Professional Documents
Culture Documents
Discussion Cyber Crime
Discussion Cyber Crime
Uploaded by
Mohsin MumtazOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Discussion Cyber Crime
Discussion Cyber Crime
Uploaded by
Mohsin MumtazCopyright:
Available Formats
Discussion Cyber Crime
Public exposure today to cyber protection continues to concentrate on the avoidance of damage
done by a malicious 'outsider,' including a hacker. However, safety violations carried out in
conjunction with an informant (or at the instigation of) that lead to severe damage. Of starters,
certain network security protocols can be removed by an employee so that an outside staff
member can have access to them. Or, an intruder may transfer large amounts of sensitive
information remotely without ever being physically checked.
It was constantly emphasized that the challenge from insiders and cybersecurity is not purely
technical. Strong policy and implementation of policy are also required. Security plans must be
established, represented, controlled, and exploited. Tools are necessary to promote policy-
making and compliance.
The attacks against insiders are growing. In recent years, whether they come from unintended
insiders vulnerable to phishing attempts or from manipulative insiders who try to expose
confidential details, insiders 'assaults have dramatically increased. The foreign actors of threats
have been even more advanced in their disruptive practices targeted at insiders by leveraging
social manipulation attacks such as phishing e-, LinkedIn, and other internet data stores to collect
intelligence on company environments.
Insider Threat Report found that the surveillance, identification, and reaction of 56 percent of
information security practitioners to internal threats is just a bit or less successful. More than half
of respondents claimed they were either not adequately monitored or uncertain whether they had
any safeguards to deter an insider's attack. Three strategic priority areas below will direct the
prevention of insiders risks in your organization:
Deterrence: 62% of respondents in the survey said dissuasion was an effective tactic to deter
attacks by outsiders. Deterrence ensures that you have good access controls, tight protection of
the data, and sufficient measures to discourage and avoid attacks from insiders.
Identification: Nearly two-thirds of respondents indicated that it is important to identify what is
occurring in their community to discourage insider violence, equivalent to deterrence. The
identification of network vulnerability behaviors through network security tools effectively
requires tracking what users are doing and guarantees visibility.
Post-Breach and Investigation Forensics: Approximately half of all cybersecurity practitioners
answered that it was also necessary to be able to carry out post-breach research to react and
avoid potential insider attacks. When an incident occurs, it must be treated promptly and
efficiently. That involves looking at what occurred in the world and being able to see and
interpret what occurs in real time readily.
It is crucial to have a comprehensive security information and event management (SIEM)
solution that detects and prioritizes threats in real-time. Recall, you can't just cause damage to
your system if you have a Windows PC. Often you can reach the car park with an IoT, Wi-Fi
access control, a surveillance camera, or a card device. Both these components are now
intertwined and threaten the system, through which anyone may exploit their connection or
maliciously attempt to manipulate the world. Both from a malicious source or unintentional
abuse, insider assaults in the corporate community would certainly continue to grow. However,
the organization should take an important part in attempting to stop them. In detecting risks,
training and empowerment of users and delivering creative information security tools and
instruments to security teams.
You might also like
- 1.1.17 Lab - Explore Social Engineering Techniques - Answer KeyDocument5 pages1.1.17 Lab - Explore Social Engineering Techniques - Answer KeyPradeepkhanth BNo ratings yet
- Cyber Security AssignmentDocument9 pagesCyber Security AssignmentusamaNo ratings yet
- Trend Micro Apex One Troubleshooting Guidev1.5Document206 pagesTrend Micro Apex One Troubleshooting Guidev1.5intime supportNo ratings yet
- Lab 05Document3 pagesLab 05Mohsin MumtazNo ratings yet
- Experiment 6 - Flow Lab Worksheet - With DataDocument2 pagesExperiment 6 - Flow Lab Worksheet - With DataMohsin MumtazNo ratings yet
- SC-900 Question BankDocument42 pagesSC-900 Question BankJoseph Chen100% (1)
- Prepost-5: Making Concrete Specimens, Slump Test, and Compression Test NAME: - DATE: - / - / - Please Answer The Following QuestionDocument2 pagesPrepost-5: Making Concrete Specimens, Slump Test, and Compression Test NAME: - DATE: - / - / - Please Answer The Following QuestionMohsin MumtazNo ratings yet
- Justifying An EvaluationDocument2 pagesJustifying An EvaluationMohsin MumtazNo ratings yet
- ThreatMetrix Cybercrime Defender PlatformDocument3 pagesThreatMetrix Cybercrime Defender PlatformJoshua McAfeeNo ratings yet
- Cyber Security For Beginners: Stay Safe!: Define CybersecurityDocument4 pagesCyber Security For Beginners: Stay Safe!: Define CybersecurityRima SadekNo ratings yet
- Cybersecurity AwarenessDocument4 pagesCybersecurity Awarenessanthonylrush4No ratings yet
- Research PaperDocument3 pagesResearch PaperGitanjaliNo ratings yet
- Cyber Security IntroductionDocument4 pagesCyber Security IntroductionRENE STEPHEN VISHAL M VNo ratings yet
- Risk Management and Cyber SecurityDocument6 pagesRisk Management and Cyber SecurityPrakrit ChandaniNo ratings yet
- Understanding Cyber Security Cyber Crimes Idris IsmailaDocument68 pagesUnderstanding Cyber Security Cyber Crimes Idris Ismailaarushigupta071No ratings yet
- Cybercrime and SecurityDocument12 pagesCybercrime and Securitysankarsankar86394No ratings yet
- Cyber Security - Organizational ImplicationsDocument40 pagesCyber Security - Organizational Implications245120737162No ratings yet
- Cyber Security AssignmentDocument9 pagesCyber Security Assignmentdeepakkumar011singhNo ratings yet
- Social Engineering Based Cyber-Attacks in Kenya: Africa Nazarene University, P.O. Box 53067, Nairobi, 00200, KenyaDocument9 pagesSocial Engineering Based Cyber-Attacks in Kenya: Africa Nazarene University, P.O. Box 53067, Nairobi, 00200, KenyaDoreen GiftNo ratings yet
- What Is Cybersecurity?Document10 pagesWhat Is Cybersecurity?JOhnny M. ROdriguezNo ratings yet
- Cyber Security - OrganisationDocument21 pagesCyber Security - OrganisationShambhu Kumar singhNo ratings yet
- Impact of Cybersecurity On Our TechnologyDocument2 pagesImpact of Cybersecurity On Our TechnologyPatryk SadowskiNo ratings yet
- Cyber Security Program: Student's Name Institution Affiliation Course Name Instructor's Name DateDocument17 pagesCyber Security Program: Student's Name Institution Affiliation Course Name Instructor's Name DateEPIC BRIEFSNo ratings yet
- Ethical Hacking by Nancy IdiongDocument21 pagesEthical Hacking by Nancy IdiongNancy IdiongNo ratings yet
- Cybersecurity:risks, Vulnerabilities and Countermeasures To Prevent Social Engineering AttacksDocument8 pagesCybersecurity:risks, Vulnerabilities and Countermeasures To Prevent Social Engineering AttacksAnish AmatyaNo ratings yet
- Cyber Security AwarenessDocument24 pagesCyber Security AwarenessPooja MohanNo ratings yet
- Shankar Adhikari CIS8018Document10 pagesShankar Adhikari CIS8018Shan AdhikariNo ratings yet
- Information SecurityDocument20 pagesInformation SecurityDewi SartikaNo ratings yet
- Risk Mitigation 5Document3 pagesRisk Mitigation 5Sukh DhaliwalNo ratings yet
- Security ThreatsDocument10 pagesSecurity ThreatsTharun BurraNo ratings yet
- CH 1 CsDocument31 pagesCH 1 CsDeeksha GuptaNo ratings yet
- COVID-19: Impact On The Cyber Security Threat Landscape COVID-19: Impact On The Cyber Security Threat LandscapeDocument5 pagesCOVID-19: Impact On The Cyber Security Threat Landscape COVID-19: Impact On The Cyber Security Threat LandscapeRAJ NIDHINo ratings yet
- CsssDocument8 pagesCsssST DOORSNo ratings yet
- What Is CybersecurityDocument8 pagesWhat Is CybersecurityMohamed TaufiqhNo ratings yet
- Introduction To Cyber Security IIIDocument7 pagesIntroduction To Cyber Security IIINandini DaggupatiNo ratings yet
- Essay About Social EnginneringDocument5 pagesEssay About Social EnginneringNadia Castaño NoreñaNo ratings yet
- Sample ResearchDocument10 pagesSample ResearchAlbert Malabad Jr.No ratings yet
- Assignment 1 CS - MergedDocument4 pagesAssignment 1 CS - MergedADEEL SARWARNo ratings yet
- ScriptDocument2 pagesScriptmahmoudsaedfathyNo ratings yet
- Cyber Security TrendsDocument7 pagesCyber Security TrendsNikitaNo ratings yet
- Ensuring Robust Security and Privacy in Today's Digital LandscapeDocument11 pagesEnsuring Robust Security and Privacy in Today's Digital LandscapeSundari KaliNo ratings yet
- Cyber Crime Research ProposalDocument7 pagesCyber Crime Research ProposalMohammed AlmalkiNo ratings yet
- CybersecurityDocument16 pagesCybersecuritygopika.26csaNo ratings yet
- CYBER SECURITY Ultimate Beginners Guide To Learn The Basics and Effective Methods of CyberDocument106 pagesCYBER SECURITY Ultimate Beginners Guide To Learn The Basics and Effective Methods of Cybervincent laneNo ratings yet
- 14 Cyber Security Awareness 1Document9 pages14 Cyber Security Awareness 1Michelle EsternonNo ratings yet
- Computer SecurityDocument17 pagesComputer Securitybentitesfa881No ratings yet
- Cyber SecurityDocument16 pagesCyber Securitygopika.26csaNo ratings yet
- Insider Threat Detection in Organization Using Machine LearningDocument11 pagesInsider Threat Detection in Organization Using Machine LearningVarsha SureshNo ratings yet
- CISSE - Organization Security Controls For Effective Cyber Defense - ProceedingsDocument25 pagesCISSE - Organization Security Controls For Effective Cyber Defense - Proceedingsmichellee12No ratings yet
- Security Training: Business Continuity and Disaster RecoveryDocument3 pagesSecurity Training: Business Continuity and Disaster RecoveryAnonymous XmvR2K6No ratings yet
- Anti Techniques HarshaDocument37 pagesAnti Techniques HarshaHarsha MajetiNo ratings yet
- CYBER SECURITY HANDBOOK Part-1: Hacking the Hackers: Unraveling the World of CybersecurityFrom EverandCYBER SECURITY HANDBOOK Part-1: Hacking the Hackers: Unraveling the World of CybersecurityNo ratings yet
- DocxDocument7 pagesDocxBree ElaineNo ratings yet
- Unit-1 CyberSecurityDocument22 pagesUnit-1 CyberSecurityAditya PandeyNo ratings yet
- Cyber Situational AwarenessDocument10 pagesCyber Situational AwarenessBob KoblovskyNo ratings yet
- CybersecurityDocument6 pagesCybersecurityPradeebha RNo ratings yet
- Detecting Insider Threat Via A Cyber Security Culture FrameworkDocument12 pagesDetecting Insider Threat Via A Cyber Security Culture FrameworkBHARATH KUMARNo ratings yet
- AI: The Future of Proactive CybersecurityDocument17 pagesAI: The Future of Proactive CybersecurityEl Sayed SanadNo ratings yet
- University Assignment Report CT7098Document16 pagesUniversity Assignment Report CT7098Shakeel ShahidNo ratings yet
- CyberDocument1 pageCyberTGC NINJANo ratings yet
- Chuvakin-Log Analysis vs. Insider AttacksDocument4 pagesChuvakin-Log Analysis vs. Insider AttacksAnton ChuvakinNo ratings yet
- Guardians of the Virtual Realm: From Protection to Penetration: Navigating Cybersecurity and Ethical Hacking TechniquesFrom EverandGuardians of the Virtual Realm: From Protection to Penetration: Navigating Cybersecurity and Ethical Hacking TechniquesNo ratings yet
- University of Caloocan City: Information Security & ManagementDocument11 pagesUniversity of Caloocan City: Information Security & ManagementMike AntolinoNo ratings yet
- LAB Manual Course Title: Gas DynamicsDocument20 pagesLAB Manual Course Title: Gas DynamicsMohsin MumtazNo ratings yet
- Brass 01Document155 pagesBrass 01Mohsin MumtazNo ratings yet
- Lab 5 Procedure: Equipment & MaterialsDocument2 pagesLab 5 Procedure: Equipment & MaterialsMohsin MumtazNo ratings yet
- What Device Is Used in A Tension Test To Measure The Elongation of The Specimen?Document2 pagesWhat Device Is Used in A Tension Test To Measure The Elongation of The Specimen?Mohsin MumtazNo ratings yet
- 8626-1 EM by Joher Videos PDFDocument26 pages8626-1 EM by Joher Videos PDFMohsin MumtazNo ratings yet
- Dataset BDocument1 pageDataset BMohsin MumtazNo ratings yet
- Dataset BDocument1 pageDataset BMohsin MumtazNo ratings yet
- The Great Stupa ResponsesDocument1 pageThe Great Stupa ResponsesMohsin MumtazNo ratings yet
- Terra Cotta Warriors DiscussionDocument1 pageTerra Cotta Warriors DiscussionMohsin MumtazNo ratings yet
- Responses 123Document1 pageResponses 123Mohsin MumtazNo ratings yet
- Reader Exercises - Chapter 1Document5 pagesReader Exercises - Chapter 1Mohsin MumtazNo ratings yet
- Remembering An EventDocument2 pagesRemembering An EventMohsin MumtazNo ratings yet
- Discussion Environmental Movements Enacted PositiveDocument3 pagesDiscussion Environmental Movements Enacted PositiveMohsin MumtazNo ratings yet
- Reader Exercise 4Document2 pagesReader Exercise 4Mohsin MumtazNo ratings yet
- Workplace Stress and Health of EmployeesDocument2 pagesWorkplace Stress and Health of EmployeesMohsin MumtazNo ratings yet
- Back2base FlyerDocument2 pagesBack2base FlyerMadalina-Coralia RosuNo ratings yet
- The Internet Is The Global System of Interconnected MainframeDocument1 pageThe Internet Is The Global System of Interconnected MainframeAngela MurrayNo ratings yet
- Understanding PhishingDocument16 pagesUnderstanding Phishingshravani kultheNo ratings yet
- A Guide To Picture Quality MeasurementsDocument20 pagesA Guide To Picture Quality Measurementsacastillos75No ratings yet
- (Cosc3092) : Object Oriented Software EngineeringDocument10 pages(Cosc3092) : Object Oriented Software EngineeringBereket AtnafuNo ratings yet
- Assignment No 4Document18 pagesAssignment No 4Jusil T. GaiteNo ratings yet
- (Coding Big Data) - Week 01 - Syllabus - Introduction To Coding - Big DataDocument82 pages(Coding Big Data) - Week 01 - Syllabus - Introduction To Coding - Big DataYudistira CahayaNo ratings yet
- IT Security Architecture & Leadership, 24 - 27 November 2013 Dubai UAEDocument4 pagesIT Security Architecture & Leadership, 24 - 27 November 2013 Dubai UAE360 BSINo ratings yet
- Theory of Computation Notes 3 - TutorialsDuniyaDocument150 pagesTheory of Computation Notes 3 - TutorialsDuniyaDewansh YadavNo ratings yet
- SpeeeeeeeeeedDocument28 pagesSpeeeeeeeeeedhasan alsarrafNo ratings yet
- Computer Viruses: By: Angelica Jurczak Anna Rog David BrackettDocument17 pagesComputer Viruses: By: Angelica Jurczak Anna Rog David Brackettcristi123321No ratings yet
- Mark ListDocument3 pagesMark ListpadmapraveenkumarNo ratings yet
- Computer Network Rcs 601Document2 pagesComputer Network Rcs 601Soyab MalikNo ratings yet
- USB Cassette Converter ManualDocument13 pagesUSB Cassette Converter ManualJose GodoyNo ratings yet
- AX5000-512 DatasheetDocument5 pagesAX5000-512 Datasheetsolution regional5No ratings yet
- VmWare Interview Questions With Answers-1Document27 pagesVmWare Interview Questions With Answers-1sagarika Mane100% (1)
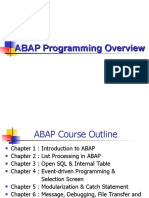
- ABAP Programming OverviewDocument393 pagesABAP Programming OverviewDuy SơnNo ratings yet
- Java Vs JavascriptDocument6 pagesJava Vs JavascriptGarry pNo ratings yet
- Create Your First PipelineDocument5 pagesCreate Your First PipelineKaushikDRokstarNo ratings yet
- Engineering Division: FF/HART ConfigurationDocument34 pagesEngineering Division: FF/HART ConfigurationJorge Pérez FrisanchoNo ratings yet
- Sample Paper 5: Computer ScienceDocument8 pagesSample Paper 5: Computer ScienceScary PeepsNo ratings yet
- Window 10 Hardening Latest Search On Control PanelDocument60 pagesWindow 10 Hardening Latest Search On Control PanelAli Hussnain100% (1)
- Sophos Managed Detection and Response DsDocument4 pagesSophos Managed Detection and Response DspopatrajkumarNo ratings yet
- PuttyDocument2 pagesPuttyenockkaysNo ratings yet
- SC-ETC-001 5.11 - Module 4 - Security Center As A ServiceDocument33 pagesSC-ETC-001 5.11 - Module 4 - Security Center As A ServiceFernando Quintero CasadiegosNo ratings yet
- Reduce Your Blast Radius by Using Multiple AWS Accounts Per Region and ServiceDocument25 pagesReduce Your Blast Radius by Using Multiple AWS Accounts Per Region and ServiceTonyNo ratings yet
- Sistem Operasi, Perangkat Lunak Dan Dasar Web ProgrammingDocument55 pagesSistem Operasi, Perangkat Lunak Dan Dasar Web ProgrammingSamuel FerdinandNo ratings yet