Professional Documents
Culture Documents
Cs8494 Software Engineering MCQ
Cs8494 Software Engineering MCQ
Uploaded by
sonu kumarCopyright:
Available Formats
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5835)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (350)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (824)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (405)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Solucionario de Calculo Diferencial e Integral - GranvilleDocument177 pagesSolucionario de Calculo Diferencial e Integral - GranvilleErick Santiago Resabala Macías60% (5)
- ACCY 302 Syllabus - Curtis - Fall 2019 - ColorDocument14 pagesACCY 302 Syllabus - Curtis - Fall 2019 - ColorhihadNo ratings yet
- How To Write An Article ReviewDocument7 pagesHow To Write An Article ReviewNur SyafiqahNo ratings yet
- Flatten Et Al (2011) - A Measure of Absorptive Capacity - Scale Development and ValidationDocument19 pagesFlatten Et Al (2011) - A Measure of Absorptive Capacity - Scale Development and ValidationAndré Moraes SantosNo ratings yet
- Cs8591 Computer Networks Multiple Choice Questions (MCQ) Anna University Regulations 2017Document31 pagesCs8591 Computer Networks Multiple Choice Questions (MCQ) Anna University Regulations 2017sonu kumarNo ratings yet
- Cs8494 Software Engineering MCQDocument34 pagesCs8494 Software Engineering MCQsonu kumarNo ratings yet
- Unit-2: Evolution of Script and Languages in IndiaDocument16 pagesUnit-2: Evolution of Script and Languages in Indiasonu kumar100% (1)
- Total Mcqs ItcsDocument33 pagesTotal Mcqs Itcssonu kumarNo ratings yet
- Apprasal SystemDocument83 pagesApprasal SystemSanjana SinghNo ratings yet
- Edl 775 FinalDocument28 pagesEdl 775 Finalapi-310209692No ratings yet
- Gandevi Draft Final HFAPoADocument146 pagesGandevi Draft Final HFAPoAshourya chaturvediNo ratings yet
- UNDP Guidance Note How To Conduct A Gender AnalysisDocument20 pagesUNDP Guidance Note How To Conduct A Gender AnalysisfeeamaliNo ratings yet
- Decomposing Intrinsic and Extrinsic MotiDocument22 pagesDecomposing Intrinsic and Extrinsic MotiPratima PatelNo ratings yet
- Auditor Independence Challenges Faced by External Auditors When Auditing Large Firms in ZimbabweDocument7 pagesAuditor Independence Challenges Faced by External Auditors When Auditing Large Firms in ZimbabweInternational Journal of Business Marketing and ManagementNo ratings yet
- Vambery ArminDocument24 pagesVambery ArminFerenczi Roland100% (1)
- Final Placement Brochure June 19 WebDocument65 pagesFinal Placement Brochure June 19 WebSurya KantNo ratings yet
- Automatic Fruit Sorting MachineDocument3 pagesAutomatic Fruit Sorting MachineJournalNX - a Multidisciplinary Peer Reviewed JournalNo ratings yet
- CEE 201 Syllabus - 2012Document3 pagesCEE 201 Syllabus - 2012Khaldoun AtassiNo ratings yet
- 2 Pol Behaviour PyqDocument1 page2 Pol Behaviour Pyqjyoti dabaasNo ratings yet
- Geostatistics in Geotechnical EngineeringDocument9 pagesGeostatistics in Geotechnical EngineeringParag Jyoti DuttaNo ratings yet
- Module 4: International Business Environment ObjectivesDocument13 pagesModule 4: International Business Environment ObjectivesPrince CalicaNo ratings yet
- Week 3: Experimental Design Energy Transfer (Mug Experiment)Document3 pagesWeek 3: Experimental Design Energy Transfer (Mug Experiment)Kuhoo UNo ratings yet
- Week 1 Overview of Public Health Nursing in The Philippines 1Document6 pagesWeek 1 Overview of Public Health Nursing in The Philippines 1Leo Santos MagnoNo ratings yet
- Developing Renewable Energy Supply in Queensland Australia - A Study of The Barriers Targets Policies and ActionsDocument9 pagesDeveloping Renewable Energy Supply in Queensland Australia - A Study of The Barriers Targets Policies and ActionsAklilu BahetaNo ratings yet
- Chintan Project ReportDocument85 pagesChintan Project ReportBhanndari JayannthNo ratings yet
- أربع أهم مصطلحات التدريب أحمد البدريDocument11 pagesأربع أهم مصطلحات التدريب أحمد البدريYahia Mustafa Alfazazi100% (1)
- ECMT 1010: Introduction To Economic StatisticsDocument27 pagesECMT 1010: Introduction To Economic StatisticsObert Charmany Waharika AnandaNo ratings yet
- SSC Personal Development Handout 13Document2 pagesSSC Personal Development Handout 13Kristine Angelie Acuña VidadNo ratings yet
- Business Economics Bba I SemDocument38 pagesBusiness Economics Bba I SemAnjalika Shalini100% (1)
- Cs Ba-Bsc 3rd Sem 2016Document4 pagesCs Ba-Bsc 3rd Sem 2016So RvNo ratings yet
- The Importance of Sidewalk and Walkways in South Caloocan City To Enhance Pedestrian SafetyDocument34 pagesThe Importance of Sidewalk and Walkways in South Caloocan City To Enhance Pedestrian SafetyJerico TabongNo ratings yet
- Philippine Health Information System: Crispinita A. Valdez Director, Information Management ServiceDocument22 pagesPhilippine Health Information System: Crispinita A. Valdez Director, Information Management ServiceJuly AlliveNo ratings yet
- International Relations & A.IDocument4 pagesInternational Relations & A.IGMAP CenterNo ratings yet
- Long-Term Follow-Up of Newborns at Neurological Risk: Research Open AccessDocument8 pagesLong-Term Follow-Up of Newborns at Neurological Risk: Research Open Accessleivaherre10No ratings yet
Cs8494 Software Engineering MCQ
Cs8494 Software Engineering MCQ
Uploaded by
sonu kumarOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cs8494 Software Engineering MCQ
Cs8494 Software Engineering MCQ
Uploaded by
sonu kumarCopyright:
Available Formats
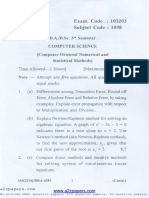
Department of Information Technology www.studymaterialz.
in
IT - Regulations 2017
2. “Software engineers should not use their
technical skills to misuse other people’s
CS8494 SOFTWARE computers.”Here the term misuse refers to:
a) Unauthorized access to computer material
ENGINEERING b) Unauthorized modification of computer
material
c) Dissemination of viruses or other malware
Common for d) All of the mentioned
CSE(4th Sem) & Answer: d
Explanation: None.
IT(5th Sem) 3. Explain what is meant by PRODUCT with
reference to one of the eight principles as per
the ACM/IEEE Code of Ethics ?
Regulations 2017 a) The product should be easy to use
b) Software engineers shall ensure that their
products and related modifications meet the
highest professional standards possible
c) Software engineers shall ensure that their
UNIT I SOFTWARE products and related modifications satisfy the
client
PROCESS AND AGILE d) It means that the product designed /created
DEVELOPMENT should be easily available
Answer: b
TOPIC 1.1 INTRODUCTION TO Explanation: None.
SOFTWARE ENGINEERING, 4. Identify an ethical dilemma from the
SOFTWARE PROCESS situations mentioned below:
a) Your employer releases a safety-critical
1. Choose the correct option in terms of system without finishing the testing of the
Issues related to professional responsibility system
a) Confidentiality b) Refusing to undertake a project
b) Intellectual property rights c) Agreement in principle with the policies of
c) Both Confidentiality & Intellectual senior management
property rights d) All of the mentioned
d) Managing Client Relationships
Answer: a
Answer: c Explanation: None.
Explanation: Engineers should normally
respect the confidentiality of their employers 5. Identify the correct statement: “Software
or clients irrespective of whether or not a engineers shall
formal confidentiality agreement has been a) act in a manner that is in the best interests
signed. of his expertise and favour.”
They should be aware of local laws governing b) act consistently with the public interest.”
the use of intellectual property such as c) ensure that their products only meet the
patents, copyright, etc.
Downloaded From: https://cse-r17.blogspot.com 1
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
SRS.” Answer: a
d) all of the mentioned Explanation: Option b & c are a part of
Software Engineering as a subject,hence
Answer: b option a covers them both.
Explanation: Software engineers shall act in
a manner that is in the best interests of their 9. The reason for software bugs and failures
client and employer consistent with the public is due to
interest and shall ensure that their products a) Software companies
and related modifications meet the highest b) Software Developers
professional standards possible.Thus options c) Both Software companies and Developers
a & c are ruled out. d) All of the mentioned
6. Select the incorrect statement: “Software Answer: c
engineers should Explanation: Software companies are
a) not knowingly accept work that is outside responsible for making policies and providing
your competence.” working atmosphere for the software
b) not use your technical skills to misuse development, so in turn these companies
other people’s computers.” become a part of software development
c) be dependent on their colleagues.” process.Bugs from developers side is no new
d) maintain integrity and independence in thing. Thus option c answers the question.
their professional judgment.”
10. Company has latest computers and state-
Answer: c of the- art software tools, so we shouldn’t
Explanation:None. worry about the quality of the product.
a) True
7. Efficiency in a software product does not b) False
include ________
a) responsiveness Answer: b
b) licensing Explanation: The infrastructure is only one
c) memory utilization of the several factors that determine the
d) processing time quality of the product.
Answer: b
Explanation: Licensing of a software product TOPIC 1.2 PERSPECTIVE AND
comes under corporate part of the software SPECIALIZED PROCESS
company. MODELS
8. As per an IBM report, “31%of the project
1. Build & Fix Model is suitable for
get cancelled before they are completed, 53%
programming exercises of ___________ LOC
overrun their cost estimates by an average of
(Line of Code).
189% and for every 100 projects, there are 94
a) 100-200
restarts”.What is the reason for these statistics
b) 200-400
?
c) 400-1000
a) Lack of adequate training in software
d) above 1000
engineering
b) Lack of software ethics and understanding Answer: a
c) Management issues in the company Explanation: Build & Fix Model is suitable
d) All of the mentioned
Downloaded From: https://cse-r17.blogspot.com 2
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
for small projects & programming exercises a) No room for structured design
of 100 or 200 lines. b) Code soon becomes unfixable &
unchangeable
2. RAD stands for c) Maintenance is practically not possible
a) Relative Application Development d) It scales up well to large projects
M
b) Rapid Application Development
c) Rapid Application Document Answer: d
d) None of the mentioned Explanation: Build & Fix Model is suitable
O
for 100-200 LOC
Answer: b
C
Explanation: None. 7. RAD Model has
a) 2 phases
3. Which one of the following models is not
T.
b) 3 phase
suitable for accommodating any change? c) 5 phases
a) Build & Fix Model d) 6 phases
b) Prototyping Model
O
c) RAD Model Answer: c
d) Waterfall Model Explanation: RAD Model consists of five
SP
phases namely:Business modeling,Data
Answer: d modeling,Process modeling,Application
Explanation: Real projects rarely follow the generation and Testing & Turnover.
sequential flow that the Waterfall Model
proposes. 8. What is the major drawback of using RAD
G
Model?
4. Which is not one of the types of prototype a) Highly specialized & skilled
LO
of Prototyping Model? developers/designers are required
a) Horizontal Prototype b) Increases reusability of components
b) Vertical Prototype c) Encourages customer/client feedback
c) Diagonal Prototype d) Increases reusability of components,
d) Domain Prototype
.B
Highly specialized & skilled
developers/designers are required
Answer: c
Explanation: Their is no such thing as Answer: d
17
Diagonal Prototype whereas other options Explanation: The client may create an
have their respective definitions. unrealistic product vision leading a team to
over or under-develop functionality.Also, the
5. Which one of the following is not a phase specialized & skilled developers are not
-R
of Prototyping Model? easily available.
a) Quick Design
b) Coding 9. SDLC stands for
c) Prototype Refinement a) Software Development Life Cycle
SE
d) Engineer Product b) System Development Life cycle
c) Software Design Life Cycle
Answer: b d) System Design Life Cycle
Explanation: A prototyping model generates
C
only a working model of a system. Answer: a
Explanation: None.
6. Which of the following statements
regarding Build & Fix Model is wrong?
Downloaded From: https://cse-r17.blogspot.com 3
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
10. Which model can be selected if user is Answer:b
involved in all the phases of SDLC? Explanation: The 4GT approach does not
a) Waterfall Model incorporate iteration and the continuous
b) Prototyping Model feedback,which is the fundamental aspect of
c) RAD Model an agile method.
d) both Prototyping Model & RAD Model
4. Agility is defined as the ability of a project
Answer: c team to respond rapidly to a change.
Explanation: None. a) True
b) False
TOPIC 1.3 INTRODUCTION TO Answer:b
AGILITY-AGILE PROCESS Explanation: The aim of agile methods is to
reduce overheads in the software process and
1. Select the option that suits the Manifesto to be able to respond quickly to changing
for Agile Software Development requirements without excessive rework.
a) Individuals and interactions
b) Working software 5. How is plan driven development different
c) Customer collaboration from agile development ?
d) All of the mentioned a) Outputs are decided through a process of
negotiation during the software development
Answer:d process
Explanation: None. b) Specification, design, implementation and
testing are interleaved
2. Agile Software Development is based on c) Iteration occurs within activities
a) Incremental Development d) All of the mentioned
b) Iterative Development
c) Linear Development Answer:c
d) Both Incremental and Iterative Explanation: A plan-driven approach to
Development software engineering is based around separate
development stages with the outputs to be
Answer:d produced at each of these stages planned in
Explanation: The software is developed in advance.
increments with the customer specifying the
requirements to be included in each increment 6. How many phases are there in Scrum ?
and the highest priority is to satisfy the a) Two
customer through early and continuous b) Three
delivery of valuable software. They are c) Four
iterative because they work on one iteration d) Scrum is an agile method which means it
followed by improvements in next iteration does not have phases
3. Which on of the following is not an agile Answer:b
method? Explanation: There are three phases in
a) XP Scrum.The initial phase is an outline planning
b) 4GT phase followed by a series of sprint cycles
c) AUP and project closure phase.
d) All of the mentioned
Downloaded From: https://cse-r17.blogspot.com 4
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
7. Agile methods seem to work best when 1. Incremental development in Extreme
team members have a relatively high skill Programming (XP) is supported through a
level. system release once every month.
a) True a) True
b) False b) False
Answer:a Answer: b
Explanation: None. Explanation: Incremental development is
supported through small, frequent system
8. Which of the following does not apply to releases.
agility to a software process?
a) Uses incremental product delivery strategy 2. In XP, as soon as the work on a task is
b) Only essential work products are produced complete, it is integrated into the whole
c) Eliminate the use of project planning and system.
testing a) True
d) All of the mentioned b) False
Answer:c Answer: a
Explanation: Testing is a major part of each Explanation: XP follows a continuous
software development process which can’t be integration approach.After any such
avoided. integration, all the unit tests in the system
must pass.
9. Which three framework activities are
present in Adaptive Software 3. In XP Increments are delivered to
Development(ASD) ? customers every _______ weeks.
a) analysis, design, coding a) One
b) requirements gathering, adaptive cycle b) Two
planning, iterative development c) Three
c) speculation, collaboration, learning d) Four
d) all of the mentioned
Answer: b
Answer:c Explanation: Extreme Programming (XP)
Explanation: None. takes an ‘extreme’ approach to iterative
development.New versions may be built
10. In agile development it is more important several times per day, hence delivering the
to build software that meets the customers’ increment for approval every 2nd week after
needs today than worry about features that testing the new version.
might be needed in the future.
a) True 4. User requirements are expressed as
b) False __________ in Extreme Programming.
a) implementation tasks
Answer:a b) functionalities
Explanation: None. c) scenarios
d) none of the mentioned
TOPIC 1.4 EXTREME Answer: c
PROGRAMMING-XP PROCESS Explanation: User requirements are
expressed as scenarios or user stories.These
Downloaded From: https://cse-r17.blogspot.com 5
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
are written on cards and the development used to run all component tests each time that
team break them down into implementation a new release is built.
tasks. These tasks are the basis of schedule
and cost estimates. 8. In XP an automated unit test framework is
used to write tests for a new piece of
5. Is a customer involved test development functionality before that functionality itself is
and validation in XP ? implemented.
a) Yes a) True
b) No b) False
c) It may vary from Customer to Customer
d) None of the mentioned Answer: a
Explanation: XP follows Test-first
Answer: c development approach.
Explanation: The role of the customer in the
testing process is to help develop acceptance 9. Developers work individually on a release
tests for the stories that are to be implemented and they compare their results with other
in the next release of the system.However, developers before forwarding that release to
people adopting the customer role have customers.
limited time available and so cannot work a) True
full-time with the development team. They b) False
may feel that providing the requirements was
enough of a contribution and so may be Answer: b
reluctant to get involved in the testing Explanation: XP follows the principle of pair
process. programming which means developers work
in pairs, checking each other’s work and
6. Programmers prefer programming to providing the support to always do a good
testing and sometimes they take shortcuts job.
when writing tests. For example, they may
write incomplete tests that do not check for 10. Which four framework activities are
all possible exceptions that may occur. found in the Extreme Programming(XP) ?
a) True a) analysis, design, coding, testing
b) False b) planning, analysis, design, coding
c) planning, design, coding, testing
Answer: a d) planning, analysis, coding, testing
Explanation: In XP Some tests can be very
difficult to write incrementally.For example, Answer: c
in a complex user interface, it is often Explanation: XP involves the mentioned four
difficult to write unit tests for the code that activities, and in the same in order.
implements the ‘display logic’ and workflow
between screens.
7. Tests are automated in Extreme
Programming. UNIT II REQUIREMENTS
a) True ANALYSIS AND
b) False
SPECIFICATION
Answer: a
Explanation: Automated test harnesses are
Downloaded From: https://cse-r17.blogspot.com 6
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
TOPIC 2.1 SOFTWARE 4. Which of the following statements explains
portability in non-functional requirements?
REQUIREMENTS: a) It is a degree to which software running on
FUNCTIONAL AND NON- one platform can easily be converted to run
FUNCTIONAL, USER on another platform
REQUIREMENTS, SYSTEM b) It cannot be enhanced by using languages,
OS’ and tools that are universally available
REQUIREMENTS, SOFTWARE and standardized
REQUIREMENTS DOCUMENT c) The ability of the system to behave
consistently in a user-acceptable manner
1. Which one of the following is a functional when operating within the environment for
requirement ? which the system was intended
a) Maintainability d) None of the mentioned
b) Portability
c) Robustness Answer: a
d) None of the mentioned Explanation: Option c is termed as reliability
and option e refers to efficiency.
Answer: d
Explanation: All are non-functional 5. Functional requirements capture the
requirements representing quality of the intended behavior of the system.
system. Functional requirements describe a) True
what the software has to do. b) False
2. Which one of the following is a Answer: a
requirement that fits in a developer’s module Explanation: The behavior of functional
? requirements may be expressed as services,
a) Availability tasks or functions the system is required to
b) Testability perform.
c) Usability
d) Flexibility 6. Choose the incorrect statement with respect
to Non-Functional Requirement(NFR).
Answer: b a) Product-oriented Approach – Focus on
Explanation: A developer needs to test his system (or software) quality
product before launching it into the market. b) Process-oriented Approach – Focus on
how NFRs can be used in the design process
3. “Consider a system where, a heat sensor c) Quantitative Approach – Find measurable
detects an intrusion and alerts the security scales for the functionality attributes
company.” What kind of a requirement the d) Qualitative Approach – Study various
system is providing ? relationships between quality goals
a) Functional
b) Non-Functional Answer: c
c) Known Requirement Explanation: Quantitative Approaches in
d) None of the mentioned NFRs are used to find measurable scales for
the quality attributes like efficiency,
Answer: a flexibility, integrity, usability etc.
Explanation: Functional requirements
describe what the software has to do. 7. How many classification schemes have
been developed for NFRs ?
Downloaded From: https://cse-r17.blogspot.com 7
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
a) Two 11. Choose the correct statement on how
b) Three NFRs integrates with Rational Unified
c) Four Process ?
d) Five a) System responds within 4 seconds on
average to local user requests and changes in
Answer: d the environment
Explanation: Software Quality Tree [Boehm b) System responds within 4 seconds on
1976], Roman [IEEE Computer 1985], average to remote user requests and changes
Process-Product-External considerations in the environment
[Sommerville 1992], Mc Call’s NFR list and c) All of the mentioned
Dimensions of Quality–Components of d) None of the mentioned
FURPS+ are the five classification schemes
for NFRs. Answer: b
. Explanation: System response to a local user
is 2 seconds on average.
8. According to components of FURPS+,
which of the following does not belong to S ?
a) Testability TOPIC 2.2 REQUIREMENT
b) Speed Efficiency ENGINEERING PROCESS:
c) Serviceability FEASIBILITY STUDIES,
d) Installability
1. Which of the following is not a diagram
Answer: b
studied in Requirement Analysis ?
Explanation: Speed Efficiency belong to
a) Use Cases
Performance (P) in FURPS+ .
b) Entity Relationship Diagram
9. Does software wear & tear by c) State Transition Diagram
decomposition ? d) Activity Diagram
a) Yes
Answer: d
b) No
Explanation: Activity Diagram comes under
Answer: b the design phase of SDLC.
Explanation: Unlike hardware, software is
2. How many feasibility studies is conducted
reliable.
in Requirement Analysis ?
10. What are the four dimensions of a) Two
Dependability ? b) Three
a) Usability, Reliability, Security, Flexibility c) Four
b) Availability, Reliability, Maintainability, d) None of the mentioned
Security
Answer: b
c) Availability, Reliability, Security, Safety
Explanation: Economic feasibility
d) Security, Safety, Testability, Usability
(cost/benefit analysis), Technical feasibility
Answer: c (hardware/software/people, etc.) and Legal
Explanation: All the traits of option c sync feasibility studies are done in Requirement
with dependability. Analysis.
3. How many phases are there in Requirement
Analysis ?
Downloaded From: https://cse-r17.blogspot.com 8
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
a) Three requirements and not the issues of
b) Four requirement analysis..
c) Five
d) Six 7. The requirements that result from
requirements analysis are typically expressed
Answer: c from one of three perspectives or
Explanation: Problem Recognition, views.WhaT is that perspective or view ?
Evaluation and Synthesis (focus is on what a) Developer
not how), Modeling, Specification and b) User
Review are the five phases. c) Non-Functional
d) Physical
4. Traceability is not considered in
Requirement Analysis. Answer: d
a) True Explanation: The perspectives or views have
b) False been described as the Operational,
Functional, and Physical views.All three are
Answer: b necessary and must be coordinated to fully
Explanation: Requirements traceability is understand the customers’ needs and
concerned with documenting the life of a objectives.
requirement and providing bi-directional
traceability between various associated 8. Requirements Analysis is an Iterative
requirements, hence requirements must be Process.
traceable. a) True
b) False
5. Requirements analysis is critical to the
success of a development project. Answer: a
a) True Explanation: Requirements analysis is
b) False conducted iteratively with functional analysis
c) Depends upon the size of project to optimize performance requirements for
d) None of the mentioned identified functions, and to verify that
synthesized solutions can satisfy customer
Answer: a requirements.
Explanation: Requirements must be
actionable, measurable, testable, related to 9. Coad and Yourdon suggested _______
identified business needs or opportunities, selection characteristics that should be used
and defined to a level of detail sufficient for as an analyst considers each potential object
system design. for inclusion in the requirement analysis
model.
6. _________ and _________ are the two a) Three
issues of Requirement Analysis. b) Four
a) Performance, Design c) Five
b) Stakeholder, Developer d) Six
c) Functional, Non-Functional
d) None of the mentioned Answer: d
Explanation: Retained information, Needed
Answer: b services, Multiple attributes, Common
Explanation: Option a and c are the types of attributes, Common operations and Essential
Downloaded From: https://cse-r17.blogspot.com 9
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
requirements are the six criterion mentioned Answer: b
by Coad and Yourdon. Explanation: Requirement Elicitation,
Requirement Analysis, Requirement
10. Requirements should specify ‘what’ but Documentation and Requirement Review are
not ‘how’. the four crucial process steps of requirement
a) True engineering.Design is in itself a different
b) False phase of Software Engineering.
Answer: a 4. FAST stands for
Explanation: ‘What’ refers to a system’s a) Functional Application Specification
purpose, while ‘How’ refers to a system’s Technique
structure and behavior. b) Fast Application Specification Technique
c) Facilitated Application Specification
TOPIC 2.3 REQUIREMENTS Technique
d) None of the mentioned
ELICITATION AND ANALYSIS,
REQUIREMENTS VALIDATION, Answer: c
REQUIREMENTS Explanation: None.
MANAGEMENT 5. QFD stands for
a) quality function design
1. What are the types of requirements ? b) quality function development
a) Availability c) quality function deployment
b) Reliability d) none of the mentioned
c) Usability
d) All of the mentioned Answer: c
Explanation: None.
Answer: d
Explanation: All the mentioned traits are 6. A Use-case actor is always a person having
beneficial for an effective product to be a role that different people may play.
developed. a) True
b) False
2. Select the developer-specific requirement ?
a) Portability Answer: b
b) Maintainability Explanation: Use-case Actor is anything that
c) Availability needs to interact with the system, be it a
d) Both Portability and Maintainability person or another (external) system.
Answer: d 7. The user system requirements are the parts
Explanation: Availability is user specific of which document ?
requirement. a) SDD
b) SRS
3. Which one of the following is not a step of c) DDD
requirement engineering? d) SRD
a) elicitation
b) design Answer: b
c) analysis Explanation: Software requirements
d) documentation specification (SRS), is a complete description
Downloaded From: https://cse-r17.blogspot.com 10
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
of the behaviour of a system to be developed SYSTEM ANALYSIS, PETRI
and may include a set of use cases that NETS- DATA DICTIONARY
describe interactions the users will have with
the software.
1. SA/SD features are obtained from which of
8. A stakeholder is anyone who will purchase the methodologies?
the completed software system under a) Constantine and Yourdon methodology
development. b) DeMarco and Yourdon methodology
a) True c) Gane and Sarson methodology
b) False d) All of the mentioned
Answer: b Answer: d
Explanation: Stakeholders are anyone who Explanation: None.
has an interest in the project. Project
stakeholders are individuals and organizations 2. Which of the following is not an activity of
that are actively involved in the project, or Structured Analysis (SA) ?
whose interests may be affected as a result of a) Functional decomposition
project execution or project completion. b) Transformation of a textual problem
description into a graphic model
9. Conflicting requirements are common in c) All the functions represented in the DFD
Requirement Engineering, with each client are mapped to a module structure
proposing his or her version is the right one. d) All of the mentioned
a) True
b) False Answer: c
Explanation: The module structure is the
Answer: a software architecture.
Explanation: This situation is seen in every
field of work as each professional has his/her 3. To arrive at a form which is suitable for
way of looking onto things & would argue to implementation in some programming
get his/her point approved. language is the purpose of
a) Structured Analysis (SA)
10. Which is one of the most important b) Structured Design (SD)
stakeholder from the following ? c) Detailed Design (DD)
a) Entry level personnel d) None of the mentioned
b) Middle level stakeholder
c) Managers Answer: b
d) Users of the software Explanation: None.
Answer: d 4. The results of structured analysis can be
Explanation: Users are always the most easily understood by ordinary customers.
important stakeholders.After all, without a) True
users or customers, what’s the point of being b) False
in business?.
Answer: a
Explanation: The results of structured
TOPIC 2.4 CLASSICAL analysis directly represents customer’s
ANALYSIS: STRUCTURED perception of the problem and uses
customer’s terminology for naming different
functions and data.
Downloaded From: https://cse-r17.blogspot.com 11
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
5. Structured Analysis is based on the not
principle of Bottom-Up Approach. d) All of the mentioned
a) True
b) False Answer: a
Explanation: None.
M
Answer: b
Explanation: Structured Analysis follows 10. Data Store Symbol in DFD represents a
uses decomposition approach. a) Physical file
O
b) Data Structure
6. The context diagram is also known as c) Logical file
C
a) Level-0 DFD d) All of the mentioned
b) Level-1 DFD
Answer: d
T.
c) Level-2 DFD
d) All of the mentioned Explanation: A logical file can be a data
structure or a physical file on disk.
Answer: a
O
Explanation: Context diagram captures the
various entities external to the system
SP
interacting with it and data flow occurring
between the system and the external entities. UNIT III SOFTWARE
7. A directed arc or line in DFD represents
DESIGN
a) Data Store
G
b) Data Process TOPIC 3.1 DESIGN PROCESS ,
c) Data Flow DESIGN CONCEPTS-DESIGN
LO
d) All of the mentioned
MODEL, DESIGN HEURISTIC ,
Answer: c ARCHITECTURAL DESIGN
Explanation: It resembles data flow in the
direction of the arrow.
.B
1. Why does architectural design occurs
during product design?
8. A DFD is always accompanied by a data
a) Stakeholders must convinced that their
dictionary.
17
needs will be met, which may be difficult
a) True
without demonstrating how the engineers
b) False
plan to build the product
Answer: a b) Product designers must judge the
feasibility of their designs
-R
Explanation: A data dictionary lists all data
items appearing in a DFD including definition c) Project planners must have some idea
and data names. about what software must be built to create
schedules and allocate resources
SE
9. Which of the following is a function of d) All of the mentioned
CASE Tool?
a) Supporting Structured analysis and design Answer: d
(SA/SD) Explanation: All of the mentioned factors are
C
b) Maintaining the data dictionary reason for the occurrence of architectural
c) Checking whether DFDs are balanced or design during product design.
Downloaded From: https://cse-r17.blogspot.com 12
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
2. What kind of investments does architectural design rationale, mapping
organization have in order to make most of by between models.
the software architects in their design?
a) Libraries 6. Which of these are included in the product
b) Standards and guidelines overview for SAD?
c) Software tools a) product vision, assumptions, constraints
d) All of the mentioned b) product scope
c) target markets, business requirements
Answer: d d) product vision, assumptions, constraints,
Explanation: Organizations investment such target markets & business requirements
as libraries, standards and guidelines,
software tools, and people with particular Answer: d
skills that software architects are expected to Explanation: Product overview includes
make the most of during its design. product vision, assumptions, constraints,
target markets and business requirements.
3. Which of the following is true?
a) The input of architectural design process is 7. Which amount the following is correct?
SAD a) Architectural models explains the main
b) The output of architectural design process design decisions made in arriving the
is SRS architecture
c) The input of architectural design process is b) Architectural design rationale presents
SRS architecture, using variety of models to
d) None of the mentioned represent different aspects or views
c) Mapping between models says sometimes
Answer: c it is difficult to connect different architectural
Explanation: The input of architectural models
design process is SRS and its output is SAD. d) All of the mentioned
4. Which of these steps are followed in Answer: c
architectural design process? Explanation: The incorrect statements are
a) Analyze SRS architectural modes presents architecture,
b) Evaluate Candidate Architectures using variety of models to represent different
c) Select architecture and finalize architecture aspects or views and Architectural design
d) All of the mentioned rationale explains the main design decisions
made in arriving the architecture.
Answer: d
Explanation: All of the mentioned steps are 8. What are the categories in which quality
followed in architectural design process. attributes are divided in?
a) Development Attributes
5. Which of these are the content for SAD? b) Operational Attributes
a) Product Overview c) Functional Attributes
b) Architectural Models d) Development & Operational Attributes
c) Architectural design rationale
d) All of the mentioned Answer: d
Explanation: Quality attributes are divided
Answer: d into two major categories development and
Explanation: Contents of SRS includes operational attributes.
product overview, architectural models,
Downloaded From: https://cse-r17.blogspot.com 13
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
9. Which of these comes under development c) Control Process
attribute? d) All of the mentioned
a) Maintainability
b) Reusability Answer: d
c) Performance Explanation: A typical top level architecture
d) Maintainability & Reusability consists of all the mentioned components.
Answer: d 3. Which among the following are valid
Explanation: Maintainability, Reusability questions raised for the top level architectural
comes under Development attributes. model?
a) What is the nature of components?
10. Which of these comes under operational b) What is the significance of the links?
attributes? c) What is the significance of the layout?
a) Performance d) All of the mentioned
b) Availability
c) Reliability Answer: d
d) All of the mentioned Explanation: All of the mentioned are the
valid questions.
Answer: d
Explanation: All of the mentioned comes 4. Which of the following are correct
under operational attributes. statements?
a) An architecture may or may not defines
components
TOPIC 3.2 ARCHITECTURAL b) An architecture is not dependable on
STYLES, ARCHITECTURAL requirements
DESIGN, ARCHITECTURAL c) An architecture is foremost an abstraction
MAPPING USING DATA FLOW of a system that suppresses details of the
components that do not affect how they are
used
1. What makes a good architecture? d) All of the mentioned
a) The architecture may not be the product of
a single architect or a small group Answer: c
b) The architect should have the technical Explanation: An architecture defines
requirements for the system and an articulated components, An architecture is dependable on
and prioritized list of qualitative properties requirements.
c) The architecture may not be well
documented 5. What does “Every software system has an
d) All of the mentioned architecture” implies?
a) System itself is a component
Answer: b b) Architecture an exist independently of its
Explanation: The architecture should be the description or specification
product of a single architect or a small group, c) All the system to be stable should posses
The architecture should be well documented. an architecture
d) None of the mentioned
2. What does a typical top level architecture
consists of? Answer: c
a) Prop Loss Model(MOPD) Explanation: All the system to be stable
b) Reverb Model(MODR) should posses an architecture, a system
Downloaded From: https://cse-r17.blogspot.com 14
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
without architecture is unstable hence every 9. Which of the following is incorrect for
software system has an architecture. Reference model, architectural styles and
reference architecture?
6. What is architectural style? a) They are not architectures
a) Architectural style is a description of b) They are useful steps towards an
component types architecture
b) It is a pattern of run-time control c) They are set of early design decisions
c) It is set of constraints on architecture d) None of the mentioned
d) All of the mentioned
Answer: d
Answer: d Explanation: All of the mentioned are
Explanation: An architectural style is a correct.
description of component types and pattern of
run-time control, It is set of constraints on 10. Which of the following can be considered
architecture. regarding client and server?
a) Client and server is an architectural style
7. What is a Reference Model? b) Client and server may be considered as an
a) It is a division of functionality together architectural style
with data flow between the pieces c) Client and server is not an architectural
b) It is a description of component types style
c) It is standard decomposition of a known d) None of the mentioned
problem into parts that cooperatively solve a
problem Answer: a
d) It is a division of functionality together Explanation: Client and server is an
with data flow between the pieces, It is architectural style.
standard decomposition of a known problem
into parts that cooperatively solve a problem 11. Which of the statements truly concludes
client and server relation with architectural
Answer: d styles?
Explanation: A reference model is division a) They are component types and their
of functionality together with data flow coordination is described in terms of
between the pieces and standard protocols that server uses to communicate
decomposition of a known problem into parts with each of its clients
that cooperatively solve a problem. b) Multiple client cannot exist at an instance
c) Architecture are countless for client and
8. What is Reference architecture? server but their architectural styles are
a) It is a reference model mapped onto different
software components d) All of the mentioned
b) It provided data flow with comments
c) It provides data flow with pieces Answer: a
d) It is a reference model mapped onto Explanation: Multiple client can exist at an
software components & data flow with instance and Architectural styles are countless
comments for client and server but their architectures are
different.
Answer: d
Explanation: Reference architecture is a 12. Which of the following is incorrect?
reference model mapped onto software a) A reference model divides the functionality
components and data flow with components. b) A reference architecture is the mapping of
Downloaded From: https://cse-r17.blogspot.com 15
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
that functionality onto system decomposition ANALYSIS, INTERFACE
c) All of the mentioned DESIGN
d) None of the mentioned
Answer: d 1. Which of the following is golden rule for
Explanation: All of the mentioned are interface design?
correct. a) Place the user in control
b) Reduce the user’s memory load
13. What truly describes the reference c) Make the interface consistent
architecture decomposition? d) All of the mentioned
a) A reference architecture is the mapping of
that functionality onto system decomposition Answer: d
may be one to one Explanation: These golden rules actually
b) A reference architecture is the mapping of form the basis for a set of user interface
that functionality onto system decomposition design principles that guide this important
is many to one software design activity.
c) A reference architecture is the mapping of
that functionality onto system decomposition 2. Which of the following is not a design
is many to many principle that allow the user to maintain
d) None of the mentioned control?
a) Provide for flexible interaction
Answer: a b) Allow user interaction to be interrupt-able
Explanation: A reference architecture is the and undo-able
mapping of that functionality onto system c) Show technical internals from the casual
decomposition may be one to one. user
d) Design for direct interaction with objects
14. Which of the following is true? that appear on the screen
a) Architecture is low level design
b) Architecture is mid level design Answer: c
c) Architecture is high level design Explanation: The user interface should move
d) None of the mentioned the user into the virtual world of the
application.
Answer: c
Explanation: Architecture is high level 3. Which of the following is not a user
design. interface design process?
a) User, task, and environment analysis and
15. What is Architecture? modeling
a) Architecture is components b) Interface design
b) Architecture is connectors c) Knowledgeable, frequent users
c) Architecture is constraints d) Interface validation
d) All of the mentioned
Answer: c
Answer: d Explanation: These are the end user for
Explanation: Architecture is whom the product is being built.
components,connectors and constraints.
4. When users are involved in complex tasks,
the demand on __________ can be
TOPIC 3.3 USER INTERFACE significant.
DESIGN: INTERFACE
Downloaded From: https://cse-r17.blogspot.com 16
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
a) short-term memory b) user’s model
b) shortcuts c) mental image
c) objects that appear on the screen d) system image
d) all of the mentioned
Answer: a
Answer: a Explanation: The requirements specification
Explanation: The interface should be may establish certain constraints that help to
designed to reduce the requirement to define the user of the system, but the interface
remember past actions and results. design is often only incidental to the design
model.
5. Which of the following option is not
considered by the Interface design? 9. What establishes the profile of end-users of
a) the design of interfaces between software the system?
components a) design model
b) the design of interfaces between the b) user’s model
software and human producers and c) mental image
consumers of information d) system image
c) the design of the interface between two
computers Answer: b
d) all of the mentioned Explanation: To build an effective user
interface, all design should begin with an
Answer: c understanding of the intended users, including
Explanation: None their profiles of their age, physical abilities,
education, etc.
6. A software might allow a user to interact
via 10. What combines the outward manifestation
a) keyboard commands of the computer-based system , coupled with
b) mouse movement all supporting information that describe
c) voice recognition commands system syntax and semantics?
d) all of the mentioned a) mental image
b) interface design
Answer: d c) system image
Explanation: All the mentioned input d) interface validation
mediums are available today.
Answer: c
7. A software engineer designs the user Explanation: When the system image and the
interface by applying an iterative process that system perception are coincident, users
draws on predefined design principles. generally feel comfortable with the software
a) True and use it effectively.
b) False
Answer: a TOPIC 3.4 COMPONENT LEVEL
Explanation: The statement is true. DESIGN: DESIGNING CLASS
BASED COMPONENTS,
8. What incorporates data, architectural,
interface, and procedural representations of
TRADITIONAL COMPONENTS
the software?
a) design model 1. Which of the following is not a construct?
a) sequence
Downloaded From: https://cse-r17.blogspot.com 17
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
b) condition c) “Code-to” ability
c) repetition d) Automatic processing
d) selection
Answer: a
Answer: d Explanation: None.
Explanation: Sequence implements
processing steps that are essential in the 5. A software component
specification of any algorithm. Condition a) Implements some functionality
provides the facility for selected processing b) Has explicit dependencies through
based on some logical occurrence, and provides and required interfaces
repetition allows for looping. c) Communicates through its interfaces only
d) All of the mentioned
2.Which of the following steps is applied to
develop a decision table? Answer: d
a) List all actions that can be associated with Explanation: All the options identify with
a specific procedure features of a software component.
b) List all conditions during execution of the
procedure 6. Which diagram evolved from a desire to
c) Define rules by indicating what action(s) develop a procedural design representation
occurs for a set of conditions that would not allow violation of the
d) All of the mentioned structured constructs?
a) State transition diagram
Answer: d b) Box diagram
Explanation: A decision table includes action c) ER diagram
stub and a condition stub with a set of rules. d) None of the mentioned
3. _________ is a pidgin(simplified version Answer: b
of a language that develops as a means of Explanation: None.
communication between two or more groups
that do not have a language in common) 7. A __________ executes the loop task first,
a) program design language then tests a condition and repeats the task
b) structured English until the condition fails.
c) pseudocode a) repeat until
d) all of the mentioned b) condition
c) do while tests
Answer: d d) if then-else
Explanation: The difference between PDL
and a real programming language lies in the Answer: a
use of narrative text embedded directly within Explanation: None.
PDL statements.
8. Which of the following is not a
4. Which of the following term is best defined characteristics of box diagram?
by the statement:”The ability to represent a) functional domain
local and global data is an essential element b) arbitrary transfer of control is impossible
of component-level design.”? c) recursion is easy to represent
a) Data representation d) providing a notation that translates actions
b) Logic verification and conditions
Downloaded From: https://cse-r17.blogspot.com 18
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
Answer: d Answer: b
Explanation: This functionality is covered by Explanation: Software testing is the process
UML diagrams. of evaluation a software item to detect
differences between given input and expected
9. The________ is represented as two output.
processing boxes connected by an line
(arrow) of control. 2. What is Cyclomatic complexity?
a) Repetition a) Black box testing
b) Sequence b) White box testing
c) Condition c) Yellow box testing
d) None of the mentioned d) Green box testing
Answer: b Answer: b
Explanation: None. Explanation: Cyclomatic complexity
measures the amount of decision logic in the
10. Which of the following term is best program module.Cyclomatic complexity
defined by the statement “Notation that can gives the minimum number of paths that can
be input directly into a computer-based generate all possible paths through the
development system offers significant module.
benefits.”?
a) Machine readability 3. Lower and upper limits are present in
b) Maintainability which chart?
c) Structure enforcement a) Run chart
d) Overall simplicity b) Bar chart
c) Control chart
Answer: a d) None of the mentioned
Explanation: Readability is processing input.
Answer: a
Explanation: A run chart is used to monitor
the behavior of a variable over time for a
process or system. Run charts graphically
UNIT IV TESTING AND display cycles, trends, shifts, or non-random
MAINTENANCE patterns in behavior over time. It contains
lower and upper limits.
TOPIC 4.1 SOFTWARE TESTING 4. Maintenance testing is performed using
FUNDAMENTALS-INTERNAL which methodology?
a) Retesting
AND EXTERNAL VIEWS OF b) Sanity testing
TESTING-WHITE BOX c) Breadth test and depth test
TESTING - BASIS PATH d) Confirmation testing
Answer: c
1. Which of the following term describes Explanation: Maintenance Testing is done on
testing? the already deployed software. The deployed
a) Finding broken code software needs to be enhanced, changed or
b) Evaluating deliverable to find errors migrated to other hardware. The Testing done
c) A stage of all projects during this enhancement, change and
d) None of the mentioned
Downloaded From: https://cse-r17.blogspot.com 19
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
migration cycle is known as maintenance c) Integration Testing
testing. d) All of the mentioned
5. White Box techniques are also classified as Answer: d
a) Design based testing Explanation: Unit, system, integration testing
b) Structural testing all of them are levels in testing.
c) Error guessing technique
d) None of the mentioned 9. Boundary value analysis belong to?
a) White Box Testing
Answer: b b) Black Box Testing
Explanation: The structural testing is the c) White Box & Black Box Testing
testing of the structure of the system or d) None of the mentioned
component. Structural testing is often referred
to as ‘white box’ or ‘glass box’ or ‘clear-box Answer: b
testing’ because in structural testing we are Explanation: Boundary value analysis is
interested in what is happening ‘inside the based on testing at the boundaries between
system/application’. partitions and checks the output with
expected output.
6. Exhaustive testing is
a) always possible 10. Alpha testing is done at
b) practically possible a) Developer’s end
c) impractical but possible b) User’s end
d) impractical and impossible c) Developer’s & User’s end
d) None of the mentioned
Answer: c
Explanation: Exhaustive testing is the testing Answer: a
where we execute single test case for multiple Explanation: Alpha testing takes place at the
test data.It means if we are using single test developer’s end. Developers observe the
case for different product or module under users and note problems. Alpha testing is
manual testing. testing of an application when development is
testing . about to complete. Minor design changes can
still be made as a result of alpha testing.
7. Which of the following is/are White box
technique?
a) Statement Testing
TOPIC 4.2 TESTING-CONTROL
b) Decision Testing STRUCTURE TESTING-BLACK
c) Condition Coverage BOX TESTING
d) All of the mentioned
1. Which of the following term describes
Answer: d testing?
Explanation: Statement testing, decision a) Finding broken code
testing, condition coverage all of them uses b) Evaluating deliverable to find errors
white box technique. c) A stage of all projects
d) None of the mentioned
8. What are the various Testing Levels?
a) Unit Testing Answer: b
b) System Testing Explanation: Software testing is the process
of evaluation a software item to detect
Downloaded From: https://cse-r17.blogspot.com 20
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
differences between given input and expected 5. White Box techniques are also classified as
output. a) Design based testing
b) Structural testing
2. What is Cyclomatic complexity? c) Error guessing technique
a) Black box testing d) None of the mentioned
b) White box testing
c) Yellow box testing Answer: b
d) Green box testing Explanation: The structural testing is the
testing of the structure of the system or
Answer: b component. Structural testing is often referred
Explanation: Cyclomatic complexity to as ‘white box’ or ‘glass box’ or ‘clear-box
measures the amount of decision logic in the testing’ because in structural testing we are
program module.Cyclomatic complexity interested in what is happening ‘inside the
gives the minimum number of paths that can system/application’.
generate all possible paths through the
module. 6. Exhaustive testing is
a) always possible
3. Lower and upper limits are present in b) practically possible
which chart? c) impractical but possible
a) Run chart d) impractical and impossible
b) Bar chart
c) Control chart Answer: c
d) None of the mentioned Explanation: Exhaustive testing is the testing
where we execute single test case for multiple
Answer: a test data.It means if we are using single test
Explanation: A run chart is used to monitor case for different product or module under
the behavior of a variable over time for a manual testing.
process or system. Run charts graphically testing .
display cycles, trends, shifts, or non-random
patterns in behavior over time. It contains 7. Which of the following is/are White box
lower and upper limits. technique?
a) Statement Testing
4. Maintenance testing is performed using b) Decision Testing
which methodology? c) Condition Coverage
a) Retesting d) All of the mentioned
b) Sanity testing
c) Breadth test and depth test Answer: d
d) Confirmation testing Explanation: Statement testing, decision
testing, condition coverage all of them uses
Answer: c white box technique.
Explanation: Maintenance Testing is done on
the already deployed software. The deployed 8. What are the various Testing Levels?
software needs to be enhanced, changed or a) Unit Testing
migrated to other hardware. The Testing done b) System Testing
during this enhancement, change and c) Integration Testing
migration cycle is known as maintenance d) All of the mentioned
testing.
Downloaded From: https://cse-r17.blogspot.com 21
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
Answer: d 2. Which of the following is not a software
Explanation: Unit, system, integration testing testing generic characteristics?
all of them are levels in testing. a) Different testing techniques are appropriate
at different points in time
9. Boundary value analysis belong to? b) Testing is conducted by the developer of
a) White Box Testing the software or an independent test group
b) Black Box Testing c) Testing and debugging are different
c) White Box & Black Box Testing activities, but debugging must be
d) None of the mentioned accommodated in any testing strategy
d) None of the mentioned
Answer: b
Explanation: Boundary value analysis is Answer: a
based on testing at the boundaries between Explanation: None.
partitions and checks the output with
expected output. 3. ITG stands for
a) instantaneous test group
10. Alpha testing is done at b) integration testing group
a) Developer’s end c) individual testing group
b) User’s end d) independent test group
c) Developer’s & User’s end
d) None of the mentioned Answer: d
Explanation: The role of an independent test
Answer: a group (ITG) is to remove the inherent
Explanation: Alpha testing takes place at the problems
developer’s end. Developers observe the associated with letting the builder test the
users and note problems. Alpha testing is thing that has been built.
testing of an application when development is
about to complete. Minor design changes can 4. By collecting ________ during software
still be made as a result of alpha testing. testing, it is possible to develop meaningful
guidelines to halt the testing process.
a) Failure intensity
TOPIC 4.3 REGRESSION b) Testing time
TESTING UNIT TESTING , c) Metrics
INTEGRATION TESTING d) All of the mentioned
VALIDATION TESTING
Answer: c
SYSTEM TESTING AND Explanation: It answers questions like:
DEBUGGING “When are we done with testing?”.
1. Software Debugging is a set of activities 5. Which of the following issues must be
that can be planned in advance and conducted addressed if a successful software testing
systematically. strategy is to be implemented?
a) True a) Use effective formal technical reviews as a
b) False filter prior to testing
b) Develop a testing plan that emphasizes
Answer: b “rapid cycle testing.”
Explanation: Software Testing is a set of c) State testing objectives explicitly
such activities. d) All of the mentioned
Downloaded From: https://cse-r17.blogspot.com 22
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
Answer: d b) Additional tests that focus on software
Explanation: All the mentioned options are functions that are likely to be affected by the
carried out for the purpose. change
c) Tests that focus on the software
6. Test cases should uncover errors like components that have been changed
a) Nonexistent loop termination d) Low-level components are combined into
b) Comparison of different data types clusters that perform a specific software sub-
c) Incorrect logical operators or precedence function
d) All of the mentioned
Answer: d
Answer: a Explanation: Regression testing may be
Explanation: Test cases should uncover conducted manually, by re-executing a subset
errors such as all the explained options and of all test cases or using automated capture or
much more. playback tools
7. Which of the following errors should not 10. Which testing is an integration testing
be tested when error handling is evaluated? approach that is commonly used when
a) Error description is unintelligible “shrink-wrapped” software products are being
b) Error noted does not correspond to error developed?
encountered a) Regression Testing
c) Error condition causes system intervention b) Integration testing
prior to error handling c) Smoke testing
d) Error description provide enough d) Validation testing
information to assist in the location of the
cause of the error Answer: c
Explanation: Smoke testing is designed as a
Answer: a pacing mechanism for time-critical projects,
Explanation: Actually, error description does allowing the software team to assess its
not provide enough information to assist in project on a frequent basis.
the location of the cause of the error.
11. In which testing level the focus is on
8. What is normally considered as an adjunct customer usage?
to the coding step a) Alpha Testing
a) Integration testing b) Beta Testing
b) Unit testing c) Validation Testing
c) Completion of Testing d) Both Alpha and Beta
d) Regression Testing
Answer: d
Answer: b Explanation: Alpha testing is done at
Explanation: After source level code has developer’s end while beta testing is done at
been developed, reviewed, and verified for user’s end.
correspondence to component level design,
unit test case design begins. 12. Validation refers to the set of tasks that
ensure that software correctly implements a
9. Which of the following is not regression specific function.
test case? a) True
a) A representative sample of tests that will b) False
exercise all software functions
Downloaded From: https://cse-r17.blogspot.com 23
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
Answer: b Answer: c
Explanation: Its verification, while Explanation: None.
validation refers to a different set of tasks that
ensure that the software that has been built is 4. Forward engineering is not necessary if an
traceable to customer requirements. existing software product is producing the
correct output.
a) True
TOPIC 4.4 SOFTWARE b) False
IMPLEMENTATION
TECHNIQUES: CODING Answer: b
PRACTICES-REFACTORING- Explanation: Forward engineering refers to
taking a high-level model and using it to build
MAINTENANCE AND a more complex lower-level implementation.
REENGINEERING
5. Which of the following is not an example
of a business process?
TOPIC 4.5 BPR MODEL- a) designing a new product
REENGINEERING PROCESS b) hiring an employee
MODEL c) purchasing services
d) testing software
1. What are the problems with re-structuring? Answer: d
a) Loss of comments Explanation: It is a part of development
b) Loss of documentation phase.
c) Heavy computational demands
d) All of the mentioned 6. Which of the following is a data problem?
a) hardware problem
Answer: b b) record organisation problems
Explanation: Restructuring doesn’t help with c) heavy computational demands
poor modularisation where related d) loss of comments
components are dispersed throughout the
code. Answer: b
Explanation: Records representing the same
2. Which of the following is not a module entity may be organised differently in
type? different programs.
a) Object modules
b) Hardware modules 7. When does one decides to re-engineer a
c) Functional modules product?
d) Process support modules a) when tools to support restructuring are
disabled
Answer: a b) when system crashes frequently
Explanation: Except option a all other are c) when hardware or software support
module types. becomes obsolete
d) subsystems of a larger system require few
3. Reverse engineering of data focuses on
maintenance
a) Internal data structures
b) Database structures Answer: c
c) ALL of the mentioned Explanation: Re-engineering involves
d) None of the mentioned
Downloaded From: https://cse-r17.blogspot.com 24
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
putting in the effort to make the system easier b) Refactoring
to maintain. c) Restructuring
d) None of the mentioned
8. Which of the following is not a business
goal of re-engineering ? Answer: c
a) Cost reduction Explanation: Restructuring involves
b) Time reduction automatic conversion from unstructured to
c) Maintainability structured code.
d) None of the mentioned
Answer: d TOPIC 4.6 REVERSE AND
Explanation: No such goal is mentioned FORWARD ENGINEERING
which is not a business goal, so option d is
correct here. 1. In reverse engineering process, what refers
to the sophistication of the design information
9. Which of these benefits can be achieved that can be extracted from the source code?
when software is restructured? a) interactivity
a) Higher quality programs b) completeness
b) Reduced maintenance effort c) abstraction level
c) Software easier to test d) direction level
d) All of the mentioned
Answer: c
Answer: d Explanation: None.
Explanation: The answer is self explanatory.
2. In reverse engineering, what refers to the
10. Data re-engineering may be part of the level of detail that is provided at an
process of migrating from a file-based system abstraction level?
to a DBMS-based system or changing from a) interactivity
one DBMS to another. b) completeness
a) True c) abstraction level
b) False d) directionality
Answer: a Answer: b
Explanation: Data re-engineering involves Explanation: None.
analyzing and reorganizing the data structures
in a program. 3. The core of reverse engineering is an
activity called
11. BPR stands for a) restructure code
a) Business process re-engineering b) directionality
b) Business product re-engineering c) extract abstractions
c) Business process requirements d) interactivity
d) None of the mentioned
Answer: c
Answer: a Explanation: The engineer must evaluate the
Explanation: The answer is self explanatory. old program and extract a meaningful
specification of the processing that is
12. Source code translation is a part of which performed, the user interface that is applied,
re-engineering technique?
a) Data re-engineering
Downloaded From: https://cse-r17.blogspot.com 25
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
and the program data structures or database Answer: a
that is used. Explanation: This is accomplished by
examining the program code with the intent
4. What have become de rigueur for of grouping related program variables.
computer-based products and systems of
every type? 8. Which of the following steps may not be
a) GUIs used to define the existing data model as a
b) Candidate keys precursor to re-engineering a new database
c) Object model model:
d) All of the mentioned a) Build an initial object model
b) Determine candidate keys
Answer: a c) Refine the tentative classes
Explanation: Therefore, the redevelopment d) Discover user interfaces
of user interfaces has become one of the most
common types of re-engineering activity. But Answer: d
before a user interface can be rebuilt, reverse Explanation: Once information defined in
engineering should occur. the preceding steps is known, a series of
transformations can be applied to map the old
5. Forward engineering is also known as database structure into a new database
a) extract abstractions structure.
b) renovation
c) reclamation 9. Much of the information necessary to
d) both renovation and reclamation create a behavioral model can be obtained by
observing the external manifestation of the
Answer: d existing
Explanation: Forward engineering, also a) candidate keys
called renovation or reclamation , not only b) interface
recovers design information from existing c) database structure
software, but uses this information to alter or d) none of the mentioned
reconstitute the existing system in an effort to
improve its overall quality. Answer: b
Explanation: The GUI or the interface
6. Reverse engineering is the process of provides the base for the behavioral model.
deriving the system design and specification
from its 10. Extracting data items and objects, to get
a) GUI information on data flow, and to understand
b) Database the existing data structures that have been
c) Source code implemented is sometimes called
d) All of the mentioned a) data analysis
b) directionality
Answer: c c) data extraction
Explanation: None d) client applications
7. Reverse engineering techniques for internal Answer: a
program data focus on the definition of Explanation: None.
classes of objects.
a) True 11. Reverse engineering and Re-engineering
b) False are equivalent processes of software
Downloaded From: https://cse-r17.blogspot.com 26
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
engineering. b) Developing a cost and effort estimate for a
a) True software project is too complex
b) False c) All of the mentioned
d) None of the mentioned
Answer: b
Explanation: Re engineering is a process of Answer: c
analysis and change whereby a system is Explanation: For these reasons, we
modified by first reverse engineering and then decompose the problem, re-characterizing it
forward engineering. as a set of smaller problems.
12. Transformation of a system from one 2. Cost and effort estimation of a software
representational form to another is known as uses only one forms of decomposition, either
a) Re-factoring decomposition of the problem or
b) Restructuring decomposition of the process.
c) Forward engineering a) True
d) Both Re-factoring and Restructuring b) False
Answer: d Answer: b
Explanation: None. Explanation: Estimation uses one or both
forms of partitioning.
13. Which of the following is not an objective
of reverse engineering? 3. If a Direct approach to software project
a) to reduce maintenance effort sizing is taken, size can be measured in
b) to cope with complexity a) LOC
c) to avoid side effects b) FP
d) to assist migration to a CASE environment c) LOC and FP
d) None of the mentioned
Answer: d
Explanation: Reverse engineering helps us to Answer: a
detect side effects rather than avoiding them. Explanation: LOC or Line of Code is a direct
measure to estimate project size.
4. Which software project sizing approach
develop estimates of the information domain
UNIT V PROJECT characteristics?
a) Function point sizing
MANAGEMENT b) Change sizing
c) Standard component sizing
TOPIC 5.1 SOFTWARE d) Fuzzy logic sizing
PROJECT MANAGEMENT: Answer: a
ESTIMATION LOC, FP BASED Explanation: None.
ESTIMATION, MAKE/BUY
DECISION 5. The expected value for the estimation
variable (size), S, can be computed as a
weighted average of the optimistic(Sopt),
1. Why is decomposition technique required? most likely (Sm), and pessimistic (Spess)
a) Software project estimation is a form of estimates given as
problem solving
Downloaded From: https://cse-r17.blogspot.com 27
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
a) EV = (Sopt + 4Sm + Spess)/4 c) Customer-built software should be
b) EV = (Sopt + 4Sm + Spess)/6 developed
c) EV = (Sopt + 2Sm + Spess)/6 d) All of the mentioned
d) EV = (Sopt + 2Sm + Spess)/4
Answer: d
Answer: b Explanation: None..
Explanation: This assumes that there is a
very small probability that the actual size 10. Which of the following is not one of the
result will fall outside the optimistic or five information domain characteristics of
pessimistic values. Function Point (FP) decomposition?
a) External inputs
6. How many forms exists of Barry Boehm’s b) External outputs
COCOMO Model? c) External process
a) Two d) External inquiries
b) Three
c) Four Answer: c
d) No form exists Explanation: External inputs, external
outputs, external inquiries, internal logical
Answer: b files, external interface files are the five
Explanation: The three forms include the domains.
basic, intermediate and advanced COCOMO
model. 11. The project planner must reconcile the
estimates based on decomposition techniques
7. Who suggested the four different to produce a single estimate of effort.
approaches to the sizing problem? a) True
a) Putnam b) False
b) Myers
c) Boehm Answer: b
d) Putnam and Myers Explanation: The planner must determine the
cause of divergence and then reconcile the
Answer: d estimates.
Explanation: None.
12. Programming language experience is a
8. In many cases, it is often more cost- part of which factor of COCOMO cost
effective to acquire, rather than develop, drivers?
computer software. a) Personnel Factor
a) True b) Product Factor
b) False c) Platform Factor
d) Project Factor
Answer: a
Explanation: Managers are faced with a Answer: a
make-buy decision in such situations. Explanation: None.
9. A make-buy decision is based on whether 13. If an Indirect approach is taken, then the
a) The software may be purchased off-the- sizing approach is represented as
shelf a) LOC
b) “Full-experience” or “Partial-experience” b) FP
software components should be used
Downloaded From: https://cse-r17.blogspot.com 28
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
c) Fuzzy Logic COCOMO I COCOMO II
d) LOC and FP It provides estimates
It provides
that represent one
Answer: b estimates pf
standard deviation
Explanation: A function point (FP) is a unit effort and
around the most likely
of measurement to express the amount of schedule.
estimate.
business functionality an information system
This model is
provides to a user. This model is based
based upon the
upon the non linear
linear reuse
reuse formula
TOPIC 5.2 COCOMO I & II formula.
MODEL This model is
This model is also
based upon reuse
also based upon
COCOMO 1 Model: model which looks at
the assumption of
The Constructive Cost Model was first effort needed to
reasonably stable
developed by Barry W. Boehm. The model is understand and
requirements.
for estimating effort, cost, and schedule for estimate.
software projects. It is also called as Basic Effort equation’s
Effort equation’s
COCOMO. This model is used to give an exponent is
exponent is
approximate estimate of the various determined by 3
determined by 5 scale
parameters of the project. Example of development
factors.
projects based on this model is business modes.
system, payroll management system and Development
inventory management systems. begins with the
It follows a spiral type
requirements
COCOMO 2 Model: of development.
assigned to the
The COCOMO-II is the revised version of the software.
original Cocomo (Constructive Cost Model) Number of
and is developed at the University of submodels in In COCOMO II,
Southern California. This model calculates COCOMO I is 3 Number of submodel
the development time and effort taken as the and 15 cost are 4 and 17 cost
total of the estimates of all the individual drivers are drivers are assigned
subsystems. In this model, whole software is assigned
divided into different modules. Example of
Size of software
projects based on this model is Spreadsheets
Size of software stated in terms of
and report generator.
stated in terms of Object points,
Lines of code function points and
Difference between COCOMO 1 and
lines of code
COCOMO 2:
COCOMO I COCOMO II TOPIC 5.3 PROJECT
COCOMO I is SCHEDULING ,SCHEDULING,
COCOMO II is useful
useful in the
in non-sequential, EARNED VALUE ANALYSIS
waterfall models
rapid development PLANNING
of the software
and reuse models of
development
software.
cycle. 1. Which of the following is the reason that
software is delivered late?
Downloaded From: https://cse-r17.blogspot.com 29
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
a) Changing customer requirements that are 5. Ensuring that no more than the allocated
not reflected in schedule changes number of people are allocated at any given
b) Technical difficulties that could not have time in Software Scheduling is known as
been foreseen in advance a) Time Allocation
c) Human difficulties that could not have b) Effort Validation
been foreseen in advance c) Defined Milestone
d) All of the mentioned d) Effort Distribution
Answer: d Answer: b
Explanation: None. Explanation: None.
2. Which of the following is an activity that 6. What is used to determine the
distributes estimated effort across the planned recommended degree of rigor with which the
project duration by allocating the effort to software process should be applied on a
specific software engineering tasks? project?
a) Software Macroscopic schedule a) Degree of Rigor
b) Software Project scheduling b) Adaptation criteria
c) Software Detailed schedule c) Task Set
d) None of the mentioned d) Both degree of Rigor and adaptation
criteria
Answer: b
Explanation: None. Answer: b
Explanation: Four different degrees of rigor
3. Every task that is scheduled should be are: casual, structured, strict, and quick
assigned to a specific team member is termed reaction.
as
a) Compartmentalization 7. What evaluates the risk associated with the
b) Defined milestones technology to be implemented as part of
c) Defined responsibilities project scope?
d) Defined outcomes a) Concept scoping
b) Preliminary concept planning
Answer: c c) Technology risk assessment
Explanation: These responsibilities are d) Customer reaction to the concept
domain specific.
Answer: b
4. What is a collection of software Explanation: None.
engineering work tasks, milestones, and
deliverables that must be accomplished to 8. Which of the following is not an adaptation
complete a particular project? criteria for software projects?
a) Task set a) Size of the project
b) Degree of milestone b) Customers Complaints
c) Adaptation criteria c) Project staff
d) All of the mentioned d) Mission criticality
Answer: a Answer: b
Explanation: None. Explanation: These can vary from client to
client.
Downloaded From: https://cse-r17.blogspot.com 30
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
9. Which of the following is a project c) Ivar Jacabson
scheduling method that can be applied to d) None of the mentioned
software development?
a) PERT Answer: a
b) CPM Explanation: Timeline chart, also called a
c) CMM Gantt chart was invented by Henry Gantt, an
d) Both PERT and CPM industrial engineer in 1917 .
Answer: d
Explanation: Program evaluation and review
TOPIC 5.4 PROJECT PLAN,
technique (PERT) and critical path method PLANNING PROCESS, RFP
(CPM) are two project scheduling methods RISK MANAGEMENT
that can be applied to software development.
1. Risk management is one of the most
10. A technique for performing quantitative important jobs for a
analysis of progress is known as a) Client
a) BCWS b) Investor
b) EVA c) Production team
c) BAC d) Project manager
d) CBSE
Answer: d
Answer: b Explanation: Risk management involves
Explanation: The earned value system anticipating risks that might affect the project
provides a common value scale for every schedule or the quality of the software being
task, regardless of the type of work being developed, and then taking action to avoid
performed. The total hours to do the whole these risks.
project are estimated, and every task is given
an earned value based on its estimated 2. Which of the following risk is the failure of
percentage of the total. a purchased component to perform as
expected?
11. What is the recommended distribution of a) Product risk
effort for a project? b) Project risk
a) 40-20-40 c) Business risk
b) 50-20-30 d) Programming risk
c) 30-40-30
d) 50-30-20 Answer: a
Explanation: Risks that affect the quality or
Answer: a performance of the software being developed.
Explanation: A recommended distribution of
effort across the software process is 40% 3. Which of the following term is best defined
(analysis and design), 20% (coding), and 40% by the statement: “There will be a change of
(testing). organizational management with different
priorities.”?
12. A project usually has a timeline chart a) Staff turnover
which was developed by b) Technology change
a) Henry Gantt c) Management change
b) Barry Boehm d) Product competition
Downloaded From: https://cse-r17.blogspot.com 31
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
Answer: c Answer: b
Explanation: None. Explanation: The risks associated with
technology might affect the product
4. Which of the following term is best defined development.
by the statement: “The underlying technology
on which the system is built is superseded by 8. Which of the following term is best defined
new technology.”? by the statement: “Derive traceability
a) Technology change information to maximize information hiding
b) Product competition in the design.”?
c) Requirements change a) Underestimated development time
d) None of the mentioned b) Organizational restructuring
c) Requirements changes
Answer: a d) None of the mentioned
Explanation: Technology changes are
common in the competitive environment of Answer: c
software engineering. Explanation: Tracing the requirements can
help us understand the risk.
5. What assess the risk and your plans for risk
mitigation and revise these when you learn 9. Which of the following strategies means
more about the risk? that the impact of the risk will be reduced?
a) Risk monitoring a) Avoidance strategies
b) Risk planning b) Minimization strategies
c) Risk analysis c) Contingency plans
d) Risk identification d) All of the mentioned
Answer: a Answer: b
Explanation: None. Explanation: None.
6. Which of the following risks are derived 10. Risk management is now recognized as
from the organizational environment where one of the most important project
the software is being developed? management tasks.
a) People risks a) True
b) Technology risks b) False
c) Estimation risks
d) Organizational risks Answer: a
Explanation: None.
Answer: d
Explanation: These risks are at management
level.
TOPIC 5.5 IDENTIFICATION,
PROJECTION - RISK
7. Which of the following risks are derived MANAGEMENT-RISK
from the software or hardware technologies
that are used to develop the system?
a) Managerial risks TOPIC 5.6 IDENTIFICATION-
b) Technology risks RMMM PLAN-CASE TOOLS
c) Estimation risks
d) Organizational risks 1. What all has to be identified as per risk
identification?
Downloaded From: https://cse-r17.blogspot.com 32
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
a) Threats c) Project risks
b) Vulnerabilities d) Technical risks
c) Consequences
d) All of the mentioned Answer: b
Explanation: Business risks often jeopardize
Answer: d the project or the product.
Explanation: Risk identification states what
could cause a potential loss. 6. Which of the following is not a business
risk?
2. Which one is not a risk management a) building an excellent product or system
activity? that no one really wants
a) Risk assessment b) losing the support of senior management
b) Risk generation due to a change in focus or change in people
c) Risk control c) lack of documented requirements or
d) None of the mentioned software scope
d) losing budgetary or personnel commitment
Answer: b
Explanation: Risk management activities Answer: c
would never want a new risk to be generated. Explanation: This is not considered as a
business risk.
3. What is the product of the probability of
incurring a loss due to the risk and the 7. Which of the following is a systematic
potential magnitude of that loss? attempt to specify threats to the project plan?
a) Risk exposure a) Risk identification
b) Risk prioritization b) Performance risk
c) Risk analysis c) Support risk
d) All of the mentioned d) Risk projection
Answer: a Answer: d
Explanation: None. Explanation: By identifying known and
predictable risks, the project manager takes a
4. What threatens the quality and timeliness first step toward avoiding them when possible
of the software to be produced? and controlling them when necessary.
a) Known risks
b) Business risks 8. Which risks are associated with the overall
c) Project risks size of the software to be built or modified?
d) Technical risks a) Business impact risks
b) Process definition risks
Answer: d c) Product size risks
Explanation: Technical risks identify d) Development environment risks
potential design, implementation, interface,
verification, and maintenance problems. Answer: c
Explanation: None.
5. What threatens the viability of the software
to be built? 9. Which risks are associated with constraints
a) Known risks imposed by management or the marketplace?
b) Business risks a) Business impact risks
b) Process definition risks
Downloaded From: https://cse-r17.blogspot.com 33
Department of Information Technology www.studymaterialz.in
IT - Regulations 2017
c) Product size risks requirements and be fit for its intended use.”?
d) Development environment risks a) Performance risk
b) Cost risk
Answer: a c) Support risk
Explanation: None. d) Schedule risk
10. Which of the following term is best Answer: a
defined by the statement:”the degree of Explanation: None.
uncertainty that the product will meet its
Downloaded From: https://cse-r17.blogspot.com 34
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5835)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (350)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (824)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (405)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Solucionario de Calculo Diferencial e Integral - GranvilleDocument177 pagesSolucionario de Calculo Diferencial e Integral - GranvilleErick Santiago Resabala Macías60% (5)
- ACCY 302 Syllabus - Curtis - Fall 2019 - ColorDocument14 pagesACCY 302 Syllabus - Curtis - Fall 2019 - ColorhihadNo ratings yet
- How To Write An Article ReviewDocument7 pagesHow To Write An Article ReviewNur SyafiqahNo ratings yet
- Flatten Et Al (2011) - A Measure of Absorptive Capacity - Scale Development and ValidationDocument19 pagesFlatten Et Al (2011) - A Measure of Absorptive Capacity - Scale Development and ValidationAndré Moraes SantosNo ratings yet
- Cs8591 Computer Networks Multiple Choice Questions (MCQ) Anna University Regulations 2017Document31 pagesCs8591 Computer Networks Multiple Choice Questions (MCQ) Anna University Regulations 2017sonu kumarNo ratings yet
- Cs8494 Software Engineering MCQDocument34 pagesCs8494 Software Engineering MCQsonu kumarNo ratings yet
- Unit-2: Evolution of Script and Languages in IndiaDocument16 pagesUnit-2: Evolution of Script and Languages in Indiasonu kumar100% (1)
- Total Mcqs ItcsDocument33 pagesTotal Mcqs Itcssonu kumarNo ratings yet
- Apprasal SystemDocument83 pagesApprasal SystemSanjana SinghNo ratings yet
- Edl 775 FinalDocument28 pagesEdl 775 Finalapi-310209692No ratings yet
- Gandevi Draft Final HFAPoADocument146 pagesGandevi Draft Final HFAPoAshourya chaturvediNo ratings yet
- UNDP Guidance Note How To Conduct A Gender AnalysisDocument20 pagesUNDP Guidance Note How To Conduct A Gender AnalysisfeeamaliNo ratings yet
- Decomposing Intrinsic and Extrinsic MotiDocument22 pagesDecomposing Intrinsic and Extrinsic MotiPratima PatelNo ratings yet
- Auditor Independence Challenges Faced by External Auditors When Auditing Large Firms in ZimbabweDocument7 pagesAuditor Independence Challenges Faced by External Auditors When Auditing Large Firms in ZimbabweInternational Journal of Business Marketing and ManagementNo ratings yet
- Vambery ArminDocument24 pagesVambery ArminFerenczi Roland100% (1)
- Final Placement Brochure June 19 WebDocument65 pagesFinal Placement Brochure June 19 WebSurya KantNo ratings yet
- Automatic Fruit Sorting MachineDocument3 pagesAutomatic Fruit Sorting MachineJournalNX - a Multidisciplinary Peer Reviewed JournalNo ratings yet
- CEE 201 Syllabus - 2012Document3 pagesCEE 201 Syllabus - 2012Khaldoun AtassiNo ratings yet
- 2 Pol Behaviour PyqDocument1 page2 Pol Behaviour Pyqjyoti dabaasNo ratings yet
- Geostatistics in Geotechnical EngineeringDocument9 pagesGeostatistics in Geotechnical EngineeringParag Jyoti DuttaNo ratings yet
- Module 4: International Business Environment ObjectivesDocument13 pagesModule 4: International Business Environment ObjectivesPrince CalicaNo ratings yet
- Week 3: Experimental Design Energy Transfer (Mug Experiment)Document3 pagesWeek 3: Experimental Design Energy Transfer (Mug Experiment)Kuhoo UNo ratings yet
- Week 1 Overview of Public Health Nursing in The Philippines 1Document6 pagesWeek 1 Overview of Public Health Nursing in The Philippines 1Leo Santos MagnoNo ratings yet
- Developing Renewable Energy Supply in Queensland Australia - A Study of The Barriers Targets Policies and ActionsDocument9 pagesDeveloping Renewable Energy Supply in Queensland Australia - A Study of The Barriers Targets Policies and ActionsAklilu BahetaNo ratings yet
- Chintan Project ReportDocument85 pagesChintan Project ReportBhanndari JayannthNo ratings yet
- أربع أهم مصطلحات التدريب أحمد البدريDocument11 pagesأربع أهم مصطلحات التدريب أحمد البدريYahia Mustafa Alfazazi100% (1)
- ECMT 1010: Introduction To Economic StatisticsDocument27 pagesECMT 1010: Introduction To Economic StatisticsObert Charmany Waharika AnandaNo ratings yet
- SSC Personal Development Handout 13Document2 pagesSSC Personal Development Handout 13Kristine Angelie Acuña VidadNo ratings yet
- Business Economics Bba I SemDocument38 pagesBusiness Economics Bba I SemAnjalika Shalini100% (1)
- Cs Ba-Bsc 3rd Sem 2016Document4 pagesCs Ba-Bsc 3rd Sem 2016So RvNo ratings yet
- The Importance of Sidewalk and Walkways in South Caloocan City To Enhance Pedestrian SafetyDocument34 pagesThe Importance of Sidewalk and Walkways in South Caloocan City To Enhance Pedestrian SafetyJerico TabongNo ratings yet
- Philippine Health Information System: Crispinita A. Valdez Director, Information Management ServiceDocument22 pagesPhilippine Health Information System: Crispinita A. Valdez Director, Information Management ServiceJuly AlliveNo ratings yet
- International Relations & A.IDocument4 pagesInternational Relations & A.IGMAP CenterNo ratings yet
- Long-Term Follow-Up of Newborns at Neurological Risk: Research Open AccessDocument8 pagesLong-Term Follow-Up of Newborns at Neurological Risk: Research Open Accessleivaherre10No ratings yet