Professional Documents
Culture Documents
Assignment # 4A The Cia Triangle: CDI 6C 1:30-TF
Assignment # 4A The Cia Triangle: CDI 6C 1:30-TF
Uploaded by
Nico JaboneOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Assignment # 4A The Cia Triangle: CDI 6C 1:30-TF
Assignment # 4A The Cia Triangle: CDI 6C 1:30-TF
Uploaded by
Nico JaboneCopyright:
Available Formats
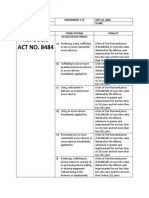
Name JABONE, NICO T.
Date OCT 06, 2020
Section CDI 6C 1:30-TF Score
ASSIGNMENT # 4A
THE CIA TRIANGLE
A. OBJECTIVE: Apply the security principles of CIA triangle in protecting confidential information
stored in the computer system of a police organization/office.
B. PROCEDURE (refer the instructions in the assignment page)
C. OUTPUT
CONFIDENTIALITY
1. AS A POLICE RECORD OFFICER, I
WILL CREATE A RULE WHERE ALL
OFFICERS WILL ONLY HAVE
“LIMITED ACCESS” ON THE DATAS
STORED WITHIN THE COMPUTER INTEGRITY
AND ONLY AUTHORIZED 1. AS A POLICE RECORD OFFICER, I
PERSONNEL CAN ACCESS THE WILL ENSURE THE INTEGRITY OF
SENSITIVE INFORMATION. THE CONFIDENTIAL FILES BY
“AUDITING THE CHANGES” I MADE
IN THE COMPUTER FILES
2. OF COURSE TO SUPPORT MY EVERYTIME.
LIMITED ACCESS RULE, I WILL
PROVIDE CONFIDENTIALITY POLICY 2. STRICTLY FOLLOW THE PROCEDURE
HANDBOOK TO THE OFFICER FOR INCLUDING THE CHAIN OF
THEM TO KNOW WHAT COMMAND IN TERMS OF HANDLING
INFORMATIONS THEY CAN AND THE CONFIDENTIAL FILES.
CAN’T HAVE AN ACCESS.
AVAILABILITY
1. TO ENSURE THE AVAILABITY OF THE
CONFIDENTIAL FILES UNDER MY
CUSTODY, I WILL ALWAYS CREATE A
BACKUP OF THOSE FILES TO
SECURE THE INFORMATION WHEN
THE MAIN FILES CORRUPTED OR
DISAPPEAR UNDER UNEXPECTED
CIRCUMSTANCES.
2. I WILL ENSURE THAT THE
COMPUTER HOLDING THE
CONFIDENTIAL FILES THAT UNDER
MY CUSTODY IS PLACED WITHIN A
VERY SECURED ROOM TO PROTECT
IT FROM EXTERNAL FACTORS LIKE
NATURAL PHENOMENON.
by cdkWorks/2020
You might also like
- bsbxcs402 Task 1Document5 pagesbsbxcs402 Task 1Maliha Qureshi100% (1)
- Maricopa County Audit - NIST - CISADocument9 pagesMaricopa County Audit - NIST - CISAJim Hoft100% (1)
- RODELDocument17 pagesRODELJefferson BeraldeNo ratings yet
- 3F Rflib Dpa3Document13 pages3F Rflib Dpa3acar.jomar18No ratings yet
- Assignment # 4C Countering Cybersecurity RisksDocument1 pageAssignment # 4C Countering Cybersecurity RisksNico JaboneNo ratings yet
- (06.05) Data Privacy Act and Its Implication To Research (TG15-CG3) - Final - MATTHEW ETHAN ANGDocument7 pages(06.05) Data Privacy Act and Its Implication To Research (TG15-CG3) - Final - MATTHEW ETHAN ANGMikmik DGNo ratings yet
- ACM - The NSA and Snowden - Securing The All - Seeing EyeDocument8 pagesACM - The NSA and Snowden - Securing The All - Seeing EyeRbto Brito RodriguezNo ratings yet
- Chapter 2Document5 pagesChapter 2Akshata HiranNo ratings yet
- Information Security Incident Reporting Procedure v1.4Document7 pagesInformation Security Incident Reporting Procedure v1.4YUGA SHREENo ratings yet
- Cyber Crime WarrantsDocument5 pagesCyber Crime WarrantsJanalin TatilNo ratings yet
- Basic Intel ReviewerDocument3 pagesBasic Intel ReviewerMichael QuidorNo ratings yet
- NDA EnglishDocument1 pageNDA EnglishdzulfatuhNo ratings yet
- Data Encryption PolicyDocument5 pagesData Encryption PolicyM. Shahid Hanif100% (1)
- IT-003 Workstation Security (Updated Version)Document3 pagesIT-003 Workstation Security (Updated Version)johnvincentcanalita2003No ratings yet
- CYBER The Cyber Security Act of 2012 FinalDocument205 pagesCYBER The Cyber Security Act of 2012 FinalGet the Cell Out - Atlanta ChapterNo ratings yet
- CYBER The Cyber Security Act of 2012 FinalDocument205 pagesCYBER The Cyber Security Act of 2012 FinalalgaenastyNo ratings yet
- ISP - 12 Communication Issue 1 2022Document2 pagesISP - 12 Communication Issue 1 2022zarraralikhanNo ratings yet
- Basic IntelligenceDocument23 pagesBasic IntelligenceJarvie John100% (2)
- Declaration of Aaron Wagner NewDocument15 pagesDeclaration of Aaron Wagner NewJim HoftNo ratings yet
- Remote AccessDocument3 pagesRemote Accessnranjit1No ratings yet
- Surgimap-Security-Assessment-Dec-2015-Information Security Third-Party Assessment SurveyDocument8 pagesSurgimap-Security-Assessment-Dec-2015-Information Security Third-Party Assessment SurveyAntar ShaddadNo ratings yet
- 2nd Semester: Unit 1 Security 2022Document32 pages2nd Semester: Unit 1 Security 2022Binadi JayarathneNo ratings yet
- Sistem Perakaunan Berkomputer Standard Untuk Kerajaan Negeri (Speks) Information Security PoliciesDocument30 pagesSistem Perakaunan Berkomputer Standard Untuk Kerajaan Negeri (Speks) Information Security Policieshafis82No ratings yet
- Government Employees: Cyber Security Guidelines ForDocument10 pagesGovernment Employees: Cyber Security Guidelines Forsobeva6070No ratings yet
- NDA Non-EmployeesDocument2 pagesNDA Non-EmployeesRupesh PatelNo ratings yet
- Data and National Security FinalDocument20 pagesData and National Security FinalJackmoeNo ratings yet
- CIA - Improper Handling of Classified Information by John M. DeutchDocument84 pagesCIA - Improper Handling of Classified Information by John M. Deutch[Unknown]100% (2)
- DPA Presentation (FINAL)Document26 pagesDPA Presentation (FINAL)Mark LawyerNo ratings yet
- Personnel SecurityDocument8 pagesPersonnel SecuritySegunto, Rafhael G.No ratings yet
- Standard Operating Procedure (SOP) On Technical Security Measures For All PNP Data Processing Systems (DPS)Document11 pagesStandard Operating Procedure (SOP) On Technical Security Measures For All PNP Data Processing Systems (DPS)Mark Anthony RoqueNo ratings yet
- Chapter 1-Introduction To Computer SecurityDocument40 pagesChapter 1-Introduction To Computer SecurityTigabu YayaNo ratings yet
- IE3072 - Tutorial - 3Document2 pagesIE3072 - Tutorial - 3Thilin ThungeeshaNo ratings yet
- Notes On Data Privacy ActDocument6 pagesNotes On Data Privacy ActRad IsnaniNo ratings yet
- Ias102 Chapter1 3Document15 pagesIas102 Chapter1 3HannieeeNo ratings yet
- Module1 Intro To Security FinalDocument11 pagesModule1 Intro To Security FinalHameed MehsudNo ratings yet
- CNSS Policy 14 FinalDocument9 pagesCNSS Policy 14 FinalJavierAmayaNo ratings yet
- Information Assurance and SecurityDocument12 pagesInformation Assurance and SecuritySimeon Cainday IIINo ratings yet
- Security Policies and ProceduresDocument6 pagesSecurity Policies and ProceduresJEXNo ratings yet
- Fundamentals of Industrial Security ManagementDocument40 pagesFundamentals of Industrial Security ManagementDesiree Val Didulo Dile100% (1)
- Five Most Significant Security BreachesDocument6 pagesFive Most Significant Security BreachesMaria Luiza Guimarães Silva MantovanelliNo ratings yet
- Varian 4Document3 pagesVarian 4Славик ПольскийNo ratings yet
- Security ConditionsDocument8 pagesSecurity ConditionsConstantinosNo ratings yet
- Activity5 - Securityreport - Script MDocument5 pagesActivity5 - Securityreport - Script Mbojim8766No ratings yet
- Infosec GatewayDocument28 pagesInfosec GatewayJoe WalkNo ratings yet
- Information AssuranceDocument6 pagesInformation AssuranceJocelyn Ubaldo AradanasNo ratings yet
- IT Tools in Business QuizessDocument7 pagesIT Tools in Business QuizessSITTIE SAILAH PATAKNo ratings yet
- SECURITYDocument3 pagesSECURITYPeter SakiwatNo ratings yet
- Module1 Intro To Security FinalDocument11 pagesModule1 Intro To Security FinalAsh KetchumNo ratings yet
- Ios Platform SecDocument17 pagesIos Platform SecAlireza HemmatiNo ratings yet
- Chapter 8 - Data Security and Data ProtectionDocument6 pagesChapter 8 - Data Security and Data ProtectionChris MumeloNo ratings yet
- Cdi Quiz ReviewerDocument6 pagesCdi Quiz Reviewer2022ccjecrutokNo ratings yet
- 3rd Party Outsourcing Information Security Assessment Questionnaire V1.4Document10 pages3rd Party Outsourcing Information Security Assessment Questionnaire V1.4Ryan GlasgowNo ratings yet
- EnggRoom Code 26 Network SecurityDocument19 pagesEnggRoom Code 26 Network SecurityTejukumar RNo ratings yet
- Cyber Security Guidelines For Govt Employees-Final Release-Page2Document5 pagesCyber Security Guidelines For Govt Employees-Final Release-Page2sobeva6070No ratings yet
- Safeguarding ePHI Policy - HIPAADocument5 pagesSafeguarding ePHI Policy - HIPAAlokeshe21No ratings yet
- MGMT Directive 11045 Protection of Classified National Security Information Accountability Control and StorageDocument24 pagesMGMT Directive 11045 Protection of Classified National Security Information Accountability Control and StoragecharlenecleoeibenNo ratings yet
- CSSL Unit 1: Need For SecurityDocument24 pagesCSSL Unit 1: Need For Securitydilip ramakrishnanNo ratings yet
- SEMI FINAL TOPIC 2024 SecurityDocument12 pagesSEMI FINAL TOPIC 2024 SecurityLendie May Leyson BecongNo ratings yet
- Assignment # 3CDocument10 pagesAssignment # 3CNico JaboneNo ratings yet
- A. OBJECTIVE: Differentiate Phishing From Spoofing B. ProcedureDocument1 pageA. OBJECTIVE: Differentiate Phishing From Spoofing B. ProcedureNico JaboneNo ratings yet
- Assignment # 4C Countering Cybersecurity RisksDocument1 pageAssignment # 4C Countering Cybersecurity RisksNico JaboneNo ratings yet
- Complaint-Affidavit: Mario MaurerDocument1 pageComplaint-Affidavit: Mario MaurerNico JaboneNo ratings yet
- Amicable Settlements Are Not AllowedDocument1 pageAmicable Settlements Are Not AllowedNico JaboneNo ratings yet
- Russia Policing System: Group 10Document37 pagesRussia Policing System: Group 10Nico JaboneNo ratings yet
- Quote On Nationalism of Ethan Chua Reaction PaperDocument1 pageQuote On Nationalism of Ethan Chua Reaction PaperNico JaboneNo ratings yet
- Ass. Internal Ballistics PhenomenaDocument3 pagesAss. Internal Ballistics PhenomenaNico Jabone67% (6)
- Ass. L7. Pistol Revolver Advantages and DisadvantagesDocument4 pagesAss. L7. Pistol Revolver Advantages and DisadvantagesNico Jabone100% (1)
- Crime Prevention vs. Crime SuppressionDocument1 pageCrime Prevention vs. Crime SuppressionNico JaboneNo ratings yet
- Police Visibility VS Police OmnipresenceDocument1 pagePolice Visibility VS Police OmnipresenceNico JaboneNo ratings yet
- Instrumentalities: Jabone, Nico T. OCT 06, 2020 CDI 6C 1:30-TFDocument1 pageInstrumentalities: Jabone, Nico T. OCT 06, 2020 CDI 6C 1:30-TFNico JaboneNo ratings yet
- The Anatomy of CrimeDocument1 pageThe Anatomy of CrimeNico JaboneNo ratings yet
- Case AnalysisDocument3 pagesCase AnalysisNico JaboneNo ratings yet