Professional Documents
Culture Documents
The Review of The Commercial Quantum Key Distribution System
The Review of The Commercial Quantum Key Distribution System
Uploaded by
Imogen SmithOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
The Review of The Commercial Quantum Key Distribution System
The Review of The Commercial Quantum Key Distribution System
Uploaded by
Imogen SmithCopyright:
Available Formats
See discussions, stats, and author profiles for this publication at: https://www.researchgate.
net/publication/334070231
The Review of the Commercial Quantum Key Distribution System
Conference Paper · December 2018
DOI: 10.1109/PDGC.2018.8745822
CITATIONS READS
6 659
2 authors:
Anton Pljonkin Pradeep Kumar Singh
Southern Federal University Jaypee University of Information Technology
28 PUBLICATIONS 120 CITATIONS 162 PUBLICATIONS 797 CITATIONS
SEE PROFILE SEE PROFILE
Some of the authors of this publication are also working on these related projects:
Cross-Domain Collaborative Filtering View project
Software Quality Model and Assessment View project
All content following this page was uploaded by Anton Pljonkin on 20 December 2019.
The user has requested enhancement of the downloaded file.
The Review of the Commercial Quantum Key
Distribution System
Anton Pljonkin Pradeep Kumar Singh
Southern federal university Jaypee University of Information Technology
Taganrog, Russia Waknaghat, Solan, H.P., INDIA
pljonkin@mail.ru pradeep_84cs@yahoo.com
Abstract—A review of the existing commercial quantum must be absolutely random, its length must be greater than or
key distribution systems was conducted. The principle of equal to the length of the encoded message and the key can
operation of a fiber-optic quantum key distribution system be used only once.
with phase coding of photon states is described. The operation
of the system in the mode of forming quantum keys is Classical cryptographic systems often use only two rules
described. The synchronization process is analyzed, which out of three. For example, using pseudo-random processes
consists in detecting a time interval with an optical pulse. The when generating an encryption key. Or using a single
basic properties and parameters of auto-compensation encryption key multiple times. But more often two rules are
quantum key distribution system are reviewed. The images of violated at once: a standard length key is used to encrypt
the current stand of the quantum-cryptographic network are long messages repeatedly. Classic cryptosystems are
given. The stand includes two stations of the quantum key vulnerable.
distribution system with phase coding of photon states, two
servers and data transmission channels. It is shown that the Practical implementation of quantum cryptography is
formation of a quantum key in the experiment is carried out at based on the quantum key distribution systems. If existing
a rate of 500 bits per second. The length of the quantum encryption algorithms can be cracked by mathematical
communication channel in the experiment is 24 km. In this improvements, then quantum cryptography is the only way
case, the quantum channel consists of a conventional single- to solve the key distribution problem. At the heart of
mode optical fiber. Trends in the development of quantum key quantum cryptography lie the following statements: it is
distribution systems, as well as trends in the development of impossible to clone an unknown quantum state and it is
protocols for quantum cryptography was conducted. impossible to extract information about non-orthogonal
quantum states without perturbation. Consequently, any
Keywords— quantum key, algorithm, synchronization, measurement performed by an attacker will lead to a change
photon pulse in the quantum state of the information carrier. The laws of
I. INTRODUCTION quantum physics cannot be violated.
The main problem in the transfer of confidential In quantum cryptography, symmetric cryptosystems are
information is the distribution of the secret key between the common [3]. In these systems, only one key is used for
correspondents. To achieve absolute secrecy in the encryption and for deciphering confidential information.
transmission of messages is possible only by solving the Messages sent along the lines of quantum communication, in
problem of key distribution. To protect the data, various theory, can neither be intercepted nor copied. To date, real-
methods, algorithms and encryption protocols are used. The functioning quantum communication systems have been
security of existing telecommunications networks is limited created. The efforts of developers are now aimed at
by the computational capabilities of the attacker. increasing the range of communication and improving the
characteristics of fiber optic components.
The physical solution of the key distribution problem is
known as quantum cryptography and is based on the Quantum key distribution is a technology based on the
encoding of the quantum state of a single particle [1, 2]. laws of quantum physics to create a string of random bits for
Quantum cryptography, as a promising direction, solving the two remote users, which is used as a cryptographic key. It is
problem of key distribution has already taken a worthy place believed that quantum key distribution systems can meet the
among systems that provide confidential information requirements of absolute secrecy when encrypting messages.
transmission. The essence of quantum cryptography lies in A symmetric cryptosystem generates a shared secret key and
the reliable distribution of a single key between legitimate distributes it among legitimate users. Such a key, or rather a
users. The attractiveness of the idea of quantum bit array, was called a "one-time notebook".
cryptography is to create an absolutely random secret key. Its
II. HISTORY OF QUANTUM CRYPTOGRAPHY
secrecy and the impossibility of an unobtrusive audition by
an unauthorized person are based on the laws of quantum The history of quantum cryptography began back in the
physics. In contrast to the classical methods of cryptography, late 1960s, when Columbia University student Steven
which are based on mathematical patterns and potentially Wiesner told Charles Bennett the idea of quantum banknotes.
lend themselves to deciphering. Now the research in the field They cannot be faked in principle, because it is excluded by
of quantum telecommunications is actively conducted. Even the laws of nature. The essence of the idea was to place
today, corporations are creating the first samples of quantum several quantum objects on each banknote. These can be, for
computers, which means that the future of classical example, traps with photons, each of which is polarized at a
cryptography is under threat. certain angle in one of two bases. Either at an angles of 0 and
90, or 45 and 135 degrees. The serial number is printed on a
To ensure the absolute secrecy of the cryptographic banknote, but the combination of polarizations and bases
scheme, it is necessary to fulfill certain conditions: the key
XXX-X-XXXX-XXXX-X/XX/$XX.00 ©20XX IEEE
corresponding to the number is known only to the bank. To they both get the same sequence. It can be used as an
counterfeit such a banknote, the counterfeiter must measure encryption key. This is a truly random sequence that cannot
the polarization of each photon. However, he does not know be guessed or calculated. If someone tries to spy entangled
in which basis each of them is polarized. If he makes a photons, the correlation between them will be lost and it will
mistake with the basis, the polarization of the photon will be impossible to extract the key from them.
change and the counterfeit banknote will be incorrectly
polarized. To date, real-functioning quantum communication
systems have been created (see Fig. 1).
At the same time, Wiesner proposed using the same
principle to protect information and this technology is now The efforts of developers are now aimed at increasing the
close to implementation. Wiesner's ideas were not avowed range of communication, increasing the speed of forming a
immediately. Back in the early 1970s, Wiesner sent his quantum key, improving the characteristics of fiber optic
article on quantum cryptography to the journal IEEE components.
Transactions on Information Theory. But the language of the
article seemed too complicated for editors and reviewers.
Only in 1983 this article was published in the journal ACM
Newsletter and it was the first publication about the
fundamentals of quantum cryptography in the history.
Initially, Wiesner and Bennett considered the option of
transmitting encrypted messages using quantum "carriers."
At the same time, eavesdropping would corrupt the message
and would not allow it to be read. Then they came to an Fig. 1. Commercial quantum key distribution systems.
improved version - the use of quantum channels for the
Quantum key distribution technology based on the laws
transfer of one-time "cipher-tags". That is encryption keys.
of quantum physics to create sequences of random bits,
Quantum communication systems are based on the use of which is used as a cryptographic key for two remote users. It
quantum properties of information carriers. If in ordinary is believed that the QKD systems can meet the requirements
telecommunications networks the data is encoded in the of absolute secrecy when encrypting messages. A symmetric
amplitude and frequency of the radiation or electrical cryptosystem generates a shared secret key and distributes it
oscillation, then in the quantum ones it is encoded in the among legitimate users for both encryption and decryption of
amplitude of the electromagnetic field or in the photon messages. An attacker attempting to investigate transmitted
polarization. Of course, much more expensive and data cannot measure photons without distorting the original
sophisticated equipment will be required, but these tricks are message. Legal users on an open channel compare and
justified. The fact is that the transmission of information discuss signals transmitted on a quantum channel, thereby
through the quantum channels provides one hundred percent verifying them for the possibility of interception. If they do
protection against "wiretapping". According to the laws of not find any errors, then the transmitted information can be
quantum mechanics, measuring the properties of a particular considered randomly distributed and secret, despite all the
quantum object, for example measuring the polarization of a technical possibilities that a cryptanalyst can use.
photon, inevitably changes its state. The receiver will see that
For the last several years, the development of quantum
the state of photons has changed, and this cannot be
cryptography technology is provided by improving the
prevented in principle. These are the fundamental laws of
characteristics of fiber-optic modules and components.
nature. The first successful experiment on quantum data
International companies are constantly expanding the range
transfer was carried out by Bennett and Gilles Brassard in the
of high-tech components of fiber optics. The most popular
end of October 1989, when a protected quantum channel was
components for improving the quantum key distribution
established at a distance of 32 cm. The setup changed the
technology are single photon sources, single photon counting
polarization of photons, but the power supply noise varied
modules, fiber optic phase modulators, random number
differently depending the polarization. In October 2007, the
generators.
methods of quantum cryptography were first applied in a
large-scale project. The quantum secure communication The development of commercial prototype QKDSs is
system, developed by the Swiss company IdQuantique, was carried out by the many laboratories [4-9]. However, only a
used to transmit voting data at the parliamentary elections in few QKD systems of MagiQ and IDQuantique have been
Geneva. Thus, the Swiss votes were protected like no other successfully implemented and brought to commercial
information. use [10, 11]. We note that both optical fiber QKD systems
operate according to an auto-compensation scheme with
A lot of research groups around the world are developing
phase coding of photon states. Such systems are
devices for "restoring" quantum data. The so-called quantum
characterized by stable operability under varying external
repeaters, which are capable of "animating" photons.
conditions.
Scientists are studying the phenomenon of quantum
entanglement, in which the states of two or more objects III. FIRST QUANTUM PROTOCOL
(atoms, photons and ions) are connected. If the state of one
of the pair of entangled photons is measured, then the state of QKD systems operate under the control of quantum
the second one will immediately become definite, and the protocols [12]. There are several protocols of quantum
states of both of them will be uniquely related. For example, cryptography based on the transmission of information by
if one photon turns out to be polarized vertically, then the coding the states of single photons, for example: BB84, B92,
second one is horizontal and vice versa. If you distribute Koashi-Imoto, SARG04 and their modifications. Note that
pairs of entangled photons between two remote partners, under the signal in QKD systems is meant the transmitted
quantum state of the photon. The first protocol that was equipment of the attacker with the aim of interfering with the
implemented in QKD systems is called BB84. Note that this operation of the QKDS. An attack "Trojan Horse" can serve
protocol has more effective modifications. And in the last as an example of the most approximate to the practical
system of quantum key distribution one-way protocol COW implementation. It provides the substitution of original
is applied. messages transmitted from the transceiver to the coding
station with messages from the attacker. General scheme of
The figure (see Fig. 2) shows the known scheme of the this attack is presented on the figure (Fig. 3).
protocol BB84. In a simplified form, the scheme is as
follows. According to the protocol BB84, the sender
generates photons with a random polarization.
Fig. 3. Optical power removal scheme. Y-type – optical divider; Det –
detectors.
Fig. 2. BB84 quantum protocol scheme.
Theoretically, Eva (attacker) is able to generate copies of
The receiver receives these photons, randomly chooses a optical pulses intercepted from the transceiver station and
way to measure the polarization and informs through the send them to the coding station. It is established that under
open channel which method is chosen for each photon this attack scheme, the percentage of quantum errors in the
without revealing the measurement results themselves. After formation of a key with the presence of an attacker does not
that, the sender on the same open channel reports whether the exceed the specified threshold. Thus, legitimate users Bob
type of measurement for each photon was chosen correctly. and Alice are not able to recognize the presence of an
As a result, a raw key is formed. attacker in the quantum channel of fiber optic transmission
line.
IV. SYNCHRONIZATION
The operation of the QKD system is impossible without Commercial auto-compensated QKDS with phase coding
synchronization [13-15]. The most important component of of photon states Clavis2 operates on the basis of a single-
the two-pass QKDS operation is the synchronization of the fiber cable in a two-pass scheme. Such an implementation
transceiver and coding stations. During the synchronization considerably complicates the attacker's task of unauthorized
process, optical pulses propagate from the transceiver station access to the quantum communication channel. However, in
to the coding one and back. Note that the transmission of 2008, a group of scientists from the Norwegian University
synchronizing signals from the transceiver station to the showed the possibility of hacking such quantum
coding one is always carried out in multiphoton mode. cryptographic systems. As in the scheme described above, an
Multiphoton mode is necessary for the implementation of the attacker simulates the operation of a transceiver and a coding
protocol of quantum cryptography when optical signal is station. The moment of arrival (interception) of an optical
transmitted in direct way. Synchronization in the pulse during a direct passage does not give complete
implemented commercial QKDS includes two stages. information to an attacker about the operation of a QKD
system (as in the case of using a two-wire circuit). The
The first stage is initiated with the initial configuration of decisive moment is the appearance of an optical pulse in the
the QKDS and consists in determining the moment of backward propagation of a reflected signal in a quantum
receiving of the optical pulse by single-photon channel. Thus, by withdrawing part of the energy of a
photodetectors of the transceiver station. This happens by multiphoton pulse at two points of the optical path (with
measuring the length of the path of propagation of the optical forward and backward propagation of the optical pulse as in
pulse from the transceiver station to the coding and vice the slide) during the synchronization, the attacker is able to
versa. The second stage of synchronization is a component of calculate the delay of the reflected optical signal for further
the algorithm of the quantum cryptography protocol and is simulation of the coding station. Data on the delay time of
necessary for controlling phase modulators in the process of the optical signal allows, at the right time, to send imitation
forming a quantum key. signals to the photodetectors of the transceiver station. Thus,
an attacker can exploit the vulnerability of the
Analysis of the literature and experimental studies of a
synchronization process in multi-photon transmission to
two-pass auto-compensation QKDS with phase coding of
obtain additional data on the parameters of the quantum
photon states show that the synchronization process is
communication channel. Recall that synchronization means
realized in a multiphoton mode. Here the average number of
the determination of the propagation path length of the
photons in a pulse is measured in tens of thousands. It is
optical pulse. The path length is not only the quantum
established that at the synchronization of QKDS, single-
communication channel itself, but also the lengths of all the
photon photodiodes operates in a linear mode. The latter
fiber-optic components inside the stations. The optical path
potentially makes it easier for an attacker to organize
includes direct and reverse propagation of the signal. The use
unauthorized access to a fiber-optic communication channel
of a powerful optical pulse at synchronization is necessary to
(to a quantum channel). The purpose of unauthorized access
increase the probability of a correct detection of the signal
can be not only to read information, but also synchronize the
time interval. At the preparatory stage of preliminary
synchronization, the transceiver station generates gating generated directly on the servers. The files are identical and
pulses for single-photon avalanche photodiodes. their contents are an array of keys and their identifiers.
Simultaneously the delay time is gradually increases Search for the necessary keys in the files is done by their
relatively to the moment of emitting of the pulse. This identifiers. The length of the key is set when generating files
determines the Coarse Delay time. Physically, this search is ranging from 32 to 512 bits. The keys are integrated into the
performed by step-by-step switching of the counter by IPsec protocol configuration simultaneously on remote
intervals. Intervals are called time windows. The procedure servers. The speed of key formation by the QKD system in
consists in the accumulation of triggers in each time window. the experiment is about 500 bit/sec. To integrate the quantum
Each trigger is the registration of photons by avalanche keys into the VPN tunnel encryption algorithms, keys of the
photodetectors. At the second stage of preliminary required length are copied to the appropriate IPsec protocol
synchronization, a more accurate calibration of the pulse configuration area.
recording time takes place. The previously defined time
interval preceding and following it in time intervals are V. CONCLUSION
divided into time intervals called Fine Delay. Each of the A review of the existing commercial quantum key
three intervals is divided into 17 subintervals. Next, a time distribution systems was conducted. The principle of
window with the largest number of pickups of the operation of a fiber-optic quantum key distribution system
photodetectors is searched. This determines the value of the with phase coding of photon states is described. The images
Fine Delay time. The result of the synchronization operation of the current stand of the quantum-cryptographic network
is the detection of a signal time window with duration of 10 are given. Today, existing systems of quantum
ps. communication are used in banks, corporations and
As noted earlier, the QKD system consists of two commercial structures. Note that scientific laboratories are
stations. The transceiver station is called "Bob", the coding developing the systems of quantum distribution of various
station is "Alice". The stations are connected by a fiber-optic types [17, 18]. For example, systems with polarization
transmission line (a quantum channel), which is made from a coding. Recently, experiments were performed on the
single-fiber single-mode optical cable. The construction of quantum coupling between ground stations and a satellite.
the stations has a standardized size for mounting 19 inches. The keys were transmitted along the optical beam.
Optical signals are transmitted from the transceiver station to Of course, to date, quantum systems are not perfect.
the coding and back through one optical path. Quantum computers are already being created. The
Note that the function of the QKD system consists not in development of quantum computers potentially threatens the
data protection, but in the formation and distribution between security of classical cryptosystems. Thus, quantum
correspondents of quantum keys. Let's show on a simple cryptography will inevitably come into our daily life. This
example how the scheme of application of quantum keys for applies to each of us. Quantum cryptography is not only
encryption of transmitted messages works. The Fig. 4 shows some kind of military or espionage secrets, these are credit
a simple scheme of a quantum-cryptographic network [16]. card numbers, they are medical records. Each of us has a lot
This is a valid stand that uses 512-bit keys. The structure of of confidential information, and the more open the world
the stand includes: a QKD system consisting of two stations; becomes, the more important it is for us to control access to
two servers with software and a data network. Interaction of it.
servers with QKD systems is carried out via USB service ACKNOWLEDGMENT
channel.
Work is performed within the grant of President of
Russian Federation for state support of young Russian
scientists МК-2338.2018.9 ―Creation of an automated
algorithm for integrating quantum keys into the data network
while providing enhanced security against unauthorized
access to the quantum communication channel‖.
REFERENCES
[1] Gisin N. et al. Quantum cryptography. Rev. Mod. Phys. 2002. Vol.
74, № 1. P. 145–195.
[2] Bennet C. H. et. al. Experimental quantum cryptography. J. Cryptol.
1992. Vol. 5. P. 3–28.
[3] Stucki D. et. al. Quantum Key Distribution over 67 km with a plug &
Fig. 4. Quantum-cryptography experimental stand. Point to point topology. play system. Quantum Phys. 2002. P.8.
[4] Broadbent A.., Schaffner C.. Quantum cryptography beyond quantum
The trusted communication channel is realized on the key distribution. Des. Codes, Cryptogr. № 78. P. 351–382.
basis of a single-fiber single-mode optical fiber. The data [5] Makarov V. Quantum cryptography and quantum cryptanalysis.
transmission network is configured in a point-to-point Science And Technology. 2007. № March. 1-158 p.
topology. Keys are generated and accumulated in the buffer [6] K.Y. Rumyantsev, A.P. Pljonkin Security of synchronization mode of
zone. This occurs in a cyclic mode. On the basis of Ethernet, quantum keys distribution system. Izvestiya SFedU. Engineering
a virtual VPN tunnel based on IPsec is organized. sciences. 2015. №5(166). P. 135−153.
Authentication and encryption are configured for each [7] V. Kurochkin, A. Zverev, J. Kurochkin, I. Riabtzev, I. Neizvestnyi.
Quantum Cryptography Experimental Investigations. Photonics.
channel being created for each direction and for each 2012. № 5. P. 54 – 66
protocol. On servers, files with key material are generated. [8] L. Lydersen, C. Wiechers, C. Wittmann, D. Elser, J. Skaar, and
The peculiarity of the formation scheme is that the files and V. Makarov, Hacking commercial quantum cryptography systems by
their contents are not transmitted over the network, but are tailored bright illumination, Nat. Photonics 4, 686 (2010).
[9] S. Sajeed, A. Huang, S. Sun, F. Xu, V. Makarov, and M. Curty
Insecurity of detector-device-independent quantum key distribution,
Phys. Rev. Lett. 117, 250505 (2016).
[10] A.P. Pljonkin, K.Y. Rumyantsev. Single-photon Synchronization
Mode of Quantum Key Distribution System. India, New Delhi,
2016, P.531–534. DOI: 10.1109/ICCTICT.2016.7514637.
[11] K.E. Rumyantsev, A. P. Pljonkin. Preliminary Stage Synchronization
Algorithm of Auto-compensation Quantum Key Distribution System
with an Unauthorized Access Security. International Conference on
Electronics, Information, and Communications (ICEIC). 2016.
Vietnam, Danang. P. 1–4. DOI:
10.1109/ELINFOCOM.2016.7562955. WOS:000389518100035.
IDS: BG5KP.
[12] K.E. Rumyantsev, A.P. Pljonkin. Synchronization algorithm of
quantum key distribution system with protection from unauthorized
access. 2015 Workshop on Recent Advances in Photonics (WRAP).
Electronic ISBN: 978-1-5090-3921-0. DOI:
10.1109/WRAP.2015.7805988. WOS:000392633700046. ISBN:978-
1-5090-3921-0.
[13] A.P. Pljonkin, Features of the Photon Pulse Detection Algorithm in
the Quantum Key Distribution System. ICCSP '17 Proceedings of the
2017 International Conference on Cryptography, Security and Privacy
Pages 81-84. Wuhan, China — March 17 - 19, 2017. ACM New
York, NY, USA ©2017. ISBN: 978-1-4503-4867-6. Doi:
10.1145/3058060.3058078.
[14] Pljonkin, A.; Rumyantsev, K.; Singh, P.K. Synchronization in
Quantum Key Distribution Systems. Cryptography 2017, 1, 18.
doi:10.3390/cryptography1030018
[15] Yuen, H. P. (2016). Security of Quantum Key Distribution. IEEE
Access, 4, 724–749.
[16] Anton Pljonkin, Konstantin Rumyantsev. Quantum-cryptographic
network. East-West Design & Test Symposium (EWDTS), 2016
IEEE. Electronic ISSN: 2472-761X. DOI:
10.1109/EWDTS.2016.7807623.
[17] Distribution, Q. K., & Cases, U. (2010). GS QKD 002 - V1.1.1 -
Quantum Key Distribution; Use Cases. Innovation, 1, 1–32.
[18] Chan, P., Lucio-Martínez, I., Mo, X., & Tittel, W. (2011). Quantum
Key Distribution. Distribution, 20. https://doi.org/10.1007/978-3-642-
04831-9.
View publication stats
You might also like
- Manual Skoda Octavia - Gearbox atDocument208 pagesManual Skoda Octavia - Gearbox atCornea Horatiu Sebastian88% (8)
- A Survey On Quantum Key Distribution ProtocolsDocument9 pagesA Survey On Quantum Key Distribution ProtocolsAnonymous lVQ83F8mCNo ratings yet
- Quantum Cryptography The Concept and Cha PDFDocument4 pagesQuantum Cryptography The Concept and Cha PDFHasan BadirNo ratings yet
- Quantum Computing: Quantum Key DistributionDocument4 pagesQuantum Computing: Quantum Key DistributionInternational Organization of Scientific Research (IOSR)No ratings yet
- The Impact of Quantum Computing On CybersecurityDocument3 pagesThe Impact of Quantum Computing On CybersecurityInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- An Overview of Major Developments, Applications and Challenges in Quantum CryptographyDocument9 pagesAn Overview of Major Developments, Applications and Challenges in Quantum CryptographyInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Chapter 94Document5 pagesChapter 94cheintNo ratings yet
- Quantum Cryptography ThesisDocument7 pagesQuantum Cryptography ThesisDoMyCollegePaperJackson100% (2)
- Quantum Cryptography State-Of-Art, Challenges and Future PerspectivesDocument7 pagesQuantum Cryptography State-Of-Art, Challenges and Future Perspectivesshahriar.iqbal.devNo ratings yet
- Quantum Computing Applications in Cryptography: A Comprehensive AnalysisDocument2 pagesQuantum Computing Applications in Cryptography: A Comprehensive Analysiskapitanjuan27No ratings yet
- Quantum Cryptography Research PaperDocument7 pagesQuantum Cryptography Research PaperDương Trần Mỹ LinhNo ratings yet
- The Impact of Quantum Computing On CryptographyDocument6 pagesThe Impact of Quantum Computing On CryptographyIJRASETPublications100% (1)
- Quantum Cryptography Thesis PDFDocument7 pagesQuantum Cryptography Thesis PDFlorischadedesmoines100% (2)
- ECE - Network - KrantishDocument4 pagesECE - Network - KrantishTJPRC PublicationsNo ratings yet
- Quantum ComputersDocument13 pagesQuantum ComputersAayush GargNo ratings yet
- State-of-the-Art Survey of Quantum CryptographyDocument38 pagesState-of-the-Art Survey of Quantum Cryptographyehtesham.k90No ratings yet
- Wang QuantumComputationQuantum 2012Document23 pagesWang QuantumComputationQuantum 2012ANo ratings yet
- Secure Quantum Network Coding TheoryDocument288 pagesSecure Quantum Network Coding Theorysomeuser287No ratings yet
- Blockchain and Quantum Computing: June 2017Document17 pagesBlockchain and Quantum Computing: June 2017Rekha SreenivasuluNo ratings yet
- SENSORS11Document13 pagesSENSORS11hppavillonNo ratings yet
- The Eclectic: Nit Andhra PradeshDocument14 pagesThe Eclectic: Nit Andhra PradeshUGNo ratings yet
- Quantum Cryptography Final VersionDocument27 pagesQuantum Cryptography Final VersionBharat AroraNo ratings yet
- Quantum Random Number Generator ThesisDocument5 pagesQuantum Random Number Generator Thesistygocixff100% (2)
- Zhai - 2019 - J. - Phys. - Conf. - Ser. - 1168 - 032077Document9 pagesZhai - 2019 - J. - Phys. - Conf. - Ser. - 1168 - 032077zthrtzaljccqnuvjdvNo ratings yet
- Implementation of Quantum Key Distribution Algorithm in Real Time IBM Quantum ComputersDocument7 pagesImplementation of Quantum Key Distribution Algorithm in Real Time IBM Quantum ComputersIJRASETPublicationsNo ratings yet
- Smart Network Field TheoryDocument49 pagesSmart Network Field TheoryDetonadorJVCNo ratings yet
- Post-Quantum and Code-Based Cryptography-Some Prospective Research DirectionsDocument31 pagesPost-Quantum and Code-Based Cryptography-Some Prospective Research Directionsmohammed.it.11rNo ratings yet
- An Improved Image Encryption Algorithm Based On CHDocument11 pagesAn Improved Image Encryption Algorithm Based On CHIqra AnamNo ratings yet
- Three Party Authenticated Key Distribution Using Quantum CryptographyDocument3 pagesThree Party Authenticated Key Distribution Using Quantum CryptographyIJMERNo ratings yet
- Quantum Cryptography: Ankit Shukla, Deepak Kumar (3 Year)Document4 pagesQuantum Cryptography: Ankit Shukla, Deepak Kumar (3 Year)Ankit ShuklaNo ratings yet
- Cryptography Using Quantum Key Distribution in Wireless NetworksDocument5 pagesCryptography Using Quantum Key Distribution in Wireless NetworksThet Hmue Hay ThiNo ratings yet
- Quantum Cryptography Thesis 2013Document9 pagesQuantum Cryptography Thesis 2013aaqvuknbf100% (2)
- Quantum Cryptography: Realizing Next Generation Information SecurityDocument4 pagesQuantum Cryptography: Realizing Next Generation Information SecurityInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- MLQCDocument14 pagesMLQCRamadevi UnknownNo ratings yet
- Thesis Quantum CryptographyDocument5 pagesThesis Quantum CryptographyYasmine Anino100% (1)
- Quantum Cryptography Research Paper PDFDocument4 pagesQuantum Cryptography Research Paper PDFhbkgbsund100% (1)
- Probablistic Queuing Model To Detect Covert Channel Communication in Wireless Sensor NetworkDocument5 pagesProbablistic Queuing Model To Detect Covert Channel Communication in Wireless Sensor NetworkRahul SharmaNo ratings yet
- Side-Channel Attacks On Post-Quantum Cryptographic Software ImplementationsDocument4 pagesSide-Channel Attacks On Post-Quantum Cryptographic Software ImplementationsMircea PetrescuNo ratings yet
- Quantem Mechanics in Data SecurityDocument21 pagesQuantem Mechanics in Data Securityibrahim zouaidNo ratings yet
- Vulnerability of Blockchain Technologies To Quantum Attacks - 2021 - ArrayDocument10 pagesVulnerability of Blockchain Technologies To Quantum Attacks - 2021 - ArraygargorisgargNo ratings yet
- Quantum Computing and Cryptography Today PDFDocument22 pagesQuantum Computing and Cryptography Today PDFBill LasosNo ratings yet
- Quantum Cryptography - A Secure Path To Future CommunicationDocument7 pagesQuantum Cryptography - A Secure Path To Future Communicationharunkleoglu1No ratings yet
- A Quantum Review - Cyber Security and Emerging TechnologiesDocument4 pagesA Quantum Review - Cyber Security and Emerging Technologiesmanoj kumarNo ratings yet
- Research Paper On Quantum CryptographyDocument8 pagesResearch Paper On Quantum Cryptographyistdijaod100% (1)
- An Invention of Quantum Cryptography Over The Classical Cryptography For Enhancing SecurityDocument4 pagesAn Invention of Quantum Cryptography Over The Classical Cryptography For Enhancing SecurityInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Quantum Cryptography SeminarDocument25 pagesQuantum Cryptography SeminarFadi AkilNo ratings yet
- Palani DocumentDocument11 pagesPalani DocumentR Naveen BabuNo ratings yet
- Chaos Based Communication System Using Reed Solomon (RS) Coding For AWGN & Rayleigh Fading ChannelsDocument5 pagesChaos Based Communication System Using Reed Solomon (RS) Coding For AWGN & Rayleigh Fading ChannelsInternational Journal of Scientific Research in Science, Engineering and Technology ( IJSRSET )No ratings yet
- Good Morning EveryoneDocument5 pagesGood Morning EveryoneUtkarsh VermaNo ratings yet
- The Future of Quantum ComputerDocument6 pagesThe Future of Quantum ComputerVIVA-TECH IJRINo ratings yet
- Applied Neuro CryptographyDocument191 pagesApplied Neuro CryptographyRaiee Dee100% (1)
- Renner Wolf 2023 Quantum Advantage in CryptographyDocument16 pagesRenner Wolf 2023 Quantum Advantage in Cryptographyprimeto002No ratings yet
- A Secure Cryptocurrency Scheme Based On PostQuantum BlockchainDocument9 pagesA Secure Cryptocurrency Scheme Based On PostQuantum BlockchainErick HernándezNo ratings yet
- Quantum Computing in Data Security: A Critical Assessment: SSRN Electronic Journal January 2020Document8 pagesQuantum Computing in Data Security: A Critical Assessment: SSRN Electronic Journal January 2020ohood alzaidiNo ratings yet
- (IJCST-V5I3P31) :P. Rajesh Kannan, Dr. MalaDocument5 pages(IJCST-V5I3P31) :P. Rajesh Kannan, Dr. MalaEighthSenseGroupNo ratings yet
- On CryptographyDocument8 pagesOn CryptographyClive AwNo ratings yet
- Quantum Internet - Bushra KhanumDocument22 pagesQuantum Internet - Bushra KhanumMd Shadab AlamNo ratings yet
- Application of Cellular Automata For Cryptography.: January 2003Document9 pagesApplication of Cellular Automata For Cryptography.: January 2003Simon LammerNo ratings yet
- Quantum Cryptography - Recent Trends: Prof. Murali PDocument11 pagesQuantum Cryptography - Recent Trends: Prof. Murali Psanthosha s mNo ratings yet
- Zhai 2019 J. Phys. Conf. Ser. 1168 032077Document9 pagesZhai 2019 J. Phys. Conf. Ser. 1168 032077euginemagturocaststudentNo ratings yet
- Pneuvay Pneumatic Conveying Inspection Hatches SystemsDocument2 pagesPneuvay Pneumatic Conveying Inspection Hatches Systemsaocun0425hotmail.comNo ratings yet
- Business Plan ProposalDocument3 pagesBusiness Plan ProposalAngel Roshni CabicalNo ratings yet
- AIRPORTBROCHUREINTEGRODocument12 pagesAIRPORTBROCHUREINTEGROsebastianNo ratings yet
- cFosSpeed Setup LogDocument22 pagescFosSpeed Setup Logdamien boyerNo ratings yet
- PC Case ModDocument42 pagesPC Case ModMihai IavorschiNo ratings yet
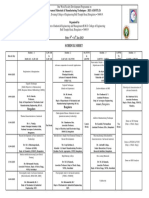
- SCHEDULE of AMMT-2022-2023Document1 pageSCHEDULE of AMMT-2022-2023SRIKUMAR BIRADARNo ratings yet
- Nog Mpls FRR PDFDocument232 pagesNog Mpls FRR PDFMoïse GuilavoguiNo ratings yet
- Linda Foulkes - Learn Microsoft Office 2021 - Your One-Stop Guide To Upskilling With New Features of Word, PowerPoint, Excel, Outlook, and Teams, (2022, Packt Publishing) - Libgen - LiDocument655 pagesLinda Foulkes - Learn Microsoft Office 2021 - Your One-Stop Guide To Upskilling With New Features of Word, PowerPoint, Excel, Outlook, and Teams, (2022, Packt Publishing) - Libgen - LimatiasNo ratings yet
- Catalog - GPS Tracker - Simply Classic 20191126Document41 pagesCatalog - GPS Tracker - Simply Classic 20191126Oscar CaguanaNo ratings yet
- USB 2.0 Architecture OverviewDocument51 pagesUSB 2.0 Architecture OverviewAbbas Raza ZaidiNo ratings yet
- Leica Pegasus MapFactory BRO enDocument4 pagesLeica Pegasus MapFactory BRO enpancaNo ratings yet
- Nokia E5-00 User Guide: Issue 1.5Document201 pagesNokia E5-00 User Guide: Issue 1.5kumar4itiNo ratings yet
- AssignmentPM ANSWERDocument2 pagesAssignmentPM ANSWERMikey Chua0% (1)
- Amir Rehman's CVDocument4 pagesAmir Rehman's CVAnonymous mznpYsQuNo ratings yet
- Macs3 Tanker FlyerDocument2 pagesMacs3 Tanker FlyerBaran BankoğluNo ratings yet
- Class Notes PDFDocument5 pagesClass Notes PDFAmirNo ratings yet
- Xerox® Phaser® 6510 Color Printer/ Workcentre® 6515 Color MFP Service ManualDocument801 pagesXerox® Phaser® 6510 Color Printer/ Workcentre® 6515 Color MFP Service ManualMarcelo Shimatai de MedioNo ratings yet
- MIL Q2 Module 8Document27 pagesMIL Q2 Module 8MICHAEL JIMENO100% (1)
- Data Sheet: HSMS-286x SeriesDocument18 pagesData Sheet: HSMS-286x SeriesWagner DiasNo ratings yet
- eu-LISA Single Programming Document 2017-2019 PDFDocument249 pageseu-LISA Single Programming Document 2017-2019 PDFRiikka PellinenNo ratings yet
- CD 533 Determination of Pipe and Bedding Combinations For Drainage Works-WebDocument27 pagesCD 533 Determination of Pipe and Bedding Combinations For Drainage Works-WebmichgebNo ratings yet
- CV Planning Engineer - GauravkadamDocument5 pagesCV Planning Engineer - GauravkadamNikunj PatharNo ratings yet
- 8-Channel, High Throughput, 24-Bit Sigma-Delta ADC: Data SheetDocument32 pages8-Channel, High Throughput, 24-Bit Sigma-Delta ADC: Data SheetPravin RautNo ratings yet
- Toshiba 2SK4107 DatasheetDocument6 pagesToshiba 2SK4107 DatasheetPedro PerezNo ratings yet
- Firewall Security Recommendations ChecklistsDocument2 pagesFirewall Security Recommendations Checkliststauqeer25No ratings yet
- IOT Based Pet Feeder: Test Engineering and Management March 2020Document12 pagesIOT Based Pet Feeder: Test Engineering and Management March 2020Rizyn ShresthaNo ratings yet
- Contiled: Continuous Led Line For Tunnel LightingDocument14 pagesContiled: Continuous Led Line For Tunnel Lightingionelg834549No ratings yet
- G0A21A Statistical Software10 PDFDocument9 pagesG0A21A Statistical Software10 PDFAnna ENo ratings yet
- FMP20 48Document2 pagesFMP20 48Andri MartianNo ratings yet