Professional Documents
Culture Documents
Col e 004653 MSCP Com079
Col e 004653 MSCP Com079
Uploaded by
AliOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Col e 004653 MSCP Com079
Col e 004653 MSCP Com079
Uploaded by
AliCopyright:
Available Formats
ESOFT METRO CAMPUS
#3, De Fonseka Road, Colombo 04.
Higher National Diploma in Computing & Systems Development / Business Management
Assignment Submission Form
Name Kushan Wijerathne Name of Group Members (If
Applicable)
ESOFT Reg. No COL/E-004653
Edexcel No
Module Name Managing a Successful Computing Project
Name of the Lecturer Ms Sumudu
Date Due 29/12/2018
Date Submitted 12/01/2019
Fine
Email-Address wkushan99@gmail.com
Contact No 0714069550
Check List CD Assignment Formatting Sheet Harvard Referencing
() Brief
Signature on Signature on Student Declaration
Coversheet
Herewith I agree for the given terms and conditions on plagiarism & Academic dishonesty also I declare the
work submitted doesn’t breach these regulations.
Note: Keep the softcopy of the assignment with you until the official results released by ESOFT. ESOFT has all rights to request the softcopy
again at any time.
wkushan99@gmail.com 12/01/2019
Signature Date
Kushan Wijerathne MSCP Unit: 6 Page 1
Higher Nationals
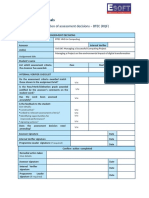
Internal verification of assessment decisions – BTEC (RQF)
INTERNAL VERIFICATION – ASSESSMENT DECISIONS
Programme title BTEC Higher National Diploma in Computing
Assessor Ms Sumudu Internal Verifier
Unit 6 Managing a Successful Computing Project
Unit(s)
Vulnerability Assessment – Management Information System (MIS) Project
Assignment title
Student’s name
List which assessment Pass Merit Distinction
criteria the Assessor has
awarded.
INTERNAL VERIFIER CHECKLIST
Do the assessment criteria awarded match
those shown in the assignment brief? Y/N
Is the Pass/Merit/Distinction grade awarded
justified by the assessor’s comments on the Y/N
student work?
Has the work been assessed
Y/N
accurately?
Is the feedback to the student:
Give details:
• Constructive?
Y/N
• Linked to relevant assessment
criteria? Y/N
• Identifying opportunities for
improved performance? Y/N
• Agreeing actions? Y/N
Does the assessment decision need
Y/N
amending?
Assessor signature Date
Internal Verifier signature Date
Programme Leader signature(if
Date
required)
Kushan Wijerathne MSCP Unit: 6 Page 2
Confirm action completed
Remedial action taken
Give details:
Assessor signature Date
Internal Verifier
Date
signature
Programme Leader
Date
signature (if required)
Kushan Wijerathne MSCP Unit: 6 Page 3
Higher Nationals - Summative Assignment Feedback Form
Student Name/ID
Unit Title Unit 6 Managing a Successful Computing Project
Assignment Number 1 Assessor Ms Sumudu
29/12/2018 Date Received 1st
Submission Date
submission
Date Received 2nd
Re-submission Date
submission
Assessor Feedback:
LO1. Assess risks to IT security
Pass, Merit & Distinction P1 P2 M1 D1
Descripts
LO2. Describe IT security solutions.
Pass, Merit & Distinction P3 P4 M2 D1
Descripts
LO3. Review mechanisms to control organisational IT security.
Pass, Merit & Distinction P5 P6 M3 M4 D2
Descripts
LO4. Create and use a Test Plan to review the performance and design of a multipage website.
Pass, Merit & Distinction P7 P8 M5 D3
Descripts
Grade: Assessor Signature: Date:
Resubmission Feedback:
Grade: Assessor Signature: Date:
Internal Verifier’s Comments:
Signature & Date:
* Please note that grade decisions are provisional. They are only confirmed once internal and external moderation has taken place and grades decisions have
been agreed at the assessment board.
Kushan Wijerathne MSCP Unit: 6 Page 4
Pearson
Higher Nationals in
Computing
Unit 6: Managing a Successful Computing Project
Kushan Wijerathne MSCP Unit: 6 Page 5
General Guidelines
1. A Cover page or title page – You should always attach a title page to your assignment. Use previous page as
your cover sheet and be sure to fill the details correctly.
2. This entire brief should be attached in first before you start answering.
3. All the assignments should prepare using word processing software.
4. All the assignments should print in A4 sized paper, and make sure to only use one side printing.
5. Allow 1” margin on each side of the paper. But on the left side you will need to leave room for binging.
Word Processing Rules
1. Use a font type that will make easy for your examiner to read. The font size should be 12 point, and should
be in the style of Time New Roman.
2. Use 1.5 line word-processing. Left justify all paragraphs.
3. Ensure that all headings are consistent in terms of size and font style.
4. Use footer function on the word processor to insert Your Name, Subject, Assignment No, and Page
Number on each page. This is useful if individual sheets become detached for any reason.
5. Use word processing application spell check and grammar check function to help edit your assignment.
Important Points:
1. Check carefully the hand in date and the instructions given with the assignment. Late submissions will not be
accepted.
2. Ensure that you give yourself enough time to complete the assignment by the due date.
3. Don’t leave things such as printing to the last minute – excuses of this nature will not be accepted for failure
to hand in the work on time.
4. You must take responsibility for managing your own time effectively.
5. If you are unable to hand in your assignment on time and have valid reasons such as illness, you may apply
(in writing) for an extension.
6. Failure to achieve at least a PASS grade will result in a REFERRAL grade being given.
7. Non-submission of work without valid reasons will lead to an automatic REFERRAL. You will then be asked to
complete an alternative assignment.
8. Take great care that if you use other people’s work or ideas in your assignment, you properly reference
them, using the HARVARD referencing system, in you text and any bibliography, otherwise you may be guilty
of plagiarism.
9. If you are caught plagiarising you could have your grade reduced to A REFERRAL or at worst you could be
excluded from the course.
Kushan Wijerathne MSCP Unit: 6 Page 6
Student Declaration
I hereby, declare that I know what plagiarism entails, namely to use another’s work and to present it as my own
without attributing the sources in the correct way. I further understand what it means to copy another’s work.
1. I know that plagiarism is a punishable offence because it constitutes theft.
2. I understand the plagiarism and copying policy of the Edexcel UK.
3. I know what the consequences will be if I plagiaries or copy another’s work in any of the assignments for this
program.
4. I declare therefore that all work presented by me for every aspects of my program, will be my own, and
where I have made use of another’s work, I will attribute the source in the correct way.
5. I acknowledge that the attachment of this document signed or not, constitutes a binding agreement
between myself and Edexcel UK.
6. I understand that my assignment will not be considered as submitted if this document is not attached to the
attached.
wkushan99@gmail.com 29/12/2018
Student’s Signature: Date:
(Provide E-mail ID) (Provide Submission Date)
Kushan Wijerathne MSCP Unit: 6 Page 7
Assignment Brief
Student Name /ID Number COL/E-004653
Unit Number and Title Unit 6: Managing a Successful Computing Project
Academic Year 2017/2018
Unit Tutor
Assignment Title Vulnerability Assessment - Management Information System Project
Issue Date
Submission Date
IV Name & Date
Submission Format:
The submission is in the form of an individual written report. This should be written in a concise, formal
business style using single spacing and font size 12. You are required to make use of headings, paragraphs
and subsections as appropriate, and all work must be supported with research and referenced using the
Harvard referencing system. Please also provide an end list of references using the Harvard referencing
system.
Unit Learning Outcomes:
LO1 Establish project aims, objectives and timeframes based on the chosen theme.
LO2 Conduct small-scale research, information gathering and data collection to generate knowledge to
support the project.
LO3 Present the project and communicate appropriate recommendations based on meaningful
conclusions drawn from the evidence findings and/or analysis.
LO4 Reflect on the value gained from conducting the project and its usefulness to support sustainable
organizational performance.
Kushan Wijerathne MSCP Unit: 6 Page 8
Assignment Brief and Guidance:
Vulnerability Assessment - Management Information System (MIS) Project
Management Information Systems (MIS) plays a very important role in today’s organizations; it creates
an impact on the organization’s functions, performance and productivity. A Management Information
System (MIS) ensures that an appropriate data is collected from the various sources, processed and send
further to all the needy destinations. A system is expected to fulfill the information needs of an individual,
a group of individuals, management functionaries, managers and top management to improve efficiency
and productivity.
On contrary, any system can be compromised with vulnerability issues. This is mostly in area of
confidentiality, integrity and availability (security triangle).
You’re advised to provide solutions for improvements for a selected Management Information System’s
in a selected organization in the area of how to improve aspects of confidentiality, integrity and
availability (security triangle) through a vulnerability study assessment.
You should investigate the causes and impacts of vulnerabilities within computing systems and explore
the solutions to the problems presented in order to make recommendations to improve their security for
Management Information System. The expected solution of the project is a vulnerability assessment and
action plan which includes, issues of varying severity.
In general, the vulnerability assessment may focus on a test of security infrastructure devices, network
servers, operational systems (including Windows and Linux), physical security of buildings, and wireless
internet security. You have to mainly focus on how can vulnerabilities in an existing system be identified
and counteracted.
Discover unknown entry points both physical and electronic – that is threat to the overall
confidentiality, integrity, and availability of network data and resources.
Problem can be discovered in the areas of installing, configuring, and maintaining servers and
infrastructure equipment as well as practices of different department managers and staff tend to
have different ways of managing their IT.
Recommendations for standardization of upcoming infrastructure installations, configurations, and
maintenance.
Educate and increase user awareness on what they could change to improve their security situation
in order to build confidence of using the Management Information System
An action plan to keep their environment secure.
Your role as a student researcher means that you are not trying to perform a specific solution to any
vulnerability problem case. You have to make expert recommendations on how to tighten security
controls, based on a proven assessment methodology, that are in the best interest of the specific project
of Management Information System which may eliminate unnecessary entry points that would greatly
reduce the threat. Introducing of a set of policies and procedures for the entire Management Information
System help eliminate threats through network entry points and infrastructure. The vulnerability trends
and recurring issues that needed careful attention. The project span 03 months in order to provide an
accurate snapshot of their current security posture.
The benefit of the project is that it provides a greater awareness among the entire staff about how any
vulnerability or weakness in any functional area affects the overall security posture of the Management
Information System at large. You are required to provide a full report on vulnerabilities you found and
how you educate the Management Information System staff on what they could change to improve their
Kushan Wijerathne MSCP Unit: 6 Page 9
security situation with an action plan to keep their environment secure.
TASK – 01
1.1 Describe aims and objectives for vulnerability assessment project which you’re introducing. Your
explanation should include a brief introduction about the company, the MIS and other relevant
information to the assessment project.
1.2 Produce a comprehensive project management plan, The plan should include milestone schedule
and project schedule for monitoring and completing the aims and objectives of the project that
includes cost, scope, time, quality, communication, risk and resources management.
1.3 Produce a work breakdown structure and a Gantt Chart to provide timeframes and stages for
completion.
TASK – 02
2.1 Explain qualitative and quantitative research methods appropriate for meeting project aims and
objectives which you produced as vulnerability assessment project.
2.2 Evaluate the project’s management process and appropriate research methodologies applied, the
accuracy and reliability of different research methods applied for the small scale research
TASK – 03
3.1 Analyze research data using appropriate tools and techniques.
3.2 Describe appropriate recommendations as a result of research and data analysis to draw valid and
meaningful conclusions.
3.3 Evaluate the selection of appropriate tools and techniques for accuracy and authenticity to support
and justify recommendations.
TASK – 04
4.1. Provide a reflection on the value of undertaking the research to meet stated objectives with your
own learning and performance which includes a discussion of the project outcomes, its
usefulness to support sustainability of the given organization and its’ performance, the decision-
making process and changes or developments of the initial project management plan to support
justification of recommendations and learning during the project.
4.2. Evaluate the value of the project management process and use of quality research to meet stated
objectives and support own learning and performance
Kushan Wijerathne MSCP Unit: 6 Page 10
Grading Rubric
Grading Criteria Achieved Feedback
LO1 Establish project aims, objectives and timeframes based on
the chosen theme
P1 Devise project aims and objectives for a chosen scenario.
P2 Produce a project management plan that covers aspects of
cost, scope, time, quality, communication, risk and resources.
P3 Produce a work breakdown structure and a Gantt Chart to
provide timeframes and stages for completion.
M1 Produce a comprehensive project management plan,
milestone schedule and project schedule for monitoring and
completing the aims and objectives of the project.
LO2 Conduct small-scale research, information gathering and
data collection to generate knowledge to support the project
P4 Carry out small-scale research by applying qualitative and
quantitative research methods appropriate for meeting project
aims and objectives.
M2 Evaluate the accuracy and reliability of different research
methods applied.
D1 Critically evaluate the project management process and
appropriate research methodologies applied.
LO3 Present the project and communicate appropriate
recommendations based on meaningful conclusions drawn from
the evidence findings and/or analysis
P5 Analyse research and data using appropriate
tools and techniques.
Kushan Wijerathne MSCP Unit: 6 Page 11
P6 Communicate appropriate recommendations as a
result of research and data analysis to draw valid and meaningful
conclusions.
M3 Evaluate the selection of appropriate tools and techniques for
accuracy and authenticity to support and justify recommendations.
LO4 Reflect on the value gained from conducting the project and
its usefulness to support sustainable organisational performance
P7 Reflect on the value of undertaking the research to meet
stated objectives and own learning and performance.
M4 Evaluate the value of the project management process and use
of quality research to meet stated objectives and support own
learning and performance.
D2 Critically evaluate and reflect on the project outcomes, the
decision making process and changes or developments of the initial
project management plan to support justification of
recommendations and learning during the project.
Kushan Wijerathne MSCP Unit: 6 Page 12
Pearson Higher Nationals in
Computing
Unit 05: Security
Kushan Wijerathne
COL/E-004653
Kushan Wijerathne MSCP Unit: 6 Page 13
Acknowledgement
The success and final outcome of this assignment required a lot of guidance and assistance from many
people and I’m extremely fortunate to have this all along the completion of the assignment work. Whatever
I have done so far is due to such guidance and assistance and I would not forget to thank them. I respect
and thank Ms. Anne Sumudu for giving me an opportunity to do this assignment work and providing me
all support and guidance which made me complete the assignment on time, I am extremely grateful to him
for the support throughout the course. MSCP takes an important place in this semister because it covers a
vast area of knowledge and it helps you to rectify errors that you make more often in managing a project. I
am really grateful because we managed to complete this assignment within the given time frame. Even
though we faced some issues in between the semester with lecturers we managed to do it successfully. I
can’t forget my friends who helped me in every way. Last but not least I would like to express my gratitude
to Esoft Metro Campus for the opportunities and teaching techniques that help every student to mold their
cooperate life.
Kushan Wijerathne MSCP Unit: 6 Page 14
Contents
Acknowledgement ....................................................................................................... 14
Task 01........................................................................................................................17
1.1 ................................................................................................................................................................. 17
Vulnerability Assessment ........................................................................................................................ 17
Company Description .............................................................................................................................. 17
Defining Security process ........................................................................................................................ 17
1.2 ................................................................................................................................................................. 19
Introduction .............................................................................................................................................. 19
Scope ........................................................................................................................................................ 20
Milestones ................................................................................................................................................ 20
Cost Management Plan ............................................................................................................................ 20
Objectives and Security Risks Objectives ............................................................................................... 20
1.3 ................................................................................................................................................................. 21
Work Breakdown Structure ..................................................................................................................... 21
Task 02....................................................................................................................... 25
Qualitative research ...................................................................................................................................... 25
Focus groups ............................................................................................................................................ 25
Interviews of one individual .................................................................................................................... 25
Benefits of Qualitative Research for Small Businesses ........................................................................... 25
Quantitative research ................................................................................................................................ 27
Quantitative market research is more structured than qualitative research because of its statistical
nature........................................................................................................................................................ 27
VULNERABILITY ASSESSTMENT QUESTIONAIRE .................................................................. 27
Task 3 .........................................................................................................................31
Quantitative research analysis .................................................................................................................. 31
Pie Chart ................................................................................................................................................... 31
Analysis .................................................................................................................................................... 31
Analysis of qualitative research ................................................................................................................ 36
3.2 ................................................................................................................................................................. 37
3.3 ................................................................................................................................................................. 37
Task 4 ........................................................................................................................ 38
Task 4.1 ....................................................................................................................................................... 38
Kushan Wijerathne MSCP Unit: 6 Page 15
Project manager’s own learning and performances................................................................................ 38
4.2 ................................................................................................................................................................. 38
Appendix.................................................................................................................. 40
REFERENCES........................................................................................................... 40
Kushan Wijerathne MSCP Unit: 6 Page 16
Task 01
1.1
Vulnerability Assessment
Vulnerability assessment is an important way of recognizing vulnerabilities in the system or application
Their filtering analyzers use them to control target frames and identify potential attack agents, deficiencies
and crossing points, while heads use them to identify already vague or unknown vulnerabilities that may
affect their security base.
For all vulnerability assessments, it is necessary to gather a summary of the potential vulnerabilities that
indicate the relative levels of risk. In this way a linking effort can put its needs to face the dangers it
encounters.
Company Description
The Kalutura Urban Council (KUC) is the local authority for Kalutara in the province of Kalutara in the
western province of Sri Lanka established in 1878. KUC is responsible for providing a variety of local
public services, including roads, sewers, sewers, homes, libraries, public parks and recreation areas.
Currently their managing assessment information through a system
The Management Information System (MIS) is a data framework used for basic initiatives and for
coordinating, managing, inspecting and impressing data in associations. Affiliated organizations can think
of different destinations and gather before they come across a risk and vulnerability assessment. These
goals and target sections may be the intended consequences of compliance should be an indication of new
laws, mandates and information security. Security as a means of setting up and assets of information
technology is essentially underlined rather than expectation, area and response. By combining a sound and
wide-ranging security process and an enthusiastic IT security plan and structure, relationships can be
created to ensure the security of IT facilities and assets, as indicated by the key satisfactory risk or the level
of introduction of the relationship.
Defining Security process
The defense system consists mainly of three parts: hopes, revelations and reactions. Depending on the
expectations, re-certifications or certifications are used in security controls and in the life cycle safety
master plan. It is automatically created by integrating the system into an unsupported system or application
type for security reasons. Balanced operating systems and application for transparency, reliability and
security of applications or application applications. Monitoring of IT organizations and asset inspection.
Enter the checklists of the logs, the research lines, the spy acceptance program, and the IT institutes for the
nineteen evaluation missions and processes. It is the responsibility of the information security experts to
Kushan Wijerathne MSCP Unit: 6 Page 17
provide reliable information and information on newly discovered information, risks and risks, information
systems and asset integration.
The reaction is a defense of a technological relationship or knowledge or a reaction from a cloud to a
security separation or a security risk, danger or power. Resistance usually crosses four areas:
• Criminological Analysis Plan
The CIRT team is properly prepared and information security experts collecting and retrieving information
and data submit the information and data collected during a security interruption or research case to a
measurable research program.
• Disaster Recovery Plan (DRP)
Associations with a significant import risk, especially in relation to air or in relation to war, must have an
arrangement to deal with a disaster (for example, an overwhelming ocean, a flood, fire).
• Business Continuity Plan (BCP)
Associations that have a lot of enthusiasm for IT deployment and assets typically perform, test and support
an internal BCP plan to disclose how they will maintain business and emancipation, basically assets.
• SIRT (Security Incident Response) and design team
Many partners have their SIRT security team, which includes a cross-section of human resources, genuine
IT and department.
Purpose of the risk and vulnerability assessment
The risk of information technology can be understood if there is a risk in terms of risk and risk if
resources have been invested in the information technology.
Determination or renewal of identified risks, risks and risk situations can be organized and
effectively organized by prioritizing or underestimating the asset and item data.
The risks, risks, threats and risks for the risk and risk assessment have been identified and the
relationship of responsibility is to provide the necessary security response and response to identified
threats, threats and risk management.
First, new information on laws, orders and safety issues can be developed in case of risk and
weakness assessment.
Provides an IT connection with the described destinations and objectives associated with case and
risk assessment in assessing risks and deficiencies.
There are informative IT resources and information resources.
Risks, accidents and acceptable weaknesses can be identified and described in detail in relation to the
relationship, system and assets.
There is a difference in the IT security plans of the contact and the gaps or the contact plan in the
box.
Vincentus windows can be distinguished and restricted due to the purity of the union.
Different assets and assets depend on the various ratings of the ITA affiliate. That is, criticism of the
importance or affinity of assets, the preferences of the dollar.
The risk, the risk and the condition of the acceptable risk depend on the impact or the risk of the
assets or assets of IT.
Kushan Wijerathne MSCP Unit: 6 Page 18
1.2
Project Management Plan
for
Vulnerability assessment of UC
Kalutara
Version 1.0
Prepared by: Kushan Wijerathne
Introduction
The project plan combines information on personnel, expenditure planning, timing, deadline, goal and
assessment. It gives further guidance on both personal and social goals of opportunities and how all aspects
of the regulation should be done. As a technique for progress is complemented as a guide to the way a free
effort works, a business plan points to the exploitation of the business.
Kushan Wijerathne MSCP Unit: 6 Page 19
This project proposes providing solutions to improve selected information management systems in selected
organizations in the ways of improving confidentiality, integrity and availability through research and
vulnerability assessment. That's because I did it. Here we have to make a major proposal with the most
sophisticated way of modifying security controls in the light of the proven evaluation strategy. This will be
the biggest benefit of a clear effort of the information management system. Threatening. The presentation
of multiple approaches and methods for the information management system as a whole contributes to the
elimination of risks through the focus and infrastructure of the part of the system. The advantage of this
exercise is that it pays more attention to all staff for the inability or lack of any utility that has moderate
impact on the overall security attitude of the information management system.
Scope
We will complete a risk assessment of the Management Information System (MIS) through this project,
identifying and strengthening complex objectives in every aspect, such as classification, dignity and
access. At the end of this task, we have approved the difficulty of managing management and have issued a
suitable arrangement for the MIS staff on specific security arrangements to change the activities to
maintain their environment safely.
Milestones
Finding a company.
Planning and preparation for the meeting
Schedule the meeting and arrange a local visit
Review the process, documents and related drawings and diagrams
Create a full complete check list.
A billing report has been designed for analysis of the field data by visiting the site.
Grant full approval from the responsible party for preparing the final report.
Cost Management Plan
To treat this risk as a research project for a college student, it is not necessary to have an extension of the
money for this purpose in gathering important data for the main business. Risk assessment is a procedure
for identifying and measuring the risk of becoming confident in the status of the association. It is important
to understand the situation and the danger when packaging needs information, minds and risk with far-
reaching vulnerability assessment program.
Objectives and Security Risks Objectives
The risk window can be identified according to the acceptable tolerance of the organization, which is
at risk for the risk.
Determine the vulnerability at the network.
New Risk and Risk can be assessed with new Information Security Laws, Regulations and
Regulations
There are flaws or gaps in the information frame of the organization.
Kushan Wijerathne MSCP Unit: 6 Page 20
Design your upgrade and build inventory of all equipment in the enterprise for the assessment of the
future.
Data protection is at a premium level.
Identify security defects before identifying the attacker.
1.3
Work Breakdown Structure
Project Management and System Engineering-the work-breakdown structure, the direction of the project
into smaller components. A team project is a project breakdown structure for managing tasks. The
PMBOK 5 (Project Management Body of Knowledge) defines the design breakdown structure.
"Hieroglydifferency in the project group in the project team to provide the required projects for the
achievement of project objectives." Work-breakdown structure is an element, product, data, service or any
combination. Providing guidance and guidance for the WBS Scheduling and Controlling the framework for
oversight and control
Kushan Wijerathne MSCP Unit: 6 Page 21
vulnerability
Assessment
Project
Initiation Planning Execution Closeout Evaluation
Developing Processing PLanning site Preparing Executing Document Transfering
Developing WBS Managing Analyzing Final report
business case requirements visit schedule checklist project tasks closeout project
Identifying The Prepare the Issuing the
communication Procument Tracking tasks Site visit records
deliverables questionaries report report
Kushan Wijerathne MSCP Unit: 6 Page 22
Gantt chart
Kushan Wijerathne MSCP Unit: 6 Page 23
Kushan Wijerathne MSCP Unit: 6 Page 24
Task 02
Qualitative research
Qualitative research is a method that focuses on how people feel; What they think and why
choose the right decisions. For example, if you look at changing your branding, some kind of
quality research will be undertaken to understand the emotional reactions of your new identity
and people associating with them. What is Qualitative Research? In simple terms, it is an
experimental method, and as a result, it is semi-structured, and the discussion - negotiating - in
one or the other, in a targeted group - applies to the quality you seek.
Focus groups
If you choose to have a group discussion with a selected person, select five or more
participants. For a discussion of a number of predefined topics, a moderator is required to
guide. The true capability of the team of the accuracy team through any dialogue will be the
true and correct answer of the targeted delegated representatives.
Interviews of one individual
Direct individual interviews are often carried out in a quality market research or by telephone or
face-to-face. Allowing your selected participants to become a more personal approach,
allowing them to be open and open about their own ideas. If the topic of the conversation is one
of the most personal or eminent, it is best to make quality market research more suitable to
allow one external interaction.
Benefits of Qualitative Research for Small Businesses
Performing or reporting through quality research via audio or video is easier to analyze
for answers.
Qualitative research gives you the ability to research a variety of topics.
Quantitative research may be more profitable than quantitative market research, and
recruiting large scale scales or using wider methods is not large.
You can make targeted exploratory explorations. No large number of participants is
required for the interview.
Qualitative research will help customers and the public to understand. A good quality research
the project manager knows what the employees think about the system. That's why employees
have a lot of questions at the system. In the section below, as the manager of the project, I have
tried to answer some of employees and unrelated systems.
Survey Strongly Agree Neutral Disagree Strongly
Question agree 1 2 3 4 disagree 5
Kushan Wijerathne MSCP Unit: 6 Page 25
This system
will promote
the LA
This will
increase
customer
support
The
environmenta
l program has
an enormous
impact on the
environment
This system
will receive
great
feedback
from the
general public
Does the crew
follow the
established
standards?
Bios is safe
with
administrator
password?
Can
privileged
users be able
to restart only
their servers?
Are there
routers and
portals on the
system?
Is there a
Kushan Wijerathne MSCP Unit: 6 Page 26
built-in
firewall?
Quantitative research
Quantitative market research is more structured than qualitative research because of its
statistical nature.
Small businesses that are explicit in quantitative research will be able to provide an accurate
picture of their target market. Sample responded samples give a list of mainly closed
questions for selecting and answering a sample of the sample. These closed questions can
provide answers, respond to business, and quickly decide on preferences.
Quantitative research may be based on paper - like postal surveys or computerized - online
surveys or phone calls. All the quantities of samples; Response for a specific area should be
minimally responded, and 100 responses are said to be of low quality. Reliable quantitative
data will require large sample sizes.
The objective of the project is to find the vulnerabilities of the assessment management
system. As a project manager, the best and best research method will be found to find the right
market for local authority. Assessment management system research by local authority has
given as follows.
Quantitative research can be done through observations, surveys, quizzes, and target groups.
Therefore, as a quantitative research for the local authority, I have conducted a survey method
for the research manager, as a project manager. So I have set up a survey questionnaire. 10
based on and on a Likert scale –
VULNERABILITY ASSESSTMENT QUESTIONAIRE
Name:
Department:
Designation:
Phone Number:
Email Address:
1. What is the status your computer literacy?
a. Excellent
b. Good
Kushan Wijerathne MSCP Unit: 6 Page 27
c. Medium
d. Low
2. Does any other office personal have access to your computer?
a. Yes
b. No
3. Is your computer password protected?
a. Yes
b. No
4. Does your computer screen lock after you are away from it for a while?
a. Yes
b. No
5. Has your local authority ever tested its network for vulnerabilities or performed a risk
assessment?
a. Yes
b. No
6. Are the staffs trained to identify unnecessary adware?
a. Yes
b. No
7. Do you have unique credentials for your access to the system?
a. Yes
b. No
8. Have you saved your credentials for access to the system in the browser?
a. Yes
b. No
9. Does your local authority have a confidential agreement with the development team of the
system who has the access to the server?
a. Yes
b. No
c. May be
10. Does the third party get remote access?
Kushan Wijerathne MSCP Unit: 6 Page 28
a. Yes
b. No
c. May be
11. What email address do the employees use to register/access the system?
a. Personal
b. Official
12. If using personal email address, does the system send confidential information to the
personal email address?
a. Yes
b. No
13. Does your firm require passwords or pins for mobile devices that can access company
email or systems?
a. Yes
b. No
14. Does every laptop/PC have malware protection which satisfies the system requirements?
a. Yes
b. No
c. May be
15. Does the system accept any kind of external devices to write/change data on it
a. Yes
b. No
c. May be
16. Can employees access to other web sites using the laptop/PC?
a. Yes
b. No
c. Some
17. What is the process of printing a document?
a. Shared printer with own key code
b. Own printer
c. Shared printer
Kushan Wijerathne MSCP Unit: 6 Page 29
Reliability and Validity in Quantitative Research
The results of this test are quantitative measurements used to test quantitative studies and
speculative and speculative experimental methods. They emphasize the factors that are
calculated and tested. Based on the results of the survey, half of the separations can be resolved,
test replacement or parallel framework strategies, and average security applies to tools. Fixed
measurement management repeatedly receives the same answer. The level of reliability is
similar to an unbeatable level of quality, and a high level of stability is a high level of
negligible quality. The result can be reproduced. Whether the test expects real measurement or
the results of the exploration is honest, determines the legitimacy of the test. Golafshani (2003)
describes the validity of quantitative research as “establishing effectiveness”. Interpretation - is
the basis for interpretation, conception or assumptions, collecting data collection and sampling
plans.
Reliability and Validity in Qualitative Research
Three different ways of managing authenticity in subjective research are as approval for
inspection, communication, and activity. Investigators rely on inclusion and writing to solve
realism, universality and reliability issues. It is solved from a quantitative perspective, but it is
subjectively confusing. In subjective research, authenticity is related to depiction and
illumination, and whether the atmosphere is consistent or not, the given clarification is
consistent with the given description. Interfaces with different technologies, such as
observations, gatherings and records, will gradually lead to considerable, intense and
contrasting material advances. In order to improve the inspection and understanding of the
progress of others, triangulation is the stage by which the master incorporates some experts or
experts to interpret the data at different times or in the field. Relatedly, subjective researchers
can use the examiner triangulation and consider the ideas and clarifications created by
additional scientists of the test panel.
Kushan Wijerathne MSCP Unit: 6 Page 30
Task 3
Quantitative research analysis
Analyse data analyses for security risks, analyse data, and analyse the best way to deliver
results. Information Survey: Basically, we first checked the results of the audit information and
information. I confirmed that I had no opportunity to get more information. Information
Summary: A better way to summarize is general information about the information I collect.
Describe the details as a result.
Pie chart
Bar graph
In line
In the histogram
Pie Chart
Pie demonstration can be used for skill test to test the experimental results. When you need to
make a difference and require a specific dependency on one variable, you can share sufficient
and productive data. By all due respect, I used a pin to show my specific results.
Cutting down the cutting of the most important cut with a shade of 4-6 cuttings.
Pie charts provide accurate and clear images.
It brings out the information as an altogether part, so it is an addictive device by strangers
from an unknown group.
Analysis
18. What is the status your computer literacy?
Kushan Wijerathne MSCP Unit: 6 Page 31
Most people have medium computer literacy. So they can use the system very easily. But most
of them could not identify the malware or any kind of vulnerability.
Solution: Conduct workshops and encourage them to participate
19. Does any other office personal have access to your computer?
Unauthorized access would be less. There for vulnerability is low
20. Is your computer password protected?
Kushan Wijerathne MSCP Unit: 6 Page 32
21. Does your computer screen lock after you are away from it for a while?
When the screen si not locked, unauthorized person can access to the system through the
computer.
Solution: IT division of Kalutara UC must put screen lock to every machine
22. Has your local authority ever tested its network for vulnerabilities or performed a risk
assessment?
Kushan Wijerathne MSCP Unit: 6 Page 33
It is hard to tell that if any malware or spyware already stablished in the network. So there is a
high chance of having a cyber attack
Solution: Must do the testing the network for vulnerabilities as soon as possible.
23. Are the staffs trained to identify unnecessary adware?
As most of them have medium computer literacy, it is hard thing to find an unnecessary
adware. In their IT section, they do not have knowledge also
Solution: Scheduling workshops
24. Does your local authority have a confidential agreement with the development team of the
system who has the access to the server?
Kushan Wijerathne MSCP Unit: 6 Page 34
Most of the workers do not have any idea about this question and some of them
have not pretty sure answer. But according to the executive level management,
UC has above mentioned agreement with Development Company
25. Does the third party get remote access?
Development team can access to the system or server using Remote Desktop Connection or
Team Viewer. But the threat is the passwords which are using to login are not recurring. There
for anyone who has connected before can reconnect again without any acknowledge of Urban
council.
Solution: Using recurring passwords
26. Does your firm require passwords or pins for mobile devices that can access company
email or systems?
Kushan Wijerathne MSCP Unit: 6 Page 35
This is a major threat for the system. Anyone can access to the system via connecting mobile
and have valuable user details. And it will hard to trace back to the user.
Solution: Add a new security layer to the network and ask recurring pin or password from the
user who is going to connect to the system via mobile device. And the pin or the password must
be issued by the system admin or relevant officer.
Analysis of qualitative research
Respondent 1
When asked by the first respondents about the quality and benefits of the assessment
management system, the researcher answered positively. The program is good for everyone,
and the UC always focuses on the consumers who are aware. the environment. I asked him
about the contentment. The answer was that the products were satisfactory, but they did not
materialize
Respondent 2
A second debater was not happy about the outcome of the Clean Environment Program. This
single program could not attract the attention of the people for a short period of time. If the
defendant is required to do so and other things to be done, the respondent should regularly do
this to the UC and have a good budget for the UC . The overall evaluation of the assessment
management system at the Kalutara Urban Council was satisfactory.
Respondent 3
When the UC inquired about its potential to focus on its system efforts, the third respondent
said that the UC could be promoted. They believe system and Corporate Social Responsibility
will help boost assessment tax collection. Later, the program is beneficial to everyone, and the
UC is socially responsible, which suggests paying tax from others at the kalutara UC. Work
better than other local authorities.
Kushan Wijerathne MSCP Unit: 6 Page 36
3.2
Several proposals have been recommended for the Kalutara Urban Council to analyze the
research data using relevant tools and techniques. Following are the recommendations.
Human Resources: System requires human resources to acquire competitive advantages in the
UC. From my own experience in the recent Corporate Social Responsibility Project, I
recommend refinancing the UC's improved human resources to the UC that meets this program
time and budget limit
Complete legal procedures: When implementing system as a department head, accountant
worked out many solutions. Therefore, before any assement management system can be
obtained for competitive advantage, the UC must be managed.
Full budget: Accountant needs resources to complete a program. The UC has to prepare an
adequate budget for system initiatives so that the program is easy to implement.
Customized Product: The main feature of the quality products is the consumer 's product
.Kalutara urban council also requires customer needs for customers.
3.3
Data analysis requires a number of intimate relationships, and requires the classification of
categories, types of categories, data types, raw data, creating tables, and creating relationships.
After summarizing, the analysis is usually based on the various sizes of the calculations. It is
ugly, such as the use of clearly defined statistical statements. In analysis, it is important to
determine that it is possible to determine whether it is possible to determine whether the
relationship between conflicting or conflicting differences can occur between the original
hypothesis or the new assumption. Data analysis and submission data plays an important role.
Projected results are the only reliable source for forecasting results. Therefore, it is important to
analyze the collection of data. Therefore, incorrect data can misidentify you by the
organization, but it can be directly submitted to you accurately and accurately. Therefore, it is
wise to select a data collection method according to the expected situation of the project and
targeted varieties. As researchers, a system was selected for managing questionnaires. Select a
group of respondents representing different fields of the organization.
Kushan Wijerathne MSCP Unit: 6 Page 37
Task 4
Task 4.1
The research method for the UC is a research methodology for marketing and business analysis.
Both qualitative and quantitative research methods are carried out efficiently to meet the
objectives of the project. Above mentioned research has been carried out by the project
manager of the project to meet the requirements of this project.
The breakdown of projects will help the Project Manager to set up a specific task for the
employees and prepare their talents. Project worker degradation of the project work has been
reduced. According to the structure, the manager will be able to accomplish the project
functions within the same period. On the other hand, the amount of time required for the work
and the required amount of labor for the purpose of the project has been specified for the
project's gantry. This work is specified by Gantt chart during the period. Therefore, the
manager will be able to perform the task within the project period.
Project manager’s own learning and performances
Cost control: As a Project Manager at the Kalutara urban council, the process for managing the
cost of the project has been learned. The most important factor in the project is the control
project. I have a great deal of idea and technology about the process of cost control of the
project.
Negotiation skills: When implementing the project, I wanted to communicate with many
projects and agents. Therefore, I intend to manage the stakeholders and do good transactions
with customers. So this is a good lesson for me.
Communication skills: Communication skills are the most important factor or quality of the
manager. I was limited in communicating with customers when I started the project. But I have
received many technologies and processes to communicate with business customers after the
project.
Risk management skills: Project management Risk management must have certain conditions,
since any business project is at risk. So at the assessment management project, I got a lesson in
project risk management as a project manager. This situation has helped me. To achieve the
project, achieve the goal of the project.
4.2
The best way to find out the security risks involved in the present infrastructure of the testing
method used by the Kalutara UC is Qualitative and quantitative research was done efficiently to
fulfill the objectives of the project. As the city council decided to know the current technology
of access to existing technologies, the aforementioned repository was studied to fulfill the
project manager's project requirements. Quantitative research has revealed that employees'
ideas are more effective in working with newer technologies, but provide insights into the
current UC status and level of security that have helped to get it through quality surveys. A
Kushan Wijerathne MSCP Unit: 6 Page 38
quality survey also helped the manager to provide better proposals to improve the current UC
subsidiary.
Project project manager's task is reduced to the task of the project. According to the structure,
the manager can get the project work during that period. On the other hand, the Gantt chart of
the project specifies the amount of time required for all tasks and the number of employees
required for that task. The accountant can perform the project within the project period, as
specified in Gantt chart during the engagement period.
Kushan Wijerathne MSCP Unit: 6 Page 39
Appendix
PROJECT LOG
SHEET.docx
REFERENCES
1. Tomczyk, C. (2011). Project Manager's Spotlight on Planning.
2. Williams, M. (2008). Principles of Project Management (SitePoint. 1st ed.
Collingwood: SitePoint
3. Maylor, H. (2010). Project management. 1st ed. Harlow, England: Financial
Times Prentice Hall is an imprint of Pearson
4. Brighthub Project Management. (2017). Types of Project Costs - Examples of
the Different Variables in Project Cost Management. [online] Available at:
http://www.brighthubpm.com/project-planning/54894-example-of-costs-in-
project-management
5. Art of Comunication in Project Management : https://www.pmi.org
6. Validity, reliability, and generalizability in qualitative research :
https://www.ncbi.nlm.nih.gov
Kushan Wijerathne MSCP Unit: 6 Page 40
Kushan Wijerathne MSCP Unit: 6 Page 41
You might also like
- Unit 6 Managing A Successful Computing Project 2021Document62 pagesUnit 6 Managing A Successful Computing Project 2021ishan maduahanka0% (2)
- PCP SampleDocument81 pagesPCP SampleDulanja OmeshNo ratings yet
- CRP-Proposal NEW 2021 - 2022 Remote Working - 69 - 70Document47 pagesCRP-Proposal NEW 2021 - 2022 Remote Working - 69 - 70nethmi gunawardhana100% (2)
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument33 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsU & Me100% (2)
- Identify The Potential Impact To IT Security of Incorrect Configuration of Firewall Policies and ThirdDocument1 pageIdentify The Potential Impact To IT Security of Incorrect Configuration of Firewall Policies and Thirdaryan thapaNo ratings yet
- Unit 6 Managing A Successful Computing Research Project 2019Document96 pagesUnit 6 Managing A Successful Computing Research Project 2019Romali Keerthisinghe100% (1)
- Unit-01 Programming Assignment-HolisticDocument15 pagesUnit-01 Programming Assignment-Holisticmhmd75% (4)
- A-008550-1624879801227-80375-57-Unit 19-DsaDocument80 pagesA-008550-1624879801227-80375-57-Unit 19-DsaHansi RanasingheNo ratings yet
- Harsha Akka 013759 Unit 13 CRP Report PDFDocument94 pagesHarsha Akka 013759 Unit 13 CRP Report PDFMinda RajanNo ratings yet
- Unit 05 - Security - Holistic AssignmentDocument20 pagesUnit 05 - Security - Holistic AssignmentRangana Perera100% (1)
- 3467 HND 10 Hajanya Kalaruban Database Devolopment Management SystemDocument90 pages3467 HND 10 Hajanya Kalaruban Database Devolopment Management Systemronica100% (1)
- SampleAnswers Unit 11 Maths For Computing 1 PDFDocument59 pagesSampleAnswers Unit 11 Maths For Computing 1 PDFjanitha werallagama50% (2)
- ProDocument131 pagesProvbr businessNo ratings yet
- 794-1601898924415-Unit 34 - System Analysis and DesignDocument12 pages794-1601898924415-Unit 34 - System Analysis and DesignVirath Pradeep100% (1)
- Unit 14 - Business Intelligence-Holistic Assignment Adjusted - IV 2019.02.07Document17 pagesUnit 14 - Business Intelligence-Holistic Assignment Adjusted - IV 2019.02.07AliNo ratings yet
- Strategic Management Assignment 1Document10 pagesStrategic Management Assignment 1nganduNo ratings yet
- A-014114-1608747919893-65801-Crp - Neg - A - 014114Document84 pagesA-014114-1608747919893-65801-Crp - Neg - A - 014114AngeloNo ratings yet
- A-008550-1624688646968-80386-Unit 34 - System Analysis and Design.Document103 pagesA-008550-1624688646968-80386-Unit 34 - System Analysis and Design.Hansi Ranasinghe100% (1)
- Unit 30-Application Development-Reworded-2021Document15 pagesUnit 30-Application Development-Reworded-2021Jimmy CyrusNo ratings yet
- Btec HND Unit 5 Security New PDFDocument46 pagesBtec HND Unit 5 Security New PDFronica100% (1)
- MSCP SampleDocument41 pagesMSCP SampleRomali KeerthisingheNo ratings yet
- Unit 10 Web Design and DevelopmentDocument13 pagesUnit 10 Web Design and DevelopmentCULPRIT BOY0% (2)
- 77-1557305671121-Unit 6 Managing A Successful Computing Research Project 2019Document14 pages77-1557305671121-Unit 6 Managing A Successful Computing Research Project 2019Kevin JeromNo ratings yet
- 785-1601896966591-Unit 04 - Database - 2020Document13 pages785-1601896966591-Unit 04 - Database - 2020Udeshika WanninayakeNo ratings yet
- Unit 9 Assignment (Spring 2021)Document5 pagesUnit 9 Assignment (Spring 2021)Ultra ChannelNo ratings yet
- Unit 10 Website Design and Development (Spring 2021) 2 of 2Document3 pagesUnit 10 Website Design and Development (Spring 2021) 2 of 2Ultra ChannelNo ratings yet
- 786-1601897169527-Unit 10 - Web Design and Development - 2020Document9 pages786-1601897169527-Unit 10 - Web Design and Development - 2020Kevin JeromNo ratings yet
- Unit 5 - Assignment 2 BriefDocument3 pagesUnit 5 - Assignment 2 BriefCục MuốiNo ratings yet
- 54-1547092378635-Unit 34 SAD - Assignment 2018.11.13Document14 pages54-1547092378635-Unit 34 SAD - Assignment 2018.11.13Kevin JeromNo ratings yet
- Col e 004653 MSCP Com079Document41 pagesCol e 004653 MSCP Com079AliNo ratings yet
- Col e 004653 MSCP Com079Document41 pagesCol e 004653 MSCP Com079AliNo ratings yet
- CemexDocument21 pagesCemexMiguel Leal100% (4)
- Partner Program OverviewDocument19 pagesPartner Program OverviewfataiusNo ratings yet
- Advance Development FinalDocument119 pagesAdvance Development FinalShrawan Shraw100% (1)
- Soft Etro Ampus: #3, de Fonseka Road, Colombo 04Document60 pagesSoft Etro Ampus: #3, de Fonseka Road, Colombo 04Zion SantosNo ratings yet
- A-019730-1635326717126-114203-W.M.supun Anjana Jayasinghe-Unit 6 Managing A Successful Research Project Reviewed - Reworded - 2021Document67 pagesA-019730-1635326717126-114203-W.M.supun Anjana Jayasinghe-Unit 6 Managing A Successful Research Project Reviewed - Reworded - 2021Dishan SanjayaNo ratings yet
- 789-1601897728690-Unit 6 Managing A Successful Computing Research Project - 2020Document14 pages789-1601897728690-Unit 6 Managing A Successful Computing Research Project - 2020Kevin JeromNo ratings yet
- Unit 6 Managing A Successful Research Project)Document15 pagesUnit 6 Managing A Successful Research Project)CULPRIT BOY0% (1)
- MSCP Pasi NewDocument38 pagesMSCP Pasi NewHimsara vihanNo ratings yet
- SAD Assignment - NewDocument10 pagesSAD Assignment - Newpratheep100% (1)
- A-065211-1606734174791-53830-Unit 10 Web Design and Development - KavinDocument115 pagesA-065211-1606734174791-53830-Unit 10 Web Design and Development - KavinRehan RatnaweeraNo ratings yet
- A 019730 1634729704082 114149 W.M.S.a.jayasinghe Unit 10 Web Design and Development - Reworded - 2021Document69 pagesA 019730 1634729704082 114149 W.M.S.a.jayasinghe Unit 10 Web Design and Development - Reworded - 2021Dishan Sanjaya100% (1)
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument27 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsSusira MednisNo ratings yet
- 1183-1620008969581-UNIT 14 - Business Inteligent Assignment - Reworded 2021Document18 pages1183-1620008969581-UNIT 14 - Business Inteligent Assignment - Reworded 2021Harshi PereraNo ratings yet
- AssDocument15 pagesAssOntime Bestwriters50% (2)
- Unit 14 - Business IntelligenceDocument14 pagesUnit 14 - Business IntelligenceIshara EroshiNo ratings yet
- A 019730 1636101756198 114163 W.M.supun Anjana Jayasinghe Unit 11 - Maths For Computing - Reworded - 2021Document63 pagesA 019730 1636101756198 114163 W.M.supun Anjana Jayasinghe Unit 11 - Maths For Computing - Reworded - 2021Dishan SanjayaNo ratings yet
- Internal Verification of Assessment Decisions - Btec (RQF) : Jghigher NationalsDocument32 pagesInternal Verification of Assessment Decisions - Btec (RQF) : Jghigher NationalsSusira MednisNo ratings yet
- ABC Different Code Premnath PDFDocument81 pagesABC Different Code Premnath PDFRaishaNo ratings yet
- HND in Computing Networking Unit 2 Assignment 1 SampleDocument85 pagesHND in Computing Networking Unit 2 Assignment 1 SampleronicaNo ratings yet
- Unit 3 PPDocument44 pagesUnit 3 PPBanuka UdayangaNo ratings yet
- Discreet MathsDocument64 pagesDiscreet MathsCRi GB80% (5)
- Unit 04 - Database AssignmentDocument131 pagesUnit 04 - Database AssignmentThushan LakshithaNo ratings yet
- Unit 04 - Database Design and Development Reworded 2021Document47 pagesUnit 04 - Database Design and Development Reworded 2021Cool Martt50% (2)
- Advance Programming Final 1Document93 pagesAdvance Programming Final 1Shrawan ShrawNo ratings yet
- A-019730-1659516307423-163428-W.M.supun Anjana Jayasinghe Advanced Programming - Reworded - 2021Document115 pagesA-019730-1659516307423-163428-W.M.supun Anjana Jayasinghe Advanced Programming - Reworded - 2021Dishan SanjayaNo ratings yet
- 788-1601897459456-Unit 05 - Security - 2020Document14 pages788-1601897459456-Unit 05 - Security - 2020Career and EducationNo ratings yet
- 203-1540467331035-Unit 5 Security 2018.07.03Document13 pages203-1540467331035-Unit 5 Security 2018.07.03SajithNo ratings yet
- A-011814-1612368830998-72379-Lahiru Viraj - ME24716 - 799-1601899513739-Unit 18 - Discrete MathematicsDocument89 pagesA-011814-1612368830998-72379-Lahiru Viraj - ME24716 - 799-1601899513739-Unit 18 - Discrete MathematicsLahiru VirajNo ratings yet
- Adv ProgrammingDocument93 pagesAdv Programmingshahzad sultanNo ratings yet
- MSCP AssignmentDocument55 pagesMSCP AssignmentSadeep SanchanaNo ratings yet
- 5214-1693458878915-Unit 6 2023 To 2024 Academic Year AssignmentDocument16 pages5214-1693458878915-Unit 6 2023 To 2024 Academic Year Assignmentpromodubiz.seoNo ratings yet
- Chapter OneDocument47 pagesChapter Oneronica cooreyNo ratings yet
- Unit 02 Networking Reworded 2022 Ahmed MushtaqDocument130 pagesUnit 02 Networking Reworded 2022 Ahmed MushtaqAhamedNo ratings yet
- Unit 06 Managing A Successful Research Project 2018.10.23Document14 pagesUnit 06 Managing A Successful Research Project 2018.10.23Thab ThabNo ratings yet
- Jalina MSCP AssignmentDocument49 pagesJalina MSCP Assignmentchamidu hansajithNo ratings yet
- Unit 40 - User Interface and User Experience Designing - Assignment 1 of 1Document18 pagesUnit 40 - User Interface and User Experience Designing - Assignment 1 of 1Ali0% (2)
- Ratio AnalysisDocument79 pagesRatio Analysisanjali dhadde100% (1)
- Dhaka Stock Exchange LimitedDocument11 pagesDhaka Stock Exchange LimitedCarl JohnsonNo ratings yet
- Agreement of Leave and LicenceDocument5 pagesAgreement of Leave and Licencevijhay_adsuleNo ratings yet
- Distribution ChannelDocument38 pagesDistribution ChannelSomalKantNo ratings yet
- Special Pricing PracticesDocument42 pagesSpecial Pricing PracticesJermaine Montaque100% (1)
- These Are Some of The Flavors: Sold in Stores, Restaurants, and in More Than 200 CountriesDocument4 pagesThese Are Some of The Flavors: Sold in Stores, Restaurants, and in More Than 200 CountriesPrasad JoshiNo ratings yet
- The Role of Social Capital in CSR (Unilever Indonesia) PDFDocument10 pagesThe Role of Social Capital in CSR (Unilever Indonesia) PDFKartika DewiNo ratings yet
- Mku M.B.A Airline Airport ManagementDocument23 pagesMku M.B.A Airline Airport ManagementRam KishoreNo ratings yet
- Espd ResponseDocument18 pagesEspd ResponseDaniel TaradaciucNo ratings yet
- 2 Cost of Project: Sr. No. Particulars Cultivation 1 Cost of Cultivation Planting MaterialDocument26 pages2 Cost of Project: Sr. No. Particulars Cultivation 1 Cost of Cultivation Planting MaterialshroffhardikNo ratings yet
- OPTIMUM Catalogue 2019 ENDocument254 pagesOPTIMUM Catalogue 2019 ENlmelmelme100% (1)
- Establishing The Effectiveness of Market Ratios in Predicting Financial Distress of Listed Firms in Nairobi Security Exchange MarketDocument13 pagesEstablishing The Effectiveness of Market Ratios in Predicting Financial Distress of Listed Firms in Nairobi Security Exchange MarketOIRCNo ratings yet
- Narrative ReportDocument8 pagesNarrative ReportNico ParboNo ratings yet
- ET SCM&Logistics SummitDocument8 pagesET SCM&Logistics SummitSagar ShindeNo ratings yet
- TF26Document2 pagesTF26Gohar Muhammad KhanNo ratings yet
- Mcdonalds ProjectDocument44 pagesMcdonalds ProjectMitika TutejaNo ratings yet
- Small Scale IndustriesDocument37 pagesSmall Scale IndustriesMRINAL KAUL100% (1)
- 2018 Profile of International Residential Real Estate in Florida 10-25-2018Document30 pages2018 Profile of International Residential Real Estate in Florida 10-25-2018National Association of REALTORS®100% (1)
- FAR1 - Bank Reconciliation and Proof of CashDocument2 pagesFAR1 - Bank Reconciliation and Proof of CashHoney MuliNo ratings yet
- Hedonic Shopping MotivationDocument23 pagesHedonic Shopping MotivationHạ QuânNo ratings yet
- View SoaDocument6 pagesView SoaZinampan GarrijayNo ratings yet
- Amended Articles of IncorporationDocument4 pagesAmended Articles of IncorporationRenson BernabeNo ratings yet
- Why Cities Matter Saskia-SassenDocument14 pagesWhy Cities Matter Saskia-Sassenpranavcha100% (1)
- Aas 2Document3 pagesAas 2Rishabh GuptaNo ratings yet
- Financial Statement Elements of Hotel DepartmentDocument4 pagesFinancial Statement Elements of Hotel DepartmentsarasatiwanamiNo ratings yet
- Catia PLM ExpressDocument10 pagesCatia PLM ExpresstkferaNo ratings yet
- Ch07tifDocument39 pagesCh07tifJc Quismundo100% (1)