Professional Documents
Culture Documents
Offshore Risk Management - Security Assessment For Offshore Oil-15
Offshore Risk Management - Security Assessment For Offshore Oil-15
Uploaded by
Argenis Moreno0 ratings0% found this document useful (0 votes)
3 views1 pageThe document outlines a 5-step process for API SVA (API RP 70 and API RP 70I) which provides a secondary evaluation of offshore facilities to identify potential security threats, assess consequences, find vulnerabilities, mitigate risks, and implement security measures. The evaluation examines a facility's characteristics, operations, and existing and planned security procedures to protect the facility.
Original Description:
1
Original Title
Offshore Risk Management_ Security Assessment for Offshore Oil-15
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document outlines a 5-step process for API SVA (API RP 70 and API RP 70I) which provides a secondary evaluation of offshore facilities to identify potential security threats, assess consequences, find vulnerabilities, mitigate risks, and implement security measures. The evaluation examines a facility's characteristics, operations, and existing and planned security procedures to protect the facility.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
3 views1 pageOffshore Risk Management - Security Assessment For Offshore Oil-15
Offshore Risk Management - Security Assessment For Offshore Oil-15
Uploaded by
Argenis MorenoThe document outlines a 5-step process for API SVA (API RP 70 and API RP 70I) which provides a secondary evaluation of offshore facilities to identify potential security threats, assess consequences, find vulnerabilities, mitigate risks, and implement security measures. The evaluation examines a facility's characteristics, operations, and existing and planned security procedures to protect the facility.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 1
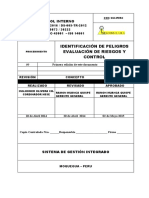
API SVA (API RP 70 and API RP 70I)
“… a secondary evaluation that examines a facility’s characteristics and operations to
identify potential threats or vulnerabilities and existing and prospective security measures
and procedures designed to protect a facility.”
Company policy that defines security goals and
commitments including and control of SSI.
STEP 1: Potential Threat
Communication protocol with authorities for emergency
preparedness, assessment and reporting of security
issues.
STEP 2: Consequence Assessment
Security Plan, Company Security Officer (CSO) and
Facility Security Officer (FSO).
STEP 3: Vulnerability Assessment
Integration of HSAS and MARSEC Security Levels rankings
into offshore and company operations.
STEP 4: Mitigation
STEP 5: Implementation
15
You might also like
- Risk Management Policy Template v1.0Document7 pagesRisk Management Policy Template v1.0rsgrthyjhNo ratings yet
- HSE Risk ManagementDocument9 pagesHSE Risk ManagementSamuelFarfanNo ratings yet
- Asis PSPDocument5 pagesAsis PSPNabeelNo ratings yet
- Offshore Risk Management - Security Assessment For Offshore Oil-15Document1 pageOffshore Risk Management - Security Assessment For Offshore Oil-15lightangeldavidNo ratings yet
- AI-PS Element Guide No 7Document11 pagesAI-PS Element Guide No 7alokcNo ratings yet
- AIPS Guide - Element 7 HEMP Rev 2Document9 pagesAIPS Guide - Element 7 HEMP Rev 2mahamed medlamineNo ratings yet
- Safe Work Procedure: Risk MatrixDocument20 pagesSafe Work Procedure: Risk MatrixScribdTranslationsNo ratings yet
- Content - 2023 Global PWC Audit Guide - Isas - Isa 315 Revised 2019 Identifying and Assessing The Risks of Material MisstatementDocument95 pagesContent - 2023 Global PWC Audit Guide - Isas - Isa 315 Revised 2019 Identifying and Assessing The Risks of Material MisstatementCường Trần MinhNo ratings yet
- AI-PS Element Guide No 7Document10 pagesAI-PS Element Guide No 7Asad KhanNo ratings yet
- SHEM-02 Assurance - Program1Document22 pagesSHEM-02 Assurance - Program1Ajith Kumar AjithNo ratings yet
- SIL Verification of Legacy System V3Document12 pagesSIL Verification of Legacy System V3Anonymous H0xnVVXypgNo ratings yet
- SOP For EHSSRM SystemDocument17 pagesSOP For EHSSRM SystemMd Rafat ArefinNo ratings yet
- Icao Spi Leading and LaggingDocument49 pagesIcao Spi Leading and LaggingAnushka MohitNo ratings yet
- OHS-PR-02-03 HIRA Hazard ID & Risk AssessmentDocument25 pagesOHS-PR-02-03 HIRA Hazard ID & Risk AssessmentShadeed MohammedNo ratings yet
- OHS-PR-02-03 HIRA Hazard ID & Risk AssessmentDocument25 pagesOHS-PR-02-03 HIRA Hazard ID & Risk AssessmentMosfer Al kerdemNo ratings yet
- ERA Chemical 1Document11 pagesERA Chemical 1arsilan324No ratings yet
- OSH-PRO-01 Procedure For Hazard Identification, Risk Assessment and Risk ControlDocument8 pagesOSH-PRO-01 Procedure For Hazard Identification, Risk Assessment and Risk ControlDaniel Cheng MahsaNo ratings yet
- Tataamalan HIRARC 2020Document42 pagesTataamalan HIRARC 2020Khaty JahNo ratings yet
- Hierarchy Risk Control - SOP-V4(1)(1) (1)Document25 pagesHierarchy Risk Control - SOP-V4(1)(1) (1)Mazhar KaleemNo ratings yet
- Risk Assessment UpdatedDocument22 pagesRisk Assessment UpdatedHabib ur rahmanNo ratings yet
- An Introduction To Chemical Process SafetyDocument10 pagesAn Introduction To Chemical Process Safetyhitesh bhoiNo ratings yet
- Exam Summary SIODocument10 pagesExam Summary SIOScarlettocNo ratings yet
- HIRAC Program PristineDocument16 pagesHIRAC Program PristineRigor La Pieta VicencioNo ratings yet
- Hira Sample IataDocument35 pagesHira Sample IataTrầnNgọcPhươngThảoNo ratings yet
- Saf-Hazard Identification ABE-SA-HI-01Document5 pagesSaf-Hazard Identification ABE-SA-HI-01Faisal RazaNo ratings yet
- Ip - 18 - HirarcDocument9 pagesIp - 18 - HirarcScha AffinNo ratings yet
- Information Security Risk Treatment Procedure: Integrated Research CampusDocument17 pagesInformation Security Risk Treatment Procedure: Integrated Research CampusbalajiNo ratings yet
- ISMS Control of Risks and OpportunitiesDocument7 pagesISMS Control of Risks and OpportunitiesAmine RachedNo ratings yet
- Ship SM Cyber SecurityDocument6 pagesShip SM Cyber Securityayhan100% (2)
- AI-PS Element Guide No 2Document7 pagesAI-PS Element Guide No 2Gopi MallikNo ratings yet
- 01 Hazard-Identification PDFDocument72 pages01 Hazard-Identification PDFIndra HazamiNo ratings yet
- M0010 Risk Assessment ManualDocument51 pagesM0010 Risk Assessment ManualnivasmarineNo ratings yet
- PR IpercDocument14 pagesPR IpercAbel Bejar EncisoNo ratings yet
- Contoh Proposal Risk Register and Process Safety Studies - PERTAMINA RU VI Balongan - RevDocument23 pagesContoh Proposal Risk Register and Process Safety Studies - PERTAMINA RU VI Balongan - RevAnonymous cKdbnUHNo ratings yet
- 2019 June 5 Safety PresentationFinalDocument21 pages2019 June 5 Safety PresentationFinalHesham HamyNo ratings yet
- Cybersecurity Audit ReportDocument11 pagesCybersecurity Audit ReportM RANGARAMANUJA ACHARYULUNo ratings yet
- NIST Cybersecurity Framework 2.0 Core Discussion Draft 4-2023 Final PDFDocument26 pagesNIST Cybersecurity Framework 2.0 Core Discussion Draft 4-2023 Final PDFRanjith KumarNo ratings yet
- SP 05 Hazard Identification Risk Assessment and Control HIRAC PDFDocument8 pagesSP 05 Hazard Identification Risk Assessment and Control HIRAC PDFDJOERI WANDHAWANo ratings yet
- Module 2 Introduction To The SRVSOP RBSDocument19 pagesModule 2 Introduction To The SRVSOP RBSAliNo ratings yet
- HIRA, HSE Hazards & Effects Management Process (HEMP) & Risk Register TemplateDocument8 pagesHIRA, HSE Hazards & Effects Management Process (HEMP) & Risk Register TemplateSARFRAZ ALINo ratings yet
- Deloitte CN Cyber Resilience Assessment Framework C Raf 2 Point 0 en 210608Document4 pagesDeloitte CN Cyber Resilience Assessment Framework C Raf 2 Point 0 en 210608Dwi Setiadi Nugroho - VTINo ratings yet
- AI-PS Element Guide No 13Document8 pagesAI-PS Element Guide No 13RazZaq AbbaSiNo ratings yet
- Risk Management Program - Critical Infrastructure (Security)Document3 pagesRisk Management Program - Critical Infrastructure (Security)crow07No ratings yet
- Operational Factors Human Performance - Attachment 19 - Transair SEIMl (Excerpts) - Redacted-RelDocument37 pagesOperational Factors Human Performance - Attachment 19 - Transair SEIMl (Excerpts) - Redacted-RelGFNo ratings yet
- Guide For Major Hazard Facilities: Safety AssessmentDocument48 pagesGuide For Major Hazard Facilities: Safety AssessmentKhaled SaadnehNo ratings yet
- AI-PS Element Guide No 9Document8 pagesAI-PS Element Guide No 9rahul kavirajNo ratings yet
- Csol 530 Biohuman-All Aspects of Risk Management Framework-Aris Nicholas-8-15-2022Document26 pagesCsol 530 Biohuman-All Aspects of Risk Management Framework-Aris Nicholas-8-15-2022api-654754384No ratings yet
- RCSA Session 1 Revised - FINAL PDFDocument9 pagesRCSA Session 1 Revised - FINAL PDFTejendrasinh GohilNo ratings yet
- Microsoft Word - A017 2010 IAASB Handbook ISA 315Document13 pagesMicrosoft Word - A017 2010 IAASB Handbook ISA 315JENNETH AMINAO CASINONo ratings yet
- Ffiec Cat May 2017Document59 pagesFfiec Cat May 2017Zayra CiliaNo ratings yet
- AI-PS Element Guide No 2Document7 pagesAI-PS Element Guide No 2zizu1234No ratings yet
- Sgs Api580Document168 pagesSgs Api580gkdimpuNo ratings yet
- AI-PS Element Guide No 10Document9 pagesAI-PS Element Guide No 10eankiboNo ratings yet
- Scenario-Based (IT) Risk Assessment & Management: Peter R. Bitterli, CISA, CISM, CGEITDocument106 pagesScenario-Based (IT) Risk Assessment & Management: Peter R. Bitterli, CISA, CISM, CGEITfawas hamdi100% (1)
- 8.1-Identify and Manage Risk & Assessment TechniqueDocument48 pages8.1-Identify and Manage Risk & Assessment TechniqueRajesh MuraliNo ratings yet
- P-SST - 002 Procedimiento Ipevr SM 8a SasDocument13 pagesP-SST - 002 Procedimiento Ipevr SM 8a SasYoselin CastrillonNo ratings yet
- SWS S-C Requirement Determination Process - RRoman 11-18-2019 FINALv2Document16 pagesSWS S-C Requirement Determination Process - RRoman 11-18-2019 FINALv2Rayfael RomanNo ratings yet
- The Risk Management Process Security 1647842463Document102 pagesThe Risk Management Process Security 1647842463Luca OrabonaNo ratings yet
- Authorizing Official Handbook: for Risk Management Framework (RMF)From EverandAuthorizing Official Handbook: for Risk Management Framework (RMF)No ratings yet