Professional Documents
Culture Documents
MEA01 Monitor, Evaluate and Assess Performance and Conformance
MEA01 Monitor, Evaluate and Assess Performance and Conformance
Uploaded by
noneCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
MEA01 Monitor, Evaluate and Assess Performance and Conformance
MEA01 Monitor, Evaluate and Assess Performance and Conformance
Uploaded by
noneCopyright:
Available Formats
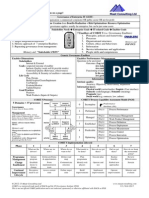
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
MEA01 – Process Setting
Process Description1
Collect, validate and evaluate business, IT and process goals and metrics. Monitor that processes are performing against agreed-on performance and conformance goals and
metrics and provide reporting that is systematic and timely.
Process Purpose Statement1
Provide transparency of performance and conformance and drive achievement of goals.
Process Assessment Objectives1
The objectives of this assessment are to determine that:
Goals and metrics are approved by the stakeholders,
Processes are measured against agreed-on goals and metrics,
The enterprise monitoring, assessing and informing approach is effective and operational,
Process reporting on performance and conformance is useful and timely, and
Goals and metrics are integrated within enterprise monitoring systems.
Process Risk Drivers2
Business expectations and needs not met
Customer expectations and business needs not identified
Decisions failing to support the business needs and concerns
Disconnect between management and IT
Good performance not recognized, demotivating staff
1 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
Inability of the board and executive to direct and control key IT activities
Incidents due to unresolved problems
Ineffective reporting on organization-wide IT process performance indicators
Lost opportunities for improvement
Metrics based on incorrect or incomplete data
Metrics based on objectives that are not aligned with business objectives
Monitored data failing to support the analysis of the overall process performance
Performance measurement not taken seriously
Poor performance not acted upon, leading to further degradation
Process performance weaknesses remaining and repeating themselves
Senior management dissatisfied with IT performance
Wrong decisions based on unreliable performance information
2 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
MEA01 – Process Goal Assessment
1
MEA01.01 Management Practice
Establish a monitoring approach. Engage with stakeholders to establish and maintain a monitoring approach to define the objectives, scope and method for measuring
business solution and service delivery and contribution to enterprise objectives. Integrate this approach with the corporate performance management system.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
MEA01.01.01 - Identify stakeholders (e.g., Determine if the IT organization has identified its stakeholders (e.g., management, process owners
Stakeholders management, process owners and users).
and users).
MEA01.01.02 - Engage with stakeholders and 1. Interview a sample of managers and determine how they communicate with stakeholders.
Stakeholder Engagement communicate the enterprise
requirements and objectives for 2. Determine how IT communicates (verbally, written, etc.) monitoring dn reporting goals.
monitoring, aggregating, and
reporting, using common 3. Determine if IT uses baselining and benchmarking as a means of engaging with stakeholders
definitions (e.g., enterprise using common terms.
glossary, metadata and
taxonomy), baselining and
benchmarking.
MEA01.01.03 - Align and Align and continually maintain 1. Determine if the organization uses common means for data gathering and enterprise reporting.
Maintain the monitoring and evaluation
approach with the enterprise 2. Determine the extent that business intelligence applications are used as a common ground.
approach and the tools to be
used for data gathering and
enterprise reporting (e.g.,
business intelligence
applications).
3 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
MEA01.01.04 - Goals and Agree on the goals and metrics 1. Using interviews with a sample of managers, determine how the organization aligns its goals
Metrics (e.g., conformance, performance, and metrics.
value, and risk), taxonomy
(classification and relationships 2. Obtain samples of how goals and metrics are used..
between goals and metrics) and
data (evidence) retention.
MEA01.01.05 - Agree on a life cycle 1. Obtain the policies, standards, and procedures associated with life cycle management including
Monitoring and Reporting management and change control the change control process.
process for monitoring and
reporting. Include improvement 2. Determine the extent of their use and how monitoring and reporting happen.
opportunities for reporting,
metrics, approach, baselining
and benchmarking.
MEA01.01.06 - Request, prioritize and allocate Through interviews with a sample set pf managers, determine if and how the organization
Monitoring Resources resources for monitoring requests, prioritizes and allocates resources.
(consider appropriateness,
efficiency, effectiveness and
confidentiality).
MEA01.01.07 - Approach Periodically validate the 1. Determine if and how the organization periodically validates the approach.
approach used and identify new
or changed stakeholders, 2. Determine how the organization becomes aware of new or changed stakeholders,
requirements and resources requirements, and/or resources.
4 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
MEA01.02 Management Practice1
Set performance and conformance targets. Work with stakeholders to define, periodically review, update and approve performance and conformance targets within the
performance measurement system.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
MEA01.02.01 - Goals and Define and periodically review 1. Obtain a listing of the metrics used in IT.
Metrics with stakeholders the goals and
metrics to identify any significant 2. Obtain the means for reporting these metrics.
missing items and define
reasonableness of targets and 3. Determine if the metrics are in line with the monitoring framework.
tolerances.
MEA01.02.02 - Changes Communicate proposed changes Inquire whether and confirm that there is a process to control all changes to performance
to performance and conformance monitoring data sources.
targets and tolerances (relating
to metrics) with key due diligence
stakeholders (e.g., legal, audit,
HR, ethics, compliance, finance).
MEA01.02.03 - Publish Publish changed targets and Determine if the organization publishes changed targets and tolerances to users of this
tolerances to users of this information.
information.
MEA01.02.04 - Evaluate Evaluate whether the goals and 1. Obtain IT goals and metrics.
metrics are adequate, i.e.,
specific, measurable, achievable, 2. Review these and determine if the goals and metrics are adequate (i.e., specific, measurable,
relevant and time-bound and achievable).
(SMART).
5 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
MEA01.03 Management Practice1
Collect and process performance and conformance data. Collect and process timely and accurate data aligned with enterprise approaches
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
MEA01.03.01 - Data Collect data from defined Determine that performance data is collected from defined processes—automated, where
Collection processes—automated, where possible.
possible.
MEA01.03.02 - Efficiency Assess efficiency (effort in Assess efficiency (effort in relation to insight provided) and appropriateness (usefulness and
and Appropriateness relation to insight provided) and meaning) and validate integrity (accuracy and completeness) of performance data.
appropriateness (usefulness and
meaning) and validate integrity
(accuracy and completeness) of
collected data.
MEA01.03.03 - Metric Aggregate data to support Determine if data is aggregated to support measurement of agreed-on metrics.
Measurement measurement of agreed-on
metrics.
MEA01.03.04 - Align aggregated data to the Determine if reports data is appropriately aligned and aggregated.
Objectives Alignment enterprise reporting approach
and objectives
MEA01.03.05 - Tools and Use suitable tools and systems Determine if the organization uses suitable tools and systems for the processing and format of
Systems for the processing and format of data for analysis.
data for analysis.
6 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
MEA01.04 Management Practice1
Analyze and report performance. Periodically review and report performance against targets, using a method that provides a succinct all-around view of IT performance and
fits within the enterprise monitoring system.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
MEA01.04.01 - Process Design process performance Notes: IT should facilitate effective, timely decision-making (e.g., scorecards, traffic light reports)
Performance Reports reports that are concise, easy to and ensure that the cause and effect between goals and metrics are communicated in an
understand, and tailored to understandable manner.
various management needs and
audiences. 1. Interview process owners to confirm that target performance levels for key processes are
established and validated against the industry and competition.
2. Inspect performance reports for timeliness of measurement and effectiveness of comparison to
the targets.
MEA01.04.02 - Compare the performance Determine if and who compares the performance values to internal targets and benchmarks and,
Performance Values values to internal targets and where possible, to external benchmarks (industry and key competitors).
benchmarks and, where
possible, to external
benchmarks (industry and key
competitors).
MEA01.04.03 - Changes Recommend changes to the Determine if and who recommends changes to the goals and metrics, where appropriate.
goals and metrics, where
appropriate.
MEA01.04.04 - Distribute reports to the relevant Determine if the organization distributes reports to the relevant stakeholders.
Stakeholder Reporting stakeholders.
MEA01.04.05 - Deviation Analyze the cause of deviations Notes: IT should, at appropriate times, review all deviations and search for root causes, where
Analysis against targets, initiate remedial necessary. Document the issues for further guidance if the problem recurs. Document results.
7 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
actions, assign responsibilities
for remediation, and follow up.
Determine if the organization analyzes the cause of deviations against targets, initiate remedial
actions, assign responsibilities for remediation, and follow up.
MEA01.04.06 - Rewards Where feasible, link Describe how the organization, where feasible, links achievement of performance targets to the
Link achievement of performance organizational reward compensation system.
targets to the organizational
reward compensation system.
8 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
MEA01.05 Management Practice1
Ensure the implementation of corrective actions. Assist stakeholders in identifying, initiating and tracking corrective actions to address anomalies.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
MEA01.05.01 - Issues Review management 1. Inquire whether processes, policies and procedures exist to initiate, prioritize and allocate
Responses responses, options and responsibility and tracking for all remedial actions.
recommendations to address
issues and major deviations 2. Confirm by inspecting the documentation of the approach and observing the process, where
possible.
MEA01.05.02 - Ensure that the assignment of Determine that the organization ensures that there is assignment of responsibility for corrective
Responsibility responsibility for corrective action.
Assignments action is maintained.
MEA01.05.03 - Track the results of actions 1. Obtain a sample of historic performance reporting.
Commitment Tracking committed.
2. Analyze and verify that substandard performance trends are routinely identified.
3. Understand if and how problems are escalated to senior management.
MEA01.05.04 - Report the results to the 1. Determine if and how the reported results go to the stakeholders.
Stakeholder Reporting stakeholders.
2. Obtain samples of these communications.
9 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
MEA01 Assessment Summary1
Management Practice Practice Description Practice Assessment Summary
Establish a monitoring approach. Engage with stakeholders to establish and
maintain a monitoring approach to define the
objectives, scope and method for measuring
business solution and service delivery and
contribution to enterprise objectives. Integrate
this approach with the corporate performance
management system.
Set performance and Work with stakeholders to define, periodically
conformance targets. review, update and approve performance and
conformance targets within the performance
measurement system.
Collect and process performance Collect and process timely and accurate data
and conformance data. aligned with enterprise approaches.
Analyze and report performance. Periodically review and report performance
against targets, using a method that provides
a succinct all-around view of IT performance
and fits within the enterprise monitoring
system.
Ensure the implementation of Assist stakeholders in identifying, initiating
corrective actions. and tracking corrective actions to address
anomalies.
10 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
MEA01 Risk Summary1
Create multiple risk scenarios for each risk identified in the summary above that affects achieving the objective.
Risk Scenario - Describe the risk/opportunity scenario, including a discussion of the negative and positive impact of the scenario. The description clarifies the threat/
vulnerability type and includes the actors, events, assets and time issues.
Risk Scenario Component Mark all that apply
Threat Type (Describe the nature of the event) ⃣
Malicious
⃣ Accidental
⃣ Error
⃣ Failure
⃣ Natural
⃣ External requirement
Actor (Who or what could trigger the threat that exploits a vulnerability) ⃣ Internal
⃣ External
⃣ Human
⃣ Non-Human
Event (Something that happens that was not supposed to happen, something does not happen ⃣ Disclosure
that was supposed to happen, or a change in circumstances. Events always have causes and ⃣ Interruption
usually have consequences. A consequence is the outcome of an event and has an impact on ⃣ Modification
objectives.) ⃣ Theft
⃣ Destruction
⃣ Ineffective design
⃣ Ineffective execution
⃣ Rules and regulations
⃣ Inappropriate use
Asset (An asset is something of tangible or intangible value that is worth and skills protecting, ⃣ Process
including people, systems, infrastructure, finances and reputation.) ⃣ People and Skills
⃣ Organizational Structure
11 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Monitor, Evaluate, and Assess
Process: MEA01 – Monitor, Evaluate and Assess Performance and Conformance
Risk Scenario Component Mark all that apply
⃣ Physical Infrastructure
⃣ IT Infrastructure
⃣ Information
⃣ Applications
Resource (A resource is anything that helps to achieve a goal.) ⃣ Process
⃣ People and Skills
⃣ Organizational Structure
⃣ Physical Infrastructure
⃣ IT Infrastructure
⃣ Information
⃣ Applications
Time Timing ⃣ Critical ⃣ Non-Critical
Duration ⃣ Short ⃣ Moderate ⃣ Extended
Detection ⃣ Slow ⃣ Moderate ⃣ Instant
Time lag ⃣ Immediate ⃣ Delayed
Velocity ⃣ Slowing ⃣ Constant ⃣ Increasing
Likelihood ⃣ Highly ⃣ Moderate ⃣ Unlikely
Impact ⃣ Great ⃣ Moderate ⃣ Little
Possible Risk Response Risk Avoidance:
Risk Acceptance:
Risk Sharing/Transfer:
Risk Mitigation:
12 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
You might also like
- CISA - 27e - CH - 4 - Information Systems Operations and Business ResilienceDocument154 pagesCISA - 27e - CH - 4 - Information Systems Operations and Business ResilienceJa'far NumeiriNo ratings yet
- IT Audit Checklist Sachin Hissaria 1691968387Document9 pagesIT Audit Checklist Sachin Hissaria 1691968387Nur Amin KadirNo ratings yet
- EDM05 Stakeholder TransparencyDocument9 pagesEDM05 Stakeholder TransparencynoneNo ratings yet
- EDM05 Stakeholder TransparencyDocument9 pagesEDM05 Stakeholder TransparencynoneNo ratings yet
- Methodological Dimensions in Curriculum DevelopmentDocument44 pagesMethodological Dimensions in Curriculum DevelopmentRivanda Debi100% (8)
- DSS01-Manage-Operations Icq Eng 1214Document28 pagesDSS01-Manage-Operations Icq Eng 1214LorenzoNo ratings yet
- Information Systems Auditing: The IS Audit Testing ProcessFrom EverandInformation Systems Auditing: The IS Audit Testing ProcessRating: 1 out of 5 stars1/5 (1)
- MEA03 Monitor, Evaluate and Assess Compliance With External RequirementsDocument12 pagesMEA03 Monitor, Evaluate and Assess Compliance With External RequirementsnoneNo ratings yet
- 3 Assessment Report Template Appendix D3Document6 pages3 Assessment Report Template Appendix D3fatsolaNo ratings yet
- CISA Domain 1 Questions and AnswersDocument33 pagesCISA Domain 1 Questions and AnswerseliNo ratings yet
- CISA Practice Questions IT GovernanceDocument4 pagesCISA Practice Questions IT GovernanceJoeFSabaterNo ratings yet
- CISA - Domain 3 - IS Acquisition, Development and ImplementationDocument153 pagesCISA - Domain 3 - IS Acquisition, Development and ImplementationPremdeepakHulagbali100% (2)
- MEA03 Monitor, Evaluate and Assess Compliance With External RequirementsDocument12 pagesMEA03 Monitor, Evaluate and Assess Compliance With External RequirementsnoneNo ratings yet
- CIS-CAT OVAL Customization GuideDocument24 pagesCIS-CAT OVAL Customization GuidenoneNo ratings yet
- CIS-CAT OVAL Customization GuideDocument24 pagesCIS-CAT OVAL Customization GuidenoneNo ratings yet
- HARD Goals PDFDocument9 pagesHARD Goals PDFZhang Yi Ling100% (1)
- Multiple Goals, Multiple Pathways: The Role of Goal Orientation in Learning and AchievementDocument12 pagesMultiple Goals, Multiple Pathways: The Role of Goal Orientation in Learning and AchievementLeticia ChontalNo ratings yet
- MEA02 Monitor, Evaluate and Assess The System of Internal ControlDocument21 pagesMEA02 Monitor, Evaluate and Assess The System of Internal Controlnone100% (1)
- Application Sys. ReviewDocument4 pagesApplication Sys. ReviewadiltsaNo ratings yet
- IT Asset Management A Complete Guide - 2020 EditionFrom EverandIT Asset Management A Complete Guide - 2020 EditionRating: 4 out of 5 stars4/5 (1)
- Cobit 5 Process Assessment Worksheet Area: Governance Domain: Evaluate, Direct and MonitorDocument9 pagesCobit 5 Process Assessment Worksheet Area: Governance Domain: Evaluate, Direct and MonitornoneNo ratings yet
- Domain 1 - The Process of Auditing Information Systems: Task StatementsDocument8 pagesDomain 1 - The Process of Auditing Information Systems: Task StatementsRashid Ahmed ShaikhNo ratings yet
- Test 1Document121 pagesTest 1JeejuNo ratings yet
- DSS04-Manage-Continuity Icq Eng 1214Document29 pagesDSS04-Manage-Continuity Icq Eng 1214Mario OrozcoNo ratings yet
- CISA Practice Questions To Prep For The Exam - TechTargetDocument9 pagesCISA Practice Questions To Prep For The Exam - TechTargetbirish2009No ratings yet
- 05.2 - 2020 - CISA-50Q - Additional - Questions - v1Document8 pages05.2 - 2020 - CISA-50Q - Additional - Questions - v1ckuesters100% (1)
- TRICS5 User Guide PDFDocument15 pagesTRICS5 User Guide PDFPhu Cong LeNo ratings yet
- WAPO04 Manage Innovation Audit Assurance Program - Icq - Eng - 0814Document28 pagesWAPO04 Manage Innovation Audit Assurance Program - Icq - Eng - 0814Jean Dumas MauriceNo ratings yet
- S15 IT Controls 14nov07 PDFDocument3 pagesS15 IT Controls 14nov07 PDFfaisal_cseduNo ratings yet
- SEARCHITSecurity Assessment ToolDocument84 pagesSEARCHITSecurity Assessment Tooltsegay.csNo ratings yet
- CISA Domain 4Document2 pagesCISA Domain 4DangerNo ratings yet
- Information Risks: Whose Business Are They?: Itgovernance DomainpracticesandcompetenciesDocument23 pagesInformation Risks: Whose Business Are They?: Itgovernance DomainpracticesandcompetenciesNegrito de JesusNo ratings yet
- Cybercrime-Audit-Assurance-Program Icq Eng 1012Document54 pagesCybercrime-Audit-Assurance-Program Icq Eng 1012ssglcnNo ratings yet
- CIS Controls v8 Mapping To ISACA COBIT 19 V21.10.spreadsheetsDocument88 pagesCIS Controls v8 Mapping To ISACA COBIT 19 V21.10.spreadsheetslero_leroNo ratings yet
- COBIT-5-Assurance Res Eng 1213Document17 pagesCOBIT-5-Assurance Res Eng 1213sheryhanNo ratings yet
- Cobit Questionnaire Template-GeneralDocument9 pagesCobit Questionnaire Template-GeneralalfiettaNo ratings yet
- InfoSystemsAuditChecklist (Version 1)Document44 pagesInfoSystemsAuditChecklist (Version 1)Merrick Martin100% (1)
- ISACA Certification IT Audit - Security - Governance and RiskDocument33 pagesISACA Certification IT Audit - Security - Governance and Riskakbisoi1No ratings yet
- WAPO13 Manage Security Audit Assurance Program Icq Eng 0814Document29 pagesWAPO13 Manage Security Audit Assurance Program Icq Eng 0814eldorado100% (1)
- Audit Program IT Business Continuity Disaster RecoveryDocument7 pagesAudit Program IT Business Continuity Disaster RecoveryGelo VidalNo ratings yet
- CISA Exam PreparationDocument6 pagesCISA Exam PreparationrushicNo ratings yet
- Audit ChecklistDocument14 pagesAudit ChecklistARRY WIDODONo ratings yet
- Cobit 2019 - Assignment 20241Document162 pagesCobit 2019 - Assignment 20241Juan VelasquezNo ratings yet
- DSS02 Manage Service Requests and Incidents - Icq - Eng - 1214Document28 pagesDSS02 Manage Service Requests and Incidents - Icq - Eng - 1214LorenzoNo ratings yet
- Management Awareness Diagnostic 1-Controlling IT: COBIT 2019 Dominios y ObjetivossDocument4 pagesManagement Awareness Diagnostic 1-Controlling IT: COBIT 2019 Dominios y Objetivossroger chavarriaNo ratings yet
- COBIT 5-Self-Assessment Templates - BAI - 25 August 2015Document97 pagesCOBIT 5-Self-Assessment Templates - BAI - 25 August 2015sannyNo ratings yet
- ITCi ITAC Change MGMT 0707Document37 pagesITCi ITAC Change MGMT 0707samanNo ratings yet
- How To Derive An IT Audit UniverseDocument4 pagesHow To Derive An IT Audit UniversekolocokroNo ratings yet
- Integrating COBIT 5 With COSO PDFDocument59 pagesIntegrating COBIT 5 With COSO PDFHenry Omar Espinal VasquezNo ratings yet
- BAI01-Manage Programs and ProjectsDocument50 pagesBAI01-Manage Programs and Projectsvenusrambo8No ratings yet
- WAPO09 Manage Service Agreements Audit Assurance Program - Icq - Eng - 0814Document28 pagesWAPO09 Manage Service Agreements Audit Assurance Program - Icq - Eng - 0814Jean Dumas MauriceNo ratings yet
- CISA 27e Sample Exam Answers and JustificationsDocument49 pagesCISA 27e Sample Exam Answers and JustificationsOzge CelikNo ratings yet
- CISA-mock Test - Domain 2 (100 Questions)Document45 pagesCISA-mock Test - Domain 2 (100 Questions)Sweeto SaniNo ratings yet
- A Practical Guide and Case Study On Leveraging ITIL v3 and ISO 20000 As Part of Your Overall Best-Practice EcosystemDocument41 pagesA Practical Guide and Case Study On Leveraging ITIL v3 and ISO 20000 As Part of Your Overall Best-Practice Ecosystemmdmnawaz123No ratings yet
- Iso20000 2Document4 pagesIso20000 2Karloz PsyNo ratings yet
- COBIT 5 Foundation Exam Revision On A PageDocument1 pageCOBIT 5 Foundation Exam Revision On A PageSergiö Montoya100% (1)
- Change Management Audit Program FinalDocument28 pagesChange Management Audit Program Finalsashi100% (1)
- Cisa Exam Mar 2021 ImportantDocument129 pagesCisa Exam Mar 2021 ImportantSushil AndreNo ratings yet
- ISAudit 2010oct18Document239 pagesISAudit 2010oct18Suvojit DeshiNo ratings yet
- CISA - Practice.questions.2009.2a It GovernanceDocument27 pagesCISA - Practice.questions.2009.2a It Governancemgdawodu50% (2)
- Cisa V26.75 - 1Document182 pagesCisa V26.75 - 1Ashfaaq CurimbaccusNo ratings yet
- VPN Security Audit Assurance Program Icq Eng 1012Document34 pagesVPN Security Audit Assurance Program Icq Eng 1012zamanbdNo ratings yet
- EDM03 Ensure Risk Optimisation Audit Assurance Program - Icq - Eng - 0214Document29 pagesEDM03 Ensure Risk Optimisation Audit Assurance Program - Icq - Eng - 0214ssglcnNo ratings yet
- Cobit 5 Process Assessment Worksheet Area: Governance Domain: Evaluate, Direct and MonitorDocument9 pagesCobit 5 Process Assessment Worksheet Area: Governance Domain: Evaluate, Direct and MonitornoneNo ratings yet
- MEA02 Monitor, Evaluate and Assess The System of Internal ControlDocument21 pagesMEA02 Monitor, Evaluate and Assess The System of Internal Controlnone100% (1)
- Resume Template MasterDocument2 pagesResume Template MasternoneNo ratings yet
- Writing Module Course LOs KennedyDocument68 pagesWriting Module Course LOs KennedynoneNo ratings yet
- Bestitdocuments InventoryDocument51 pagesBestitdocuments InventorynoneNo ratings yet
- 1 Finding A Career: 1.1 Exploring CareersDocument1 page1 Finding A Career: 1.1 Exploring CareersnoneNo ratings yet
- 1.1 A Good Research Paper Will Have A ThesisDocument3 pages1.1 A Good Research Paper Will Have A ThesisnoneNo ratings yet
- CIS-CAT OVAL Customization GuideDocument43 pagesCIS-CAT OVAL Customization GuidenoneNo ratings yet
- Darktrace Tech AppliancesDocument2 pagesDarktrace Tech AppliancesnoneNo ratings yet
- CIS-CAT Users GuideDocument101 pagesCIS-CAT Users GuidenoneNo ratings yet
- 5 Yogas Aspects 1Document4 pages5 Yogas Aspects 1Yogesh PrajapatiNo ratings yet
- Games: Mixed Strategies: MicroeconomicsDocument38 pagesGames: Mixed Strategies: MicroeconomicsnoneNo ratings yet
- I PluginsDocument6 pagesI PluginsnoneNo ratings yet
- Medical Astro DiagnosisDocument10 pagesMedical Astro DiagnosisnoneNo ratings yet
- Strategic Mindset - Action GuideDocument19 pagesStrategic Mindset - Action GuidePoodle McdoodleNo ratings yet
- Competency Examples With Performance StatementsDocument20 pagesCompetency Examples With Performance StatementsRRSC GCCSCNo ratings yet
- Case Study: Prepared By: Karan Rai Section B ROLL NO. 083Document7 pagesCase Study: Prepared By: Karan Rai Section B ROLL NO. 083Paras BablaniNo ratings yet
- Assignment Paper On Administrative Processes and Human BehaviorDocument5 pagesAssignment Paper On Administrative Processes and Human BehaviorRemigio Eskandor100% (1)
- The Hypothesis Oriented Algorithm IIDocument18 pagesThe Hypothesis Oriented Algorithm IIScot MorrisonNo ratings yet
- What Is Leaders-WPS OfficeDocument10 pagesWhat Is Leaders-WPS OfficeJackline Fabian DaudiNo ratings yet
- End Chapter Test Module 3Document4 pagesEnd Chapter Test Module 3Jareb RoguelNo ratings yet
- Roles and Competencies of School Heads: Learning OutcomeDocument8 pagesRoles and Competencies of School Heads: Learning OutcomeAndrew Florencio RabalNo ratings yet
- A Study On Employee Engagement IN Lucas Indians ServiceDocument60 pagesA Study On Employee Engagement IN Lucas Indians ServiceRocks KiranNo ratings yet
- Facilitation TheoryDocument2 pagesFacilitation TheoryYessamin Valerie PergisNo ratings yet
- Informations Sistems Defined Chapter 2: DCWVRDocument11 pagesInformations Sistems Defined Chapter 2: DCWVRDaniel BogischNo ratings yet
- How To Pitch TV Series in Hollywood: Bob LevyDocument37 pagesHow To Pitch TV Series in Hollywood: Bob LevyRogerio Cathala100% (1)
- A Study On Quality of Work Life Balance in Xenon Auto Spare Parts Private Limited at CoimbatoreDocument21 pagesA Study On Quality of Work Life Balance in Xenon Auto Spare Parts Private Limited at CoimbatoreMeena SivasubramanianNo ratings yet
- 00 - Performance Evaluation Security - ThisDocument9 pages00 - Performance Evaluation Security - ThisKen CruzNo ratings yet
- The Evolution of Succession Planning 4Document10 pagesThe Evolution of Succession Planning 4Ghansham PanwarNo ratings yet
- Training - Development Survey at BSNL Mba HR Project ReportDocument74 pagesTraining - Development Survey at BSNL Mba HR Project ReportSrinivasa SaluruNo ratings yet
- IMS654 ExerciseDocument6 pagesIMS654 ExerciseLopee RahmanNo ratings yet
- Cliftonstrengths Top 5 ReportDocument17 pagesCliftonstrengths Top 5 Reportapi-662145947No ratings yet
- Detailing Types of PlansDocument3 pagesDetailing Types of PlanswithraviNo ratings yet
- Strengths Insight Guide: Donald CliftonDocument7 pagesStrengths Insight Guide: Donald CliftonFrensen Salim100% (1)
- MNG302B 2011-S2 - Discussion Class Slides InclDocument104 pagesMNG302B 2011-S2 - Discussion Class Slides Inclangus_princeNo ratings yet
- Customer - Service Policy Session 2Document29 pagesCustomer - Service Policy Session 2Anca Irimia100% (1)
- A Comprehensive Guide To Employee EngagementDocument67 pagesA Comprehensive Guide To Employee EngagementSamawat ShakeelNo ratings yet
- An Attributional Theory of Achievement Motivation and Emotion PDFDocument26 pagesAn Attributional Theory of Achievement Motivation and Emotion PDFAndreea JazmínNo ratings yet
- Basic Competencies 3Document6 pagesBasic Competencies 3Mariam SalongaNo ratings yet
- Empployee Evaluation FormDocument2 pagesEmpployee Evaluation FormIrish AgpoonNo ratings yet
- TII Workbook Mar20 FINAL PDFDocument342 pagesTII Workbook Mar20 FINAL PDFeverydayisagift9999No ratings yet