocument2 pages3 and 4 TH Unit Cloud Computing III Yrsuriyakala vinothNo ratings yet
- CNS Assignment 3Document1 pageCNS Assignment 3Aishwarya BiradarNo ratings yet
- CAT2 QP Set2Document2 pagesCAT2 QP Set2Marie Claude AGACE090No ratings yet
- Maharaja Institute of Technology, Mysore Computer Science & Engineering First Internal's Question PaperDocument1 pageMaharaja Institute of Technology, Mysore Computer Science & Engineering First Internal's Question PaperAL VarunNo ratings yet
- Big Data QpapersDocument4 pagesBig Data QpapersSushma SNo ratings yet
- Share OS Model Paper2 V18Document3 pagesShare OS Model Paper2 V18Pavansaikumar SamudrapuNo ratings yet
- IV B.tech CN Mid-IDocument1 pageIV B.tech CN Mid-IAmbica AnnavarapuNo ratings yet
- 7 Semester - EEE Duration: 90 Minutes Date: 12.09.2019 Maximum Marks: 50Document4 pages7 Semester - EEE Duration: 90 Minutes Date: 12.09.2019 Maximum Marks: 50MATHAN RAJ MNo ratings yet
- (M19RD1101) I M. Tech I Semester (R19) Regular ExaminationsDocument1 page(M19RD1101) I M. Tech I Semester (R19) Regular Examinationsbaddem jaya chandraNo ratings yet
- CT1Document1 pageCT1Nithyasri ANo ratings yet
- Fir Cat 1 QuestionsDocument3 pagesFir Cat 1 Questions5033 - John Jabes .JNo ratings yet
- Mid Sem 1Document5 pagesMid Sem 1uttkarsh singhNo ratings yet
- Assignment 02 CSS (Unit 4)Document1 pageAssignment 02 CSS (Unit 4)Gud GuyNo ratings yet
- Ec 2354 Vlsi DesignDocument144 pagesEc 2354 Vlsi DesigndivyalakshmiNo ratings yet
- Bca - Iot 2020Document126 pagesBca - Iot 2020yogesh dhamiNo ratings yet
- CSC - 202 - Security Architecture - Subjective Question PaperDocument1 pageCSC - 202 - Security Architecture - Subjective Question PaperSanjay SinghNo ratings yet
- Model QP For Cloud ComputingDocument2 pagesModel QP For Cloud ComputingMarie Claude AGACE090No ratings yet
- (M19RD1101) I M. Tech I Semester (R19) Regular ExaminationsDocument1 page(M19RD1101) I M. Tech I Semester (R19) Regular Examinationsraja raoNo ratings yet
- FRD A280420 A2141248Document1 pageFRD A280420 A2141248Balakrishna ReddyNo ratings yet
- MCS-218 AllDocument17 pagesMCS-218 Allxitere5524No ratings yet
- Amala Ajin - CNCIT2Document1 pageAmala Ajin - CNCIT2ECE DeptNo ratings yet
- Iat1 CNDocument24 pagesIat1 CNMj KumarNo ratings yet
- BCT - Subjective QBDocument2 pagesBCT - Subjective QBabhijit kateNo ratings yet
- Model Exam IVyrDocument3 pagesModel Exam IVyrsuriyakala vinothNo ratings yet
- IoT Basics and Smart Sensors IA-II Paper - Ruchira PatoleDocument1 pageIoT Basics and Smart Sensors IA-II Paper - Ruchira PatoleAvishkar [IIT BOMBAY]No ratings yet
- Internal - 2 IV YrDocument3 pagesInternal - 2 IV Yrsuriyakala vinothNo ratings yet
- 29 Cryptography and Network Security May June 2019Document2 pages29 Cryptography and Network Security May June 2019KeerthanaNo ratings yet
- Complete AssignmentDocument5 pagesComplete AssignmentYogita PalNo ratings yet
- ISS Assi 1-5 QuesDocument5 pagesISS Assi 1-5 QuesNupoor BombNo ratings yet
- Computer Network QBDocument6 pagesComputer Network QBmonish anandNo ratings yet
- CN (18) 3rd IADocument1 pageCN (18) 3rd IASuhan BNo ratings yet
- Assignment-4 CSSDocument1 pageAssignment-4 CSSAllo KarimNo ratings yet
- 6th Sem Pyq'sDocument17 pages6th Sem Pyq'sManeeshMahajanNo ratings yet
- Is Question BankDocument4 pagesIs Question BankShaik UbedNo ratings yet
- Cns QPDocument2 pagesCns QPsridharchandrasekarNo ratings yet
- BCT - Subjective QBDocument2 pagesBCT - Subjective QBHimanshu SahuNo ratings yet
- 1.2b Timing - Sense - Timing Arc inDocument5 pages1.2b Timing - Sense - Timing Arc inSudheer GangisettyNo ratings yet
- Assignment CS801-IoT-Assignment No 3Document1 pageAssignment CS801-IoT-Assignment No 3Radheshyam ShahNo ratings yet
- Lecture Plan: Goel Institute of Technology and Management Department of Computer Science & EngineeringDocument2 pagesLecture Plan: Goel Institute of Technology and Management Department of Computer Science & EngineeringAbcNo ratings yet
- VLSI Design Assignment-1Document1 pageVLSI Design Assignment-1educational9hubNo ratings yet
- IoT 2020-21 CIE 2 SchemeDocument6 pagesIoT 2020-21 CIE 2 SchemephalanetraNo ratings yet
- Quasi-Cyclic Low-Density Parity-Check Codes in The McEliece CryptosystemDocument6 pagesQuasi-Cyclic Low-Density Parity-Check Codes in The McEliece Cryptosystemgauarv vermaNo ratings yet
- DCN III-I Mid-2 PaperDocument1 pageDCN III-I Mid-2 PaperHari KethanNo ratings yet
- Put QP MP KCS 403Document2 pagesPut QP MP KCS 403LakshitNo ratings yet
- NM 18CS742 Ia3 QPDocument1 pageNM 18CS742 Ia3 QPGeetha A LNo ratings yet
- WSN Question Bank For Mid 2Document6 pagesWSN Question Bank For Mid 2praneetha ChowdaryNo ratings yet
- 19eec431 Mid Iii QPDocument1 page19eec431 Mid Iii QPkarthickpandianeieNo ratings yet
- RDBMS(1)Document2 pagesRDBMS(1)Shubhanka ANo ratings yet
- Department of Computer Science and Engineering Internal Assessment Test-IiiDocument2 pagesDepartment of Computer Science and Engineering Internal Assessment Test-IiiOmeshwarNo ratings yet
- Multiplexed Networks for Embedded Systems: CAN, LIN, FlexRay, Safe-by-Wire...From EverandMultiplexed Networks for Embedded Systems: CAN, LIN, FlexRay, Safe-by-Wire...No ratings yet
- Internet Security: Cryptographic Principles, Algorithms and ProtocolsFrom EverandInternet Security: Cryptographic Principles, Algorithms and ProtocolsNo ratings yet
- Nee Indri Naan IllaiDocument120 pagesNee Indri Naan IllaipramelaNo ratings yet
- Neela Nayanangalil PDFDocument161 pagesNeela Nayanangalil PDFSangeetha61% (18)
- Nee Indri Naan Illai PDFDocument36 pagesNee Indri Naan Illai PDFpramelaNo ratings yet
- Kaalai Nera Katru PDFDocument152 pagesKaalai Nera Katru PDFAnonymous VZL5ZzEm83% (6)
- 15CS32 SyllabusDocument2 pages15CS32 SyllabuspramelaNo ratings yet
- 10CS661 Ia2 QBDocument3 pages10CS661 Ia2 QBpramelaNo ratings yet
- Eap Auth Protocols Leap Eap Peap1 PDFDocument4 pagesEap Auth Protocols Leap Eap Peap1 PDFHafeez MohammedNo ratings yet
- Security ProcedureDocument8 pagesSecurity ProcedureBoobalan RNo ratings yet
- Self Paced / Online Web Application Security Testing Certification CoursesDocument4 pagesSelf Paced / Online Web Application Security Testing Certification CoursesSharmila SubbarajuNo ratings yet
- Comtrend AR-5389 Default Login, Password and IP PDFDocument4 pagesComtrend AR-5389 Default Login, Password and IP PDFHTMNo ratings yet
- ECMA-386 NFC PDFDocument26 pagesECMA-386 NFC PDFLazar IvanicNo ratings yet
- Unit 1: The Importance of Computer SecurityDocument11 pagesUnit 1: The Importance of Computer SecurityATULNo ratings yet
- Vulnerabilities of IEEE 802.11i Wireless LAN CCMP ProtocolDocument6 pagesVulnerabilities of IEEE 802.11i Wireless LAN CCMP ProtocolasNo ratings yet
- FGTS: Fine-Grained Time-Sensitive Data Publishing in Attribute Based Encryption For Cloud EnvironmentDocument3 pagesFGTS: Fine-Grained Time-Sensitive Data Publishing in Attribute Based Encryption For Cloud EnvironmentHarikrishnan ShunmugamNo ratings yet
- Certified List of Candidates: Rizal - Rodriguez Rizal - RodriguezDocument4 pagesCertified List of Candidates: Rizal - Rodriguez Rizal - RodriguezLuis LacsonNo ratings yet
- PKI and Digital SignaturesWA.1Document10 pagesPKI and Digital SignaturesWA.1wasirifieNo ratings yet
- Executive Summary - Documentation Iso 27k - Implementation PlanDocument3 pagesExecutive Summary - Documentation Iso 27k - Implementation PlanGVS RaoNo ratings yet
- IT-552 Executive SummaryDocument12 pagesIT-552 Executive SummaryRoland BeauchesneNo ratings yet
- CNS MCQ QuizDocument2 pagesCNS MCQ QuizHaarish TomarNo ratings yet
- Certified List of Candidates: Tarlac - Camiling Tarlac - CamilingDocument2 pagesCertified List of Candidates: Tarlac - Camiling Tarlac - Camilingjoey bustamanteNo ratings yet
- Ulangan Mandarin Kelas 5Document8 pagesUlangan Mandarin Kelas 5Maya HeryantoNo ratings yet
- Data Protection R-1742Document12 pagesData Protection R-1742Вадим ДикийNo ratings yet
- Scanning Ike and Ipsec Based VPN With IkescanDocument9 pagesScanning Ike and Ipsec Based VPN With IkescanCristian BujorNo ratings yet
- How To Configure SSL VPN in Cyber o AmDocument13 pagesHow To Configure SSL VPN in Cyber o Amolfa0No ratings yet
- Legal and Ethical Considerations in Nursing InformaticsDocument29 pagesLegal and Ethical Considerations in Nursing InformaticsReita Ryuzaki100% (3)
- Office 365 Secure Configuration AlignmentDocument82 pagesOffice 365 Secure Configuration AlignmentGarry Martin100% (1)
- CEH Practice ExamDocument170 pagesCEH Practice Examseshahbaz100% (4)
- And Electronic Commerce (Boston: Kluwer Law International, 1998), XVDocument1 pageAnd Electronic Commerce (Boston: Kluwer Law International, 1998), XVSandra RodriguezNo ratings yet
- 5 LD Registration FormDocument4 pages5 LD Registration FormGener Taña AntonioNo ratings yet
- Network Security DesignDocument5 pagesNetwork Security DesignMahbubur RahmanNo ratings yet
- Public Key CertificateDocument9 pagesPublic Key CertificaterahulsmbjNo ratings yet
- It-Essentials Chapter 12 Exam v6.0 2016Document9 pagesIt-Essentials Chapter 12 Exam v6.0 2016Prayudha LazuardiNo ratings yet
- 117dy - Information Security PDFDocument8 pages117dy - Information Security PDFvenkiscribd444No ratings yet