Professional Documents
Culture Documents
437 1717 1 PB PDF
437 1717 1 PB PDF
Uploaded by
juliaCopyright:
Available Formats
You might also like
- EUDR Compliance GuidanceDocument6 pagesEUDR Compliance Guidanceyohanneshaymanot777No ratings yet
- Advance Local INMA23NYBLUETOURDocument38 pagesAdvance Local INMA23NYBLUETOURsachdevag100% (1)
- Concise Guide to OTN optical transport networksFrom EverandConcise Guide to OTN optical transport networksRating: 4 out of 5 stars4/5 (2)
- Spider Man Mask Full Size Paper Craft PDFDocument3 pagesSpider Man Mask Full Size Paper Craft PDFDiego AlejandroNo ratings yet
- Strategic Management of Resources (SMR) Practice Questions - APICS CPIMDocument17 pagesStrategic Management of Resources (SMR) Practice Questions - APICS CPIMCerticoNo ratings yet
- Sensor77 VLC Ieee Sensors JDocument9 pagesSensor77 VLC Ieee Sensors JHai LeNo ratings yet
- Relation Ref To Lifi Probgation ProblemDocument7 pagesRelation Ref To Lifi Probgation ProblemSallar S MuradNo ratings yet
- Performance of Outdoor Lamp Implementation For VisDocument6 pagesPerformance of Outdoor Lamp Implementation For Visimran1703075No ratings yet
- A Review of Visible Light Communication (VLC) Technology: Articles You May Be Interested inDocument9 pagesA Review of Visible Light Communication (VLC) Technology: Articles You May Be Interested inahmedNo ratings yet
- LIFIDocument7 pagesLIFIRajeshNo ratings yet
- Concept of Visible Light Communication and VIDAS: Navin Kumar, Luis A Nero, Rui L AguiarDocument4 pagesConcept of Visible Light Communication and VIDAS: Navin Kumar, Luis A Nero, Rui L AguiarnavinrkNo ratings yet
- Ieee802-18 IecDocument3 pagesIeee802-18 IecSurya KashyapNo ratings yet
- Design and Implementation of Visible Light Communication Using Error Correcting Turbo CodesDocument10 pagesDesign and Implementation of Visible Light Communication Using Error Correcting Turbo CodesWA Q ASNo ratings yet
- Optical Communication System V2V, Using LED Transmission and Camera ReceptionDocument14 pagesOptical Communication System V2V, Using LED Transmission and Camera ReceptionDavidReyesNo ratings yet
- Vehicle Motion and Pixel Illumination Modeling For Image Sensor Based Visible Light CommunicationDocument13 pagesVehicle Motion and Pixel Illumination Modeling For Image Sensor Based Visible Light Communicationlogu1234No ratings yet
- Mobile Phone Camera-Based Indoor Visible Light Communications With Rotation CompensationDocument9 pagesMobile Phone Camera-Based Indoor Visible Light Communications With Rotation CompensationRuchith ReddyNo ratings yet
- An LED Detection and Recognition Method Based On DDocument10 pagesAn LED Detection and Recognition Method Based On Dimran1703075No ratings yet
- 2 Lifi Based Vehicle To Vehicle CommunicationDocument50 pages2 Lifi Based Vehicle To Vehicle CommunicationCHENNAISKIVE PROJECTSNo ratings yet
- V L C H N: P W U - C D: Isible Ight Ommunications in Eterogeneous Etworks Aving The Ay For SER Entric EsignDocument9 pagesV L C H N: P W U - C D: Isible Ight Ommunications in Eterogeneous Etworks Aving The Ay For SER Entric Esigncharu dattaNo ratings yet
- VLC Challeng and PossibilitiesDocument5 pagesVLC Challeng and PossibilitiestieuphapsNo ratings yet
- Simulation of Efficient Access Point Placement Strategies in Li-Fi Network Using Point ProcessesDocument7 pagesSimulation of Efficient Access Point Placement Strategies in Li-Fi Network Using Point ProcessesKiya Key ManNo ratings yet
- Device To Device Communication Using Li-FiDocument3 pagesDevice To Device Communication Using Li-Fidab redNo ratings yet
- Lifi - Technology: A Technical Seminar ReportDocument23 pagesLifi - Technology: A Technical Seminar Reportrehana mohammed100% (1)
- Visible Light Communications Principle PDocument8 pagesVisible Light Communications Principle PJONAH ALU KALUNo ratings yet
- Ae Mte ReportDocument21 pagesAe Mte Reportkartikaysinghco20b446No ratings yet
- Transferring Data Using A Visible LightDocument6 pagesTransferring Data Using A Visible LightInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- An Overview of Visible LightDocument12 pagesAn Overview of Visible LightAIRCC - IJCNCNo ratings yet
- Audio and Video Transmission Using Visible Light TransmissionDocument4 pagesAudio and Video Transmission Using Visible Light Transmissionmuhammad usamaNo ratings yet
- Vehicle To Vehicle CommunicationDocument9 pagesVehicle To Vehicle CommunicationDarwinNo ratings yet
- IEEE2023 PhuongDocument7 pagesIEEE2023 Phuongkali_vnNo ratings yet
- Modulation Schemes For Visible Light CommunicationsDocument10 pagesModulation Schemes For Visible Light CommunicationsSuriza A ZabidiNo ratings yet
- The Technology of LiFi A Brief Introduction PDFDocument11 pagesThe Technology of LiFi A Brief Introduction PDFSreeja ReddyNo ratings yet
- Analysis of Wireless Fidelity and Light Fidelity For PAN and ImplementationDocument6 pagesAnalysis of Wireless Fidelity and Light Fidelity For PAN and ImplementationAnn RazonNo ratings yet
- Design and Implementation of A Vehicle TDocument4 pagesDesign and Implementation of A Vehicle TdgcgtwgnnNo ratings yet
- IJCT Paper 2 PP 1136 1140Document5 pagesIJCT Paper 2 PP 1136 1140erparveenkaur86No ratings yet
- Performance Investigation of Visible Light Communication System Using Optisystem Simulation ToolDocument8 pagesPerformance Investigation of Visible Light Communication System Using Optisystem Simulation ToolLuisNo ratings yet
- Visible Light Communications: Challenges and Possibilities: October 2008Document6 pagesVisible Light Communications: Challenges and Possibilities: October 2008ਡਾ. ਹਰਮੀਤ ਸਿੰਘNo ratings yet
- Shlomi ArnonDocument9 pagesShlomi Arnonhendra lamNo ratings yet
- 134 139, Tesma507, IJEASTDocument6 pages134 139, Tesma507, IJEASTRishan KundetyNo ratings yet
- 2020 An Overview of Optical Architectures Necessary To Achieve 5g S Key Performance IndicatorsDocument11 pages2020 An Overview of Optical Architectures Necessary To Achieve 5g S Key Performance IndicatorsTaha AlhatmiNo ratings yet
- VLC Case StudyDocument3 pagesVLC Case StudyVedant KaushishNo ratings yet
- Reliable High Speed Data Transmission Using Li-Fi CommunicationDocument7 pagesReliable High Speed Data Transmission Using Li-Fi CommunicationlambanaveenNo ratings yet
- 3385 Li-Fi TechnologyDocument20 pages3385 Li-Fi TechnologyMr. GyanprakashNo ratings yet
- Led-Id S: C F L R T: Ystem Overage and AST INK Ecovery EchniqueDocument13 pagesLed-Id S: C F L R T: Ystem Overage and AST INK Ecovery EchniqueijcsesNo ratings yet
- Serial and Parallel Data Transmission Through Li-FiDocument5 pagesSerial and Parallel Data Transmission Through Li-FibelaoufamiraNo ratings yet
- On Optimizing VLC Networks For Downlink Multi-User Transmission: A SurveyDocument30 pagesOn Optimizing VLC Networks For Downlink Multi-User Transmission: A Surveyhendra lambNo ratings yet
- V2X Communications With An Image SensorDocument10 pagesV2X Communications With An Image SensorBaraa MNo ratings yet
- Irjet Li Fi Technology Transmission of DDocument7 pagesIrjet Li Fi Technology Transmission of Dسدن آرماNo ratings yet
- AP - Smart Grids 61850 (EN) 2017.01Document34 pagesAP - Smart Grids 61850 (EN) 2017.01Assis JúniorNo ratings yet
- IF You Want The Original Copy of This Document Please Mail Me atDocument18 pagesIF You Want The Original Copy of This Document Please Mail Me atShashi Shekhar AcharyaNo ratings yet
- US Paper DistDocument5 pagesUS Paper DistBaraa MNo ratings yet
- Research PaperDocument4 pagesResearch PaperRaj DasNo ratings yet
- Short Range Optical Wireless Communications For Indoor and Interconnects ApplicationsDocument10 pagesShort Range Optical Wireless Communications For Indoor and Interconnects Applicationszeadzizo715No ratings yet
- Design of Li-Fi Technology Based Underwater Data Communication System Using IotDocument11 pagesDesign of Li-Fi Technology Based Underwater Data Communication System Using IotdgcgtwgnnNo ratings yet
- Optical Distribution Network Evolution - 24feb2023Document14 pagesOptical Distribution Network Evolution - 24feb2023Zarroug HoussemNo ratings yet
- Detection and Recognition of RGB-LED Based On Visible Light Communication Using Covoltional Neural NetworkDocument12 pagesDetection and Recognition of RGB-LED Based On Visible Light Communication Using Covoltional Neural Networkphamdonhuhuynh11lnhom11.1No ratings yet
- Data Transmission Using Lifi: Dhirajlal Gandhi College of TechnologyDocument10 pagesData Transmission Using Lifi: Dhirajlal Gandhi College of TechnologyMuhammad AwaisNo ratings yet
- Audio Transmission Using Visible Light Communication Technology With Pre-Equalization TechniqueDocument8 pagesAudio Transmission Using Visible Light Communication Technology With Pre-Equalization TechniqueIJRASETPublicationsNo ratings yet
- Smart and Energy Efficient Led Street Light Control System Using Zigbee NetworkDocument5 pagesSmart and Energy Efficient Led Street Light Control System Using Zigbee NetworkVishwaraj BhagwatNo ratings yet
- Mini Project Report (P)Document16 pagesMini Project Report (P)Pranav BhaleraoNo ratings yet
- A Technical Seminar On Visible Light Communication: Vikas R 1HK10CS085Document30 pagesA Technical Seminar On Visible Light Communication: Vikas R 1HK10CS085vikas11031992No ratings yet
- Proposed Framework For V2V Communication Using Li-Fi TechnologyDocument4 pagesProposed Framework For V2V Communication Using Li-Fi TechnologyBrightworld ProjectsNo ratings yet
- Reference Guide OTNDocument60 pagesReference Guide OTNjoaquic100% (1)
- Accounting - Foundation Course 2023-24Document5 pagesAccounting - Foundation Course 2023-24Zoom MailNo ratings yet
- UNIT 1 Introduction To SPM, Project Evaluation Project PlanningDocument7 pagesUNIT 1 Introduction To SPM, Project Evaluation Project PlanningRamZ SkullyNo ratings yet
- Agile Questions Set 1Document19 pagesAgile Questions Set 1Zain NisarNo ratings yet
- Jawaban Latihan SoalDocument31 pagesJawaban Latihan SoalRizalMawardiNo ratings yet
- Basic Information of Multi-National Company: Guided by Dr. Navjyot RavalDocument14 pagesBasic Information of Multi-National Company: Guided by Dr. Navjyot RavalAxay PatelNo ratings yet
- Study Notes Trading StrategiesDocument16 pagesStudy Notes Trading Strategiesalok kundaliaNo ratings yet
- Bottom and Shell Bom - Up12Document27 pagesBottom and Shell Bom - Up12Karthimeena MeenaNo ratings yet
- Matrikulasi Bahasa InggrisDocument5 pagesMatrikulasi Bahasa InggrisMr DAY DAYNo ratings yet
- Single Entry SystemDocument4 pagesSingle Entry Systemanurags pageNo ratings yet
- Entrepreneurship Development and InnovationDocument6 pagesEntrepreneurship Development and Innovationvamsi krishnaNo ratings yet
- MDOT Secretary Slater Letter - TeleworkDocument2 pagesMDOT Secretary Slater Letter - TeleworkAnonymous sKgTCo2100% (1)
- Summary of IAS 40Document2 pagesSummary of IAS 40Zes ONo ratings yet
- Lubricant Oil System MaintenanceDocument2 pagesLubricant Oil System MaintenancePaul AbonitaNo ratings yet
- FS00055 - Mohammad Parwez-188202215227Document3 pagesFS00055 - Mohammad Parwez-188202215227K DNo ratings yet
- National Union of Workers in Hotel Restaurant and Allied Industries (NUWHRAIN - APL-IUF) v. Philippine Plaza Holdings, IncDocument3 pagesNational Union of Workers in Hotel Restaurant and Allied Industries (NUWHRAIN - APL-IUF) v. Philippine Plaza Holdings, IncKobe Lawrence VeneracionNo ratings yet
- Leave and License Agreement: Particulars Amount Paid GRN/Transaction Id DateDocument5 pagesLeave and License Agreement: Particulars Amount Paid GRN/Transaction Id DateAvi MarodkarNo ratings yet
- Seatwork # 1Document2 pagesSeatwork # 1Joyce Anne GarduqueNo ratings yet
- Lesson-3 EeDocument15 pagesLesson-3 EeChristian MagdangalNo ratings yet
- Dissertation On BrexitDocument5 pagesDissertation On BrexitWriteMyPaperCollegeUK100% (1)
- Notice of Post-DisqualificationDocument2 pagesNotice of Post-DisqualificationLiwayway MadaliNo ratings yet
- Be A Pirate StoryDocument14 pagesBe A Pirate StorySemira FocoNo ratings yet
- FG - ASCQ3109 - Welding and Quality Technician - Final - PKG - 01.08.2019 PDFDocument390 pagesFG - ASCQ3109 - Welding and Quality Technician - Final - PKG - 01.08.2019 PDFJim KaliNo ratings yet
- Formation of Business OrganizationDocument28 pagesFormation of Business OrganizationJichang HikNo ratings yet
- Bid Document For T2 of 2015Document23 pagesBid Document For T2 of 2015Donald SolomonNo ratings yet
- RAO (Autosaved)2019Document26 pagesRAO (Autosaved)2019Barangay Poblacion NaawanNo ratings yet
- CHP 7 Strategy and StructureDocument21 pagesCHP 7 Strategy and StructureBBHR20-A1 Wang Jing TingNo ratings yet
437 1717 1 PB PDF
437 1717 1 PB PDF
Uploaded by
juliaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
437 1717 1 PB PDF
437 1717 1 PB PDF
Uploaded by
juliaCopyright:
Available Formats
IIAI International Journal of Service and Knowledge Management
International Institute of Applied Informatics
2019, Vol. 3, No. 2, 35 – 47
Secure Architecture of Visible Light Communication
System for Market Expansion
Shigeaki Tanimoto *, Chise Nakamura *, Motoi Iwashita *,
Shinsuke Matsui *, Takashi Hatashima †, Hitoshi Fuji †,
Kazuhiko Ohkubo †, Junichi Egawa ‡, Yohsuke Kinouchi §
Abstract
Progress in visible light technology has provided increased opportunities for new mobile com-
munication infrastructures and business creation using visible light communication (VLC). This
paper proposes a secure business architecture for VLC market expansion through a combination
of VLC technologies, public key cryptography, power line communication, and ID management
technology. The proposed architecture provides the light source of an LED with an optical lo-
cation authentication ID characterized by a strict location authentication that enciphers data us-
ing public key cryptography. The network between the server for distributing the optical location
authentication ID and the LED light source enables high security using power line communica-
tion. In addition, scalability can be achieved securely by means of the ID management tech-
nology. The results of an evaluation clarified the suitability of this architecture for utilization in
concrete business services. Used in combination with VLC, it will contribute to the market ex-
pansion of new business related to optical electronic value trading platforms, optical digital
signage, and optical Fintech.
Keywords: Location Authentication, Optical Location Authentication ID, Visible Light Com-
munication, Public Key Cryptography, ID Management
1 Introduction
The global trend towards environmental protection aimed at a low carbon society is prompting
changes and advancements in the field of optical lighting. The systematic replacement of
old incandescent lamps with light emitting diode (LED) electric light has enabled substantial
* Chiba Institute of Technology, Chiba, Japan
† NTT Secure Platform Laboratories, Tokyo, Japan
‡ EXGEN NETWORKS Co., Ltd., Tokyo, Japan
§ Tokushima University, Tokushima, Japan
36 S. Tanimoto, C. Nakamura, M. Iwashita, S. Matsui, T. Hatashima, H. Fuji, K. Ohkubo, J. Egawa, Y. Kinouchi
power savings along with lower CO2 emissions. The utilization of LEDs in visible light
communication (VLC) has also attracted attention, and new telecom infrastructures brought
about thanks to cooperation with power line communication has emerged [1] – [4].
Mobile communication traffic generated by cellular and smartphone usage is increasing, so
VLC has generated high interest. The amount of traffic related to mobile communications in
2016 was 18 times than that in 2011 and 2.6 times than that in 2014, and the demand for mobile
communication is only expected to increase [5] – [6]. These trends have led to an increased in-
terest in optical space communication using visible light for implementation in mobile commu-
nication. Moreover, the communication path can be seen as light, in contrast to radio waves,
which is advantageous because the secure side of the information disclosure range can be limited
to VLC.
The Visible Light Communication Consortium (VLCC) in Japan is now focused on stand-
ardization activities. A standard method for VLC was enacted by the Japan Electronics and In-
formation Technology Industries Association (JEITA) in 2006 [7] A business architecture uti-
lizing this method has been proposed, and communication infrastructure as a new source of VLC
has been developed. For example, many broadcast services linked to locations, such as
on-the-spot explanations of art museums and information distribution linked with digital signage,
have been appearing [8] – [10]. However, these models do not have satisfactory security.
In light of this background, in this paper, we propose an architecture of secure VLC by at-
taching “optical location authentication ID” information to the light source (LED) of VLC in
combination with public key encryption and ID management technology [11] – [13]. We provide
the details of this architecture and evaluate its effectiveness through an examination of several
concrete service cases.
In the following, Section 2 of this paper goes over the problems facing the current VLC sys-
tems and business architectures and clarifies the necessity of a more secure design. We propose a
secure business architecture using a VLC system in Section 3 and evaluate its effectiveness
through an examination of concrete service cases in Section 4. We conclude in Section 5 with a
brief summary and mention of future work.
2 Issues of Current Business Architecture with VLC
2.1 Current VLC Systems
As shown in Fig. 1(a), a typical VLC system performs data communication by means of rapidly
blinking LEDs at a speed so fast that it cannot be perceived by the human eye [1] – [2]. VLC
includes the transmission and reception of the characteristic data (ID) of a location and other
relevant details.
As shown in Fig. 1(b), a digital modulation signal is placed on the spot where the area fixed by
the light source is irradiated. Accordingly, IDs can be transmitted from a light source [8], [14].
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
Secure Architecture of Visible Light Communication System for Market Expansion 37
Transmission data
Light source
Modulation circuit
LED
driver
Visible light Circuit
LED
Visible light
Photo
Detector
Amplifier
circuit
Demodulation circuit
Receiving side
device
Received data
(a) Image of VLC (b) Principle of VLC
Figure 1: Principle of data communications using VLC.
2.2 Issues of Current VLC Business Architecture
As shown in Fig. 2, the business architecture using VLC is a broadcast service linked to a loca-
tion and is used for tasks such as on-the-spot explanations at a museum and information distri-
bution linked with digital signage [8] – [10]. Security measures are largely unnecessary because
the usage is small scale.
However, the use of location information for car navigation systems and GPS pedestrian
navigation using mobile phones is rapidly spreading, and location information is becoming in-
creasingly important [15]. This means that, even in VLC, examining security measures is crucial
in terms of promoting business applications in the future. Incidentally, an international standard
(ISO 15408, Common Criteria) is now used for computer security in software development [16]
– [17]. Moreover, the concept of security-by-design, which considers the importance of how
security is ensured right from the initial processes of the planning and design phases, has been
proposed [18]. The aims of these proposals include reducing the cost of total security counter-
measures and efficiently developing good software by investigating security countermeasures
during the early stages of development.
From the above, the importance of considering security measures from the viewpoint of
business architecture is clear. However, in the current VLC business architecture, this is not yet
being done at a sufficient level.
Visible light Visible light
(a) Spot explanation of the museum (b) Information distribution with signage
Figure 2: Typical business architecture using VLC.
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
38 S. Tanimoto, C. Nakamura, M. Iwashita, S. Matsui, T. Hatashima, H. Fuji, K. Ohkubo, J. Egawa, Y. Kinouchi
3 Proposal of Secure Business Architecture using VLC
3.1 Requirement Specifications
Here, we clarify the requirement specifications for implementing a VLC system into business.
Obviously, the authentication function, the encryption function, and network security are indis-
pensable here. Next, existing functions are used to reduce costs when introducing these functions.
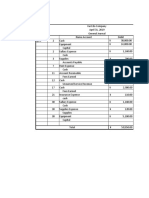
Table 1 lists the required specifications, which we briefly describe below.
Table 1: Requirement specifications and existing functions for VLC.
Requirement specifications Corresponding existing function
・Public Key Cryptography
Authentication function
・Identity Management Technology
Encryption function ・Public Key Cryptography
・Public Key Cryptography
Network security
・Power Line Communication (PLC)
3.1.1 Public Key Cryptography
Public key infrastructure means the security infrastructure for a public key cryptosystem. As
shown in Fig. 3, this technology enables various security countermeasures, such as encryption,
digital signatures, and certification.
Public key Different Key Secret key
Plain Crypto- Plain
Encryption Decryption
text gram text
An enciphering key and a decryption key are different keys.
Figure 3: Public Key Cryptosystem.
3.1.2 Power Line Communication (PLC)
This type of communication refers to the technique of using a power line as a conduit for
communication. Low-speed PLC uses frequencies of 450 kHz or less, and high-speed PLC uses
frequencies of 2 to 30 MHz. In Japan, the Ministry of Internal Affairs and Communications
revised a ministerial ordinance in October 2006 by adding an item that restricts indoor usage and
that will accept 2–30-MHz frequency usage. Products corresponding to high-speed power line
communication have been in distribution from December 2006 onward in response to this min-
isterial ordinance revision [19] – [20]. An example of PLC connected to a normal outlet is shown
in Fig. 4 [20].
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
Secure Architecture of Visible Light Communication System for Market Expansion 39
Power Line
PLC PLC
Internet
Figure 4: Usage pattern of PLC.
3.1.3 ID Management Technology
ID management guarantees the validity of the ID and provides a mechanism of access control
(i.e., only people with the appropriate authority can gain access to need-to-know information).
Combining the ID management infrastructure with the optical location authentication ID guar-
antees the validity of the optical location authentication ID and enables thorough control access
by the administrator. As shown in Fig. 5, an ID management infrastructure using Shibboleth
provides the system with a user ID and enables unified management of authority [21].
Using an ID management base among multiple organizations requires creating a policy for the
operation management of the optical location authentication IDs. In addition, the structure of the
operation (called a trust framework) has to be taken into account, including the audits for making
this policy observed.
User
Web Browser 1
2
3
4
IdP: Identity Provider SP: Service Provider
1. The SP detects the user attempting to access restricted content within the
resource.
2. The SP generates an authentication request, then sends the request, and the
user, to the user's IdP.
3. The IdP authenticates the user, then sends the authentication response, and
the user, back to the SP.
4. The SP verifies the IdP's response and sends the request through to the
resource which returns the originally requested content.
Figure 5: Example of ID management by Shibboleth [21].
3.2 Proposal of Secure Business Architecture of VLC
Here, we present a secure business architecture plan with functions that satisfy the requirement
specifications shown in Table 1 for a VLC system [11]–[13].
3.2.1 Basic Architecture of Secure VLC
(1) Service flow from distribution of optical location authentication ID to user reception
Figure 6 shows how security is guaranteed by combining the new VLC system with 1) public
key cryptography and 2) power line communication. Respective procedures for the service pro-
vision side and the user side are performed as follows.
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
40 S. Tanimoto, C. Nakamura, M. Iwashita, S. Matsui, T. Hatashima, H. Fuji, K. Ohkubo, J. Egawa, Y. Kinouchi
(Location authentication Service Provider side (Fig. 6))
① Enter the optical location authentication ID corresponding to the location of the light source
② Create public key and secret key of the optical location authentication ID
③ Distribute the public key of the optical location authentication ID corresponding to the light
source on the Web page
④ Encrypt the optical location authentication ID with the secret key corresponding to the light
source (LED)
-> enc (optical location authentication ID, secret key)
(User side (Fig. 6))
⑤ Obtain the public key of the optical location authentication ID from the Web page
⑥ Decrypt the encrypted data received from the VLC system with the public key of the optical
location authentication ID
-> dec (enc (optical location authentication ID, secret key), public key)
In this way, the user receives the optical location authentication ID and can access the service
associated with it.
Administrator
Define services corresponding to the optical
1) OMS: location authentication ID information in
Optical location authentication advance between OMS and SP 4) SP:
Management Server Service Provider
Pre-processing
①Enter the optical location authentication ID corresponding
to the location of the light source
②Creating public key and secret key of the optical location ③ Distributing the public key of the optical
authentication ID location authentication ID corresponding Location
④ Encrypting the optical location authentication ID with to the light source on the webpage
the secret key corresponding to the light source (LED) authentication
→ enc (optical location authentication ID,secret key) Service Provider
side
2) PLC:
Power line
communication User side
Internet
3) VLC:
Transmission data
Visible light
communication Modulation circuit
system
LED
drive
circuit
LED
⑤ The user obtains the public key of the
④ Distribution of encrypted data
optical location authentication ID from
using visible light communication
the webpage
→ enc (optical location authentication ID,secret key)
Move to the light User
source location
⑥ The user decrypts the encrypted data received from the visible light communication
system with the public key of the optical location authentication ID
User → dec (enc (optical location authentication ID,secret key), public key)
As a result, the user can receive the optical location authentication ID
Figure 6: Basic architecture of secure VLC.
(2) Service utilization flow using optical location authentication ID
After receiving the optical location authentication ID, the user can use the service associated
with it, as shown in Fig. 7. Hereinafter, we refer to the optical location authentication base as the
optical location authentication service provider (OLASP).
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
Secure Architecture of Visible Light Communication System for Market Expansion 41
*1; Here, we integrated the system configuration
((1) OMS, (2) PLC, (3) VLC) as an optical
location information authentication service
provider (OLASP).
1) OMS: ③ Validation of the optical location
Optical location authentication ID OK
authentication
Management Server
OLASP: SP*2:
Simplification
2) PLC: indication*1 Optical Location ② Confirm the optical Service
Power line Authentication location authentication ID Provider
communication to LASP
Service Provider
3) VLC: ① Login with the
Visible light optical location
authentication ID *2; Define services
communication
enc (optical location corresponding to
system
authentication ID,secret key) optical location
authentication ID
④ Service information in
Acquisition of the optical delivery advance between
location authentication ID OLASP and SP
with public key*3
*3; dec (enc (optical location authentication ID,secret key),
User public key)
Figure 7: Service usage flow of basic architecture using optical location authentication ID.
3.2.2 Extended Architecture of Secure VLC
Sub section 3.2.1 clarified the basic architecture of the location authentication infrastructure
using the optical location authentication ID for the light source. Here, we propose cooperation
with ID management from the viewpoint of scalability of the optical location authentication
infrastructure. From the viewpoint of the service extensibility, the optical location authentication
infrastructure needs to be installed in many places (locations). In this case, multiple optical lo-
cation authentication service providers (OLASP) in the basic architecture shown in sub section
3.2.1 are also generated in the optical location authentication infrastructure. Furthermore, in
consideration of the scalability of the optical location authentication utilization service, man-
agement of these services is facilitated by using an intermediary between the OLASP and various
service providers (SP).
In general, two ideas have been suggested for this intermediary: Idea 1) use of a certificate
authority (issue digital certificate to optical location authentication ID) and Idea 2) use of ID
management infrastructure [13]. In light of the strictness of the optical location authentication,
using a certificate authority (Idea 1) is a superior idea. On the other hand, when users need to
provide certificates, economic difficulties are incurred due to the cost of issuing certificates at the
optical location authentication service provider side. Using the ID management infrastructure
(Idea 2) centrally manages the optical location authentication ID by setting up the ID manage-
ment infrastructure (described in sub section 3.1.3), so it is significantly superior to Idea 1 in
terms of economic efficiency. Therefore, from the viewpoint of business, using the ID man-
agement infrastructure (Idea 1) is desirable as an extension of the optical location authentication
ID [13].
(1) Service flow from distribution of optical location authentication ID to user reception
Figure 8 shows the extended architecture of the optical location authentication infrastructure
using the VLC system utilizing the ID management infrastructure. A location authentication ID
management infrastructure (LA_IDP) is newly provided as an ID management. In this case, the
extension is as follows.
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
42 S. Tanimoto, C. Nakamura, M. Iwashita, S. Matsui, T. Hatashima, H. Fuji, K. Ohkubo, J. Egawa, Y. Kinouchi
(a) Pre-processing
In advance, the OLASP registers the optical location authentication ID in the optical location
authentication ID management provider (LA _ IDP).
(b) From distribution of optical location authentication ID to user reception
The service flow from the delivery of the optical location authentication ID to the reception of
the user (Fig. 8) is the same as the basic architecture outlined in sub section 3.2.1.
In advance, the optical location
Administrator authentication ID and the location
information thereof are registered in the IDP.
4) LA_IDP: 5) SP:
1) OMS: Location Service Provider
Optical location authentication authentication ID
Management Server Pre-processing management provider
①Enter the optical location authentication ID corresponding
to the location of the light source
②Creating public key and secret key of the optical location Define services corresponding to optical
authentication ID ③ Distributing the public key of the optical location authentication ID information in
④ Encrypting the optical location authentication ID with location authentication ID corresponding advance between OMS and SP
the secret key corresponding to the light source (LED) to the light source on the webpage
→ enc (optical location authentication ID,secret key)
2) PLC: Location
Power line authentication
communication
Service Provider
OLASP: side
Optical Location
Authentication
Service Provider 3) VLC: Internet
Transmission data
Visible light User side
communication Modulation circuit
system
LED
drive
circuit
LED
④ Distribution of encrypted ⑤ The user obtains the public key of
data using visible light the optical location authentication
communication ID from the webpage.
→ enc (optical location authentication ID,secret key)
User
Move to the light source location
⑥ The user decrypts the encrypted data received from the visible light
communication system with the public key
→ dec (enc (optical location authentication ID,secret key), public key)
User As a result, the user can receive the optical location authentication ID
Figure 8: Extended architecture of secure VLC.
(2) Service utilization flow using optical location authentication ID
After receiving the optical location authentication ID, the user can access the associated
service. An example of service utilization using the ID management infrastructure
(LA_IDP) is shown in Fig. 9.
① The user logs in to the SP (in this case, SP no.1) by using the optical location authentication
ID no. i in order to use the service.
② SP no. 1 confirms the validity of the optical location authentication ID no. i with the optical
location authentication ID management provider (LA_IDP).
③ From the optical location authentication ID management provider, the verification result
(“OK” in this case) of the optical location authentication ID no. i is received.
④ SP no. 1 provides the service to the user.
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
Secure Architecture of Visible Light Communication System for Market Expansion 43
LA_IDP:
Location authentication
③ Confirmation OK of optical
ID management provider
Pre-processing
location authentication ID no. i
The optical location information ID
and the location information thereof
are registered in the IDP. ② Confirmation of
optical location SP SP
authentication ID no. i
no.1 no. n
OLA OLA to LA_IDP
SP no. 1 SP no. n ① Log in with SP:Service Provider
optical location
authentication
ID no. i
enc (optical location enc (optical location
authentication ID no. 1, authentication ID no. n, ④ Service
secret key no.1) secret key no.n) delivery to User
Acquisition of location
authentication ID no.i,
(i = 1,2, , n)
User Moved to the light source location
Figure 9: Service usage flow of extended architecture using optical location authentication ID.
3.3 Features of proposed business architecture
Sub section 3.2.1 clarified the basic architecture of the location authentication infrastructure
using the optical location authentication ID for the light source. In sub section 3.2.2, we proposed
cooperation with ID management from the viewpoint of scalability of the optical location au-
thentication infrastructure.
As described above, the key feature of the proposed model is that the existing VLC system is
linked with multiple existing secure technologies such as public key encryption, power line
communication, and ID management. Specifically, as shown in Table 2, we added security
functions to the conventional visible light communication system through cooperation with
existing technologies. Furthermore, by distributing part of the authentication information (public
key of the optical authentication ID) on the Internet, the expandability of the business of the
visible light communication system is guaranteed.
Table 2: Features of the proposed model.
Viewpoint of
Technical features Application technology
modeling
Public key cryptography
Strict identification of users by intro-
ID management infrastructure
ducing ID management
technology
Security
Limited information distribution of Visible light communication
guarantee
visible light communication recipients technology
Information circulation limited to Power line communication
power line communication network technology
Expansibility
of conducting ID distribution by the Internet Internet security technology
business
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
44 S. Tanimoto, C. Nakamura, M. Iwashita, S. Matsui, T. Hatashima, H. Fuji, K. Ohkubo, J. Egawa, Y. Kinouchi
4 Use Case of Secure Business Architecture Using VLC
This section presents an evaluation of real operability with an application to actual business using
the secure business architecture proposed in Section 3.
4.1 Use Case as a Business Architecture
As shown in Figs. 6 and 8, the proposed architecture improves on the conventional VLC system
by enabling public key cryptography, power line communication, ID management infrastructure,
and existing systems to cooperate. The key advantage here is that a strict location authentication
infrastructure can be provided by means of the optical location authentication IDs. This is ex-
pected to promote various kinds of business creation and applications. In the following, we
evaluate the proposed model on the basis of concrete business.
(1) B2C tourism industry
The optical location authentication ID and the public key cryptography technology can be ap-
plied to the tourism industry, where strict location authentication of users is possible. First, light
sources can be installed in tourist spots. The light source is given an optical location authentica-
tion ID (Fig. 6 ①) and encrypted using a secret key (Fig. 6 ④). Next, the sightseeing spot asso-
ciated with OMS distributes a public key (Fig. 6 ③) corresponding to the optical location au-
thentication ID through its own Web page. Users (in this case, tourists) obtain the public key (Fig.
6 ⑤) from the Web page and visit the sightseeing spot. This allows them to receive their optical
location authentication ID (Fig. 6 ⑥) from the light source using VLC.
In this case, linking the optical location authentication ID to tourists with discount tickets
(electronic value) in the tourist spot enables the user to receive the intended benefits. In other
words, added value (e.g., discount tickets) can be given exclusively to tourists who visit the
tourist spots without fail, thereby improving the cost effectiveness of the tickets. In this way, the
electronic value can be distributed only to specific users (in this case, tourists who obtain a public
key after viewing the Web page).
In the same way, this concept can be applied to location authentication services for YouTubers
by enabling rigorous location authentication. If YouTubers go to a specific sightseeing area and
send locational proof, more reliable information can be sent, and the number of views can be
expected to increase.
(2) The B2C advertising industry
Similarly, in the case of digital signage (where a sign is a light source), the security performance
of a service provider can be improved by utilizing public key cryptography. In addition, the ef-
fectiveness of advertisements can be improved using digital signage because the system can
strictly confirm that an intended user has come to the location of the digital sign.
(3) Optical Fintech
The proposed architecture can also be applied to Fintech. The new optical location authentication
ID can be utilized as a base for distributing electronic value, as in the aforementioned tourist
spots example.
(4) Other business applications
The following business adaptations are also possible.
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
Secure Architecture of Visible Light Communication System for Market Expansion 45
- Education: A system for managing attendance. A light source for classrooms. Students
are not allowed to attend unless they are actually in the class.
- Entertainment: Orienteering. The user can prove that he or she actually went to the
designated spot by acquiring the optical location authentication ID of the light source
set at various points.
4.2 Consideration
The key idea of the proposed model (as shown in Figs. 6 and 8) is that, by incorporating cryp-
tographic technology into conventional VLC, it is possible to strictly specify which user visited
the location of the light source. As a result, as shown in Section 4.1, it becomes possible to use
B-C type business and even strict location authentication for electronic value distribution. In
other words, by utilizing VLC, we can achieve a new electronic value distribution infrastructure
(optical FinTech infrastructure).
Figure 10 shows the extendibility of the existing VLC business with this proposed architecture.
Although qualitative, the results clearly show that business broadening by the extension of reli-
ability based on strengthening the security function is possible.
Business
Expandability
Wide area
Optical
Fintech
Region area Tourist Discount
Service
Secure Optical location
Spot authentication ID +
Service Optical location IDP
authentication ID
In a building Service of
Attendance
Visit Proof
Management
Spot
Service
Secure Orienteering
Digital
Digital
Signage
Signage
Security
Existing VLC Secure VLC Service Secure VLC Service Strength
Service (Basic Architecture) (Extended Architecture)
Figure 10: Scalability evaluation result of VLC business based on enhancement of security
function.
5 Conclusion and Future Work
In this paper, in light of the ongoing spread of VLC development, we proposed a secure business
architecture using our previously researched concept, “optical location authentication ID” in-
formation, by combining an ID management function with a location authentication infrastruc-
ture on the basis of multiple VLC systems. A qualitative comparative evaluation demonstrated
that it is possible to construct a secure business model using this architecture.
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
46 S. Tanimoto, C. Nakamura, M. Iwashita, S. Matsui, T. Hatashima, H. Fuji, K. Ohkubo, J. Egawa, Y. Kinouchi
In future work, we will evaluate the infrastructure in real-world situations using an actual
system configuration. An accounting function will also be added for increased functionality.
References
[1] T. Komine,M. Nakagawa, Fundamental analysis for visible-light communication system
using LED lights,IEEE Transactions on Consumer Electronics, Vol. 50, No. 1, pp.100-107,
FEBRUARY 2004
[2] L. Grobe, et al., High-Speed Visible Light Communication Systems, IEEE Communications
Magazine, pp.60-66, Dec., 2013
[3] T. Komine and M. Nakagawa, Integrated System of White LED Visible-Light Communica-
tion and Power-Line Communication, IEEE Transactions on Consumer Electronics, Vol. 49,
No. 1, pp.71-79, FEBRUARY 2003
[4] S. Shimada, Y. Takeda, Trends in Visible Light Communication and Application to ITS,
Toshiba Review, Vol.64, No.4, pp.27-30, 2009, in Japanese
[5] H. Saini, LI-FI (LIGHT FIDELITY)-THE FUTURE TECHNOLOGY IN WIRELESS
COMMUNICATION, Journal of Computer Application, Volume 7, No. 1, pp.13-15, January,
2016
[6] Psychic thought, The next "Li-Fi" coming after Wi-Fi - Relationship between Li-Fi and 5G in
IoT era -, http://blog.livedoor.jp/utakknn/archives/2017-01-15.html, in Japanese, 2017
[7] Visible Light Communication Consortium, About a standard, http://vlca.jp/standard/, in
Japanese, 2014
[8] Panasonic, Started business of information linkage service using "optical ID" technology,
https://news.panasonic.com/jp/press/data/2015/12/jn151209-3/jn151209-3.html, in Japanese,
in Japanese, 2015
[9] Nakagawa Lab., Inc., Products Information, http://www.naka-lab.jp/product/index_e.html,
2018
[10] K. Suzuki, Visible Light Communication System for Application to ITS, Toshiba Review,
Vol.61, No.8, pp.20-23, 2006, in Japanese
[11] S. Tanimoto, et al., Concept Model of Electronic Value Trading Platform with Visible Light,
Proceedings of LED synthesis forum 2018 in Tokushima, P-25, pp.157-158, 2018
[12] S. Tanimoto, et al., Proposal of Secure Business Architecture by Visible Light Communi-
cation System, Proceedings of 7th International Congress on Advanced Applied Informatics,
pp.817-822, Yonago, July, 2018
[13] S. Tanimoto, et al., Secure Visible Light Communication Business Architecture Based on
Federation of ID Management, Advances in Network-Based Information Systems, The 21st
International Conference on Network-Based In-formation Systems (NBiS-2018), pp.
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
Secure Architecture of Visible Light Communication System for Market Expansion 47
578–589, Springer, ISBN 978-3-319-98529-9, 2019
[14] H. Ueno, et al., Visible Light ID System, Toshiba Review, Vol.62, No.5, pp.44-47, 2007, in
Japanese
[15] Y. Takahashi et al., The Study for the Position Authentication and the Security of Location
Information, CSEC-38, pp.1-6, IPSJ, 2007
[16] ISO, ISO/IEC 15408-1:2009, https://www.iso.org/standard/50341.html
[17] S. Tsujii, Paradigm of Information Security as Interdisciplinary Comprehensive Science,
Proceedings of the 2004 International Conference on Cyberworlds (CW'04), pp.1-12, 2004
[18] T. Kaneko, Introduction to security by design, https://www.ipa.go.jp/files/000055823.pdf,
in Japanese, 2016
[19] Kobelco Systems, Internet connected to an outlet? ! -What is PLC (Power Line Commu-
nications) -, http://www.kobelcosys.co.jp/column/itwords/42/, in Japanese, 2007
[20] CNET Japan, Currently the "HD-PLC" communication standard using power lines,
https://japan.cnet.com/article/35089788/, in Japanese, 2016
[21] Shibboleth, Component Interface,
https://wiki.shibboleth.net/confluence/display/CONCEPT/Home, 2017
Copyright © by IIAI. Unauthorized reproduction of this article is prohibited.
You might also like
- EUDR Compliance GuidanceDocument6 pagesEUDR Compliance Guidanceyohanneshaymanot777No ratings yet
- Advance Local INMA23NYBLUETOURDocument38 pagesAdvance Local INMA23NYBLUETOURsachdevag100% (1)
- Concise Guide to OTN optical transport networksFrom EverandConcise Guide to OTN optical transport networksRating: 4 out of 5 stars4/5 (2)
- Spider Man Mask Full Size Paper Craft PDFDocument3 pagesSpider Man Mask Full Size Paper Craft PDFDiego AlejandroNo ratings yet
- Strategic Management of Resources (SMR) Practice Questions - APICS CPIMDocument17 pagesStrategic Management of Resources (SMR) Practice Questions - APICS CPIMCerticoNo ratings yet
- Sensor77 VLC Ieee Sensors JDocument9 pagesSensor77 VLC Ieee Sensors JHai LeNo ratings yet
- Relation Ref To Lifi Probgation ProblemDocument7 pagesRelation Ref To Lifi Probgation ProblemSallar S MuradNo ratings yet
- Performance of Outdoor Lamp Implementation For VisDocument6 pagesPerformance of Outdoor Lamp Implementation For Visimran1703075No ratings yet
- A Review of Visible Light Communication (VLC) Technology: Articles You May Be Interested inDocument9 pagesA Review of Visible Light Communication (VLC) Technology: Articles You May Be Interested inahmedNo ratings yet
- LIFIDocument7 pagesLIFIRajeshNo ratings yet
- Concept of Visible Light Communication and VIDAS: Navin Kumar, Luis A Nero, Rui L AguiarDocument4 pagesConcept of Visible Light Communication and VIDAS: Navin Kumar, Luis A Nero, Rui L AguiarnavinrkNo ratings yet
- Ieee802-18 IecDocument3 pagesIeee802-18 IecSurya KashyapNo ratings yet
- Design and Implementation of Visible Light Communication Using Error Correcting Turbo CodesDocument10 pagesDesign and Implementation of Visible Light Communication Using Error Correcting Turbo CodesWA Q ASNo ratings yet
- Optical Communication System V2V, Using LED Transmission and Camera ReceptionDocument14 pagesOptical Communication System V2V, Using LED Transmission and Camera ReceptionDavidReyesNo ratings yet
- Vehicle Motion and Pixel Illumination Modeling For Image Sensor Based Visible Light CommunicationDocument13 pagesVehicle Motion and Pixel Illumination Modeling For Image Sensor Based Visible Light Communicationlogu1234No ratings yet
- Mobile Phone Camera-Based Indoor Visible Light Communications With Rotation CompensationDocument9 pagesMobile Phone Camera-Based Indoor Visible Light Communications With Rotation CompensationRuchith ReddyNo ratings yet
- An LED Detection and Recognition Method Based On DDocument10 pagesAn LED Detection and Recognition Method Based On Dimran1703075No ratings yet
- 2 Lifi Based Vehicle To Vehicle CommunicationDocument50 pages2 Lifi Based Vehicle To Vehicle CommunicationCHENNAISKIVE PROJECTSNo ratings yet
- V L C H N: P W U - C D: Isible Ight Ommunications in Eterogeneous Etworks Aving The Ay For SER Entric EsignDocument9 pagesV L C H N: P W U - C D: Isible Ight Ommunications in Eterogeneous Etworks Aving The Ay For SER Entric Esigncharu dattaNo ratings yet
- VLC Challeng and PossibilitiesDocument5 pagesVLC Challeng and PossibilitiestieuphapsNo ratings yet
- Simulation of Efficient Access Point Placement Strategies in Li-Fi Network Using Point ProcessesDocument7 pagesSimulation of Efficient Access Point Placement Strategies in Li-Fi Network Using Point ProcessesKiya Key ManNo ratings yet
- Device To Device Communication Using Li-FiDocument3 pagesDevice To Device Communication Using Li-Fidab redNo ratings yet
- Lifi - Technology: A Technical Seminar ReportDocument23 pagesLifi - Technology: A Technical Seminar Reportrehana mohammed100% (1)
- Visible Light Communications Principle PDocument8 pagesVisible Light Communications Principle PJONAH ALU KALUNo ratings yet
- Ae Mte ReportDocument21 pagesAe Mte Reportkartikaysinghco20b446No ratings yet
- Transferring Data Using A Visible LightDocument6 pagesTransferring Data Using A Visible LightInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- An Overview of Visible LightDocument12 pagesAn Overview of Visible LightAIRCC - IJCNCNo ratings yet
- Audio and Video Transmission Using Visible Light TransmissionDocument4 pagesAudio and Video Transmission Using Visible Light Transmissionmuhammad usamaNo ratings yet
- Vehicle To Vehicle CommunicationDocument9 pagesVehicle To Vehicle CommunicationDarwinNo ratings yet
- IEEE2023 PhuongDocument7 pagesIEEE2023 Phuongkali_vnNo ratings yet
- Modulation Schemes For Visible Light CommunicationsDocument10 pagesModulation Schemes For Visible Light CommunicationsSuriza A ZabidiNo ratings yet
- The Technology of LiFi A Brief Introduction PDFDocument11 pagesThe Technology of LiFi A Brief Introduction PDFSreeja ReddyNo ratings yet
- Analysis of Wireless Fidelity and Light Fidelity For PAN and ImplementationDocument6 pagesAnalysis of Wireless Fidelity and Light Fidelity For PAN and ImplementationAnn RazonNo ratings yet
- Design and Implementation of A Vehicle TDocument4 pagesDesign and Implementation of A Vehicle TdgcgtwgnnNo ratings yet
- IJCT Paper 2 PP 1136 1140Document5 pagesIJCT Paper 2 PP 1136 1140erparveenkaur86No ratings yet
- Performance Investigation of Visible Light Communication System Using Optisystem Simulation ToolDocument8 pagesPerformance Investigation of Visible Light Communication System Using Optisystem Simulation ToolLuisNo ratings yet
- Visible Light Communications: Challenges and Possibilities: October 2008Document6 pagesVisible Light Communications: Challenges and Possibilities: October 2008ਡਾ. ਹਰਮੀਤ ਸਿੰਘNo ratings yet
- Shlomi ArnonDocument9 pagesShlomi Arnonhendra lamNo ratings yet
- 134 139, Tesma507, IJEASTDocument6 pages134 139, Tesma507, IJEASTRishan KundetyNo ratings yet
- 2020 An Overview of Optical Architectures Necessary To Achieve 5g S Key Performance IndicatorsDocument11 pages2020 An Overview of Optical Architectures Necessary To Achieve 5g S Key Performance IndicatorsTaha AlhatmiNo ratings yet
- VLC Case StudyDocument3 pagesVLC Case StudyVedant KaushishNo ratings yet
- Reliable High Speed Data Transmission Using Li-Fi CommunicationDocument7 pagesReliable High Speed Data Transmission Using Li-Fi CommunicationlambanaveenNo ratings yet
- 3385 Li-Fi TechnologyDocument20 pages3385 Li-Fi TechnologyMr. GyanprakashNo ratings yet
- Led-Id S: C F L R T: Ystem Overage and AST INK Ecovery EchniqueDocument13 pagesLed-Id S: C F L R T: Ystem Overage and AST INK Ecovery EchniqueijcsesNo ratings yet
- Serial and Parallel Data Transmission Through Li-FiDocument5 pagesSerial and Parallel Data Transmission Through Li-FibelaoufamiraNo ratings yet
- On Optimizing VLC Networks For Downlink Multi-User Transmission: A SurveyDocument30 pagesOn Optimizing VLC Networks For Downlink Multi-User Transmission: A Surveyhendra lambNo ratings yet
- V2X Communications With An Image SensorDocument10 pagesV2X Communications With An Image SensorBaraa MNo ratings yet
- Irjet Li Fi Technology Transmission of DDocument7 pagesIrjet Li Fi Technology Transmission of Dسدن آرماNo ratings yet
- AP - Smart Grids 61850 (EN) 2017.01Document34 pagesAP - Smart Grids 61850 (EN) 2017.01Assis JúniorNo ratings yet
- IF You Want The Original Copy of This Document Please Mail Me atDocument18 pagesIF You Want The Original Copy of This Document Please Mail Me atShashi Shekhar AcharyaNo ratings yet
- US Paper DistDocument5 pagesUS Paper DistBaraa MNo ratings yet
- Research PaperDocument4 pagesResearch PaperRaj DasNo ratings yet
- Short Range Optical Wireless Communications For Indoor and Interconnects ApplicationsDocument10 pagesShort Range Optical Wireless Communications For Indoor and Interconnects Applicationszeadzizo715No ratings yet
- Design of Li-Fi Technology Based Underwater Data Communication System Using IotDocument11 pagesDesign of Li-Fi Technology Based Underwater Data Communication System Using IotdgcgtwgnnNo ratings yet
- Optical Distribution Network Evolution - 24feb2023Document14 pagesOptical Distribution Network Evolution - 24feb2023Zarroug HoussemNo ratings yet
- Detection and Recognition of RGB-LED Based On Visible Light Communication Using Covoltional Neural NetworkDocument12 pagesDetection and Recognition of RGB-LED Based On Visible Light Communication Using Covoltional Neural Networkphamdonhuhuynh11lnhom11.1No ratings yet
- Data Transmission Using Lifi: Dhirajlal Gandhi College of TechnologyDocument10 pagesData Transmission Using Lifi: Dhirajlal Gandhi College of TechnologyMuhammad AwaisNo ratings yet
- Audio Transmission Using Visible Light Communication Technology With Pre-Equalization TechniqueDocument8 pagesAudio Transmission Using Visible Light Communication Technology With Pre-Equalization TechniqueIJRASETPublicationsNo ratings yet
- Smart and Energy Efficient Led Street Light Control System Using Zigbee NetworkDocument5 pagesSmart and Energy Efficient Led Street Light Control System Using Zigbee NetworkVishwaraj BhagwatNo ratings yet
- Mini Project Report (P)Document16 pagesMini Project Report (P)Pranav BhaleraoNo ratings yet
- A Technical Seminar On Visible Light Communication: Vikas R 1HK10CS085Document30 pagesA Technical Seminar On Visible Light Communication: Vikas R 1HK10CS085vikas11031992No ratings yet
- Proposed Framework For V2V Communication Using Li-Fi TechnologyDocument4 pagesProposed Framework For V2V Communication Using Li-Fi TechnologyBrightworld ProjectsNo ratings yet
- Reference Guide OTNDocument60 pagesReference Guide OTNjoaquic100% (1)
- Accounting - Foundation Course 2023-24Document5 pagesAccounting - Foundation Course 2023-24Zoom MailNo ratings yet
- UNIT 1 Introduction To SPM, Project Evaluation Project PlanningDocument7 pagesUNIT 1 Introduction To SPM, Project Evaluation Project PlanningRamZ SkullyNo ratings yet
- Agile Questions Set 1Document19 pagesAgile Questions Set 1Zain NisarNo ratings yet
- Jawaban Latihan SoalDocument31 pagesJawaban Latihan SoalRizalMawardiNo ratings yet
- Basic Information of Multi-National Company: Guided by Dr. Navjyot RavalDocument14 pagesBasic Information of Multi-National Company: Guided by Dr. Navjyot RavalAxay PatelNo ratings yet
- Study Notes Trading StrategiesDocument16 pagesStudy Notes Trading Strategiesalok kundaliaNo ratings yet
- Bottom and Shell Bom - Up12Document27 pagesBottom and Shell Bom - Up12Karthimeena MeenaNo ratings yet
- Matrikulasi Bahasa InggrisDocument5 pagesMatrikulasi Bahasa InggrisMr DAY DAYNo ratings yet
- Single Entry SystemDocument4 pagesSingle Entry Systemanurags pageNo ratings yet
- Entrepreneurship Development and InnovationDocument6 pagesEntrepreneurship Development and Innovationvamsi krishnaNo ratings yet
- MDOT Secretary Slater Letter - TeleworkDocument2 pagesMDOT Secretary Slater Letter - TeleworkAnonymous sKgTCo2100% (1)
- Summary of IAS 40Document2 pagesSummary of IAS 40Zes ONo ratings yet
- Lubricant Oil System MaintenanceDocument2 pagesLubricant Oil System MaintenancePaul AbonitaNo ratings yet
- FS00055 - Mohammad Parwez-188202215227Document3 pagesFS00055 - Mohammad Parwez-188202215227K DNo ratings yet
- National Union of Workers in Hotel Restaurant and Allied Industries (NUWHRAIN - APL-IUF) v. Philippine Plaza Holdings, IncDocument3 pagesNational Union of Workers in Hotel Restaurant and Allied Industries (NUWHRAIN - APL-IUF) v. Philippine Plaza Holdings, IncKobe Lawrence VeneracionNo ratings yet
- Leave and License Agreement: Particulars Amount Paid GRN/Transaction Id DateDocument5 pagesLeave and License Agreement: Particulars Amount Paid GRN/Transaction Id DateAvi MarodkarNo ratings yet
- Seatwork # 1Document2 pagesSeatwork # 1Joyce Anne GarduqueNo ratings yet
- Lesson-3 EeDocument15 pagesLesson-3 EeChristian MagdangalNo ratings yet
- Dissertation On BrexitDocument5 pagesDissertation On BrexitWriteMyPaperCollegeUK100% (1)
- Notice of Post-DisqualificationDocument2 pagesNotice of Post-DisqualificationLiwayway MadaliNo ratings yet
- Be A Pirate StoryDocument14 pagesBe A Pirate StorySemira FocoNo ratings yet
- FG - ASCQ3109 - Welding and Quality Technician - Final - PKG - 01.08.2019 PDFDocument390 pagesFG - ASCQ3109 - Welding and Quality Technician - Final - PKG - 01.08.2019 PDFJim KaliNo ratings yet
- Formation of Business OrganizationDocument28 pagesFormation of Business OrganizationJichang HikNo ratings yet
- Bid Document For T2 of 2015Document23 pagesBid Document For T2 of 2015Donald SolomonNo ratings yet
- RAO (Autosaved)2019Document26 pagesRAO (Autosaved)2019Barangay Poblacion NaawanNo ratings yet
- CHP 7 Strategy and StructureDocument21 pagesCHP 7 Strategy and StructureBBHR20-A1 Wang Jing TingNo ratings yet