Professional Documents
Culture Documents
Common Subjects-5
Common Subjects-5
Uploaded by
varsha guptaCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Common Subjects-5
Common Subjects-5
Uploaded by
varsha guptaCopyright:
Available Formats
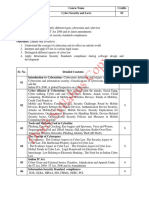
RUC501 /RUC601 CYBER SECURITY L-T-P: 3-0-0
Proposed
Unit Topic
Lecture
Introduction- Introduction to Information Systems, Types of Information
Systems, Development of Information Systems, Introduction to Information
I 08
Security, Need for Information Security, Threats to Information Systems,
Information Assurance, Cyber Security, and Security Risk Analysis.
Application Security- (Database, E-mail and Internet), Data Security
Considerations-Backups, Archival Storage and Disposal of Data, Security
Technology-Firewall and VPNs, Intrusion Detection, Access Control. Security
II Threats -Viruses, Worms, Trojan Horse, Bombs, Trapdoors, Spoofs, E-mail 08
Viruses, Macro Viruses, Malicious Software, Network and Denial of Services
Attack, Security Threats to E-Commerce- Electronic Payment System, e- Cash,
Credit/Debit Cards. Digital Signature, Public Key Cryptography
Developing Secure Information Systems- Application Development
Security, Information Security Governance & Risk Management, Security
III Architecture & Design Security Issues in Hardware, Data Storage & 08
Downloadable Devices, Physical Security of IT Assets, Access Control, CCTV
and Intrusion Detection Systems, Backup Security Measures.
Security Policies- Development of Policies, WWW Policies, Email Security
Policies, Policy Review Process-Corporate Policies-Sample Security Policies,
IV 08
Publishing and Notification Requirement of the Policies.
Evolving Technology Security – Mobile, Cloud, Outsourcing, SCM.
Information Security Standards-ISO, IT Act, Copyright Act, Patent Law,
IPR. Cyber Laws in India; IT Act 2000 Provisions, Intellectual Property Law:
V 08
Copy Right Law, Software License, Semiconductor Law and Patent Law.
Case Study – Corporate Security
References:
1. Charles P. Pfleeger, Shari Lawerance Pfleeger, “Analysing Computer Security”, Pearson
Education India.
2. V.K.Pachghare, “Cryptography and information Security”, PHI Learning Private Limited, Delhi
India.
3. Sarika Gupta & Gaurav Gupta, Information Security and Cyber Laws, Khanna Publishing House
4. Anshul Kaushik, Cyber Security, Khanna Publishing House
5. Dr.Surya Prakash Tripathi, Ritendra Goyal, Praveen Kumar Shukla ,”Introduction to Information
Security and Cyber Law” Willey Dreamtech Press.
6. Michael E.Whitman and Herbert J Mattord "Principle of Information Security" Cengage
7. Mike Chapple and David Seidl "Cyberwarfare: Information operations in a connected world"
Jones & Bartlett Learning
8. Schou, Shoemaker, “Information Assurance for the Enterprise”, Tata McGraw Hill.
9. CHANDER, HARISH,” Cyber Laws And It Protection ” , PHI Learning Private Limited ,Delhi
10. V.K. Jain, Cryptography and Network Security, Khanna Publishing House, Delhi
You might also like
- Saab340 LimitationsDocument39 pagesSaab340 LimitationsAsdrubal Chavez100% (1)
- Design Thinking and Innovation at AppleDocument15 pagesDesign Thinking and Innovation at AppleAmit Chaudhary100% (1)
- Cyber Security SyllabusDocument1 pageCyber Security Syllabusshubh1996sriNo ratings yet
- Cyberlaws and SecurityDocument1 pageCyberlaws and Security17001009023 HINGULA BHATNo ratings yet
- Cyber Security AlignmentDocument1 pageCyber Security AlignmentbcadeptNo ratings yet
- Cyber SecurityDocument39 pagesCyber SecurityprateekguptadelNo ratings yet
- Syllabus BCA 6th SemDocument4 pagesSyllabus BCA 6th Semvk421622No ratings yet
- Cyber SecurityDocument53 pagesCyber SecurityAnvesha SharmaNo ratings yet
- Renewable 1.0Document8 pagesRenewable 1.073035537rishubrother95827594No ratings yet
- Digital Notes ON Cyber Security (R18A0521) : B.Tech Iii Year - Ii Sem (R18)Document38 pagesDigital Notes ON Cyber Security (R18A0521) : B.Tech Iii Year - Ii Sem (R18)Shyam Sulbhewar100% (1)
- Cyber Security NotesDocument106 pagesCyber Security NotesBhure Vedika100% (1)
- Information Security Viii Semester: Department of Computer Science and Engineering (DEC 2019 - APR 2020)Document46 pagesInformation Security Viii Semester: Department of Computer Science and Engineering (DEC 2019 - APR 2020)KalpanaMohanNo ratings yet
- (R17A0526) Information Security Digital NotesDocument143 pages(R17A0526) Information Security Digital NotesPrafulla Durgadhar GawandeNo ratings yet
- (IJCST-V5I2P93) :G. Ambika, Dr.P.SrivaramangaiDocument3 pages(IJCST-V5I2P93) :G. Ambika, Dr.P.SrivaramangaiEighthSenseGroupNo ratings yet
- Cyber Security - I.ravi KumarDocument38 pagesCyber Security - I.ravi KumarMr. RAVI KUMAR INo ratings yet
- Cyber Security Unit-5 Davesh Singh Som: Information Security Standard (ISO)Document4 pagesCyber Security Unit-5 Davesh Singh Som: Information Security Standard (ISO)davesh somNo ratings yet
- Adobe Scan Jan 17, 2024Document1 pageAdobe Scan Jan 17, 2024SWARUP SAMANTANo ratings yet
- Mca Degree SubjectsDocument2 pagesMca Degree SubjectsVarun UpadhyayNo ratings yet
- It2042 Unit1Document32 pagesIt2042 Unit1Udemy FreeNo ratings yet
- Network Security & Cryptography BookDocument204 pagesNetwork Security & Cryptography BookYash Bhardwaj100% (1)
- ManagementDocument16 pagesManagementAbhishek KhandekarNo ratings yet
- Cyber Security (Open Elective) ObjectivesDocument2 pagesCyber Security (Open Elective) Objectivessriramganesh81070% (1)
- Phobia (Disease)Document5 pagesPhobia (Disease)Naim MirzaNo ratings yet
- Network Security: Seminar Report OnDocument31 pagesNetwork Security: Seminar Report Onabhishek100% (1)
- Systems SecurityDocument257 pagesSystems SecurityMuriithi MurageNo ratings yet
- New and Forthcoming From William Stallings: Computer Security, Fourth Edition (With Lawrie Brown)Document1 pageNew and Forthcoming From William Stallings: Computer Security, Fourth Edition (With Lawrie Brown)pedrollNo ratings yet
- Nptel: Industry 4.0: CybersecurityDocument137 pagesNptel: Industry 4.0: Cybersecuritylayal sekaNo ratings yet
- Unit IDocument32 pagesUnit Ijayaraj2024No ratings yet
- CNCS2004-Cybersecurity SyllabusDocument3 pagesCNCS2004-Cybersecurity SyllabusZoyaNo ratings yet
- SPECILIZATION IN Cyber SecurityDocument8 pagesSPECILIZATION IN Cyber SecurityASHISHNo ratings yet
- Security Defi. 2019Document6 pagesSecurity Defi. 2019Eng Mohamed NajiNo ratings yet
- Internet of Things IoT Security PerspectiveDocument3 pagesInternet of Things IoT Security PerspectiveEditor IJTSRDNo ratings yet
- Guide To Computer Network Security Chapter2Document22 pagesGuide To Computer Network Security Chapter2SonjaNo ratings yet
- NIS Project Final PMV 23Document3 pagesNIS Project Final PMV 23Pooja AbhangNo ratings yet
- Is Unit1Document38 pagesIs Unit1SaniyaNo ratings yet
- IOTDocument8 pagesIOTBhupati MakupallyNo ratings yet
- CSL SyllabusDocument2 pagesCSL SyllabusKrupesh PatilNo ratings yet
- White Paper SecurityThreatsDocument56 pagesWhite Paper SecurityThreatsSamuel ChanNo ratings yet
- White Paper SecurityThreatsDocument56 pagesWhite Paper SecurityThreatsSamuel ChanNo ratings yet
- CSE2008 SyllabusDocument2 pagesCSE2008 SyllabusABHAY POTLURI 20BCI0017No ratings yet
- Chapter 1 - Introduction To Information SecurityDocument13 pagesChapter 1 - Introduction To Information SecurityAshura OsipNo ratings yet
- Chapter 1 InfoSecDocument60 pagesChapter 1 InfoSecAlebel AyalnehNo ratings yet
- Applied Sciences: Iot Privacy and Security: Challenges and SolutionsDocument17 pagesApplied Sciences: Iot Privacy and Security: Challenges and SolutionsMSAMHOURINo ratings yet
- Jntuh College of Engineering Hyderabad Dept of Computer Science and EngineeringDocument4 pagesJntuh College of Engineering Hyderabad Dept of Computer Science and EngineeringsidNo ratings yet
- CSS (Computer System Security)Document162 pagesCSS (Computer System Security)Ashmit JaiswalNo ratings yet
- IEEE DL Survey ExactDocument82 pagesIEEE DL Survey ExactArthee PandiNo ratings yet
- Cyber SecurityDocument3 pagesCyber Securitysweta.jethava24460No ratings yet
- CNS SyllabusDocument1 pageCNS SyllabusgdeepthiNo ratings yet
- Final PresenDocument14 pagesFinal PresenThana JamalNo ratings yet
- IT661 Cyber SecurityDocument1 pageIT661 Cyber SecurityKaikala Ram Charan TejNo ratings yet
- IT661Document1 pageIT661abcdefNo ratings yet
- IT6611212Document1 pageIT6611212abcdefNo ratings yet
- (An Introduction To Computer) : SecurityDocument51 pages(An Introduction To Computer) : SecurityguntureanNo ratings yet
- Instructor Materials Chapter 8: Becoming A Cybersecurity SpecialistDocument24 pagesInstructor Materials Chapter 8: Becoming A Cybersecurity SpecialistDewi Ayu LestariNo ratings yet
- Cyber Security NotesDocument51 pagesCyber Security NotesBhure VedikaNo ratings yet
- Cyber SecurityDocument68 pagesCyber SecuritymoisertarienNo ratings yet
- IS SolutionsDocument3 pagesIS SolutionsrohithatimsiNo ratings yet
- Chapter 1Document34 pagesChapter 1Glenmar BayucanNo ratings yet
- Fundamentals of Cyber SecurityDocument2 pagesFundamentals of Cyber SecurityDr-Samson ChepuriNo ratings yet
- Block 1 MBSC-4.2G Information Security PDFDocument83 pagesBlock 1 MBSC-4.2G Information Security PDFSRIram sriramNo ratings yet
- The Future of Cybersecurity: Guarding the Digital Frontier: Strategies, Tools, and Best PracticesFrom EverandThe Future of Cybersecurity: Guarding the Digital Frontier: Strategies, Tools, and Best PracticesNo ratings yet
- C OperatorDocument30 pagesC Operatorvarsha guptaNo ratings yet
- Internship Program Day-11Document56 pagesInternship Program Day-11varsha guptaNo ratings yet
- Lec11 PDFDocument38 pagesLec11 PDFvarsha guptaNo ratings yet
- KIET School of Engineering & Technology, Ghaziabad: Project PerformaDocument1 pageKIET School of Engineering & Technology, Ghaziabad: Project Performavarsha guptaNo ratings yet
- Assignmnet 1 PDFDocument4 pagesAssignmnet 1 PDFvarsha guptaNo ratings yet
- Internship Program (Problem Solving With C) : AssignmentsDocument5 pagesInternship Program (Problem Solving With C) : Assignmentsvarsha guptaNo ratings yet
- Practice QuestionsDocument5 pagesPractice Questionsvarsha guptaNo ratings yet
- DSGT SyallbusDocument3 pagesDSGT Syallbusvarsha guptaNo ratings yet
- Unit 1 Programming in C and Primitive Data TypesDocument26 pagesUnit 1 Programming in C and Primitive Data Typesjhaa98676No ratings yet
- TicketsDocument3 pagesTicketsBurhanuddin IndorewalaNo ratings yet
- Toyota Training Automatic Transmission BasicsDocument20 pagesToyota Training Automatic Transmission Basicsnorman100% (41)
- LEGO Club Magazine Red Brick MarchpdfDocument47 pagesLEGO Club Magazine Red Brick Marchpdfmartayensid96% (28)
- Com BankDocument25 pagesCom BankAnonymous y3E7iaNo ratings yet
- Bibliografia - Metodologia AgilDocument2 pagesBibliografia - Metodologia AgilJane DDNo ratings yet
- Consumer ActDocument35 pagesConsumer ActAnnabelle RafolsNo ratings yet
- Explosive PDFDocument241 pagesExplosive PDFthehoang12310100% (1)
- End-Test 1-Semester2Document6 pagesEnd-Test 1-Semester2ToQuyen LyThiNo ratings yet
- Joinder of PartiesDocument5 pagesJoinder of PartiessaifulNo ratings yet
- Spons GuideDocument12 pagesSpons GuideMelyssa Dawn GullonNo ratings yet
- UPDATED-Evolution of ComputersDocument22 pagesUPDATED-Evolution of ComputersimpalerNo ratings yet
- The $25,000,000,000 Eigenvector: The Linear Algebra Behind GoogleDocument13 pagesThe $25,000,000,000 Eigenvector: The Linear Algebra Behind Googlebob sedgeNo ratings yet
- ARAW 2020 Call For PapersDocument10 pagesARAW 2020 Call For PapersAlex GonzalesNo ratings yet
- Mochi ManiaDocument6 pagesMochi Maniasilentchase332No ratings yet
- B. Sc. Nursing Course (4 Years) : Entrance Examination 2022 (CET-2022)Document6 pagesB. Sc. Nursing Course (4 Years) : Entrance Examination 2022 (CET-2022)Tannu PalNo ratings yet
- Atmega8 Uc: Uart !!!Document16 pagesAtmega8 Uc: Uart !!!malhiavtarsinghNo ratings yet
- DCPS Chief Procurement Officer Position Description 7-22-09Document5 pagesDCPS Chief Procurement Officer Position Description 7-22-09api-15105945No ratings yet
- Chemical ContactDocument118 pagesChemical ContactkasvikrajNo ratings yet
- Module Title Construction Technology I Module Code Credits Prerequisites Module Aim(s)Document2 pagesModule Title Construction Technology I Module Code Credits Prerequisites Module Aim(s)LokuliyanaNNo ratings yet
- The Excretory System (The Urinary System) : Responsible For The Processing and Elimination of Metabolic Waste Consists ofDocument8 pagesThe Excretory System (The Urinary System) : Responsible For The Processing and Elimination of Metabolic Waste Consists ofDeeptanshu PrakashNo ratings yet
- SocaDocument9 pagesSocaAlexandre AGNo ratings yet
- List of Public Information Officers For Punjab Transparency and Right To Information ACT 2013Document41 pagesList of Public Information Officers For Punjab Transparency and Right To Information ACT 2013arhijaziNo ratings yet
- Formulae HandbookDocument60 pagesFormulae Handbookmgvpalma100% (1)
- Pause-Pose-Pounce-Bounce: What Are The Implications For Teachers?Document1 pagePause-Pose-Pounce-Bounce: What Are The Implications For Teachers?ShruthiNo ratings yet
- Major Challenges To The Effective Management of HuDocument16 pagesMajor Challenges To The Effective Management of HuRussell MasseyNo ratings yet
- An-Intro To-Vibration MATLAB 1998a LinkedDocument22 pagesAn-Intro To-Vibration MATLAB 1998a LinkedEbrahim ZolfagharyNo ratings yet
- Nor 66243510668Document1 pageNor 66243510668herysyam1980No ratings yet