Professional Documents
Culture Documents
Osi Layer, Device Used and Type of Attack Carried Out On Each Layer of OSI
Osi Layer, Device Used and Type of Attack Carried Out On Each Layer of OSI
Uploaded by
ANil0 ratings0% found this document useful (0 votes)
14 views1 pageThis document outlines the OSI layers, common devices used in each layer, protocols and standards associated with each layer, and examples of attack types that can target each layer. It shows that the application layer can be attacked using application proxies, firewalls and gateways targeting protocols like SMTP, POP3, IMAP, DNS and more. The physical layer is most vulnerable to denial of service attacks like jamming and tampering since it involves basic network cables, connectors, and hardware.
Original Description:
OSI and Attacks
Original Title
ATTACKS ON OSI
Copyright
© © All Rights Reserved
Available Formats
DOC, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document outlines the OSI layers, common devices used in each layer, protocols and standards associated with each layer, and examples of attack types that can target each layer. It shows that the application layer can be attacked using application proxies, firewalls and gateways targeting protocols like SMTP, POP3, IMAP, DNS and more. The physical layer is most vulnerable to denial of service attacks like jamming and tampering since it involves basic network cables, connectors, and hardware.
Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
Download as doc, pdf, or txt
0 ratings0% found this document useful (0 votes)
14 views1 pageOsi Layer, Device Used and Type of Attack Carried Out On Each Layer of OSI
Osi Layer, Device Used and Type of Attack Carried Out On Each Layer of OSI
Uploaded by
ANilThis document outlines the OSI layers, common devices used in each layer, protocols and standards associated with each layer, and examples of attack types that can target each layer. It shows that the application layer can be attacked using application proxies, firewalls and gateways targeting protocols like SMTP, POP3, IMAP, DNS and more. The physical layer is most vulnerable to denial of service attacks like jamming and tampering since it involves basic network cables, connectors, and hardware.
Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
Download as doc, pdf, or txt
You are on page 1of 1
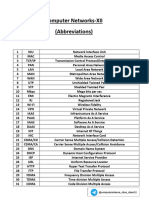
OSI LAYER, DEVICE USED AND TYPE OF ATTACK CARRIED OUT ON EACH LAYER OF
OSI
OSI LAYER DEVICES PROTOCOLS / TYPE OF ATTACK
STANDARDS
APPLICATION LAYER Application Proxy SMTP, POP#, IMAP,
Firewall, Gateway DNS, DHCP, FTP, HTTP,
TFTP, SNMP, VoIP, NTP
PRESENTATION JPEG, JPG, TIFF, PNG,
LAYER GIF, MIME, MP3
SESSION LAYER SQL, NFS, ASP, RPC
TRANSPORT LAYER Firewall TCP, UDP
NETWORK LAYER Router, Layer 3 IP, ICMP
Switch
DATA LINK LAYER Switches, Bridges, Ethernet, PPP, HDLC,
NICs, Encryption Frame Relay, ATM
Devices
PHYSICAL LAYER Cables, V.35 DOS : Jamming,
Connectors, NICs, Tempering
Hubs, Repeaters,
Modems
You might also like
- OSI and Types of AttackDocument1 pageOSI and Types of AttackANilNo ratings yet
- Telecommunications & Network SecurityDocument56 pagesTelecommunications & Network SecurityCORAL ALONSO JIMÉNEZNo ratings yet
- TCP-IP (Protocols and Services) OSI (Protocols and Services)Document1 pageTCP-IP (Protocols and Services) OSI (Protocols and Services)Gohar ZamanNo ratings yet
- Exam Pointers Domain 4Document7 pagesExam Pointers Domain 4Amar DeepNo ratings yet
- # OSI Model Key Responsibilities Data Type 7 ApplicationDocument3 pages# OSI Model Key Responsibilities Data Type 7 ApplicationFatima Binte Mahmud StudentNo ratings yet
- AbbriviationsDocument6 pagesAbbriviationsconstanceestinanceNo ratings yet
- Febbry Setiawan 15: Protokol OSI Osi Layer TCP / IpDocument2 pagesFebbry Setiawan 15: Protokol OSI Osi Layer TCP / IpFebbry SetiawanNo ratings yet
- Osi ModelDocument2 pagesOsi ModelMaulana KahirawanNo ratings yet
- CN IiDocument35 pagesCN Iiyachsin27No ratings yet
- Internet Security: How The Internet Works and Some Basic VulnerabilitiesDocument39 pagesInternet Security: How The Internet Works and Some Basic Vulnerabilitiessalim ucarNo ratings yet
- 7 Tcp-Ip-DnsDocument36 pages7 Tcp-Ip-DnsManaarul HidayatNo ratings yet
- ALL in ONE Interview Questions & Answers (Ccna, CCNP, Asa, VPN) - 1Document69 pagesALL in ONE Interview Questions & Answers (Ccna, CCNP, Asa, VPN) - 1Karan MehtaNo ratings yet
- An toàn hệ thốngDocument35 pagesAn toàn hệ thốngnhiNo ratings yet
- Tcp/Ip Protocol Suite: RTTC TVMDocument21 pagesTcp/Ip Protocol Suite: RTTC TVMVinothNo ratings yet
- RT018 DS R3000 V3.2.11Document2 pagesRT018 DS R3000 V3.2.11saadullahNo ratings yet
- Lecture 2 - Basic Concepts of Computer Communication ModelDocument45 pagesLecture 2 - Basic Concepts of Computer Communication ModelThế Anh NguyễnNo ratings yet
- Chapter1 Spring15Document57 pagesChapter1 Spring15edeNo ratings yet
- 01 Cyber Security Interview Topics Related NetworkingDocument5 pages01 Cyber Security Interview Topics Related Networkingpanthergamer539No ratings yet
- OSI LayerDocument4 pagesOSI LayerZuhairAhmedNo ratings yet
- Lecture1 - Part 2Document35 pagesLecture1 - Part 2Muhammad MurtazaNo ratings yet
- Chapter1 - Fall 2019Document65 pagesChapter1 - Fall 2019Furkan DemirNo ratings yet
- SocketsDocument54 pagesSocketsTuhin Paul100% (1)
- Resource Presentation1Document6 pagesResource Presentation1Alph TJNo ratings yet
- TCP-IP Protokoli - ŠalabahterDocument3 pagesTCP-IP Protokoli - ŠalabahterKrešimir Kolac100% (1)
- DS LG5100 V1.0.1Document2 pagesDS LG5100 V1.0.1Quan NguyenNo ratings yet
- Key Features: Industrial Dual SIM Cellular VPN Router 2 Eth + 1 RS232 + 1 RS485 + 1 USB HostDocument2 pagesKey Features: Industrial Dual SIM Cellular VPN Router 2 Eth + 1 RS232 + 1 RS485 + 1 USB HostRómulo VelásquezNo ratings yet
- Generalidades TCP-IPDocument54 pagesGeneralidades TCP-IPJuana Valentina Garcia ArizaNo ratings yet
- Clustering Tech OverviewDocument48 pagesClustering Tech Overviewyums30No ratings yet
- Computer Network Chapter - FullformsDocument5 pagesComputer Network Chapter - Fullformsnithya mountNo ratings yet
- Ad 01Document7 pagesAd 01Tirthankar ChakrabortyNo ratings yet
- Network ProtocolsDocument21 pagesNetwork ProtocolsanilNo ratings yet
- Homework 1 - CSE 343 - 192 - SOLUTIONDocument6 pagesHomework 1 - CSE 343 - 192 - SOLUTIONMaram AbdullahNo ratings yet
- Abbrev NetDocument2 pagesAbbrev NetING CDSDNo ratings yet
- 1 Linux&TCPIP Spring10Document7 pages1 Linux&TCPIP Spring10vibrant_dhavalNo ratings yet
- CCNA Quick ReferenceDocument4 pagesCCNA Quick ReferenceNorwell SagunNo ratings yet
- CCNA Quick ReferenceDocument4 pagesCCNA Quick Referenceyoussefasmi157No ratings yet
- Week 1Document149 pagesWeek 1gojan39660No ratings yet
- OSI LayersDocument37 pagesOSI LayersAjit WaderNo ratings yet
- Networking Full FormsDocument2 pagesNetworking Full Formskadaipaneer523No ratings yet
- Cheat SheetDocument1 pageCheat SheetNheb Naares Nheb NaareesNo ratings yet
- OSI and TCP - IP Lecture SlideDocument28 pagesOSI and TCP - IP Lecture SlideBobby IgbeNo ratings yet
- CyberPower DS PDU81002Document1 pageCyberPower DS PDU81002Roberto TorresNo ratings yet
- Network Security 2Document82 pagesNetwork Security 2Sibghat RehmanNo ratings yet
- ET4280 ACN-06 Security Internet ProtocolDocument40 pagesET4280 ACN-06 Security Internet ProtocolHưng NguyễnNo ratings yet
- Chapter 2 TCP-IPDocument29 pagesChapter 2 TCP-IPAbdi HafidNo ratings yet
- Digital Network - Lecturer2Document43 pagesDigital Network - Lecturer2sammydtechNo ratings yet
- 4 IpDocument80 pages4 Ipxitibo4337No ratings yet
- Protocol NotesDocument11 pagesProtocol NotesThiba SivanaihNo ratings yet
- Domain4: (Chapter 11,12)Document72 pagesDomain4: (Chapter 11,12)babyNo ratings yet
- ISCOM5204-H1 DatasheetDocument2 pagesISCOM5204-H1 Datasheetsvana.nelsonNo ratings yet
- Computer and Multimedia NetworksDocument35 pagesComputer and Multimedia NetworksAamir HiraniNo ratings yet
- Bulletcatm: Bulletcatm - Catm Nbiot Lte GatewayDocument2 pagesBulletcatm: Bulletcatm - Catm Nbiot Lte GatewayJo AnorienNo ratings yet
- Sheetal: Outdoor 4G Lte RouterDocument3 pagesSheetal: Outdoor 4G Lte RoutervsuneelgNo ratings yet
- WK6 Lecture PTC Model PDFDocument19 pagesWK6 Lecture PTC Model PDFStephen AdingoNo ratings yet
- IT A+ Certification Acronyms - Sheet1Document8 pagesIT A+ Certification Acronyms - Sheet1potatogronkNo ratings yet
- Hildebrand IP Audio StandardsDocument129 pagesHildebrand IP Audio StandardsChaabane FaouziNo ratings yet
- SKJ ExamDocument30 pagesSKJ Examekrasnov278No ratings yet
- Industry and Verimatrix AcronymsDocument6 pagesIndustry and Verimatrix AcronymsReyes Saul Rodriguez EstradaNo ratings yet
- SP883BDocument2 pagesSP883BM R KhanNo ratings yet
- IP Telephony: Deploying VoIP Protocols and IMS InfrastructureFrom EverandIP Telephony: Deploying VoIP Protocols and IMS InfrastructureNo ratings yet