Professional Documents
Culture Documents
Symmetric and Asymmetric Encryption: Sandm Laboratories, Albuquerque, New Mexico 87185
Symmetric and Asymmetric Encryption: Sandm Laboratories, Albuquerque, New Mexico 87185
Uploaded by
Laine VenâncioOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Symmetric and Asymmetric Encryption: Sandm Laboratories, Albuquerque, New Mexico 87185
Symmetric and Asymmetric Encryption: Sandm Laboratories, Albuquerque, New Mexico 87185
Uploaded by
Laine VenâncioCopyright:
Available Formats
Symmetric and Asymmetric Encryption
GUSTAVUS J. SIMMONS
Sandm Laboratories, Albuquerque, New Mexico 87185
All c r y p t o s y s t e m s currently m use are s y m m e t r m m t h e sense t h a t t h e y require t h e
t r a n s m i t t e r a n d receiver to share, m secret, either t h e s a m e pmce of reformation (key) or
one of a paLr of related keys easdy c o m p u t e d from each other, t h e key is u s e d m t h e
encryption process to introduce u n c e r t a i n t y to an u n a u t h o r i z e d receiver. N o t only is a n
a s y m m e t r i c encryption s y s t e m one in w h m h t h e t r a n s m i t t e r a n d receiver keys are
different, b u t in addition it Is c o m p u t a t m n a l l y mfeaslble to c o m p u t e at least one from t h e
other. A s y m m e t r i c s y s t e m s m a k e it possible to authent2cate m e s s a g e s whose c o n t e n t s
m u s t be revealed to a n o p p o n e n t or allow a t r a n s m i t t e r w h o s e key h a s b e e n c o m p r o m i s e d
to c o m m u n m a t e m privacy to a receiver whose key h a s been kept s e c r e t - - n e i t h e r of w h i c h
is possible using a s y m m e t r i c cryptosystem.
T h i s paper opens with a brmf dmcussion of e n c r y p t m n principles a n d t h e n proceeds to
a c o m p r e h e n s i v e discussion of t h e a s y m m e t r i c e n c r y p t m n / d e c r y p t i o n c h a n n e l a n d its
application m secure c o m m u n m a t i o n s .
Keywords and Phrases: cryptography, secure c o m m u n i c a t i o n s , a s y m m e t r i c e n c r y p t m n ,
c o m p u t a t m n a l complexity, public-key cryptosystems, a u t h e n t m a t m n
CR Categortes. 3,81, 5.25, 5.6
INTRODUCTION metric e n c r y p t i o n / d e c r y p t i o n c h a n n e l - -
solves the new requirements in secure com-
T h e object of secure communications has
munications. For perspective, the reader
been to provide privacy or secrecy, i.e., to
should keep in mind t h a t all current cryp-
hide the contents of a publicly exposed
tosystems are symmetric in the sense t h a t
message from unauthorized recipients. In
c o n t e m p o r a r y commercial and diplomatic either the same piece of information (key)
applications, however, it is frequently of is held in secret by b o t h communicants, or
equal or even greater concern t h a t the re- else t h a t each communicant holds one from
ceiver be able to verify t h a t the message a pair of related keys where either key is
has not been modified during transmission easily derivable from the other. T h e s e se-
or t h a t it is not a counterfeit from an un- cret keys are used in the encryption process
authorized transmitter. In at least one im- to introduce uncertainty (to the unauthor-
portant class of problems message authen- ized receiver), which can be r e m o v e d in the
tication is needed at the same time t h a t the process of decryption by an authorized re-
message itself is revealed. ceiver using his copy of the key or the
In this paper secure communications are "inverse key." This means, of course, t h a t
discussed with emphasis on applications if a key is compromised, further secure com-
t h a t cannot be satisfactorily handled by munications are impossible with that key.
present cryptographic techniques. Fortu- T h e new cryptosystems are asymmetric in
nately, an entirely new c o n c e p t - - t h e asym- the sense t h a t the transmitter and receiver
hold different keys at least one of which it
T h i s article was sponsored by t h e U.S D e p a r t m e n t of
is computationally infeasible to derive from
E n e r g y u n d e r Contract DE-AC04-76DP00789. the other.
P e r m m s m n to copy w i t h o u t fee all or part of this material is g r a n t e d provided t h a t t h e copies are n o t m a d e or
distributed for direct commercial advantage, t h e A C M copyright notice a n d t h e title of t h e publication a n d its
date appear, a n d notice is given t h a t copying is by permtssion of t h e Association for C o m p u t i n g M a c h i n e r y . T o
copy otherwise, or to r e p u b h s h , requires a fee a n d / o r specific permmslon.
© 1979 A C M 0010-4892/79/1200-0305 $00 75
Computing Surveys, Vol. 11, No. 4, December 1979
306 • Gustavus J. Simmons
CONTENTS stream and block ciphers. The plaintext
message is a sequence of symbols from
some alphabet d (letters or numbers). A
stream cipher operates on the plaintext
INTRODUCTION symbol by symbol to produce a sequence of
1 CLASSICAL CRYPTOGRAPHY cipher symbols from an alphabet c#. ((d and
2 READER'S GUIDE
d are frequently the same.) Symbolically,
3 THE COMMUNICATIONS CHANNEL
4 THE ENCRYPTION/DECRYPTION
if lr is a nonsingular mapping it:d---) cd, and
CHANNEL M is a plaintext message
5 COMPUTATIONAL COMPLEXITY AND SYM-
METRIC ENCRYPTION M = (ala~ . . . a~]a, E d ) ,
6 COMPUTATIONAL COMPLEXITY AND
ASYMMETRIC ENCRYPTION then the stream cipher C -- It(M) is given
6 1 The Knapsack Trapdoor by
6 2 The Factonzatlon Trapdoor
7 AUTHENTICATION C = (Ir(al), ~r(a2). . . . . Ir(ak) I f(a,) ~ ~d).
8 SECURE COMMUNICATIONS
SUMMARY AND CONCLUSION The mapping ~ is commonly a function of
APPENDIX previous inputsmas in the rotor cryptoma-
ACKNOWLEDGMENTS chines of the World War II period. The
REFERENCES various versions of Vigen~re encryption to
be discussed shortly are all examples of
v
stream ciphers, some of which use a f'Lxed
mapping and others, such as the running
It is possible to communicate in secrecy key and autokey systems, a usage-depen-
and to "sign" digital messages using either dent mapping.
symmetric or asymmetric techniques if In a block cipher a block of symbols from
both the receiver and transmitter keys can M is operated on jointly by the encryption
be secret. One of these functions can be algorithm, so that in general one may view
accomplished with an asymmetric system a block cipher as a nonsingular I mapping
even though the transmitter or the receiver from the set of plaintext n-tuples ~ n into
key has been revealed. It is also possible to the set of cipher n-tuples ~n. For crypto-
communicate privately without a prior systems which use the same key repeatedly,
covert exchange of keys and to authenticate block ciphers are cryptographicaUy
messages even when the contents cannot stronger than stream ciphers. Conse-
be concealed from an opponent--neither of quently, most contemporary cryptosystems
which is possible with a symmetric crypto- are block ciphers, although one-time key
system. The current revolution in secure systems are used in applications where the
communications is based on the ability to very highest security is required. Examples
secure communications even when one ter- of block ciphers are the Playfair digraph
minal (and the key) is located in a physi- substitution technique, the Hill linear
caUy unsecured installation.
transformation scheme, and the NBS Data
Encryption Standard (DES). The distinc-
1. CLASSICAL CRYPTOGRAPHY tion between block and stream ciphers is
Classical cryptography seeks to prevent an more apparent than real since a block ci-
unauthorized (unintended) recipient from pher on n-tuples from d is equivalent
determining the content of the message. In to a stream cipher over the enlarged
this section we illustrate the concepts of all alphabet d n.
cryptosystems, such as key, stream or block Since much of the discussion relies on
ciphers, and unicity point. A more detailed the concept of a "key" in the cryptosystem,
account can be found in the paper by Lem- we shall present several examples that il-
pel [LEMP79] and in Kahn's encyclopedic lustrate keys and possible attacks to dis-
The Codebreakers, the Story of Secret cover them.
Writing [KA~IN67].
A primitive distinction among cryptosys- Nonsingularsnnplymeansthat everycipherdecrypts
to a unique message. In Section 6.2 an example of a
terns is the structural classification into singular cryptomappmgis described.
C o m p u t m g Surveys, Vol 11, N o 4, D e c e m b e r 1979
Symmetric and Asymmetric Encryption . 307
In the most general terms possible, an substitution cipher or cryptogram simply
encryption system must combine two ele- replaces each plaintext symbol by a cipher
ments: some information--called the key-- symbol; the key specifies the mapping. An
known only to the authorized communi- example is the Caesar cipher, in which each
cants, and an algorithm which operates on letter is replaced by the letter occurring k
this key and the message (plaintext) to places later in the alphabet (considered
produce the cipher. The authorized re- cyclically); when k ffi 3,
ceiver, knowing the key, must be able to
recover the message (decrypt the cipher); COMPUTING SURVEYS
an unauthorized receiver should not be able -- FRPSXWLQJ VXUYHBV.
to deduce either the message or the un- Simple transposition permutes symbols in
known key. The key as defined here is very the plaintext. The permutation is the key.
general: It is the total equivocation of For example, if the permutation (15327468) 3
everything that is kept secret from an op- is applied to the two blocks of eight symbols
posing cryptanalyst. By this definition, a above,
key can be much longer than the bit stream
serving as the key in some cryptodevices. COMPUTING SURVEYS
= NMUICPOTS UVYGRSE.
The encryption algorithm must be so
constructed that even if it becomes known In either of these simple cases the fre-
to the opponent, it gives no help in deter- quency of occurrence of symbols is unaf-
mining either the plaintext messages or the fected by the encryption operation. The
key. This principle, first formulated by Ker- cryptanalyst can get a good start toward
choffs in 1883, is now universally assumed breaking the code by a frequency analysis
in determining the security of cryptosys- of cipher symbols [KtJLL76]. In secure sys-
terns. tems complicated usage-dependent combi-
Preprocessing a text by encoding into nations of the two primitive encryption op-
some other set of symbols or symbol groups erations are used to cause all cipher sym-
by an unvarying rule is not considered to bols to occur with equal frequency.
be a part of the encryption process, even It might seem that such simple systems
though the preprocessing may complicate would offer reasonable cryptosecurity since
the cryptanalyst's task. For example, The there are 26! .~ 4 × 1026 substitutions pos-
Acme Commercial Code [ACME23] replaces sible on the 26 alphabetic characters in the
entire phrases and sentences by five-letter first case and n! permutations on n-symbol
groups; the preprocessed text E J E H S blocks in the second. But the redundancy
OHAOR CZUPA, which is derived from of English (indeed, any natural language) is
(BUDDY) (CAN YOU SPARE) ((A) so great that the log2(26!) ~ 88.4 bits of
DIME(S)), would be as baffling to the equivocation introduced by the encryption
cryptanalyst as a cipher. Continued use of algorithm can be resolved by a cryptana-
fixed preprocessing codes, however, de- lyst, using frequency of occurrence counts
stroys this apparent cryptosecurity, which on symbols, with approximately 25 symbols
is therefore considered to be nonexistent of cipher text! This illustrates how decep-
from the beginning. Common operations tive the appearance of large numbers of
which compress text by deleting superflu- choices to the cryptanalyst can be in judg-
ous symbols or expand text with null sym- ing the cryptosecurity of a cryptosystem.
bols are considered to be part of the encod- An obvious means of strengthening sub-
ing of the text rather than part of the en- stitution ciphers is to use not one but sev-
cryption process. eral monoalphabetic substitutions, with the
The encryption process itself consists of key specifying which substitution is to be
two primary operations and their combi- used for each symbol of the cipher. Such
nations, substitution and transposition. 2 A systems are known as polyalphabetics. The
2 K a h n lKAHN67, p. 764] has analogized substitution J This notation means: move the first symbol to the
and transposition ciphers with continuous and batch fifth place, t h e fifth symbol to t h e third place, the
manufacturing processes, respectively. thtrd symbol to the second place, and so on.
Computing Surveys, Vol. 11, No. 4, December 1979
308 • Gustavus J. Simmons
best known are the simple Vigen~re ciphers ning-key ciphers is the so-called probable
wherein the substitutions are taken as the word method in which the cryptanalyst
mod 26 sum of a symbol of the message m, "subtracts" from the cipher words that are
and a symbol of the key ks, with the con- considered likely to occur in the text until
vention A -~ 0, . . . , Z ~- 25. Depending on fragments of sensible key text are re-
the complexity of the substitution rule covered; these are then expanded using
{key) chosen, the equivocation of such a either of the two techniques just discussed.
Vigen~re-type system can be made as great The vital point is that although the equiv-
as desired, as we see later in examining the ocation in the running text can be made as
random key Vernam-Vigen~re system. The large as desired, the redundancy in the lan-
following examples illustrate how the key guage is so high that the number of bits of
complexity can affect the security of a cryp- information communicated per bit of cipher
tosystem. exceeds the rate at which equivocation is
In the simplest Vigen4re-type systems, introduced by the running key. Therefore,
the key is a word or phrase repeated as given sufficient cipher text, the cryptana-
many times as necessary to encrypt the lyst will eventually have enough informa-
message; for example, if the key is COVER tion to solve the cipher.
and the message is T H E M A T H E M A T I C S The most important of all key variants to
OF SECRECY, the resulting cipher is the Vigen~re system was proposed in 1918
by the American engineer G. S. Veruam
Message T H E M A T H E M A T I C S OF SECRECY
[VEI~N26]. Messages for transmission over
Key COV ERCOVERCOVE RC OVERCOV
C~pher VVZ RQVVZRQVWXW FH GZGIGQT.
the AT&T teletype system were at that
time encoded in Baudot code, a binary code
Kasiski's general solution of repeated key consisting of marks and spaces. Vernam
Vigen4re ciphers starts from the fact that recognized that if a random sequence of
like pairings of message and key symbols marks and spaces were added rood 2 to the
produce the same cipher symbols; these message, then all of the frequency infor-
repetitions are recognizable to the crypt- mation, intersymbol correlation, and pe-
analyst [KAHN67]. The example above riodicity, on which earlier successful meth-
shows the group VVZRQ repeated twice; ods of attack against various Vigen~re sys-
the length of the repeated group reveals tems had been based, would be totally lost
that the key length is five. The cipher sym- to the cryptanalyst. In this judgment Ver-
bols would then be partitioned into five nam's intuition was absolutely right, as
monoalphabets each of which is solved as would be proved two decades later by an-
a substitution cipher. other AT&T scientist, Claude Shannon
To avoid the problems of the preceding [SHAN49]. Vernam proposed to introduce
example, one can use a nonrepeating text uncertainty at the same rate at which it
for the key. The result is called a running- was removed by redundancy among sym-
key Vigen~re cipher. The running key pre- bols of the message. Unfortunately, this
vents the periodicity exploited by the Kas- ideal requires exchanging impractical
iski solution. However, there are two basic amounts of key in advance of communica-
types of solution available to the cryptana- tion, i.e., one symbol of key must be pro-
lyst in this case [KAHN66]. One can apply vided for every symbol of message. In Ver-
statistical analysis by assuming that both nam's invention the keys were made up in
cipher text and key have the same fre- the form of punched paper tapes which
quency distributions of symbols. For ex- were read automatically as each symbol
ample, E encrypted with E occurs with a was typed at the keyboard of a teletype-
frequency of =0.0169 and T by T occurs writer and encrypted "on line" for trans-
only half as often. A much longer segment mission. An inverse operation at the receiv-
of cipher test is required to decrypt a run- ing teletype decrypted the cipher using a
ning-key Vigen~re cipher; however, the copy of the tape. Vernam at first thought
methods, based on recurrence of like that a short random key could safely be
events, are similar. used over and over; however, the resulting
The other technique for attacking run- periodicity of the key permits a simple Kas-
Computing Surveys, Vol 11, No. 4, December 1979
Symmetric a n d A s y m m e t r i c Encryption • 309
iski-type solution. A second proposed solu- unconditionally secure, it is necessary to
tion was to compute a key of n~n2 bits in add the qualification that each symbol of
length by forming the logical sum, bit by the key introduce at least as much uncer-
bit, of two shorter key tapes of relatively tainty as is removed by a symbol of the
prime lengths nl and n2, so that the result- cipher.
ing key stream would not repeat until n~n2 An interesting example of the need for
bits of key had been generated. This form the key to introduce uncertainty, even with
of Vernam system was used for a time by a nonrepeating random key, appears in a
the U.S. Army. recent article by Deavours on the unicity
The greatest contribution of the two-tape point 6 of various encryption systems
Vernam system came from its successful [DEAV77]. In Deavours's example, the
cryptanalysis, which led to the recognition key introduces exactly 1 bit per symbol
of the unconditional cryptosecurity of one- using the random binary stream
time keys or pads. Major J. O. Mauborgne 0011001100100000101110111 ... to en-
of the U.S. Army Signal Corps showed that cipher a message in the Vigen~re scheme
cipher produced from key generated by the with B as key if k, ffi 0 and C as key if k, ffi
linear combination of two or more short 1. Deavours's cipher is
tapes could be successfully analyzed by TPOGD JRJFS UBSFC SQLGP COFUQ
techniques essentially the same as those NFDSF CLVIF TONWG T.
used against running-key systems. The un-
avoidable conclusion was that the Vernam- The first four letters, for example, could
Vigen~re system with either a repeating decrypt sensibly to either SOME or ROME,
single key tape or with linear combinations etc., but the reader should have no diffi-
of repeating short tapes to form a long key culty determining the intended message to
sequence were both insecure. The truly sig- be: SOME CIPHERS ARE BROKEN
nificant conclusion was arrived at by Fried- AND SOME BREAK THEMSELVES.
man and Mauborgne: The key in an uncon- All of the preceding examples are of
ditionally secure stream cipher 4 must be stream ciphers, illustrating the way in
incoherent (the uncertainty, or entropy, of which the key equivocation appears in each
each key symbol must be at least as great case, and also the concepts of unicity point
as the average information content per and one-time pad or key. We turn now to
symbol of the message}. Such a cryptosys- block ciphers, of which we will describe
tem is referred to as a random one-time key two. Block ciphers attempt to deny to the
or pad. 5 In other words, the system is un- cryptanalyst the frequency statistics which
conditionally secure--not because of any have proved so useful against stream ci-
failure on the cryptanalyst's part to find the phers. One way to accomplish this is to
right technique, but rather because the operate on pairs of symbols (digraphs), tri-
equivocation faced by the cryptanalyst ples (trigraphs), or, in general, on blocks
leaves an irresolvable number of choices for (polygraphs). For manageability, manual
key or plaintext message. While it is often block cryptosystems are limited to digraph
stated that a Vernam-Vigen~re cryptosys- substitutions. The best known manual di-
tem with a nonrepeating random key is graph system is Wheatstone's Playfair
cipher, in which a 25-symbol alphabet 7 is
written in a 5 × 5 array with a simple
4 This condition applies to both block and stream geometric rule [GAIN56] specifying the
ciphers, although at the time the conditions were cipher digraph to be substituted for each
stated, block ciphers were not considered because of digraph in the message.
the difficulty of manual implementation.
One needs to clearly distmgmsh between two kmds
of undecipherabihty In one kind the equivocation is
too high even if the analyst makes perfect use of all 6 The unicity point was defined by Shannon to be the
available information. This may be because of the length of cipher beyond which only a single plamtext
brevity of cipher or of a lost key, as with the famous message could have produced the cipher, i.e, the point
Thomas Jefferson Beale book ciphers, numbers 1 and of zero eqmvocatlon to the cryptanalyst [SHAN49].
3 [HART64]. In the other, the code can be deciphered 7 The letter J is usually dropped m the Playfair cipher
in principle but not m practice, as is probably the case smce it occurs infrequently and can almost always be
with the MIT challenge cipher [GARD77|. filled m by context or by substituting I m the text
Computing Surveys, Voi. 11, No. 4, December 1979
310 Gustavus J. S i m m o n s
TABLE 1
Number of Letter Number of Letter Number of
Letter Occurrences Occurrences Occurrences
E 540 C 212 Y 57
T 479 M 177 B 44
O 384 D 168 U 42
A 355 H 145 K 33
N 354 U 136 Q 11
I 326 P 114 x 7
R 317 F 87 Z 4
S 3O8 G 67 J 1
L 219 W 65
The cornerstone of modern mathemati- Note that the three L's in LULL encipher
cal cryptography was laid by Hill [HILL29, into different symbols. This illustrates the
HILL31, ALBE41] in 1929. Hill recognized cryptographic advantage of polygraphic
that nearly all the existing cryptosystems systems: The raw frequency-of-occurrence
could be formulated in the single model of statistics for blocks up to size n are ob-
linear transformations on a message space. scured in the encryption process; in the
Hill identified a message n-tuple with an n- limit (with n), they are lost completely.
tuple of integers and equated the operations Table i shows the number of occurrences
of encryption and decryption with a pair of of each letter in 4652 letters of an English
inverse linear transformations. The sim- language computing science article. These
plest representation for such transforma- patterns, which survive any monographic
tions is multiplication of an n-tuple (mes- substitution, are invaluable clues to the
sage) by a nonsingular n )< n matrix to form cryptanalyst. For instance, he knows that
the cipher and by the inverse matrix to T is one of the most frequently occurring
decrypt and recover the message. For ex- letters and can be quite sure that T is one
ample, let the digits zero-nine be repre- of the eight most frequently seen letters.
sented by the numbers 0-9, blank by 10, Figure 1 shows the frequency-of-occurrence
and the 26 letters of the alphabet by 11-36. data for single symbols in the cipher, for a
The number of symbols, 37, is a prime; the simple monographic encryption, and for po-
encoding and decoding can be carried out lygraphic encryption distributions with ma-
with arithmetic modulo 37. If the encrypt- trix sizes 2 × 2, 3 × 3, and 4 × 4. A perfect
ing matrix is encryption system would have a flat distri-
bution for all n-tuples; i.e., all possible n-
tuples would be equally likely,s
Tuckerman [TucK70] in his analysis
and the decrypting matrix is of Vigen~re-Vernam cryptosystems has
shown that Vigen~re systems using nonran-
dom transformations are always subject to
15 ' statistical attack. This is to be expected
then the message L U L L = (22, 31, 22, 22)
would encrypt to the cipher
Hill's s y s t e m using an n t h - o r d e r t r a n s f o r m a t i o n re-
sists simple statistical m e t h o d s of c r y p t a n a l y s m b a s e d
(7311,\226~(22 ~12)__(21~ 162) o n t h e frequency of occurrence of i-tuples in t h e cipher
for t less t h a n n; however, if t h e c r y p t a n a l y s t h a s two
ciphers r e s u l t m g from t h e encryption of a single mes-
(all computations mod 37). sage with two m v o l u t o r y t r a n s f o r m a t i o n s 3~ a n d ~2., in
M n so t h a t for all m e s s a g e s M ~ ~¢n, ~ ( ~ ( M ) ) =
Similarly, the cipher (27, 16, 12, 2) decrypts -¢2(-¢2(M) = M, a n d if h e k n o w s ~ , h e c a n recover ~l
to yield the message LULL by, a n d 22. It was n o t thin cryptanalytlc weakness, how-
ever, w h m h p r e v e n t e d t h e a d o p h o n of Hill's crypto-
s y s t e m , b u t r a t h e r t h e difficulty of carrying o u t t h e
(119530~(272]\121~)=(~22 ~)(mod37). m a n u a l e n c r y p t i o n / d e c r y p t i o n operations he h a d de-
fined
Computing Surveys, Vol 11, No 4, December 1979
Symmetric and Asymmetric Encryption * 311
550.
MS@0.
U
N 450 •
B
E4@0 •
0 350 •
F
0 300.
cC250.
U 2@@.
R
R ISO.
N
C lee,
C
S 50.
@.
5 9 13 17 21 25
3 ? 11 15 19 23
flUNERIC EQUIUALENT
FIGURE l [1]' Monographm substitution, [2] polygraphic substituhon, matrix size
2 × 2, [3] polygraphicsubstitutmn, matrix size 3 x 3; [4] polygraphicsubstitution,
matrix size 4 x 4
since the initial equivocation to the oppo- cryption/decryption process. To illustrate
nent must eventually be eroded by usage. this, a frequently rediscovered encryption
Tuckerman provides the neat proof of this scheme dependent on maximal length lin-
intuitive statement. ear feedback shift registers (LFSRs) is dis-
The reader wishing a more complete cussed to show how computational feasibil-
treatment is referred to GAIN56, KAHN67, ity can destroy cryptosecurity. In the dis-
or BRIG77 for further details of crypta- cussion of asymmetric encryption two ex-
nalysis. In a later section we take up current amples of computationaUy infeasible prob-
cryptotechnology, which has developed lems are described in detail.
since World War II. Linear feedback shift registers provide
not only a simple illustration of the rela-
2. READER'S GUIDE tionship between cryptosecurity and com-
putational feasibility, but they also illus-
Because of the unavoidable length and de-
trate how redundancy is used in error de-
tail of the subsequent sections, a brief out-
tecting and correcting codes. The main text
line of the development is given here. First, emphasizes these points, while a brief dis-
a parallel between the classical noisy com- cussion of these devices is given in the
munications channel and the general en- appendix.
cryption/decryption channel is drawn. The
The ultimate objective of the paper is to
reason for doing this is that error detecting
impart to the reader a clear perception of
and correcting codes and message or trans-
how secrecy and authentication are accom-
mitter authentication are mathematically
plished in both symmetric and asymmetric
dual problems. In both cases redundancy,
encryption systems. This implies a clear
i.e., extra symbols, is introduced in the mes-
understanding of which forms of secure
sage, but the way in which this redundancy
communication can only be realized
is used to communicate through the chan-
through asymmetric techniques, and which
nel is different in the two applications. This
forms can be realized by either symmetric
is true whether the cryptosystem is sym-
or asymmetric cryptosystems.
metric or asymmetric.
Second, computationally infeasible prob-
3. THE COMMUNICATIONS CHANNEL
lems are the source of cryptosecurity for
both symmetric and asymmetric systems. A transmitter draws a message M from a
One of the important points to this paper is space of possible messages Jg and sends it
to make clear how these computationaUy to a receiver over a noisy communications
complex problems are embedded in an en- channel. It is possible that some M' ~ M
Computing Surveys, Vol 11, No 4, December 1979
312 • Gustavus J. S i m m o n s
m a y be received. In 1948 S h a n n o n [SHAN48] TABLE2
proposed the concept of the entropy of a Message Co~ W o ~
message, which measures its information 000o 000 0000
content. H e showed how to introduce re- 0001 011 0001
d u n d a n c y by means of a code; the extra 0010 11o 0OlO
symbols could be used to detect (and cor- 0011 1010011
rect) errors in the received message M'.
0100 1110100
0101 10o 0101
For example, H a m m i n g codes add 2k + 1 0110 001 0110
bits for each k errors to be detected 0111 010 0111
[MAcW77]. How this r e d u n d a n c y is intro- 1000 lOl 100o
duced and utilized is a function of the way 1001 110 1001
1010 011 lOlO
in which the errors occur in transmission, 1011 00o 1011
i.e., the statistics of the communications 1100 010 1100
channel shown schematically in Figure 2. 1101 0Ol 1101
Essentially one wishes to impose a metric 1110 100,1110
1111 111,1111
on the message space J¢ so t h a t the set of
messages most apt to result from errors in
the transmission of a given message M is subsequences having the 4-bit messages in
also the one "closest" to M in de. For ex- the low-order bit positions from the o u t p u t
ample, if the errors in the binary symmetric of the linear feedback shift register (see
channel are independent and uniformly dis- appendix). If any single bit of the 7-bit code
tributed, the H a m m i n g metric is a natural word is altered in transmission, the receiver
one to use; however, if adjacent symbol can recover the message correctly by find-
errors are more apt to occur, Berlekamp ing the code word t h a t differs from the
[BERL68] has shown the Lee metric 9 to be received block in the fewest n u m b e r of bits.
preferable. Coding t h e o r y is concerned with Figure 3 is a schematic diagram of the
finding a partitioning o f ~ into a collection S h a n n o n channel. T h e codes in ~ are so
of disjoint subsets (ideally "spheres") with designed t h a t the likelihood of an altered
all points in the ith set less t h a n some message being misinterpreted by the re-
specified distance from a central point C, in ceiver is minimum. In the case of error
the set. T h e code t h e n consists of the labels correction, the code is designed to maximize
(code words) of the collection of central the likelihood t h a t the receiver will be able
points in the subsets of J~, with the maxi- to transform the received message to the
m u m likelihood error correction rule being message actually sent correctly.
to decode any received point in ~ as the
central point of the class t h a t it belongs to 4, THE ENCRYPTION/DECRYPTION
in the partition. CHANNEL
Since we shall later wish to contrast the
partitioning of J / f o r message authentica- T h e encryption channel also consists of a
tion to the kind of partitioning useful for transmitter who wishes to send a message
error detection and c o r r e c t i o n - - w h e r e the M to a receiver. B u t now the channel is
objective in b o t h instances is to d e t e c t an assumed to be u n d e r surveillance by a hos-
incorrect message--we give in T a b l e 2 an tile opponent. Cryptographic t h e o r y seeks
example of a H a m m i n g code t h a t adds to devise codes t h a t cannot systematically
three extra bits to each 4-bit block of mes- be distinguished from purely r a n d o m bit
sage code [MAss69]. This code can be gen- strings by the opponent. T h e statistical
erated by taking as code words the 7-bit communications channel of the coding/de-
coding model has been replaced by a game-
theoretic channel; nature has been replaced
by an intelligent opponent. T h e o p p o n e n t
9 Whereas the H a m m i n g metric is the n u m b e r of sym- can have one or more of the following pur-
bol differences between two words, the Lee metric is
the s u m of the absolute differences of the symbols: for
poses:
WI = (0, 1, 2) and W2 = (2, 0, 1), H(W~, W2) = 3 and
L(W1, We) = 4. For binary code words the H a m m i n g a) T o determine the message M.
and Lee metrms are identical. b) T o alter the message M to some other
Computing Surveys, Vol I l, No 4, December 1979
Symmetric and Asymmetric Encryption
bO
~.,.-I
,r4
0 o ~
• N
~ 0 r~
~,r5
T
0 -8
U3
6
¢9 0
0 ,~ ,,H PH
e.
oo
0
¢9
0 ¢D
.L
6
¢#
bO -a
4~
4~ ¢q O
•el .,o
~3 r..)
0 o ~ e~
It
4~
o 0
ilJ
•,.O
rd -I~
ra l ~
N % ~e
0
£
t~)q)
Computing Surveys, V o l 11, No. 4, December 1979
314 * Gustavus J. Simmons
message M' and have M' accepted by random n-bit binary number. In this case
the receiver as the message actually every proposed decipherment produces an
sent. acceptable message. When there is no re-
c) To impersonate the transmitter. dundancy in the messages, there is no basis
on which to deduce the authenticity of a
Thwarting a), i.e., ensuring secrecy, is the received cipher. An authentication system
best known purpose of cryptographic sys- must introduce redundancy such that the
tems, but modern data processing systems space of ciphers is partitioned into the im-
with controlled log-in and access to busi- ages (encryptions) of the messages in J4
ness files are greatly concerned with au- and a class of unacceptable ciphers. If au-
thenticating the "transmitter" (thwarting thentication is to be perfect, then the en-
c)) and ensuring the integrity of the re- cryption scheme must consist of a family of
ceived messages (thwarting b)) [FErn73, partitions of the cipher space such that on
HOFF77, LIPT78, MART73]. In many cases learning any message-cipher pair, the op-
the privacy or secrecy of communications ponent who does not know the key will be
is a secondary objective. An intelligent op- unable to do any better than pick a cipher
ponent could easily defeat the fixed strate- at random from the cipher space. In other
gies underlying error detecting codes by words, the objective is to diffuse the unac-
making improbable changes such that the ceptable ciphers throughout the entire
received code words would be interpreted cipher space. This is precisely the opposite
as incorrect messages. Moreover the oppo- of the error defeating code's objective,
nent's task of "breaking" the code is not which is the clustering of the incorrect
difficult because the code space is parti- codes about an acceptable (correct) code.
tioned into spheres, which reduces the Figure 4 is a schematic diagram of the
search. A perfectly secure code is one in abstract encryption/decryption channel.
which each cipher symbol is produced with The parallel with the Shannon coding/de-
equal probability by any message symbol coding channel is apparent. Figure 4 is more
when averaged over all possible keys. Dea- general than the secrecy systems described
vours's example [DEAv77] was not secure by Shannon [SHAN49], Albert [ALBE41], or
because each cipher symbol could have Feistel [FEIs73]; Shannon's and Albert's
been produced by only two message sym- models were concerned only with secrecy,
bols rather than all 26 message symbols. and Feistel's model dealt with a restricted
To be perfectly secure, an encryption form of message authentication. The model
system should randomly map the message of Figure 4 encompasses all the objectives
space onto itself such that the opponent for secure communications. It should be
must consider all points in ~ to be equally noted that a cipher can be encoded to allow
likely candidates for the plaintext cor- for the detection and correction of errors in
responding to the received ciphertext. transmission. This requires that the re-
Whereas a satisfactory "random" number ceiver first decode and correct errors before
generator need not be a good encryption decrypting. In fact, such compound encryp-
function (as we shall see in an example a tion/encoding is routinely used with satel-
little later), a good encryption system is lite communications systems.
necessarily a good random number gener- In encryption/decryption systems, the
ator. In fact, Gait [GAIT77] has used the functions E and D (encryption and decryp-
DES algorithm for random number gener- tion) are assumed known to the opponent.
ation with considerable success. If the system were to depend completely on
As Shannon pointed out [SHAN49], this E and D, the opponent would have suffi-
implies that a perfect encryption scheme is cient information to defeat it. Therefore,
equivalent to a latin square where rows something must be unknown if the oppo-
correspond to messages, entries to keys, nent is to be unable to duplicate the actions
and columns to ciphers. However, a perfect performed by the authorized receiver. The
cryptosystem may be unable to authenti- unknown information is called the crypto-
cate messages. Suppose that ~( is the space graphic key. The authorized receiver can
of all n-bit binary numbers, and that en- use his secret deciphering key K' to decrypt
cryption consists in adding, modulo 2, a the encrypted message.
Computing Surveys, Vol 11, No 4, December 1979
Symmetric and Asymmetric Encryption 315
t~
o ~no
II
'~x~ o
.H v
~o
I~vO
o m
T
0
I.-I
~
~'~
Z
o~
ID
Oo~T ~ II
~°
q)
~×° o
v
~ ~ ~':::: o
~)
m~
C o m p u t i n g S u r v e y s , Vol. 11, No. 4, D e c e m b e r 1979
316 • Gustavus J. Simmons
An encryption system can be described 5. COMPUTATIONAL COMPLEXITY
formally with the help of the message space AND SYMMETRIC
J4, the key spaces 9V and ~V', the cipher ENCRYPTION
space cd, a space d' of mappings from ~ ×
A fundamental change in the practice of
X i n t o ~d, and a related space @ of inverse
cryptography began in the early 1950s. We
mappings. For a particular mapping E from
have already pointed out that a perfectly
~, M from J~, and K from ~ , E(M, K) ffi C
secure cryptosystem requires impractical
is the encipherment of message M by key
quantities of key for most applications. Al-
K. There must be a deciphering function
most all of cryptography has been devoted
DE corresponding to E and a key K' corre- to finding ways of "diffusing" smaller, man-
sponding to K such that messages can be
ageable amounts of uncertainty in order to
uniquely recovered:
approximate longer keys, that is, keys
which appear to have come from a key
M = DE(E(M, K), K')
space with greater uncertainty. This is usu-
= DE(C, K') for all M. (1) ally done with an easily computed function
of an input sequence, the true key, which
By itself (1) does not describe a secure produces as output a much longer sequence,
encryption system. For example, if J4 = cd the pseudokey. The pseudokey is used as K
and E is the identity function, then (1) is in Figure 4.
trivially satisfied with C = M for all M; If such a procedure is to be cryptosecure,
obviously there is no cryptosecurity for any it must be infeasible to invert the function
choice of K. Shannon [SHAN49] defines a to recover the true key from the pseudokey;
secrecy system E to be perfect (uncondi- that is, it must be intractable to compute
tionally secure) if an opponent knowing E the future output of the function even
and arbitrarily much cipher C is still left though the function itself is known and
with a choice from among all possible mes- lengthy observations of the output are
sages M from ~ . For this to be true, there available. From World War II until the
must be as many keys as there are mes- early 1950s these objectives were met on an
sages. Moreover the uncertainty about the ad hoc basis through the intuitive judgment
key K must be essential: The opponent's of cryptosystem designers. However, elec-
uncertainty about messages must be at tronic computing and the theory of com-
least as great as his uncertainty about the putational complexity transformed the idea
key. In Shannon's model ) i f - 9(' and ~ - of "diffusing" a limited amount of uncer-
9, and only objective a), secrecy, is consid- tainty into an analytical design question.
ered. Under these constraints, E is a map- In Figure 4 the key spaces ~f and
ping from the message space J4 into the represent the equivocation to the opponent
cipher space cd, and D is E -l, the inverse of the system at any given stage in its
function to E; the key K then acts as an operation. For example, in an English al-
index for a pair (E, D). Perfect security is phabet one-time pad of n equally likely
achieved by having one key for each possi- symbols, [ 3if] ffi 26n; each point in 3Krepre-
ble (E, D) pair. Contemporary cryptosys- sents about log2(26)n = 4.7n bits of infor-
terns seldom realize this level of uncondi- mation, and so a 1000-symbol one-time
tional security. In fact, most of current "key" would be represented as a point in a
cryptology deals with systems which are binary space of 24700 possible sequences.
secure in the sense that exploiting the avail- Because keys are as voluminous as the mes-
able information is computationally infeas- sages they secure, one-time keys are im-
ible; but these systems are not uncondition- practical for large-volume communications.
ally secure in Shannon's sense. The impor- In the early 1950s cryptologists recognized
tant exceptions include the Washington- that if a (true) key K from a smaller dimen-
Moscow hot line and various high-level sional key space ~ w a s used to generate a
command circuits. In the remainder of this much longer (pseudo) k e y / ~ using an algo-
paper, we are concerned with computation- rithm whose inversion was sufficiently com-
ally secure systems, but not unconditionally plex computationally, then the cryptanalyst
secure ones. would be unable to compute either K or/~.
ComputingSurveys,Vol 11,No 4, December1979
Symmetric and Asymmetric Encryption • 317
shift register
code
Feedback Network
FIGURE 5 t Exc|uslve OR.
Modern cryptology rests largely on the im- the feedback polynomial, and the starting
plementation of this principle. state of the register serve as the key.
In terms of Figure 4, the "diffusing" of Assuming that the cryptanalyst can by
uncertainty is defined by this condition: For some means, such as probable word analy-
nearly all encryption/decryption pairs sis, recover bits of the cipher (which need
(E, D) and keys K and K', it is computa- not be consecutive), he can set up and solve
tionally infeasible to compute K (or K') a system of at most 2n linear equations
from a knowledge of E, D, C, and M. A with which to duplicate the future output
system in which either K -- K' or one of K of the original sequence generator. Berle-
and K' is easily computed from knowledge kamp [BERL68] and Massey [MAss69] have
of the other is called a symmetric system. found efficient algorithms for doing this in
All the examples in the introduction are at most 2n steps. Thus the problem of find-
of symmetric systems. For a one-time key, ing K is only of linear complexity (in n);
the two communicants must each have a hence K is not well concealed despite the
copy of the same key; K = K' in this case. apparently large number of possible feed-
Similarly, the simple Vigen~re and Ver- back functions. A more complete descrip-
nam-Vigen~re systems both have K =- K'. tion of LFSRs is given in the appendix.
On the other hand, in the Hill linear trans- Another proposed mode of crypto use for
formation system, described in Section 1, LFSRs is for block ciphers: The register is
the receiver must have E -1, not E, although loaded with an n-bit block of plaintext, it is
it is easy to compute E -1 from a knowledge stepped for k :> n steps, and the resulting
of E. register state is taken as the cipher. Figure
Maximal length linear feedback shift reg- 6 shows an example of the state diagram
isters (LFSRs), which are used for error for such an LFSR. Using k ffi 7, for example,
detecting and correcting codes, illustrate the message 00001 encrypts to 11010. To
that one must take great care in choosing decrypt, one uses the "inverse feedback
key functions. Some apparently complex function," which reverses the stepping or-
functions are not so. Because the (2" - 1)- der of the state diagram of Figure 6, when
bit sequence from a maximal length LFSR a 00001 would be the register state resulting
satisfies many tests for randomness, e.g., from stepping the register seven steps from
the runs property [GoLo67] and lack of the starting point (cipher) of 11010. In this
intersymbol correlation up to the register example K (forward stepping) and K' (re-
length n, numerous suggestions have been verse stepping) are easily computable from
made to use these sequences either as key each other. Although the output is suffi-
in a Vernam-Vigen~re stream cipher mode, ciently random to be useful as a pseudo-
as shown in Figure 5, or as block encryption random bit sequence generator, the inver-
devices on n-bit blocks of message bits sion to find K' or K is only of linear com-
[BRIG76, GEFF73, GOLO67, MEYE72]. The putational complexity.
feedback network, i.e., the coefficients of The National Bureau of Standards Data
Computing Surveys, Vol. 11, No. 4, December 1979
Gustavus J. Simmons
11010
9 2 ~
FIGURE 6
Encryption Standard (DES) provides a provide "diffusion"). There is considerable
widely recognized example of a symmetric controversy H about the cryptosecurity of
encryption/decryption whose keys are well the DES [DIFF77, MoRn77] centering on
concealed by computational complexity. the possible brute force attack of a system
Roberts [ROBE75] states that by enumerating all the keys for the present
56-bit key; yet no one has proposed an
The algorithm is designed to encipher and
decipher blocks of data consisting of 64 bits inversion of the encryption function itself,
under control of a 64-bit key. ~° Deciphering which thus far appears to be as computa-
must be accomplished by using the same key tionally complex as its designers believed it
as for enciphering, but with the schedule of to be.
addressing the key bits altered so that the
deciphering process is the reverse of the en- 6. COMPUTATIONAL COMPLEXITY AND
ciphering process. A block to be enciphered ASYMMETRIC ENCRYPTION
is subjected to an initial permutation IP, then
to a complex key-dependent computation and In symmetric cryptosystems, the keys at
finally to a permutation which is the inverse the transmitter and receiver, K and K',
of the initial permutation IP -~. respectively, either are the same or can be
This shows clearly that the system is sym- easily computed from each other. We now
consider cryptosystems in which this is not
metric. It indicates that the "complex key-
the case. There are three possibilities.
dependent computation" conceals the key.
The encryption function used in the DES a) Forward asymmetric: The receiver's
is known as a product cipher [MORR77]; it
comprises 16 successive repetitions of a
nonlinear substitution (to provide "confu-
sion") alternating with permutations (to ~T h e controversy is centered on HeUman's accusation
t h a t the National Security Agency has deliberately
chosen the D E S key to be of a size that it can break.
T h e pros [HELL79a, DAvI79] and cons [TvcrI79,
BRAN79] of this a r g u m e n t are summarized In the
io Actually only 56 bits rather t h a n the stated 64, since recent editorial debate In the IEEE Spectrum
8 bits are used for a parity check [SUGA79]
Computing Surveys, Vol 11, No 4, December 1979
Symmetric and Asymmetric Encryption • 319
key (K') cannot easily be computed keys (K, K') such that
given the transmitter's key (K).
b) Backward asymmetric: The transmit- DE(E(M, K ) , K ' ) -- M .
ter's key (K) cannot easily be computed 3) The encryption and decryption func-
given the receiver's key (K'). tions, E and D are implemented by fast
c) Bidirectional asymmetric: Neither K algorithms.
nor K' can be computed given the 4) At least one of the keys (K and K') is
other. concealed from a knowledge of the other
As usual, the enemy is assumed to know E, key by a computationally complex problem.
D, M, and C. The term "asymmetric sys- 5) For almost all messages it must be
tem" refers to all three cases. infeasible to find cipher/key pairs that yield
The primary applications of (bidirec- that message. That is, the opponent is
tional) asymmetric encryption systems de- forced to find the "true" (M, K) that en-
rive from these two properties: crypted to the cipher C at hand.
1) Secure (i.e., secret) communication is These conditions differ slightly from
possible even if the transmitter's key is those imposed on public-key cryptosystems
compromised. [DIFF76]. Condition 1) is the basic require-
2) Authentication of the transmitter (mes- ment for a practical privacy system; we
sage) is possible even if the receiver's state it explicitly to exhibit one of the two
key is compromised. places in the abstract encryption channel
where computational complexity is essen-
Note that 1) applies to the forward asym- tial. The public-key cryptosystem was for-
metric encryption system and 2) to the mulated as a two-way communications
backward encryption system. channel by its inventors, so that the keys
Whereas symmetric cryptosystems have are interchangeable: E(DE(M, K'), K) = M
been in use for many years, asymmetric = D(E(M, K), K')[ADLE78, HELL78]. Con-
encryption systems are a recent develop- dition 5) enables detecting deception: The
ment in cryptography. In 1976 Diffie and opponent cannot easily find alternate keys
Hellman [DIFF76] published a conceptual giving the same ciphertext [GraB74].
scheme for this kind of cryptosystem, which As of 1979, no one had exhibited func-
they called a public-key cryptosystem be- tions that provably satisfied these condi-
cause no pair of potential communicants tions. The working approach toward con-
had to exchange a key secretly in advance. structing such functions has been to take
It is essential, however, that the key ex- some problem, known or believed to be
change be secure, so that the communicants exceedingly complex, and make the "ob-
can be confident of the keys' owners-- vious" method of finding the keys equiva-
otherwise authentication is not possible. lent to solving the hard problem. Examples
Merkle [MERK78a] contemporaneously dis- of hard problems are factoring a product of
covered a related principle that allows the very large prime factors, the general knap-
communicants to exchange a key with work sack problem, and finding the logarithm of
O (n), while requiring the opponent to face an element in a large field with respect to
work O (n 2) to determine the key from mon- a primitive element. What is hoped for in
itoring the communicants' exchange. Mer- such a scheme is that the converse is also
kle discovered a forward asymmetric en- true; i.e., decryption is equivalent to solving
cryption system. the hard problem. The first results toward
In terms of Figure 4, these conditions this crucial step in "proving" the cryptose-
must be satisfied by an asymmetric encryp- curity of any asymmetric system were ob-
tion scheme: tained by Rabin [RAm79] and Williams
[WILL79b]; they showed that the factori-
1) The keys are concealed by a compu- zation problem for large moduli is equiva-
tationally complex problem from the plain- lent to decryption for almost all ciphers in
text and cipher. Rabin's encryption scheme. We will return
2) It is easy to compute matched pairs of to this point later.
Computing Surveys, Vol II, No. 4, December 1979
320 • Gustavus J. S i m m o n s
6.1 The Knapsack Trapdoor problem can be for special w. An encryp-
tion system based on such a simple w would
One of the best known proposals for a for-
ward asymmetric system was made by Mer- not be secure.
Merkle and Hellman defined two special
kle and Hellman [MERK78b], who sug-
classes of vectors w, which they call trap-
gested basing asymmetric encryption on
door knapsacks; with a trapdoor knapsack
the knapsack (or subset sum) problem. T h e
the designer can easily compute the subset
knapsack problem is to determine whether
vector s, while the opponent is faced with
a weight S can be realized as the sum of
solving a h a r d (O (2n/2)?) problem. T h e sim-
some subset of a given collection of n
plest scheme is an "additive trapdoor knap-
weights w,--i.e., to determine w h e t h e r
sack," in which the designer starts with any
there exists a binary vector s for which S
strictly dominating weight vector w con-
ffi s • w. ~2 Without restrictions on w , so-
taining n weights, as described above, and
lutions need not exist or there m a y be sev-
eral. For example, S ffi 515 has three solu- derives a related weight vector v, which is
believed to be a h a r d knapsack. This is
tions, while S ffi 516 has no solution in the
done by choosing a modulus n and a mul-
10-weight knapsack appearing in Hellman's
tiplier e which is relatively prime with re-
paper [HELL78]J 3 T h e time to verify
spect to n, and t h e n computing the n
whether a given vector s is a solution is
weights v~ of v by the rule ew, =-- v~
O(n). In contrast, the time needed to find
(mod m). Since e is relatively prime with
a solution vector s is believed to be of
exponential complexity. Horowitz and respect to m, there exists a d, easily com-
p u t e d using the Euclidean algorithm, such
Sahni [HORo74] have published a search
t h a t ed - 1 (mod n). T h e n u m b e r s d and m
algorithm for the knapsack problem requir-
ing O (2n/2) time and 0 ( 2 n/2) memory; and are the receiving key K', and the " h a r d "
knapsack weight vector v is the transmit-
more recently Schroeppel and S h a m i r
ting key K. A binary message is broken into
[ScHR79] have devised an algorithm of the
same time complexity but requiring only n-bit blocks. E a c h n-bit block becomes a
vector s for the knapsack problem: the
0 ( 2 n/4) memory. T h e knapsack problem is
transmitter computes the cipher S' -- s • v.
an NP-complete problem [KARP72].
Since the cryptanalyst only knows S' and
It is important to r e m e m b e r t h a t the
v, he is forced to solve the knapsack prob-
computational complexity of NP-complete
lem for v. T h e authorized receiver, how-
problems is measured by the difficulty of
ever, computes dS' - S (mod m); he t h e n
solving the worst cases, whereas cryptose-
solves the simple knapsack (S, w) in O (n)
curity is measured by the expected diffi-
time because w is of the dominating form.
culty over all members of the class. Sup-
If m is chosen to strictly dominate the sum
pose, for example, t h a t the knapsack vector
of all the weights, t h e n the computations
w is chosen with the w, in strict dominance,
m a y be done in integer arithmetic as well
i.e., w~ > ~=~ w~. In this cage s can either
as in the modular arithmetic.
be found or shown not to exist in at most n
T o further illustrate this simple trapdoor
subtractions: st ~- 1 if and only if S - S,-~
knapsack, use the easy knapsack weight
_ w,, where S,-~ is the partial sum of the
vector w = (1, 2, 4, 8); choose m -- 17 > 1
first i - 1 components of the dot product.
+ 2 + 4 + 8 = 15 a n d e - - 5. T h e n d = 7 a n d
Another example is w, = 2 '-~, in which case
v ~- (5, 10, 3, 6). In this system the subset
the problem reduces to finding the binary
vector s = (0, 1, 0, 1) would be transmitted
representation of 0 _< S _< 2n - 1. B o t h these
as S' = s ° v -~ 16. T h e receiver finds S =
examples illustrate how simple a knapsack
7 . 1 6 = 10 (mod 17); since he also knows w,
the authorized receiver can solve for s in
three subtractions. T h e same principles ap-
~2 I f s = ( S l , s.) a n d w = (w~, ., w.), t h e n t h e
,
d o t p r o d u c t s . w = ~ , ~ s,w, T h e v e c t o r s. w h e r e ply to realistic implementations, which use
s, = 0 or 1 s u c h t h a t S = s . w , s e l e c t s s o m e of t h e n = 100 or larger.
" o b j e c t s " to fill a " k n a p s a c k " of c a p a c i t y S Note t h a t it has not yet been proved t h a t
L3w = (14, 28, 56, 82, 90, 132, 197, 284, 3 4 1 , 4 5 5 ) , a n d
s = ( 1 0 0 i l l 1 0 0 0 ) , (0110100010), or (1100010010) for the modular derivation of v from the easy
S = 515 knapsack w results in a h a r d knapsack.
Computing Surveys, Vol ll, No 4, December 1979
Symmetric and Asymmetric Eneryption • 321
Shamir and Zippel [SHAM78] have shown party is in possession of the information
t h a t if the opponent knows m as well as v, which could compromise the system.
he can employ a simple algorithm whose A message M ~ ~ is e n c r y p t e d in this
o u t p u t is w with high probability. system to the cipher C b y the transmitter
using key K = (e, n) by the rule
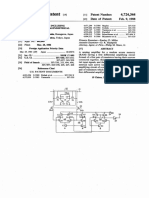
6.2 The Factorization Trapdoor
M e-=C (modn),
Another asymmetric system is the public-
and C is decrypted by the authorized re-
key encryption scheme proposed by Rivest,
ceiver using K = (d, n) by the rule
Shamir, and Adleman [RIVE78]. T h e trap-
door in the scheme is based on the differ- C e~M (modn).
ence in computational difficulty in finding For example, if p = 421 and q = 577 so
large primes as opposed to factoring large t h a t n = p q = 242,917 and ¢p(n) = 241,920,
numbers. T h e best algorithms known at the t h e n for e = 101, d = 9581. Using these
present can find a d-digit prime n u m b e r in values K = (101:242,917) and K' = (9581:
time O (d3), while the complexity of factor- 242,917) so t h a t the message M = 153,190
ing a large n u m b e r n exceeds any polyno- encrypts by
mial bound, currently O (n (l"(l",)/1,,)~/2). In
the proposed system, one chooses a pair of C = 153,1901°1 -- 203,272 (mod 242,917),
primes p and q so large t h a t factoring n = and C decrypts by
p q is beyond all projected computational
capabilities. One also chooses a pair of num- M-- 203,272°~' -= 153,190 (mod242,917).
bers e and d, where (e, q~(n)) = 1, '4 and e d Much effort has been devoted to the in-
-= 1 mod q0(n); q0(n) = ( p - 1)(q - 1). In vestigation of whether the scheme just de-
other words, e and d are multiplicative in- scribed is secure and whether decryption
verses in the group of residue classes mod- (for almost all ciphers) is as hard as the
ulo ¢p(n). When used as a public-key cryp- factorization ofn. Several authors [HERL78,
tosystem, e and n are published in the SIMM77, WILL79a] have investigated the
public-key directory and d is kept secret. restrictions on the p r i m e s p and q t h a t must
Because the receiver (designer) knows p be imposed to ensure cryptosecurity; t h e y
and q, the system is forward asymmetric. conclude t h a t it is not difficult to choose
A variant of this scheme illustrates a the primes so t h a t the known cryptoweak-
bidirectional asymmetric encryption sys- nesses are avoided [WILL79a]. It is probable
tem. Assume t h a t a higher level of com- t h a t these same steps are also sufficient to
mand designs the system, e.g., choosesp, q, ensure t h a t decryption of almost all ciphers
and e, computes d, and then gives (e, n) is as hard as the factorization of n. How-
and (d, n) to two subordinate commands ever, this crucial result has not been proved.
that require an asymmetric encryption Instead, Rabin [RAm79] has shown t h a t if
channel between them. Since computing instead of the encryption function C -- M e
the multiplicative inverse d of e from a one uses
knowledge of e and n is essentially the same
as factoring n or determining q~(n), d is C--M(M+b) (modn), b>_0,
secure from an opponent knowing only n which is effectively the same as e = 2 where
and e. Conversely, computing e from a
n = p q , as in the Rivest et al. scheme, t h e n
knowledge of d and n is of the same diffi-
decryption to an unauthorized user is not
culty. T h e two keys (e, n) and (d, n) are
simply a consequence of being able to factor
separated by a computationally difficult
n but is actually equivalent. Unfortunately,
problem. Obviously, the "higher level of
even the authorized user is left with an
c o m m a n d " can be replaced by a volatile
ambiguity among four potential messages
m e m o r y computing device so that no single
in this scheme. Williams has completed this
work by proving t h a t for suitably chosen
,4 q~(n) m t h e E u l e r t o t i e n t ; i t is s i m p l y t h e n u m b e r of primes p and q the ambiguity is removed
integers less than n and relatwely prime with respect
to n. (e, q~(n)) = 1 Is a n o t a t i o n m d m a t l n g t h a t e a n d and t h a t decryption of almost all messages
q~(n) are r e l a t i v e l y pmme. is equivalent to factoring n [ W I L L 7 9 b ] .
Computing Surveys, Vol. 11, No 4, December 1979
322 • Gustavus J. S~mmons
(Ron Rivest has pointed out that this state- cerns of the transmitter and receiver: The
ment is precisely true for ciphertext-only transmitter wishes assurances that the mes-
attack and that it does not hold for chosen- sage cannot be disclosed or altered, whereas
plaintext attack [BRIG77].) the receiver is primarily concerned that the
For example, using the same primes and message could only have come from the
message as above in the simple Rabin transmitter.
scheme, p = 421, q -- 577, and M = 153,190, The different security concerns of trans-
and letting b = 0, one obtains the cipher mitter and receiver are well illustrated by
C = 153,1902 -- 179,315 (mod 242,917). the concerns of the various parties involved
in a transaction by check. The person writ-
Four messages from d4 have C as their ing the check (the transmitter) is not con-
square mod n: M, of course, and - M = cerned with its authenticity, but he is con-
089,727, as well as M' = 022,788 and - M ' cerned that no one will be able to alter the
= 220,129. amount shown on his signed draft. The
The important point is that these results person accepting the check (the receiver) is
are persuasive evidence of equivalence be- primarily concerned with the authenticity
tween decryption for almost all messages of the check. An intermediate party accept-
and the factorization of n in these schemes. ing the check as a second-party draft is
A common misconception is that asym- concerned with both of these aspects: that
metric encryption/decryption (public-key the check is unaltered and authentic. The
encryption) is more secure than its (sym- ultimate receiver, the bank, keeps signature
metric) predecessors. For example, Gardner cards on file to help verify (if needed) the
[GARD77] suggests that public-key crypto- identity of the person who wrote the check,
systems are more cryptosecure than exist- but its concerns are the same as those of
ing systems, and a lengthy editorial in the the other intermediate receivers.
Washington Post, July 9, 1978, was entitled Authentication is closely related to error
"The New Unbreakable Codes--Will They detecting codes. The message J¢ is parti-
Put NSA Out of Business?" [SHAP78]. The tioned into two classes, acceptable and un-
discussion in the two previous sections on acceptable messages, similar to the classes
symmetric and asymmetric encryption comprising the most probably correct and
demonstrates clearly that asymmetric cryp- incorrect messages in the previous case. To
tosecurity depends on precisely the same realize authentication despite an intelligent
mathematical condition as most high-qual- opponent, it is essential to conceal these
ity symmetric cryptosystems--computa- classes in the ciphers. Using an uncondi-
tional work factor. Basing cryptosystems tionally secure cryptosystem to encrypt the
on NP-hard problems opens new worlds of messages from J4 into ciphers from ~d,every
codes which may be as secure as traditional cipher C E ~d would with equiprobability
codes. But the new systems are not neces- over ~ be the encryption of any message
sarily more or less secure than existing in J4. But in this ideal case, if the opponent
cryptosystems. substituted another cipher C' for the
correct cipher C, the probability that it
7. AUTHENTICATION would decrypt to a message in the class of
The asymmetric encryption channel serves acceptable messages would be simply
two functions: Id l / IJ4 I, where d i s the class of acceptable
1) Secret communication is possible even messages. For example, i f ~ is the set of 264
if the transmitter's key (K) is public. -- 456,976 four-letter alphabetic sequences
2) Authentication of messages is possible and d is the set of four-letter English words
by anyone who knows the receiver's key in Webster' s Unabridged International
(K'), assuming that K and K' are not Dictionary, then the probability that a ran-
easily computed from each other. domly chosen four-letter cipher will decrypt
to an English word is very close to 1/7. In
The separation of secrecy and authentica- other words, the equivocation to the oppo-
tion in asymmetric systems has a natural nent of this "natural" authentication sys-
counterpart in the different security con- tem is =2.81 bits.
Computing Surveys, Vol 11, No 4, December 1979
Symmetric and Asymmetric Encryption • 323
The point is that authentication is only It has been argued that since M, CA, and
achievable by introducing redundancy into C are all the same length, say k bits, there
the message--exactly as is done to achieve is no apparent redundancy, as is required
an error detecting or correcting capability. for authentication. But this is not true:
Simply having the required level of redun- Suppose that M were perfectly encoded,
dancy is not sufficient. The redundancy i.e., a random (equiprobable) k-bit binary
must be diffused throughout the cipher, lest number. Now the observer has no way of
the signature information be separated rejecting any k-bit number as not having
from the proper message and appended to been originated by A. A must therefore
another message. include in M identifiers, such as his name
The bidirectional public-key encryption or ID number, time of day, or transaction
system proposed by Rivest, Shamir, and number, which serve only to distinguish
Adleman can be used by two subscribers, A acceptable from unacceptable messages.
and B, as a means of authenticating (sign- The security of the authenticator is still
ing} messages. Assume that A wishes to measured by the degree of signature redun-
send a message M to B; B must later be dancy introduced.
able to prove to a third party {observer or Authentication is possible using either
judge) that M originated with A. For ex- symmetric or asymmetric channels. We
ample, A is ordering B (his broker) to make noted earlier that with DES, a symmetric
a large stock sale which B fears A may block ciphering system, messages can be
disavow if the market value of the stock authenticated using Feistel's block chaining
should increase. A has entered his public- [FEIs73] technique. In this approach suc-
key (eA, nA) into the public directory. Sim- cessive blocks of 56 bits of the text are used
ilarly B has entered (es, riB). A computes as keys to successively encrypt the ciphers
from the preceding step, with one 56-bit
M dA=-CA (modnn) initial key unknown to the opponent. The
using his secret key (dn, hA) and then com- resulting cipher is a "function" of every bit
putes in the message and is resistant to inversion
even against a known plaintext attack. The
CAe B = C (modnB) appended authenticator must match an
using B's public key. This cipher can only "acceptable" message, usually in a natural
be decrypted by B; A is therefore assured language to be accepted.
of the secrecy of his message. On receiving The unique feature of asymmetric en-
C, B computes cryption systems for authentication is that
a receiver can decrypt but not encrypt; one
C dB -= CA (mod nB) terminal of the communications link can be
using his secret key and saves CA as his intentionally exposed without compromis-
"signed" version of the message. He then ing the other terminal. This is not possible
computes in a symmetric system.
CAeA----M (mod nA)
8. SECURE COMMUNICATIONS
using A's public key. Since this later step
Despite the different concerns of the trans-
can be duplicated by any observer given CA
mitter, the receiver, or the intermediary in
by using A's public information, the claim
authentication, the objective is always an
is that M could only have come from AJ 5 authentication system whose cryptosecur-
ity is equivalent to the security of the trans-
~ T h e r e is a significant difference between digital sig- mitter's encryption key. This means that
n a t u r e s a n d a mgnature to a d o c u m e n t . Once t h e signer the transmitter can purposely introduce re-
affixes his signature to a d o c u m e n t , t h e r e is n o t h i n g dundancy in such forms as message identi-
he can do t h a t will interfere with t h e future verification
of t h e a u t h e n t m l t y of t h e signature. In t h e digital fiers prior to encryption, or else he can
signature s c h e m e described above, however, A can depend on redundancy inherent in the mes-
dehberately expose hm secret key dA a n d t h e r e b y m a k e
t h e authenticity of all digital signatures a t t n b u t e d to sage format or language to allow the au-
h i m questionable thorized receiver to reject bogus messages.
Computing Surveys, Vol. II, No 4, December 1979
324 • Gustavus J. Simmons
The cryptosystem may be either symmetric incorrectly--that there is no key distribu-
if all communications terminals are secure, tion problem for public-key systems.
or asymmetric if one of the communications Class III is an unusual communications
terminals is at a physically unsecured site. system that could not exist in a symmetric
There are four possible combinations of cryptosystem. In a system of this type, mes-
security concerns. They are listed in Table sage and transmitter authentication is re-
3. Each corresponds to a class of real com- quired, but secrecy cannot be tolerated. We
munications systems. call this a signature channel. An applica-
tion of this channel for treaty verification
TABLE 3 has been developed at Sandia Laboratories
Class Message~Transmitter [SIMM79].
Authent~catmn Secrecy Assume that the United States and the
I No No Soviet Union sign a comprehensive test ban
II No Yes treaty in which each party agrees to stop
III Yes No all underground testing of nuclear weapons.
IV Yes Yes Each side wishes to verify that the other is
complying, that is, is not surreptitiously
Class I corresponds to normal, nonsecure carrying out underground tests. One of the
communications. We call this the public most reliable techniques for detecting un-
channel. derground tests uses medium-distance
Class II is the classical case of secret or seismic observatories that measure the
private communications. We call this the ground motions resulting from an under-
private channel. This channel is realizable ground detonation. These techniques are
with symmetric or asymmetric techniques. highly reliable; either nation could have
In the symmetric case a compromise of the confidence in the output message from
key at either end of the communications seismic instruments suitably located in the
channel precludes all further secret com- host (other) nation's territory. It is not dif-
munications. In a forward asymmetric sys- ficult to secure the instruments physically
tem secret communications are still possi- in subsurface emplacements; only the data
ble even if the transmitter's key is public. stream sent through an open communica-
The necessity for communicants' using tions channel is subject to attack. If the
symmetric systems to provide a secure way host nation could successfully substitute
to exchange keys in advance is a severe innocuous seismic records for the incrimi-
restriction. A commercial cryptonet, for ex- nating records of underground tests, it
ample, could have many thousands of sub- could cheat undetected. This problem is
scribers, any pair of whom might wish to solvable using either symmetric or asym-
communicate. Clearly the number of keys metric encryption techniques. The receiver
to support symmetric encryption would be (nation to which the seismic installation
unmanageable. In a forward asymmetric belongs) need only encrypt the seismic data
encryption system, however, a subscriber S, along with as many identifiers--station ID
could publish his encryption pair E, and K, number, date, or clocks--as might be
in a public directory. Anyone wishing to needed for authentication. This method of
communicate a secret message M to S, in authentication is as secure as the encryp-
secrecy transmits E~(M, K~), which can only tion system used to produce the cipher.
be deciphered by S~. It is this application However this solution would almost cer-
that led to the name "public-key cryptosys- tainly be unacceptable to the host nation
tern." It is essential, however, that the (in whose territory the seismic observatory
transmitter be certain that E, and K, are is placed), which would be ignorant of the
the key entries for S,: In other words, while contents of the enciphered messages; it
a secret exchange of keys is no longer (in would fear that the cipher contains infor-
an asymmetric system as opposed to a sym- mation other than the agreed-upon seismic
metric one) needed, an authenticated ex- data. If the host nation were given the key
change of keys is still required! This is an to a symmetric encryption system (so that
important point since it is frequently said-- it could decrypt the cipher and verify the
Computing Surveys. Vol I l, No 4, December 1979
Symmetric and A s y m m e t r w Encryption ° 325
message content), it would also, by defini- would like to be certain that no one can
tion, be able to generate counterfeit ciphers. wiretap the communication link while he is
A compromise solution is to form an au- authenticating himself and then later be
thenticator much shorter than the entire able to impersonate him to the bank's com-
message; the authenticator depends on all puter or to the CPU. Secure log-in com-
of the symbols in the message through some puter systems require the user to identify
hashing function. The authenticator is also himself before granting him access to the
encrypted. (The block chaining technique operating computer system [HOFF77,
was implemented in such a solution in the MART73], but these systems may be com-
late 1960s for a similar application.) The plex. Many low-security systems simply
shorter authenticator (cipher) is of course store all user numbers and the correspond-
still inscrutable to the host nation, but its ing passwords in a file normally inaccessible
smaller size means that less information to users. Anyone gaining (illegal) access to
could be concealed in each transmission. this file could then impersonate any system
Periodically, the hashing algorithm and key user. The most common defense is the one-
could be changed; the hashing algorithm way cipher [EvAN74, PtJRD74, WILK68],
and key used in the previous period would which does not store the user's password
be given to the host, which could then W~, but rather a function E(WJ, where E is
verify that the authenticators had not con- chosen to be computationaUy infeasible to
cealed unauthorized information in the pre- invert. Anyone gaining access to the pass-
vious period. After satisfying itself that the word file would know E ( W J for all the
system had not been misused, the host authorized users but would be unable to
would renew the license to operate for one determine any W, and hence unable to im-
more period. This compromise is not com- personate any user. Obviously, there are
pletely satisfying to both parties because requirements other than the difficulty of
the host nation still must trust the other inverting E; for instance, the file can con-
nation not to begin concealing information tain only a vanishingly small fraction of the
in the current authenticators. total number of possible passwords; other-
The problem can be solved completely wise the opponent could simply choose a
with either a forward or a bidirectional random collection of W~, form the corre-
asymmetric encryption system. The mes- sponding E(W,), and if a match were found
sage M and the cipher E(M, K) are given in the file, use that identity. This type of
to the host nation, which has already been system has generally been adopted by the
given DE and K', but not K. The host would banking industry for "window identifica-
compare DE(E(M, K), K') with the pur- tion" of passcard holders for savings ac-
ported message M. If the two agree, the counts.
host is assured of the content of the mes- The requirement for a full-fledged secure
sage. The other nation also compares channel arises with the brokerage house
DE(E(M, K), K') and M to determine if the that responds to either a very large buy or
message is authentic. sell order. The house wants the highest
Class IV is typified by commercial trans- possible level of secrecy concerning the de-
actions in which it is essential to be certain tails of the order lest it disturb the market.
both that the message came from the pur- The house also wants full authentication of
ported transmitter and that it has not been the giver of the order. Private commercial
altered in transmission--and also to ensure codes were once used for precisely these
that outsiders are not privy to the commu- purposes; these codes, however, provide lit-
nication. Since all the secure communica- tle cryptosecurity.
tions objectives are met in such a system, As further illustration of the require-
we call this the secure channel. ments on secure channels, consider a mili-
There are many business applications in tary commander who sends scouting pa-
which a secure channel is desirable, for trols into enemy territory. A two-way radio
example, the remote automatic bank teller communication link exists between each
or the control of access to a computer's patrol and the command post, and all the
unsecured data files. In these cases the user patrols use the same asymmetric system.
Computing Surveys, Vo|. II, No. 4, December |979
326 • Gustavus J. Simmons
Before the mission is completed, some of Ks), KA) = EB(EA(M, KA), Ks). If A wishes
the patrols may have been captured and to communicate a message M to B in se-
their cryptosystems divulged. Communica- crecy where no advance arrangements such
tion from the uncompromised patrols to as key distribution or public-key disclosure
headquarters remains secret because only have been made, A chooses EA, DA, and KA
the transmitter's key has been compro- and KA'. He then transmits the cipher
mised. Moreover, the enemy cannot imper- EA(M, KA) to B, who cannot decrypt the
sonate the commander's messages because cipher. Now B chooses EB, DB, and KB and
it knows only a receiver's key. KB' from the family of commutative en-
Now, suppose that a hybrid cryptosystem cryption functions and transmits the cipher
is used. The first communication over the Es(EA(M, KA), Ks) to A. A computes
asymmetric channel from a patrol to the DA(Es(EA(M, KA), Ks), KA'), which reduces
commander could be a key, for example, a to EB(M, KB) because DA "undoes" EA.
56-bit random number for the DES sym- Then A relays this cipher back to B, who
metric cryptosystem. This communication computes DB(EB(M, Ks), KB') to recover
is in secret since only the transmitter key M. On the surface it appears that an im-
could have been compromised for this possible result has been accomplished be-
channel. Thereafter the commander and cause the keys were kept secret all through
patrol can engage in a secure two-way com- the exchange. In fact, A has communicated
munication over the symmetric channel us- in secret to whomever responded to his
ing the new "session" key. This is not pos- original transmission of the cipher
sible using the asymmetric system alone EA(M, KA), but A cannot establish the iden-
because the commander's ciphers may be tity of his receiver. In other words, A can
legible to the enemy. This system is not only be certain that he has a private com-
foolproof, however, because the com- munication with an unknown party.
mander has no way to authenticate the Perhaps the most intriguing example of
patrol initiating the communication. Some this paradox of initiating secret communi-
other concealed information, such as a sign cations between two parties who cannot
or countersign, could be used, but this ad- establish each other's identities occurs in
ditional information would be considered Shamir, Rivest, and Adleman's protocol for
to be a part of the key according to the playing mental poker [SHAM79]. In this
strict definition given earlier and hence case the names of the cards are encrypted
may have been divulged to the enemy. by player A and the resulting ciphers
The foregoing discussion assumes that passed to B who chooses a random subset
the sender and receiver are sure of each (deal), etc., to relay to B using a commu-
other's identity and keys--for example, a tative encryption function as described in
higher level commander has generated the the preceding paragraph. The resulting
keys, or each user has generated his own game is self-consistent in the sense that the
pair of keys. Needham and Schroeder players can verify that a game of poker is
[NEED78] have shown that the secure dis- being played fairly--but with an unknown
tribution of keys is essential to cryptose- opponent.
curity and is the same for symmetric and The point of the preceding three para-
asymmetric systems. The following exam- graphs is to illustrate an essential point
ple illustrates the possibility that com- about asymmetric encryption systems. It ts
pletely anonymous communicants can en- not true that "in a public-key cryptosys-
ter into a private conversation. Let o~ be a tem 17 there is no need of a secure channel
class of commutative encryption func-
tions, 16 i.e., EA, Es E 8 implies EA(Es(M, relays (M e)d (also m GF(2 127)), whmh A then raises to
the e - I power to get M d = ( ( M e)d ,,~t,
' ) e - 1 , which Is retrans-
mttted to B who computes ( M ) ' to o b t a m M. An
~6An example of a commutative cryptosystem m a o p p o n e n t will have seen M e, M", and (M'T I and will
variant of the P o h h g - H e l l m a n log-antilog scheme know the s p a c e , tO, so he is faced with the "known
over large finite fields [PoHL78] L e t . g = {GF(2127)/ plalntext" decryptlon problem with the twmt that he
{0, 1} } be the message space known to everyone. A knows two messages w h m h encrypt to a c o m m o n
selects an exponent 2 _< e ~ 2127 - 2 and encrypts M as cipher.
M e m GF(21~). B chooses an exponent d similarly and 17 Read asymmetric cryptosystem
Computing Surveys, Vol 11, No 4, December 1979
Symmetric a n d Asymmetric Encryption • 327
for the distribution of keys" [HELL79b]. putational cryptosecurity. An essential dif-
What is true is that whereas the secure key ference between symmetric and asymmet-
distribution system must be able to certify ric cryptosystems is that one of the trans-
the secrecy of the delivered key for use in mitter or receiver keys can be compromised
symmetric systems, it need only be able to in the asymmetric system with some secure
certify the authenticity of the key for asym- communications still possible. In some in-
metric systems. There is implicit in this stances, such as the public-key cryptosys-
statement a distinction between a passive tem, the exposure may be deliberate; in
wiretapper {eavesdropper) who only listens others it cannot be insured against simply
to but does not originate ciphers and an because of the physical exposure of one end
active wiretapper who may alter or origi- of the communications link. If in an asym-
nate ciphers. An eavesdropper listening to metric system the receiver key is concealed
the microwave scatter from a microwave from a knowledge of the transmitter key, it
link illustrates the first threat, while a is still possible to communicate in secrecy
wiretapper in a central switching office il- even after the transmitter key is exposed.
lustrates the second. In the case of the Conversely, if the transmitter key is con-
active wiretapper, the only way to avoid cealed from a knowledge of the receiver
the "postal chess ploy ''1~ is to have the keys key, it is possible for the transmitter to
delivered securely, either in a face-to-face authenticate himself even though the re-
exchange by the transmitter and receiver ceiver key is known to an opponent. These
or by trusted couriers, etc. unique capabilities of asymmetric systems
distinguish them from symmetric systems.
SUMMARY AND CONCLUSION Two vital points need to be restated.
First, it is false that key protection and
The primary objectives in this paper have secure key dissemination are unnecessary
been to develop the concept of the asym- in an asymmetric system. As Needham and
metric encryption/decryption channel and Schroeder [NEED78] have shown for net-
to show some real problems that can only work authentication, the protocols are quite
be solved by using such a channel. A sec- similar, and the number of protocol mes-
ondary objective has been to draw analo- sages which must be exchanged is compa-
gies between coding theory and encryption rable using either symmetric or asymmetric
theory in order to clarify the concepts of encryption techniques. At the end of the
secrecy and authentication. section on secure communications we illus-
Cryptosystems are naturally classified trated an anomaly, the establishing of a
into two classes, symmetric or asymmetric, secret link with a party whose identity can-
depending only on whether the keys at the not be verified, which can arise in the ab-
transmitter and receiver are easily com- sence of key dissemination. For this reason
puted from each other. The only well-tested asymmetric techniques can be used to dis-
operational cryptosystems in 1979 were seminate a key which is then used in a
symmetric. All depend on the computa- symmetric system.
tional intractability of working backward The second point is that asymmetric sys-
from a knowledge of the cipher, plaintext, tems are not a priori superior to symmetric
and encryption/decryption function for ones. The particular application determines
their cryptosecurity. Asymmetric crypto- which system is appropriate. In the 1979
systems are inherently neither more nor state of the art, all the proposed asymmet-
less secure than symmetric cryptosystems. ric systems exact a high price for their
Both kinds of system depend on the high asymmetry: The higher amount of compu-
"work factor" associated with a computa- tation in the encryption/decryption process
tionally infeasible problem to provide com- significantly cuts the channel capacity (bits
per second of message information com-
~s In this s c h e m e a thLrd p a r t y interposes h n n s e l f sim- municated). No asymmetric scheme known
ply to relay m o v e s m t h e correspondence of two postal to the author has a capacity better than
c h e s s players with a g u a r a n t e e of either drawing
against both or else winning against one while losing C 1/2, where C is the channel capacity of a
to t h e other, irrespective of his c h e s s playing abilities symmetric channel having the same cryp-
Computing Surveys, Vol. II, No 4, December 1979
328 • Gustavus J. S i m m o n s
tosecurity and using the s a m e basic clock
or bit m a n i p u l a t i o n rate. U n d e r these con-
ditions, the higher o v e r h e a d of a s y m m e t r i c
encryption is w a r r a n t e d only for applica-
tions in which one of the c o m m u n i c a t i o n s
terminals is physically insecure.
APPENDIX FIGURE 7.
T h e following brief discussion of L F S R s is
t h a t Pn(x) m a y also divide x d + 1 where d
included for the benefit of readers who m a y
is a divisor of 2 n - 1, in which case the
not be familiar with the inner workings of
m a x i m u m period of the sequences f r o m the
these devices. Given an n t h - o r d e r n o n h o m -
associated L F S R is also a p r o p e r divisor of
ogeneous polynomial, i.e., P~(x) = ~,".-o c,x', 2 n - 1. I f the polynomial Pn(x) has no
where Co = Cn = 1, with binary coefficients, ~9
factors and does not divide x d + 1 for a n y
we define an associated n-stage linear feed-
p r o p e r divisor d of 2" - 1, t h e n P ' ( x ) is said
b a c k shift register by the rules
to be primitive. T h e i m p o r t a n t point is t h a t
n the nonzero cycle g e n e r a t e d b y the associ-
Xl t = Ec, a t e d linear f e e d b a c k shift register for a n y
z-1
primitive p o l y n o m i a l h a s the m a x i m u m
and possible period of 2" - 1:00 . . . 0 is always
x, t = x~=], i> 1 in a cycle b y itself. For example, P*(x) = x*
+x+ ldividesx ~+ lbutnotx d+ lfor
where x, t is the state of the ith stage of the a n y d < 15; hence P*(x) is primitive and
register on the t t h step and ~ is the m o d u l o the m a x i m a l length nonzero cycle gener-
2 s u m (binary arithmetic). For example, if ated by the associated L F S R is:
P4(x) = x 4 + x 3 + x 2 + x + 1, the shift
1000 0101
register is of the f o r m shown in Figure 7
and the sequence of states of the register 0001 1011
(depending on the initial fill) is one of four 0011 0110
cycles: 0111 1100
1111 1001
0000 1000 0100 1110
1110 0010
0001 1001 1101
1101 0100
0011 0010 1011
1010
0110 0101 0111
1100 1010 1111 Linear feedback shift registers based on
primitive polynomials are therefore said to
In this case the 16 possible 4-bit binary be m a x i m a l length, and the resulting bit
n u m b e r s are divided into t h r e e cycles of sequences h a v e b e e n shown to satisfy m a n y
length 5 a n d one of length 1. T h e explana- tests for r a n d o m n e s s [GoLo67, TAUS65].
tion is t h a t x 4 + x 3 + x 2 + x + 1 divides F o r example, 0, 1 and 00, 01, 10, 11, etc. (up
x 5 + 1 evenly; i.e., to n-tuples), are as nearly uniform in their
( x + 1)(x 4 + x 3 + x 2 + x + l ) =x ~+1. probability of occurrence as is possible; i.e.,
since the all-zero n-tuple is not in the cycle,
Note: R e m e m b e r t h a t the coefficients are the all-zero k-tuple will occur one t i m e less
t r e a t e d as residues modulo 2. t h a n do the o t h e r k-tuples. Because of these
A well-known result f r o m algebra says v e r y useful p r o p e r t i e s and also because of
t h a t Pn(x) always divides x '~'-~ + 1, b u t the ease of i m p l e m e n t i n g m a x i m a l length
L F S R s in either h a r d w a r e or software, a
~' M o d u l o 2 u s i n g t h e r u l e s v o l u m i n o u s literature exists on the sub-
j e c t - - i n c l u d i n g extensive tables of the
0 1 0 0 0 primitive polynomials [GoLo67, PETE72]
1 0 1 0 1 needed to c o m p u t e the feedback functions.
C o m p u t | n g Surveys, Vol 11, No 4, December 1979
Symmetric and Asymmetric Encryption • 329
A n especially simple class of primitive poly- EVAN74 EVANS, A, JR., AND KANTROWITZ,
W. "A user authenticationscheme not
nomial [ZIER68, ZIER69], both to analyze reqmring secrecyin the computer," Com-
and to implement, is the trinomials, x" + m u n A C M 17, 8 (Aug. 1974),437-442.
x a + 1, which require only two stages of the FEIS73 FEISTEL, H. "Cryptography and com-
puter privacy," SCL Am. 228, 5 (May
feedback shift register to be tapped and 1973), 15-23.
c o m b i n e d by an Exclusive O R GAIN56 GAINES, H.F. Cryptanalys~s"a study of
ciphers and their solutzon, Dover, New
0 1 York, 1956.
GAIT77 GAIT, J "A new nonlinear pseudoran-
0 0 1 dora number generator," [EEE Trans
1 1 0 Softw Eng. SE-3, 5 (Sept. 1977), 359-363
GARD77 GARDNER, M. Mathematical games
to c o m p u t e the feedback sum. (section), Sct. Am. 237, 2 (Aug 1977),
120-124.
GEFF73 GEFFE, P.R. "How to protect data with
ACKNOWLEDGMENTS ciphers that are really hard to break,"
The author wishes to acknowledge the many and Electronws 46, 1 (Jan. 4, 1973), 99-101.
GILB74 GILBERT, E. N., MACWILLIAMS, F J.,
valuable contributions of M J. Norris to the ideas AND SLOANE, N. J. A "Codes which
presented here. He is also grateful to D. Kahn and H. detect deception," Bell Syst Tech. J. 53,
Bright for careful reviews of a first draft of the man- 3 (March 1974), 405-423.
uscript and to the anonymous referees whose detailed GOLO67 GOLOMR, S W. Shift register sequences,
Holden-Day, San Francisco, Calif., 1967.
suggestions materially shaped the present form of the HART64 HART, G L The Beale papers, Roan-
paper. Finally, he wishes to express his appreciation oke Public Library, Roanoke, Va, 1964
to R. J. Hanson and P. J. Denning whose assmtance HELL78 HELLMAN, M. E "An overview of pub-
has made it possible for this material to be published hc-key cryptography," IEEE Trans.
Commun COM-16, 6 (Nov. 1978), 24-32.
in Computing Surveys. HELL79a HELLMAN, M . E . "DES will be totally
insecure within ten years," IEEE Spec-
REFERENCES trum 16, 7 (July 1979), 32-39.
HELL79b HELLMAN, U . E "The mathematics of
ACME23 Acme commodity and phrase code, Acme public-key cryptography," Scz. Am. 241,
Code Co., San Francisco, Calif., 1923. 3 (Aug. 1979), 146-157.
ADLE78 ADLEMAN, L. M , AND RIVEST, R HERL78 HERLESTAM, T. "Critical remarks on
L "The use of public-keycryptography some public-key cryptosystems," BIT 18
in communication system design,"I E E E (1978), 493-496
Trans Commun. COM-16, 6 (Nov 1978), HILL29 HILL, L. S "Cryptography in an alge-
20-23. braic alphabet," Am. Math. Monthly 36
ALBE41 ALBERT, A. A "Some mathematical as- (June-July 1929), 306-312.
pects of cryptography," presented at the HILL31 HILL, L. S. "Concerning certain linear
A M S 382nd Meeting, Manhattan, Kans., transformation apparatus of cryptogra-
Nov 22, 1941. phy," Am Math. Monthly 38 (March
BERL68 BERLEKAMP, E. R. Algebrazc coding 1931), 135-154.
theory, McGraw-Hill, New York, 1968. HOFF77 HOFFMAN, L. J. Modern methods for
BRAN79 BRANSTAD, D. "Hellman's data does not computer security and prwacy, Prentice-
support his conclusion," IEEE Spectrum Hall, Englewood Cliffs, N J., 1977
16, 7 (July 1979), 41 HORO74 HOROWITZ, E., AND SAHNI, S.
BRIG76 BRIGHT, H S , AND ENISON, R "Computing partitions with applications
L. "Cryptography using modular soft- to the knapsack problem," J. ACM 21, 2
ware elements," in Proc AFIPS 1976 (April 1974), 277-292
NCC, Vol. 45, AFIPS Press, Arlington, KAHN66 KAHN, D. "Modern cryptology," Scz
Va, pp 113-123 Am. 215 (July 1966), 38-46
BRIG77 BRIGHT, H. S. "Cryptanalytic attack KAHN67 KAHN, D. The codebreakers, the story
and defense, ciphertext-only, known- of secret writing, MacMillan, New York,
plaintext, chosen-plaintext," Cryptologta 1967
1, 4 (Oct 1977), 366-370. KARP72 KARP, R.M. "Reducibility among com-
DAVI79 DAVZDA, G. I. "Hellman's scheme binatorial problems," in Complexzty of
breaks DES in its basic form," IEEE computer computations, R. E Mdler and
Spectrum 16, 7 (July 1979), 39. J. W Thatcher (Eds.), Plenum Press,
DEAD77 DEAVOURS, C. A. "UnIcity points In New York, 1972, pp. 85-104.
cryptanalysis," Cryptologta 1, 1 (Jan KULL76 KULLBACK, S Statistical methods in
1977}, 46-68 cryptanalysis, Aegean Park Press, La-
DIFF76 DIFFI]$, W , AND HELLMAN, M E. "New guna Hills, Calif, 1976.
dLrections in cryptography," IEEE Trans LEMP79 LEMPEL, A "Cryptology In transitmn" a
Inform. Theory ITo22, 6 (Nov. 1976), 644- survey," Comput. Surv. 11, 4 (Dec. 1979},
654. 285-304.
DIFF77 DIFFIE, W., AND HELLMAN, M. E LIPT78 LIPTON, S M., AND MATYAS, S. M
"Exhaustive cryptanalysIs of the NBS "Making the digital signature legal--and
data encryptlon standard," Computer 10, safeguarded," Data Commun. 7, 2 (Feb
6 (June 1977), 74-84. 1978), 41-52.
Computing Surveys, VoI 11. No 4, December 1979
330 G u s t a v u s J. S i m m o n s
MAcW77 MACWILLIAMS, F J., AND SLOANE, N . J . SHAM78 SHAMIR, A., AND ZIPPEL, R. E On the
A. The Theory of error-correcting security of the Merkle-Hellman crypto-
codes, Vols. I and II, North-Holland, New graphw scheme, Teeh. Rep. M I T / L C S /
York, 1977. TM-119, MIT Lab. Comput. Sci., Cam-
MART73 MARTIN, J. Security, accuracy and pri- bridge, Mass., Dec. 1978.
racy tn computing systems, Prentice- SHAM79 SHAMIR, A., RIVEST, R. L., AND ADLE-
Hall, Englewood Cliffs, N J., 1973. MAN, L. M. Mental poker, Tech. Rep.
MASS69 MASSEY, J. L "Shift-register synthesis MIT/LCS/TM-125, MIT Lab. Comput.
and BCH decoding," IEEE Trans. In- Scl., Cambridge, Mass., Feb. 1979.
form. Theory IT-15, 1 (Jan. 1969), 122- SHAN48 SHANNON, C. E "A mathematical the-
127. ory of communication," Bell Syst. Tech.
MERK78a MERKLE, R C. "Secure communica- J. 27 (July 1948), 379--423; (Oct. 1948),
tions over insecure channels," Commun. 623-656.
ACM 21, 4 (April 1978), 294-299. SHAN49 SHANNON, C . E . "Communication the-
MERK78b MERKLE, R. C, AND HELLMAN, M. ory of secrecy systems," Bell Syst. Tech.
E "Hiding information and signatures J. 28 (Oct. 1949), 656-715.
in trapdoor knapsacks," IEEE Trans. In- SHAP78 SHAPLEY, D. "The new unbreakable
form Theory IT-24, 5 (Sept. 1978), 525- codes--will they put NSA out of busi-
530. nessg, '' The Washington Post, Outlook,
MEYE72 MEYER, C, AND TUCHMAN, W. sec BI, July 9, 1978
"Pseudo-random codes can be cracked," SIMM77 SIMMONS, G. J, AND NORRIS, M.
Electron Des. 23 (1972), 74-76. J. "Prehmmary comments on the
MORRIS, R., SLOANE, N. J A., AND WY- M I.T. public-key cryptosystem," Cryp-
MORR77 tologla 1, 4 (Oct. 1977),406-414.
NER, A. D "Assessment of the National SIMM79 SIMMONS, G.J. "Cryptology the math-
Bureau of Standards proposed federal ematics of secure communication," Math.
Data Encryptlon Standard," Cryptologla Intell.1, 4 (Jan 1979),233-246
1, 3 (July 1977), 281-291. SUGA79 SUGARMAN, R "On foihng computer
NEED78 NEEDHAM, R. M., AND SCHROEDER, M. crime," IEEE Spectrum 16, 7 (July 1979),
D. "Using encryptIon for authentication 31-32.
in large networks of computers," Corn- TAUS65 TAUSWORTHE,R. C "Random numbers
mun. ACM 21, 12 (Dec. 1978), 993-999 generated by linear recurrence modulo
PETE72 PETERSON, W. W., AND WELDON, E. two," Math Comput. 19 (1965), 201-209
J Error correcting codes, 2nd ed., MIT TUCH79 TUCHMAN, W "Hellman presents no
Press, Cambridge, Mass, 1972 shortcut solutions to the DES," IEEE
POHL78 POHLIG, S C, AND HELLMAN, M Spectrum 16, 7 (July 1979), 40-41.
E. "An improved algorithm for comput- TUCK70 TUCKERMAN, B. A study of the Vlge-
mg logarithms over GF(p) and its cryp- ndre-Vernam smgle and multiple loop
tographlc significance," IEEE Trans In- enciphering systems, Rep. RC-2879
form Theory IT-24, 1 (Jan 1978), 106- (#13538), IBM T. J. Watson Res. Ctr.,
110 Yorktown Heights, N.Y., May 14, 1970.
PURD74 PURDY, G. B "A high security log-In VERN26 VERNAM, G. S. "Cipher printing tele-
procedure," Commun. ACM 17, 8 (Aug graph systems for secret wire and radio
1974), 442-445. telegraphic communications," J AIEE
RARI79 RABIN, M. O. Dtgttahzed signatures 45 (Feb. 1926), 109-115.
and pubhc-key functions as retractable WILK68 WILKES, M. V Time-sharing computer
as factor~zat:on, Tech Rep M I T / L C S / systems, American Elsevier, New York,
TR-212, MIT Lab Comput SCL, Cam- 1968
bridge, Mass, Jan 1979. WILL79a WILLIAMS,H. C., AND SCHMID,B. Some
RIVE78 RIVEST, R., SHAMIR, A., AND ADLEMAN, remarks concerning the M.LT. pubhc-
L. "A method for obtaining digltalsig- key cryptosystem, Rep. 91, U. of Manitoba
natures and pubhc-key cryptosystems," Dep. of Comput Sci., May 22, 1979.
C o m m u n A C M 21, 2 (Feb 1978), 120- WILL79b WILLIAMS, H. C. A mod~fwat:on of the
126. RSA pubhc-key encryptlon procedure,
ROBE75 ROBERTS, R . W . Encryption algorithm Rep. 92, U. of Manitoba Dep of Comput.
for computer data encryption," (NBS) Sci., 1979.
Fed. Reg. 40, 52 (March 17, 1975), 12134- ZIER68 ZIERLER, N., AND BRILLHART, J. "On
12139 primitive trinomials (rood 2)," Inform.
SCHR79 SCHROEPPEL, R., AND SHAMIR, A. "A Control 13 (1968), 541-554.
T. S 2 = O(2") time/space tradeoff for eer- ZIER69 Z1ERLER, i . , AND BRILLHART, J. "On
tain NP-complete problems," to appear prLmltlve trinomlals (rood 2, II)," Inform.
as MIT Lab. Comput Sei Rep. Control 14 (1969), 566-569.
RECEIVED NOVEMBER1978, FINAL REVISIONACCEPTEDAUGUST 1979
Cornputmg Surveys, Vo| l 1, No 4. December 1979
You might also like
- NAPRD03 Version 6.14 V1Document42 pagesNAPRD03 Version 6.14 V1hoseseoNo ratings yet
- Acto 071Document11 pagesActo 071abigail pyeNo ratings yet
- SSL/TLS Under Lock and Key: A Guide to Understanding SSL/TLS CryptographyFrom EverandSSL/TLS Under Lock and Key: A Guide to Understanding SSL/TLS CryptographyRating: 4 out of 5 stars4/5 (1)
- LOGIX 5000 Controllers SecurityDocument62 pagesLOGIX 5000 Controllers Securityskv004100% (1)
- Symmetric and Asymmetric EncryptionDocument26 pagesSymmetric and Asymmetric EncryptionViney BansalNo ratings yet
- Code and Ciphers NSA Guide PDFDocument9 pagesCode and Ciphers NSA Guide PDFJason JiaNo ratings yet
- Seminar RepDocument55 pagesSeminar RepArpit SharmaNo ratings yet
- Computer and Data Security 4 Class: Dr. Ashwaq Mahmood Alabaichi 2015-2016 Lec.1Document15 pagesComputer and Data Security 4 Class: Dr. Ashwaq Mahmood Alabaichi 2015-2016 Lec.1ashraf8No ratings yet
- Chapter 3 - Cryptography and Encryption TechniquesDocument88 pagesChapter 3 - Cryptography and Encryption TechniquesEthio FanaNo ratings yet
- Codes and Ciphers (Cryptology)Document8 pagesCodes and Ciphers (Cryptology)perhackerNo ratings yet
- CSS Lab Manual - PrintDocument45 pagesCSS Lab Manual - PrintXavier TxANo ratings yet
- Unit 4Document99 pagesUnit 4testNo ratings yet
- Chapter 2 & 3Document20 pagesChapter 2 & 3Yakubu AliuNo ratings yet
- p612 ShamirDocument2 pagesp612 ShamirSanjeev Naik RNo ratings yet
- ShamirHowToShareASecret PDFDocument2 pagesShamirHowToShareASecret PDFjuanNo ratings yet
- U21CS601 CT Unit 123 Part B QADocument13 pagesU21CS601 CT Unit 123 Part B QASanthosh kannaNo ratings yet
- Quantum Computing and Blockchain:: The Definitive GuideDocument40 pagesQuantum Computing and Blockchain:: The Definitive GuideAndrés Cárdenas NovoaNo ratings yet
- Cryptography: BY, Ayesha FarhinDocument41 pagesCryptography: BY, Ayesha FarhinnidhirgusainNo ratings yet
- Classical Encryption Techniques: M. Odeo LecturerDocument39 pagesClassical Encryption Techniques: M. Odeo LecturerSNo ratings yet
- Cryptography ReportDocument6 pagesCryptography ReportSakthiSriNo ratings yet
- Rsa PDFDocument5 pagesRsa PDFRoseri SinagaNo ratings yet
- Topic: Network Security CRYPTOGRAPHY (One of Its Possible Solution)Document9 pagesTopic: Network Security CRYPTOGRAPHY (One of Its Possible Solution)api-19799369No ratings yet
- Cryptography Course WorkDocument27 pagesCryptography Course WorkSovan PalNo ratings yet
- Paillier - cryptosystem-đã Chuyển ĐổiDocument5 pagesPaillier - cryptosystem-đã Chuyển ĐổiDuy HoangNo ratings yet
- Cryptography: Essay 15Document36 pagesCryptography: Essay 15Dhairav PatelNo ratings yet
- CryptosystemsDocument5 pagesCryptosystemsAnasham TegegnNo ratings yet
- An Introductionto CryptologyDocument18 pagesAn Introductionto CryptologyAudrey Lingstuyl AraujoNo ratings yet
- Security of C.N.: By: Eng. Ahmed K. DarajDocument8 pagesSecurity of C.N.: By: Eng. Ahmed K. DarajAHMED DARAJNo ratings yet
- Index 2. Cryptography-Purpose 3. Types of Cryptographic AlgorithmsDocument12 pagesIndex 2. Cryptography-Purpose 3. Types of Cryptographic Algorithmstimothyosaigbovo3466No ratings yet
- Chapter 2Document91 pagesChapter 2Destaye Sole WonideNo ratings yet
- فتح Public keyDocument22 pagesفتح Public keygymfitness202320No ratings yet
- InfoSecurity Lect Week3Document31 pagesInfoSecurity Lect Week3Shaheer ArshadNo ratings yet
- Lattice Klepto: Turning Post-Quantum Crypto Against ItselfDocument19 pagesLattice Klepto: Turning Post-Quantum Crypto Against ItselfCharles MoimoiNo ratings yet
- Securing Network Transactions - Pptx/vijetha BhatDocument27 pagesSecuring Network Transactions - Pptx/vijetha BhatVijetha bhatNo ratings yet
- CryptographyDocument5 pagesCryptographyJoelNo ratings yet
- Notes of Unit-1 Information SecurityDocument18 pagesNotes of Unit-1 Information SecurityAbhishek NarwariyaNo ratings yet
- ProvablesecurityDocument11 pagesProvablesecurityJesus Manuel Muñoz PachecoNo ratings yet
- Secure Audio TeleconferenceDocument9 pagesSecure Audio TeleconferencealanroytNo ratings yet
- Unit IiimcDocument26 pagesUnit Iiimckashokkumar sctengNo ratings yet
- Playing Hide and Seek With Stored Keys: Adi Shamir and Nicko Van Someren September 22, 1998Document9 pagesPlaying Hide and Seek With Stored Keys: Adi Shamir and Nicko Van Someren September 22, 1998Rihards KubilisNo ratings yet
- Classical Encryption TechniquesDocument12 pagesClassical Encryption Techniquessushantluitel39No ratings yet
- Unit 4Document18 pagesUnit 421EE026 Anushka SrivastavaNo ratings yet
- Modified RSA Public Key Cryptosystem Using Two Key PairsDocument3 pagesModified RSA Public Key Cryptosystem Using Two Key PairsJainul AbudinNo ratings yet
- Index: 3.1 Private Key Algorithm 3.2 Public Key Algorithm 3.3 Hash FunctionsDocument11 pagesIndex: 3.1 Private Key Algorithm 3.2 Public Key Algorithm 3.3 Hash FunctionsYogesh YadavNo ratings yet
- Part ADocument14 pagesPart AHANISHA SAALIHNo ratings yet
- CryptographyDocument23 pagesCryptographyAnubhav KumarNo ratings yet
- Computer Security Chapter 2-3-4-1Document72 pagesComputer Security Chapter 2-3-4-1guta lamessaNo ratings yet
- Major Doc Fine1Document75 pagesMajor Doc Fine1Anil SagarNo ratings yet
- Unit 3 Cryptography and Public Key InfrastrucutreDocument34 pagesUnit 3 Cryptography and Public Key InfrastrucutreDarshit ChhatbarNo ratings yet
- Cryptographic AlgorithmsDocument4 pagesCryptographic AlgorithmstedsgamerNo ratings yet
- Information SecurityDocument11 pagesInformation Securityapi-3798998No ratings yet
- Microsoft Word - Cryptography - NewDocument12 pagesMicrosoft Word - Cryptography - NewSwapnilDalveNo ratings yet
- Review Article: A Survey of Homomorphic Encryption For NonspecialistsDocument10 pagesReview Article: A Survey of Homomorphic Encryption For NonspecialistsAnagnostopoulos AggelosNo ratings yet
- Network Security and CryptographyDocument11 pagesNetwork Security and CryptographyRajesh Kumar JoshNo ratings yet
- Gemmw: Mathematics in The Modern World Module 5: Cryptography Learning OutcomesDocument15 pagesGemmw: Mathematics in The Modern World Module 5: Cryptography Learning OutcomesDANINo ratings yet
- Of Public Key CryptographyDocument9 pagesOf Public Key CryptographyChirag KoliNo ratings yet
- Computer Security (Chapter-3)Document88 pagesComputer Security (Chapter-3)Naoly GetNo ratings yet
- Answer - Model - CS409 - Cryptography and Network Security - Nov 2018Document16 pagesAnswer - Model - CS409 - Cryptography and Network Security - Nov 2018Harshit SrivastavaNo ratings yet
- Adobe Scan Apr 22, 2024Document25 pagesAdobe Scan Apr 22, 2024Shiva TejaNo ratings yet
- New Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNAFrom EverandNew Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNANo ratings yet
- Transformation of Cryptography: Fundamental concepts of Encryption, Milestones, Mega-Trends and sustainable Change in regard to Secret Communications and its NomenclaturaFrom EverandTransformation of Cryptography: Fundamental concepts of Encryption, Milestones, Mega-Trends and sustainable Change in regard to Secret Communications and its NomenclaturaNo ratings yet
- Work-Related Musculoskeletal Disorders: The Epidemiologic Evidence and The DebateDocument12 pagesWork-Related Musculoskeletal Disorders: The Epidemiologic Evidence and The DebateLaine VenâncioNo ratings yet
- Illilllhiulll Liillllllll: Ulllted States Patent (19) (11) Patent Number: 5,748,735Document19 pagesIllilllhiulll Liillllllll: Ulllted States Patent (19) (11) Patent Number: 5,748,735Laine VenâncioNo ratings yet
- Dynamic Key Cryptography and ApplicationsDocument14 pagesDynamic Key Cryptography and ApplicationsLaine VenâncioNo ratings yet
- Configuring Distributed Systems in A Java-Based Environment: Louis J Botha, Judith M BishopDocument15 pagesConfiguring Distributed Systems in A Java-Based Environment: Louis J Botha, Judith M BishopLaine VenâncioNo ratings yet
- 7 PDFDocument8 pages7 PDFLaine VenâncioNo ratings yet
- United States Patent (10) Patent No.: US 8.477,940 B2Document10 pagesUnited States Patent (10) Patent No.: US 8.477,940 B2Laine VenâncioNo ratings yet
- Experiences With Ides and Java Teaching: What Works and What Doesn'TDocument2 pagesExperiences With Ides and Java Teaching: What Works and What Doesn'TLaine VenâncioNo ratings yet
- Image Encryption Using Affine Transform and XOR OperationDocument4 pagesImage Encryption Using Affine Transform and XOR OperationLaine VenâncioNo ratings yet
- A Comparative Survey of Symmetric and Asymmetric Key CryptographyDocument12 pagesA Comparative Survey of Symmetric and Asymmetric Key CryptographyLaine VenâncioNo ratings yet
- Iiihiii Iiii: United States Patent 19Document20 pagesIiihiii Iiii: United States Patent 19Laine VenâncioNo ratings yet
- Comparison of Symmetric and Asymmetric Cryptography With Existing Vulnerabilities and CountermeasuresDocument4 pagesComparison of Symmetric and Asymmetric Cryptography With Existing Vulnerabilities and CountermeasuresLaine VenâncioNo ratings yet
- Optimal Asymmetric EncryptionDocument20 pagesOptimal Asymmetric EncryptionLaine VenâncioNo ratings yet
- Asymmetric Cryptography With: Hidden MonomialDocument16 pagesAsymmetric Cryptography With: Hidden MonomialLaine VenâncioNo ratings yet
- Michael Wiener (Ed.) : CRYPTO'99, LNCS 1666, Pp. 537-554, 1999. Springer-Verlag Berlin Heidelberg 1999Document18 pagesMichael Wiener (Ed.) : CRYPTO'99, LNCS 1666, Pp. 537-554, 1999. Springer-Verlag Berlin Heidelberg 1999Laine VenâncioNo ratings yet
- Exploiting The Power of Gpus For Asymmetric Cryptography: Abstract. Modern Graphics Processing Units (Gpu) Have Reached ADocument21 pagesExploiting The Power of Gpus For Asymmetric Cryptography: Abstract. Modern Graphics Processing Units (Gpu) Have Reached ALaine VenâncioNo ratings yet
- Entangled State Quantum Cryptography: Eavesdropping On The Ekert ProtocolDocument4 pagesEntangled State Quantum Cryptography: Eavesdropping On The Ekert ProtocolLaine VenâncioNo ratings yet
- Quantum Cryptography Based On Orthogonal States: Lior Goldenberg and Lev VaidmanDocument12 pagesQuantum Cryptography Based On Orthogonal States: Lior Goldenberg and Lev VaidmanLaine VenâncioNo ratings yet
- Optimal Eavesdropping in Cryptography With Three-Dimensional Quantum StatesDocument4 pagesOptimal Eavesdropping in Cryptography With Three-Dimensional Quantum StatesLaine VenâncioNo ratings yet
- E. Wolf, Progress in Optics VVV C 199X All Rights ReservedDocument61 pagesE. Wolf, Progress in Optics VVV C 199X All Rights ReservedLaine VenâncioNo ratings yet
- Quantum Cryptography With Imperfect ApparatusDocument7 pagesQuantum Cryptography With Imperfect ApparatusLaine VenâncioNo ratings yet
- Quantum Cryptography Using Entangled Photons in Energy-Time Bell StatesDocument4 pagesQuantum Cryptography Using Entangled Photons in Energy-Time Bell StatesLaine VenâncioNo ratings yet
- "Plug and Play" Systems For Quantum CryptographyDocument6 pages"Plug and Play" Systems For Quantum CryptographyLaine VenâncioNo ratings yet
- Single Photon Quantum Cryptography: PACS Numbers: 03.67.Dd, 42.50.DvDocument4 pagesSingle Photon Quantum Cryptography: PACS Numbers: 03.67.Dd, 42.50.DvLaine VenâncioNo ratings yet
- Optimal Eavesdropping in Quantum Cryptography With Six StatesDocument5 pagesOptimal Eavesdropping in Quantum Cryptography With Six StatesLaine VenâncioNo ratings yet
- Continuous Variable Quantum CryptographyDocument11 pagesContinuous Variable Quantum CryptographyLaine VenâncioNo ratings yet
- Beating The PNS Attack in Practical Quantum CryptographyDocument12 pagesBeating The PNS Attack in Practical Quantum CryptographyLaine VenâncioNo ratings yet
- Quantum Cryptography With 3-State Systems: Helle Bechmann-Pasquinucci and Asher PeresDocument11 pagesQuantum Cryptography With 3-State Systems: Helle Bechmann-Pasquinucci and Asher PeresLaine VenâncioNo ratings yet
- Device-Independent Security of Quantum Cryptography Against Collective AttacksDocument5 pagesDevice-Independent Security of Quantum Cryptography Against Collective AttacksLaine VenâncioNo ratings yet
- United States Patent (19) : Watanabe (54) - Sensing Amplifier IncludingDocument8 pagesUnited States Patent (19) : Watanabe (54) - Sensing Amplifier IncludingLaine VenâncioNo ratings yet
- Quantum Cryptography With Entangled PhotonsDocument4 pagesQuantum Cryptography With Entangled PhotonsLaine VenâncioNo ratings yet
- Unit 3Document47 pagesUnit 3Andualem BegunoNo ratings yet
- Common Types of Online and Mobile Fraud Include:: Vous Avez Atteint Le Nombre Maximum de Réponses AutoriséesDocument4 pagesCommon Types of Online and Mobile Fraud Include:: Vous Avez Atteint Le Nombre Maximum de Réponses Autoriséeshakim hamadacheNo ratings yet
- Palo-Alto-Networks Certkey ACE v2018-10-19 by Simon 99q PDFDocument42 pagesPalo-Alto-Networks Certkey ACE v2018-10-19 by Simon 99q PDFpradeepNo ratings yet
- Cryptographic Controls Policy and GuidanceDocument8 pagesCryptographic Controls Policy and Guidancejustforfun2009No ratings yet
- Image Encryption and Decryption Using BL PDFDocument6 pagesImage Encryption and Decryption Using BL PDFNaresh PurohitNo ratings yet
- Lecture 2 Security ThreatsDocument56 pagesLecture 2 Security ThreatsWycliff Jonathan KituriNo ratings yet
- 2 Talk1 PublicKeyCryptography 23june2021Document68 pages2 Talk1 PublicKeyCryptography 23june2021lakshmisudarshanNo ratings yet
- Biometrics in Banking Security A Case StudyDocument17 pagesBiometrics in Banking Security A Case StudyAnonymous tZJktxmHSNo ratings yet
- Leveraging LDAP Groups Users With SonicWALL UTM Appliance TechnoteDocument57 pagesLeveraging LDAP Groups Users With SonicWALL UTM Appliance TechnoteDoug SiskNo ratings yet
- Ovation Control & Optimization Solutions For GE Heavy-Duty Gas TurbinesDocument2 pagesOvation Control & Optimization Solutions For GE Heavy-Duty Gas TurbinesHoucine BelhaskaNo ratings yet
- NS by MU PDFDocument252 pagesNS by MU PDFakash mayekarNo ratings yet
- CHAPTER 5 QUIZ QUESTIONS With ANSWERSDocument3 pagesCHAPTER 5 QUIZ QUESTIONS With ANSWERSJonathan RyanNo ratings yet
- NDPR Audit Checklist S/N Audit Requirement Status CommentsDocument6 pagesNDPR Audit Checklist S/N Audit Requirement Status CommentsOluwatomi BabatundeNo ratings yet
- Software Requirement System: User Classes and CharacteristicsDocument3 pagesSoftware Requirement System: User Classes and CharacteristicsChocolatey Boy AmarNo ratings yet
- Cryptography and Network SecurityDocument37 pagesCryptography and Network SecurityPrachiNo ratings yet
- Online Medical ProposalDocument3 pagesOnline Medical ProposalsherazNo ratings yet
- CISO Perspectives Data ClassificationDocument5 pagesCISO Perspectives Data ClassificationMSFTSIRNo ratings yet
- Deepak Jeengar Report Part 1Document7 pagesDeepak Jeengar Report Part 1jayaNo ratings yet
- Chapter Two (Network Thesis Book)Document16 pagesChapter Two (Network Thesis Book)Latest Tricks100% (1)
- Ccna Security Ch2 Understanding Security Policies Lifecycle ApproachDocument7 pagesCcna Security Ch2 Understanding Security Policies Lifecycle Approachflorinn81No ratings yet
- CC Ques Bank Cloud Computing QB UNIT 5Document7 pagesCC Ques Bank Cloud Computing QB UNIT 5aparna chinnarajNo ratings yet
- Cyber Risk: A Growing Concern For Macrofinancial StabilityDocument1 pageCyber Risk: A Growing Concern For Macrofinancial StabilityibedawyNo ratings yet
- Web Vulnerability Detection and Security Mechanism: Katkar Anjali S., Kulkarni Raj BDocument5 pagesWeb Vulnerability Detection and Security Mechanism: Katkar Anjali S., Kulkarni Raj Bcrack wallNo ratings yet
- IT Security Risk Management Lecture 3Document62 pagesIT Security Risk Management Lecture 3ridwan setiawanNo ratings yet
- Everest Group RFP Questionnaire For ESG AttributesDocument7 pagesEverest Group RFP Questionnaire For ESG AttributesAbhijeet ShindeNo ratings yet
- E-Voting System Using Homomorphic EncryptionDocument8 pagesE-Voting System Using Homomorphic EncryptionIJRASETPublicationsNo ratings yet
- Introduction To Digital ForensicsDocument28 pagesIntroduction To Digital ForensicsSurendra Dawadi50% (2)