Professional Documents
Culture Documents
Wep Keys (64 Bits) : Month Week Date Password Users
Wep Keys (64 Bits) : Month Week Date Password Users
Uploaded by
pangdownloadlang0 ratings0% found this document useful (0 votes)
10 views3 pagesThe document contains tables listing WEP keys and WPA/PSK keys used for wireless network security on a monthly basis over a year. Each table includes the month, week, date, password, and number of users. It provides 64-bit WEP keys for each week from May to December and blank entries for the WPA/PSK keys, suggesting the network migrated to a more secure authentication protocol.
Original Description:
kuill
Original Title
WIFI
Copyright
© © All Rights Reserved
Available Formats
XLSX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document contains tables listing WEP keys and WPA/PSK keys used for wireless network security on a monthly basis over a year. Each table includes the month, week, date, password, and number of users. It provides 64-bit WEP keys for each week from May to December and blank entries for the WPA/PSK keys, suggesting the network migrated to a more secure authentication protocol.
Copyright:
© All Rights Reserved
Available Formats
Download as XLSX, PDF, TXT or read online from Scribd
Download as xlsx, pdf, or txt
0 ratings0% found this document useful (0 votes)
10 views3 pagesWep Keys (64 Bits) : Month Week Date Password Users
Wep Keys (64 Bits) : Month Week Date Password Users
Uploaded by
pangdownloadlangThe document contains tables listing WEP keys and WPA/PSK keys used for wireless network security on a monthly basis over a year. Each table includes the month, week, date, password, and number of users. It provides 64-bit WEP keys for each week from May to December and blank entries for the WPA/PSK keys, suggesting the network migrated to a more secure authentication protocol.
Copyright:
© All Rights Reserved
Available Formats
Download as XLSX, PDF, TXT or read online from Scribd
Download as xlsx, pdf, or txt
You are on page 1of 3
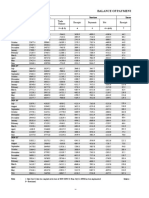
WEP KEYS (64 BITS)
MONTH WEEK DATE PASSWORD USERS
1 2926736E5B
2 4C21536526
MAY
3 215B637A21
4 4627435A40
1 576D63232B
2 2C766C756D
JUNE
3 6A47782227
4 3B46247C70
1 665D57692A
2 233A4B2759
JULY
3 44477C5371
4 7446284D23
1 5C59707C64
2 69272B732B
AUGUST
3 4759202A5C
4 5A58525677
1 5E2A77515C
2 5D7B377A7B
SEPTEMBER
3 7B5A372B5B
4 2C49637D2B
1 2C7067652C
2 5B4D2B4C75
OCTOBER
3 6C5A4A7427
4 7C52335143
1 6C3678555A
2 755125416A
NOVEMBER
3 6D6837246E
4 4163493476
1 4B243C517A
2 283D5A646A
DECEMBER
3 79613F6D75
4 363422775F
WPA/PSK KEYS
MONTH WEEK DATE
1
2
MAY
3
4
1
2
JUNE
3
4
1
2
JULY
3
4
1
2
AUGUST
3
4
1
2
SEPTEMBER
3
4
1
2
OCTOBER
3
4
1
2
NOVEMBER
3
4
1
2
DECEMBER
3
4
WPA/PSK KEYS
PASSWORD USERS
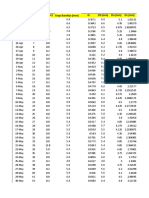
3C705E27484F425F2B675B3944526367675C6B6D
356F5C293D53703B7857673D56206C6A5B39223D
7A686E543D73473C3B386F787776632C79647E28
593B636A6E4E3E4D6E775C27395F276E276E3C6C
237E497B527828372A4A6952333529383C404942
5D2A4056205E7B452E37467974612577206B4574
405D24533D2022733264767E3C672C53773D6746
2431674F5A41274336314724626C332F6F6E2976
6D773F5A716B77637E4E62457D425F5B37627A22
7C6F283754577049705A7B4F7D3B515D633C3067
6D536D3B6B583533476D3F21596D43466A4E3428
7B66565B213449582475406C34292F6D6A487058
647030777C7B4A773334464030693F34236C6263
303A45534F4D4B53754A433B3346205466612F48
3436627440285E6177267B67234436472D3E3130
3436627440285E6177267B67234436472D3E3130
444C334F715F67305E502D70244C222A20516942
732956365A5429333967372327277B694F562729
4B4026625F626C613A715E336966576B6D4A5525
3C47537A3D656C7424754A7C793E397E483E387C
2B496A6B3F77454E51784D38205C425A54373939
4E38725F5630235E6C3B2D3543464058493C5468
4E38725F5630235E6C3B2D3543464058493C5468
417E407D292D3D524D705F254567335C4267536A
3745726C206E2B3C4C414B54783F792E777A7721
6F7E2A4E4B204A33613D3B7B304A455A6A4F2655
58545B3254295F2137574E775D6B302F73494C72
6A7A525D2128336D6A275D79395D35765F557946
455A5170424B734E48522D7849495648524B4065
2C724B3A30585A385F512C536C50474B3750277C
52656A5524635F23377453213B527E215A515D27
23397D29273A48215E22782341292E7C6C622533
You might also like
- BMC Helix IT Service Management Deployment 22.1.06: Technical DocumentationDocument486 pagesBMC Helix IT Service Management Deployment 22.1.06: Technical DocumentationSupria GeraNo ratings yet
- Huanyang VFD Spindle Control: Setting Up The VFDDocument5 pagesHuanyang VFD Spindle Control: Setting Up The VFDSandro Alcantara100% (1)
- QSS3001 Service ManualDocument734 pagesQSS3001 Service ManualSimionStoianovici67% (3)
- Month Week Date Changed Password People Who Requested: Wep Keys (64 Bits)Document1 pageMonth Week Date Changed Password People Who Requested: Wep Keys (64 Bits)pangdownloadlangNo ratings yet
- Year End Summery ReportDocument2 pagesYear End Summery Reportdushani thathsaraniNo ratings yet
- Purchasing Managers' Index, 2010 MarchDocument4 pagesPurchasing Managers' Index, 2010 MarchSwedbank AB (publ)No ratings yet
- Northeast Pantry 2009 Ethnic Origin HouseholdDocument12 pagesNortheast Pantry 2009 Ethnic Origin HouseholdGary NyeNo ratings yet
- Electricity BillDocument1 pageElectricity BillSahil KumarNo ratings yet
- Purchasing Managers' Index Report May 2009Document4 pagesPurchasing Managers' Index Report May 2009Swedbank AB (publ)No ratings yet
- CHAS Medical Clinic 2009: Ethnic Origin Household InformationDocument11 pagesCHAS Medical Clinic 2009: Ethnic Origin Household InformationGary NyeNo ratings yet
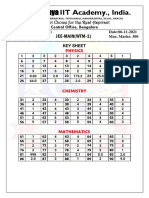
- Sec: SR Iit (Outgoing) Date:16-03-24 Time:3HRS GTM-1 Max. Marks: 300Document1 pageSec: SR Iit (Outgoing) Date:16-03-24 Time:3HRS GTM-1 Max. Marks: 300Vinod AgrawalNo ratings yet
- Cid 159925Document4 pagesCid 159925Swedbank AB (publ)No ratings yet
- Report Card: SR No Name Maths Sci His Geo Eco Total PercentageDocument8 pagesReport Card: SR No Name Maths Sci His Geo Eco Total PercentageSushant AminNo ratings yet
- 23-07-2023 - SS KeyDocument1 page23-07-2023 - SS KeyRAJANI SAINo ratings yet
- Fbos Release No:Xx, 2019, Seasonally Adjusted Monthly Visitor Arrivals, November 2019, Page 6Document2 pagesFbos Release No:Xx, 2019, Seasonally Adjusted Monthly Visitor Arrivals, November 2019, Page 6Eroni PuamauNo ratings yet
- Headstart/ECEAP 2009 Ethnic OriginDocument10 pagesHeadstart/ECEAP 2009 Ethnic OriginGary NyeNo ratings yet
- Sri Chaitanya IIT Academy., India.: JEE-MAIN (WTM-1)Document1 pageSri Chaitanya IIT Academy., India.: JEE-MAIN (WTM-1)Kumkum KumbarahalliNo ratings yet
- Lab Report-2 Irrigation Engineering: Lec. UkashaDocument6 pagesLab Report-2 Irrigation Engineering: Lec. UkashaAhmed SulemanNo ratings yet
- DV&PS - Lab 3 & 4Document6 pagesDV&PS - Lab 3 & 4DHWANI JOSHINo ratings yet
- Tracking SignalDocument9 pagesTracking SignallisnaNo ratings yet
- Sapphire Textile Mills LTD No 2: (70 DENIER)Document19 pagesSapphire Textile Mills LTD No 2: (70 DENIER)Danish NawazNo ratings yet
- דרך עץ החייםDocument96 pagesדרך עץ החייםTomNo ratings yet
- UCMAS Qatar Educational Center Level 5 - Abacus and Mental Worksheets 5Document3 pagesUCMAS Qatar Educational Center Level 5 - Abacus and Mental Worksheets 5malay_ex0% (1)
- Period: Receipts Payments Net Receipts Export (F.o.b) Import (F.o.b) Trade BalanceDocument3 pagesPeriod: Receipts Payments Net Receipts Export (F.o.b) Import (F.o.b) Trade BalanceJannat TaqwaNo ratings yet
- BeefDocument82 pagesBeefFelix PopNo ratings yet
- Population by Single-Year Age Classification and Sex: 2018 Single-Year Age Classification Cabanatuan CityDocument3 pagesPopulation by Single-Year Age Classification and Sex: 2018 Single-Year Age Classification Cabanatuan CityAnonymous Pu7TnbCFC0No ratings yet
- 16..01.24 - SR - STAR CO-SC (MODEL-A, B&C) - Jee - Main - GTM-18 (N) - KEY&SOLDocument1 page16..01.24 - SR - STAR CO-SC (MODEL-A, B&C) - Jee - Main - GTM-18 (N) - KEY&SOLtiwariakhilesh21361No ratings yet
- Data Ilustrasi ExcelDocument7 pagesData Ilustrasi ExcelHari putraNo ratings yet
- Data Set - 5: No Visit Income Travel Vacation Hhsize AgeDocument1 pageData Set - 5: No Visit Income Travel Vacation Hhsize AgeLAWRENCE VIVEK TOPPO PGP 2019-21 BatchNo ratings yet
- Rata2 Re-Use 2017Document7 pagesRata2 Re-Use 2017Anonymous 2f6R7NnWANo ratings yet
- Nilai Ulangan HarianDocument3 pagesNilai Ulangan HarianMOCHAMAD FATAKHUL MUFIDNo ratings yet
- HVAC Invoice Details 2Document12 pagesHVAC Invoice Details 2padmasunilNo ratings yet
- Jee Main Answer Key: Code: A DATE: 02/04/2017Document1 pageJee Main Answer Key: Code: A DATE: 02/04/2017NeelMehtaNo ratings yet
- GST Calculation - XLSX TilakDocument18 pagesGST Calculation - XLSX TilakTarun sharmaNo ratings yet
- Lab Report-2 Irrigation Engineering: Lec. UkashaDocument7 pagesLab Report-2 Irrigation Engineering: Lec. UkashaAhmed SulemanNo ratings yet
- SpecialDocument6 pagesSpecialKRISHNENDU DUTTANo ratings yet
- Book 1Document7 pagesBook 1Yono HpNo ratings yet
- Rajasthan SATDocument1 pageRajasthan SATNikhil prajapatiNo ratings yet
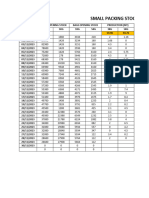
- Small Packing StockDocument5 pagesSmall Packing StockrajatNo ratings yet
- Agricultural Management Practices NSC QP Nov 2023 EngDocument18 pagesAgricultural Management Practices NSC QP Nov 2023 EngCamilleNo ratings yet
- Id International: B-39 Hosiery Complex Phase-2 NoidaDocument3 pagesId International: B-39 Hosiery Complex Phase-2 Noidaid internationalNo ratings yet
- Incoming Sr.C-120 - JEE Mains - WTM - Key & Sol'sDocument1 pageIncoming Sr.C-120 - JEE Mains - WTM - Key & Sol'snikhil sridharaNo ratings yet
- AbtDocument2 pagesAbtsudirmanNo ratings yet
- AbtDocument2 pagesAbtsudirmanNo ratings yet
- All Us Bef 2018Document6 pagesAll Us Bef 2018Araminta PranotoNo ratings yet
- c0 User - Grade 2017 1 2017 2 2017 3 2017 4 2017 5: MonthDocument6 pagesc0 User - Grade 2017 1 2017 2 2017 3 2017 4 2017 5: MonthAraminta PranotoNo ratings yet
- Design Weather Parameters - DXBDocument1 pageDesign Weather Parameters - DXBtony thomasNo ratings yet
- 2014 IEX Electricity PricesDocument1 page2014 IEX Electricity PriceshimanshusabooNo ratings yet
- 2022 Daily StatsDocument9 pages2022 Daily Statsjeromebpalacio5058No ratings yet
- Forecasting - Muhammad Idzhar Faisa - 120310200084Document10 pagesForecasting - Muhammad Idzhar Faisa - 120310200084MUHAMMAD IDZHAR FAISANo ratings yet
- Data 1 - ExperimentDocument1 pageData 1 - Experimentparas bagdeNo ratings yet
- General Mathematics FsoDocument4 pagesGeneral Mathematics FsoNDTVNo ratings yet
- Maximum Deflections Forload Case Wind - X: X:8 .0 9 M M A T N O D E 2 7 1 3 Y:-0.22 MM Atnode 352 Z:-0.00 MM Atnode 35Document1 pageMaximum Deflections Forload Case Wind - X: X:8 .0 9 M M A T N O D E 2 7 1 3 Y:-0.22 MM Atnode 352 Z:-0.00 MM Atnode 35Anonymous koR9VtfNo ratings yet
- Calculo Del Calculo de Momento de Riego de Un Cultivo Caso Del TrigoDocument11 pagesCalculo Del Calculo de Momento de Riego de Un Cultivo Caso Del TrigoJames Albert BarreraNo ratings yet
- 28-03-2024 - Osr - Iit - Jee Main Model - GTM-6 - KeyDocument1 page28-03-2024 - Osr - Iit - Jee Main Model - GTM-6 - KeychaitubudatiNo ratings yet
- Core Industries 2011-12Document10 pagesCore Industries 2011-12RhytaNo ratings yet
- Data Are From Energy Information Administration October 2008 InternationalDocument30 pagesData Are From Energy Information Administration October 2008 Internationalapi-26190745No ratings yet
- Imds Fe: Imda 2017Document7 pagesImds Fe: Imda 2017Davila Yalli JhonNo ratings yet
- Questionbookletseries ADocument1 pageQuestionbookletseries ArashmiNo ratings yet
- PLTG Peaking - Juli 2023Document402 pagesPLTG Peaking - Juli 2023Jeffry BahariNo ratings yet
- Day 10.8e56f1aDocument20 pagesDay 10.8e56f1anjatoliya123No ratings yet
- Machine Verification DataDocument3 pagesMachine Verification Dataopenymartine11No ratings yet
- Tsong GohDocument3 pagesTsong GohpangdownloadlangNo ratings yet
- Case FirstTennBankDocument5 pagesCase FirstTennBankpangdownloadlangNo ratings yet
- Option Explicit Private Sub Cmdcrayonscompute - Click If Val (Txtstockcrayons - Text) Val (Cbocrayonsqty - Text) ThenDocument3 pagesOption Explicit Private Sub Cmdcrayonscompute - Click If Val (Txtstockcrayons - Text) Val (Cbocrayonsqty - Text) ThenpangdownloadlangNo ratings yet
- Apex ManualDocument17 pagesApex ManualpangdownloadlangNo ratings yet
- Month Week Date Changed Password People Who Requested: Wep Keys (64 Bits)Document1 pageMonth Week Date Changed Password People Who Requested: Wep Keys (64 Bits)pangdownloadlangNo ratings yet
- 04 AcknowledgementDocument2 pages04 AcknowledgementpangdownloadlangNo ratings yet
- Problem Solving and Algorithm Design: Nell Dale - John LewisDocument43 pagesProblem Solving and Algorithm Design: Nell Dale - John LewispangdownloadlangNo ratings yet
- Meal Time1Document1 pageMeal Time1pangdownloadlangNo ratings yet
- Meal Time: Lunch: 12:00 NN - 1:00 PM Dinner: 6:00 PM - 7:00 PM Breakfast: 7:00 Am - 8:00 AMDocument1 pageMeal Time: Lunch: 12:00 NN - 1:00 PM Dinner: 6:00 PM - 7:00 PM Breakfast: 7:00 Am - 8:00 AMpangdownloadlangNo ratings yet
- Tutorial 6Document8 pagesTutorial 6yılmaz çepniNo ratings yet
- Lecture 6Document7 pagesLecture 6Milind BhatiaNo ratings yet
- DEVNET-1200-There and Back-A Network Automation JourneyDocument26 pagesDEVNET-1200-There and Back-A Network Automation Journeyhabib kamaieNo ratings yet
- Roof PurlinsDocument2 pagesRoof PurlinsmaheshbandhamNo ratings yet
- Decoding Raw Frames - Generic - Libre Space CommunityDocument7 pagesDecoding Raw Frames - Generic - Libre Space CommunityGeneration GenerationNo ratings yet
- BiometricsDocument22 pagesBiometricsJaspreet BarmotaNo ratings yet
- Introduction To WPFDocument28 pagesIntroduction To WPFPonni MoluNo ratings yet
- Student CertificationDocument4 pagesStudent CertificationGegeyz1028No ratings yet
- Introduction To Relational ModelDocument55 pagesIntroduction To Relational ModelHimanshiNo ratings yet
- Jurnal NasalDocument7 pagesJurnal Nasalnagya novraskaNo ratings yet
- 02 Gaddis Python Lecture PPT Ch02Document71 pages02 Gaddis Python Lecture PPT Ch02Ugaas ShaahdiidNo ratings yet
- Evaluation of Properties of Coconut Coir Fiber Reinforced Concrete PDFDocument86 pagesEvaluation of Properties of Coconut Coir Fiber Reinforced Concrete PDFKit Meng LimNo ratings yet
- 2022 - 2 (1004) Assignment 2Document3 pages2022 - 2 (1004) Assignment 2skylerNo ratings yet
- dsd412 App111 GroundingDocument2 pagesdsd412 App111 GroundingKs BharathiyarNo ratings yet
- Lecture 2.2 Merge Sort AlgorithmsDocument59 pagesLecture 2.2 Merge Sort AlgorithmsPablo ChanNo ratings yet
- 09 Flight Techniques 747 400 v10Document18 pages09 Flight Techniques 747 400 v10flightstudent100% (1)
- Prestressed Concrete Structures Unit-3Document15 pagesPrestressed Concrete Structures Unit-3chinnaNo ratings yet
- IS 2553 - Part 1 Amd 1 - Fire Resistant GlassDocument7 pagesIS 2553 - Part 1 Amd 1 - Fire Resistant GlassNoel Federer SarkarNo ratings yet
- Scotchman Circular Cold Saw Operators Manual SUP-600-NFDocument36 pagesScotchman Circular Cold Saw Operators Manual SUP-600-NFJay100% (1)
- AN713 - Controller Area Network (CAN) BasicsDocument9 pagesAN713 - Controller Area Network (CAN) BasicsRam Krishan SharmaNo ratings yet
- Experiment 1 - Crank and RodDocument3 pagesExperiment 1 - Crank and Rodalextty75% (12)
- Sample Question Paper 1Document6 pagesSample Question Paper 1aaravNo ratings yet
- GPS Engine Board: User's GuideDocument13 pagesGPS Engine Board: User's GuideGábor SvercsokNo ratings yet
- SnoopyDocument25 pagesSnoopyM VerbeeckNo ratings yet
- Shabeer Et Al-2018-Journal of PerinatologyDocument8 pagesShabeer Et Al-2018-Journal of PerinatologyrenataNo ratings yet
- Open Ended LabDocument11 pagesOpen Ended LabM. TahmanNo ratings yet
- Report Survey Setting Out Civil EngineeringDocument11 pagesReport Survey Setting Out Civil EngineeringMuhammad MuazzamNo ratings yet