Professional Documents
Culture Documents
Ijit8558 12
Ijit8558 12
Uploaded by
Harini VemulaCopyright:
Available Formats
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5834)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (349)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (824)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (405)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- 08 GULN ZXRAN Base Station TroubleshootingDocument39 pages08 GULN ZXRAN Base Station Troubleshootinga2227 jglNo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Websense Web Security Gateway DLP ICAP IntegrationDocument7 pagesWebsense Web Security Gateway DLP ICAP IntegrationM_BBNo ratings yet
- Inventions and InnovationsDocument77 pagesInventions and InnovationsHarini VemulaNo ratings yet
- Creativity: Madhav Madhira IIT & JNTU HyderabadDocument137 pagesCreativity: Madhav Madhira IIT & JNTU HyderabadHarini VemulaNo ratings yet
- Research Quality - Evaluation Parameters: Dr. A. Gopala Krishna Professor Department of Mechanical EngineeringDocument17 pagesResearch Quality - Evaluation Parameters: Dr. A. Gopala Krishna Professor Department of Mechanical EngineeringHarini VemulaNo ratings yet
- VRN 3 5 16Document129 pagesVRN 3 5 16Harini VemulaNo ratings yet
- Design, Validation and Correlation of Characterized SODIMM Modules Supporting DDR3 Memory InterfaceDocument11 pagesDesign, Validation and Correlation of Characterized SODIMM Modules Supporting DDR3 Memory InterfaceHarini VemulaNo ratings yet
- Excersizes in CREATIVITYDocument47 pagesExcersizes in CREATIVITYHarini VemulaNo ratings yet
- Green Cellular Network Deployment To Reduce RF Pollution: Sumit Katiyar Prof. R. K. Jain Prof. N. K. AgrawalDocument6 pagesGreen Cellular Network Deployment To Reduce RF Pollution: Sumit Katiyar Prof. R. K. Jain Prof. N. K. AgrawalHarini VemulaNo ratings yet
- The PSD of The Random Process X (T) With Mean I andDocument11 pagesThe PSD of The Random Process X (T) With Mean I andHarini VemulaNo ratings yet
- Unit-2: Operations On Single Random VariablesDocument11 pagesUnit-2: Operations On Single Random VariablesHarini VemulaNo ratings yet
- Refer Slide Time: 00:35Document15 pagesRefer Slide Time: 00:35Harini VemulaNo ratings yet
- Satellite Navigation & The Global Positioning System: Figure 1: GPS Block II-F SatelliteDocument26 pagesSatellite Navigation & The Global Positioning System: Figure 1: GPS Block II-F SatelliteHarini Vemula100% (1)
- Lec 22Document8 pagesLec 22Harini VemulaNo ratings yet
- Review On Millimeter Wave Antennas-Potential Candidate For 5G Enabled ApplicationsDocument8 pagesReview On Millimeter Wave Antennas-Potential Candidate For 5G Enabled ApplicationsHarini VemulaNo ratings yet
- Lec 14Document8 pagesLec 14Harini VemulaNo ratings yet
- Investigation of Three Dimensional Empirical Indoor Path Loss Models For Femtocell NetworksDocument11 pagesInvestigation of Three Dimensional Empirical Indoor Path Loss Models For Femtocell NetworksHarini VemulaNo ratings yet
- M.Tech Project Proposal FormatDocument3 pagesM.Tech Project Proposal FormatHarini VemulaNo ratings yet
- Acadamic Calender For 2012-13Document1 pageAcadamic Calender For 2012-13Harini VemulaNo ratings yet
- 829-Research Article-3061-2-10-20181209Document6 pages829-Research Article-3061-2-10-20181209Harini VemulaNo ratings yet
- Mooc: 2016 July: Fundamentals of MIMO Wireless CommunicationsDocument23 pagesMooc: 2016 July: Fundamentals of MIMO Wireless CommunicationsHarini VemulaNo ratings yet
- Let2 WDocument46 pagesLet2 WGetnete degemuNo ratings yet
- Open FlowDocument20 pagesOpen FlowAhmed SharifNo ratings yet
- Important Cisco Chow CommandsDocument21 pagesImportant Cisco Chow CommandsSyed Rahmath AliNo ratings yet
- Computer Networks TFTP ReportDocument11 pagesComputer Networks TFTP ReportNour AllamNo ratings yet
- Enabling and Understanding Iot TechnologiesDocument21 pagesEnabling and Understanding Iot TechnologiesMelhemhelouNo ratings yet
- Scrip Ega Chanel New Version 2 Isp Game Isp KhususDocument43 pagesScrip Ega Chanel New Version 2 Isp Game Isp KhususYan Mahendra FNo ratings yet
- RG-1000e Remote Gateway: User GuideDocument40 pagesRG-1000e Remote Gateway: User GuideThanh Kieu TienNo ratings yet
- WLC-Best Practices-SecurityDocument3 pagesWLC-Best Practices-SecurityBudiartoNo ratings yet
- Cdma PDFDocument22 pagesCdma PDFMahmoud MallahNo ratings yet
- Optimum 32bit CRC For Internet KOOPMANDocument10 pagesOptimum 32bit CRC For Internet KOOPMANgoutambiswaNo ratings yet
- 60-Objects TabDocument11 pages60-Objects TabArun SomashekarNo ratings yet
- User ManagerDocument4 pagesUser ManagerHarry Chan Putra. SP. MTCNA. MTCTCE. MTCRENo ratings yet
- En ReleaseNotes FirewareXTM 11-3-2Document52 pagesEn ReleaseNotes FirewareXTM 11-3-2Mario Diaz ParhamNo ratings yet
- MX Warm Spare - High Availability PairDocument9 pagesMX Warm Spare - High Availability PairDaveNo ratings yet
- 5G For Military Communications 5G For Military Communications 5G For Military CommunicationsDocument10 pages5G For Military Communications 5G For Military Communications 5G For Military Communicationssamaa adelNo ratings yet
- TSN Schneele AFDX 0515 v01 - 2Document31 pagesTSN Schneele AFDX 0515 v01 - 2caportNo ratings yet
- VPN Remote Access 2ndeditionDocument246 pagesVPN Remote Access 2ndeditionMilton ReyesNo ratings yet
- 12-MPLS Configuration CommandsDocument40 pages12-MPLS Configuration CommandsEder Ollora ZaballaNo ratings yet
- SniffingDocument120 pagesSniffingWoyNo ratings yet
- ENSC427 Team6 ReportDocument22 pagesENSC427 Team6 ReportAnonymous TTVlXoNo ratings yet
- SQF NS2Document6 pagesSQF NS2Sharmain QuNo ratings yet
- AResC63-2013 en PDFDocument146 pagesAResC63-2013 en PDFDaljeet Kaur DhaliwalNo ratings yet
- Ece@booksDocument6 pagesEce@booksSrinivas GoudNo ratings yet
- App Note DVB S2x and NovelSat NS3Document8 pagesApp Note DVB S2x and NovelSat NS3csystemsNo ratings yet
- Zero-Trust Remote AccessDocument16 pagesZero-Trust Remote Accessoscar tebarNo ratings yet
- Connecting Lans, Backbone Networks, and Virtual LansDocument30 pagesConnecting Lans, Backbone Networks, and Virtual LansIndra AtmajaNo ratings yet
- Zte ZXSDR b8200 Product DescriptionDocument32 pagesZte ZXSDR b8200 Product DescriptionterdpongNo ratings yet
- First CourseDocument5 pagesFirst CoursefifaacessNo ratings yet
Ijit8558 12
Ijit8558 12
Uploaded by
Harini VemulaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Ijit8558 12
Ijit8558 12
Uploaded by
Harini VemulaCopyright:
Available Formats
ISSN 2321-8665
Vol.04,Issue.01,
WWW.IJITECH.ORG January-2016,
Pages:0058-0063
Improved Energy Based Security System for Mobile Ad-Hoc Networks with
Belief Management System
K.KARTHEEKA1, V.HARINI2, S.SRINIVAS3
1
PG Scholar, Dept of ECE, Vardhaman College of Engineering, Hyderabad, JNTUH, TS, India, Email: karthi.be21@gmail.com.
2
Asst Prof, Dept of ECE, Vardhaman College of Engineering, Hyderabad, JNTUH, TS, India, Email: v.harini@vardhaman.org.
3
Assoc Prof, Dept of ECE, Vardhaman College of Engineering, Hyderabad, JNTUH, TS, India, Email:s.srinivas@vardhaman.org.
Abstract: Our final goal is to realize the protection while decentralised manner. All peers square measure each
not looking forward to key management in MANET with shoppers and suppliers of resources and might access one
new trusting mechanism known as Trustworthy Energy another directly while not negotiator peers. Compared with a
management system. With recent advances in wireless centralized system, a peer-to-peer (P2P) system provides a
technologies and mobile devices, Mobile Ad hoc Networks straightforward thanks to mixture massive amounts of
became widespread as a key communication technology in resources residing on the sting of web or in ad-hoc networks
military plan of action environments. There square measure with a coffee price of system maintenance. P2P systems
in the main 2 issues in security techniques, one is depends on have attracted increasing attention from researchers recently,
the key management and another one is to depends on some however they additionally mention some issues. Since peers
intermediate nodes. We tend to propose a unified trust square measure heterogeneous, some peers can be
management theme that enhances the protection in benevolent in providing services. Some can be buggy or
MANETs. Within the proposed trust management theme, the malicious and can't give services with the standard that they
trust model has 2 components: trust from direct observation advertise. Since there's no centralized node to function
and trust from indirect observation. And that we enhance our associate authority to observe and penalise the peers that
base work with energy trust management system. We’ll use behave badly, malicious peers have associate incentive to
the quality AODV protocol to style SEMT protocol. produce poor quality services for his or her profit as a result
of they'll depart. Some ancient security techniques, like
Keywords: MANET, Security, Trust Management, AODV service suppliers requiring access authorization, or shoppers
Protocol. requiring server authentication, square measure used as
I. INTRODUCTION protection from well-known malicious peers.
Wireless networks is essentially either infrastructure based
mostly networks or infrastructure less networks. The
infrastructure based mostly networks uses fastened base
stations, that area unit answerable for coordinating
communication between the mobile hosts (nodes). The
unintentional networks falls underneath the category of
infrastructure less networks, wherever the mobile nodes
communicate with one another with none fastened
infrastructure between them. an advert hoc network could be
a assortment of nodes that don't believe a predefined
infrastructure to stay the network connected. Therefore the
functioning of Ad-hoc networks relies on the trust and co-
operation between nodes. Nodes facilitate one another in
conveyance of title data concerning the topology of the
network and share the responsibility of managing the
network. Therefore additionally to acting as hosts, every
mobile node will perform of routing and relaying messages
for different mobile node.
Fig1. Mobile ad-hoc network.
II. RELATED WORK
[1] Peer-to-peer networks square measure networks during
However, they can't forestall from peers providing
which peers get together to perform a vital operate during a
variable-quality service, or peers that square measure
Copyright @ 2016 IJIT. All rights reserved.
K.KARTHEEKA, V.HARINI, S.SRINIVAS
unknown. Mechanisms for trust and name will be wont to A. Existing system & disadvantages
facilitate peers distinguish sensible from dangerous partners. There are two complementary categories of approaches
This [1]paper describes a trust and name mechanism that that may safeguard tactical MANETs: prevention-based and
permits peers to find partners WHO meet their individual detection based mostly approaches. One issue of those
needs through individual expertise and sharing experiences prevention-based approaches is that a centralized key
with different peers with similar preferences. In our model a management infrastructure is required, which cannot be
peer builds 2 varieties of trust in another peer, say peer A realistic in distributed networks like MANETs. Additionally,
and peer B respectively. The primary one is that the trust that centralized infrastructures are the most targets of rivals in
peer A has in peer B’s capability in providing services. battlefields. If the infrastructure is destroyed, then the total
Alternative is that the trust that peer A has in peer B’s network could also be paralytic. Serving because the second
dependability in providing recommendations regarding other wall of protection, detection-based approaches will
peers. Here the dependability includes 2 aspects: effectively facilitate determine malicious activities. Though
Truthfulness – whether or not peers B is truthful in telling some wonderful work has been done on detection based
its data. mostly approaches supported trust in MANETs, observation
in most approaches is simply accustomed assess the
Similarity – whether or not peers B is comparable to peer A dependability of nodes, that don't seem to be within the vary
in preferences and ways that of deciding problems. of the observer node. Therefore, inaccurate trust values
could also be derived.
In the[2] future generation of wireless communication
technology, there'll be a necessity for the fast readying of III. PROPOSED SYSTEM
freelance mobile users. Substantial examples embody We have a tendency to projected the system with 2
establishing survivable, dynamic,economical communication observations one is direct and alternative one is indirect, in
for emergency/rescue operations, military, and disaster relief direct methodology every node will observe the behavior of
effort networks. Such technology eventualities cannot alternative immediate nodes, and indirect model every node
believe centralized and arranged infrastructure, however are observes the knowledge regarding multi-hop node by the
often formed as applications of MANET. A Mobile Ad Hoc immediate trustworthy node. We’ll use the history of the
Networks is associate autonomous assortment of mobile every immediate nodes behavior for direct observation. And
users that communicate over comparatively information name theme for indirect observation. By victimisation the
measure affected wireless ties. projected trust management theme able to get the correct
price and that we can avoid the misconduct nodes from the
Since the nodes square measure movable, the constellation route. In our base model, the researchers have used the direct
could modification apace and erratically over time. observation by overhearing the knowledge. This
Technology is redistributed, wherever all network activity methodology is best in a number of the situations however
together with discovering the topology and delivering this won’t be sensible altogether alternative situations.
messages should be dead by the nodes itself, i.e., the routing
practicality are going to be incorporated into mobile node. In
[2] paper, associate approach has been planned to combat
black-hole attack in AODV routing protocol. During this
approach any node uses variety rules to illation regarding
honesty of reply’s sender. Activities of a node in a very
network show its honesty. To participate in data transfer
methodology, a node ought to demonstrate its honesty. Early
of simulation, all nodes square measure able to transfer data;
in order that they would like enough time to point its truth Fig.2. Overhearing technique.
(Though every node square measure typically a control less
one). If a node is that the first receiver of a RREP packet, it The misbehavior node may capable of change the coverage
forwards packets to provide and initiates judgment area. In this situation the misbehavior may reduce the
methodology on regarding replier. The judgment method- coverage it will show like forwarding the data to next node,
logy is base on opinion of network nodes regarding replier. but indeed the data won’t be receive in next node.
The activities of node data square measure logged by its
neighbors table given in fig.3. These neighbors square
measure requested to send their opinion one or two of node.
Once a node collects all opinions of neighbors, it decides if
the replier is also a malicious node. The selection is base on
vary rules. The following rules used during this paper to
measure regarding honesty of a node in network. This
judgment is base on nodes square measure activity in
network. Fig.3. Overhearing method security problem.
International Journal of Innovative Technologies
Volume.04, Issue No.01, January-2016, Pages: 0058-0063
Improved Energy Based Security System for Mobile Ad-Hoc Networks with Belief Management System
To avoid this problem we will introduce the technique for be stored into database for future use. Before storing Energy
direct observation with end to end acknowledgement method information, it has to be compared with old energy from
with secret sign sharing. database of same node. If old energy is more than new
energy then the node will be considered as good node Or
else the node will be malicious.
B. Algorithm
Our ultimate aim in this project is to avoid malicious node
in the route while communication. We are assuming that
each node has the capability to detect nearest malicious node
why because there are the number of implementation already
have been done for detection methods, even though we are
considered the simple algorithm which will detect the
malicious in the route named as M-detection.
1. M-detection algorithm:
1) Define the control pkts
a. RREQ
Fig.4. ACK based security implementation. b. RREP
c. RERR
d. Hello
2) Receive pkts
a. If pkt is Hello
i. Set as disturbance message is received
ii. Start the message count
1. If the message count is exceeds the
threshold(variable)
a. Check the Meli table
i. If node not found
1. Add the node in table
ii. Else
1. Ignore the message
2. Malicious prevention method:
1) If node has the data
a. Check route cache
Fig.5. Block diagram.
i. If route is available
1. Forward the data
In our enhancement work, we have addressed the problem
ii. If route is not found
of Energy based routing attack by using our base trust
1. Initiate the route discovery
management work. Initially all nodes collects the data about
a. Check the Meli cache
neighbor nodes. The network monitors having the detailed
i. If Meli found
information of neighbor nodes such as routing table. It
1. Update the Meli info in RREQ
provides the connection information to Route manager. The
iii. Send the broadcast the RREQ
mobile devices periodically share their residual energy into
2) If RREQ received
all the nodes which are participating in the network. Based
a. Check the RREQ
on this energy nodes will select the route in reliable. When
i. If Meli_list != Null
source node sends RREQ, nodes will check the energy of all
1. Update Meli-table
its one hop neighbor nodes. Then the node select the next
b. Check the Meli Table
node which one has high energy cost. All the nodes do the
i. If forwarder table
same process. Finally Destination node receive the RREQ
and also it know the energy cost of both hop-by-hop also 1. Ignore the message
end-to-end communication. After validate these factors ii. If forwarder Meli table
destination will send RREP through the high energy path. 1. For i Meli table
Each node need generate the Hello message in periodic a. Updates “i” in RREQ
interval. Own Energy level must be added into Hello 2. If current node == destination of the pkt
message. Each node can able to receive the hello Message a. RREQ RREP
from neighbor node. Node has to extract the energy i. Update the reverse route info
information from Hello message. Energy information should b. Send to source
3. If current node destination
International Journal of Innovative Technologies
Volume.04, Issue No.01, January-2016, Pages: 0058-0063
K.KARTHEEKA, V.HARINI, S.SRINIVAS
a. Broadcast the RREQ as forwarder i. Send data to next node
3) Meli-maintenance routine b. Else
a. If expire time<Current time i. Generate the req
i. Delete the Meli ID 1. Attach energy level with pkt
4) If RREP is received ii. Broadcast req
a. Check the RREP 5) If node received packet
i. If Meli_list != Null a. If packet is hello packet
1. Update Meli-table i. Checks database
b. Check the Meli Table 1. If old energy is less than current energy
i. If forwarder Meli table a. Set as misbehavior node
1. Ignore the message b. If packet is Req
ii. If forwarder Meli table i. If received node is destination
1. If current node == destination of the pkt 1. Check in routing table
a. Update the reverse route info a. If old min energy is less than new
b. Send data pkt to destination i. Accept and send reply
2. If current node destination b. If old min energy is equal to new
a. For i Meli table i. Checks the energy cost
i. Updates “i” in RREP 1. If old cost is more than new
b. Forward RREP a. Accept and send reply
2. ignore the packet
3. Malicious node detection ii. if node is intermediate node
1) If RREP received in source 1. if pkt is duplicate or prev node is malicious
a. Check RREP Meli list a. ignore pkt
i. If list == Null (***we planed to improve this in 2. Else
future with behavior checking) a. Check in routing table
1. Set the path as un trusted path i. Add the energy cost
2. Generate the OREQ ii. If pkt min energy is more than own
a. Broadcast OREQ 1. Add own energy as min energy
2) If OREQ received iii. Forward the pkt
a. set val = 0 c. If pkt is Reply
b. For “i” OREQ list i. If prev node is malicious
i. If “i” Meli table 1. Ignore the packet
ii. Else
1. Generate the OREP
1. If node is not destination
2. Forward to source of OREQ
a. Forward the pkt
3. Set Val = 1
4. break
c. if val ==0 IV. RESULT ANALYSIS
We have tested our proposed system with the help of
i. broadcast OREQ
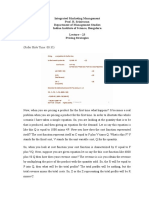
popular simulator (NS2). The fig.5 and 6 shows the
3) if OREP received
animation result. And fig. 7-9 shows the graph result.
a. update the Meli information in Meli table
In this module, we have assumed that if reply contains empty
malicious list then the route may contain malicious nodes,
then the source node will get the doubt in the route. So the
source will ask the opinion to other neighbor regarding
malicious details. In future we will implement the history
maintenance to check the behavior of the node so further we
can improve the reliability in security on route.
4. Enhanced Energy based attacker avoidance algorithm
1) Set initial energy level for each node
2) Initialize Hello timer
3) If Hello timer triggered
a. Generate the hello message
i. Attach current energy
b. Broadcast the pkt
4) If node has data
a. If route is found Fig.6. Network setup.
International Journal of Innovative Technologies
Volume.04, Issue No.01, January-2016, Pages: 0058-0063
Improved Energy Based Security System for Mobile Ad-Hoc Networks with Belief Management System
Fig.7. Node failure due to attack. Fig.10. Delay comparison (our method provides less
delay {green}).
V. CONCLUSION
We have achieved our ultimate goal, which is to provide
the security without relying on key management in MANET.
We proposed a unified trust management scheme that
enhances the security in MANETs. In this proposed trust
management scheme, the trust model had two components:
trust from direct observation and trust from indirect
observation. We have test our enhanced energy based trust
management system, which detects and eliminates the
malicious node from the route. In our proposed solution we
have considered the security based on the direct and indirect
trust mechanism, in our future work to improve the security
mechanism we will use position based trust management
system.
VI. REFERENCES
[1] “Trust and Reputation Model in Peer-to-Peer Networks”,
Fig.8. Packet delivery comparison (Enhanced system Yao Wang, Julita Vassileva.
provides more packet delivery {green} than existing [2] “Design of Novel Agitation AODV routing protocol for
work). defense against Black hole Attack”, T.Bhavana, M.Tech
(DECS), Sri Indu College of Engineering & Tech.
[3] S. Corson and J. Macker, “Mobile ad hoc networking
(MANET): routing protocol performance issues and
evaluation considerations,” IET RFC 2501, Jan. 1999.
[4] F. R. Yu, Cognitive Radio Mobile Ad Hoc Networks.
New York: Springer, 2011.
[5] J. Loo, J. Lloret, and J. H. Ortiz, Mobile Ad Hoc
Networks: Current Status and Future Trends. CRC Press,
2011.
[6] Q. Guan, F. R. Yu, S. Jiang, and V. Leung, “Joint
topology control and authentication design in mobile ad hoc
networks with cooperative communications,” IEEE Trans.
Veh. Tech., vol. 61, pp. 2674 –2685, July 2012.
[7] F. R. Yu, H. Tang, S. Bu, and D. Zheng, “Security and
quality of service (QoS) co-design in cooperative mobile ad
hoc networks,” EURASIP J.
[8]Wireless Commun. Networking, vol. 2013, pp. 188–190,
Fig.9. Energy comparison (our method provides high July 2013.
energy saving {green}).
International Journal of Innovative Technologies
Volume.04, Issue No.01, January-2016, Pages: 0058-0063
K.KARTHEEKA, V.HARINI, S.SRINIVAS
[9] Y. Wang, F. R. Yu, H. Tang, and M. Huang, “A mean
field game theoretic approach for security enhancements in
mobile ad hoc networks,” IEEE Trans. Wireless Commun.,
vol. 13, pp. 1616–1627, March 2014.
[9] J. Chapin and V. W. Chan, “The next 10 years of DoD
wireless networking research,” in Proc. IEEE Milcom’11,
(Baltimore, MD, USA), Nov. 2011.
Author’s Profile:
K.Kartheeka has completed her B.Tech in
ECE Department from Methodist College of
Engineering and technology, OU Hyderabad.
Presently she is pursuing her Masters in
Electronics and Communications from
Vardhaman College of Engineering,
Shamshabad, Hyderabad, India.
Mrs.V. Harini received the M.TECH degree
from VIT University. She is the Assistant
professor in the Department of Electronics
and Communication Engineering. She has 5
years of teaching experience.
Mr.S.Srinivas has completed his B.TECH
(ECE) from JNTU 2004 and M.TECH
(WMC) from JNTU 2010. He has 9 years of
teaching experience. Currently working as
an Assistant Professor and H.O.D of
WMC in Vardhaman College, Hyderabad,
T.S, India.
International Journal of Innovative Technologies
Volume.04, Issue No.01, January-2016, Pages: 0058-0063
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5834)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (349)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (824)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (405)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- 08 GULN ZXRAN Base Station TroubleshootingDocument39 pages08 GULN ZXRAN Base Station Troubleshootinga2227 jglNo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Websense Web Security Gateway DLP ICAP IntegrationDocument7 pagesWebsense Web Security Gateway DLP ICAP IntegrationM_BBNo ratings yet
- Inventions and InnovationsDocument77 pagesInventions and InnovationsHarini VemulaNo ratings yet
- Creativity: Madhav Madhira IIT & JNTU HyderabadDocument137 pagesCreativity: Madhav Madhira IIT & JNTU HyderabadHarini VemulaNo ratings yet
- Research Quality - Evaluation Parameters: Dr. A. Gopala Krishna Professor Department of Mechanical EngineeringDocument17 pagesResearch Quality - Evaluation Parameters: Dr. A. Gopala Krishna Professor Department of Mechanical EngineeringHarini VemulaNo ratings yet
- VRN 3 5 16Document129 pagesVRN 3 5 16Harini VemulaNo ratings yet
- Design, Validation and Correlation of Characterized SODIMM Modules Supporting DDR3 Memory InterfaceDocument11 pagesDesign, Validation and Correlation of Characterized SODIMM Modules Supporting DDR3 Memory InterfaceHarini VemulaNo ratings yet
- Excersizes in CREATIVITYDocument47 pagesExcersizes in CREATIVITYHarini VemulaNo ratings yet
- Green Cellular Network Deployment To Reduce RF Pollution: Sumit Katiyar Prof. R. K. Jain Prof. N. K. AgrawalDocument6 pagesGreen Cellular Network Deployment To Reduce RF Pollution: Sumit Katiyar Prof. R. K. Jain Prof. N. K. AgrawalHarini VemulaNo ratings yet
- The PSD of The Random Process X (T) With Mean I andDocument11 pagesThe PSD of The Random Process X (T) With Mean I andHarini VemulaNo ratings yet
- Unit-2: Operations On Single Random VariablesDocument11 pagesUnit-2: Operations On Single Random VariablesHarini VemulaNo ratings yet
- Refer Slide Time: 00:35Document15 pagesRefer Slide Time: 00:35Harini VemulaNo ratings yet
- Satellite Navigation & The Global Positioning System: Figure 1: GPS Block II-F SatelliteDocument26 pagesSatellite Navigation & The Global Positioning System: Figure 1: GPS Block II-F SatelliteHarini Vemula100% (1)
- Lec 22Document8 pagesLec 22Harini VemulaNo ratings yet
- Review On Millimeter Wave Antennas-Potential Candidate For 5G Enabled ApplicationsDocument8 pagesReview On Millimeter Wave Antennas-Potential Candidate For 5G Enabled ApplicationsHarini VemulaNo ratings yet
- Lec 14Document8 pagesLec 14Harini VemulaNo ratings yet
- Investigation of Three Dimensional Empirical Indoor Path Loss Models For Femtocell NetworksDocument11 pagesInvestigation of Three Dimensional Empirical Indoor Path Loss Models For Femtocell NetworksHarini VemulaNo ratings yet
- M.Tech Project Proposal FormatDocument3 pagesM.Tech Project Proposal FormatHarini VemulaNo ratings yet
- Acadamic Calender For 2012-13Document1 pageAcadamic Calender For 2012-13Harini VemulaNo ratings yet
- 829-Research Article-3061-2-10-20181209Document6 pages829-Research Article-3061-2-10-20181209Harini VemulaNo ratings yet
- Mooc: 2016 July: Fundamentals of MIMO Wireless CommunicationsDocument23 pagesMooc: 2016 July: Fundamentals of MIMO Wireless CommunicationsHarini VemulaNo ratings yet
- Let2 WDocument46 pagesLet2 WGetnete degemuNo ratings yet
- Open FlowDocument20 pagesOpen FlowAhmed SharifNo ratings yet
- Important Cisco Chow CommandsDocument21 pagesImportant Cisco Chow CommandsSyed Rahmath AliNo ratings yet
- Computer Networks TFTP ReportDocument11 pagesComputer Networks TFTP ReportNour AllamNo ratings yet
- Enabling and Understanding Iot TechnologiesDocument21 pagesEnabling and Understanding Iot TechnologiesMelhemhelouNo ratings yet
- Scrip Ega Chanel New Version 2 Isp Game Isp KhususDocument43 pagesScrip Ega Chanel New Version 2 Isp Game Isp KhususYan Mahendra FNo ratings yet
- RG-1000e Remote Gateway: User GuideDocument40 pagesRG-1000e Remote Gateway: User GuideThanh Kieu TienNo ratings yet
- WLC-Best Practices-SecurityDocument3 pagesWLC-Best Practices-SecurityBudiartoNo ratings yet
- Cdma PDFDocument22 pagesCdma PDFMahmoud MallahNo ratings yet
- Optimum 32bit CRC For Internet KOOPMANDocument10 pagesOptimum 32bit CRC For Internet KOOPMANgoutambiswaNo ratings yet
- 60-Objects TabDocument11 pages60-Objects TabArun SomashekarNo ratings yet
- User ManagerDocument4 pagesUser ManagerHarry Chan Putra. SP. MTCNA. MTCTCE. MTCRENo ratings yet
- En ReleaseNotes FirewareXTM 11-3-2Document52 pagesEn ReleaseNotes FirewareXTM 11-3-2Mario Diaz ParhamNo ratings yet
- MX Warm Spare - High Availability PairDocument9 pagesMX Warm Spare - High Availability PairDaveNo ratings yet
- 5G For Military Communications 5G For Military Communications 5G For Military CommunicationsDocument10 pages5G For Military Communications 5G For Military Communications 5G For Military Communicationssamaa adelNo ratings yet
- TSN Schneele AFDX 0515 v01 - 2Document31 pagesTSN Schneele AFDX 0515 v01 - 2caportNo ratings yet
- VPN Remote Access 2ndeditionDocument246 pagesVPN Remote Access 2ndeditionMilton ReyesNo ratings yet
- 12-MPLS Configuration CommandsDocument40 pages12-MPLS Configuration CommandsEder Ollora ZaballaNo ratings yet
- SniffingDocument120 pagesSniffingWoyNo ratings yet
- ENSC427 Team6 ReportDocument22 pagesENSC427 Team6 ReportAnonymous TTVlXoNo ratings yet
- SQF NS2Document6 pagesSQF NS2Sharmain QuNo ratings yet
- AResC63-2013 en PDFDocument146 pagesAResC63-2013 en PDFDaljeet Kaur DhaliwalNo ratings yet
- Ece@booksDocument6 pagesEce@booksSrinivas GoudNo ratings yet
- App Note DVB S2x and NovelSat NS3Document8 pagesApp Note DVB S2x and NovelSat NS3csystemsNo ratings yet
- Zero-Trust Remote AccessDocument16 pagesZero-Trust Remote Accessoscar tebarNo ratings yet
- Connecting Lans, Backbone Networks, and Virtual LansDocument30 pagesConnecting Lans, Backbone Networks, and Virtual LansIndra AtmajaNo ratings yet
- Zte ZXSDR b8200 Product DescriptionDocument32 pagesZte ZXSDR b8200 Product DescriptionterdpongNo ratings yet
- First CourseDocument5 pagesFirst CoursefifaacessNo ratings yet