Professional Documents
Culture Documents
cmptn2 PDF
cmptn2 PDF
Uploaded by
mukesh244Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
cmptn2 PDF
cmptn2 PDF
Uploaded by
mukesh244Copyright:
Available Formats
logixfirm
The legend lists R for all RIP routes in the routing table. Also note that the administrative
distance of 120 is shown, together with the metric of 1.
passive-interface command
Consider the following example network with RIP turned on:
The RIP configuration on R2 looks like this:
router rip
version 2
network 10.0.0.0
network 192.168.0.0
As we’ve already mentioned, the network command does two things:
advertises the defined network in RIP.
activates RIP on the interfaces whose addresses fall within the specified classful networks.
So in the example network above, RIP will also be activated on the interface connected to the
workstation on the right. This means that the workstation will also receive RIP updates, which is
pointless. To prevent this from happening, the passive interface command is used:
R2(config)#router rip
R2(config-router)#passive-interface Gi0/1
Logixfirm network fundamental Page 1
logixfirm
Now, the RIP process will no longer send RIP updates out the Gi0/1 interface. However, all
received RIP updates will be processed and the subnet 10.0.0.0/24 will still be advertised.
RIP loop prevention
Distance vector protocols are susceptible to routing loops. Routing loops occur when a packet is
continually routed through the same routers over and over again, in an endless circle. Because
they can render a network unusable, distance vector routing protocols (such as RIP and EIGRP)
employ several different mechanisms to prevent routing loops. We will describe them in this
article.
Split Horizon
Split horizon is one of the features of distance vector routing protocols that prevents routing
loops. This feature prevents a router from advertising a route back onto the interface from which
it was learned.
Consider the following network topology:
Router R1 has a route to the subnet 10.0.1.0/24 that is advertised to router R2 by using RIP.
Router R2 receives the update and stores the route in its routing table. Router R2 knows that the
routing update for that route has come from R1, so it won’t advertise the route back to router
R1. Otherwise, if the network 10.0.1.0/24 goes down, router R1 could receive a route to the
subnet 10.0.1.0/24 from R2. Router R1 would think that R2 has the route to reach the subnet,
and would send packets destinated for the 10.0.1.0/24 to R2. R2 would receive the packets from
R1 and sends them back to R1, because R2 thinks that R1 has a route to reach the subnet,
thereby creating a routing loop.
Route poisoning
Route poisoning is another method for preventing routing loops employed by distance vector
routing protocols. When a router detects that one of its directly connected routes has failed, it
sends the advertisement for that route with an infinite metric (poisoning the route). A router that
receives the update knows that the route has failed and doesn’t use it anymore.
Consider the following example:
Router R1 is directly connected to the 10.0.1.0/24 subnet. Router R1 runs RIP and the subnet is
advertised to R2. When the R1’s Fa0/1 interface fails, the route advertisement is sent by R1 to
Logixfirm network fundamental Page 2
logixfirm
R2 indicating that the route has failed. The route has a metric of 16, which is more than the
RIP’s maximum hop count of 15, so R1 considers the route to be unreachable.
Holddown timer
Holddown is another loop-prevention mechanism employed by distance vector routing protocol.
This feature prevents a router from learning new information about a failed route. When a router
receives the information about the unreachable route, the holddown timer is started. The router
ignores all routing updates for that route until the timer expires (by default, 180 seconds in RIP).
Only updates allowed during that period are updates sent from the router that originally
advertised the route. If that router advertise the update, the holddown timer is stopped and the
routing information is processed.
An example will help you understand the concept better. Consider the following network
topology.
Router R1 has advertised its directly connected subnet 10.0.1.0/24 through RIP. After some
period of time, the interface Fa0/1 on R1 fails and the router R1 sends the poisoned route to R2.
R2 receives the routing update, marks the route as unreachable and starts the holddown timer.
During that time all updates from any other routers about that route are ignored to prevent
routing loops. If interface Fa0/1 on R1 comes back up, R1 again advertises the route. R2 process
that update even if the holddown timer is still running, because the update is sent by the same
router that originally advertised the route.
Advertise default routes using RIP
Consider the following example network:
Logixfirm network fundamental Page 3
logixfirm
In the network above we have three routers running RIP. Router R3 is connected to the ISP’s
internet router and and has a static default route that points to it. It is possible to advertise that
default route using RIP to other routers in the local network. On R3, we simply need to enter
the default-information originate command in the RIP configuration mode.
Here is the configuration on R3:
R3(config)#ip route 0.0.0.0 0.0.0.0 50.50.50.1
R3(config)#router rip
R3(config-router)#default-information originate
R1 and R2 don’t need any additional configuration – they learn the default route just like any
other RIP route:
R1#show ip route rip
R* 0.0.0.0/0 [120/1] via 10.0.0.1, 00:00:04, GigabitEthernet0/0
As you can see from the output above, R1 learned about the default route via RIP. The route is
marked with an asterisk (*), indicating that the route is a candidate to be the default route.
Introduction to Virtual LAN:-
What is a VLAN?
VLANs (Virtual LANs) are logical grouping of devices in the same broadcast domain. VLANs are
usually configured on switches by placing some interfaces into one broadcast domain and some
interfaces into another. VLANs can be spread across multiple switches, with each VLAN being
treated as its own subnet or broadcast domain. This means that frames broadcasted onto the
network will be switched only between the ports within the same VLAN.
A VLAN acts like a physical LAN, but it allows hosts to be grouped together in the same
broadcast domain even if they are not connected to the same switch. Here are the main reasons
why you should use VLANs in your network:
VLANs increase the number of broadcast domains while decreasing their size.
VLANs reduce security risks by reducing the number of hosts that receive copies of frames
that the switches flood.
you can keep hosts that hold sensitive data on a separate VLAN to improve security.
you can create more flexible network designs that group users by department instead of by
physical location.
network changes are achieved with ease by just configuring a port into the appropriate VLAN.
Logixfirm network fundamental Page 4
logixfirm
The following topology shows a network with all hosts inside the same VLAN:
Without VLANs, a broadcast sent from host A would reach all devices on the network. By placing
interfaces Fa0/0 and Fa0/1 on both switches into a separate VLAN, a broadcast from host A
would reach only host B, since each VLAN is a separate broadcast domain and only host B is
inside the same VLAN as host A. Hosts in VLAN 3 and VLAN 5 will not even be aware that the
communication took place. This is shown in the picture below:
Logixfirm network fundamental Page 5
logixfirm
NOTE
To reach hosts in another VLAN, a router is needed.
Access & trunk ports
Each port on a switch can be configured as either an access or a trunk port. An access port is a
port that can be assigned to a single VLAN. This type of interface is configured on switch ports
that are connected to devices with a normal network card, for example a host on a network. A
trunk interface is an interface that is connected to another switch. This type of interface can
carry traffic of multiple VLANs.
In the example network pictured above, the link between SW1 and SW2 would be configured as
a trunk interface. All other switch ports connect to end user devices, so they would need to be
configured as access ports.
Configuring VLANs
By default, all ports on a switch are in the VLAN 1. We can verify that by typing the show
vlan command from the IOS enable mode of a switch:
In the picture above, you can see that all of the 24 ports of the switch are in the same VLAN,
namely VLAN 1.
Two steps are required to create a VLAN and assign a switch port to the VLAN:
1. create a vlan using the vlan NUMBER global mode command
2. assing a port to the VLAN by using two interface subcommands. The first command is
the switchport mode access command. This command specifies that the interface is an access interface. The
second command is the switchport access vlan NUMBER command. This command assigns the interface to a
VLAN.
Logixfirm network fundamental Page 6
logixfirm
Here is an example of assigning the VLAN 2 to the interface:
The first command (vlan 2) created the VLAN 2. We’ve then entered the Fa0/1 subinterface
mode and configured the interface as an access interface that belongs to VLAN 2. To verify this,
we can again use the show vlan command:
Configuring access & trunk ports
To configure an interface to be an access interface, the switchport mode acess interface
command is used. This type of interface can be assigned only to a single VLAN.
To configure a trunk interface, the switchport mode trunk interface command is used. This type
of interface can carry traffic of multiple VLANs.
An example will help you understand the concept.
Logixfirm network fundamental Page 7
logixfirm
Host A and host B are in different VLANs, VLAN 1 and VLAN 2. These ports need to be configured
as access ports and assigned to their respective VLANs by using the following sequence of
commands:
Because the link between SW1 and SW2 needs to carry traffic of multiple VLANs, it needs to be
configured as a trunk interface. This is done by using the following commands on both SW1 and
SW2:
On SW1:
On SW2:
Now the link between SW1 and SW2 can carry traffic from both the VLAN1 and VLAN2. You can
verify that an interface is indeed a trunk interface by using the show interface Fa0/3
switchport command on SW1:
Logixfirm network fundamental Page 8
logixfirm
NOTE
VLAN 1 doesn’t have to be created, it exists by default. Also, by default, all ports are in the VLAN
1, so Fa0/1 doesn’t need the switchport access vlan 1 command.
Frame tagging
To identify the VLAN a packet is belonging to, switches use tagging to assign a numerical value
to each frame in a network with multiple VLANs. This is done to ensure that switches know out
which ports to forward frames.
For example, consider the following network topology.
There are two VLANs in the toplogy pictured above, namely VLAN 3 and VLAN 4. Host A sends a
broadcast packet to switch SW1. Switch SW1 receives the packet, tags the packet with the VLAN
ID of 3 and sends it to SW2. SW2 receives the packet, looks up at the VLAN ID, and forwards the
packet only out the port Fa0/1, since only that port is in VLAN 3. Host B and host C will not
receive the packet because they are in different VLAN than host A.
NOTE
When forwarding a tagged frame to a host device a switch will remove the VLAN tag, since host
devices don’t understand tagging and would drop the packet.
IEEE 802.1Q
IEEE 802.1Q is one of the VLAN tagging protocols supported by Cisco switches. This standard
was created by the Institute of Electrical and Electronics Engineers (IEEE), so it an open standard
and can be used on non-Cisco switches.
To identify to which VLAN a frame belongs to, a field is inserted into the frame’s header.
Original frame:
802.1Q frame:
An example will attempt to clarify the concept. Let’s say that we have a network of 2 switches
and 4 hosts. Hosts A and host D are in VLAN 2, while hosts B and C are in VLAN 3.
Logixfirm network fundamental Page 9
logixfirm
On the segment between two switches, a process called VLAN trunking is used. Let’s say that
host A sends a broadcast frame. SW1 “tags” the frame by inserting the VLAN ID in the header of
the frame before sending the frame to SW2. SW2 receives the frame and knows that the frame
belongs to VLAN 3, so it sends the frame only to host D, since that host is in VLAN 3.
Inter-Switch Link (ISL)
Another VLAN tagging protocol is Inter-Switch Link (ISL). This protocol is Cisco proprietary,
which means that, unlike 802.1Q, it can be used only between Cisco switches. It is considered to
be deprecated, and newer Cisco switches don’t even support it.
ISL works by encapsulating a frame in an ISL header and trailer. The encapsulated frame
remains unchanged. The VLAN ID is included in the ISL header.
Original frame:
ISL frame:
UNIT- IV
Logixfirm network fundamental Page 10
logixfirm
Transport Layer: -
Transport Layer is the third layer of the four layer TCP/IP model. The position of the Transport layer is
between Application layer and Internet layer. The purpose of Transport layer is to permit devices on the
source and destination hosts to carry on a conversation. Transport layer defines the level of service and
status of the connection used when transporting data.
The main protocols included at Transport layer are TCP (Transmission Control Protocol) and UDP (User
Datagram Protocol)
Functions of transport layer:-
The Transport layer includes two major protocols Transmission Control Protocol (TCP) and User
Datagram Protocol (UDP). Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) at
the Transport Layer help in data communication as explained below.
1) An interface for network applications to access the network.
2) Provides means accepting data from different applications and directing that data to the recipient
application on the receiving device (Multiplexing). Same way, on the receiving device the data need to
be directed to the correct application, for that data was meant for (De-multiplexing).
3) Error checking, flow control, and verification. Two major protocols at the Transport
layer, Transmission Control Protocol (TCP) and User Datagram Protocol (UDP), work differently to
achieve these goals.
Transmission Control Protocol (TCP): TCP is a reliable protocol. TCP provides extensive error control
and flow control to ensure the successful delivery of data. TCP is called as a connection-oriented
protocol.
User Datagram Protocol (UDP): UDP is not a reliable protocol. There is no error checking features
for UDP and is designed for situations when extensive control features are not necessary. User Datagram
Protocol (UDP) is called as a connectionless protocol.
Difference between working of TCP and UDP:-
Logixfirm network fundamental Page 11
logixfirm
The Transmission Control Protocol/Internet Protocol (TCP/IP) suite was created by the U.S. Department of
Defense (DoD) to ensure that communications could survive any conditions and that data integrity wouldn't be
compromised under malicious attacks.
The Open Systems Interconnection Basic Reference Model (OSI Model) is an abstract description for
network protocol design, developed as an effort to standardize networking.
In this article, I will present the differences between the DoD and the OSI models and then provide details
about the DoD's version of TCP/IP. I will also describe the protocols used at the various layers of the DoD
model and provide you with the details of TCP and UDP protocols so you can see the differences between TCP
and UDP. Throughout this article you will find useful information concerning the protocol suite of the century:
TCP/IP.
Logixfirm network fundamental Page 12
logixfirm
TCP/IP and the OSI Model Comparison
Let's Start by Comparing TCP/IP and the OSI Models. The TCP/IP model is basically a shorter version of the
OSI model. It consists of four instead of seven layers. Despite their architectural differences, both models have
interchangeable transport and network layers and their operation is based upon packet-switched technology.
The diagram below indicates the differences between the two models:
Application Layer: The Application layer deals with representation, encoding and dialog control issues. All these issues are
combined together and form a single layer in the TCP/IP model whereas three distinctive layers are defined in the OSI model.
Logixfirm network fundamental Page 13
logixfirm
Host-to-Host: Host-to-Host protocol in the TCP/IP model provides more or less the same services with its equivalent
Transport protocol in the OSI model. Its responsibilities include application data segmentation, transmission reliability, flow and
error control.
Internet: Again Internet layer in TCP/IP model provides the same services as the OSIs Network layer. Their purpose is to route
packets to their destination independent of the path taken.
Network Access: The network access layer deals with all the physical issues concerning data termination on network media.
It includes all the concepts of the data link and physical layers of the OSI model for both LAN and WAN media.
The diagram below shows clearly the way TCP/IP protocol suite relates to the TCP/IP model.
Logixfirm network fundamental Page 14
logixfirm
Host-to-Host Layer Protocols
Two protocols: Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) are defined for
transmitting datagrams. We will look at the details of both these protocols as well as their interaction with the
upper layer.
What is the difference between TCP and UDP?
Transmission Control Protocol (TCP)
TCP is connection-oriented in the sense that prior to transmission end points need to establish a connection
first. TCP protocol data units are called segments. The sending and receiving TCP entities exchange data in
the form of segments, which consist of a fixed 20-byte header followed by a variable size data field.
TCP is responsible for breaking down a stream of bytes into segments and reconnecting them at the other end,
retransmitting whatever might be lost and also organizing the segments in the correct order. The segment size
is restricted by the maximum transfer unit (MTU) of the underlying link layer technology (MTU is generally 1500
bytes which is the maximum payload size of the Ethernet).
The image below shows the TCP segment format. The most important fields are explained further on.
Logixfirm network fundamental Page 15
logixfirm
Source Port and Destination Port fields together identify the two local end points of the particular connection. A port plus its
hosts' IP address forms a unique end point. Ports are used to communicate with the upper layer and distinguish different
application sessions on the host.
The Sequence Number and Acknowledgment Number fields specify bytes in the byte stream. The sequence number is
used for segment differentiation and is useful for reordering or retransmitting lost segments. The Acknowledgment number is
set to the next segment expected.
Data offset or TCP header length indicates how many 4-byte words are contained in the TCP header.
The Window field indicates how many bytes can be transmitted before an acknowledgment is received.
The Checksum field is used to provide extra reliability and security to the TCP segment.
The actual user data are included after the end of the header.
Let's have a look at how a TCP segment is captured by Ethereal network analyzer. The image below shows a
request-response message sequence carried over TCP. Notice the fields discussed above: Source Port,
Destination Port, Sequence number, Acknowledgement number, Window size and checksum.
Logixfirm network fundamental Page 16
logixfirm
Logixfirm network fundamental Page 17
logixfirm
User Datagram Protocol (UDP)
UDP protocol consists of fewer fields compared to TCP. The reason for that is because certain data types do
not require reliable delivery and extra overhead. Real-time traffic for example, needs to be transported in an
efficient way without error correction and retransmission mechanisms.
UDP is considered to be a connectionless protocol. It leaves reliability to be handled by the application layer.
All it cares about is fast transmission. The UDP segment format is presented in the diagram below:
Let's see how a UDP segment is captured by Ethereal. Notice the small header size.
Logixfirm network fundamental Page 18
logixfirm
Which One Should You Use?
Choosing the right transport protocol to use depends on the type of data to be transferred. For information that
needs reliability, sequence transmission and data integrity -- TCP is the transport protocol to use. For data that
require real-time transmission with low overhead and less processing -- UDP is the right choice.
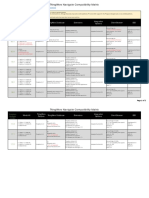
The following table summarizes the key-characteristics of each one of these protocols. Keep them in mind
when choosing the transport protocol for your data.
Logixfirm network fundamental Page 19
logixfirm
Application Layer:-
The lower layers of TCP/IP protocol suit are primarily concerned with formatting, encapsulating and
transmitting data across the network. These layers are closely associated with the underlying network
hardware and network infrastructure devices.
The topmost layer, Application Layer of TCP/IP protocol suit suit is concerned mainly with human
interaction and the implementation of software applications and related protocols.
TCP/IP protocol suit is included with a large number of applications and application protocols. Using these
applications and application protocols, data can be moved between hosts, and remote users can
communicate. Following are a partial list of applications and application protocols included with TCP/IP
protocol suit and operate in the Application Layer.
Hypertext Transfer Protocol (HTTP)
Simple Mail Transfer Protocol (SMTP)
Dynamic Host Configuration Protocol (DHCP)
Domain Name System (DNS)
Simple Network Management Protocol (SNMP)
File Transfer Protocol (FTP)
Trivial File Transfer Protocol (TFTP)
Domain Name System (DNS),
DNS in Networking-
DNS is short for Domain Name Service or Domain Name System.
It is an application layer protocol.
Purpose-
DNS is a host name to IP Address translation service.
It converts the names we type in our web browser address bar to the IP Address of web servers hosting those sites.
Need-
Logixfirm network fundamental Page 20
logixfirm
The need for Domain Name Service arises due to the following reasons-
Point-01:
IP Addresses are not static and may change dynamically.
So, a mapping is required which maps the domain names to the IP Addresses of their web servers.
Point-02:
IP Addresses are a complex series of numbers.
So, it is difficult to remember IP Addresses directly while it is easy to remember names.
DNS Resolution-
DNS Resolution is a process of resolving a domain name onto an IP Address.
The following diagram illustrates the process of DNS resolution-
The steps involved in DNS Resolution are-
Logixfirm network fundamental Page 21
logixfirm
Step-01:
A user program sends a name query to a library procedure called the resolver.
Step-02:
Resolver looks up the local domain name cache for a match.
If a match is found, it sends the corresponding IP Address back.
If no match is found, it sends a query to the local DNS server.
Step-03:
DNS server looks up the name.
If a match is found, it returns the corresponding IP Address to the resolver.
If no match is found, the local DNS server sends a query to a higher level DNS server.
This process is continued until a result is returned.
Step-04:
After receiving a response, the DNS client returns the resolution result to the application.
Important Notes-
Note-01:
DNS uses UDP (port 53) at the transport layer.
DNS uses UDP at the transport layer due to the following reasons-
Point-01:
UDP is much faster than TCP.
TCP is slow as it uses Three-way handshake to start the data transfer.
Point-02:
DNS requests are very small.
So, they fits well within UDP segments.
Logixfirm network fundamental Page 22
logixfirm
Point-03:
Although UDP is not reliable but reliability can be added on application layer.
Reliability can be added by using timeouts and resend at the application layer.
Thus, in the end both speed and protection are achieved.
Note-02:
DNS is a connection less protocol.
DNS uses UDP at the transport layer for replying to the DNS queries of clients.
Therefore, it is a connection less protocol.
Note-03:
DNS is non-persistent.
Note-04:
DNS is a stateless protocol.
This is because-
DNS server accepts the requests, process them, resolves the query and forget about them.
It does not make any assumption how long this will be.
Note-05:
Mapping an IP Address onto a domain name is referred to as Inverse domain.
It is important to note-
DNS can translate a domain name onto an IP Address.
Also, it can translate an IP Address onto a domain name.
Note-06:
Logixfirm network fundamental Page 23
logixfirm
For the first time,
There is more delay in translating the domain name onto an IP Address.
Converting a domain name onto an IP Address is an extra overhead.
This overhead is called as DNS Overhead.
It causes an unnecessary delay in serving the request.
So, there is more delay for the first time.
To reduce the delay next time, IP Addresses are stored in the computer using log.
This avoids the DNS overhead next time and takes less time in serving the request.
When it gets expired, the request is again served through DNS.
Remote logging,(Telnet):- A remote login facility permits a user who is using
one computer to interact with a program on another computer. The service
extends the login concept used by conventional timesharing computer
systems to permit access to a remote timesharing system.
The Internet's remote login service is called TELNET. To use the service,
one must invoke a local application program and specify a remote machine.
The local program becomes a client, which forms a connection to a server
on the remote computer. The client passes keystrokes and mouse
movements to the remote machine, and displays output from the remote
machine on the user's display screen.
Remote login is significant because it shows how the Internet can provide
interactive services. Unlike other available services, remote login does not
merely transfer static data. Instead, remote login permits a user to interact
with a program that runs on a remote computer. The remote program can
respond to input from the usre, and the user can respond to output the
display program displays.
Logixfirm network fundamental Page 24
logixfirm
FTP:-
File Transfer Protocol-
FTP is short for File Transfer Protocol.
It is an application layer protocol.
Purpose-
It is used for exchanging files over the internet.
It enables the users to upload and download the files from the internet.
Working-
FTP establishes two TCP connections between the client and the server.
One connection is used for transferring data.
Other connection is used for transferring control information.
Characteristics of FTP-
FTP uses TCP at the transport layer.
FTP uses port number 21 for control connection.
FTP uses port number 20 for data connection.
FTP uses persistent TCP connections for control connection.
FTP uses non-persistent connections for data connection.
FTP is a connection oriented protocol.
FTP is an out-of-band protocol as data and control information flow over different connections.
SMTP is a stateful protocol.
Important Notes-
Note-01:
Logixfirm network fundamental Page 25
logixfirm
Emails can’t be sent using FTP.
This is because-
FTP requires the connection establishment between the client and server before transferring the files.
So, both have to be online at the same time.
That is why, emails are not sent using FTP.
Note-02:
FTP can transfer one file at a time.
FTP is used for transferring one file at a time in either direction between the client and the server.
Note-03:
FTP is a stateful protocol.
This is because-
The client establishes control connection for the duration of an FTP session.
It typically spans multiple data transfers.
So, FTP is a stateful protocol
HTTP:-
Hypertext Transfer Protocol (HTTP) is the protocol that enables the connection between a web server and
a client. Hypertext Transfer Protocol (HTTP) is an application layer protocol for distributing information
in the World Wide Web (WWW). Hypertext Transfer Protocol (HTTP) is based on the client–server
architecture. An Hypertext Transfer Protocol (HTTP) server (commonly called as a web server) uses
the well-known port number 80. Examples of Hypertext Transfer Protocol (HTTP) Server or web server
are Internet Information Server (IIS), Apache Web Server etc. A Hypertext Transfer Protocol (HTTP)
client is also called a web browser (Mozilla FireFox, Internet Explorer, Google chrome etc). Hypertext
Transfer Protocol (HTTP) operates on a request-response model. A browser sends a request to a server for
a file, and the server responds with the requested file if it is available.
Logixfirm network fundamental Page 26
logixfirm
In WWW, information is typically provided as Hypertext Markup Language (HTML) files (called web
pages). WWW resources are specified by Uniform Resource Locators (URL). Uniform Resource Locator
identifies where a resource is available and the mechanism for retrieving it.
An example for Uniform Resource Locator is http://www.omnisecu.com/tcpip/index.php. The first part of
a URL is the protocol part, which is identified by “http://”. When we use any other protocol like File
Transfer Protocol (FTP), this part can be replaced by “ftp://”. The protocol pat is followed by a server
domain name or server IP address, and path to a resource (an.HTML file or a PHP server side program).
Hypertext Transfer Protocol (HTTP) messages are English-based and flexible. Format of Hypertext
Transfer Protocol (HTTP) headers are given below.
A Hypertext Transfer Protocol (HTTP) client request.
GET / HTTP/1.1
Host: www.google.com
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; en-US; rv:1.9.0.7) Gecko/2009021910 Firefox/3.0.7 (.NET CLR
3.5.30729)
Accept: text.html,application/.html+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-us,en;q=0.5
Accept-Encoding: gzip,deflate
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7
Keep-Alive: 300
Connection: keep-alive
A Hypertext Transfer Protocol (HTTP) Server Response
HTTP/1.x 200 OK
Cache-Control: private, max-age=0
Date: Sat, 21 Mar 2009 04:09:39 GMT
Expires: -1
Content-Type: text.html; charset=UTF-8
Content-Encoding: gzip
Server: gws
Content-Length: 2671
Since HTTP/1.0, the first line of the HTTP response is called the status line and includes a numeric status code (As in example
200) and the reason in text ("OK").
In Simple Mail Transfer Protocol (SMTP) - How SMTP works lesson, you will learn the basics of Simple Mail Transfer
Protocol (SMTP), RFC's related with Simple Mail Transfer Protocol (SMTP) and the working of Simple Mail Transfer
Logixfirm network fundamental Page 27
logixfirm
Protocol (SMTP).
An electronic mail (e-mail) allows users to send mails across an internet. E-mail is one of the most widely used application
services in internet and widely used in business activities. Currently, the electronic mail (e-mail) standard for the Internet is
Simple Mail Transport Protocol (SMTP). SMTP is the Application Level protocol that handles message services
over TCP/IP networks. SMTP uses TCP Well Known port 25.
SMTP was first defined in RFC 788 in 1981. In 1982, RFC 821 revised SMTP, along with RFC 822. In 2001, major revisions
of RFC 821 and 822 were released as RFC 2821 (SMTP) and RFC 2822 (Internet Message Format).
The exchange of email using TCP is performed by a message transfer agent (MTA). An example for MTA for UNIX
Operating Systems is Sendmail. End users normally don't deal with the MTA. MTA's are set by the System Administrators.
The communication between a SMTP client and SMTP server is by human readable ASCII text.
How Simple Mail Transfer Protocol (SMTP) works
Simple Mail Transfer Protocol (SMTP) is based on end-to-end message delivery. An Simple Mail Transfer Protocol (SMTP)
client contacts the destination host's Simple Mail Transfer Protocol (SMTP) server on well-known port 25, to deliver the mail.
The client then waits for the server to send a 220 READY FOR MAIL message. Upon receipt of the 220 message, the client
sends a HELO command. The server then responds with a "250 Requested mail action okay" message.
After this, the mail transaction will begin with a MAIL command that gives the sender identification as well as a FROM: field
that contains the address to which errors should be reported.
After a successful MAIL command, the sender issues a series of RCPT commands that idenclfy recipients of the mail message.
The receiver will the acknowledge each RCPT command by sending 250 OK or by sending the error message 550 No such
user here.
After all RCPT commands have been acknowledged, the sender issues a DATA command to inform the receiver that the
sender is ready to transfer a complete mail message. The receiver responds with message 354 Start mail command with an
ending sequence that the sender should use to terminate the message data. The termination sequence consists of 5 characters:
carriage return, line feed, period, carriage return, and line feed (<CRLF>.<CRLF>).
The client now sends the data line by line, ending with the 5-character sequence <CRLF>.<CRLF> line, upon which the
receiver will acknowledge with a 250 OK, or an appropriate error message if anything went wrong.
After the sending is completed, the client can follow any of these actions.
Terminate Session: If the current Simple Mail Transfer Protocol (SMTP) client has no more messages to send, the connection
can be closed with a QUIT command, which will be answered with a 221 Service closing transmission channel reply.
Exchange Roles: If the current Simple Mail Transfer Protoco (SMTP) client has no more messages to send, but is ready to
receive any messages from the current Simple Mail Transfer Protoco (SMTP) server, it can issue the TURN command. Now
the SMTP client and the SMTP server will switch their role of sender/receiver, and the sender (previous receiver) can now
send messages by issuing a MAIL command.
Send Another Mail: If the Simple Mail Transfer Protoco (SMTP) client (sender) has another message to send, it can issue a
new MAIL command.
Dynamic Host Configuration Protocol (DHCP) is used to dynamically (automatically) assign TCP/IP configuration parameters to network
devices (IP address, Subnet Mask, Default Gateway, DNS server etc). Dynamic Host Configuration Protocol (DHCP) is described in RFC
1531. Other RFCs related with Dynamic Host Configuration Protocol (DHCP) are RFC 1534, RFC 1541, RFC 2131, and RFC 2132. DHCP is
an IETF standard based on the BOOTP protocol. A computer that gets its configuration information by using Dynamic Host Configuration
Protocol (DHCP) is known as a Dynamic Host Configuration Protocol (DHCP) client. DHCP clients communicate with a DHCP server to
obtain IP addresses and related TCP/IP configuration information. DHCP server should be configured properly by the DHCP administrator.
Using Dynamic Host Configuration Protocol (DHCP), DHCP Clients cab be configured with TCP/IP configuration values like IP Address,
Subnet Mask, Default Gateway, DNS Server, DNS suffix etc.
How Dynamic Host Configuration Protocol (DHCP) Works?
The Dynamic Host Configuration Protocol (DHCP) client TCP/IP software is not configured with a static IP address and it is configured to
obtain an IP address dynamically from a Dynamic Host Configuration Protocol (DHCP) Server. When a DHCP client device boots up, it not
capable send and receive network traffic, because TCP/IP is not configured. But it can participate in broadcast traffic. DHCP Clients and
DHCP Servers uses broadcast messages to communicate with each other. The scope of a broadcast message is only within the local broadcast
domain. Broadcast messages will never cross the router to reach another network, because Routers drop Limited Broadcast IP Address .
Two important IPv4 addresses used in DHCPv4 messages are 0.0.0.0 and 255.255.255.255. IPv4 address 0.0.0.0 is used by an IPv4 device,
Logixfirm network fundamental Page 28
logixfirm
when it has not yet been assigned an IPv4 address. When a DHCP client boots up, it doesnt have a valid IPv4 Address.
IPv4 address 255.255.255.255 is also known as Limited Broadcast IP Address . An IPv4 datagram with 255.255.255.255 as destination IPv4
address is broadcasted in the LAN.
DHCPDISCOVER and DHCPREQUEST messages are sent from DHCP Client to DHCP Server. DHCPOFFER and DHCPACK messages
are sent from DHCP Server to DHCP Client.
The process of leasing TCP/IP configuration from the Dynamic Host Configuration Protocol (DHCP) server involves four steps as listed
below.
1. DHCPDISCOVER: The Dynamic Host Configuration Protocol (DHCP) client broadcasts a DHCP discover message on the network
containing its MAC address destined for UDP port number 68 (used by BOOTP and Dynamic Host Configuration Protocol (DHCP) servers).
This first datagram is known as a DHCPDISCOVER message, which is a request to any DHCP Server that receives the datagram for
configuration information. As the name implies, the purpose of DHCPDISCOVER mesage is to discover a DHCP server.
As you can see from the screenshot copied below, the destination MAC Address of a DHCPDISCOVER message is ff:ff:ff:ff:ff:ff, which is
the Broadcast MAC Address. An Ethernet Frame with Broadcast MAC Address as the destination MAC Address is flooded to every port of
the connected LAN Switch. DHCPDISCOVER message is delivered to every connected computer in the Broadcast Domain.
Logixfirm network fundamental Page 29
logixfirm
Key values to remember for a DHCPDISCOVER message are tabulated below.
Description Value
Message Direction DHCP Client to DHCP Server
Source MAC Address Interface MAC Address of DHCP Client
Destination MAC Address ff:ff:ff:ff:ff:ff (Broadcast MAC Address)
Source IPv4 Address 0.0.0.0
Destination IPv4 Address 255.255.255.255 (Limited Broadcast)
Source Port Number UDP 68
Destination Port Number UDP 67
2. DHCPOFFER: DHCPDISCOVER Message was delivered to every connected computers in the Broadcast Domain. Every DHCP Server in
the Broadcast Domain which received the DHCPDISCOVER message responds with a DHCPOFFER message. Other computers simply drop
the DHCPDISCOVER Message.
DHCPOFFER Message contains the offered TCP/IP Configuration values like IPv4 address and subnet mask . If the DHCP client device
received multiple DHCPOFFER, the DHCP client accepts the first DHCPOFFER Message that arrives.
Logixfirm network fundamental Page 30
logixfirm
Logixfirm network fundamental Page 31
logixfirm
Key values to remember for a DHCPOFFER message are tabulated below.
Description Value
Message Direction DHCP Server to DHCP Client
Source MAC Address Interface MAC Address of DHCP Server
Destination MAC Address ff:ff:ff:ff:ff:ff (Broadcast MAC Address)
Source IPv4 Address Interface IPv4 Address of DHCP Server
Destination IPv4 Address 255.255.255.255 (Limited Broadcast)
Source Port Number UDP 67
Destination Port Number UDP 68
3. DHCPREQUEST: The Dynamic Host Configuration Protocol (DHCP) client accepts an offer and broadcasts a DHCPREQUEST
datagram. The DHCPREQUEST datagram contains the IP address of the server that issued the offer and the physical address (MAC
Address) of the DHCP client. DHCPREQUEST message requests the selected DHCP server to assign the DHCP client an IP address and
other TCP/IP configuration values. DHCPREQUEST message also notifies all other DHCP servers that their offers were not accepted by the
DHCP client.
Logixfirm network fundamental Page 32
logixfirm
Logixfirm network fundamental Page 33
logixfirm
Key values to remember for a DHCPREQUEST message are tabulated below.
Description Value
Message Direction DHCP Client to DHCP Server
Source MAC Address Interface MAC Address of DHCP Client
Destination MAC Address ff:ff:ff:ff:ff:ff (Broadcast MAC Address)
Source IPv4 Address 0.0.0.0
Destination IPv4 Address 255.255.255.255 (Limited Broadcast)
Source Port Number UDP 68
Destination Port Number UDP 67
4. DHCPACK: When the DHCP server from which the offer was selected receives the DHCPREQUEST datagram, it constructs a
DHCPACK datagram. This datagram is known as a DHCPACK (DHCP ACKNOWLEDGEMENT). The DHCPACK includes an IP address
and subnet mask for the DHCP client. It may include other TCP/IP configuration information like IP address of the default gateway, IP
addresses of DNS servers, IP addresses of WINS servers etc.
Logixfirm network fundamental Page 34
logixfirm
Logixfirm network fundamental Page 35
logixfirm
Key values to remember for a DHCPACK message are tabulated below.
Description Value
Message Direction DHCP Server to DHCP Client
Source MAC Address Interface MAC Address of DHCP Server
Destination MAC Address ff:ff:ff:ff:ff:ff (Broadcast MAC Address)
Source IPv4 Address Interface IPv4 Address of DHCP Server
Destination IPv4 Address 255.255.255.255 (Limited Broadcast)
Source Port Number UDP 67
Destination Port Number UDP 68
Once the DHCPACK message is received from the DHCP Server, DHCP Client can start using that IPv4 Addrees.
Logixfirm network fundamental Page 36
logixfirm
HTTPS:-
What is https?
HTTPS stands for Hyper Text Transfer Protocol Secure. It is a protocol for securing the
communication between two systems e.g. the browser and the web server.
The following figure illustrates the difference between communication over http and https:
Communication over https and http
As you can see in the above figure, http transfers data between the browser and the web server
in the hypertext format, whereas https transfers data in the encrypted format. Thus, https
prevents hackers from reading and modifying the data during the transfer between the browser
and the web server. Even if hackers manage to intercept the communication, they will not be
able to use it because the message is encrypted.
HTTPS established an encrypted link between the browser and the web server using the Secure
Socket Layer (SSL) or Transport Layer Security (TLS) protocols. TLS is the new version of SSL.
Secure Socket Layer (SSL)
SSL is the standard security technology for establishing an encrypted link between the two
systems. These can be browser to server, server to server or client to server. Basically, SSL
ensures that the data transfer between the two systems remains encrypted and private.
The https is essentially http over SSL. SSL establishes an encrypted link using an SSL certificate
which is also known as a digital certificate.
Logixfirm network fundamental Page 37
logixfirm
SSL
http vs https
http https
Transfers data in hypertext (structured text) format Transfers data in encrypted format
Uses port 80 by default Uses port 443 by default
Not secure Secured using SSL technology
Starts with http:// Starts with https://
Advantage of https
Secure Communication: https makes a secure connection by establishing an encrypted
link between the browser and the server or any two systems.
Data Integrity: https provides data integrity by encrypting the data and so, even if
hackers manage to trap the data, they cannot read or modify it.
Privacy and Security: https protects the privacy and security of website users by
preventing hackers to passively listen to communication between the browser and the
server.
Faster Performance: https increases the speed of data transfer compared to http by
encrypting and reducing the size of the data.
SEO: Use of https increases SEO ranking. In Google Chrome, Google shows the Not
Secure label in the browser if users' data is collected over http.
Future: https represents the future of the web by making internet safe for users and
website owners.
Introduction to Network Security:-
What is Network Security?
Network security is the process of taking preventative measures to protect the
underlying networking infrastructure from unauthorized access, misuse, malfunction,
modification, destruction or improper disclosure.
The Internet has undoubtedly become a huge part of our lives. Many people in today’s
generation rely on the Internet for many of their professional, social and personal activities. But
are you sure your network is secure?
There are many people who attempt to damage our Internet-connected computers, violate our
privacy and make it impossible to the Internet services. Given the frequency and variety of
existing attacks as well as the threat of new and more destructive future attacks, network
security has become a central topic in the field of cybersecurity. Implementing network security
measures allows computers, users and programs to perform their permitted critical functions
within a secure environment.
Now that we know what network security is, let’s take a look at two major categories of network
Logixfirm network fundamental Page 38
logixfirm
attacks.
What is network security attack?
A network attack can be defined as any method, process, or means used to maliciously attempt
to compromise network security. Network security is the process of preventing network attacks
across a given network infrastructure, but the techniques and methods used by the attacker
further distinguish whether the attack is an active cyber attack, a passive type attack, or some
combination of the two.
Let’s consider a simple network attack example to understand the difference between active and
passive attack.
Active Attacks
An active attack is a network exploit in which attacker attempts to make changes to data on the
target or data en route to the target.
bMeet Alice and Bob. Alice wants to communicate to Bob but distance is a problem. So,
Alice sends an electronic mail to Bob via a network which is not secure against attacks.
There is another person, Tom, who is on the same network as Alice and Bob. Now, as
the data flow is open to everyone on that network, Tom alters some portion of an
authorized message to produce an unauthorized effect. For example, a message
meaning “Allow BOB to read confidential file X” is modified as “Allow Smith to read
confidential file X”.
Active network attacks are often aggressive, blatant attacks that victims immediately become
aware of when they occur. Active attacks are highly malicious in nature, often locking out users,
destroying memory or files, or forcefully gaining access to a targeted system or network.
Passive Attacks
A passive attack is a network attack in which a system is monitored and sometimes scanned for
open ports and vulnerabilities, but does not affect system resources.
Let’s consider the example we saw earlier:
Logixfirm network fundamental Page 39
logixfirm
Alice sends an electronic mail to Bob via a network which is not secure against attacks. Tom,
who is on the same network as Alice and Bob, monitors the data transfer that is taking place
between Alice and Bob. Suppose, Alice sends some sensitive information like bank account
details to Bob as plain text. Tom can easily access the data and use the data for malicious
purposes.
So, the purpose of the passive attack is to gain access to the computer system or network and to
collect data without detection.
So, network security includes implementing different hardware and software techniques
necessary to guard underlying network architecture. With the proper network security in place,
you can detect emerging threats before they infiltrate your network and compromise your data.
Types of network security
There are many components to a network security system that work together to improve your
security posture. The most common network security components are discussed below.
Access Control
To keep out potential attackers, you should be able to block unauthorized users and devices from
accessing your network. Users that are permitted network access should only be able to work
with the set of resources for which they’ve been authorized.
Application Security
Application security includes the hardware, software, and processes that can be used to track
and lock down application vulnerabilities that attackers can use to infiltrate your network.
Firewalls
A firewall is a device or service that acts as a gatekeeper, deciding what enters and exits the
network. They use a set of defined rules to allow or block traffic. A firewall can be hardware,
software, or both.
Virtual Private Networks(VPN)
A virtual private network encrypts the connection from an endpoint to a network, often over the
Internet. This way it authenticates the communication between a device and a secure network,
creating a secure, encrypted “tunnel” across the open internet.
Behavioral Analytics
You should know what normal network behavior looks like so that you can spot anomalies or
network breaches as they happen. Behavioral analytics tools automatically identify activities that
deviate from the norm.
Wireless Security
Wireless networks are not as secure as wired ones. Cybercriminals are increasingly targeting
mobile devices and apps. So, you need to control which devices can access your network.
Intrusion Prevention System
These systems scan network traffic to identify and block attacks, often by correlating network
activity signatures with databases of known attack techniques.
So, these are some ways of implementing network security. Apart from these, you’ll need a
variety of software and hardware tools in your toolkit to ensure network security, those are:
Firewalls
Packet crafters
Web scanners
Packet sniffers
Intrusion detection system
Logixfirm network fundamental Page 40
logixfirm
Penetration testing software
Network security is essential for overall cybersecurity because network is a significant line of
defense against external attack. Given that, virtually all data and applications are connected to
the network, robust network security protects against data breaches.
Logixfirm network fundamental Page 41
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5823)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (898)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (349)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (823)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (403)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Electrical Discharge MachiningDocument11 pagesElectrical Discharge MachiningRizwan MrnNo ratings yet
- Wired Drill Pipe-Fosse - Martin PDFDocument62 pagesWired Drill Pipe-Fosse - Martin PDFMohamed Anis Boumaza100% (1)
- Devops Research PaperDocument115 pagesDevops Research Paperrreddym100% (1)
- Regulatory Affairs Certification (Drugs) : Candidate GuideDocument24 pagesRegulatory Affairs Certification (Drugs) : Candidate GuideAmarNo ratings yet
- Eddie The Carpet FitterDocument3 pagesEddie The Carpet Fittermaria praveenNo ratings yet
- Insulating Coatings For Electrical Steels by Composition, Relative Insulating Ability and ApplicationDocument4 pagesInsulating Coatings For Electrical Steels by Composition, Relative Insulating Ability and ApplicationjalilemadiNo ratings yet
- Mac ShiftDocument2 pagesMac ShiftanoopsreNo ratings yet
- Daily Task of Disbursing OfficerDocument2 pagesDaily Task of Disbursing OfficerEijneb OptionalNo ratings yet
- LTE Signaling FlowDocument42 pagesLTE Signaling FlowNeeraj MittalNo ratings yet
- 135G/245G LC Excavators: 13 900-25 500-kg (30,617-56,167 LB.) Operating WeightDocument9 pages135G/245G LC Excavators: 13 900-25 500-kg (30,617-56,167 LB.) Operating Weightapi-282795606No ratings yet
- CFA Level 1 Economics - Our Cheat Sheet - 300hoursDocument22 pagesCFA Level 1 Economics - Our Cheat Sheet - 300hoursMichNo ratings yet
- Atm PresentationDocument71 pagesAtm PresentationSaram Zahid0% (1)
- MICE Brochure For U.S.A. by Cox and KingsDocument19 pagesMICE Brochure For U.S.A. by Cox and KingsCox and Kings IndiaNo ratings yet
- Spouses Buado Vs Court of Appeals - DigestDocument2 pagesSpouses Buado Vs Court of Appeals - DigestJohn Leo SolinapNo ratings yet
- Analytical1 100Document27 pagesAnalytical1 100kaushik4208No ratings yet
- Catalogue of CSM Telescopic Boom Crane - OverseasDocument5 pagesCatalogue of CSM Telescopic Boom Crane - OverseasPhạm Thịnh LongNo ratings yet
- SRDC Rman CDBinfoDocument4 pagesSRDC Rman CDBinfoarun kumarNo ratings yet
- Vickers Vc-10 BoacDocument7 pagesVickers Vc-10 Boacduythinhdanh4No ratings yet
- Service Manual: Washing Machine Frontloader AWM 5085Document17 pagesService Manual: Washing Machine Frontloader AWM 5085stana_petruNo ratings yet
- Sampling Methods in Metallurgical AnalysDocument8 pagesSampling Methods in Metallurgical AnalysEarl JimenezNo ratings yet
- Posse. Analecta Vaticana. 1878.Document240 pagesPosse. Analecta Vaticana. 1878.Patrologia Latina, Graeca et OrientalisNo ratings yet
- ThingWorx Navigate Compatibility MatrixDocument2 pagesThingWorx Navigate Compatibility Matrixair_jajaNo ratings yet
- Steyn City BrochureDocument36 pagesSteyn City BrochureCorey AcevedoNo ratings yet
- Pigeonhole PrincipleDocument5 pagesPigeonhole PrincipleNoisyPoisyNo ratings yet
- All in Alfloc2Document12 pagesAll in Alfloc2Choice OrganoNo ratings yet
- Truscreen Cervical Screening SystemDocument39 pagesTruscreen Cervical Screening SystemVyacheslav PilyaevNo ratings yet
- Kill Team Campaign Cheat SheetDocument3 pagesKill Team Campaign Cheat SheetangelofmenothNo ratings yet
- Fiji Government Successfully Raises Us $250M Global BondDocument48 pagesFiji Government Successfully Raises Us $250M Global BondfijitimescanadaNo ratings yet
- Material Safety Data SheetDocument4 pagesMaterial Safety Data SheetIvani SoaresNo ratings yet
- Canadian Importers Lists - Coconut OilDocument4 pagesCanadian Importers Lists - Coconut OilIndo Coconut PremiumNo ratings yet