Professional Documents
Culture Documents
LAB 6 - Certificate Operations PDF
LAB 6 - Certificate Operations PDF
Uploaded by
kaleabOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
LAB 6 - Certificate Operations PDF
LAB 6 - Certificate Operations PDF
Uploaded by
kaleabCopyright:
Available Formats
DO NOT REPRINT
© FORTINET
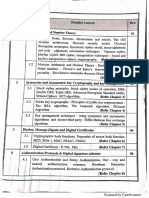
Lab 6: Certificate Operations
In this lab, you will configure SSL deep inspection using a self-signed SSL certificate on FortiGate to inspect
outbound traffic. You will also import a web server certificate on FortiGate and configure inbound SSL inspection.
Objectives
l Configure and enable SSL deep inspection on outbound traffic.
l Import an external web server certificate.
l Configure and enable SSL deep inspection on inbound traffic.
Time to Complete
Estimated: 40 minutes
Prerequisites
Before beginning this lab, you must restore a configuration file on each FortiGate.
Make sure to restore the correct configuration on each FortiGate using the following
steps. Failure to restore the correct configuration on each FortiGate will prevent you
from doing the lab exercise.
To restore the Remote-FortiGate configuration file
1. On the Local-Windows VM, open a browser and log in to the Remote-FortiGate GUI at 10.200.3.1 with the
user name admin and password password.
2. In the upper-right corner of the screen, click admin, and then click Configuration > Restore.
110 FortiGate Security 6.0 Lab Guide
Fortinet Technologies Inc.
DO Lab
NOT REPRINT
6: Certificate Operations
© FORTINET
3. Click Local PC, and then click Upload.
4. Click Desktop > Resources > FortiGate-Security > Certificate-Operations > remote-certificate-
operations.conf, and then click Open.
5. Click OK.
6. Click OK to reboot.
To restore the Local-FortiGate configuration file
1. On the Local-Windows VM, open a browser and log in to the Local-FortiGate GUI at 10.0.1.254 with the user
name admin and password password.
2. In the upper-right corner of the screen, click admin, and then click Configuration > Restore.
3. Click Local PC, and then click Upload.
4. Click Desktop > Resources > FortiGate-Security > Certificate-Operations > local-certificate-
operations.conf, and then click Open.
5. Click OK.
6. Click OK to reboot.
FortiGate Security 6.0 Lab Guide 111
Fortinet Technologies Inc.
DO NOT REPRINT
© FORTINET
Exercise 1: Configuring SSL Deep Inspection
on Outbound Traffic
SSL deep inspection on outbound traffic allows FortiGate to inspect encrypted Internet-bound traffic, and apply
security profiles to that traffic to protect your network and end users. FortiGate employs a man-in-the-middle
(MITM) attack to inspect the traffic and apply security profiles such as antivirus, web filter, and application
control.
In this exercise, you will configure and enable SSL inspection on all outbound traffic.
Configure SSL Inspection
By default, FortiGate includes two security profiles for SSL/SSH inspection: certificate-inspection and deep-
inspection, which you cannot modify. Because this exercise involves configuring FortiGate for SSL full
inspection, you will configure a new SSL/SSH inspection profile for full SSL inspection.
To configure SSL inspection
1. On the Local-Windows VM, open a browser and log in to the Local-FortiGate GUI at 10.0.1.254 with the user
name admin and password password.
2. Click Security Profiles > SSL/SSH Inspection.
3. In the upper-right corner, click the plus (+) icon to create a new profile.
4. In the Name field, type Custom_Full_Inspection.
5. At the bottom of the page, in the Common Options section, enable Allow Invalid SSL Certificates.
6. Click OK.
Enable SSL Inspection on a Firewall Policy
You must enable SSL inspection on a firewall policy to start inspecting traffic. However, you cannot enable
SSL inspection by itself. The firewall policy must have one or more other security profiles enabled, because
enabling SSL inspection tells FortiGate only how to handle encrypted traffic—you still need to tell FortiGate
which traffic to inspect. For the purposes of this lab, you will enable the default web filter security profile.
To enable SSL inspection on a firewall policy
1. Continuing on the Local-FortiGate GUI, click Policy & Objects > IPv4 Policy.
2. Double-click the Full_Access firewall policy to edit it.
112 FortiGate Security 6.0 Lab Guide
Fortinet Technologies Inc.
DO Exercise
NOT1: Configuring
REPRINT SSL Deep Inspection on Outbound Traffic Install the Fortinet_CA_SSL Certificate
© FORTINET
3. In the Security Profiles section, enable the following security profiles:
Security Profile Value
Web Filter default
SSL/SSH Inspection Custom_Full_Inspection
This is the profile you created previously.
4. In the Logging Options section, enable Log Allowed Traffic, and select All Sessions.
5. Click OK.
Install the Fortinet_CA_SSL Certificate
FortiGate includes an SSL certificate called Fortinet_CA_SSL that you can use for full SSL inspection. It is signed
by a certificate authority (CA) called FortiGate CA, which is not public. Because the CA is not public, your browser
will display a certificate warning each time a user connects to an HTTPS site. This is because the browser is
receiving certificates signed by FortiGate, which is a CA it does not know and trust. You can avoid this warning by
downloading the Fortinet_CA_SSL certificate and installing it on all the workstations as a public authority.
In this procedure, you will first test access to an HTTPS site without the Fortinet_CA_SSL certificate installed.
Then, you will install the Fortinet_CA_SSL certificate and test again.
To test SSL deep inspection without a trusted CA
1. On the Local-Windows VM, open a new browser tab and go to an HTTPS site, such as:
https://salesforce.com
2. Click Advanced.
Notice the certificate warning. This appears because the browser is receiving certificates signed by the
FortiGate CA's private key, and the corresponding CA certificate is not in the Local-Windows certificate store.
3. Leave the browser tab open and continue to the next procedure. Do not add the exception.
FortiGate Security 6.0 Lab Guide 113
Fortinet Technologies Inc.
DO Install
NOT REPRINT
the Fortinet_CA_SSL Certificate Exercise 1: Configuring SSL Deep Inspection on Outbound Traffic
© FORTINET
To install the Fortinet_CA_SSL certificate in the browser
1. Return to the browser tab where you are logged in to the Local-FortiGate GUI, and click System > Certificates.
2. In the Local CA Certificates section, click Fortinet_CA_SSL, and then click Download.
3. Click Save File.
The certificate downloads to your Downloads folder.
4. In Firefox, in the upper-right corner of the window, click the Open menu icon, and then click Options.
5. Click Privacy & Security.
114 FortiGate Security 6.0 Lab Guide
Fortinet Technologies Inc.
DO Exercise
NOT1: Configuring
REPRINT SSL Deep Inspection on Outbound Traffic Install the Fortinet_CA_SSL Certificate
© FORTINET
6. In the Certificates section, click View Certificates.
7. In the Certificate Manager window, click the Authorities tab, and then click Import.
8. Click Downloads > Fortinet_CA_SSL.cer, and then click Open.
9. In the Downloading Certificate window, select Trust this CA to identify websites, and then click OK.
FortiGate Security 6.0 Lab Guide 115
Fortinet Technologies Inc.
DO Test
NOT REPRINT
Full SSL Inspection Exercise 1: Configuring SSL Deep Inspection on Outbound Traffic
© FORTINET
The Fortinet_CA_SSL certificate is added to the Firefox Authorities certificate store.
10. Click OK.
11. Restart Firefox.
Test Full SSL Inspection
Now that you have added the Fortinet_CA_SSL certificate to your browser, you will not receive any certificate
warnings when accessing a secure site.
The CA that signed this certificate is not public, but the browser is aware of it because you added it as a trusted
authority in the previous exercise.
To test SSL full inspection
1. Continuing on the Local-Windows VM, open a new browser and go to a secure site, such as:
https://salesforce.com
This time you are passed through to the site without any certificate warnings.
2. Close the browser.
116 FortiGate Security 6.0 Lab Guide
Fortinet Technologies Inc.
DO NOT REPRINT
© FORTINET
Exercise 2: Configuring SSL Deep Inspection on Inbound
Traffic
You can use SSL deep inspection on inbound traffic to protect internal resources, such as web servers, that users
can access on the Internet. Implementing inbound SSL deep inspection allows you to apply antivirus, IPS, and
web application firewall (WAF) on encrypted traffic destined for your web servers, to protect them from malicious
files and traffic.
In this exercise, you will import an external web server certificate to Local-FortiGate, and then configure SSL
deep inspection to protect a web server with an antivirus profile.
Configure a Virtual IP and Firewall Policy
First, you will configure a virtual IP to map an external IP address to the web server's internal IP address. Then,
you will configure a firewall policy to allow access to the virtual IP.
Take the Expert Challenge!
l On the Local-FortiGate GUI, configure a new virtual IP to map the external IP, 10.200.1.200, to the
internal IP, 10.0.1.10, using port1 as the external interface. Use VIP-WEB-SERVER as the name of
your virtual IP.
l Create a new firewall policy to allow all inbound traffic to the virtual IP. Use Web_Server_Access as the
name of the firewall policy.
If you require assistance, or to verify your work, use the step-by-step instructions that follow.
After you complete the challenge, see Install the Training CA Certificate on page 118.
To configure a virtual IP
1. On the Local-Windows VM, open a browser and log in to the Local-FortiGate GUI at 10.0.1.254 with the user
name admin and password password.
2. Click Policy & Objects > Virtual IPs.
3. Click Create New, and select Virtual IP.
4. Configure the following settings:
Field Value
Name VIP-WEB-SERVER
Interface port1
FortiGate Security 6.0 Lab Guide 117
Fortinet Technologies Inc.
DO Install
NOT REPRINT
the Training CA Certificate Exercise 2: Configuring SSL Deep Inspection on Inbound Traffic
© FORTINET
Field Value
External IP Address/Range 10.200.1.200
Mapped IP Address/Range 10.0.1.10
5. Click OK.
To configure a firewall policy
1. Continuing on the Local-FortiGate GUI, click Policy & Objects > IPv4 Policy.
2. Click Create New, and then create a new firewall policy using the following settings:
Field Value
Name Web_Server_Access
Incoming Interface port1
Outgoing Interface port3
Source all
Destination VIP-WEB-SERVER
Schedule always
Service ALL
Action ACCEPT
NAT <disable>
3. Click OK.
Install the Training CA Certificate
Now, you will verify access to the web server URL, and then install the Training CA certificate on Firefox to
eliminate certificate errors.
118 FortiGate Security 6.0 Lab Guide
Fortinet Technologies Inc.
DO Exercise
NOT2: Configuring
REPRINT SSL Deep Inspection on Inbound Traffic Install the Training CA Certificate
© FORTINET
Take the Expert Challenge!
l On the Remote-Windows VM, verify that you have access to the web server using
https://10.200.1.200.
l Using Firefox, review the web server certificate details and identify the certificate issuer.
l Install the Training CA certificate in Firefox's Authorities certificate store. The certificate file is located on
Desktop > Resources > FortiGate-Security > Training.crt.
l Make sure certificate-related warning messages no longer appear before proceeding to the next section.
If you require assistance, or to verify your work, use the step-by-step instructions that follow.
After you complete the challenge, see Configure Inbound SSL Deep Inspection on page 123.
To verify access
1. On the virtual lab portal, click the Remote-Windows VM.
2. Open Firefox and access the web server using https://10.200.1.200.
A security warning opens.
3. Click Advanced, and then review the warning message.
4. Click Add Exception.
5. Click View.
FortiGate Security 6.0 Lab Guide 119
Fortinet Technologies Inc.
DO Install
NOT REPRINT
the Training CA Certificate Exercise 2: Configuring SSL Deep Inspection on Inbound Traffic
© FORTINET
6. In the Issued By section, review the information.
7. Click Close.
8. Click Cancel.
To install the Training CA certificate
1. Continuing on the Remote-Windows VM, in the upper-right corner of theFirefox browser, click the Open menu
icon, and then select Options.
120 FortiGate Security 6.0 Lab Guide
Fortinet Technologies Inc.
DO Exercise
NOT2: Configuring
REPRINT SSL Deep Inspection on Inbound Traffic Install the Training CA Certificate
© FORTINET
2. Click Privacy & Security.
3. In the Certificates section, click View Certificates.
FortiGate Security 6.0 Lab Guide 121
Fortinet Technologies Inc.
DO Install
NOT REPRINT
the Training CA Certificate Exercise 2: Configuring SSL Deep Inspection on Inbound Traffic
© FORTINET
4. In the Certificate Manager window, click the Authorities tab, and then click Import.
5. Click Desktop > Resources > FortiGate-Security > Certificate-Operations > Training.crt, and then click
Open.
The Downloading Certificate window opens.
6. Click Trust this CA to identify websites.
7. Click OK.
8. Click OK.
9. Restart Firefox.
10. Go to https://10.200.1.200, and then verify that the security warning is no longer displayed.
122 FortiGate Security 6.0 Lab Guide
Fortinet Technologies Inc.
DO Exercise
NOT2: Configuring
REPRINT SSL Deep Inspection on Inbound Traffic Configure Inbound SSL Deep Inspection
© FORTINET
Configure Inbound SSL Deep Inspection
On Local-FortiGate, you will configure and enable SSL deep inspection on all inbound traffic destined to the web
server using the default certificate. You will also observe the changes to the end-user browser session on
Remote-Windows. Then, you will import the external web server certificate on Local-FortiGate, and use it to
perform SSL deep inspection to eliminate security errors.
To configure inbound SSL deep inspection
1. Return to the Local-Windows VM, and on the Local-Fortigate GUI, click Security Profiles
> SSL/SSH Inspection.
2. In the upper-right corner, click the plus (+) icon to create a new profile.
3. Configure the following settings:
Field Value
Name Inbound_SSL_Inspection
Enable SSL Inspection of Protecting SSL Server
Server Certificate Fortinet_SSL
4. Click OK.
5. Click Policy & Objects > IPv4 Policy.
6. Edit the Web_Server_Access policy.
7. In the Security Profiles section, enable the following security profiles:
Security Profile Value
AntiVirus default
SSL/SSH Inspection Inbound_SSL_Inspection
8. Click OK.
FortiGate Security 6.0 Lab Guide 123
Fortinet Technologies Inc.
DO Configure
NOTInboundREPRINT
SSL Deep Inspection Exercise 2: Configuring SSL Deep Inspection on Inbound Traffic
© FORTINET
To verify inbound SSL deep inspection
1. Return to the Remote-Windows VM, and close any existing instances of Firefox.
2. Open Firefox again, and go to https://10.200.1.200.
A security warning opens. If you do not receive a security warning, refresh the page (F5). This forces Firefox
to update its local cache.
3. Click Advanced, and review the error message.
4. Click Add Exception.
5. Click View.
6. Review the certificate information.
Stop and think!
To inspect the encrypted traffic, Local-FortiGate must proxy the connection between Remote-Windows and
the web server. To do this, FortiGate must use its own certificate (FortiGate_SSL), which is not a trusted
certificate. It is also not issued for the hostname you are using in the URL to access the secure website.
While this does verify that Local-FortiGate is inspecting the encrypted traffic, you must perform a few more
configuration steps to make sure the correct certificate is being used, to eliminate any end-user-side
security errors.
7. Click Close.
8. Click Cancel.
To import the web server certificate and private key on Local-FortiGate
1. Return to the Local-Windows VM.
2. On the Local-FortiGate GUI, click System > Certificates.
3. Click Import, and then select Local Certificate.
4. In the Type drop-down list, select PKCS # 12 Certificate.
5. Click Upload.
6. Click Desktop > Resources > FortiGate-Security > Certificate-Operations > webserver.p12, and then click
Open.
The Certificate Name field is auto-populated from the certificate file name.
124 FortiGate Security 6.0 Lab Guide
Fortinet Technologies Inc.
DO Exercise
NOT2: Configuring
REPRINT SSL Deep Inspection on Inbound Traffic Configure Inbound SSL Deep Inspection
© FORTINET
PKCS#12 (.p12 file extension) is an archive file format used to bundle a certificate
with its private key. It is usually protected using a password.
The webserver.p12 file contains the web server's certificate and private key.
7. In the Password field, enter fortinet.
8. Click OK.
The certificate and key are imported.
To modify the inbound SSL inspection profile
1. Continuing on the Local-FortiGate GUI, click Security Profiles > SSL/SSH Inspection.
2. In the upper-right corner, in the profile drop-down list, select Inbound_SSL_Inspection.
3. In the Server Certificate drop-down list, select webserver.
4. Click Apply.
To verify the SSL inspection profile change
1. Return to the Remote-Windows VM, and close any existing instances of Firefox.
2. Open Firefox again, and go to https://10.200.1.200.
Verify that there are no more security errors. If you still receive errors, refresh the page (F5). This forces
Firefox to update its local cache.
FortiGate Security 6.0 Lab Guide 125
Fortinet Technologies Inc.
You might also like
- Real-World: Next - JsDocument367 pagesReal-World: Next - JskaleabNo ratings yet
- Dial Plan and Call Routing Demystified On Cisco Collaboration Technologies: Cisco Unified Communication ManagerFrom EverandDial Plan and Call Routing Demystified On Cisco Collaboration Technologies: Cisco Unified Communication ManagerNo ratings yet
- NSE5 - FMG-7.0 whatsAPP 0021655255099Document37 pagesNSE5 - FMG-7.0 whatsAPP 0021655255099juan carlos alvarez rojasNo ratings yet
- CSS TechmaxDocument392 pagesCSS TechmaxRushi Shah100% (5)
- Do Not Reprint © Fortinet: Fortimanager Lab GuideDocument182 pagesDo Not Reprint © Fortinet: Fortimanager Lab Guideravi pithawalaNo ratings yet
- QuestionsDocument10 pagesQuestionsRizzy Shinigami50% (2)
- FortiAnalyzer 05 ReportsDocument59 pagesFortiAnalyzer 05 ReportscrgonzalezfloresNo ratings yet
- SSH Pentest - Cheat SheetDocument1 pageSSH Pentest - Cheat Sheetregister NameNo ratings yet
- NSE 8 Immersion: Course DescriptionDocument2 pagesNSE 8 Immersion: Course DescriptionasaldarreagaNo ratings yet
- FortiNAC Deployment Prerequisite Task ListDocument26 pagesFortiNAC Deployment Prerequisite Task Listaykargil100% (1)
- Lab 11 - SSL-VPNDocument15 pagesLab 11 - SSL-VPNkaleabNo ratings yet
- LAB 4 - Transparent ModeDocument13 pagesLAB 4 - Transparent ModeJuan Perez100% (1)
- How To Setup FortiGate Firewall To Access The InternetDocument7 pagesHow To Setup FortiGate Firewall To Access The InternetArio Dhilla HattaNo ratings yet
- VDOM ConfigurationDocument7 pagesVDOM ConfigurationJeanNo ratings yet
- Configuring A FortiGate Unit As An L2TP IPsec ServerDocument8 pagesConfiguring A FortiGate Unit As An L2TP IPsec ServerJonatas NobreNo ratings yet
- Troubleshooting Tricks and HintsDocument10 pagesTroubleshooting Tricks and HintsAnkur SaxenaNo ratings yet
- Lab 11 - SSL-VPNDocument15 pagesLab 11 - SSL-VPNkaleabNo ratings yet
- Information Security Policy ChecklistDocument2 pagesInformation Security Policy ChecklistRead Rule100% (6)
- Lab 3 - Nat PDFDocument24 pagesLab 3 - Nat PDFkaleabNo ratings yet
- LAB 7 - Web Filtering PDFDocument19 pagesLAB 7 - Web Filtering PDFkaleabNo ratings yet
- Lab 2: Security Fabric: Do Not Reprint © FortinetDocument27 pagesLab 2: Security Fabric: Do Not Reprint © FortinetCarlos MuñozNo ratings yet
- LAB 5 - Logging and MonitoringDocument20 pagesLAB 5 - Logging and MonitoringNils GarciaNo ratings yet
- Install and Configure FortiGate Default CertificateDocument3 pagesInstall and Configure FortiGate Default CertificatePravin100% (1)
- LAB 10 - IPS and DoSDocument13 pagesLAB 10 - IPS and DoSkaleabNo ratings yet
- Installing The FortiGate UnitDocument17 pagesInstalling The FortiGate Unitmanoj22490No ratings yet
- Lab 1: Routing: Do Not Reprint © FortinetDocument20 pagesLab 1: Routing: Do Not Reprint © FortinetJuan Perez100% (1)
- Configuring Split Tunnel Client VPN - Cisco MerakiDocument6 pagesConfiguring Split Tunnel Client VPN - Cisco Merakikatherine painiiNo ratings yet
- Basic Fortigate Firewall Configuration: Content at A GlanceDocument17 pagesBasic Fortigate Firewall Configuration: Content at A GlanceDenisa PriftiNo ratings yet
- Fortigate VMDocument22 pagesFortigate VMHoang NguyenHuyNo ratings yet
- Fortigate Ipsecvpn 56 PDFDocument242 pagesFortigate Ipsecvpn 56 PDFdavidNo ratings yet
- Secure SD-WAN: Abgesichert Sein in Zeiten, in Denen Das Internet Das Neue WAN IstDocument23 pagesSecure SD-WAN: Abgesichert Sein in Zeiten, in Denen Das Internet Das Neue WAN IstJailer Edintongh JimenezNo ratings yet
- NSE4 Study G-7Document70 pagesNSE4 Study G-7chaaben927100% (1)
- LAB 7 - High Availability (HA)Document17 pagesLAB 7 - High Availability (HA)Juan Perez100% (1)
- 203 Lab GuideDocument17 pages203 Lab GuidezarandijaNo ratings yet
- Troubleshooting PDFDocument96 pagesTroubleshooting PDFJeanNo ratings yet
- Fortigate Cookbook ExpandedDocument418 pagesFortigate Cookbook ExpandedBogdan Ungureanu100% (1)
- Fortianalyzer Lab Guide: Do Not Reprint © FortinetDocument90 pagesFortianalyzer Lab Guide: Do Not Reprint © FortinetDarko SpunkyNo ratings yet
- Hosting More Than One Fortios Instance On A Single Fortigate Unit Using Vdoms and VlansDocument35 pagesHosting More Than One Fortios Instance On A Single Fortigate Unit Using Vdoms and VlansRatheesh RavindranNo ratings yet
- Fortigate CommandDocument17 pagesFortigate Commandmanoj22490100% (1)
- Course - FortiGate Essentials 6.4 Self-PacedDocument4 pagesCourse - FortiGate Essentials 6.4 Self-PacedMOhamedNo ratings yet
- NSE3 FortiAP Course 20201204Document46 pagesNSE3 FortiAP Course 20201204king jumper343No ratings yet
- FortiSwitch and Security Fabric v2 - Public PDFDocument37 pagesFortiSwitch and Security Fabric v2 - Public PDFDJ JAMNo ratings yet
- Checkpoint CCSA (CBT)Document3 pagesCheckpoint CCSA (CBT)asegunloluNo ratings yet
- Fortigate Troubleshooting 56Document64 pagesFortigate Troubleshooting 56Sridhar bvnlNo ratings yet
- Fortinac: Fortigate VPN Device IntegrationDocument45 pagesFortinac: Fortigate VPN Device IntegrationAlbert Osorio GalegoNo ratings yet
- Fortigate VDOMDocument120 pagesFortigate VDOMMauricio TorresNo ratings yet
- NSE 8 Certification Public HandbookDocument26 pagesNSE 8 Certification Public HandbookSahil Wadhawan0% (1)
- Nse4 Infraestructura 101-150Document50 pagesNse4 Infraestructura 101-150leydis GarciaNo ratings yet
- FortiNAC FortiGate VPN IntegrationDocument58 pagesFortiNAC FortiGate VPN IntegrationFrancisco JuniorNo ratings yet
- Fortigate FirewallDocument15 pagesFortigate FirewallSteven it100% (1)
- FortiManager Lab Guide-OnlineDocument182 pagesFortiManager Lab Guide-OnlineFelipe Gabriel Nieto Concha100% (2)
- Eb Network Leaders Guide To SD WAN PDFDocument17 pagesEb Network Leaders Guide To SD WAN PDFAayushNo ratings yet
- Fortigate Firewall How To InternetDocument8 pagesFortigate Firewall How To InternetKaushal KishorNo ratings yet
- FortiGate III Student Guide-Online V8Document521 pagesFortiGate III Student Guide-Online V8neoalt100% (1)
- FortiAnalyzer 6.4 Instructor GuideDocument12 pagesFortiAnalyzer 6.4 Instructor GuidecrgonzalezfloresNo ratings yet
- FortiMail 6.0 Lab Guide-OnlineDocument182 pagesFortiMail 6.0 Lab Guide-Onlineravi pithawalaNo ratings yet
- FORTIGATE Firewall Policies-2Document42 pagesFORTIGATE Firewall Policies-2Kevin MulluhuaraNo ratings yet
- Checkpoint FirewallDocument14 pagesCheckpoint FirewallJonnalagadda Harshavardhan100% (2)
- FortiGate - Infrastructure New PDFDocument2 pagesFortiGate - Infrastructure New PDFMohammad Baba FakruddinNo ratings yet
- Installing A FortiGate in Transparent Mode PDFDocument5 pagesInstalling A FortiGate in Transparent Mode PDFFrontos CeleriusNo ratings yet
- FortiManager Student Guide-OnlineDocument330 pagesFortiManager Student Guide-OnlineEmilio PazNo ratings yet
- IPSEC Config - FortigateDocument220 pagesIPSEC Config - FortigatesuryababaNo ratings yet
- FortiGate 7.4 Operator Lesson ScriptsDocument33 pagesFortiGate 7.4 Operator Lesson ScriptsAdolfo Feliz MorenoNo ratings yet
- LAB 5 - Configuring A Site-to-Site IPsec VPNDocument23 pagesLAB 5 - Configuring A Site-to-Site IPsec VPNDin CessareNo ratings yet
- 41.1 Printf Cheatsheet PDFDocument1 page41.1 Printf Cheatsheet PDFkaleabNo ratings yet
- Midea R410A T3 50Hz Split Type Top-Dishcharge Series Technical Manual - V201707Document157 pagesMidea R410A T3 50Hz Split Type Top-Dishcharge Series Technical Manual - V201707kaleabNo ratings yet
- 78.1 Understand Untyped ConstantsDocument95 pages78.1 Understand Untyped ConstantskaleabNo ratings yet
- SQLite ExpertDocument134 pagesSQLite ExpertkaleabNo ratings yet
- 4.1 Variables - Basic Data Types and LiteralsDocument1 page4.1 Variables - Basic Data Types and LiteralskaleabNo ratings yet
- 67.1 Overflow CheatsheetDocument1 page67.1 Overflow CheatsheetkaleabNo ratings yet
- 45.1 Arithmetic Operators TableDocument1 page45.1 Arithmetic Operators TablekaleabNo ratings yet
- 37.1 Learn Go's Switch Statement PDFDocument45 pages37.1 Learn Go's Switch Statement PDFkaleabNo ratings yet
- 23.1 Error HandlingDocument13 pages23.1 Error HandlingkaleabNo ratings yet
- 11.1 If StatementDocument37 pages11.1 If StatementkaleabNo ratings yet
- LAB 7 - Web Filtering PDFDocument19 pagesLAB 7 - Web Filtering PDFkaleabNo ratings yet
- 9.1 Logical Operators RecapDocument8 pages9.1 Logical Operators RecapkaleabNo ratings yet
- Lab 3 - Nat PDFDocument24 pagesLab 3 - Nat PDFkaleabNo ratings yet
- LAB 13 - Data Leak Prevention (DLP) PDFDocument14 pagesLAB 13 - Data Leak Prevention (DLP) PDFkaleabNo ratings yet
- LAB 10 - IPS and DoSDocument13 pagesLAB 10 - IPS and DoSkaleabNo ratings yet
- LAB 8 - Application ControlDocument4 pagesLAB 8 - Application ControlkaleabNo ratings yet
- LAB 9 - AntivirusDocument13 pagesLAB 9 - AntiviruskaleabNo ratings yet
- Nutch Installation GuideDocument7 pagesNutch Installation GuidekaleabNo ratings yet
- DBS C1Document63 pagesDBS C1kaleabNo ratings yet
- DBS C2Document97 pagesDBS C2kaleabNo ratings yet
- Implementation of Rail Fence Ciphers: BY: M.SATYA HARSHA (19BCE7026) P.Radha Viswanath (19Bcn7110)Document13 pagesImplementation of Rail Fence Ciphers: BY: M.SATYA HARSHA (19BCE7026) P.Radha Viswanath (19Bcn7110)Radha ViswanathNo ratings yet
- Re-Evaluating The Necessity of Third-Party Antivirus Software On Windows Operating SystemDocument16 pagesRe-Evaluating The Necessity of Third-Party Antivirus Software On Windows Operating SystemFaisal AliNo ratings yet
- The Beauty of Stealing Internet - "Broadband Theft": Article Published On NW3C Informant MagazineDocument5 pagesThe Beauty of Stealing Internet - "Broadband Theft": Article Published On NW3C Informant MagazineNoorSoormallyNo ratings yet
- Case Study On Whatsapp End To End EncryptionDocument6 pagesCase Study On Whatsapp End To End EncryptionIcarusNo ratings yet
- Cryptography and Network Security Feb 2020Document1 pageCryptography and Network Security Feb 2020Akshita dammuNo ratings yet
- Security Value Map™: Next Generation Firewall (NGFW)Document1 pageSecurity Value Map™: Next Generation Firewall (NGFW)Wagner MarlonNo ratings yet
- Events Codes For Fun & ProfitDocument19 pagesEvents Codes For Fun & ProfitMarcia MéndezNo ratings yet
- Eduroam: King's College LondonDocument29 pagesEduroam: King's College LondonJustin FratermanNo ratings yet
- Data BreachDocument5 pagesData Breachallen martin almeidaNo ratings yet
- Itec-85 Reviewer SirjephDocument5 pagesItec-85 Reviewer SirjephLizette PaezNo ratings yet
- AesDocument48 pagesAesGeetha KoteswaraNo ratings yet
- Mikrotik - User Management and HotspotDocument47 pagesMikrotik - User Management and HotspotMusyaffak SNo ratings yet
- Exam Questions 312-50V12: Certified Ethical Hacker Exam (Cehv12)Document31 pagesExam Questions 312-50V12: Certified Ethical Hacker Exam (Cehv12)Bilal AhmedNo ratings yet
- Password Policy 325048 7Document3 pagesPassword Policy 325048 7Srikanta MishraNo ratings yet
- Module 4 - PK InfrastructureDocument23 pagesModule 4 - PK InfrastructureDon JinoNo ratings yet
- Background Guide of UNSCDocument18 pagesBackground Guide of UNSCArchit SharmaNo ratings yet
- Qualys API Quick ReferenceDocument73 pagesQualys API Quick ReferenceN prasanthNo ratings yet
- Dingo Coin White PaperDocument4 pagesDingo Coin White PaperMrkike kNo ratings yet
- 1.1 War Stories: 1 © 2020 Cisco And/or Its Affiliates. All Rights Reserved. Cisco ConfidentialDocument18 pages1.1 War Stories: 1 © 2020 Cisco And/or Its Affiliates. All Rights Reserved. Cisco ConfidentialToyota CelicaNo ratings yet
- Net HSMDocument4 pagesNet HSMJosé Tudela de la RosaNo ratings yet
- Lab Da-4Document25 pagesLab Da-4xyzNo ratings yet
- ReportDocument15 pagesReportAnonymous vZpw8dPNo ratings yet
- Fresh 40x SMTP Valid HitsDocument2 pagesFresh 40x SMTP Valid HitsbensonbuffordNo ratings yet
- Typology ResistanceDocument118 pagesTypology ResistanceBillyNo ratings yet
- New British Foreign PolicyDocument119 pagesNew British Foreign PolicyNamlessINo ratings yet
- Fuzzy Scheme CryptoDocument4 pagesFuzzy Scheme CryptoBianco NeroNo ratings yet