Professional Documents
Culture Documents
143-151 MobPhoneAutenticationToken tcm26-36823
143-151 MobPhoneAutenticationToken tcm26-36823
Uploaded by
mleg80Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
143-151 MobPhoneAutenticationToken tcm26-36823
143-151 MobPhoneAutenticationToken tcm26-36823
Uploaded by
mleg80Copyright:
Available Formats
The Mobile Phone as Authentication Token
IVAR JØRSTAD, DO VAN THANH
This paper provides a study of the various ways the mobile phone can be used as an authentication
token towards service providers on the Internet. It starts by discussing the need for a strong
authentication scheme and the motivation for using the mobile phone to improve on several aspects
of the current authentication processes. Then, the general architecture for authentication with mobile
phones is presented. Several different authentication solutions using the mobile phone as authentica-
tion token are then described, where the solutions vary in complexity, strength and user-friendliness.
Ivar Jørstad is The paper ends with an evaluation of the different solutions, and a discussion of the most probable
CEO of
attacks. A classification of the solutions is also provided, according to defined criteria.
Ubisafe AS
1 Introduction • Its widespread deployment (over 100 % market
A lot of value-added services on the Internet today penetration in Norway);
require authentication, i.e. the proper verification of
the user’s identity, before the user gets access to the • It usually follows the user at all times (you seldom
service itself. The most common authentication leave home without).
Do Van Thanh is scheme which is employed is the use of username and
Senior Research password. However, the username/password scheme Thus, by using the mobile phone as an authentication
Scientist in has several weaknesses which make it unsuitable for solution, the major weaknesses of existing solutions
Telenor R&I very many (most) services. Most importantly they are reduced:
reduce security and make service access inconvenient
for the users due to: • More convenient for the user who now only
requires one device;
• Username/password can be subject to phishing;
• Usually higher level of security (depends on the
• Too many username/password pairs make it impos- specific authentication scheme implemented);
sible to remember all;
• Reduction in deployment and maintenance costs
• It is common to reuse the same username/password for service providers (reuses existing infrastructure,
for different services; i.e. the mobile phone and the mobile network).
• It is common to write down username/password In addition, some such solutions can provide mobile
where others can easily find them. network operators with new sources of revenue since
they control much of the required infrastructure.
Due to these weaknesses of the username/password
scheme, other solutions must be used. For services This paper starts with a discussion of authentication
with particularly high security requirements, One- strength and discusses the concept of multi-channel
Time-Passwords (OTP) [1] or Smart Card solutions authentication as a mechanism for stronger authenti-
have been taken into use, e.g. for Internet-banking cation. Then some different authentication schemes
services or corporate service access. These more using the mobile phone as an authentication token
secure solutions usually increase the cost of the will be described. An evaluation of the different
security solutions both in the deployment phase schemes will then be performed according to specific
(provide all users with OTP-calculators or Smart criteria.
Cards w/readers) but also in the maintenance phase
(defective OTP-calculators, lost Smart Cards, invali-
dation of users etc.). 2 Strong Authentication
As a consequence of the weaknesses of existing 2.1 Two Factor Authentication
authentication solutions, new solutions should be Two factor authentication means that the authentica-
investigated. Using the mobile phone as an authenti- tion process consists of two stages, where each stage
cation solution towards Internet-based services is uses a different credential. For example, the mobile
particularly compelling due to: phone authentication process is (usually) two factor
ISSN 0085-7130©Telenor ASA 2007
Telektronikk 3/4.2007 143
because it relies on 1) the PIN-code to activate the with a working SIM card. If the computer and mobile
SIM-card, and 2) the possession of the SIM-card phone are equipped with Bluetooth, higher usability
itself with the appropriate keys and algorithms. Lack- can be obtained. Through the Internet browser on the
ing one of these will usually mean that it is impossi- computer the user can access web services provided
ble to authenticate. However, it is possible to reduce by service providers. The service provider (SP) is
the SIM authentication to one factor by disabling the connected to an Authentication Server (AS) that will
PIN-code verification. handle the authentication on behalf of the SP. The AS
is connected to the GSM network which enables it to
2.2 Multi-channel Authentication communicate with the user’s mobile phone and the
Multi-channel authentication is the process of utilis- operator’s Authentication Center (AuC). The AS is
ing more than one communication channel for the composed of two parts, an authenticator and an AAA
secure establishment of the user’s identity. It is cru- server. The authenticator communicates with the
cial to understand the properties of the different chan- client and relays messages to the AAA server which
nels in order to implement authentication solutions handles the authentication.
with adequate properties. When using the mobile
phone for authentication, it is today possible to use When designing an authentication scheme which uses
the connection between the mobile phone and a com- two separate devices that communicate over two dif-
puter, which again communicates with an authentica- ferent networks it is very important to ensure that it
tion server on the Internet, as one channel, e.g. to ini- is the same user that controls both devices. This is
tiate the authentication process. The response to the done by ensuring that there is a “closed loop” going
authentication request can be sent on another channel through all the components involved in the authenti-
back to the user, e.g. using an SMS message. The cation as illustrated in Figure 1. The loop starts in the
user can then again either complete the authentication device requesting the service, the user’s computer,
process by responding with an SMS or by sending a goes through the network with SP and AS and then
message through the initial channel. via the mobile phone and back to the initial device,
either by user interaction or Bluetooth.
3 The Different Mobile Phone This closed loop can be realized in several ways as
Authentication Schemes described in the solutions presented below.
To be able to authenticate users through a mobile
phone, certain main components must be in place. 3.2 SMS Authentication
Figure 1 shows the main components and the basic with Session-ID Check
architecture needed for the solutions described later This solution exploits that a user with a valid mobile
to work. subscription is already authenticated through the
GSM system. Session IDs are used to ensure that it
The user must have access to a computer connected is the same user that controls both the computer and
to the Internet and be in possession of a mobile phone the mobile phone.
When the user accesses a service provider a unique
session ID is created and sent both to the user’s com-
puter and to the mobile phone. The session ID is sent
over the Internet to the computer and shown in the
GSM network
web browser and sent to the phone by SMS. Then the
M user can confirm that the session IDs match and send
GS
a confirmation by SMS to the service provider. When
Authentication server receiving the confirmation from the user the AS
Mobile phone knows that the user is in possession of the phone and
Radius
TP the authentication is successful.
HT
Bluetooth/ The comparison of the session ID can be made by the
user interaction user or automatically by software if the phone is con-
nected to the computer by Bluetooth.
HTTP
User User computer Service provider 3.2.1 User Verification of Session ID
The user accesses the service provider through the
Internet browser and chooses to be authenticated by
Figure 1 A general architecture of mobile authentication his mobile phone. The user identifies himself with his
ISSN 0085-7130©Telenor ASA 2007
144 Telektronikk 3/4.2007
Mobile phone Computer Service provider Authentication server
Request/access
Request/identity
Response/identity
Request/authentication (identity)
Session ID
Session ID
Confirmation
Response/authentication (identity)
Access granted
Figure 2 Session ID check
mobile phone number and the request is redirected to [3]. When the AS receives the confirmation it notifies
the authentication server. The authentication server the authenticator that the user is authenticated and
then creates a unique session ID and sends this to the redirects the browser back to the SP. The message
user by SMS and over the Internet to the computer. exchange is shown in Figure 3.
The user checks that the session ID in the SMS is the
same as the one shown in the browser. If this is the 3.3 One-Time-Password from PC to SMS
case the user replies by sending an SMS back to the The next two solutions make use of the OTP principle
AS confirming that the session IDs match. When [4] for authentication. The solutions describe differ-
receiving the confirmation the authentication server ent ways to securely use the mobile phone as an OTP
redirects the browser back to the service provider and token.
the user is given access to the service. The message
exchange is shown in Figure 2. The authentication procedure for the OTP from PC
to SMS solution is shown in Figure 4. When the
3.2.2 Automatic Check of Session ID client wants to access the SP the client’s identity is
To make it even easier for the user the session ID can requested. The client responds by typing his user-
be checked automatically. This can be done by pair- name in the browser. The message is relayed to the
ing the mobile phone and the computer by Bluetooth. AS which handles the authentication. Upon receiving
When the computer receives the session ID from the
AS a Java applet running in the browser contacts the
SIM card using the Bluetooth SAP. SAP requires that Java applet (PC) SIM
a 16 digit pass-phrase is used during the pairing pro-
Session ID (from AS) Session ID (SMS from AS)
cess. The applet checks the SIM for an SMS with an
Setup SAP connection
appropriate session ID. For this to function it must be
ensured that the SMS received from the AS is stored Read SMS
on the SIM. This can be done by setting the TP-PID
in the SIM header to require SIM data download [2]. Send SMS (confirmation)
This forces the mobile phone to store the SMS on the
SIM. If a matching session ID is found the applet cre- Confirmation (SMS to AS)
ates a confirmation message that is sent to the AS by Terminate connection
SMS. This is done with a proactive SIM which can
issue commands to the mobile phone as described in Figure 3 Automatic check of session ID
ISSN 0085-7130©Telenor ASA 2007
Telektronikk 3/4.2007 145
Client Authenticator Authentication server AuC
Access
Request/identity
Response/identity
Challenge
Challenge
OTP
OTP
Authentication successful
Access granted
Figure 4 OTP from PC to phone
the client’s identity the AS generates a challenge, typ- on the phone which can communicate with the SIM
ically a random number based on the client’s profile, card through SATSA-APDU [5] as shown in Figure
and a corresponding OTP. Then the AS sends the 5. The user is prompted for the challenge and enters
challenge to the client. The client enters the challenge it on the phone. The MIDlet transfers the challenge
on the mobile phone. The OTP applet on the SIM to the OTP applet which responds with an OTP. The
card generates an OTP from the challenge. The OTP user creates an SMS containing the OTP and sends it
is then sent to the AS by SMS. The AS compares the to the AS.
calculated and received OTP and notifies the authen-
ticator that the client is authenticated. The browser is 3.3.2 Automatic Variant
redirected back to the SP and the user is successfully If the mobile phone and computer are connected
logged in. through Bluetooth the challenge can be sent to the
phone automatically. To realize this, a Java applet
3.3.1 Manual Variant will run in the browser and communicates with the
When the client receives the challenge from the AS it Java MIDlet on the mobile phone. The MIDlet on the
is displayed in the browser. The user starts a MIDlet phone also has to be expanded so that it can create
and send an SMS with the OTP to the AS. This can
be done by the Wireless Message API[6].
MIDIet Java ME SIM
When the user wants to log in using the automatic
Connect solution the first thing to be done is to pair the mobile
Manage channel phone and the computer. If this is the first time these
two devices are paired a pass-phrase must be entered
on both devices. When the pairing is done the user
Select applet can choose to log in with the automatic solution and
Connection confirmed after providing an identity the rest of the procedure
will go automatically.
OTP applet
Challenge After providing the identity a challenge is sent to
the user. The Java applet retrieves the challenge and
Challenge
contacts the MIDlet on the mobile phone. When the
Bluetooth connection is set up the challenge is sent
to the MIDlet. The MIDlet contacts the SIM card as
Response (OTP)
Response (OTP) shown in Figure 5. When the OTP is created the
MIDlet creates an SMS containing the OTP and
sends it by the GSM network to the AS.
Figure 5 OTP Applet
ISSN 0085-7130©Telenor ASA 2007
146 Telektronikk 3/4.2007
3.4 One-Time-Password from SMS to PC Client Authenticator Authentication server
This solution builds on the same principle as the
session ID check, that a user with a working phone is Access
already authenticated through the GSM network. The
Request/identity
difference is that the check is done by the server and
therefore relieves the user from this burden. Response/identity
OTP (by SMS)
The user starts the authentication procedure by enter-
ing his username. The session is redirected to the AS OTP (in browser)
which creates an OTP based on the user’s identity by
a cryptographic hash function. The OTP is then sent Authentication successful
to the user by SMS. When receiving the SMS the Access granted
user types the OTP in the browser. The AS verifies
that the OTP is correct and redirects the browser back
to the service provider and the user is logged in. Fig- Figure 6 OTP SMS to PC
ure 6 shows the message exchange of this solution.
3.4.1 Manual Variant
When the user receives the SMS with the OTP from In order to be able to run the EAP-SIM protocol
the AS he types the OTP in the browser and presses between the AS and the client the AS needs to
the log-in button. If the OTP is correct the user is communicate with the SIM card. To avoid having to
successfully logged in. install specific software on the client’s computer this
communication is handled by a Java applet [8].
3.4.2 Automatic Variant
If the mobile phone and the computer are paired The applet will play the role as supplicant and run in
through Bluetooth the OTP can be transferred auto- the client’s browser and relay messages between the
matically from the phone to the computer and then authenticator and the SIM card.
forwarded to the AS through the browser. This can be
handled by a Java applet on the computer communi- Its main functions will be to
cating with the SIM card through SAP. When the AS
has sent the OTP by SMS it notifies the client that 1 Receive EAP request from the EAP authenticator;
this has been done. When receiving this notification 2 Send the content of the these packets to the SIM
the Java application contacts the mobile phone and card;
retrieves the SMS from the AS. The applet retrieves 3 Build EAP response packets from the SIM
the OTP from the SMS and sends it to the AS responses;
through the Internet browser. As in the session ID 4 Send the EAP response packets to the EAP authen-
solution the TP-PID field in the SMS header must ticator.
be set to “SIM DATA DOWNLOAD” so that the
SMS is guaranteed to be stored on the SIM card. The applet communicates with the SIM card using
Bluetooth SIM Access Protocol (SAP) [9]. The EAP
3.5 SIM Strong Authentication via Mobile authenticator is implemented as a Java Servlet run-
Phones ning inside the AS. The authenticator first request an
This solution makes use of the EAP-SIM protocol [7] EAP identity from the supplicant. The supplicant
to authenticate the user. EAP-SIM is run between the translates this request and relays it to the SIM card.
SIM and the AS. The protocol can be run through the The SIM card responds with the international mobile
computer over Bluetooth and Internet or over the subscriber identity (IMSI). The authenticator sends
GSM network by SMS. the identity received to the AAA server which con-
tacts the user’s AuC for GSM triplets. The challenges
When the user accesses an SP the browser is redi- contained in the triplets are concatenated and sent
rected to an AS. If the user chooses to run the SIM back to the supplicant. The supplicant relays the
strong authentication the rest of the procedure is hid- challenges to the SIM card that
den for the user as the SIM card and the AS authenti-
cate each other. If the authentication is successful the 1 Authenticates the server by verifying that the
browser is redirected back to the SP and the user is MAC1 received is in order;
logged in. 2 Runs the GSM algorithms to calculate a MAC2
that is sent back to the AS.
ISSN 0085-7130©Telenor ASA 2007
Telektronikk 3/4.2007 147
SIM Supplicant Authenticator Authentication server
EAP-request identity
Get IMSI
IMSI
EAP-response - identity (based on IMSI)
EAP-request/SIM/start
EAP-request/SIM/start (with Nonce)
EAP-request/SIM/challenge (with n*RAND, MAC1)
Run GSM algorithm (RAND, MAC)
Message 1
EAP-response/SIM/challenge (with MAC2)
EAP-success
Figure 7 EAP SIM authentication
The supplicant receives the response from the SIM performed between the SIM card and the AAA server
and sends them to the authenticator in EAP format. by exchanging SMS messages. If the authentication
The authenticator relays the response to the AAA is successful, the SP is notified that the user with the
server that verifies that the MAC2 is correct. If corresponding session ID is authenticated, and the
MAC2 is correct the authentication is successful and user is provided access to the protected resources.
the user is logged in. The EAP-SIM authentication is
shown in Figure 7. To enable the phone to perform EAP authentication
over SMS an applet on the SIM card must be
3.5.1 SMS Variant installed. The applet generates the session ID to be
This solution is a variant that does not require a Blue- entered in the browser. Thereafter, the SIM applet
tooth enabled mobile phone. Instead the EAP-SIM performs authentication towards GSM using SMS
protocol will run over SMS. messages which encapsulate the EAP-SIM protocol.
This solution is similar to the previous, however it
The user chooses to log in using the EAP over SMS does not require the Bluetooth connection between
solution. When this is done, a web page is presented the mobile phone and the user’s PC since it instead
asking for a session ID. An authentication applet on uses SMS to close the authentication loop. SAP is
the SIM card is started by the AS through SAT and used to control the SIM card and mobile phone dur-
the user is asked to confirm that he wants to start the ing authentication.
authentication. A session ID is displayed on the
mobile phone screen and the user enters the session The implementation can be optimized so that only
ID in the browser. If the session ID is correct the user two mobile-originated short messages and one server-
must accept to start authentication by pressing an OK originated short message are required for full EAP-
button on the phone. Then EAP-SIM authentication is SIM authentication.
ISSN 0085-7130©Telenor ASA 2007
148 Telektronikk 3/4.2007
4 Evaluation
6. GSM network
4.1 Criteria
This section provides an evaluation of the different
authentication schemes using the mobile phone as AS
authentication token. The evaluation is performed 1. Mobile phone
4. Internet 5. SP - AS 5. SP-AS
according to the following criteria:
connection structure structure
• Strength & vulnerability 2.
• Cost Bluetooth
• User friendliness
3. Computer SP
As Figure 8 illustrates, the different authentication
solutions can be subject to attacks in several areas,
depending on the specific scheme: Figure 8 Possible points of attack in mobile
authentication solutions
1 On the mobile phone;
2 Across the Bluetooth connection;
3 On the computer;
4 Across the Internet connection; 4.2.2 Automatic
5 Across the connection between service provider This solution, being rather similar to the previous
and authentication server; one, eliminates the human factor in the verification of
6 On and between GSM network components and the received session-id in the SMS. Instead, it intro-
connections. duces another point of possible attack; the Bluetooth
connection (2) between the mobile phone and the
The following sections will discuss some of the most user’s computer. The equality of the session-id on the
probable attacks on the different mobile authentica- mobile phone and the user’s computer is performed
tion solutions. over this Bluetooth connection. Consider a hijacker
which is able to intercept communication over this
4.2 Session-ID check with SMS connection (man-in-the-middle attack), thus being
able to receive requests over it as well as sending
4.2.1 Manual responses in return. A hijacker could then, similarly
With regard to Figure 8, this solution is realistically to in 4.2.1, establish a session towards the service in
most susceptible to an attack in the response phase, question with the user’s identity (cellular phone
i.e. when the user sends an acknowledgement back to number). An SMS will then be received by the valid
the AS through the GSM network. Consider a possible user’s mobile phone, with the appropriate session-id.
hijacker whose goal it is to steal a session from a valid However, if the hijacker is able to redirect his Java
user. If the hijacker establishes a session towards a Applet so that it contacts the valid user’s mobile
service at the same time as the valid user, using the phone, instead of his own, to access the valid session-
valid user’s identity (i.e. cellular phone number), two id, he can in theory hijack a user session, and this
messages with session-ids will be sent to the valid could happen even when the valid user is not actually
user. Being unaware of the hijack attempt, the valid in the process of establishing a session towards the
user might respond with acceptance to the invalid service at the same time. The Java Applet must also
user’s request, instead of to the valid user’s request. send the confirmation SMS through the valid user’s
mobile phone, since the AS will check that the confir-
However, such an attempt requires a hijacker to be mation comes from the appropriate cellular phone
familiar with the valid user’s identity as well as being number.
well synchronised with the valid user’s activitity (e.g.
through visual observation). The likeliness of such The Bluetooth connection between the user computer
a successful hijack attempt is therefore in practice and the mobile phone is protected by encryption
extremely low, since it also assumes that the user using a 16 digit key (as required by SAP) which is
does not properly study each of the incoming SMS used in the pairing process, so the feasibility to estab-
messages with session-ids. Another problem with the lish such an attack is very limited.
solution is that it is technically possible to spoof SMS
sender addresses, i.e. send SMS messages with the
valid user’s number. Additional security mechanisms
should be applied to prevent this.
ISSN 0085-7130©Telenor ASA 2007
Telektronikk 3/4.2007 149
4.3 OTP PC-to-SMS solution requires a wireless Bluetooth connection
between the phone and the user’s computer, which in
4.3.1 Manual theory could be compromised, but as previously dis-
In this solution, it is the OTP which is the most cru- cussed, this is in reality unfeasible. The biggest secu-
cial element. If an eavesdropper can get hold of the rity risk with the solution is loss of terminal, but the
OTP, he could in theory hijack a user session. How- SIM is also protected by a PIN-code, which renders
ever, since a user’s session (and OTP) is associated the device useless when unknown. The PIN-code
with a specific challenge, it is not enough to get hold must be used to activate the SIM when the phone is
of the OTP, it is also necessary to hijack the HTTP- switched on, but in addition, the solution can require
session which has previously been created by the the user to also enter the PIN-code each time an
valid user. The solution could also in addition to the authentication is to be performed, further strengthen-
OTP include a check of the sender address of the ing the solution in case of loss of mobile phone.
SMS carrying the OTP, to further improve the
strength and reduce the possibility of malicious 4.5.2 SIM in USB-dongle
attacks. This solution is slightly less user friendly than the
previous one due to the need for an additional device,
4.3.2 Automatic and in theory a bit more secure since it requires a
The automatic variant of the OTP-solution mostly physical connection between the user’s computer and
improves the user-friendliness. However, it also the SIM-card. This solution also requires a PIN-code
reduces the possibility of attacks due to a strong for activation of the SIM-card prior to authentication,
association between the user’s phone and computer which prevents use by arbitrary users if the dongle
through an authenticated and encrypted Bluetooth with SIM is lost.
connection. Attacks towards this solution could be
launched on the Bluetooth-connection, but this is 4.5.3 SIM Strong Authentication with SMS
not trivial. This solution combines the strength of SIM strong
authentication with the session-id check, and the
4.4 OTP SMS-to-PC result is a relatively strong authentication solution.
However, it requires the installation of a special
4.4.1 Manual applet on the user’s SIM-card. The solution also
Since the OTP in this solution is sent to the user, requires a check of session-id, and could also possi-
attacks must be directed towards obtaining the OTP. bly include the PIN-verification procedure to provide
However, the OTP is typically associated with an further protection in case of loss of mobile phone.
HTTP-session created by the valid user. Therefore,
both the OTP and the HTTP-session must be attacked All the SIM strong authentication solutions above are
in order for a malicious user to get access to the valid based on well-proven, standardised technologies and
user’s services. protocols where the strength and weaknesses have
been scrutinized by computer and communication
4.4.2 Automatic network security experts.
This solution simplifies the work of the user, and pre-
vents eavesdroppers from visually getting hold of the 4.6 Comparison of Authentication
OTP which is received by the valid user’s mobile Solutions
phone. The OTP is never actually exposed to the Table 1 illustrates some of the security properties of
user, but handled only by the system components. the major categories of authentication solutions dis-
cussed in this paper. It shows what type of attacks the
The solutions are rated with relative weights from different solutions can be susceptible to.
1 to 6, with 6 as the best.
Figure 9 shows a comparison of the different authenti-
4.5 SIM Strong Authentication cation solutions with respect to four parameters; secu-
The SIM strong authentication solution can be used rity, cost, infrastructure and user-friendliness. The
with the SIM-card in the mobile phone, but also with comparison is informal and only meant to provide
the SIM-card in a USB-dongle or similar. The two some insight into the properties of the various solu-
different solutions differ in some of their properties. tions in relation to each other. As with all such solu-
tions, the actual implementations might have other
4.5.1 SIM in Mobile Phone properties than illustrated here. The scores are relative
From a user’s perspective, this is the most ideal solu- from 1 to 10, with 10 as the best rating. High rating in
tion, since no additional device is required to perform e.g. cost and infrastructure does not mean high cost,
authentication. Regarding the security properties, this nor a lot of infrastructure, but rather the opposite.
ISSN 0085-7130©Telenor ASA 2007
150 Telektronikk 3/4.2007
5 Conclusion Security requirement Session ID OTP solutions SIM strong
solutions
This paper has suggested several ways to employ the
mobile phone as an authentication token, with the Online guessing n/a √ n/a
purpose of addressing shortcomings of existing
Replay √ √ √
authentication solutions on the Internet today. The
solutions show that there are many different possibili- Eavesdropping √ √
ties, and that the authentication process can take one Shared secrets not revealed n/a √ √
single path back and forth, or exploit several channels Multi-factor authentication √ √ √
(multi-channel authentication) to complete the
Man-in-the-middle √
authentication. The paper also informally illustrates
the security properties of the solutions and provides Session hijacking √
a comparison between the solutions with respect to Authenticated data transfer √
four important criteria.
Table 1 Security properties
References
1 OATH – An industry roadmap for Open Strong 2006 [online] – URL: http://www.gemplus.com
Authentication. October 22, 2007 [online] – URL: /pss/telecom/download/jsr177_whitepaper
http://www.openauthentication.org/ _april05.pdf
2 3GPP. Technical realization of the Short Message 6 Ortiz, C E. The Wireless Messaging API, 2002.
Service. 2003. (3GPP TS 23.040) March 2007 [online] – URL:
http://developers.sun.com/techtopics/mobility
3 ETSI. GSM 11.14 Specification of the SIM Appli- /midp/articles/wma/
cation Toolkit for the Subscriber Module –
Mobile Equipment (SIM – ME) Interface. Sophia 7 Aboba, B et al. Extensible Authentication Proto-
Antipolis, 1996. col. IETF, 2004.
4 Haller, N, Metz, C, Nesser, P, Straw, M. A One- 8 Lunde, L, Wangensteen, A. Using SIM for strong
Time Password System. IETF, 1989. (RFC 2289) end-to-end application authentication. In: Tele-
matics. Trondheim, NTNU, 2006. (MSc thesis)
5 Cricco, R, Vinson, Y. Integrating the SIM Card
into J2ME as a Security Element, 2005. October 9 Bluetooth-SIG. Bluetooth specification SIM
Access Profile v.10, 2005.
Score
12 Session-ID check (manual)
Session-ID check (automatic)
10
OTP PC-to-SMS (manual)
8
OTP PC-to-SMS (automatic)
6
OTP SMS-to-PC (manual)
4 OTP SMS-to-PC (automatic)
2 SIM Strong authentication
SIM Strong authentication with SMS
0
Security Cost Infrastructure User-friendliness
Criteria
Figure 9 Comparison of the different authentication solutions based on the mobile phone
For a presentation of Ivar Jørstad and Do Van Thanh, please turn to page 10 and 2, respectively.
ISSN 0085-7130©Telenor ASA 2007
Telektronikk 3/4.2007 151
You might also like
- Project Report On 2factor AuthenticationDocument47 pagesProject Report On 2factor Authenticationkuldeep0511100% (9)
- Pre Seclevels Vapen Shahmehri PrimelifeDocument8 pagesPre Seclevels Vapen Shahmehri PrimelifeMani BmvNo ratings yet
- 10 11648 J WCMC 20130101 15Document9 pages10 11648 J WCMC 20130101 15tolufakanleNo ratings yet
- Visolve - : Open Source SolutionsDocument18 pagesVisolve - : Open Source SolutionsUmair JavedNo ratings yet
- A Secure Web Authentication ProtocolDocument18 pagesA Secure Web Authentication ProtocolLavanyaNo ratings yet
- SET With SMS OTP Using Two Factor AuthenticationDocument4 pagesSET With SMS OTP Using Two Factor AuthenticationSrikanthNo ratings yet
- Delegation-Based in On-Line and Off-Line Authentication Over Wireless CommunicationDocument8 pagesDelegation-Based in On-Line and Off-Line Authentication Over Wireless CommunicationJournal of Computer ApplicationsNo ratings yet
- A Study On Comparison of Algorithm For One Time Password SystemDocument6 pagesA Study On Comparison of Algorithm For One Time Password SystemInternational Organization of Scientific Research (IOSR)No ratings yet
- A Novel User Authentication Scheme Based On QR-Code: Kuan-Chieh LiaoDocument5 pagesA Novel User Authentication Scheme Based On QR-Code: Kuan-Chieh LiaoSaiprasanthi Rakesh0% (1)
- Internship ReportDocument13 pagesInternship Reportlajuvanthi mNo ratings yet
- Two-Factor AuthenticationDocument2 pagesTwo-Factor Authenticationumair riazNo ratings yet
- Multi Factor Authentication Whitepaper Arx - Intellect DesignDocument12 pagesMulti Factor Authentication Whitepaper Arx - Intellect DesignIntellect DesignNo ratings yet
- Two-Factor Authentication:: A Tokenless ApproachDocument15 pagesTwo-Factor Authentication:: A Tokenless ApproachPistolStar Tailored AuthenticationNo ratings yet
- Q.1) A Telecommunication Network Is A Collection of Diverse Media Supporting Communication Between End-Point. Explain in DetailDocument8 pagesQ.1) A Telecommunication Network Is A Collection of Diverse Media Supporting Communication Between End-Point. Explain in DetailYasir ButtNo ratings yet
- Telstra Integrated Messaging Powered by Soprano Mobile AuthenticaDocument2 pagesTelstra Integrated Messaging Powered by Soprano Mobile AuthenticaD8RH8R .oOo.oOo.No ratings yet
- Nonintrusive Smartphone User Verification Using Anonymzed Multimodal DataDocument13 pagesNonintrusive Smartphone User Verification Using Anonymzed Multimodal DataThanksNo ratings yet
- PROTECT Efficient Password-Based Threshold Single-Sign-On Authentication For Mobile Users Against Perpetual LeakageDocument12 pagesPROTECT Efficient Password-Based Threshold Single-Sign-On Authentication For Mobile Users Against Perpetual LeakageAbhi SNo ratings yet
- Three - BduDocument76 pagesThree - BduDharshini AnbazhaganNo ratings yet
- Reducing Reauthentication Delay in Wireless Networks: Tuomas Aura and Michael Roe Microsoft Research, Cambridge, UKDocument10 pagesReducing Reauthentication Delay in Wireless Networks: Tuomas Aura and Michael Roe Microsoft Research, Cambridge, UKsathish14singhNo ratings yet
- A Comparative Analysis of Various Multistep Login Authentication MechanismsDocument7 pagesA Comparative Analysis of Various Multistep Login Authentication MechanismsMbaye Babacar MBODJNo ratings yet
- Mobile Code SecurityDocument39 pagesMobile Code SecurityNarender KumarNo ratings yet
- PROTECT - Implementing Multi-Factor Authentication (October 2021)Document8 pagesPROTECT - Implementing Multi-Factor Authentication (October 2021)asdd111asNo ratings yet
- AAA Administration For Clouds Unit 4Document35 pagesAAA Administration For Clouds Unit 4sambangialekhya846No ratings yet
- Visolve - : Open Source SolutionsDocument18 pagesVisolve - : Open Source Solutionsmartinwaits4uNo ratings yet
- Secure, Fast, and Energy-Efficient Outsourced Authentication For SmartphonesDocument15 pagesSecure, Fast, and Energy-Efficient Outsourced Authentication For SmartphonesIsi IndiaNo ratings yet
- DIT: De-Identified Authenticated Telemetry at ScaleDocument15 pagesDIT: De-Identified Authenticated Telemetry at ScaleMarsha GustiNo ratings yet
- 1 IntroductionDocument103 pages1 IntroductionHimanshu ShekharNo ratings yet
- An Extensive Formal Analysis of Multi Factor Authentication ProtocolsDocument15 pagesAn Extensive Formal Analysis of Multi Factor Authentication Protocolsmulemy46No ratings yet
- Pid 2878063Document4 pagesPid 2878063ChengappaNo ratings yet
- E-Commerce: Technical and Market Approach: UktiDocument4 pagesE-Commerce: Technical and Market Approach: UktiAvisheik Barua 1721158No ratings yet
- Digital Signatures and Authentication ProtocolsDocument19 pagesDigital Signatures and Authentication ProtocolsMerryl Lorraine GonzagaNo ratings yet
- Two Novel Biometric Features in Keystroke Dynamics Authentication Systems For Touch Screen DevicesDocument9 pagesTwo Novel Biometric Features in Keystroke Dynamics Authentication Systems For Touch Screen Devices張庭毅No ratings yet
- Why Digital Certificates Are Essential For Managing Mobile Devices 05 04 20Document12 pagesWhy Digital Certificates Are Essential For Managing Mobile Devices 05 04 20davidNo ratings yet
- Multi-Factor Password-Authenticated Key Exchange: Douglas Stebila Poornaprajna Udupi Sheueling ChangDocument11 pagesMulti-Factor Password-Authenticated Key Exchange: Douglas Stebila Poornaprajna Udupi Sheueling ChangFotis MarnerasNo ratings yet
- StrongAuthentication SecureEmployeeAccess SB (En) WebDocument2 pagesStrongAuthentication SecureEmployeeAccess SB (En) WebtutakhaluNo ratings yet
- Kony Retail Banking Solutions BriefDocument4 pagesKony Retail Banking Solutions BriefMaheswar ReddyNo ratings yet
- Chapter 1 IntroductionDocument8 pagesChapter 1 IntroductionSwapnil BhardwajNo ratings yet
- A Protected Single Sign On Technique Using 2D Password in DistributedDocument6 pagesA Protected Single Sign On Technique Using 2D Password in DistributedEditor IJRITCCNo ratings yet
- Best Practices For Wireless Network SecurityDocument7 pagesBest Practices For Wireless Network SecuritymatNo ratings yet
- A Secure N-Secret Based Client Authentication ProtDocument14 pagesA Secure N-Secret Based Client Authentication Proteugenchirilov05No ratings yet
- Distributed Security and Authentication Protocols, Fault-Tolerant DatabasesDocument17 pagesDistributed Security and Authentication Protocols, Fault-Tolerant DatabasesFredNo ratings yet
- Demystifying Authentication Concepts in SmartphoneDocument16 pagesDemystifying Authentication Concepts in Smartphoneswarna_793238588No ratings yet
- Authentication System For Banking Using Implicit Password: Ms. Prajakta.D.Kulkarni, Mr. C.S.Satsangi, Mr. Santhosh EasoDocument4 pagesAuthentication System For Banking Using Implicit Password: Ms. Prajakta.D.Kulkarni, Mr. C.S.Satsangi, Mr. Santhosh EasoIJERDNo ratings yet
- 10 1 1 67Document12 pages10 1 1 67sekhargNo ratings yet
- Advanced Penetration Testing Methodology For VPNDocument6 pagesAdvanced Penetration Testing Methodology For VPNRahmad Rumoh Aceh100% (1)
- Managing The Risk For Mobile IT UsersDocument4 pagesManaging The Risk For Mobile IT UsersquocircaNo ratings yet
- 2factor Pro MZCDocument61 pages2factor Pro MZCShibin VarghesNo ratings yet
- Network Security Paper2015 OriginalDocument6 pagesNetwork Security Paper2015 OriginalPriyanka BedekarNo ratings yet
- Security Mechanisms in The Service of Mobile Banking: Wojciech WodoDocument3 pagesSecurity Mechanisms in The Service of Mobile Banking: Wojciech WodoMircea PetrescuNo ratings yet
- Joint Biometric ATM - Rewritten PaperDocument8 pagesJoint Biometric ATM - Rewritten PaperAfza FathimaNo ratings yet
- Analysis of Single Sign On Web - Emergence of Google Service ProviderDocument5 pagesAnalysis of Single Sign On Web - Emergence of Google Service ProviderInternational Journal of Engineering Inventions (IJEI)No ratings yet
- The Importance of Transaction Signing To Banks: © 2014 EntersektDocument8 pagesThe Importance of Transaction Signing To Banks: © 2014 EntersektAtif KhanNo ratings yet
- Chapter 1Document46 pagesChapter 1Kalyan Reddy AnuguNo ratings yet
- Cnets - Chapter 5 - PPTDocument22 pagesCnets - Chapter 5 - PPTjmquintua05No ratings yet
- CryptographyDocument6 pagesCryptographyKaleeswariNo ratings yet
- Seminar Report On "Image Based Authentication System"Document26 pagesSeminar Report On "Image Based Authentication System"SaurabhNo ratings yet
- 8thsem 3rd DefenceDocument7 pages8thsem 3rd DefenceAyush SinghalNo ratings yet
- PrijectDocument66 pagesPrijectARSHEEYA BONo ratings yet
- CC 5Document17 pagesCC 5bhargav242004No ratings yet
- Securing .NET Web Services with SSL: How to Protect “Data in Transit” between Client and Remote ServerFrom EverandSecuring .NET Web Services with SSL: How to Protect “Data in Transit” between Client and Remote ServerNo ratings yet
- t60 User ManualDocument97 pagest60 User ManualmenacoreaNo ratings yet
- Auth Shield Lab - Mobile One Touch Authentication SolutionsDocument12 pagesAuth Shield Lab - Mobile One Touch Authentication SolutionsAuthShield LabNo ratings yet
- Account Activation Kotak SecuritiesDocument5 pagesAccount Activation Kotak SecuritiesShashank ChandraNo ratings yet
- Lesson 7: Implementing Authentication ControlsDocument35 pagesLesson 7: Implementing Authentication ControlsPhan Sư Ýnh100% (2)
- PDF-ROSSLARE ACF44 Manual PDFDocument24 pagesPDF-ROSSLARE ACF44 Manual PDFDeni Khan100% (1)
- Accounting Information Systems 2Nd Edition Richardson Solutions Manual Full Chapter PDFDocument32 pagesAccounting Information Systems 2Nd Edition Richardson Solutions Manual Full Chapter PDFmary.wiles168100% (23)
- 44 RP 2002 Notifier IselecDocument4 pages44 RP 2002 Notifier IselecAlejandro RoperoNo ratings yet
- C209A41AdmitCard PDFDocument1 pageC209A41AdmitCard PDFSourav VishwakarmaNo ratings yet
- Matrix Presentation COSEC Face Recognition PDFDocument43 pagesMatrix Presentation COSEC Face Recognition PDFashok kalaguntaNo ratings yet
- Kerberos NotesDocument7 pagesKerberos Notesskhanshaikh3No ratings yet
- Appointment - Slip Urmila HazraDocument1 pageAppointment - Slip Urmila HazraRanu mohdNo ratings yet
- End Term Time Table UG PG 1st Year JUNE 2023 EXAMDocument12 pagesEnd Term Time Table UG PG 1st Year JUNE 2023 EXAMkanakvani39No ratings yet
- Secure Distributed Single Sign-On With Two-Factor AuthenticationDocument78 pagesSecure Distributed Single Sign-On With Two-Factor AuthenticationDungPhamTuanNo ratings yet
- (Download PDF) Isc SSCP Systems Security Certified Practitioner Official Practice Tests Chapple Online Ebook All Chapter PDFDocument42 pages(Download PDF) Isc SSCP Systems Security Certified Practitioner Official Practice Tests Chapple Online Ebook All Chapter PDFconrad.smith263100% (9)
- CISSP Exam TipsDocument6 pagesCISSP Exam Tipsrahuls256No ratings yet
- Online Application PresentationDocument9 pagesOnline Application PresentationmissdphiriNo ratings yet
- SoD Analysis and Access GovernanceDocument8 pagesSoD Analysis and Access Governancevansh143No ratings yet
- Access Control SystemDocument8 pagesAccess Control SystemAkande Oluwadamilola TosinNo ratings yet
- ACR122U NFC Reader SDK User ManualDocument12 pagesACR122U NFC Reader SDK User ManualMagabata GoguNo ratings yet
- Alarma Inteligente - EyeSiteDocument5 pagesAlarma Inteligente - EyeSiteMarco Antonio AlejoNo ratings yet
- Application For Retention of NameDocument2 pagesApplication For Retention of NameNatyra Rani0% (1)
- Onward Journey Ticket Details: ConfirmedDocument2 pagesOnward Journey Ticket Details: ConfirmedRanjithNo ratings yet
- SecretDocument20 pagesSecretnarendrasingh4039No ratings yet
- OOSE Case Study Converted 1Document13 pagesOOSE Case Study Converted 1Babin BistaNo ratings yet
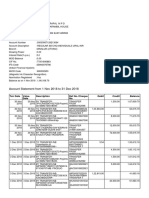
- Account Statement From 1 Nov 2018 To 31 Dec 2018: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDocument3 pagesAccount Statement From 1 Nov 2018 To 31 Dec 2018: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceJithendrapal MuthangaparambilNo ratings yet
- Applicant'S Copy: Additional Course DetailDocument1 pageApplicant'S Copy: Additional Course DetailMonu SoodNo ratings yet
- Access Card 2017Document26 pagesAccess Card 2017pegiNo ratings yet
- Kmpnai Rijast/Ar Kayaa-Laya Rayt/Iya Rajaqaanai Xao Idllai Evam Hiryaanaa Kmpnai Aiqainayama 1956 Ki Qaara 140 Rohna Aaid Ko Samtuytikrna Ka &apnaDocument2 pagesKmpnai Rijast/Ar Kayaa-Laya Rayt/Iya Rajaqaanai Xao Idllai Evam Hiryaanaa Kmpnai Aiqainayama 1956 Ki Qaara 140 Rohna Aaid Ko Samtuytikrna Ka &apnalomNo ratings yet
- Script TACACSDocument2 pagesScript TACACScrosspopzNo ratings yet
- Incidentrequest Closed Monthly JanDocument320 pagesIncidentrequest Closed Monthly Janأحمد أبوعرفهNo ratings yet