Professional Documents
Culture Documents
Warisha Rehman - 14768 X.509 Certificates The Extensions in X.509 Certificates
Warisha Rehman - 14768 X.509 Certificates The Extensions in X.509 Certificates
Uploaded by
Syed Hamza HasanOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Warisha Rehman - 14768 X.509 Certificates The Extensions in X.509 Certificates
Warisha Rehman - 14768 X.509 Certificates The Extensions in X.509 Certificates
Uploaded by
Syed Hamza HasanCopyright:
Available Formats
WARISHA REHMAN– 14768
X.509 Certificates
The extensions in X.509 certificates:
1. Authority Key Identifier: The authority key identifier (AKI) is an X.509 v3 certificate
extension. It contains a key identifier which is derived from the public key in the issuer
certificate. According to RFC 5280, the AKI contains the keyIdentifier,
authorityCertIssuer and authorityCertSerialNumber. These two combinations can be
used to identify the issuer certificate i.e. either from the keyIdentifier or from the
authorityCertIssuer and authorityCertSerialNumber. In AKI, keyIdentifier is commonly
used way to identify the issuer certificate.
2. Subject Key identifier extension: this provides a means of identifying certificates that
contain a particular public key.
• To facilitate certification path construction, this extension MUST appear in all
conforming CA certificates, that is, all certificates including the basic constraints
extension (section 4.2.1.10) where the value of CA is TRUE. The value of the subject key
identifier MUST be the value placed in the key identifier field of the Authority Key
Identifier extension (section 4.2.1.1) of certificates issued by the subject of this
certificate.
• This extension MUST NOT be marked critical.
• For CA certificates, subject key identifiers SHOULD be derived from the public key or a
method that generates unique values. Two common methods for generating key
identifiers from the public key are: either a hash value or a 4 bit type field
(keyIdentifier)
3. Subject Alternative Name: Subject Alternative Name (SAN) is an extension to X.509
that allows various values to be associated with a security certificate using a
subjectAltName field. These values are called Subject Alternative Names (SANs). Names
include: email addresses, IP addresses, URIs, DNS names, directory names, other names,
given as a general name or universal principal name: a registered object identifier
followed by a value.
4. Extended Key Usage: Extended Key Usage (EKU) is a method of enforcing the public
key of a certificate to be used for a pre-determined set of key purposes. There can be one
or more such key purposes defined. This extension is usually defined by the end entity
systems in their certificates to support their security design constraints. When EKU is
present in a certificate, it implies that the public key can be used in addition to or in
place of the basic purposes listed in the key usage extension. The EKU extension is
always tagged as critical. The EKU extension has key purposes as follows:
• Server authentication (OID 1.3.6.1.5.5.7.3.1)
• Client Authentication (OID 1.3.6.1.5.5.7.3.2)
• anyExtendedKeyUsage (OID 2.5.29.37.0)
• Every fields are uniquely identified by an OID.
5. CRL Distribution Points: A certificate revocation list (CRL) is a mechanism for
cancelling a client-side certificate. A CRL distribution point (CDP) is a location on an
LDAP directory server or Web server where a CA publishes CRLs. The system
downloads CRL information from the CDP at the interval specified in the CRL, at the
interval that you specify during CRL configuration, and when you manually download
the CRL.
6. Certificate policies: The certificate policies extension contains a sequence of one or
more policy information terms, each of which consists of an object identifier (OID) and
optional qualifiers. Optional qualifiers, which MAY be present, are not expected to
change the definition of the policy. A certificate policy OID MUST NOT appear more
than once in a certificate policies extension
7. Authority Information Access: Authority information access (AIA) is a service location
descriptor that is included in every certificate issued by the CA. Technically, it is one of
the many properties of a certificate. It contains LDAP, HTTP, and CER file location points,
which allow clients to access the CA's own certificate information. Address of the OCSP
responder from where revocation of this certificate can be checked (OCSP access
method). Information about how to get the issuer of this certificate (CA issuer access
method).
8. SCT List: When someone submits a valid certificate to a log, the log responds with a
signed certificate timestamp (SCT), which is simply a promise to add the certificate to
the log within some time period. Certificate authorities can attach an SCT to a certificate
using an X.509v3 extension. The certificate authority (CA) submits a pre certificate to
the log, and the log returns an SCT. The CA then attaches the SCT to the pre certificate as
an X.509v3 extension, signs the certificate, and delivers the certificate to the server
operator.
You might also like
- LPIC-3 Exam 303-300 SecurityDocument102 pagesLPIC-3 Exam 303-300 SecurityBoris IvanovNo ratings yet
- Deep Learning GPU Cluster: Lambda EchelonDocument38 pagesDeep Learning GPU Cluster: Lambda Echeloncephas01100% (1)
- X 509 CertificatesDocument29 pagesX 509 CertificatesRameshkumar MNo ratings yet
- (Win2k3) Certificate Revocation and Status CheckingDocument45 pages(Win2k3) Certificate Revocation and Status Checkingthe verge3No ratings yet
- X 509-PIKDocument5 pagesX 509-PIKMarianinu antonyNo ratings yet
- Certificate Revocation and Status CheckingDocument45 pagesCertificate Revocation and Status CheckingMarcin CiezakNo ratings yet
- Cryptography and Network Security: Fourth Edition by William StallingsDocument33 pagesCryptography and Network Security: Fourth Edition by William Stallingsprudhvi chowdaryNo ratings yet
- NIST Recommendation For X509 PVMsDocument28 pagesNIST Recommendation For X509 PVMsfitoezNo ratings yet
- Public Key InfrastructureDocument4 pagesPublic Key InfrastructurechristineNo ratings yet
- PKI Trust ModelsDocument31 pagesPKI Trust ModelsJennifer HansenNo ratings yet
- CH 14Document26 pagesCH 14hemashekhawat1994007No ratings yet
- Semnaturi PKCDocument26 pagesSemnaturi PKCSrbNo ratings yet
- What Is A Digital Certificate: CA HierarchyDocument11 pagesWhat Is A Digital Certificate: CA HierarchyAgustina RomeroNo ratings yet
- Chapter 04Document30 pagesChapter 04Fatima AlshareefNo ratings yet
- X.509 and Its NeedDocument21 pagesX.509 and Its NeedDhirBagulNo ratings yet
- AuthenticationDocument34 pagesAuthenticationYUVASHRI V PSGRKCWNo ratings yet
- SEC3014 Part4Document42 pagesSEC3014 Part4Yeong Lee SenggNo ratings yet
- Jacobus Ockhuizen Assignment 70-412Document4 pagesJacobus Ockhuizen Assignment 70-412jacobusNo ratings yet
- Unit 4 (Part II) - Authentication Framework For PKCDocument20 pagesUnit 4 (Part II) - Authentication Framework For PKCRAMESH M (RA2113003011001)No ratings yet
- Authorization Policy in A PKI EnvironmentDocument22 pagesAuthorization Policy in A PKI EnvironmentKaran JahlNo ratings yet
- Creating Certificate Policies and Certificate Practice StatementsDocument12 pagesCreating Certificate Policies and Certificate Practice Statementssreeni87No ratings yet
- X.509 - WikipediaDocument10 pagesX.509 - WikipediaAlok TripathiNo ratings yet
- CNS Unit IV PDFDocument80 pagesCNS Unit IV PDFKartheeNo ratings yet
- Cisco Expressway Certificate Creation and Use Deployment Guide X8 2Document29 pagesCisco Expressway Certificate Creation and Use Deployment Guide X8 2repartidorNo ratings yet
- Public Key InfrastructureDocument10 pagesPublic Key InfrastructureYUVASHRI V PSGRKCWNo ratings yet
- Understanding X.509 Certificates and Certificate Path Validation in BWDocument16 pagesUnderstanding X.509 Certificates and Certificate Path Validation in BWkandi_raoNo ratings yet
- ISS Notes Unit-5Document124 pagesISS Notes Unit-5CHIRAG GUPTA PCE19IT010No ratings yet
- Certificate ValidationDocument20 pagesCertificate ValidationUser name second nameNo ratings yet
- Unit 4 - Information Security - WWW - Rgpvnotes.inDocument11 pagesUnit 4 - Information Security - WWW - Rgpvnotes.inshesh6200No ratings yet
- Managing CertificatesDocument4 pagesManaging Certificatesoutplayer65No ratings yet
- X.509 Certificates: R.Muthukkumar Asst - Prof. (SG) /IT NEC, KovilpattiDocument25 pagesX.509 Certificates: R.Muthukkumar Asst - Prof. (SG) /IT NEC, KovilpattiRmkumarsNo ratings yet
- X.509 CertificateDocument15 pagesX.509 CertificateShivani ShahNo ratings yet
- Key Management and Distribution: Cryptographic, Protocol, & Management IssuesDocument33 pagesKey Management and Distribution: Cryptographic, Protocol, & Management IssuessunnyNo ratings yet
- Public Key Infrastructure Configuration Guide, Cisco IOS XE Everest 16.6 Configuring Certificate Enrollment For A PKIDocument50 pagesPublic Key Infrastructure Configuration Guide, Cisco IOS XE Everest 16.6 Configuring Certificate Enrollment For A PKIMitiku ShirkoNo ratings yet
- Subkey: The Client's Choice For An Encryption Key To Be Used To Protect This SpecificDocument11 pagesSubkey: The Client's Choice For An Encryption Key To Be Used To Protect This SpecificDHARINI R SIT 2020No ratings yet
- Key ManagementDocument9 pagesKey ManagementlykamopiaNo ratings yet
- Code Signing NoriDocument4 pagesCode Signing NoriAurelian Ionel CostinNo ratings yet
- Configuring IBM HTTP Server SSL Mutual AuthenticationDocument8 pagesConfiguring IBM HTTP Server SSL Mutual AuthenticationaneturaNo ratings yet
- Digital Certificates and X.509 Authentication ServiceDocument5 pagesDigital Certificates and X.509 Authentication ServiceShiva prasadNo ratings yet
- A.1. What Is An X.509 Certificate?: Role of CertificatesDocument2 pagesA.1. What Is An X.509 Certificate?: Role of CertificatesMaher Saad MechiNo ratings yet
- Understanding Path construction-DS2 PDFDocument14 pagesUnderstanding Path construction-DS2 PDFsh0101No ratings yet
- Implementing and Troubleshooting Certificate Deployment in ISA Server 2006Document9 pagesImplementing and Troubleshooting Certificate Deployment in ISA Server 2006Khodor AkoumNo ratings yet
- Public Key Infrastructure (PKI)Document45 pagesPublic Key Infrastructure (PKI)api-3737433No ratings yet
- Troubleshooting Digital CertificatesDocument12 pagesTroubleshooting Digital Certificatesolam batorNo ratings yet
- Configuring IBM HTTP Server SSL Mutual Authentication PDFDocument8 pagesConfiguring IBM HTTP Server SSL Mutual Authentication PDFstevicNo ratings yet
- 21bce2735 VL2023240505905 Ast05Document25 pages21bce2735 VL2023240505905 Ast05EXTERMINATORNo ratings yet
- CH 23Document25 pagesCH 23Darwin VargasNo ratings yet
- Digital CertificateDocument8 pagesDigital CertificateRachana SonawaneNo ratings yet
- Unit4 x.509Document18 pagesUnit4 x.509yo yoNo ratings yet
- Authentication ServicesDocument23 pagesAuthentication Servicessr23shubhiNo ratings yet
- ADSS SCVP Server DatasheetDocument2 pagesADSS SCVP Server DatasheetannastacyNo ratings yet
- 06-Implementing Public Key Infrastructure: Senior Technical Instructor Ahmedsultan - Me/aboutDocument25 pages06-Implementing Public Key Infrastructure: Senior Technical Instructor Ahmedsultan - Me/aboutManuNo ratings yet
- Rajagiri School of Engineering & Technology: Security in Computing - Module IvDocument21 pagesRajagiri School of Engineering & Technology: Security in Computing - Module IvAdhnan Rafeek KNo ratings yet
- Authentication Authorization and Accounting (AAA) Schemes in WiMAXDocument6 pagesAuthentication Authorization and Accounting (AAA) Schemes in WiMAXUsman MasoodNo ratings yet
- SWL 1.2 2848bhbhDocument5 pagesSWL 1.2 2848bhbh19bcs2856No ratings yet
- Crypto Unit 5 ...Document9 pagesCrypto Unit 5 ...Roshan PradhanNo ratings yet
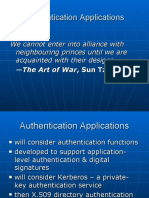
- Management and Security of Telecommunication Networks: Authentication ApplicationsDocument25 pagesManagement and Security of Telecommunication Networks: Authentication ApplicationsZeeshan Afzal AwanNo ratings yet
- Mutual AuthenticationDocument4 pagesMutual Authenticationhey yowNo ratings yet
- Fourth Edition by William StallingsDocument26 pagesFourth Edition by William Stallingskstu1112No ratings yet
- Configure EAP-TLS Authentication With ISE PDFDocument18 pagesConfigure EAP-TLS Authentication With ISE PDFkongarajaykumarNo ratings yet
- Deploying Certificates Cisco Meeting Server: Design your certificates for CMS services and integrate with Cisco UCM Expressway and TMSFrom EverandDeploying Certificates Cisco Meeting Server: Design your certificates for CMS services and integrate with Cisco UCM Expressway and TMSNo ratings yet
- Smart Door SrsDocument18 pagesSmart Door SrsBohtyar KhanNo ratings yet
- Module WiFi-F Pour Onduleur Growatt SPFDocument2 pagesModule WiFi-F Pour Onduleur Growatt SPFSINES FranceNo ratings yet
- Android 7.1 CDDDocument88 pagesAndroid 7.1 CDDGasston GonzaleezzNo ratings yet
- Farah Muse CV and Cover LetterDocument4 pagesFarah Muse CV and Cover LetterFIVE STARNo ratings yet
- Encryption Methods JackieDocument4 pagesEncryption Methods JackieJackilene Anne EleazarNo ratings yet
- Jshara Icsns Viii CryptomlDocument10 pagesJshara Icsns Viii CryptomlBahr SimoNo ratings yet
- Product - SmartModemDocument16 pagesProduct - SmartModemReportBackup BusinessNo ratings yet
- RP E9788793102293Document570 pagesRP E9788793102293Ranjith KumarNo ratings yet
- STQA SyllabusDocument2 pagesSTQA SyllabusNeha KumariNo ratings yet
- RRU1400 RAIN RFID Reader Unit: Minimum Format, Maximum Performance!Document1 pageRRU1400 RAIN RFID Reader Unit: Minimum Format, Maximum Performance!UrdaNo ratings yet
- Chapter 7 Using Data Flow Diagrams: Systems Analysis and Design, 9e (Kendall/Kendall)Document12 pagesChapter 7 Using Data Flow Diagrams: Systems Analysis and Design, 9e (Kendall/Kendall)Mahmoud IbrahimNo ratings yet
- Steganography 2Document23 pagesSteganography 2Manasa SiddannavarNo ratings yet
- Major Project Report ON Attendance Sytem With FACEAPP Using PythonDocument41 pagesMajor Project Report ON Attendance Sytem With FACEAPP Using PythonShivangi tyagiNo ratings yet
- Data Security in Local Network Using Distributed FirewallDocument9 pagesData Security in Local Network Using Distributed FirewallSumanth NallaNo ratings yet
- Computer CrimeDocument15 pagesComputer CrimePravina RavinaNo ratings yet
- 2020 - Industrial Control Systems Cyberattack Trends and CountermeasuresDocument8 pages2020 - Industrial Control Systems Cyberattack Trends and CountermeasureschrisalexoNo ratings yet
- Mlinux 5.3.0b - Software Release NotesDocument7 pagesMlinux 5.3.0b - Software Release Notesskeleton00No ratings yet
- Mod - 1-Programming ConceptsDocument34 pagesMod - 1-Programming ConceptsSeanPharrell18 OfficialNo ratings yet
- Sameer Singh: Professional SummaryDocument3 pagesSameer Singh: Professional Summarysameer singhNo ratings yet
- MixiDocument2 pagesMixiBibi Shafiqah Akbar ShahNo ratings yet
- Unified Payment Interface SecurityDocument4 pagesUnified Payment Interface Securityakumar4uNo ratings yet
- Chapter 4Document44 pagesChapter 4Girma MogesNo ratings yet
- Mod - 1 Programming ConceptsDocument34 pagesMod - 1 Programming ConceptsmargelynmijaresNo ratings yet
- Wachemo University College of Engineering and Technology School OF Computing AND Informatics Department of Software EngineeringDocument47 pagesWachemo University College of Engineering and Technology School OF Computing AND Informatics Department of Software EngineeringHasen AumerNo ratings yet
- DBMS Full 1st SemDocument147 pagesDBMS Full 1st SemAnziya AbdulkhaderNo ratings yet
- Library Management Project Proposal EditDocument5 pagesLibrary Management Project Proposal EditJ.A.S.M JAYASINGHENo ratings yet
- Journal Learning Bima Arya Dewangga - 1913025020Document2 pagesJournal Learning Bima Arya Dewangga - 1913025020Niskala ProjectNo ratings yet
- Ui5 Front-End Gensoft Technologies: Mobile: E-Mail: WebsiteDocument4 pagesUi5 Front-End Gensoft Technologies: Mobile: E-Mail: WebsiteJanardhanNo ratings yet
- Training - PeopleCode EventsDocument187 pagesTraining - PeopleCode Eventsprabindas100% (1)