Professional Documents
Culture Documents
Jurnal CPM Pert
Jurnal CPM Pert
Uploaded by
Yurisdal Bowie AzwanOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Jurnal CPM Pert
Jurnal CPM Pert
Uploaded by
Yurisdal Bowie AzwanCopyright:
Available Formats
SIMPLIFIED CPM/PERT SIMULATION MODEL
By Ming Lu1 and S. M. AbouRizk2
ABSTRACT: Formal stochastic simulation study has been recognized as a remedy for the shortcomings inherent
to classic critical path method (CPM) project evaluation and review technique (PERT) analysis. An accurate and
efficient method of identifying critical activities is essential for conducting PERT simulation. This paper discusses
the derivation of a PERT simulation model, which incorporates the discrete event modeling approach and a
simplified critical activity identification method. This has been done in an attempt to overcome the limitations
and enhance the computing efficiency of classic CPM/PERT analysis. A case study was conducted to validate
the developed model and compare it to classic CPM/PERT analysis. The developed model showed marked
enhancement in analyzing the risk of project schedule overrun and determination of activity criticality. In ad-
dition, the beta distribution and its subjective fitting methods are discussed to complement the PERT simulation
Downloaded from ascelibrary.org by New York University on 05/16/15. Copyright ASCE. For personal use only; all rights reserved.
model. This new solution to CPM network analysis can provide project management with a convenient tool to
assess alternative scenarios based on computer simulation and risk analysis.
INTRODUCTION stochastic simulation study. In such a study, the true properties
of the activity duration distributions (including all of its sta-
The classic critical path method (CPM) has been widely tistical descriptors such as mean and variance) are used, and
used for network analysis and project planning in industry and the concept of activity criticality rather than path criticality is
in academe ever since its invention in the 1950s. Project eval- used to overcome most of the PERT shortfalls (Ahuja et al.
uation and review technique (PERT) was originally oriented 1995).
to the time elements of a project and used probabilistic time To perform PERT analysis through simulation, two relevant
estimates to aid in determining the probability that a project issues need to be studied carefully. They are (1) how to de-
could be completed by a given date. Both techniques identify termine the critical path; and (2) how to model activity dura-
a project critical path, activities that cannot be delayed, and tion statistically.
slack activities that can be delayed without lengthening the The following section, Review of CPM/PERT Simulation,
project completion time. first reviews the classic CPM and two approaches specially
Deterministic CPM is easy to use for the purpose of project devised for PERT simulation. Next, the simplified CPM/PERT
control. However, lack of flexibility and uncertainty consid- simulation model is presented, which is an enhancement in-
erations limit its effectiveness. Most industry professionals tended to tackle PERT simulation more effectively and more
view such an analytical method as potentially hemming them efficiently. In the section entitled Fitting Distribution for Ac-
into a fixed definition or performance (Halpin 1998). This tivity Duration, the beta distribution along with its role in
‘‘straight jacket’’ based on theoretical assumptions such as the PERT simulation and its fitting methods is discussed.
estimated normal activity duration and project completion time
is not attractive to practitioners who are used to incorporating REVIEW OF CPM/PERT SIMULATION
personal experience and the ever-changing actual conditions In the classic CPM analysis, earliest start time ES, latest
into their decision making. This reflects the early (1970s) re- start time LS, earliest finish time EF, latest finish time LF, and
action to CPM scheduling. Most professionals were against its total float TF must be documented for every activity. The crit-
use as CPM was viewed as enforcing arbitrary or unattainable icality of an activity can be decided based on TF. The classic
goals (Halpin 1998). CPM analysis is straightforward and effective for simple,
PERT, which can be thought of as an improvement to CPM small-scale CPM networks.
that incorporates uncertainty and risk analysis, still proves baf- However, when facing complex, large-scale CPM networks
fling to practitioners because of its underlying theoretical as- with a great number of nodes and activities, the classic CPM
sumptions. Based on the central limit theorem of statistics, the algorithm becomes cumbersome and inefficient for two rea-
classic CPM/PERT analysis takes into account the uncertainty sons. First, the duration for all the activities must be tracked
of activity duration or costs to analyze the overrun risk of the and stored during the forward pass calculation to conduct the
project schedule or cost. However, the PERT calculated mean ensuing backward pass calculations. Second, five time attri-
project time is always an underestimate of the true project butes (ES, EF, LS, LF, and TF ) must be calculated prior to
mean (Ahuja et al. 1995). This bias in the mean estimate is determining the criticality of an activity. A real project may
called the ‘‘merge event bias.’’ Ahuja et al. (1995) give a thor- consist of hundreds of distinct activities. To expose the implicit
ough analysis and theoretical explanation of the PERT draw- schedule risk of each activity and of the whole project, the
backs and argue that the solution to the PERT’s inherent prob- simulation may need to be run hundreds of times. It is only
lems is to conduct the network analysis through a formal in recent years, with the dramatic upgrading of computer tech-
1
nology, that such CPM-based risk analysis tools appeared in
PhD Candidate, Constr. Engrg. and Mgmt., 103 Civ. Engrg. Build., the market. The major software includes Risk⫹ by Project-
Univ. of Alberta, Edmonton, Alta., Canada T6G 2G7. E-mail: mlu@
ualberta.ca
Gear Inc. (a companion of MS Project) and Monte Carlo by
2
Prof., Constr. Engrg. and Mgmt., 220 Civ. Engrg. Build., Univ. of Primevera (a companion of P3).
Alberta, Edmonton, Alta., Canada T6G 2T3. E-mail: abourizk@civil. Pritsker et al. (1989) presented an approach to PERT sim-
ualberta.ca ulation in which the backward pass is processed as a ‘‘re-
Note. Discussion open until November 1, 2000. To extend the closing versed’’ forward pass. To have the same time duration for
date one month, a written request must be filed with the ASCE Manager backward and forward passes for each activity of the network,
of Journals. The manuscript for this paper was submitted for review and
possible publication on May 24, 1999. This paper is part of the Journal
a separate random stream number is used to generate the du-
of Construction Engineering and Management, Vol. 126, No. 3, May/ ration for each activity. Pritsker et al.’s approach still falls into
June, 2000. 䉷ASCE, ISSN 0733-9634/00/0003-0219–0226/$8.00 ⫹ $.50 the category of the classic CPM in that the activity criticality
per page. Paper No. 21099. is determined based on the TF of an activity. Pritsker et al.
JOURNAL OF CONSTRUCTION ENGINEERING AND MANAGEMENT / MAY/JUNE 2000 / 219
J. Constr. Eng. Manage. 2000.126:219-226.
pointed out that after a sufficient number of simulation runs, (not free float) to be equal to 0. As in the classic CPM, de-
a ranking of the activities by high value of average slack (TF) termination of TF for each activity requires the backward pass
time becomes a possible method for ordering the activities that calculation.
can be delayed. A more appropriate ranking is based on the In the proposed ‘‘simplified CPM/PERT simulation’’ algo-
ratio of the average slack time to the standard deviation of rithm, the strategy used in the forward pass is similar to PERT
activity duration. A higher ratio value indicates that there is simulation in CYCLONE; however, a new backward pass al-
less likelihood that the average slack time will be exceeded gorithm is devised to identify the critical activities in a simple
due to the value of the basic variability inherent in the per- and efficient manner and does not calculate TF to determine
formance of the activity. A low ratio value indicates there is the critical path.
little leeway in the start time for the activity. The above anal-
ysis demands some in-depth knowledge of statistics and is not
easy for the common practitioner to use. STRUCTURE AND ELEMENTS OF SIMPLIFIED
Pritsker et al.’s (1989) final conclusion was that ‘‘there is a CPM/PERT SIMULATION
large positive correlation between the ranking of critical activ- The simplified CPM/PERT simulation follows the conven-
Downloaded from ascelibrary.org by New York University on 05/16/15. Copyright ASCE. For personal use only; all rights reserved.
ities based on the ratio of average slack (TF ) to activity du- tion of the classic CPM network, which is built using the ac-
ration standard deviation and the criticality index.’’ Criticality tivity-on-arrow structure. The network is constructed with two
index CI for an activity in a percentage term is defined as the basic elements that are interconnected by arrows; these are the
number of simulation runs in which the activity is critical, merge node and the burst node. In the proposed model, a
divided by the total number of simulation runs. merge node is strictly defined as a node with two or more
Halpin and Riggs (1992) presented a PERT simulation ap- incoming branches (activity arrows) and only one outgoing
proach using CYCLONE (Halpin 1990). By performing non- branch, and a burst node is defined as a node with only one
cyclic simulation in CYCLONE, the forward pass calculation incoming branch and two or more outgoing branches. If a node
was solved and the statistics for total project completion time has only one incoming branch and only one outgoing branch,
were obtained; these were the average project completion it is treated as a burst node for the sake of simplicity in cal-
time recorded by a COUNTER node of CYCLONE. However, culation, because no attribute needs to be tracked and deter-
Halpin and Riggs pointed out that ‘‘a somewhat troublesome mined in the calculation for a burst node. (This is clarified
aspect in the interpretation of any computer simulation of a later in the section entitled Forward Pass Calculation.) If a
network regards the critical path.’’ They identified the statistics node has more than two incoming branches and more than
of the waiting times of entities converging at a merge node in two outgoing branches, as is often encountered in the CPM
the CPM network as a good indication of activity criticality; network, it must be changed into a merge node and a burst
the lower the average waiting time, the more critical the ac- node by adding one dummy activity between nodes as shown
tivity (Halpin and Riggs 1992). in Fig. 1.
The limitation of this CPM is that the ‘‘amount of time an Only one terminal node is allowed to exist in a network to
entity had to wait in a QUEUE node (converging activity) earmark the finish milestone of the whole project. A dummy
before being processed by the following COMBI activity activity (zero duration) is added to link the last node of the
(merge node)’’ is actually the local slack or free float in CPM CPM network to a terminal node, as shown in Fig. 2.
terminology. According the CPM analysis, the condition re- As long as a node has no preceding activities or incoming
quired for an activity to be deemed critical is for the TF value branches, it is defined as an origin node. The following rules
apply to the origin node:
• A network may have more than one origin node.
• At a particular control moment when the prerequisite ac-
tivities of a merge node or a burst node are all completed,
the merge node or burst node mutates into an origin node
dynamically.
• An origin node is closely associated with a control time
at which moment the origin node releases a simulation
entity. At the planning stage (i.e., before the implemen-
tation of project), the control time may be set to zero or
to the expected project commencement date in the future.
During the execution stage (i.e., when the project is un-
derway), the control time may be set to the current time
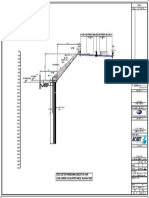
FIG. 1. Processing Complex Node or calendar date.
FIG. 2. CPM Network for Sample Application
220 / JOURNAL OF CONSTRUCTION ENGINEERING AND MANAGEMENT / MAY/JUNE 2000
J. Constr. Eng. Manage. 2000.126:219-226.
ALGORITHM OF SIMPLIFIED CPM/PERT SIMULATION node without any other merge node in its way), then AT
at merge node I from branch k can be calculated as
Discrete Event Modeling
shown
A discrete event simulation system consists of discrete en-
tities that occupy discrete states that will change over time AT(k) = ControlTime ⫹ PathDur(k) (1)
(Pidd 1996). The simplified CPM/PERT simulation takes the where AT(k) = arrival time of the entity coming from
discrete event modeling approach. An entity is an object that branch k; ControlTime = control time of the origin node;
is created at the start of simulation, processed in the simulation and PathDur(k) = sum of activity duration along the path
model, and terminated at the end of simulation. The states and from merge node I to the origin node.
behaviors of an entity within the model will be explicitly 2. If the entity is released from a merge node (i.e., if in-
tracked as simulation proceeds such as ‘‘Start activity ij ’’ and coming branch k can be traced back to previous merge
‘‘Finish activity ij .’’ The entity persists in a state for a defined node J that is closest to current merge node I in the
period of time; for instance, ‘‘Being processed by activity ij ’’ network), AT at merge node I from branch k can be cal-
state is maintained for the duration of activity ij. The time at culated as shown
Downloaded from ascelibrary.org by New York University on 05/16/15. Copyright ASCE. For personal use only; all rights reserved.
which the entity changes its state is known as an event. For
instance, ‘‘Arriving at a simple burst node (one incoming AT(k) = DT(J ) ⫹ PathDur(k) (2)
branch and one outgoing branch)’’ event changes the entity
where AT(k) = arrival time of the entity coming from
state from ‘‘Being processed by the previous activity’’ to ‘‘Be-
branch k; DT(J ) = departure time of the entity from
ing processed by the next activity.’’ The complex logic con-
merge node J; PathDur(k) = sum of activity durations
straining an event can be defined as a set of prerequisite con-
along the path from current merge node I to previous
ditions. For instance, the ‘‘Departing from a merge node’’
merge node J.
event (batch entities and release one entity) will not occur
unless all entities have arrived from the incoming branches.
An activity or arrow in the network always begins with a ‘‘De- DT from Merge Node
parting from a node’’ event and ends with an ‘‘Arriving at a The DT of the batched entity from merge node I depends
node’’ event. on AT from all the converging branches, dictated by
Forward Pass Calculation DT(I ) = AT(c) (3)
The algorithm of the simplified CPM/PERT simulation for where DT(I ) = entity departure time from merge node I; and
computing simulation event times on the forward pass can be c corresponds to the incoming branch that gives the maximum
summarized as follows: AT from Steps 1 and 2, in other words, the entity from incom-
ing branch c arrives last.
1. At the control time of an origin node, entities are created.
The number of entities created is equal to the number of WT at Merge Node
branches emanating from the origin node.
2. Starting from the origin node, entities travel along the WT(k) = DT(I ) ⫺ AT(k) (4)
forward direction of the network (usually from left to
where WT(k) = waiting time of the entity coming from branch
right) until arriving at a merging node I that has N con-
k; AT(k) = arrival time of the entity coming from branch
verging branches (N ⱖ 2).
k; and DT(I ) = batched entity departure time from merge
3. When N entities all arrive at merge node I, N entities
node I.
will be batched into one entity.
Once the above event times are all determined on a merge
4. The batched entity will immediately be released from
node, the same process is repeated on every other merge node
node I and travel along the network path until arriving
in the network until the terminal node is reached.
at another merge node.
The total project completion time is equal to AT at the ter-
5. Steps 3 and 4 will be repeated until an entity arrives at
minal node as given by
the terminal node, at which point the entity is terminated.
project completion time = AT(end dummy) (5)
It should be noted that calculation only occurs at all the
merge nodes and the terminal node in the CPM network, as Backward Passing Processing
is discussed next.
If the merge node I has N converging branches (N ⱖ 2), The simplified CPM/PERT simulation algorithm is a stream-
then 2N variables are needed to capture the entity arrival times lined network analysis method, which is reflected in the back-
AT and entity waiting times WT of the N branches. One extra ward pass calculation. It is unnecessary to calculate LS, LF,
variable is used to capture the departure time of the batched and TF of each activity to determine activity criticality. Fur-
entity released from the merge node. Therefore, 2N ⫹ 1 var- ther, unlike Pritsker et al.’s approach (1989), no simulation
iables suffice to keep track of all the event time information entity is involved in the backward pass. The backward pass
associated with a merge node. The calculations are given in calculation can be treated as a postprocessing of the PERT
the following formulas. Notice that k corresponds to the kth simulation.
converging branch at the merge node I, k = 1, 2, . . . , N. In the backward pass calculation, four steps are followed:
The remainder of this section outlines the computations that
take place during simulation. 1. Associate a CI variable of ‘‘byte type’’ (i.e., 1 or 0) with
each branch or activity
Entity Arrival Time (AT )
CIIJ = 1 or 0
To calculate AT on a given branch, two cases must be dif-
ferentiated: where I = activity start node; and J = end node; CIIJ =
1 indicates activity I-J being critical, 0 being noncritical.
1. If the entity is released from an origin node (i.e., if in- 2. Initialize CI for the end dummy activity with 1.
coming branch k can be traced back directly to an origin 3. Next, apply the following two criticality rules along the
JOURNAL OF CONSTRUCTION ENGINEERING AND MANAGEMENT / MAY/JUNE 2000 / 221
J. Constr. Eng. Manage. 2000.126:219-226.
backward path (usually from right to left in the CPM Roundup Error
network).
• Rule 1 (applicable to a merge node): If the emanating Internal roundup errors arising from the computer’s inability
branch of a merge node has a CI value equal to 1, then to accommodate float point notation are often encountered in
the CI value is set to 1 only for the converging branch the backward pass calculation of the classic CPM; this may
that is associated with the zero WT; for the other con- result in errors in the determination of the critical path. For
verging branches, CI values are all equal to 0. instance, if the earliest and latest finish time of an activity are
If the emanating branch of a merge node has a CI both 10, then TF will be zero and the activity is deemed crit-
value equal to 0, then the CI values for all the con- ical. However, the computer may return 9.9999 as the latest
verging branches are set to 0. finish time, hence the TF will be calculated as 10 ⫺ 9.9999
The WT is calculated in the forward pass. = 0.0001, which may lead to the wrong conclusion.
• Rule 2 (applicable to a burst node): If the sum of the Because the backward algorithm of the simplified CPM/
CI values for all the emanating branches of a burst PERT simulation does not need the determination of TF, it
node is equal to zero, then the incoming branch must avoids the roundup error problem completely.
Downloaded from ascelibrary.org by New York University on 05/16/15. Copyright ASCE. For personal use only; all rights reserved.
have a CI value of 0; otherwise, the CI value of the
incoming branch is 1. Observations
Rule 2 is also applicable to a burst node that has From the above comparison, it can be observed that the
only one outgoing branch. simplified CPM/PERT simulation is both simple and robust.
4. Rules 1 and 2 are applied in the backward direction until The efficiency enhancement and memory savings of the sim-
the origin nodes are reached. plified CPM/PERT simulation will be even greater when per-
forming multiple-run PERT simulations on large-scale CPM
Once the backward path processing of one simulation run is networks.
completed, it is easy to detect all critical activities, which are The simplified CPM/PERT simulation can be easily vali-
distinctly marked by the CI value of 1. dated by applying it to any simple CPM network. Some quick
manual calculations will lead to the identical critical path and
project completion time as that determined by using the classic
COMPARISON BETWEEN SIMPLIFIED CPM/PERT CPM. Mathematical proofs of Rules 1 and 2 are included in
SIMULATION AND CLASSIC CPM Appendix I.
As discussed in the previous sections, computing efficiency
FITTING DISTRIBUTION FOR ACTIVITY DURATION
regarding activity criticality is essential for successful PERT
simulation on a large-scale network. The simplified CPM/ Despite the CPM utilized, the statistical distribution fitting
PERT simulation exceeds the performance of the classic CPM of activity duration always plays a pivotal role in PERT sim-
in terms of computing efficiency in the following two ways. ulation.
Cottrell (1999) attempts to reduce the number of time esti-
Number of Event Times mates required for activity duration by using the normal dis-
tribution instead of the beta distribution in a simplified version
As discussed in the Forward Pass Calculation section, by of PERT. Only the ‘‘most likely time’’ and the ‘‘pessimistic
using the simplified CPM/PERT simulation, calculations are time’’ are estimated and are considered sufficient to fit a nor-
only performed on the merge nodes and the terminal node. No mal distribution. However, the gain of one less time estimate
entity event times need to be tracked for burst nodes and origin carries the loss of ‘‘a fixed, skewed distribution that can ap-
nodes. The number of event time variables required is ex- proximate activity duration with long tails’’ (Cottrell 1999).
pressed as follows: Therefore, if the simplified CPM/PERT simulation is imple-
mented in PERT simulation, beta distribution should be used.
冘 In the following sections, the beta distribution and its fitting
m
{2N ⫹ 1}i (6) methods are overviewed, and the methods of fitting beta dis-
i=1 tribution based on subjective time estimates are discussed.
where m = total number of merge nodes (note that the terminal Beta Distribution
node here is also treated as a merge node with only one in-
coming branch); and N = number of converging branches for Beta distribution, which was originally used in the classic
merge node I, (N ⱖ 2, except N = 1 for the terminal node). CPM-based PERT to model activity duration, has been thor-
The simplified CPM/PERT simulation ignores the burst oughly studied and conditioned. Many methods have been
nodes and origin nodes in the forward pass and does not need found to fit a beta distribution and have been documented in
to calculate TF in the backward pass. Therefore, much fewer literature (AbouRizk et al. 1991, 1994). When a sufficient
event time variables are stored than with the classic CPM, in amount of sample data is available (this may be historically
which five time variables are required for every activity (ES, accumulated or simulation generated), an objective approach
EF, LS, LF, and TF ). Additionally, in the classic CPM, the can be taken to fit the parameters of beta distribution to the
duration of every activity needs to be stored in a variable for sample data. If sample data is unavailable, or if historical data
the purpose of the backward pass calculation. So each activity is missing or too expensive and time-consuming to be col-
needs a total of six time variables for classic CPM/PERT anal- lected, a subjective approach may be utilized to fit a beta dis-
ysis. In contrast, in the simplified CPM/PERT simulation, ac- tribution based on human experience. Furthermore, during the
tivity duration is used only once in the forward pass calcula- project planning and execution stages of a project, subjective
tion and does not need to be stored. Given a CPM network beta distribution fitting provides a more flexible and effective
with 17 activities, the simplified CPM/PERT takes up only means for the project manager to experiment with different
one-third of the time variables that are needed for the classic scenarios and analyze the risk of schedule overrun through
CPM analysis. This means savings of computer memory and PERT simulation. This is demonstrated later in the section en-
enhancement of computing efficiency, which will become even titled Sample Application. In short, an accurate and efficient
more considerable for large-scale networks. method to fit the beta distribution parameters based on sub-
222 / JOURNAL OF CONSTRUCTION ENGINEERING AND MANAGEMENT / MAY/JUNE 2000
J. Constr. Eng. Manage. 2000.126:219-226.
TABLE 1. Activity Description and Duration Estimates
Activity Optimistic time Most likely time Pessimistic time
description Description Source of uncertainty estimate L estimate M estimate U
(1) (2) (3) (4) (5) (6)
1-3 Order/prefab metal building Past experience with supplier 20 22 25
1-2 Clear site Weather 5 10 15
2-3 Underground and foundation Unforeseen conditions underground may be 5 10 15
unfavorable
3-4 Erect prefab building Possibility of cold weather, precipitation, 8 10 20
etc.
4-5 Finish interior Labor productivity 9 10 11
jective time estimates will make PERT simulation more useful TABLE 2. Base Case Scenario: PERT Simulation Results ver-
to assist risk analysis and decision making. sus Classic PERT Analysis
Downloaded from ascelibrary.org by New York University on 05/16/15. Copyright ASCE. For personal use only; all rights reserved.
Simplified
Subjective Beta Distribution Fitting Statistics of project CPM/PERT Classic CPM/
completion time simulation PERT analysis
Three time estimates describing the activity duration are (days) results results
used in fitting the beta distribution (McLaughlin and Pickhardt (1) (2) (3)
1997):
Minimum duration 39.3 N/A
Maximum duration 48.9 N/A
• The ‘‘most optimistic’’ time, which is an estimate of the Mean 43.6 43.5
minimum time required to complete an activity and be Standard deviation 2.1 2.2
obtained only if everything goes right. 95% confidence interval 43.2–44.1 N/A
• The ‘‘most pessimistic’’ time is an estimate of the maxi- Probability of completing by Day 45 72% 75%
mum time required to complete an activity and be ob-
tained only if everything goes wrong. TABLE 3. Base Case Scenario: Comparison of Activity Criti-
• The ‘‘most likely’’ time is an estimate of the normal time cality and Path Criticality
required to complete an activity. It is an estimate of the
result that would occur most often if the activity were CI (simplified On/off critical
repeated a large number of times. CPM/PERT path (classic
simulation) CPM/PERT
Activity description (%) analysis)
The two shape parameters of the beta distribution can be de-
(1) (2) (3)
termined using five methods from subjective time estimates
(AbouRizk et al. 1991). The mean and variance specified 1-3 (Prefab metal building) 85 On
1-2 (Clear site) 15 Off
method is found to be accurate and efficient to fit the shape 2-3 (Foundations) 15 Off
parameters and is recommended for use in the simplified CPM/ 3-4 (Erect building) 100 On
PERT simulation. 4-5 (Finish building) 100 On
SAMPLE APPLICATION
standard deviation of which are obtained based on the central
Base Case Scenario limit theorem. In the sample application, the mean and stan-
dard deviation of a normal distribution from the classic PERT
The sample CPM network for building a convenience store
analysis are determined as 43.5 and 2.2, respectively [refer to
is taken from Ahuja et al. (1995, Chapter 15) as shown in Fig.
Ahuja et al. (1995) for details]. Next, the control date is con-
2, which was originally used to illustrate the PERT calculation.
verted to a standardized term for the standard normal distri-
The activity description, the factors causing uncertainty, and
bution [(45 ⫺ 43.5)/2.2 ⫺ 0.6818]. By looking up the standard
the time estimates of activity duration are listed in Table 1. In
normal distribution table, the cumulative probability of com-
the sample application, the simplified CPM/PERT simulation
pleting the project by Day 45 can be determined to be 75%.
and mean and variance specified method are utilized to do a
The comparison in Table 2 exposes the drawback of the
PERT simulation analysis. Note that in the CPM network (Fig.
classic CPM/PERT analysis due to the merge event bias: the
2); node 1 is an origin node with the control time set to zero;
mean calculated by PERT is an underestimate of the mean
node 6 is the terminal node; node 3 is a merge node; and nodes
resulting from simulation (43.5 < 43.6), and the schedule over-
2, 4, and 5 are the three burst nodes.
run risk is also underestimated (72% < 75%). If the network
A program is developed using Microsoft Excel 97 and Vi-
is larger and has more merge nodes, the bias will become more
sual Basic for application to conduct beta distribution fitting
obvious.
and random sampling and to implement the simplified CPM/
In Table 3, the activity criticality in terms of CI resulting
PERT simulation. For the base case scenario, the simulation
from simplified CPM/PERT simulation is compared to the path
results are generated after 100 runs as listed in Tables 2 and
criticality resulting from the classic CPM/PERT analysis. It is
3, and are compared with classic CPM/PERT analysis results
observed that simplified CPM/PERT simulation can better
if applicable. The histogram and cumulative probability curve
quantify the criticality of an activity than the classic CPM/
of the project completion time drawn from the simulation re-
PERT analysis. This is more obvious in Scenario 1.
sults are shown in Fig. 3.
Note that for the simplified CPM/PERT simulation, the
Scenario 1
probability of completing the project by Day 45 is read from
the generated cumulative probability curve, as shown in Fig. If the general contractor feels uncomfortable with the over-
3. For the classic CPM/PERT analysis calculation, the proba- run risk of project schedule, it is easy to do some simulation
bility of completing the project by Day 45 is calculated from experiments by changing duration estimates for an alternative
a theoretical normal cumulative distribution, the mean and scenario. The following scenario is an example: What if the
JOURNAL OF CONSTRUCTION ENGINEERING AND MANAGEMENT / MAY/JUNE 2000 / 223
J. Constr. Eng. Manage. 2000.126:219-226.
Downloaded from ascelibrary.org by New York University on 05/16/15. Copyright ASCE. For personal use only; all rights reserved.
FIG. 3. PERT Simulation Results for Base Case Scenario
general contractor cooperates with another fabrication subcon- TABLE 4. PERT Simulation Results: Scenario 1 versus Base
tractor who is able to deliver the job in a shorter time? Based Case
on factors such as reputations and past experiences on similar Simplified Simplified
work, the three time estimates for activity 1-3 are reevaluated Statistics of project CPM/PERT CPM/PERT
for an alternative supplier as L = 18, M = 20, and U = 22. completion time simulation simulation
Next, the general contractor runs the simplified CPM/PERT (days) scenario 1 base case
simulation again and obtains the results for a different scenario (1) (2) (3)
(scenario 1) as shown in Tables 4 and 5 and Fig. 4. Minimum duration 37.4 39.3
Table 4 compares the overrun risk of project schedule to Maximum duration 50.1 48.9
that of the base case scenario as well, showing that turning to Mean 42.4 43.6
the alternative supplier can reduce the overrun risk of project Standard deviation 2.7 2.1
95% confidence interval 41.9–42.9 43.2–44.1
schedule. For example, the mean project completion time is
Probability of completing by Day 45 85% 72%
reduced from 43.6 to 42.4 days, and the probability of com-
pleting the project within 45 days increases from 72% in the
base case scenario to 85% in scenario 1.
The change of CI shown in Table 5 reveals that the value
of CI for activity 1-3 decreases from 85 to 48%. With the TABLE 5. Scenario 1: Comparison of Activity Criticality and
classic CPM/PERT analysis, activity 1-3 is off the critical path Path Criticality
and therefore may not be brought to the project manager’s CI (simplified On/off critical
attention. However, the simplified CPM/PERT simulation re- CPM/PERT path (classic
sults give a CI value for activity 1-3 that is only 4% less than simulation CPM/PERT
that of activities 1-2 or 2-3, which are on the critical path from scenario 1) analysis
the classic CPM/PERT calculation. Therefore, to complete the Activity description (%) scenario 1)
convenience store project within schedule, the general con- (1) (2) (3)
tractor should almost equally prioritize prefab metal building 1-3 (Prefab metal building) 48 Off
(activity 1-3), clear site (activity 1-2), and foundations (activity 1-2 (Clear site) 52 On
2-3). This demonstrates the advantage of the activity criticality 2-3 (Foundations) 52 On
3-4 (Erect building) 100 On
concept in PERT simulation over the path criticality concept 4-5 (Finish building) 100 On
in the classic CPM/PERT analysis.
FIG. 4. PERT Simulation Results for Scenario 1
224 / JOURNAL OF CONSTRUCTION ENGINEERING AND MANAGEMENT / MAY/JUNE 2000
J. Constr. Eng. Manage. 2000.126:219-226.
CONCLUSIONS Based on (13), we can conclude that TFkI = LFkI ⫺ EFkI = 0.
Accordingly, by the definition of the classic CPM, converg-
By taking a discrete event modeling approach and incor- ing branch k with WT = 0 is a critical activity; hence we set
porating a simplified critical activity identification method, the CIkI = 1.
proposed simplified CPM/PERT simulation model is validated For the other converging branches at merge node I, with
through the comparison with the classic CPM/PERT analysis WTkI > 0, from (10) we have WTkI = ESIJ ⫺ EFkI > 0, then
and is proved to be both simple and robust. This new solution ESIJ > EFkI from (8), LSIJ > EFkI from (12), and LFkI > EFkI .
to CPM network analysis can provide project management Thus, TFkI = LFkI ⫺ EFkI > 0, we can clearly conclude that
with a convenient tool to assess alternative scenarios based on the other converging branches at merge node I, with WTkI >
computer simulation and risk analysis. 0, must be off the critical path; therefore we assign 0 to CIkI ,
which proves the first part of Rule 1.
APPENDIX I. PROOFS OF CRITICALITY RULES Part 2 of Rule 1 can be put into a simple mathematical
Proof of Rule 1 representation as follows:
Part 1 of Rule 1 can be put into a simple mathematical For a merge node I given CIIJ = 0, then CIkI = 0
Downloaded from ascelibrary.org by New York University on 05/16/15. Copyright ASCE. For personal use only; all rights reserved.
representation as follows:
for all the converging branches at the merge node I
For a merge node I given CIIJ = 1, if WTkI = 0, then CIkI = 1; Because CIIJ = 0, the emanating activity I-J must be noncritical
otherwise CIkI = 0 so that we can have TFIJ > 0 or
where CIIJ = criticality index variable for activity I-J, which ESIJ < LSIJ (14)
emanates from node I and flows into node J, as shown in Fig. We also know
5; WTkI = waiting time of an entity flowing into merge node
I from converging branch k; CIkI = criticality index of con- EFkI ⱕ ESIJ (15)
verging branch k; k = 1, 2, 3, . . . , N, N = total number of
i.e., the earliest finish time of converging branch k must be
converging branches. (Seasoned schedulers will soon realize
less than or equal to the earliest start time of merge node I.
the equivalence of the term WT in the classical CPM: the local
Now from (14) and (15), we can have
slack or free float.)
Because CIIJ = 1, branch I-J must be on the critical path by EFkI < LSIJ (16)
the definition of CI. According to the classic CPM, TF for the
branch I-J (TFIJ) must be 0, therefore It also holds true that
TFIJ = LSIJ ⫺ ESIJ = 0 (7) LFkI = LSIJ (17)
Hence i.e., the latest start time of merge node I is equal to the latest
finish time of any converging branch. Now from (16) and (17),
ESIJ = LSIJ (8) we can have EFkI < LFkI , i.e.
where ESIJ = earliest start time of activity I-J in the classic TFkI = LFkI ⫺ EFkI > 0 (18)
CPM terms; and LSIJ = latest start time of activity I-J in the
classic CPM terms. If CIIJ = 0, any converging branch at the merge node is non-
By the definition of the arrival time of converging branch critical; hence, the CI values for all of them should be equal
k at merge node I, ATkI is equivalent to the earliest finish time to 0, i.e., CIkI = 0, which proves the second part of Rule 1.
of converging branch EFkI , therefore
Proof of Rule 2
EFkI = ATkI (9)
Rule 2 can be put into a simple mathematical representation
From (8) and (9) we can have as follows:
WTkI = DT(I ) ⫺ ATkI = ESIJ ⫺ EFkI (10) For a burst node I given 兺 CIIk = 0, then CIJI = 0;
where DT(I ) = entity departure time or earliest release time otherwise, i.e., 兺 CIIk > 0, then CIJI = 1
from node I and should be equal to the ESIJ .
If WTkI = 0, then from (10) ESIJ ⫺ EFkI = 0, and so we have where k = 1, 2, . . . , N, N = total number of outgoing branches
ESIJ = EFkI from (8), and at burst node I shown in Fig. 6.
If 兺 CIIk = 0 (i.e., none of the emanating branches at the
LSIJ = EFkI (11) burst node is critical, hence TFIk > 0 for every emanating
branch) or LSIk ⫺ ESIk > 0, we have
In the classic CPM backward pass calculation, we have
ESIk < LSIk (19)
LFkI = LSIJ (12)
At burst node
i.e., the latest finish time of converging branch k is equal to
the latest start time of merge node I. ESIk = ES(I ) (20)
From (11) and (12), we have
i.e., the earliest start times of all the emanating activities equal
LFkI = EFkI (13) to the earliest start time of burst node I
FIG. 5. Illustration for Proving Rule 1 FIG. 6. Illustration for Proving Rule 2
JOURNAL OF CONSTRUCTION ENGINEERING AND MANAGEMENT / MAY/JUNE 2000 / 225
J. Constr. Eng. Manage. 2000.126:219-226.
min[LSIk] = LS(I ) (21) AbouRizk, S. M., Halpin, D. W., and Wilson, J. R. (1994). ‘‘Fitting beta
distributions based on sample data.’’ J. Constr. Engrg. and Mgmt.,
i.e., the latest start time of burst node I is equal to the mini- ASCE, 120(2), 288–305.
mum of the latest start time of all the emanating activities. Ahuja, H., Dozzi, S. P., and AbouRizk, S. M. (1995). Project management
From (19) and (21), we have techniques in planning and controlling construction projects. 2nd Ed.,
Wiley, N.Y.
ES(I ) < LS(I ) (22) Cottrell, W. D. (1999). ‘‘Simplified program evaluation and review tech-
nique (PERT).’’ J. Constr. Engrg. and Mgmt., ASCE, 125(1), 16–22.
i.e., the earliest start time of burst node I is less than its latest Halpin, D. W. (1990). MicroCYCLONE user’s manual. Div. of Constr.
start time. Also, based on the classic CPM, we have Engrg. and Mgmt., Purdue University, West Lafayette, Ind.
Halpin, D. W. (1998). ‘‘Construction simulation: A status report.’’ Proc.,
ES(I ) = EFJI (23) 5th Can. Constr. Res. Forum, NSERC/Alberta Construction Industry
Research Chair, Edmonton, Alberta, 33–42.
i.e., the earliest start time of burst node I is equal to the earliest Halpin, D., and Riggs, L. (1992). Planning and analysis of construction
finish time of its incoming branch J-I operations. Wiley, New York.
McLaughlin, F., and Pickhardt, R. (1979). Quantitative techniques for
LS(I ) = LFJI (24) management decisions. Houghton Mifflin, Boston.
Downloaded from ascelibrary.org by New York University on 05/16/15. Copyright ASCE. For personal use only; all rights reserved.
i.e., the latest start time of burst node I is equal to the latest Pidd, M. (1996). Tools for thinking, modelling in management science.
Wiley, London.
finish time of its incoming branch J-I. Pritsker, A., Sigal, C., and Hammesfahr, R. (1989). SLAM II network
From (22)–(24), we can conclude EFJI < LFJI or TFJI = LFJI models for decision support. Prentice-Hall, Englewood Cliffs, N.J.
⫺ EFJI > 0, thus the incoming branch J-I burst node I is not ProjectGear Inc. (Risk⫹ for MS Project). 具http://www.cs-solutions.com/
critical, and a 0 value is accordingly assigned to CIJI , which riskplus.htm典
proves the first part of Rule 2. ‘‘Monte Carlo娃 3.0 for Primavera.’’ (1995). Project Risk Analysis Soft-
If 兺 CIIk > 0 (i.e., at least one of the emanating branches, ware, Primavera Systems, Inc., Bala Cynwyd, Pa.
say branch k, at burst node I is critical), we have TFIk = 0 or
ESIk = LSIk (25) APPENDIX III. NOTATIONS
For burst node I, according to the classic CPM The following symbols are used in this paper:
ES(I ) = ESIk (26) CI = criticality index variable for corresponding activity;
i.e., the earliest start time of burst node I is equal to the earliest DT = entity departure time or earliest release time from corre-
start times of all the emanating branches sponding node;
ES = earliest start time of corresponding activity or node;
LS(I ) ⱕ LSIk (27) L = subjective estimate of lower end point of beta distribution
(i.e., optimistic time to complete corresponding activity);
i.e., the latest start time of burst node I is less than or equal LS = latest start time of corresponding activity or node;
to the latest start times of all the emanating branches. From M = subjective estimate of the mode of beta distribution (i.e.,
(25)–(27), we have LS(I ) ⱕ ES(I ). Because the latest start most likely time to complete corresponding activity);
time is impossible to be less than earliest start time for a merge N = total number of incoming branches at merge node or out-
node, we conclude going branches at burst node;
LS(I ) = ES(I ) (28) TF = total float of the corresponding activity;
U = subjective estimate of the upper end point of beta distri-
From (28), along with (23) and (24), we know LFJI = EFJI , bution (i.e., pessimistic time to complete corresponding
thus TFJI = LFJI ⫺ EFJI = 0, the incoming branch at merge activity); and
node I must be critical, and a value of 1 is accordingly as- WT = waiting time of entity flowing into merge node from cor-
signed to CIJI . responding branch.
ACKNOWLEDGMENTS
Subscripts
This work was funded by a number of construction companies in Al-
berta, Canada, and by the National Science and Engineering Research IJ = branch or activity starting from node I and ending at node
Council of Canada under grant number IRC-5558/96. J;
I, J = network node ID;
APPENDIX II. REFERENCES Ik = kth outgoing branch linking with burst node I;
AbouRizk, S. M., Halpin, D. W., and Wilson, J. R. (1991). ‘‘Visual in- k = positive integer index, k = 1, 2, 3, . . . , N; Ik or kI also
teractive fitting of beta distributions.’’ J. Constr. Engrg. and Mgmt., stands for kth branch linking with node I; and
ASCE, 117(4), 589–605. kI = kth incoming branch linking with merge node I.
226 / JOURNAL OF CONSTRUCTION ENGINEERING AND MANAGEMENT / MAY/JUNE 2000
J. Constr. Eng. Manage. 2000.126:219-226.
You might also like
- Machine Learning With Random Forests and Decision Trees - A Visual Guide For Beginners (Naren) PDFDocument68 pagesMachine Learning With Random Forests and Decision Trees - A Visual Guide For Beginners (Naren) PDFalpema80No ratings yet
- Skills, Rules, and Knowledge Signals, Signs, and Symbols, and Other Distinctions in Human Performance ModelsDocument10 pagesSkills, Rules, and Knowledge Signals, Signs, and Symbols, and Other Distinctions in Human Performance Modelsjvalle26498No ratings yet
- Juhani Pallasmaa. Space Place and Atmosphere 2011Document16 pagesJuhani Pallasmaa. Space Place and Atmosphere 2011Rigoberto Sánchez100% (1)
- Fuzzy Numbers in Cost Range EstimatingDocument10 pagesFuzzy Numbers in Cost Range EstimatingAmeer Hamza Khan DreshakNo ratings yet
- Burns2016Document4 pagesBurns201618.quliyevNo ratings yet
- 2018 ICPE Smart CPSDocument4 pages2018 ICPE Smart CPSJosé Manuel Ortiz RodriguezNo ratings yet
- Probabilistic Analysis of Solar Cell Optical PerfoDocument7 pagesProbabilistic Analysis of Solar Cell Optical PerfomtopanyuzaNo ratings yet
- Li - 2020 - Software Reliability Growth Fault Correction Model Based On Machine Learning and Neural Network AlgorithmDocument5 pagesLi - 2020 - Software Reliability Growth Fault Correction Model Based On Machine Learning and Neural Network AlgorithmibrahimNo ratings yet
- Use of Artificial Intelligence in Well-Test Interpretation: Olivier F. Allain, Roland N. HorneDocument8 pagesUse of Artificial Intelligence in Well-Test Interpretation: Olivier F. Allain, Roland N. Horneipali4christ_5308248No ratings yet
- 1 s2.0 S0951832021003677 MainDocument13 pages1 s2.0 S0951832021003677 Mainyangdw1998No ratings yet
- Reliability Safety and Security of InnovDocument6 pagesReliability Safety and Security of InnovRubenNo ratings yet
- Expert Systems With Applications: Hazem Abdallah, Hassan M. Emara, Hassan T. Dorrah, Ahmed BahgatDocument12 pagesExpert Systems With Applications: Hazem Abdallah, Hassan M. Emara, Hassan T. Dorrah, Ahmed BahgatFARIKHUDDIN DZIKRILLAHNo ratings yet
- Yaynlanm HaliDocument14 pagesYaynlanm HalisinghnamrtaNo ratings yet
- Access: Vahid Khezri, Mehdi Panahi, Elham Yasari, and Sigurd SkogestadDocument11 pagesAccess: Vahid Khezri, Mehdi Panahi, Elham Yasari, and Sigurd SkogestadHusnain AliNo ratings yet
- Assessment by Fact Sheets (ACM Conference)Document22 pagesAssessment by Fact Sheets (ACM Conference)Mahesh PanchalNo ratings yet
- Identifying Critical Variables of Principal Components For Unsupervised Feature SelectionDocument6 pagesIdentifying Critical Variables of Principal Components For Unsupervised Feature SelectionFantanesh TegegnNo ratings yet
- Hankel Matrix Rank Minimization With Applications To System Identification and RealizationDocument32 pagesHankel Matrix Rank Minimization With Applications To System Identification and RealizationFethi BencherkiNo ratings yet
- Review of Cost Estimation Models: Nikhil K Gilson, Alester Joseph VanreykDocument3 pagesReview of Cost Estimation Models: Nikhil K Gilson, Alester Joseph VanreykDoni RamadhanNo ratings yet
- Two-Stepped Evolutionary Algorithm and Its Application To Stability Analysis of SlopesDocument9 pagesTwo-Stepped Evolutionary Algorithm and Its Application To Stability Analysis of SlopesLaedson PedreiraNo ratings yet
- Artificial Intelligence and Parametric Construction Cost Estimate Modeling State-of-The-Art ReviewDocument31 pagesArtificial Intelligence and Parametric Construction Cost Estimate Modeling State-of-The-Art ReviewmrvictormrrrNo ratings yet
- An Efficient Effort and Cost Estimation Framework For Scrum Based Projects PDFDocument6 pagesAn Efficient Effort and Cost Estimation Framework For Scrum Based Projects PDFLuisNo ratings yet
- Literature ReviewDocument21 pagesLiterature ReviewKuntal GhoshNo ratings yet
- Cmengr To Be PrintedDocument11 pagesCmengr To Be PrintedJOSYHLL LYKA ROSE VILLENANo ratings yet
- Feature Analysis of Predictive Maintenance Models: Zhaoan WangDocument4 pagesFeature Analysis of Predictive Maintenance Models: Zhaoan WangBen GuhmanNo ratings yet
- Task-Based Automated Test Case Generation For Human-Machine InteractionDocument5 pagesTask-Based Automated Test Case Generation For Human-Machine InteractionTrâm TrầnNo ratings yet
- Reliability Modelling and Evaluation of Dynamic Systems With Stochastic Petri NetsDocument4 pagesReliability Modelling and Evaluation of Dynamic Systems With Stochastic Petri Netsgetachew-hagos.geletaNo ratings yet
- Sistemas de SimulacionDocument6 pagesSistemas de SimulacionDeysi Mancilla FrancoNo ratings yet
- Quality Prediction Modeling For Multistage ManufacDocument6 pagesQuality Prediction Modeling For Multistage Manufacronald christenkksonNo ratings yet
- (FM) Fast Context-Aware Recommendations With Factorization Machines (UKON 2011) PDFDocument10 pages(FM) Fast Context-Aware Recommendations With Factorization Machines (UKON 2011) PDFOstrockNo ratings yet
- Development of A Parmetric Estimating Model For Technology-Driven Deployment ProjectsDocument6 pagesDevelopment of A Parmetric Estimating Model For Technology-Driven Deployment ProjectsincubusmanNo ratings yet
- Use of Project Schedules and The Critical Path Method in ClaimsDocument16 pagesUse of Project Schedules and The Critical Path Method in ClaimsHaytham BarakaNo ratings yet
- Program Evaluation and Review Technique (PERT) : Chapter ObjectivesDocument9 pagesProgram Evaluation and Review Technique (PERT) : Chapter ObjectivesManjunath ReddyNo ratings yet
- Software AnalogiesDocument8 pagesSoftware AnalogiesclausseNo ratings yet
- Multi-Objective Robust Optimization Using Adaptive Surrogate Models For Problems With Mixed Continuous-Categorical ParametersDocument36 pagesMulti-Objective Robust Optimization Using Adaptive Surrogate Models For Problems With Mixed Continuous-Categorical ParametersmarezguiNo ratings yet
- Proceedings of Spie: Metrics For Image SegmentationDocument13 pagesProceedings of Spie: Metrics For Image SegmentationZAHRA FASKANo ratings yet
- Effective Measurements For Structural Dynamics TestingDocument12 pagesEffective Measurements For Structural Dynamics TestingAdeoti OladapoNo ratings yet
- Model Predictive Control of Distillation Column Based Recursive Parameter Estimation Method Using HYSYS SimulationDocument4 pagesModel Predictive Control of Distillation Column Based Recursive Parameter Estimation Method Using HYSYS Simulationdicky julistianNo ratings yet
- Modelling, Simulation and Optimisation of Network Planning MethodsDocument6 pagesModelling, Simulation and Optimisation of Network Planning MethodsronicaNo ratings yet
- Using The Analytic Hierarchy Process in Engineering EducationDocument6 pagesUsing The Analytic Hierarchy Process in Engineering Educationfahma87No ratings yet
- Consequence Analysis of Complex Events On Critical U.S. InfrastructureDocument9 pagesConsequence Analysis of Complex Events On Critical U.S. InfrastructureRobert CoopNo ratings yet
- Machine-Learning Approaches To Power-System Security AssessmentDocument13 pagesMachine-Learning Approaches To Power-System Security AssessmentIfedayo OladejiNo ratings yet
- Quantization of ModelsDocument11 pagesQuantization of ModelsganeshNo ratings yet
- A Cost Estimation Model For Machining Operations An ANN Parametric ApproachDocument13 pagesA Cost Estimation Model For Machining Operations An ANN Parametric Approachjoko setiawanNo ratings yet
- Validation of System Dynamics Models - A Case Study: Justyna Lemke, Małgorzata ŁatuszyńskaDocument15 pagesValidation of System Dynamics Models - A Case Study: Justyna Lemke, Małgorzata ŁatuszyńskaMadinahNo ratings yet
- How To Conduct A Simulation StudyDocument5 pagesHow To Conduct A Simulation StudyMiguel CasaresNo ratings yet
- WiSe2324 ProjectWork Company List 2024Document1 pageWiSe2324 ProjectWork Company List 2024kimrita222No ratings yet
- Operational Research: DR Anshuli Trivedi I ST Year P.G. NSCB Medical College JabalpurDocument21 pagesOperational Research: DR Anshuli Trivedi I ST Year P.G. NSCB Medical College Jabalpurdranshulitrivedi100% (1)
- An Evaluation of Change Point Detection Algorithms: Gerrit J. J. Van Den Burg Christopher K. I. WilliamsDocument33 pagesAn Evaluation of Change Point Detection Algorithms: Gerrit J. J. Van Den Burg Christopher K. I. WilliamsDUVAN CAMILO GOMEZ PALACIOSNo ratings yet
- End-To-End Autonomous Driving: Challenges and FrontiersDocument21 pagesEnd-To-End Autonomous Driving: Challenges and FrontiersbassoarnoNo ratings yet
- Computers in Industry: Gonca Tuncel, Gu Lgu N AlpanDocument10 pagesComputers in Industry: Gonca Tuncel, Gu Lgu N AlpanJUAN ALEJANDRO TASCÓN RUEDANo ratings yet
- 2014-Yusof-Survey On Computer-Aided Process PlanningDocument13 pages2014-Yusof-Survey On Computer-Aided Process PlanningsachinkashidNo ratings yet
- A Look: NetworkDocument4 pagesA Look: NetworkBrayan HuertasNo ratings yet
- The Architecture Tradeoff Analysis MethodDocument11 pagesThe Architecture Tradeoff Analysis MethoducinfpracticasNo ratings yet
- Analysis of Effort Estimation Model in Traditional and AgileDocument4 pagesAnalysis of Effort Estimation Model in Traditional and AgileiirNo ratings yet
- Model CheckingDocument6 pagesModel CheckingRicardo AqpNo ratings yet
- Behavior Prediction For Decision & Control in Cognitive Autonomous SystemsDocument4 pagesBehavior Prediction For Decision & Control in Cognitive Autonomous SystemsSAMUELNo ratings yet
- Integer Programming DualityDocument229 pagesInteger Programming Dualitypofibig689No ratings yet
- Neural Network MPCDocument8 pagesNeural Network MPCluzpachecoblNo ratings yet
- Robust Design Optimization in Aeronautics UsingDocument21 pagesRobust Design Optimization in Aeronautics UsingReyMysterioNo ratings yet
- Design Pattern Detection by Using Meta PatternsDocument12 pagesDesign Pattern Detection by Using Meta PatternsHoria IgnatNo ratings yet
- Asme DTM TJP 5 19 97Document15 pagesAsme DTM TJP 5 19 97Henz RabinoNo ratings yet
- HKS Aluminum Formwork BrochureDocument10 pagesHKS Aluminum Formwork BrochureYurisdal Bowie AzwanNo ratings yet
- 05.cross Section Strauss Pile (0+0095)Document1 page05.cross Section Strauss Pile (0+0095)Yurisdal Bowie AzwanNo ratings yet
- BIM 360 Docs BrochureDocument2 pagesBIM 360 Docs BrochureYurisdal Bowie AzwanNo ratings yet
- Sr38 Lean AccountingDocument24 pagesSr38 Lean AccountingYurisdal Bowie AzwanNo ratings yet
- QTZ 160Document2 pagesQTZ 160Yurisdal Bowie AzwanNo ratings yet
- CRAAP - Source EvaluationDocument1 pageCRAAP - Source Evaluationsixiong.geNo ratings yet
- Npi 3-PsychDocument6 pagesNpi 3-PsychhaniesoftpawsNo ratings yet
- Ability of SportDocument12 pagesAbility of Sportsiri ashokNo ratings yet
- Discussion 2 The Philosophical SelfDocument23 pagesDiscussion 2 The Philosophical SelfEthan Manuel Del ValleNo ratings yet
- Imp Questions of School Administration & SupervisionDocument6 pagesImp Questions of School Administration & SupervisionMehmood Hassan100% (1)
- Literacy at Home Upper ElementaryDocument2 pagesLiteracy at Home Upper Elementaryapi-270794375No ratings yet
- Writing Portfolio Reflection PaperDocument5 pagesWriting Portfolio Reflection Paperapi-302023389No ratings yet
- LP23 01112022Document6 pagesLP23 01112022TSL3-0620 Shanice Chin Ying XuanNo ratings yet
- Ethical Guidelines PsychologyDocument3 pagesEthical Guidelines PsychologyManal_99xoNo ratings yet
- Topic 5 (Consumer Markets and Buyer Behaviour)Document19 pagesTopic 5 (Consumer Markets and Buyer Behaviour)Sameer AiryNo ratings yet
- The Effectiveness of Differentiated Instruction Implementation in Indonesia Higher Education A Literature ReviewDocument16 pagesThe Effectiveness of Differentiated Instruction Implementation in Indonesia Higher Education A Literature ReviewLily BelacquaNo ratings yet
- Time For MappingDocument289 pagesTime For MappingMarcoJuan100% (2)
- Science Investigatory Project RubricDocument5 pagesScience Investigatory Project Rubricyasminva2017No ratings yet
- Lesson Plan 0f Procedure Text + Numeracy Amir Muayyin GKDocument5 pagesLesson Plan 0f Procedure Text + Numeracy Amir Muayyin GKsupyan76No ratings yet
- Conditional Sentences Grammar Drills Grammar Guides - 88240Document2 pagesConditional Sentences Grammar Drills Grammar Guides - 88240iñigoNo ratings yet
- Impact of Aesthetics in An Apparel StoreDocument44 pagesImpact of Aesthetics in An Apparel StoreVarian CrastoNo ratings yet
- Digital Unit Plan Template ww2Document3 pagesDigital Unit Plan Template ww2api-334307362No ratings yet
- Amara Halawatunnisa HSBDocument12 pagesAmara Halawatunnisa HSBOktaNo ratings yet
- Quiz Chapter 1Document4 pagesQuiz Chapter 1Thương TrươngNo ratings yet
- Students Perception in Using Youtube in Learning English: Neneng Islamiah Universitas Islam Kalimantan MAB BanjarmasinDocument8 pagesStudents Perception in Using Youtube in Learning English: Neneng Islamiah Universitas Islam Kalimantan MAB BanjarmasinButoq LataqNo ratings yet
- Discurs OrganizationalDocument23 pagesDiscurs OrganizationalAndreea TudorNo ratings yet
- Case Study Child Presentation 1Document7 pagesCase Study Child Presentation 1api-657969654No ratings yet
- Mathematics Action Plan 2018 2021Document8 pagesMathematics Action Plan 2018 2021Risheru RuiNo ratings yet
- The Art of Cold Reading PeopleDocument50 pagesThe Art of Cold Reading PeopletemijohnNo ratings yet
- Freud and AnesthesiaDocument5 pagesFreud and AnesthesiaRaluca LNo ratings yet
- Toulmin Method Essay With Annotated Bib AssignmentsDocument2 pagesToulmin Method Essay With Annotated Bib Assignmentsapi-214013163No ratings yet
- Cult in The Age of Mass - RieglDocument8 pagesCult in The Age of Mass - RieglPau MalgapuNo ratings yet
- 1 Review Verb Patterns!Document193 pages1 Review Verb Patterns!Felipe PulidoNo ratings yet