Professional Documents
Culture Documents
Information Technology (IT) End User Policy
Information Technology (IT) End User Policy
Uploaded by
GCIR ITCopyright:
Available Formats
You might also like
- Itnsa Pra WSMB2023Document10 pagesItnsa Pra WSMB2023hazwanNo ratings yet
- 13-PAS-ADMIN-Exercise Guide (v10.3) (New UI) PDFDocument159 pages13-PAS-ADMIN-Exercise Guide (v10.3) (New UI) PDFBryan Astudillo CabreraNo ratings yet
- Acceptable Use PolicyDocument6 pagesAcceptable Use PolicyShah KhanNo ratings yet
- Acceptable Use Policy PDFDocument7 pagesAcceptable Use Policy PDFMuhammad Shahbaz KhanNo ratings yet
- AdvisorStream Compliance GuideDocument26 pagesAdvisorStream Compliance GuideAnonymous jMDxKv8No ratings yet
- Employee Management SystemDocument68 pagesEmployee Management SystemFaiq100% (4)
- BakreidiazzaportfolioDocument389 pagesBakreidiazzaportfolioapi-111039291No ratings yet
- Sample Internet Usage PolicyDocument12 pagesSample Internet Usage Policyjorge alverezNo ratings yet
- Cybersecurity PolicyDocument6 pagesCybersecurity PolicyShuvamNo ratings yet
- It PolicyDocument4 pagesIt PolicyRoen AbeNo ratings yet
- Computer and Internet Usage PolicyDocument8 pagesComputer and Internet Usage PolicyChristopher ColuccioNo ratings yet
- Website and Computer Use Policy: Master Builders Human Resources ManualDocument2 pagesWebsite and Computer Use Policy: Master Builders Human Resources ManualJeremy CouchNo ratings yet
- Acceptable Use PolicyDocument4 pagesAcceptable Use Policyandri_puspoNo ratings yet
- Vaish Associates, AdvocatesDocument5 pagesVaish Associates, Advocatesswayamjit19llb077No ratings yet
- Computer Email and Internet UsageDocument2 pagesComputer Email and Internet UsageTonkeyYongNo ratings yet
- Information Technology PolicyDocument4 pagesInformation Technology PolicyRajendra KumarNo ratings yet
- Use of Company Equipment (Voice Mail, E-Mail, Computers, Etc.)Document3 pagesUse of Company Equipment (Voice Mail, E-Mail, Computers, Etc.)AyushiNo ratings yet
- BSBTWK502 Policy and Procedures TemplateDocument2 pagesBSBTWK502 Policy and Procedures Templatev6vdj9xc79No ratings yet
- Internet, Email and Social Media Policy PDFDocument3 pagesInternet, Email and Social Media Policy PDFRyan Alderman100% (1)
- PolicyDocument6 pagesPolicyULTIMATE MOVIESNo ratings yet
- Acceptable Use PolicyDocument7 pagesAcceptable Use PolicyHiren DhadukNo ratings yet
- Employee Internet Usage PolicyDocument3 pagesEmployee Internet Usage PolicypcykyueyzcjiumhNo ratings yet
- Ramada Limited Policy and Procedure Manual Section6 5Document2 pagesRamada Limited Policy and Procedure Manual Section6 5Usama JavedNo ratings yet
- Computer, Email and Internet UsageDocument2 pagesComputer, Email and Internet UsageAneelKhatriNo ratings yet
- Information Security Acceptable Use Policy: 1.0 OverviewDocument4 pagesInformation Security Acceptable Use Policy: 1.0 OverviewTony AbreuNo ratings yet
- Internet Acceptable Use PolicyDocument3 pagesInternet Acceptable Use PolicyFritz BoholNo ratings yet
- Data Security PolicyDocument4 pagesData Security PolicySudhakar RNo ratings yet
- IT Security Policy Template Acceptable Use Policy OSIBeyondDocument7 pagesIT Security Policy Template Acceptable Use Policy OSIBeyondSanda NechiforNo ratings yet
- Internet, E-Mail, and Computer Usage PolicyDocument4 pagesInternet, E-Mail, and Computer Usage PolicyNelson ChegeNo ratings yet
- Use of Internet & EmailDocument5 pagesUse of Internet & EmailNitiNo ratings yet
- Technology Ressources Use Policy: Policy Restricting Personal Use of Employer's Computers and SystemsDocument6 pagesTechnology Ressources Use Policy: Policy Restricting Personal Use of Employer's Computers and Systemshai phamNo ratings yet
- Internet PolicyDocument4 pagesInternet PolicyRocketLawyerNo ratings yet
- Internet and Email Access PolicyDocument6 pagesInternet and Email Access PolicyMohammad Shahban HashmiNo ratings yet
- Computer Email and Internet Usage PolicyDocument3 pagesComputer Email and Internet Usage PolicyJames LemaNo ratings yet
- Computer and Technology Resource Usage Policy of Al Qamra GroupDocument3 pagesComputer and Technology Resource Usage Policy of Al Qamra GroupManhar MohammedNo ratings yet
- Internet & Software Use PolicyDocument5 pagesInternet & Software Use Policyapi-281092679No ratings yet
- Sample Workplace Internet & Email Usage Policy TemplateDocument1 pageSample Workplace Internet & Email Usage Policy TemplateBrendan RolfeNo ratings yet
- A8.1 Acceptable Use Policy v1Document7 pagesA8.1 Acceptable Use Policy v1Rharif AnassNo ratings yet
- Leicester Medical Support: Internet, Email and Social Media Usage IT - and - Social - Media - Policy - v1Document5 pagesLeicester Medical Support: Internet, Email and Social Media Usage IT - and - Social - Media - Policy - v1stephanieNo ratings yet
- Employee Internet Usage PolicyDocument3 pagesEmployee Internet Usage PolicyAasif MajeedNo ratings yet
- Mobile Phone Internet Usage PolicyDocument5 pagesMobile Phone Internet Usage PolicycxvcxvNo ratings yet
- Assignement # 2 Analyze & Design Security PolicesDocument10 pagesAssignement # 2 Analyze & Design Security PolicesephertNo ratings yet
- Creating Your Acceptable Use PolicyDocument4 pagesCreating Your Acceptable Use PolicyBruno GuimarãesNo ratings yet
- Internet Security PolicyDocument2 pagesInternet Security PolicyIbrahim qashtaNo ratings yet
- 16 07 04 - IT Security Policy - Version 1 - NOVODocument9 pages16 07 04 - IT Security Policy - Version 1 - NOVObmdolivNo ratings yet
- Acceptable Use of Assets PolicyDocument4 pagesAcceptable Use of Assets PolicySomnath Kadavergu100% (1)
- Information Security PolicyDocument7 pagesInformation Security PolicyAdaa JarsoNo ratings yet
- Internet Usage Policy FormDocument1 pageInternet Usage Policy FormShashank RaiNo ratings yet
- Acceptable Use Policy For Contractors and Subcontractors: PurposeDocument6 pagesAcceptable Use Policy For Contractors and Subcontractors: PurposeДенис КлебановичNo ratings yet
- Cyber Security PolicyDocument5 pagesCyber Security PolicyPanganayi JamesNo ratings yet
- Internet Usage PolicyDocument8 pagesInternet Usage PolicyRaven ShieldNo ratings yet
- SAMPLE COMPUTER USE POLICY: Policy Restricting Personal Use of Employer's ComputerDocument5 pagesSAMPLE COMPUTER USE POLICY: Policy Restricting Personal Use of Employer's ComputerSaad Al-Subaie100% (1)
- Internet Security Policy: PurposeDocument2 pagesInternet Security Policy: PurposeEXTECH CERTIFICATIONSNo ratings yet
- 4.2 Acceptable Usage PolicyDocument4 pages4.2 Acceptable Usage PolicyVamsi KrishnaNo ratings yet
- Acceptable Use PolicyDocument6 pagesAcceptable Use PolicyKaiNo ratings yet
- Internet Email Usage PolicyDocument4 pagesInternet Email Usage PolicySrikesh GSNo ratings yet
- Computer Use PolicyDocument9 pagesComputer Use Policychristian_mark819No ratings yet
- Internet Usage PolicyDocument9 pagesInternet Usage PolicyWaqas HafeezNo ratings yet
- Acceptable Use Policy: 1. OverviewDocument7 pagesAcceptable Use Policy: 1. OverviewRichter BelmontNo ratings yet
- Acceptable Use PolicyDocument7 pagesAcceptable Use PolicyRichter BelmontNo ratings yet
- TUP - North America (v4.8) (2) - 1Document3 pagesTUP - North America (v4.8) (2) - 1Alessandra TorresNo ratings yet
- Deve Letech Acceptable Use PolicyDocument3 pagesDeve Letech Acceptable Use PolicyEdison ZapataNo ratings yet
- Handout For App - ByOD Acceptable Use Policy TemplateDocument6 pagesHandout For App - ByOD Acceptable Use Policy TemplateVikas KumarNo ratings yet
- Srs E-Market WebsiteDocument13 pagesSrs E-Market WebsitePratik HepatNo ratings yet
- ×IBM Maximo 6.2 Finance Manager GuideDocument127 pages×IBM Maximo 6.2 Finance Manager GuideEric WooNo ratings yet
- COB20 - Online Note SharingDocument24 pagesCOB20 - Online Note SharingVenu RachanNo ratings yet
- Train CacsDocument10 pagesTrain Cacsapi-93198487No ratings yet
- Sis System IeeeDocument10 pagesSis System IeeeAbhijeet PradhanNo ratings yet
- Student Elearning User ManualDocument12 pagesStudent Elearning User ManualDavid NwankwereNo ratings yet
- Car Service Management System: Aim:-Develop The Software Requirements Specifications (SRS)Document8 pagesCar Service Management System: Aim:-Develop The Software Requirements Specifications (SRS)dd100% (1)
- 08-PAM-ADMIN Privileged Access WorkflowsDocument38 pages08-PAM-ADMIN Privileged Access WorkflowsyaohangNo ratings yet
- VRD SRSDocument10 pagesVRD SRSSiddartha KethireddyNo ratings yet
- Manual Supervisor - Elastix CallCenterPRO - EN PDFDocument74 pagesManual Supervisor - Elastix CallCenterPRO - EN PDF4NET VZLANo ratings yet
- Hrms OnlineDocument536 pagesHrms OnlineTesfaye YenealemNo ratings yet
- Security GuideDocument95 pagesSecurity GuideAdel AhmedNo ratings yet
- Isam 0212Document75 pagesIsam 0212gamurphy65No ratings yet
- Hat Is Human-Centric Computing?: ISRC Future Technology Topic BriefDocument5 pagesHat Is Human-Centric Computing?: ISRC Future Technology Topic BriefKavithaDNo ratings yet
- Setting Up Implementation Users and SFTP For Oracle Fusion Release 9Document46 pagesSetting Up Implementation Users and SFTP For Oracle Fusion Release 9vivek_khoslaNo ratings yet
- CyberArk Enterprise Password Vault 4-28-2014 enDocument2 pagesCyberArk Enterprise Password Vault 4-28-2014 enRitu RajNo ratings yet
- TPAM 2.5.916 ReleaseNotesDocument13 pagesTPAM 2.5.916 ReleaseNotesLakshmi Narayanan AmarnathNo ratings yet
- ULIP VOCPT Integration RequirementDocument24 pagesULIP VOCPT Integration RequirementGokulganth ThirumalNo ratings yet
- EN SFD-Manual For UMB PDFDocument16 pagesEN SFD-Manual For UMB PDFTonyNo ratings yet
- E - CampusDocument38 pagesE - CampusZainab AafiaNo ratings yet
- Manual FinalDocument60 pagesManual FinalSeetha LaxmiNo ratings yet
- Remote Desktop Manager Piri 000622Document6 pagesRemote Desktop Manager Piri 000622Farhad PiriNo ratings yet
- Pri Dlbt1617693enDocument7 pagesPri Dlbt1617693enC-TecNo ratings yet
- Graphical Password Authentication SystemDocument32 pagesGraphical Password Authentication SystemNishan Kumar100% (1)
- GL Profile OptionsDocument11 pagesGL Profile Optionssurendra008No ratings yet
Information Technology (IT) End User Policy
Information Technology (IT) End User Policy
Uploaded by
GCIR ITOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
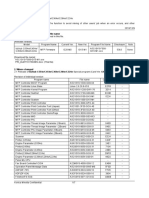
Information Technology (IT) End User Policy
Information Technology (IT) End User Policy
Uploaded by
GCIR ITCopyright:
Available Formats
Information Technology (IT) End User Policy
Statement from Executive Management Team
GCIR has a long and proud tradition of conducting business in accordance with the highest ethical
standards and in full compliance with all applicable laws. The Information Technology (IT) End User
Policy was developed at the direction of Axiomatic Executive Management to provide clear guidance to
all Axiomatic employees and to ensure a consistent approach to business practices throughout
Axiomatic expanding operations.
Axiomatic Executive Management is fully committed to conduct business with the highest level of
integrity and we expect your strict adherence to the Information Technology (IT) End User Policy and
the law. There will be zero tolerance of non-compliance and any violations will result in swift corrective
action, including possible termination of employment from Axiomatic Consultants.
Thank you for your commitment to comply unequivocally with the highest standards of integrity and
business ethics.
Purpose for this Policy
To effectively manage and safeguard the use of all IT equipment, data, infrastructure and facilities by
GCIR IT users and Representatives.
Statement of Responsibilities
The Company employees may access the Internet and/or email through the Company’s network for
conducting Company business. Creating, viewing, copying, storing or sending content outside of the
scope of the Company employment is prohibited. The Company provides Internet and e- mail access to
all of the employees as a privilege that is based on adherence to the Company’s policies and rules
regarding Internet and/or e-mail access. In addition to being responsible to abide by the conditions as
set out in, but not limited to this end-user policy, an employee who uses the Internet and/or e-mail shall:
• Ensure that no communication interfere with the employees productivity;
• Be responsible for the content of all text, data, audio, video or images that the employee creates,
place on or send over the Internet and/or e-mail.
• Not transmit copyrighted materials without permission of the author thereof, and without defining
and acknowledging the owner thereof.
• Avoid, where possible, transmission of information confidential to the Company or any of its
clients/representatives. If it is absolutely necessary to transmit confidential information,
employees are required to ensure that information is delivered to the proper intended recipient
and any attached information should be password protected.
Internet and E-Mail Usage
Access to the internet is provided to employees for the benefit of the Company and its business.
Employees using the Internet, including e-mail, are representing the Company. Employees are
responsible for ensuring that the Internet is used in an efficient, ethical and lawful manner. The
following indicate examples of acceptable use:
• Utilizing the Internet, including e-mail, as a tool to advance the business objectives of the
Company.
Employees and/or other Company Representatives may not use the Internet or e-mail for purposes that
are illegal, unethical, harmful, or contrary to the Company’s interests. The following examples indicate
unacceptable use:
• Creating, viewing, accessing, intercepting, retaining, copying, processing or transmitting any
content or material that is offensive, harassing, fraudulent, illegal or obscene including any
pornography, hate mail, racist remarks or hoaxes to any company employee, client or any other
individual or entity whether a Company Representative or not.
• Sending or receiving large non-business related e-mails – acceptable size is MB or less.
• Misrepresenting personal opinions as that of the Company via e-mail, or publication of
unauthorized statements onto web sites, bulletin boards, forums, discussions areas.
• Using a third party e-mail provider, i.e. “Hotmail”, “Yahoo mail”, “Free mail”, “Gmail” or any other
e-mail service provided by any outside Internet Service Provider or party, to send Company
information or any files emanating from within the Company to external recipients. This
INCLUDES any Company work or Data forwarded to personal e-mail addresses for working at
home, unless explicitly approved by the Company.
• Providing computing or storage resources, including file sharing or swapping, to external parties
through parties such as “Napster” and “Gnutella”, or any other torrent networks.
• Breaking through or even attempting to break through security controls, whether on the
Company’s official equipment, personal Laptop or on any other computer system connected to
the/a Company network;
• Intentionally or recklessly accessing or transmitting computer viruses and similar software;
• Forwarding internal e-mail distribution lists to outside agencies and organisations;
• Political lobbying of any kind;
• Downloading games, programs, shareware or freeware or data not intended for Company use.
• Any activities which could cause congestion and disruption of networks and systems;
• All e-mails are retained on a central server and will be backed up automatically subject to
Company policy.
• Private email addresses must be used, outside business hours, outside the Company network, to
register with online social networking services such as Facebook, MySpace, Bebo or Friendster,
etc.
Senior Management, reserves the right to recommend the following remedies, in case of any breach of
policy, involving use of the Company’s network/systems/data:
• Immediately and without notice withdraw and revoke temporarily/permanently the employee’s
access to any/all computer systems and communication services, including e-mail, if it is found
that an employee is using e-mail in breach of this document, subject to disciplinary action, in line
with the Company’s disciplinary procedures as governed regarding Personnel, in addition to being
required to pay any appropriate part of costs and/or damages incurred.
Senior Management may recommend the following response to violations of usage policies by any
combination of:
• Informal warning;
• Disciplinary action, potentially for gross misconduct, through the normal disciplinary process;
• Provision of information to the police and law authorities, for possible criminal proceedings.
Copyrights and Downloads
Employees using the Internet are not permitted to illegally and/or wrongfully copy, transfer, rename,
add, modify or delete protected works, information or programs. Employee are responsible for
observing copyright and licensing agreements that may apply when downloading or distributing files,
documents and software. Any copyrighted martial attached to a message should identify the author and
acknowledge his/her copyright.
Monitoring and Privacy
All messages created, sent or retrieved over the Internet and e-mail are the property of the Company
and may be regarded as public information and the Company reserves the right to intercept, retain,
read and inspect the same if the Company believes, in its sole judgment, that it is justified to so in order
to protect its business. Should any private information of the employee be contained in such message,
the Company agrees to honor such privacy, it being recorded that any messages which may be personal
by nature may be accessed and used by the Company where such message may cause harm to the
Company and has the potential of causing harm and where the nature or content of the message is or is
suspect to be contrary to this policy, or is otherwise unlawful.
All communications, including text, video or audio clips and images, can be disclosed to law
enforcement authorities, or other third parties without prior consent of the sender or the receiver.
Computer Viruses
The following responsibilities to computer viruses prevention rest with each of the company’s
employees:
• Employees shall not knowingly introduce a computer virus into Company computers;
• Employees will not make use of any USB devices;
• Any employee who suspects that his/her workstation has been infected by a virus shall
immediately power off the workstation and notify their Manager to take corrective action.
User Accounts and Passwords
The confidentiality and integrity of data stored on Company computers systems must be protected by
access controls to ensure that only authorized employees have access. The access shall be restricted
to only those capabilities that are appropriate to each employee’s job duties.
In addition employees shall access the Internet in a manner that does not compromise the Company’s
network security. This includes the employees keeping his/her username and password secure,
prohibiting access to intruders or viruses, and reporting any suspicious activity to their Manager.
Employees that want to download Internet content from a non-Company source must observe
Company security procedures.
Password Policy
Passwords should be complex and must have minimum length of 8 alphanumeric and special
characters.
Passwords must be changed every 90 days.
If the security of a password is in doubt, the password must be changed immediately;
• Computing devices must not be left unattended without logging of the device or enabling a
password protected screensaver.
Employee responsibilities
Each employee:
• Shall be responsible for all computer transactions that are made with his/her User ID (username)
and password.
• Shall not disclose password to others. Passwords must be changed immediately if it is suspected
that it may have become known to others.
• Should log out when leaving a workstation unmanned, or for an extended period.
Data Storage
The employee will exclusively store Axiomatic Consultants related information on his/her system as well
as on network servers to ensure appropriate security protection and backup.
An Audit may be conducted at any time and without notice to ensure compliance with the agreement.
Cybersecurity General Conditions
1) Users must not write down, electronically store, or disclose any
password or authentication code that is used to access Company’s
Assets.
2) Users must not save credentials on browsers.
Conditions for communicating with Aramco.
1) Users must use company’s Email ID for establishing communication
with Aramco. Use of personal email is strictly prohibited.
2) Disclosing Saudi Aramco policies, procedures and standards or any
type of data with unauthorized entities or on the Internet is strictly
prohibited.
Software Copyright and License Agreements
All software acquired for or on behalf of the Company or developed by Company
employees/representatives or contract personnel on behalf of the Company shall be deemed Company
property. All such software must be used in compliance with applicable licenses, notices, contracts and
agreements.
Non-compliance with legislation dealing with intellectual property, including copyrights, such as the
Copyright Act and with license agreements can expose the Company and the responsible
employee(s)/representatives to civil and/or criminal liability. Unless otherwise provided in the applicable
license, notice, contract or agreement any duplication of copyrighted software, except for backup and
archival purposes, may be violation of law.
This policy applies to all software that is owned by the Company, licensed to the Company, rented to
the Company including SaaS (Software as a Service) or developed using the Company’s resources by
employees/representatives.
Home and Mobile Use
Employees should take care when traveling, especially in aircraft, buses and any other mass transport,
that external parties cannot read information off computer screens and tablets. Employees should
therefore exercise the necessary care when working on Company related information in public
or non-Company areas.
In the event of an iPad, tablet, workstation or laptop being stolen, this should be reported immediately
to your Manager, to arrange for all security access to be suspended.
You might also like
- Itnsa Pra WSMB2023Document10 pagesItnsa Pra WSMB2023hazwanNo ratings yet
- 13-PAS-ADMIN-Exercise Guide (v10.3) (New UI) PDFDocument159 pages13-PAS-ADMIN-Exercise Guide (v10.3) (New UI) PDFBryan Astudillo CabreraNo ratings yet
- Acceptable Use PolicyDocument6 pagesAcceptable Use PolicyShah KhanNo ratings yet
- Acceptable Use Policy PDFDocument7 pagesAcceptable Use Policy PDFMuhammad Shahbaz KhanNo ratings yet
- AdvisorStream Compliance GuideDocument26 pagesAdvisorStream Compliance GuideAnonymous jMDxKv8No ratings yet
- Employee Management SystemDocument68 pagesEmployee Management SystemFaiq100% (4)
- BakreidiazzaportfolioDocument389 pagesBakreidiazzaportfolioapi-111039291No ratings yet
- Sample Internet Usage PolicyDocument12 pagesSample Internet Usage Policyjorge alverezNo ratings yet
- Cybersecurity PolicyDocument6 pagesCybersecurity PolicyShuvamNo ratings yet
- It PolicyDocument4 pagesIt PolicyRoen AbeNo ratings yet
- Computer and Internet Usage PolicyDocument8 pagesComputer and Internet Usage PolicyChristopher ColuccioNo ratings yet
- Website and Computer Use Policy: Master Builders Human Resources ManualDocument2 pagesWebsite and Computer Use Policy: Master Builders Human Resources ManualJeremy CouchNo ratings yet
- Acceptable Use PolicyDocument4 pagesAcceptable Use Policyandri_puspoNo ratings yet
- Vaish Associates, AdvocatesDocument5 pagesVaish Associates, Advocatesswayamjit19llb077No ratings yet
- Computer Email and Internet UsageDocument2 pagesComputer Email and Internet UsageTonkeyYongNo ratings yet
- Information Technology PolicyDocument4 pagesInformation Technology PolicyRajendra KumarNo ratings yet
- Use of Company Equipment (Voice Mail, E-Mail, Computers, Etc.)Document3 pagesUse of Company Equipment (Voice Mail, E-Mail, Computers, Etc.)AyushiNo ratings yet
- BSBTWK502 Policy and Procedures TemplateDocument2 pagesBSBTWK502 Policy and Procedures Templatev6vdj9xc79No ratings yet
- Internet, Email and Social Media Policy PDFDocument3 pagesInternet, Email and Social Media Policy PDFRyan Alderman100% (1)
- PolicyDocument6 pagesPolicyULTIMATE MOVIESNo ratings yet
- Acceptable Use PolicyDocument7 pagesAcceptable Use PolicyHiren DhadukNo ratings yet
- Employee Internet Usage PolicyDocument3 pagesEmployee Internet Usage PolicypcykyueyzcjiumhNo ratings yet
- Ramada Limited Policy and Procedure Manual Section6 5Document2 pagesRamada Limited Policy and Procedure Manual Section6 5Usama JavedNo ratings yet
- Computer, Email and Internet UsageDocument2 pagesComputer, Email and Internet UsageAneelKhatriNo ratings yet
- Information Security Acceptable Use Policy: 1.0 OverviewDocument4 pagesInformation Security Acceptable Use Policy: 1.0 OverviewTony AbreuNo ratings yet
- Internet Acceptable Use PolicyDocument3 pagesInternet Acceptable Use PolicyFritz BoholNo ratings yet
- Data Security PolicyDocument4 pagesData Security PolicySudhakar RNo ratings yet
- IT Security Policy Template Acceptable Use Policy OSIBeyondDocument7 pagesIT Security Policy Template Acceptable Use Policy OSIBeyondSanda NechiforNo ratings yet
- Internet, E-Mail, and Computer Usage PolicyDocument4 pagesInternet, E-Mail, and Computer Usage PolicyNelson ChegeNo ratings yet
- Use of Internet & EmailDocument5 pagesUse of Internet & EmailNitiNo ratings yet
- Technology Ressources Use Policy: Policy Restricting Personal Use of Employer's Computers and SystemsDocument6 pagesTechnology Ressources Use Policy: Policy Restricting Personal Use of Employer's Computers and Systemshai phamNo ratings yet
- Internet PolicyDocument4 pagesInternet PolicyRocketLawyerNo ratings yet
- Internet and Email Access PolicyDocument6 pagesInternet and Email Access PolicyMohammad Shahban HashmiNo ratings yet
- Computer Email and Internet Usage PolicyDocument3 pagesComputer Email and Internet Usage PolicyJames LemaNo ratings yet
- Computer and Technology Resource Usage Policy of Al Qamra GroupDocument3 pagesComputer and Technology Resource Usage Policy of Al Qamra GroupManhar MohammedNo ratings yet
- Internet & Software Use PolicyDocument5 pagesInternet & Software Use Policyapi-281092679No ratings yet
- Sample Workplace Internet & Email Usage Policy TemplateDocument1 pageSample Workplace Internet & Email Usage Policy TemplateBrendan RolfeNo ratings yet
- A8.1 Acceptable Use Policy v1Document7 pagesA8.1 Acceptable Use Policy v1Rharif AnassNo ratings yet
- Leicester Medical Support: Internet, Email and Social Media Usage IT - and - Social - Media - Policy - v1Document5 pagesLeicester Medical Support: Internet, Email and Social Media Usage IT - and - Social - Media - Policy - v1stephanieNo ratings yet
- Employee Internet Usage PolicyDocument3 pagesEmployee Internet Usage PolicyAasif MajeedNo ratings yet
- Mobile Phone Internet Usage PolicyDocument5 pagesMobile Phone Internet Usage PolicycxvcxvNo ratings yet
- Assignement # 2 Analyze & Design Security PolicesDocument10 pagesAssignement # 2 Analyze & Design Security PolicesephertNo ratings yet
- Creating Your Acceptable Use PolicyDocument4 pagesCreating Your Acceptable Use PolicyBruno GuimarãesNo ratings yet
- Internet Security PolicyDocument2 pagesInternet Security PolicyIbrahim qashtaNo ratings yet
- 16 07 04 - IT Security Policy - Version 1 - NOVODocument9 pages16 07 04 - IT Security Policy - Version 1 - NOVObmdolivNo ratings yet
- Acceptable Use of Assets PolicyDocument4 pagesAcceptable Use of Assets PolicySomnath Kadavergu100% (1)
- Information Security PolicyDocument7 pagesInformation Security PolicyAdaa JarsoNo ratings yet
- Internet Usage Policy FormDocument1 pageInternet Usage Policy FormShashank RaiNo ratings yet
- Acceptable Use Policy For Contractors and Subcontractors: PurposeDocument6 pagesAcceptable Use Policy For Contractors and Subcontractors: PurposeДенис КлебановичNo ratings yet
- Cyber Security PolicyDocument5 pagesCyber Security PolicyPanganayi JamesNo ratings yet
- Internet Usage PolicyDocument8 pagesInternet Usage PolicyRaven ShieldNo ratings yet
- SAMPLE COMPUTER USE POLICY: Policy Restricting Personal Use of Employer's ComputerDocument5 pagesSAMPLE COMPUTER USE POLICY: Policy Restricting Personal Use of Employer's ComputerSaad Al-Subaie100% (1)
- Internet Security Policy: PurposeDocument2 pagesInternet Security Policy: PurposeEXTECH CERTIFICATIONSNo ratings yet
- 4.2 Acceptable Usage PolicyDocument4 pages4.2 Acceptable Usage PolicyVamsi KrishnaNo ratings yet
- Acceptable Use PolicyDocument6 pagesAcceptable Use PolicyKaiNo ratings yet
- Internet Email Usage PolicyDocument4 pagesInternet Email Usage PolicySrikesh GSNo ratings yet
- Computer Use PolicyDocument9 pagesComputer Use Policychristian_mark819No ratings yet
- Internet Usage PolicyDocument9 pagesInternet Usage PolicyWaqas HafeezNo ratings yet
- Acceptable Use Policy: 1. OverviewDocument7 pagesAcceptable Use Policy: 1. OverviewRichter BelmontNo ratings yet
- Acceptable Use PolicyDocument7 pagesAcceptable Use PolicyRichter BelmontNo ratings yet
- TUP - North America (v4.8) (2) - 1Document3 pagesTUP - North America (v4.8) (2) - 1Alessandra TorresNo ratings yet
- Deve Letech Acceptable Use PolicyDocument3 pagesDeve Letech Acceptable Use PolicyEdison ZapataNo ratings yet
- Handout For App - ByOD Acceptable Use Policy TemplateDocument6 pagesHandout For App - ByOD Acceptable Use Policy TemplateVikas KumarNo ratings yet
- Srs E-Market WebsiteDocument13 pagesSrs E-Market WebsitePratik HepatNo ratings yet
- ×IBM Maximo 6.2 Finance Manager GuideDocument127 pages×IBM Maximo 6.2 Finance Manager GuideEric WooNo ratings yet
- COB20 - Online Note SharingDocument24 pagesCOB20 - Online Note SharingVenu RachanNo ratings yet
- Train CacsDocument10 pagesTrain Cacsapi-93198487No ratings yet
- Sis System IeeeDocument10 pagesSis System IeeeAbhijeet PradhanNo ratings yet
- Student Elearning User ManualDocument12 pagesStudent Elearning User ManualDavid NwankwereNo ratings yet
- Car Service Management System: Aim:-Develop The Software Requirements Specifications (SRS)Document8 pagesCar Service Management System: Aim:-Develop The Software Requirements Specifications (SRS)dd100% (1)
- 08-PAM-ADMIN Privileged Access WorkflowsDocument38 pages08-PAM-ADMIN Privileged Access WorkflowsyaohangNo ratings yet
- VRD SRSDocument10 pagesVRD SRSSiddartha KethireddyNo ratings yet
- Manual Supervisor - Elastix CallCenterPRO - EN PDFDocument74 pagesManual Supervisor - Elastix CallCenterPRO - EN PDF4NET VZLANo ratings yet
- Hrms OnlineDocument536 pagesHrms OnlineTesfaye YenealemNo ratings yet
- Security GuideDocument95 pagesSecurity GuideAdel AhmedNo ratings yet
- Isam 0212Document75 pagesIsam 0212gamurphy65No ratings yet
- Hat Is Human-Centric Computing?: ISRC Future Technology Topic BriefDocument5 pagesHat Is Human-Centric Computing?: ISRC Future Technology Topic BriefKavithaDNo ratings yet
- Setting Up Implementation Users and SFTP For Oracle Fusion Release 9Document46 pagesSetting Up Implementation Users and SFTP For Oracle Fusion Release 9vivek_khoslaNo ratings yet
- CyberArk Enterprise Password Vault 4-28-2014 enDocument2 pagesCyberArk Enterprise Password Vault 4-28-2014 enRitu RajNo ratings yet
- TPAM 2.5.916 ReleaseNotesDocument13 pagesTPAM 2.5.916 ReleaseNotesLakshmi Narayanan AmarnathNo ratings yet
- ULIP VOCPT Integration RequirementDocument24 pagesULIP VOCPT Integration RequirementGokulganth ThirumalNo ratings yet
- EN SFD-Manual For UMB PDFDocument16 pagesEN SFD-Manual For UMB PDFTonyNo ratings yet
- E - CampusDocument38 pagesE - CampusZainab AafiaNo ratings yet
- Manual FinalDocument60 pagesManual FinalSeetha LaxmiNo ratings yet
- Remote Desktop Manager Piri 000622Document6 pagesRemote Desktop Manager Piri 000622Farhad PiriNo ratings yet
- Pri Dlbt1617693enDocument7 pagesPri Dlbt1617693enC-TecNo ratings yet
- Graphical Password Authentication SystemDocument32 pagesGraphical Password Authentication SystemNishan Kumar100% (1)
- GL Profile OptionsDocument11 pagesGL Profile Optionssurendra008No ratings yet