Professional Documents
Culture Documents
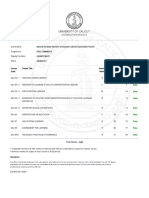
1.1 Vulnerability Assessment vs. Penetration Testing
1.1 Vulnerability Assessment vs. Penetration Testing
Uploaded by
Felix OdhiamboOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
1.1 Vulnerability Assessment vs. Penetration Testing
1.1 Vulnerability Assessment vs. Penetration Testing
Uploaded by
Felix OdhiamboCopyright:
Available Formats
1.1 Vulnerability Assessment vs.
Penetration Testing
Corporations and individuals need to understand how the damage is being done so they
understand how to stop it.
Corporations also need to understand the extent of the threat that a vulnerability
represents.
The vast amount of functionality that is provided by an organization’s networking,
database, and desktop software can be used against them.
Within each and every organization, there is the all-too-familiar battle of functionality vs.
security.
This is the reason that, in most environments, the security officer is not the most well-
liked individual in the company.
o Security officers are in charge of ensuring the overall security of the environment,
which usually means reducing or shutting off many functionalities that users love.
o They are responsible for the balance between functionality and security within the
company, and it is a hard job.
The ethical hacker’s job is to find these things running on systems and networks, and he
needs to have the skill set to know how an enemy would use these things against the
organization.
This work is referred to as a penetration test, which is different from a vulnerability
assessment.
1.1.1 Vulnerability Assessment
A vulnerability assessment is usually carried out by a network scanner on steroids.
Some type of automated scanning product is used to probe the ports and services on a
range of IP addresses.
Most of these products can also test for the type of operating system and application
software running and the versions, patch levels, user accounts, and services that are also
running.
These findings are matched up with correlating vulnerabilities in the product’s database.
The end result is a large pile of reports that provides a list of each system’s vulnerabilities
and corresponding countermeasures to mitigate the associated risks.
Basically, the tool states,
o “Here is a list of your vulnerabilities and here is a list of things you need to do
to fix them.”
The problem with just depending upon this large pile of printouts is that it was generated
by an automated tool that has a hard time putting its findings into the proper context of
the given environment.
For example,
o Several of these tools provide an alert of “High” for vulnerabilities that do not
have a highly probable threat associated with them.
o The tools also cannot understand how a small, seemingly insignificant,
vulnerability can be used in a large orchestrated attack.
Vulnerability assessments are great for identifying the foundational security issues within
an environment, but many times, it takes an ethical hacker to really test and qualify the
level of risk specific vulnerabilities pose.
You might also like
- Vulnerability Management TrainingDocument10 pagesVulnerability Management TrainingdedcecdNo ratings yet
- Threat Modeling Checklist and RequirementDocument17 pagesThreat Modeling Checklist and Requirementdas100% (4)
- Complete Denture ManualDocument23 pagesComplete Denture ManualCitra PurnamasariNo ratings yet
- Topic 3.1 Programming MethodologyDocument5 pagesTopic 3.1 Programming MethodologySiena Duerme GutierrezNo ratings yet
- Analysis of Incident Response Tactics For The Extreme Insecure WebsiteDocument18 pagesAnalysis of Incident Response Tactics For The Extreme Insecure WebsiteAmandaNo ratings yet
- Vulnerability IntelligenceDocument22 pagesVulnerability IntelligenceelwoodkkkNo ratings yet
- Computer Virus Thesis StatementDocument7 pagesComputer Virus Thesis StatementCustomWritingPapersUK100% (2)
- Vulnerability Management Tools Buyersguide Part1Document14 pagesVulnerability Management Tools Buyersguide Part1Luis BarretoNo ratings yet
- VAPTDocument4 pagesVAPTPramod JadhavNo ratings yet
- Unit 2 Security and EncryptionDocument36 pagesUnit 2 Security and Encryptionmaumita100% (1)
- Practitioners Guide SOCDocument10 pagesPractitioners Guide SOChz100% (1)
- 3.impediments o SecurityDocument16 pages3.impediments o SecurityTakudzwa MusaririNo ratings yet
- INTEGRATIVE PROGRAMMING - W14 Software Security PracticesDocument8 pagesINTEGRATIVE PROGRAMMING - W14 Software Security Practicestakenusername0010No ratings yet
- Pentester and Network Security For A Secure Modern SocietyDocument8 pagesPentester and Network Security For A Secure Modern SocietyOfrates SiringanNo ratings yet
- IT Security and Safety: BriefingDocument7 pagesIT Security and Safety: Briefingمحمد سمورNo ratings yet
- What Is System Vulnerability?: Default PermitDocument6 pagesWhat Is System Vulnerability?: Default Permitapi-26370766No ratings yet
- Security+ Lab AnswersDocument160 pagesSecurity+ Lab Answersdeepholm0% (1)
- General Approach To Security TestingDocument11 pagesGeneral Approach To Security TestingKarthik BsNo ratings yet
- Practitioners Guide SOCDocument24 pagesPractitioners Guide SOCgerenciaitgpoalsavisionNo ratings yet
- Can Vendors Ever Provide Secure Solutions? (HITB 2015) Version 2 2Document27 pagesCan Vendors Ever Provide Secure Solutions? (HITB 2015) Version 2 2BarryRaveendranGreeneNo ratings yet
- Security in ComputingDocument62 pagesSecurity in Computingakilrsdi100% (1)
- The Goals of Penetration TestingDocument7 pagesThe Goals of Penetration TestingAnteGrNo ratings yet
- An Approach To Vulnerability Management: by Umesh Chavan, CISSPDocument3 pagesAn Approach To Vulnerability Management: by Umesh Chavan, CISSPRaju PatleNo ratings yet
- Beginner's Guide To: Threat IntelligenceDocument17 pagesBeginner's Guide To: Threat IntelligenceVivek R KoushikNo ratings yet
- How To Perform An IT Cyber Security Risk Assessment 1595802501Document11 pagesHow To Perform An IT Cyber Security Risk Assessment 1595802501Florick Le MahamatNo ratings yet
- Malicious Software: Essay 4Document15 pagesMalicious Software: Essay 4Anjan KrishnamurthyNo ratings yet
- Cyber Security Risk Assessment - Step-by-Step GuideDocument9 pagesCyber Security Risk Assessment - Step-by-Step GuideviandsNo ratings yet
- Internet Security, Vulnerability Disclosure, and Software ProvisionDocument19 pagesInternet Security, Vulnerability Disclosure, and Software Provisionluis demetrio martinez ruizNo ratings yet
- Prof - Senthil Kumar.K: Under The Guidance ofDocument15 pagesProf - Senthil Kumar.K: Under The Guidance ofSuba LakshmiNo ratings yet
- Vulnerability ManagementDocument6 pagesVulnerability ManagementAzeddien SllameNo ratings yet
- Vulnerability Management - Cyber SecurityDocument42 pagesVulnerability Management - Cyber SecurityVasundhara INo ratings yet
- Research PlanDocument6 pagesResearch PlanPrince OpokuNo ratings yet
- Proactive and Reactive ConceptDocument4 pagesProactive and Reactive ConceptSaied HasanNo ratings yet
- Testing Chapter 1Document3 pagesTesting Chapter 1kelceye2earchiveuploaderNo ratings yet
- Final PrintDocument117 pagesFinal PrintChandan SrivastavaNo ratings yet
- Penetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsFrom EverandPenetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsNo ratings yet
- Lesson 6 - Reading Material - PDF EditedDocument4 pagesLesson 6 - Reading Material - PDF EditedEmillie Kristine SalorNo ratings yet
- Bsi10 Ops PDFDocument5 pagesBsi10 Ops PDFTrong Thua HuynhNo ratings yet
- Information Security and Cyber Security White Paper Michael Lassiter JRDocument12 pagesInformation Security and Cyber Security White Paper Michael Lassiter JRDiana SmithNo ratings yet
- Security Analysis, Assessment, and Assurance JAGCDocument37 pagesSecurity Analysis, Assessment, and Assurance JAGCJaimeAnatoliGonzalesCaceresNo ratings yet
- Kali Linux Web Penetration Testing Cookbook - Sample ChapterDocument31 pagesKali Linux Web Penetration Testing Cookbook - Sample ChapterPackt Publishing100% (3)
- Malware Reverse EngineeringDocument10 pagesMalware Reverse EngineeringShahriar MahmudNo ratings yet
- Security Testing ArticlesDocument7 pagesSecurity Testing ArticlesVara PrasadNo ratings yet
- Malware Analysis GuideDocument19 pagesMalware Analysis GuideanyfantidisNo ratings yet
- Malware Analysis GuideDocument19 pagesMalware Analysis GuideMuhammad Abdul WaheedNo ratings yet
- ALS Security+ Lab01Document10 pagesALS Security+ Lab01Mishel JiménezNo ratings yet
- Data Security (Viruses and Crime) : Nt213 - Engleski Za InformatičareDocument35 pagesData Security (Viruses and Crime) : Nt213 - Engleski Za InformatičareTNo ratings yet
- White Paper: Building An Application Vulnerability Management ProgramDocument32 pagesWhite Paper: Building An Application Vulnerability Management Programhai TrầnNo ratings yet
- Vulnerability ScanningDocument12 pagesVulnerability ScanningSonuNo ratings yet
- Zero Day AttackDocument6 pagesZero Day AttackWerda FarooqNo ratings yet
- N .WhitepaperDocument19 pagesN .Whitepaperrotedi4150No ratings yet
- Chapter 2 - Attacks, Concepts and TechniquesDocument21 pagesChapter 2 - Attacks, Concepts and TechniquesS. M. AkashNo ratings yet
- Response Itsec2 Ex1 MalwareDocument7 pagesResponse Itsec2 Ex1 Malwaretanmaya1991No ratings yet
- Risk Triage For Security Vulnerability AnnouncementsDocument7 pagesRisk Triage For Security Vulnerability AnnouncementstonnycultNo ratings yet
- Vulnerability ScanningDocument12 pagesVulnerability ScanningahgilanNo ratings yet
- It SecurityDocument4 pagesIt Security47 SARANG XII BNo ratings yet
- Pen Testing BasicsDocument153 pagesPen Testing BasicsChristopher C. Cheng100% (2)
- Computer Security Audit ChecklistDocument5 pagesComputer Security Audit ChecklistPetrrNo ratings yet
- Tugas 8 - Defananda Arya Fadaldala - 2006576552Document10 pagesTugas 8 - Defananda Arya Fadaldala - 2006576552Defan AryaNo ratings yet
- Conspect LetsdefendDocument10 pagesConspect LetsdefendНұртас ТойбекNo ratings yet
- CybercrimeDocument4 pagesCybercrimeមរតកខ្មែរ ចម្រៀងខ្មែរNo ratings yet
- Penetration TestingDocument2 pagesPenetration TestingFelix OdhiamboNo ratings yet
- Goals Attackers Try To AchieveDocument1 pageGoals Attackers Try To AchieveFelix OdhiamboNo ratings yet
- Introduction To Ethical HackingDocument2 pagesIntroduction To Ethical HackingFelix OdhiamboNo ratings yet
- Gray Areas in Computer SecurityDocument3 pagesGray Areas in Computer SecurityFelix OdhiamboNo ratings yet
- Fundermental Drivers For HackersDocument2 pagesFundermental Drivers For HackersFelix OdhiamboNo ratings yet
- Ethical Hacking TerminologiesDocument2 pagesEthical Hacking TerminologiesFelix OdhiamboNo ratings yet
- Acct Lesson 9Document9 pagesAcct Lesson 9Gracielle EspirituNo ratings yet
- 2020a1t182 Assgn1Document9 pages2020a1t182 Assgn1Aahib NazirNo ratings yet
- LemleyDocument64 pagesLemleyMeshandren NaidooNo ratings yet
- Assessment-2: Sithind002 Source and Use Information On The Hospitality IndustryDocument19 pagesAssessment-2: Sithind002 Source and Use Information On The Hospitality IndustryNidhi GuptaNo ratings yet
- Demonic Corruption RulesetDocument4 pagesDemonic Corruption RulesetJeffrey BeaumontNo ratings yet
- SfdfdsDocument4 pagesSfdfdsDominikCampanellaNo ratings yet
- Group Assignment 2Document2 pagesGroup Assignment 2zinilNo ratings yet
- Anushka Bhavsar T.Y B.Arch Working Drawing 2 Trinity College of Architecture Date: Sign: StampDocument1 pageAnushka Bhavsar T.Y B.Arch Working Drawing 2 Trinity College of Architecture Date: Sign: StampAnushka BhavsarNo ratings yet
- Dcc9 2019 Summer Model Answer Paper (Msbte Study Resources)Document39 pagesDcc9 2019 Summer Model Answer Paper (Msbte Study Resources)Sunita DhokneNo ratings yet
- 0 Physics SyllabusDocument2 pages0 Physics Syllabusiffat fatima patilNo ratings yet
- DDP Prithla 2021 Exp NoteDocument22 pagesDDP Prithla 2021 Exp Notelalit singhNo ratings yet
- Fevo 10 828503 1Document10 pagesFevo 10 828503 1keilazache2780No ratings yet
- Uji Statistik T TEST: Mean N Std. Deviation Std. Error Mean Pair 1 Pre 4,15 27 1,064, 205 Post 2,30 27, 775, 149Document3 pagesUji Statistik T TEST: Mean N Std. Deviation Std. Error Mean Pair 1 Pre 4,15 27 1,064, 205 Post 2,30 27, 775, 149GUSNAN AFRIZALNo ratings yet
- Burner Manual - 60 FTDocument18 pagesBurner Manual - 60 FTsambhajiNo ratings yet
- Microlearning Lesson Plan IntelDocument3 pagesMicrolearning Lesson Plan IntelAditi JadhavNo ratings yet
- BHC - Shakib AhmedDocument3 pagesBHC - Shakib AhmedDaniel CrumpNo ratings yet
- How Effective Were Apache Guerrilla Warfare Techniques?Document9 pagesHow Effective Were Apache Guerrilla Warfare Techniques?JayNo ratings yet
- TR - 2D Game Art Development NC IIIDocument66 pagesTR - 2D Game Art Development NC IIIfor pokeNo ratings yet
- Lesson PlanDocument2 pagesLesson PlanLUZ SELENE OLIVARES BONILLANo ratings yet
- Notiuni AUTOCADDocument15 pagesNotiuni AUTOCADDany MelNo ratings yet
- HG-G8 Module 5 RTPDocument12 pagesHG-G8 Module 5 RTPJonoh Sebastian L TerradoNo ratings yet
- 17.0 DistillationDocument73 pages17.0 DistillationcheesewizzNo ratings yet
- Bermundo Task 3 Iii-20Document2 pagesBermundo Task 3 Iii-20Jakeson Ranit BermundoNo ratings yet
- When Simulation Is The Appropriate Tool:: Answer 1Document14 pagesWhen Simulation Is The Appropriate Tool:: Answer 1Syeda Rabia JamilNo ratings yet
- MSP 430 G 2553Document75 pagesMSP 430 G 2553diosb3No ratings yet
- ChancroidDocument4 pagesChancroidDaniel Vergara ArceNo ratings yet
- A.1 Steak SauceDocument21 pagesA.1 Steak SauceNorhaslinda Mohd RoslinNo ratings yet
- Bed 2nd Sem ResultDocument1 pageBed 2nd Sem ResultAnusree PranavamNo ratings yet
- Technical Note 156 Correction Factors For Combustible Gas LEL Sensorsnr 02 16Document3 pagesTechnical Note 156 Correction Factors For Combustible Gas LEL Sensorsnr 02 16napoleon5976No ratings yet