Professional Documents
Culture Documents
0 ratings0% found this document useful (0 votes)
5 viewsTutorial 8 (Lecture 8) : TDW3431 Digital Watermarking Trimester 1, 2014/2015
Tutorial 8 (Lecture 8) : TDW3431 Digital Watermarking Trimester 1, 2014/2015
Uploaded by
Bunny EstronavellaThis document provides a list of 7 questions for a tutorial on digital watermarking. The questions cover topics such as: comparing exact and selective authentication; describing exact authentication methods and erasable watermarks; outlining selective authentication approaches; defining localization and discussing its use for authentication; and differentiating restoration strategies and approaches including embedded redundancy, self-embedding, and blind restoration.
Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
You might also like
- AD Model Paper 1 Answers-ESOFTDocument7 pagesAD Model Paper 1 Answers-ESOFTShihan Mohamed50% (2)
- Lesson Plan Instrument Sterilization-10 13 To 10 16 SophmoresDocument4 pagesLesson Plan Instrument Sterilization-10 13 To 10 16 Sophmoresapi-528785412No ratings yet
- BT0056Document1 pageBT0056Prosad BaulNo ratings yet
- BCA 424 Software Testing - (B)Document1 pageBCA 424 Software Testing - (B)Nikita BhorNo ratings yet
- Tutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- ME6019-Non Destructive Testing and Materials Question BankDocument13 pagesME6019-Non Destructive Testing and Materials Question BankVasantha Seelan0% (1)
- Tan Survey QuestionnaireDocument3 pagesTan Survey Questionnairee-MEL ChannelNo ratings yet
- National Hiv Counselling and Testing Policy Guidelines: RSA HCT Updated GuidelinesDocument52 pagesNational Hiv Counselling and Testing Policy Guidelines: RSA HCT Updated GuidelinesChristina RaxenidisNo ratings yet
- TR F & B Services NC IIDocument79 pagesTR F & B Services NC IIMarites AblogNo ratings yet
- Dissertation Sefanyetso JDocument99 pagesDissertation Sefanyetso Jvela3dlaminiNo ratings yet
- Electronic Engagement: A Guide For Public Sector ManagersDocument122 pagesElectronic Engagement: A Guide For Public Sector ManagersChahat JauraNo ratings yet
- Analysis Within the Systems Development Life-Cycle: Book 2 Data Analysis — The MethodsFrom EverandAnalysis Within the Systems Development Life-Cycle: Book 2 Data Analysis — The MethodsNo ratings yet
- Question 4 - CONCEPTUAL FRAMEWORKDocument30 pagesQuestion 4 - CONCEPTUAL FRAMEWORKSITI NURHIDAYAH BINTI AZMEENo ratings yet
- Fundamental Auditing Syllabus - Class 62BDocument10 pagesFundamental Auditing Syllabus - Class 62BQuốc Việt LêNo ratings yet
- Swarn TantramDocument377 pagesSwarn TantramRahul Mishra0% (2)
- IMC ReportDocument95 pagesIMC ReportNGOC Nguyen The MinhNo ratings yet
- RPS Pemeriksaan Akuntansi 2Document21 pagesRPS Pemeriksaan Akuntansi 2dennis wahyuda0% (1)
- Block Based Medical Image Watermarking Technique For Tamper Detection and RecoveryDocument10 pagesBlock Based Medical Image Watermarking Technique For Tamper Detection and RecoveryناصرھرەNo ratings yet
- TR Biomedical Equipment Servicing NC IIDocument69 pagesTR Biomedical Equipment Servicing NC IIInternational Technology Center Inc100% (1)
- TG 03b - Fraud Response - ProactiveDocument2 pagesTG 03b - Fraud Response - Proactivetrac.sucNo ratings yet
- Perf Task 1 PR 2 Q 2 Copy - EditedDocument3 pagesPerf Task 1 PR 2 Q 2 Copy - EditedLoren TejonesNo ratings yet
- Auditing PaperDocument1 pageAuditing Paperbatulchunawala10No ratings yet
- Chemical Risk Assessment-Framework PDFDocument77 pagesChemical Risk Assessment-Framework PDFBoni MagtibayNo ratings yet
- 12 Hums S Trends QuinteroDocument10 pages12 Hums S Trends QuinteronaygelaNo ratings yet
- Fingerprint Based Student AttendanceDocument59 pagesFingerprint Based Student AttendanceSadiq IsmailNo ratings yet
- Tutorial Exam BiometricsDocument3 pagesTutorial Exam BiometricsFranck TiomoNo ratings yet
- JCI Mock Interview Feedback 2021Document2 pagesJCI Mock Interview Feedback 2021Rolando FernandezNo ratings yet
- UserZoom - Remote Moderated 101Document36 pagesUserZoom - Remote Moderated 101lairisNo ratings yet
- Supervised Work-Based TrainingDocument26 pagesSupervised Work-Based TrainingLloyd Arnold Catabona100% (1)
- Tutorial 7 (Lecture 7) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 7 (Lecture 7) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Computer Systems Servicing NC II CGDocument80 pagesComputer Systems Servicing NC II CGHaidhar HusinNo ratings yet
- Targeting The Poorest:: An Assessment of The Proxy Means Test MethodologyDocument52 pagesTargeting The Poorest:: An Assessment of The Proxy Means Test MethodologyDxtr MedinaNo ratings yet
- Dissertation Matambele K PDFDocument204 pagesDissertation Matambele K PDFSaood AwanNo ratings yet
- Biometric Technology: Group 1Document17 pagesBiometric Technology: Group 1DearlynnNo ratings yet
- CSN Technical Bulletin No. 10 Bioretention IllustratedDocument95 pagesCSN Technical Bulletin No. 10 Bioretention IllustratedHollman Yecid Cano SalazarNo ratings yet
- ME6019-Non Destructive Testing and MaterialsDocument14 pagesME6019-Non Destructive Testing and MaterialscamilaskishoreNo ratings yet
- TR Hilot (Wellness) NC IIDocument72 pagesTR Hilot (Wellness) NC IIvenieroseNo ratings yet
- All in One CSTEDocument45 pagesAll in One CSTEapi-3700815No ratings yet
- TR Hilot (Wellness) NC IIDocument73 pagesTR Hilot (Wellness) NC IIMae Socao PagbaNo ratings yet
- IPC Training 3 Anexes On IPC SC-11-02 Specification On Training Issue 1Document13 pagesIPC Training 3 Anexes On IPC SC-11-02 Specification On Training Issue 1saladinNo ratings yet
- Biometric Authentication: - Technology and EvaluationDocument20 pagesBiometric Authentication: - Technology and EvaluationMaheshwaran BalasubramanianNo ratings yet
- Biophysical Characterization TechnologyDocument14 pagesBiophysical Characterization TechnologyAkindele O AdigunNo ratings yet
- Appendix 1 Forms PDFDocument6 pagesAppendix 1 Forms PDFCrinaNo ratings yet
- TR Housekeeping NC III PDFDocument80 pagesTR Housekeeping NC III PDFMa Zaira ObilloNo ratings yet
- FIN 5104 RM EconometricsDocument3 pagesFIN 5104 RM EconometricsNayan SahaNo ratings yet
- TR Beauty Care NC IiiDocument66 pagesTR Beauty Care NC IiiAljon BalanagNo ratings yet
- Eng F184 Rev0 17024 Checklist-Template Report On Performance of The PRCB 2021Document49 pagesEng F184 Rev0 17024 Checklist-Template Report On Performance of The PRCB 2021OQC PetroleumNo ratings yet
- 3.2 (Pascal - Eng) VN Workshop Oct 2023 - 3.0Document16 pages3.2 (Pascal - Eng) VN Workshop Oct 2023 - 3.0tovanbac96No ratings yet
- The Brazilian State and Transparency - Evaluating Compliance With Freedom of InformationDocument131 pagesThe Brazilian State and Transparency - Evaluating Compliance With Freedom of InformationAlexNo ratings yet
- Qualitative Analysis 2Document81 pagesQualitative Analysis 2nateq oikNo ratings yet
- Abiola Brian Com 0045 16Document24 pagesAbiola Brian Com 0045 16Top Overseas Ghost WritersNo ratings yet
- General Knowledge: Specific ObjectivesDocument33 pagesGeneral Knowledge: Specific ObjectivesJahan ZebNo ratings yet
- The Influence of Audit Committee Characteristics On Voluntary Corporate Social Responsibility Disclosure: Australian EvidenceDocument92 pagesThe Influence of Audit Committee Characteristics On Voluntary Corporate Social Responsibility Disclosure: Australian EvidenceAmal HameedNo ratings yet
- Oecd Survey On Social and Emotional SkillsDocument249 pagesOecd Survey On Social and Emotional Skillsaliserdaryildiz37No ratings yet
- Forum 2021aDocument77 pagesForum 2021aValfar RoblesNo ratings yet
- Certification Exam Content Outline: Certification in Monitoring, Evaluation, Accountability, and Learning (MEAL)Document7 pagesCertification Exam Content Outline: Certification in Monitoring, Evaluation, Accountability, and Learning (MEAL)AD Evaluation&PlanningNo ratings yet
- QUT Digital RepositoryDocument414 pagesQUT Digital RepositoryPhạm KhảiNo ratings yet
- Treatment of Adolescents and Children With Chronic HCV Infection, and HCV Simplified Service Delivery and DiagnosticsDocument155 pagesTreatment of Adolescents and Children With Chronic HCV Infection, and HCV Simplified Service Delivery and DiagnosticsSara Valentina GarciaNo ratings yet
- Quality of Life Outcomes in Clinical Trials and Health-Care Evaluation: A Practical Guide to Analysis and InterpretationFrom EverandQuality of Life Outcomes in Clinical Trials and Health-Care Evaluation: A Practical Guide to Analysis and InterpretationNo ratings yet
- Analysis within the Systems Development Life-Cycle: Data Analysis — The DeliverablesFrom EverandAnalysis within the Systems Development Life-Cycle: Data Analysis — The DeliverablesNo ratings yet
- TDW3431 Tutorial 3Document1 pageTDW3431 Tutorial 3Bunny EstronavellaNo ratings yet
- Tutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Tutorial 1 (Lecture 1) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 1 (Lecture 1) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- TDW3431 Tutorial 6 - Solution PDFDocument4 pagesTDW3431 Tutorial 6 - Solution PDFBunny EstronavellaNo ratings yet
- Tutorial 7 (Lecture 7) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 7 (Lecture 7) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Tutorial 4 (Lecture 4) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 4 (Lecture 4) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Tutorial 1 (Lecture 1) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document2 pagesTutorial 1 (Lecture 1) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- TDW3431 Tutorial 7 - Solution PDFDocument5 pagesTDW3431 Tutorial 7 - Solution PDFBunny EstronavellaNo ratings yet
- TDW3431 Tutorial 3 - Solution PDFDocument2 pagesTDW3431 Tutorial 3 - Solution PDFBunny EstronavellaNo ratings yet
- Lecture01 02 Part1Document27 pagesLecture01 02 Part1Bunny EstronavellaNo ratings yet
- Tutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document3 pagesTutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Differentiate Direct Message Coding From Multisymbol Message CodingDocument3 pagesDifferentiate Direct Message Coding From Multisymbol Message CodingBunny EstronavellaNo ratings yet
- TDB2111 Project GuidelinesDocument2 pagesTDB2111 Project GuidelinesBunny EstronavellaNo ratings yet
- RobotsDocument1 pageRobotsBunny EstronavellaNo ratings yet
- CS8092 SyllabusDocument2 pagesCS8092 Syllabussathyaaaaa1No ratings yet
- Bare Overhead TransDocument174 pagesBare Overhead TransWilmer SuarezNo ratings yet
- CS8791-CC Unit-IIDocument75 pagesCS8791-CC Unit-IIparth_iarjunNo ratings yet
- TOR Anonymity NetworkDocument32 pagesTOR Anonymity NetworkJános JuhászNo ratings yet
- Abeba DebruDocument90 pagesAbeba Debruabera alemayehuNo ratings yet
- CLORIOUS - Self Acting Temperature Controllers Thermostat - 3400 PDFDocument4 pagesCLORIOUS - Self Acting Temperature Controllers Thermostat - 3400 PDFRM HaroonNo ratings yet
- MUL-280 - Multimetro SterenDocument18 pagesMUL-280 - Multimetro SterenRicardoNo ratings yet
- ZE500 Series - Parts List (2016)Document11 pagesZE500 Series - Parts List (2016)Jonathan LongNo ratings yet
- Systems of Linear EquationsDocument3 pagesSystems of Linear EquationsMichael Domanais0% (1)
- David Thai Resume - MEP Electrical EngineerDocument2 pagesDavid Thai Resume - MEP Electrical EngineerDuong Thai BinhNo ratings yet
- Dental Photography 101Document54 pagesDental Photography 101Sweet ToothNo ratings yet
- 9 Data Entry Interview Questions and AnswersDocument2 pages9 Data Entry Interview Questions and AnswersBIRIGITA AUKANo ratings yet
- Version 6 IssuesDocument6 pagesVersion 6 IssuesABDEDDAIM EL HAFIDINo ratings yet
- Tutorial - Microsoft Expression Design Basics - Abhishek ShuklaDocument14 pagesTutorial - Microsoft Expression Design Basics - Abhishek ShuklalundingNo ratings yet
- Pso PosterDocument1 pagePso PosterGeorge IskanderNo ratings yet
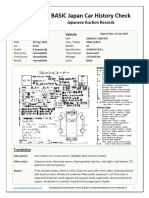
- Japan Car History Check Basic Report With Translation - Gws191-5005476Document2 pagesJapan Car History Check Basic Report With Translation - Gws191-5005476tutins5546No ratings yet
- V033e1-5 NT620S+NT620CDocument337 pagesV033e1-5 NT620S+NT620CMERTAL JAYA ABADINo ratings yet
- Questionnaire - Building Material - Steel - V11Document14 pagesQuestionnaire - Building Material - Steel - V11Salman HaiderNo ratings yet
- SKF GE 200 ES-2RS SpecificationDocument5 pagesSKF GE 200 ES-2RS SpecificationvishnuNo ratings yet
- Assignment OUMH2203 English For Workplace Communication January 2023 Semester InstructionDocument13 pagesAssignment OUMH2203 English For Workplace Communication January 2023 Semester InstructionThiviyaa DarshiniNo ratings yet
- Ai White Paper UpdatedDocument21 pagesAi White Paper UpdatedRegulatonomous OpenNo ratings yet
- CSS SLM GRADE 11 Module 1 Reynan FINAL FOR QADocument33 pagesCSS SLM GRADE 11 Module 1 Reynan FINAL FOR QAAnjail Fatea MhaNo ratings yet
- Online Services - Access Nova Scotia - Government of Nova Scotia PDFDocument2 pagesOnline Services - Access Nova Scotia - Government of Nova Scotia PDFsheldon jessomeNo ratings yet
- DevOps Brochure AS USENDocument5 pagesDevOps Brochure AS USENmd imranNo ratings yet
- Damage To Stern Tube Bearing and SealsDocument4 pagesDamage To Stern Tube Bearing and SealsJoão Henrique Volpini MattosNo ratings yet
- Elphistone - R2900 MANUALDocument662 pagesElphistone - R2900 MANUALMartin CalderonNo ratings yet
- Basic Pentest TrainingDocument67 pagesBasic Pentest TrainingZaini ZainuddinNo ratings yet
- Inventory List - Fire Extinguisher and Fire System Certification Renewal-1Document13 pagesInventory List - Fire Extinguisher and Fire System Certification Renewal-1stanley ujangNo ratings yet
- Cmo Mlis ProgramDocument35 pagesCmo Mlis Programapacedera689100% (1)
Tutorial 8 (Lecture 8) : TDW3431 Digital Watermarking Trimester 1, 2014/2015
Tutorial 8 (Lecture 8) : TDW3431 Digital Watermarking Trimester 1, 2014/2015
Uploaded by
Bunny Estronavella0 ratings0% found this document useful (0 votes)
5 views1 pageThis document provides a list of 7 questions for a tutorial on digital watermarking. The questions cover topics such as: comparing exact and selective authentication; describing exact authentication methods and erasable watermarks; outlining selective authentication approaches; defining localization and discussing its use for authentication; and differentiating restoration strategies and approaches including embedded redundancy, self-embedding, and blind restoration.
Original Description:
Original Title
_TDW3431__Tutorial_8.doc
Copyright
© © All Rights Reserved
Available Formats
DOC, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document provides a list of 7 questions for a tutorial on digital watermarking. The questions cover topics such as: comparing exact and selective authentication; describing exact authentication methods and erasable watermarks; outlining selective authentication approaches; defining localization and discussing its use for authentication; and differentiating restoration strategies and approaches including embedded redundancy, self-embedding, and blind restoration.
Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
Download as doc, pdf, or txt
0 ratings0% found this document useful (0 votes)
5 views1 pageTutorial 8 (Lecture 8) : TDW3431 Digital Watermarking Trimester 1, 2014/2015
Tutorial 8 (Lecture 8) : TDW3431 Digital Watermarking Trimester 1, 2014/2015
Uploaded by
Bunny EstronavellaThis document provides a list of 7 questions for a tutorial on digital watermarking. The questions cover topics such as: comparing exact and selective authentication; describing exact authentication methods and erasable watermarks; outlining selective authentication approaches; defining localization and discussing its use for authentication; and differentiating restoration strategies and approaches including embedded redundancy, self-embedding, and blind restoration.
Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
Download as doc, pdf, or txt
You are on page 1of 1
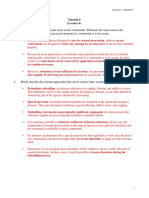
TDW3431 Digital Watermarking Trimester 1, 2014/2015
Tutorial 8
(Lecture 8)
1. Compare exact authentication to selective authentication.
2. Briefly describe the TWO basic methods for exact authentication.
3. What is an erasable watermark? Describe the steps of generating an erasable watermark.
4. Briefly describe the THREE basic approaches used for selective authentication.
5. Define localization. Discuss whether localization is useful in content authentication.
6. Briefly describe the TWO basic restoration strategies: exact restoration and approximation
restoration.
7. Differentiate the following restoration approaches: embedded redundancy, self-embedding, and blind
restoration.
You might also like
- AD Model Paper 1 Answers-ESOFTDocument7 pagesAD Model Paper 1 Answers-ESOFTShihan Mohamed50% (2)
- Lesson Plan Instrument Sterilization-10 13 To 10 16 SophmoresDocument4 pagesLesson Plan Instrument Sterilization-10 13 To 10 16 Sophmoresapi-528785412No ratings yet
- BT0056Document1 pageBT0056Prosad BaulNo ratings yet
- BCA 424 Software Testing - (B)Document1 pageBCA 424 Software Testing - (B)Nikita BhorNo ratings yet
- Tutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- ME6019-Non Destructive Testing and Materials Question BankDocument13 pagesME6019-Non Destructive Testing and Materials Question BankVasantha Seelan0% (1)
- Tan Survey QuestionnaireDocument3 pagesTan Survey Questionnairee-MEL ChannelNo ratings yet
- National Hiv Counselling and Testing Policy Guidelines: RSA HCT Updated GuidelinesDocument52 pagesNational Hiv Counselling and Testing Policy Guidelines: RSA HCT Updated GuidelinesChristina RaxenidisNo ratings yet
- TR F & B Services NC IIDocument79 pagesTR F & B Services NC IIMarites AblogNo ratings yet
- Dissertation Sefanyetso JDocument99 pagesDissertation Sefanyetso Jvela3dlaminiNo ratings yet
- Electronic Engagement: A Guide For Public Sector ManagersDocument122 pagesElectronic Engagement: A Guide For Public Sector ManagersChahat JauraNo ratings yet
- Analysis Within the Systems Development Life-Cycle: Book 2 Data Analysis — The MethodsFrom EverandAnalysis Within the Systems Development Life-Cycle: Book 2 Data Analysis — The MethodsNo ratings yet
- Question 4 - CONCEPTUAL FRAMEWORKDocument30 pagesQuestion 4 - CONCEPTUAL FRAMEWORKSITI NURHIDAYAH BINTI AZMEENo ratings yet
- Fundamental Auditing Syllabus - Class 62BDocument10 pagesFundamental Auditing Syllabus - Class 62BQuốc Việt LêNo ratings yet
- Swarn TantramDocument377 pagesSwarn TantramRahul Mishra0% (2)
- IMC ReportDocument95 pagesIMC ReportNGOC Nguyen The MinhNo ratings yet
- RPS Pemeriksaan Akuntansi 2Document21 pagesRPS Pemeriksaan Akuntansi 2dennis wahyuda0% (1)
- Block Based Medical Image Watermarking Technique For Tamper Detection and RecoveryDocument10 pagesBlock Based Medical Image Watermarking Technique For Tamper Detection and RecoveryناصرھرەNo ratings yet
- TR Biomedical Equipment Servicing NC IIDocument69 pagesTR Biomedical Equipment Servicing NC IIInternational Technology Center Inc100% (1)
- TG 03b - Fraud Response - ProactiveDocument2 pagesTG 03b - Fraud Response - Proactivetrac.sucNo ratings yet
- Perf Task 1 PR 2 Q 2 Copy - EditedDocument3 pagesPerf Task 1 PR 2 Q 2 Copy - EditedLoren TejonesNo ratings yet
- Auditing PaperDocument1 pageAuditing Paperbatulchunawala10No ratings yet
- Chemical Risk Assessment-Framework PDFDocument77 pagesChemical Risk Assessment-Framework PDFBoni MagtibayNo ratings yet
- 12 Hums S Trends QuinteroDocument10 pages12 Hums S Trends QuinteronaygelaNo ratings yet
- Fingerprint Based Student AttendanceDocument59 pagesFingerprint Based Student AttendanceSadiq IsmailNo ratings yet
- Tutorial Exam BiometricsDocument3 pagesTutorial Exam BiometricsFranck TiomoNo ratings yet
- JCI Mock Interview Feedback 2021Document2 pagesJCI Mock Interview Feedback 2021Rolando FernandezNo ratings yet
- UserZoom - Remote Moderated 101Document36 pagesUserZoom - Remote Moderated 101lairisNo ratings yet
- Supervised Work-Based TrainingDocument26 pagesSupervised Work-Based TrainingLloyd Arnold Catabona100% (1)
- Tutorial 7 (Lecture 7) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 7 (Lecture 7) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Computer Systems Servicing NC II CGDocument80 pagesComputer Systems Servicing NC II CGHaidhar HusinNo ratings yet
- Targeting The Poorest:: An Assessment of The Proxy Means Test MethodologyDocument52 pagesTargeting The Poorest:: An Assessment of The Proxy Means Test MethodologyDxtr MedinaNo ratings yet
- Dissertation Matambele K PDFDocument204 pagesDissertation Matambele K PDFSaood AwanNo ratings yet
- Biometric Technology: Group 1Document17 pagesBiometric Technology: Group 1DearlynnNo ratings yet
- CSN Technical Bulletin No. 10 Bioretention IllustratedDocument95 pagesCSN Technical Bulletin No. 10 Bioretention IllustratedHollman Yecid Cano SalazarNo ratings yet
- ME6019-Non Destructive Testing and MaterialsDocument14 pagesME6019-Non Destructive Testing and MaterialscamilaskishoreNo ratings yet
- TR Hilot (Wellness) NC IIDocument72 pagesTR Hilot (Wellness) NC IIvenieroseNo ratings yet
- All in One CSTEDocument45 pagesAll in One CSTEapi-3700815No ratings yet
- TR Hilot (Wellness) NC IIDocument73 pagesTR Hilot (Wellness) NC IIMae Socao PagbaNo ratings yet
- IPC Training 3 Anexes On IPC SC-11-02 Specification On Training Issue 1Document13 pagesIPC Training 3 Anexes On IPC SC-11-02 Specification On Training Issue 1saladinNo ratings yet
- Biometric Authentication: - Technology and EvaluationDocument20 pagesBiometric Authentication: - Technology and EvaluationMaheshwaran BalasubramanianNo ratings yet
- Biophysical Characterization TechnologyDocument14 pagesBiophysical Characterization TechnologyAkindele O AdigunNo ratings yet
- Appendix 1 Forms PDFDocument6 pagesAppendix 1 Forms PDFCrinaNo ratings yet
- TR Housekeeping NC III PDFDocument80 pagesTR Housekeeping NC III PDFMa Zaira ObilloNo ratings yet
- FIN 5104 RM EconometricsDocument3 pagesFIN 5104 RM EconometricsNayan SahaNo ratings yet
- TR Beauty Care NC IiiDocument66 pagesTR Beauty Care NC IiiAljon BalanagNo ratings yet
- Eng F184 Rev0 17024 Checklist-Template Report On Performance of The PRCB 2021Document49 pagesEng F184 Rev0 17024 Checklist-Template Report On Performance of The PRCB 2021OQC PetroleumNo ratings yet
- 3.2 (Pascal - Eng) VN Workshop Oct 2023 - 3.0Document16 pages3.2 (Pascal - Eng) VN Workshop Oct 2023 - 3.0tovanbac96No ratings yet
- The Brazilian State and Transparency - Evaluating Compliance With Freedom of InformationDocument131 pagesThe Brazilian State and Transparency - Evaluating Compliance With Freedom of InformationAlexNo ratings yet
- Qualitative Analysis 2Document81 pagesQualitative Analysis 2nateq oikNo ratings yet
- Abiola Brian Com 0045 16Document24 pagesAbiola Brian Com 0045 16Top Overseas Ghost WritersNo ratings yet
- General Knowledge: Specific ObjectivesDocument33 pagesGeneral Knowledge: Specific ObjectivesJahan ZebNo ratings yet
- The Influence of Audit Committee Characteristics On Voluntary Corporate Social Responsibility Disclosure: Australian EvidenceDocument92 pagesThe Influence of Audit Committee Characteristics On Voluntary Corporate Social Responsibility Disclosure: Australian EvidenceAmal HameedNo ratings yet
- Oecd Survey On Social and Emotional SkillsDocument249 pagesOecd Survey On Social and Emotional Skillsaliserdaryildiz37No ratings yet
- Forum 2021aDocument77 pagesForum 2021aValfar RoblesNo ratings yet
- Certification Exam Content Outline: Certification in Monitoring, Evaluation, Accountability, and Learning (MEAL)Document7 pagesCertification Exam Content Outline: Certification in Monitoring, Evaluation, Accountability, and Learning (MEAL)AD Evaluation&PlanningNo ratings yet
- QUT Digital RepositoryDocument414 pagesQUT Digital RepositoryPhạm KhảiNo ratings yet
- Treatment of Adolescents and Children With Chronic HCV Infection, and HCV Simplified Service Delivery and DiagnosticsDocument155 pagesTreatment of Adolescents and Children With Chronic HCV Infection, and HCV Simplified Service Delivery and DiagnosticsSara Valentina GarciaNo ratings yet
- Quality of Life Outcomes in Clinical Trials and Health-Care Evaluation: A Practical Guide to Analysis and InterpretationFrom EverandQuality of Life Outcomes in Clinical Trials and Health-Care Evaluation: A Practical Guide to Analysis and InterpretationNo ratings yet
- Analysis within the Systems Development Life-Cycle: Data Analysis — The DeliverablesFrom EverandAnalysis within the Systems Development Life-Cycle: Data Analysis — The DeliverablesNo ratings yet
- TDW3431 Tutorial 3Document1 pageTDW3431 Tutorial 3Bunny EstronavellaNo ratings yet
- Tutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Tutorial 1 (Lecture 1) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 1 (Lecture 1) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- TDW3431 Tutorial 6 - Solution PDFDocument4 pagesTDW3431 Tutorial 6 - Solution PDFBunny EstronavellaNo ratings yet
- Tutorial 7 (Lecture 7) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 7 (Lecture 7) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Tutorial 4 (Lecture 4) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document1 pageTutorial 4 (Lecture 4) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Tutorial 1 (Lecture 1) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document2 pagesTutorial 1 (Lecture 1) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- TDW3431 Tutorial 7 - Solution PDFDocument5 pagesTDW3431 Tutorial 7 - Solution PDFBunny EstronavellaNo ratings yet
- TDW3431 Tutorial 3 - Solution PDFDocument2 pagesTDW3431 Tutorial 3 - Solution PDFBunny EstronavellaNo ratings yet
- Lecture01 02 Part1Document27 pagesLecture01 02 Part1Bunny EstronavellaNo ratings yet
- Tutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Document3 pagesTutorial 5 (Lecture 5) : TDW3431 Digital Watermarking Trimester 1, 2014/2015Bunny EstronavellaNo ratings yet
- Differentiate Direct Message Coding From Multisymbol Message CodingDocument3 pagesDifferentiate Direct Message Coding From Multisymbol Message CodingBunny EstronavellaNo ratings yet
- TDB2111 Project GuidelinesDocument2 pagesTDB2111 Project GuidelinesBunny EstronavellaNo ratings yet
- RobotsDocument1 pageRobotsBunny EstronavellaNo ratings yet
- CS8092 SyllabusDocument2 pagesCS8092 Syllabussathyaaaaa1No ratings yet
- Bare Overhead TransDocument174 pagesBare Overhead TransWilmer SuarezNo ratings yet
- CS8791-CC Unit-IIDocument75 pagesCS8791-CC Unit-IIparth_iarjunNo ratings yet
- TOR Anonymity NetworkDocument32 pagesTOR Anonymity NetworkJános JuhászNo ratings yet
- Abeba DebruDocument90 pagesAbeba Debruabera alemayehuNo ratings yet
- CLORIOUS - Self Acting Temperature Controllers Thermostat - 3400 PDFDocument4 pagesCLORIOUS - Self Acting Temperature Controllers Thermostat - 3400 PDFRM HaroonNo ratings yet
- MUL-280 - Multimetro SterenDocument18 pagesMUL-280 - Multimetro SterenRicardoNo ratings yet
- ZE500 Series - Parts List (2016)Document11 pagesZE500 Series - Parts List (2016)Jonathan LongNo ratings yet
- Systems of Linear EquationsDocument3 pagesSystems of Linear EquationsMichael Domanais0% (1)
- David Thai Resume - MEP Electrical EngineerDocument2 pagesDavid Thai Resume - MEP Electrical EngineerDuong Thai BinhNo ratings yet
- Dental Photography 101Document54 pagesDental Photography 101Sweet ToothNo ratings yet
- 9 Data Entry Interview Questions and AnswersDocument2 pages9 Data Entry Interview Questions and AnswersBIRIGITA AUKANo ratings yet
- Version 6 IssuesDocument6 pagesVersion 6 IssuesABDEDDAIM EL HAFIDINo ratings yet
- Tutorial - Microsoft Expression Design Basics - Abhishek ShuklaDocument14 pagesTutorial - Microsoft Expression Design Basics - Abhishek ShuklalundingNo ratings yet
- Pso PosterDocument1 pagePso PosterGeorge IskanderNo ratings yet
- Japan Car History Check Basic Report With Translation - Gws191-5005476Document2 pagesJapan Car History Check Basic Report With Translation - Gws191-5005476tutins5546No ratings yet
- V033e1-5 NT620S+NT620CDocument337 pagesV033e1-5 NT620S+NT620CMERTAL JAYA ABADINo ratings yet
- Questionnaire - Building Material - Steel - V11Document14 pagesQuestionnaire - Building Material - Steel - V11Salman HaiderNo ratings yet
- SKF GE 200 ES-2RS SpecificationDocument5 pagesSKF GE 200 ES-2RS SpecificationvishnuNo ratings yet
- Assignment OUMH2203 English For Workplace Communication January 2023 Semester InstructionDocument13 pagesAssignment OUMH2203 English For Workplace Communication January 2023 Semester InstructionThiviyaa DarshiniNo ratings yet
- Ai White Paper UpdatedDocument21 pagesAi White Paper UpdatedRegulatonomous OpenNo ratings yet
- CSS SLM GRADE 11 Module 1 Reynan FINAL FOR QADocument33 pagesCSS SLM GRADE 11 Module 1 Reynan FINAL FOR QAAnjail Fatea MhaNo ratings yet
- Online Services - Access Nova Scotia - Government of Nova Scotia PDFDocument2 pagesOnline Services - Access Nova Scotia - Government of Nova Scotia PDFsheldon jessomeNo ratings yet
- DevOps Brochure AS USENDocument5 pagesDevOps Brochure AS USENmd imranNo ratings yet
- Damage To Stern Tube Bearing and SealsDocument4 pagesDamage To Stern Tube Bearing and SealsJoão Henrique Volpini MattosNo ratings yet
- Elphistone - R2900 MANUALDocument662 pagesElphistone - R2900 MANUALMartin CalderonNo ratings yet
- Basic Pentest TrainingDocument67 pagesBasic Pentest TrainingZaini ZainuddinNo ratings yet
- Inventory List - Fire Extinguisher and Fire System Certification Renewal-1Document13 pagesInventory List - Fire Extinguisher and Fire System Certification Renewal-1stanley ujangNo ratings yet
- Cmo Mlis ProgramDocument35 pagesCmo Mlis Programapacedera689100% (1)