Professional Documents
Culture Documents
Data Storage Management in Cloud
Data Storage Management in Cloud
Uploaded by
Daniel MatthiasOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Data Storage Management in Cloud
Data Storage Management in Cloud
Uploaded by
Daniel MatthiasCopyright:
Available Formats
SSRG International Journal of Computer Science and Engineering (SSRG-IJCSE) – Volume 7 Issue 7 – July 2020
Data Storage Management in Cloud
Computing Using Deduplication Technique
Marcel Chibuzor Amaechi#1, Matthias Daniel*2, Bennett E.O#3
#1
Msc Student, Computer Science department, Rivers State University, Nigeria.
*2#3
Leturers, Computer Science department, Rivers State University, Nigeria.
Abstract has a very specific effect in the modern age of
Duplication of data stored in the cloud response, adequacy and competence in the provision
occupies more space. However, during data update, of Information Technology resources. Innovative
duplicate data must be changed in more than one advances later diminish the production of unreliable
place, which is more complex to rectify and would computerized material. The project requires the
increase operational cost in cloud. This research aim transfer, collection and allocation of the re-
at developing data storage management in cloud appropriated data in the pay-per-use program. The
computing using deduplication technique. Object- need for better and simpler options on the part of
oriented methodology was used. Data deduplication companies and government agencies is practically
has been achieved via block level deduplication and expressed in this general enthusiasm for shared
key generation (symmetric algorithm). The data file storage benefits. In other words, cloud appropriation
was divided into number of blocks and of fixed length. has a very specific effect in the modern age of
Each block was divided into segments and the files response, adequacy and competence in the provision
were saved only once. However, each file was of Information Technology resources. Now you no
converted into cipher text (key form) using symmetric longer have to spend much money to buy expensive
algorithm, the system checked for existence of key software or advanced equipment, which you may
and excluded redundant key maintaining only one never need again. The main inspiration behind these
copy of the key in the cloud storage, the stored key cautious benefits is the decrease of capital
was shrinked to reduce the storage space using expenditure (CapEx), a steady charge to maintain
ShrinKey algorithm and rejection algorithm was used operational expenditure (OpEx) and a persistent fee
to remove replicated key. System was implemented in to manage OpEx, which is an ongoing cost to run a
Java programming language. File in cloud appeared business [2].
in encrypted key with size of 16bytes thereby storage
space was minimized. The system supported data Cloud computing is just another way of
privacy since data stored in cloud was encrypted and describing information technology "outsourcing"; it
user privacy was supported, as data was uploaded by also refers to any computer service render over a
different users. network [3]. Cloud computing means that it is
delivered as a service by another organization and
Keywords — Deduplication, Data storage generally accessible over the internet in a completely
management, Cloud computing smooth form, instead of using all of its hardware and
software that is stored on your machine or on the
I. INTRODUCTION network of your business. It is in the nebulous
The US International Data Corporation (IDC) "cloud" that the Internet represents precisely where
estimates that, by 2020, the digital world would hardware and software are located and how they all
produce up to 40 trillion giga-bytes of replicated data work, regardless of the user. Data storage is one of
[1]. This upswing in the digital world continues to the most widely used cloud services. The benefit to
increase interest in IT/Network infrastructure, cloud usage is that they can store and view large
increasing demand on board for a great deal of volumes of data at anytime and anywhere without
financially knowledgeable use of data limits and updating their devices. Data stored in the cloud that
network communication capacity for information require different forms of protection due to the
exchange. Remote storage systems in this field are different nature of the data. Data stored in the cloud
used to study Cloud storage-based services which, in includes private personal data, shared information,
particular, provides efficient network storage shared data within a group.
platforms, is of widespread importance. The project Data deduplication or single instancing
requires the transfer, collection and allocation of the applies specifically to the deletion of redundant data.
re-appropriated data in the pay-per-use program. The Owing to the exponential increase in the amount of
need for better and simpler options on the part of digital information, storage systems must be put in
companies and government agencies is practically place to store and preserve this information
expressed in this general enthusiasm for shared effectively. Deduplication is essentially the removal
storage benefits. In other words, cloud appropriation of redundant data [4]. Deduplication techniques are
ISSN: 2348 – 8387 www.internationaljournalssrg.org Page 1
SSRG International Journal of Computer Science and Engineering (SSRG-IJCSE) – Volume 7 Issue 7 – July 2020
widely used in cloud services to reduce server space. DepSky-A and DepSky-CA. these algorithms are
Cloud Service Providers (CSPs) also execute supported by the theory and performance assessment.
deduplications to ensure optimal use of disk capacity The system uses existing cloud computing systems
or use server redundancy to avoid multiple client and avoids running codes on database server
redundant file storage. Duplication saves about
90-95% and 68% on storage space for backup Meta Storage was launched by [13]. It is
systems and standard file systems, while many highly accessible Hash table that duplicates data in
corporate cloud storage services such as Bitcasa, various storage systems. It offers a description of a
Dropbox and Google Drive to-deductions make use wide selection of stock approaches such as cloud
of cost savings [1]. [5] suggested a PRE-based storage, SSH file servers and local file systems by
deduplicatibility program but relied entirely on the unifying them in a single Application Program
Approved Party to control the deduplicatibility of the Interface (API).
results. Data access regulated by data holders cannot
be tailored flexibly to different scenarios. [6] III. RESEARCH METHODOLOGY
Proposed access control for Cloud Attributes-Based The research methodology used in the study
Encryption (ABE) encrypted data. Set a set of is the CRA and Object-Oriented Design (OOD),
attributes for the user to identify and encrypt data on Object-Oriented Design. The study is based on
the basis of a given access mechanism for the objects. CRA is a methodology to solve problems
attribute. [7] has introduced modern server-side that allows the development of systems, procedures,
deductibility for authenticated data. The Cloud tools and technology that can be applied far beyond
service will control access to outsourced data even case study. The study used in early-development
when controlled dynamically by random converging prediction of several diseases with various
encryption and protected community ownership premature and ill-tea full-tea, has been born after the
allocation. Greek goddess of principle [14] The design approach
is aimed at providing the best solution for any
II. LITERATURE REVIEW problem situation in industrial design, electronics or
Data storage is a way to store information in architectural design.
memory. Data are managed in large storage rather
than saving it on the hard disk of a computer. Storage A. SYSTEM DESIGN
Area Network (SAN) is a distributed storage network
that provides centralized block storage. Such SANs The proposed system is based on Deduplication
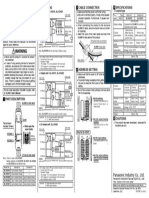
are easily saccessible by clients because they are Technique on Block Level. Figure 1 represents
directly connected to the operating system. proposed system.
Furthermore, A SAN has its own network storage
system and is typically inaccessible over a standard DEDUPLICATION
USER
network for normal users. It should also be UPLOAD
TECHNIQUE
remembered that the SAN does not abstract the file (BLOCK LEVEL
DATA DEDUPLICATION)
itself but blocks operations only. Network Attached
Storage (NAS) uses, like SAN, NFS and SMB / CIFS
protocols, where remote storage is supported and
computers are ordering data rather than disk blocks
[8]. End-users can link their data to a local archive KEY
with a copy from a remote server by means of cloud GENERATIO
N
storage [9] Document updates are synchronized in the (ENCRYPTIO
local folder automatically to the cloud service
provider. It may be mounted on multiple devices to
ensure the data is modified in the same folder,
independently of the user. Only with the same WEB CLIENT
approach is data available to the customer [10] (CHECK
REPLICATE
[11] Introduced a very strong cloud storage KEY)
system. This system uses various cloud storage
providers for data storage and streaming of proxies,
this eliminates the one-time cost for switching
network providers on a separate computer the
machine is running.
CLOUD
[12] Published two algorithms that permit STORAGE
users to create Byzantine cloud tolerant storage
through the quorum of cloud storage providers, Fig. 1: Architecture of the Proposed System
ISSN: 2348 – 8387 www.internationaljournalssrg.org Page 2
SSRG International Journal of Computer Science and Engineering (SSRG-IJCSE) – Volume 7 Issue 7 – July 2020
The file is uploaded to a server by the user For example, given a series of data file Vi with name
(data owner). The user (database data owner) uses the V and content i (iϵ1,..,n). Assuming V1 is identified
encryption algorithm and web- client searches for key as first data file. Vi's (iϵ 2,...,n) offset compared to V1
presence within the cloud storage and stores key in in the data chain is L = F(Vi).
the server. Five components of the data owner are
included in this scheme. Where F is the calculated offset function for
finding out Vi's offset relative to the first data file in
a) USER the chain. If the data file's content is large, its offset
Before accessing cloud storage information, value relative to the first data file in the chain is the
the user must be authenticated. The user is needed to maximum content length Lmax. In the data file, the
provide device authentication needs including user content category can be simply executed by dividing
name and password. The user will start the server the segment maximum length.
when opening the cloud environment. Then the user
can upload file to the cloud. System input is shown in However, once the data storage threshold is
Table 1. given, the number of content groups G can be
obtained by:
Table 1: Input Data G = Lmax/T
S|N INPUT DATA FORMAT
Where,
1 Document Docx, pdf, txt T is the storage threshold.
G is the content groups.
Lmax is the maximum length of the content.
2 Audio Mp3 V is the data file
i is the content.
3 Video Mp4
We used a chunk level often referred to as
4 Image Jpeg, png "Deduplicate Block Level." the data file is divided
into blocks and fixed lengths. The block must be
broken into pieces, and the files will only be saved
once. The main benefit of using block level is that
Cloud storage accepts files in different file any form of file can be carried.
format, but the listed format is applied in this study.
b) DEDUPLICATION TECHNIQUE
Deduplication is the process used to delete
redundant data copies and to maintain only one data
copy on cloud storage. With respect to data storage in
cloud, deduplication check undergoes the following
stages as shown in Figure 2.
DATA FILE NAME
DATA FILE FORMAT
Fig 3: Block Level Deduplication
DATA FILE CONTENT
File 1, File 2 and File 3 consists of 8 blocks,
each block represents 1MB. With deduplication, File
1 and File 3 have same content in each block, so the
KEY GENERATION content in File 3 is removed. In File 2, block A, B, C,
D and E have same content with File 1 block A, B, C,
Fig. 2: Deduplication Check D and E, thus block I, J and K in File 2 remain with
3MB. In Data de-duplication, the data blocks are
The data file input is contrasted with name, format checked to find the same data block. Thus, there is
and content. The data file would be removed if the more storage space.
parameters remain the same.
ISSN: 2348 – 8387 www.internationaljournalssrg.org Page 3
SSRG International Journal of Computer Science and Engineering (SSRG-IJCSE) – Volume 7 Issue 7 – July 2020
In block level segments are assigned using The cloud storage will store file in an encrypted
hash code which generates uniqueness to identify key as shown in Table 2.
chunks. This can be achieved via key generation
using encryption algorithm. Table 2: Expected Output Key Generation
c) KEY GENERATION (ENCRYPTION S/N ENCRYPTION KEY
ALGORITHM)
The user encrypts and saves the cloud key, and
encrypted message is stored in the data block. First, 1. Key 1
depositors use k key for encoding data, based on a
SymEnc symmetrical encryption method, to encode
the data file F. The F data key is extracted by a 2. Key 2
special hash function using a converging
cryptographer solution from the original F data file.
Any data uploaded to the cloud is saved and to reduce
Algorith 1: To Encrypt a Message (kaaniche, 2014) storage space in an encoded key. The program
1. Input: {f, H, SymEncg}, where f is the data monitors the presence of a new file in cloud storage
file, H is a one-way hash function and before storing the key.
SymEnc is a symmetric encryption
algorithm. d) WEB CLIENT
2. Output: (Cf, k) The deduplicate system uses a data key-keying
3. k = H(f); technique while the depositor produces the respective
4. Cf = SymEnc(f; k); enciphering key to encrypt data information before
5. return (Cf, k) saving on remote servers. This approach leads to
multiple encryption and reduction of the storage
To retrieve outsourced data file, the authorized capacity of the cloud provider.
recipient Uj extracts the enciphered file Cf key, using The KF enciphering key is extracted from one-Way
the public key k by the depositor Ui. hash-function H() when the data owner wants to store
a new data file F in the cloud. Please note that data is
Algorithm 2: To Shrink a file stored on a symmetrical algorithm on cloud servers
To reduce data file in a storage space R, ee denote with the derived KF key. The data owner must first
each key element by key.elt as; encrypt the data file to be outsourced. The key KF for
𝑘𝑒𝑦. 𝑒𝑙𝑡𝑖𝜖1,2,3 = {𝐶𝑖, 𝑅(𝐶𝑖 )}𝑖𝜖1,2,3 data identification is then generated. The file created
(3.1) (key) must be special in the database of Cloud
1. Input: {C2, skc} Provider. Client sends message to test the uniqueness
2. Output: C3 of created KF to start the storage process. The type of
1 file storage is as follows:
3. 𝐶3 = (𝐶3 )𝑠𝑘𝑐
4. return C3 a. ClientRequestVerif
In order to get a redirected C3 key element, the Cloud b. ResponseVerif
Service provider (CSP) gets the second key element c. ClientRequestStorage
(C3) element, and runs the ShrinKey algorithm as d. ResponseStorage
shown in Algorithm 2. a. ClientRequestVerif: This message checks whether
KF is unique. If the key is sent, the customer must
Subsequent ciphertext elements are shrink to reduce keep the provider secure. Upon completing the
the storage space. inspection, the cloudserver labels the requesting
company and only asks the customer to give allowed
Algorithm 3: To Decrypt a file access to the data owner.
1. Input: {Cf, k, SymEnc}
2. Output: f b. ResponseVerif: This message must be sent by the
3. f = SymEnc(Cf, k) cloud services provider to tell the customer that the re-
4. return f applied KF is in its databases.
Algorithm 4: To remove replicated file c. ClientRequestStorage: If the file does not exist on
1. Let HCf := hash(Cf ) be computed for once cloud servers, the client sends the encrypted and
and stored for later use. decrypted key KD using the registered users ' public
2. If Y1 = HCf , key.
3. set Y2 = accept,
4. Else Y2 = reject. d. ResponseStorage: This message confirms the data
storage capacity of the data owner.
ISSN: 2348 – 8387 www.internationaljournalssrg.org Page 4
SSRG International Journal of Computer Science and Engineering (SSRG-IJCSE) – Volume 7 Issue 7 – July 2020
IV. RESULTS uploaded with eighty files as Table 3 reveals. Every
Cloud storage allows different files to be user is authenticated prior to storing the file.
stored. We used audio, video, document in the form
of pdf and docx in this research. The cloud was
Table 3: Deduplication Check
USER FILE FILE FILE ENCRYPTED KEY DEDUPLICATI DUPLICAT
S|N SIZE FORMAT ON E KEY
BEFORE CHECK
UPLOAD
1 Joy.cey mp3 2xZQCz51dSc3weDq2gaH 100%
7.53MB NONE
2 Mike_mi mp4 BxLjDq5Am7BUWGXUkpPT 100%
13.63MB NONE
3 CJ Pdf OjteXOIcRB5UIY2XCmQF 100%
2.75MB NONE
4 CJ mp3 OagPxzNbaRx3dNPNXH36 100%
22.29MB NONE
5 Joy.cey 600KB Docx SMREyhnjN8qIy1Ne 100% NONE
6 Smart_ivy Docx Ckp82oNpIjsseKerWcge 100%
430KB NONE
7 Clement.uju 28.30MB mp4 JNWZZuxtnuG7zZc7aETU 100% NONE
8 Smart_ivy Pdf IHk0UXi6QTS0wUa9MJMU 100%
16.11MB NONE
The length of a key in bits is just a size specification. 16 bytes of space is needed with a 128-bit key. Table
4shows file size before and after uploading.
Table 4: Reduction in Storage Space due to Deduplication
S|N USER FILE UPLOADING FILE ENCRYPTED ENCRYPTION STORAGE
SIZE DURATION KEY BITS SPACE
BEFORE (SECOND) (FILE SIZE
UPLOAD AFTER
UPLOAD)
1 Joy.cey 2xZQCz51dSc3weDq2ga 128 16bytes
7.53MB 9
H
2 Mike_mi BxLjDq5Am7BUWGXU 128 16bytes
13.63MB 11 kpPT
3 CJ OjteXOIcRB5UIY2XCm 128 16bytes
2.75MB 6 QF
4 CJ OagPxzNbaRx3dNPNXH 128 16bytes
22.29MB 17 36
5 Joy.cey 600KB 4 SMREyhnjN8qIy1Ne 128 16bytes
6 Smart_iv Ckp82oNpIjsseKerWcge 128 16bytes
430KB 3
y
7 Clement.u JNWZZuxtnuG7zZc7aET 128 16bytes
ju 28.30MB 21 U
8 Smart_iv IHk0UXi6QTS0wUa9MJ 128 16bytes
y 16.11MB 14 MU
ISSN: 2348 – 8387 www.internationaljournalssrg.org Page 5
SSRG International Journal of Computer Science and Engineering (SSRG-IJCSE) – Volume 7 Issue 7 – July 2020
A. COMPARISON storage, the new file would be successfully stored in
cloud as found. It shows the list of files stored in
As data is encrypted, the proposed and current system cloud storage. Symmetric key encryption was used
supports data privacy. Nevertheless, as shown in and the key size was long enough to satisfy security
Table 5, the proposed system allows different users to requirement and has facilitated data protection in
access data. cloud.
Data was decrypted during download, data
Table 5: Comparison Analysis owner or any user could download the file using
System Deduplicatio Data Data access control assigned to users.
n Privacy access
VI. CONCLUSION
Heterogeneous Yes Encrypt Single We developed a data storage management
Data ion user system for deduplication of cloud computing in this
Storage Mana research Data duplication by block level
gement deduplication was prevented in cloud storage. The
with Deduplic cloud is based on the application of a data keying
ation in approach, while the remote server stores the associate
Cloud Comput encoding key for the encryption of data contents.
ing [3]
This approach leads to the same content being
encrypted several times and to the cloud provider's
Proposed Yes Encryp Multi-
storage capabilities being reduced. Data stored on
System tion user
access cloud servers based on a symmetrical algorithm was
shrunk to minimize space in storage using the
ShrinKey algorithm, and replicating file removal
V. DISCUSSION algorithm is used. The system has successfully
Data can be stored in documents images, removed duplicate data by searching for the presence
voice and pictures; this research is done in pdf and of encryption key in cloud storage. Thus, file in cloud
docx format using audio, video, image and data. In storage appeared in encrypted key with a storage
this study, we use audio, video, document in PDF and space of 16bytes thus storage space was minimized.
docx formats. The deduplication test is provided in The system supports data privacy of cloud users as
Table 3. The cloud was uploaded with 80 files. data stored inthe cloud was in an encrypted form.
Before storing files, each user has been authenticated.
All stored files have been translated into key and ACKNOWLEDGEMENTS
deduplication was performed on each of the keys. First and foremost, all praises and thanks be
When testing deduplication, duplicate key was to God Almighty for his unsurpassed favour and
removed. There was no duplicate key in the grace and for the successful completion of this
encrypted key column of the register, so the research work. I would like to express my deep and
deduplication was met. sincere gratitude to my supervisor, Dr. Daniel
Matthias and co-supervisor, Dr. Bennett E. O. for
A decrease in storage area is shown in Table giving me valuable guidance, encouragements, and
4. The table indicates the number of files uploaded, patience during this research. Also, I will in the same
the file size before uploading, the file transfer time vein genuinely appreciate my entire family my wife
and the file size after uploading. Each file has a Mrs. Juicy Chinaka Marcel and my child Master
different file size, video and audio files are higher in Daniel Chibuike Marcel, Miss Shalom Oluebebe
megabytes of 6 to 11 seconds, while the docx and pdf Marcel and Miss Joy Ozichukwu Marcel as well my
text files are in bytes of 2 to 3 seconds. siblings. I am grateful for the love, patience, support,
understanding and prayers towards the success of this
There are 16 bytes of space for 128-bit key study.
files have been accessed from various users, and data Finally, to my course mates, Tuase
are 20 in a cloud. The storage space of files was Emmanuel, Ene Donald and Charles Davidba, I
therefore reduced to a minimum. cannot forget the cooperation and team work that
existed between us, you guys are the best, I Thank
After selecting a file by a data owner (user),
God I was part of you.
the storage process starts. A file is stored and
processed; an imported file has been encrypted and
"ClientRequestVerif" checks that the cloud storage
key is available, A message has been returned back to
the data owner to suggest that the file "exists already".
However, if there exist no duplicate key in the cloud
ISSN: 2348 – 8387 www.internationaljournalssrg.org Page 6
SSRG International Journal of Computer Science and Engineering (SSRG-IJCSE) – Volume 7 Issue 7 – July 2020
REFERENCES
[1] Chen, R. “Secure Data Storage and Retrieval in Cloud [9] Drago, I., Mellia, M., Munafo, M., Sperotto, A., Sadre, R
Computing. Doctor of Philosophy thesis, School of and Pras, A. Inside Dropbox. The ACM Conference, 481.
Computing and Information Technology”, University of (2012).
Wollongong. http://www.ro.uow.edu.au/theses/4648,(2016). [10] Geel, M. Cloud Storage: File Hosting and Synchronisation
[2] Kaanichie, N. “Cloud Data Storage Security based on 2.0. [Online] Available at:
Cryptographic Mechanisms”. Telecom Sudparis in https://www.vis.ethz.ch/de/visionen/pdfs/2012/visionen_20
Partnership with Pierre Et Marie Curie University. (2014). 12_3.pdf?end=15&start=11, (2013).
[3] Sangeetha, A and Geetha, K. “Heterogeneous Data Storage [11] Abu-Libdeh, H., Princehouse L and Weatherspoon, H
Management with Deduplication in Cloud Computing.” “Racs: a case for cloud storage diversity,” in Proceedings of
Asian Journal of Applied Science and Technology (AJAST) the 1st ACM symposium on Cloud computing, ser.
(Open Access Quarterly International Journal) 2(2), pp SoCC ’10, pp(229–240). [Online]. Available:
(840-845). (2018). http://www.cs.cornell.edu/projects/racs/pubs/racs-
[4] Li, J., Jia, C., Li, J and Liu, Z. “A Novel Framework for socc2010.pdf, (2010).
Outsourcing and Sharing Searchable Encrypted Data on [12] Bessani, A., Correia, M., Quaresma, B., André, F and Sousa,
Hybrid Cloud,” Fourth International Conference on P. “Depsky: dependable and secure storage in a cloud-of-
Intelligent Networking and Collaborative Systems, pp(1–7). clouds,” in Proceedings of the sixth conference on
(2012). Computer systems, ser. EuroSys ’11. ACM, pp(31–46).
[5] Yan, Z., Ding, W. X and Zhu, H. Q. "A scheme to manage [Online]. Available: http://www.gsd.inesc-
encrypted data storage with deduplication in cloud," in id.pt/~mpc/pubs/eurosys219-bessani.pdf, (2011).
Proc. of ICA3PP, pp (547-561), Springer, (2015). [13] Bermbach, D., Klems, M., Tai, S and Menzel, M.
[6] Bethencourt, J., Sahai, A and Waters, B. "Ciphertext-policy “Metastorage: A federated cloud storage system to manage
attribute-based encryption," in Proc. of IEEE Symp. Secure consistency-latency tradeoffs,” in Cloud Computing
Privacy (07), pp(321-334), (2007). (CLOUD), IEEE International Conference on, pp (452–459),
[7] Hur, J., Koo, D., Shin, Y and Kang, K. “Secure Data (2011).
Deduplication with Dynamic Ownership Management in [14] Blount, M., McGregor, C., James, A., Sow, D.,
Cloud Storage,” IEEE Trans. Knowl.Data Eng., 28, (11), pp Kamaleswaran, R., Tuuha, S., Percival, Jand Percival, N. On
(3113-3125), (2016). the Integration of an Artifact System and a Real-Time
[8] Singh, A and Tech, G. “Server-Storage Virtualization: Healthcare Analytics System.In Proceedings of the 1st ACM
Integration and Load Balancing in Data Centers,” In International Health Informatics Symposium,Arlington,
International Conference for High Performance Computing, Virginia, USA.pp (647–655), (2010).
Networking, Storage and Analysis, pp(1-12), (2008).
ISSN: 2348 – 8387 www.internationaljournalssrg.org Page 7
You might also like
- Distributed Data Storage Systems - From RAID To BlockchainsDocument6 pagesDistributed Data Storage Systems - From RAID To BlockchainsanevelkoskaNo ratings yet
- DAC Election Terminology DictionaryDocument170 pagesDAC Election Terminology DictionaryStefanie DoseNo ratings yet
- Basic Computer Terminology - FormDocument4 pagesBasic Computer Terminology - Formapi-260638744No ratings yet
- Seiger 2011Document4 pagesSeiger 2011Thati PonceNo ratings yet
- Seed Block Algorithm A Remote Smart Data Back-Up Technique For Cloud ComputingDocument5 pagesSeed Block Algorithm A Remote Smart Data Back-Up Technique For Cloud ComputingKarthik BGNo ratings yet
- Encrypted Data Management With Deduplication in Cloud ComputingDocument13 pagesEncrypted Data Management With Deduplication in Cloud ComputingsharathNo ratings yet
- 1.1 Working of Cloud ComputingDocument76 pages1.1 Working of Cloud ComputingTharun Theja ReddyNo ratings yet
- Iaetsd Controlling Data Deuplication in Cloud StorageDocument6 pagesIaetsd Controlling Data Deuplication in Cloud StorageiaetsdiaetsdNo ratings yet
- Seed Block AlgorithmDocument5 pagesSeed Block AlgorithmSandeep Reddy KankanalaNo ratings yet
- A Design of Lightweight Secure Data SharingDocument6 pagesA Design of Lightweight Secure Data SharingEditor IJTSRDNo ratings yet
- IJETR2137Document4 pagesIJETR2137anil kasotNo ratings yet
- Data MangementDocument4 pagesData Mangementessid sabraNo ratings yet
- 2018 Conferecne-Asymmetric Secure Storage Scheme For Big Data On Multiple Cloud ProvidersDocument5 pages2018 Conferecne-Asymmetric Secure Storage Scheme For Big Data On Multiple Cloud ProvidersRajesh KumarNo ratings yet
- Cloud PDFDocument5 pagesCloud PDFhelloeveryNo ratings yet
- An Efficient Data Compression and Storage Technique With Key Management Authentication in Cloud ComputingDocument9 pagesAn Efficient Data Compression and Storage Technique With Key Management Authentication in Cloud ComputingRevathiNo ratings yet
- Study On Cloud Storage and Its Issues in Cloud ComputingDocument6 pagesStudy On Cloud Storage and Its Issues in Cloud ComputingNellai SamuraiNo ratings yet
- IJSRST - Paper - Survey Ppaer B-15Document4 pagesIJSRST - Paper - Survey Ppaer B-15cyan whiteNo ratings yet
- Cloud JointPhysicalLayerProject Dotnet 09112158Document10 pagesCloud JointPhysicalLayerProject Dotnet 0911215818ITR028 Janaranjan ENo ratings yet
- DropStore A Secure Backup System Using Multi-Cloud and Fog ComputingDocument10 pagesDropStore A Secure Backup System Using Multi-Cloud and Fog ComputingPremkNo ratings yet
- Cloud: Figure - The Symbol Used To Denote The Boundary of A Cloud EnvironmentDocument27 pagesCloud: Figure - The Symbol Used To Denote The Boundary of A Cloud Environmentαηαητ αφπαωαΙNo ratings yet
- Studies On Application of Cloud Computing Techniques in GIS: YANG Jinnan, WU ShengDocument4 pagesStudies On Application of Cloud Computing Techniques in GIS: YANG Jinnan, WU ShengRummat Fateen TazmeeNo ratings yet
- Attribute-Based Access Control With Constant-Size Ciphertext in Cloud ComputingDocument14 pagesAttribute-Based Access Control With Constant-Size Ciphertext in Cloud ComputingGateway ManagerNo ratings yet
- Analysis of Security Algorithms in Cloud ComputingDocument6 pagesAnalysis of Security Algorithms in Cloud ComputingInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- A Study On Secure Data Storage in Public Clouds: T. Dhanur Bavidhira C. SelviDocument5 pagesA Study On Secure Data Storage in Public Clouds: T. Dhanur Bavidhira C. SelviEditor IJRITCCNo ratings yet
- SSRN Id3649074Document3 pagesSSRN Id3649074Riva MakNo ratings yet
- What Is Cloud Computing? Cloud Computing Is The Use of Computing Resources (Hardware andDocument74 pagesWhat Is Cloud Computing? Cloud Computing Is The Use of Computing Resources (Hardware andSanda MounikaNo ratings yet
- An Assignment On Cloud ComputingDocument5 pagesAn Assignment On Cloud ComputingMD Monowar Ul IslamNo ratings yet
- Enhanced Secure Data Sharing Over Cloud Using ABE AlgorithmDocument4 pagesEnhanced Secure Data Sharing Over Cloud Using ABE Algorithmcyan whiteNo ratings yet
- Compusoft, 2 (12), 404-409 PDFDocument6 pagesCompusoft, 2 (12), 404-409 PDFIjact EditorNo ratings yet
- (IJCST-V10I5P53) :MR D Purushothaman, M NaveenDocument8 pages(IJCST-V10I5P53) :MR D Purushothaman, M NaveenEighthSenseGroupNo ratings yet
- A Study On Review and Analysis of Cloud, Fog and Edge Computing PlatformsDocument7 pagesA Study On Review and Analysis of Cloud, Fog and Edge Computing PlatformsInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Cloud ComputingDocument6 pagesCloud Computingshariful islamNo ratings yet
- Data Storage in Cloud ComputingDocument6 pagesData Storage in Cloud ComputingIsrat6730 JahanNo ratings yet
- Data Storage 2pdfDocument5 pagesData Storage 2pdfIsrat6730 JahanNo ratings yet
- Seed Block Algorithm A Remote Smart DataDocument7 pagesSeed Block Algorithm A Remote Smart DataChandan Athreya.SNo ratings yet
- The VPC Offers The Function of The PrivateDocument3 pagesThe VPC Offers The Function of The PrivatedaliasobhiNo ratings yet
- Achieving Availability - ijaeSTDocument6 pagesAchieving Availability - ijaeSTiserpNo ratings yet
- Data Deduplication Strategies in Cloud ComputingDocument5 pagesData Deduplication Strategies in Cloud ComputingInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Survey of Cloud ComputingDocument13 pagesSurvey of Cloud ComputingijwscNo ratings yet
- Cloud Databases: A Paradigm Shift in DatabasesDocument7 pagesCloud Databases: A Paradigm Shift in Databasessimrika thakuriNo ratings yet
- Role Based Access Control Model (RBACM) With Efficient Genetic Algorithm (GA) For Cloud Data Encoding, Encrypting and ForwardingDocument8 pagesRole Based Access Control Model (RBACM) With Efficient Genetic Algorithm (GA) For Cloud Data Encoding, Encrypting and ForwardingdbpublicationsNo ratings yet
- 8.IJAEST Vol No 5 Issue No 2 Achieving Availability, Elasticity and Reliability of The Data Access in Cloud Computing 150 155Document6 pages8.IJAEST Vol No 5 Issue No 2 Achieving Availability, Elasticity and Reliability of The Data Access in Cloud Computing 150 155noddynoddyNo ratings yet
- Data Storage in Cloud ComputingDocument6 pagesData Storage in Cloud ComputingswathyNandhiniNo ratings yet
- Rsa SecurityDocument6 pagesRsa SecuritySumana SikdarNo ratings yet
- Clearing The Clouds On Cloud Computing S-51490823 PDFDocument6 pagesClearing The Clouds On Cloud Computing S-51490823 PDFFisehaNo ratings yet
- Block Level Data Deduplication For Faster Cloud BackupDocument5 pagesBlock Level Data Deduplication For Faster Cloud BackupPradyumna ReddyNo ratings yet
- Comp Sci - Cloud - Awfa HasanDocument10 pagesComp Sci - Cloud - Awfa HasanTJPRC PublicationsNo ratings yet
- Deduplication on Encrypted Data in Cloud ComputingDocument4 pagesDeduplication on Encrypted Data in Cloud ComputingInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Enhanced Secure Data Sharing Over Cloud Using ABE AlgorithmDocument4 pagesEnhanced Secure Data Sharing Over Cloud Using ABE Algorithmcyan whiteNo ratings yet
- Efficient Technique To Optimize Cloud Storage in Multi-Tenant EnvironmentDocument5 pagesEfficient Technique To Optimize Cloud Storage in Multi-Tenant EnvironmentIJCERT PUBLICATIONSNo ratings yet
- Encryption in Cloud Storage and Demonstration Computer Science EssayDocument34 pagesEncryption in Cloud Storage and Demonstration Computer Science Essaysohan hazraNo ratings yet
- Enhanced-Elliptic Curve Diffie Hellman Algorithm For Secure Data Storage in Multi Cloud EnvironmentDocument8 pagesEnhanced-Elliptic Curve Diffie Hellman Algorithm For Secure Data Storage in Multi Cloud EnvironmentVijay ThalaNo ratings yet
- Overview of Cloud StorageDocument4 pagesOverview of Cloud StorageSpidey McuNo ratings yet
- A Study On Application-Aware Local-Global Source Deduplication For Cloud Backup Services of Personal StorageDocument3 pagesA Study On Application-Aware Local-Global Source Deduplication For Cloud Backup Services of Personal StorageInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- What Are Data Centers? How They Work and How They Are Changing in Size and ScopeDocument8 pagesWhat Are Data Centers? How They Work and How They Are Changing in Size and ScopeIT NYPNo ratings yet
- BFC: High-Performance Distributed Big-File Cloud Storage Based On Key-Value StoreDocument10 pagesBFC: High-Performance Distributed Big-File Cloud Storage Based On Key-Value StoredbpublicationsNo ratings yet
- 69 - Developing Middleware For Hybrid Cloud Computing ArchitecturesDocument3 pages69 - Developing Middleware For Hybrid Cloud Computing ArchitecturesLARS Projetos & Soluções em Engenharia ElétricaNo ratings yet
- A Survey On Security Challenges in Cloud Computing - Issues - Threats - andDocument41 pagesA Survey On Security Challenges in Cloud Computing - Issues - Threats - andmiguex_reloadedNo ratings yet
- Cloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingFrom EverandCloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingNo ratings yet
- Data Mesh: Building Scalable, Resilient, and Decentralized Data Infrastructure for the Enterprise Part 1From EverandData Mesh: Building Scalable, Resilient, and Decentralized Data Infrastructure for the Enterprise Part 1No ratings yet
- Cloud: Get All The Support And Guidance You Need To Be A Success At Using The CLOUDFrom EverandCloud: Get All The Support And Guidance You Need To Be A Success At Using The CLOUDNo ratings yet
- 15TV016 - Software Packages Follow-Up For GN1G Chassis (REVISION 29)Document4 pages15TV016 - Software Packages Follow-Up For GN1G Chassis (REVISION 29)taviNo ratings yet
- AN - 259 FT800 Example With 8-Bit MCUDocument24 pagesAN - 259 FT800 Example With 8-Bit MCUreemaNo ratings yet
- Victorian AgeDocument2 pagesVictorian AgeBaloch Karawan100% (1)
- The Importance of Being ErnestDocument9 pagesThe Importance of Being ErnestLaurentiu CovrescuNo ratings yet
- The Lexical Features of English Advertisement: AbstractDocument3 pagesThe Lexical Features of English Advertisement: AbstractRegina ApsalyamovaNo ratings yet
- The Structure of Society in MahabharataDocument8 pagesThe Structure of Society in MahabharataSushant KishoreNo ratings yet
- Bjorkman and Zeijlstra 2016Document65 pagesBjorkman and Zeijlstra 2016Anahí Lopez FavilliNo ratings yet
- Written Test in English - Grade 9: I. Choose A, B, C, D To Complete The Following Sentences (6M)Document1 pageWritten Test in English - Grade 9: I. Choose A, B, C, D To Complete The Following Sentences (6M)api-3727838No ratings yet
- Client LogDocument7 pagesClient LogAlexander MoranteNo ratings yet
- Lit1021 1025Document2 pagesLit1021 1025api-237641032No ratings yet
- Reading Sample Sap Bw4hana The Comprehensive GuideDocument41 pagesReading Sample Sap Bw4hana The Comprehensive Guidetenken13No ratings yet
- Bailey K A Three Level Measurement ModelDocument21 pagesBailey K A Three Level Measurement ModelprimosichNo ratings yet
- Iep Scavenger HuntDocument3 pagesIep Scavenger Huntapi-511044803No ratings yet
- DLP in English 9Document3 pagesDLP in English 9Kris LabiosNo ratings yet
- Linear Algebra, Terence Tao UCLA 2002Document243 pagesLinear Algebra, Terence Tao UCLA 2002PedroNo ratings yet
- Colour Lab Glass ApparatusDocument3 pagesColour Lab Glass ApparatusJo CaubinNo ratings yet
- Grade - 9 - MATHEMATICS - 2nd - Summative TestDocument2 pagesGrade - 9 - MATHEMATICS - 2nd - Summative Testkoi80% (5)
- Derrida, Jacques. Te Work of Mourning PDFDocument135 pagesDerrida, Jacques. Te Work of Mourning PDFRemmy_ANo ratings yet
- Quiz-1 Functions MathematicsDocument3 pagesQuiz-1 Functions MathematicssikkaNo ratings yet
- Cal 11 q3 0701 FinalDocument24 pagesCal 11 q3 0701 FinalMira Rochenie CuranNo ratings yet
- Should Writers Use They Own EnglishDocument10 pagesShould Writers Use They Own EnglishYira Melissa CASTILLO RAMOSNo ratings yet
- Task 1: Pengandaian Diikuti SaranDocument4 pagesTask 1: Pengandaian Diikuti Sarancewe moodyNo ratings yet
- SL-VCH eDocument1 pageSL-VCH eAjay MayalNo ratings yet
- Observation 2Document4 pagesObservation 2api-526299421No ratings yet
- 4947 19328 2 PB PDFDocument6 pages4947 19328 2 PB PDFWassemAbbasNo ratings yet
- Mathematics SL - Applications and Interpretation - OXFORD 2019 (ESTIMACION)Document8 pagesMathematics SL - Applications and Interpretation - OXFORD 2019 (ESTIMACION)zaraarciniegascNo ratings yet
- How To Use INSERT in Psycopg2 Connection PoolingDocument3 pagesHow To Use INSERT in Psycopg2 Connection Poolingleonard1971No ratings yet
- Ratgpt: Turning Online Llms Into Proxies For Malware AttacksDocument6 pagesRatgpt: Turning Online Llms Into Proxies For Malware AttacksimeemkhNo ratings yet