Professional Documents
Culture Documents
0 ratings0% found this document useful (0 votes)
295 viewsDiffie-Hellman Key Exchange
Diffie-Hellman Key Exchange
Uploaded by
deekshantDiffie–Hellman key exchange is a method for securely exchanging cryptographic keys over a public channel. It allows two parties that have no prior knowledge of each other to jointly establish a shared secret key. Each party generates a public/private key pair and computes a shared secret using both keys, arriving at the same secret value. This key can then be used to encrypt subsequent communications over the insecure public channel.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You might also like
- Super Secreto - The Third Epoch of Cryptography: Multiple, exponential, quantum-secure and above all, simple and practical Encryption for EveryoneFrom EverandSuper Secreto - The Third Epoch of Cryptography: Multiple, exponential, quantum-secure and above all, simple and practical Encryption for EveryoneNo ratings yet
- Diffie-Hellman Key Exchange PDFDocument6 pagesDiffie-Hellman Key Exchange PDFZxzxzxz007No ratings yet
- Diffie-Hellman and Its Application in Security Protocols: ISO 9001:2008 CertifiedDocument5 pagesDiffie-Hellman and Its Application in Security Protocols: ISO 9001:2008 CertifiedHarish KumarNo ratings yet
- Foundations of Computer Security: Lecture 52: Diffie-Hellman Key ExchangeDocument6 pagesFoundations of Computer Security: Lecture 52: Diffie-Hellman Key ExchangegingeevimalNo ratings yet
- Prac V1Document4 pagesPrac V1Niket BhaleraoNo ratings yet
- Diffie-Hellman Key ExchangeDocument6 pagesDiffie-Hellman Key ExchangeMilica LukicNo ratings yet
- Diffie-Hellman Key ExchangeDocument5 pagesDiffie-Hellman Key ExchangeNikitaNo ratings yet
- Diffie Hellman WriteupDocument3 pagesDiffie Hellman WriteupSumitThoratNo ratings yet
- The Diffie-Hellman Algorithm: Dr. Amjad Ali Department of Computer Science COMSATS University Islamabad, Lahore CampusDocument14 pagesThe Diffie-Hellman Algorithm: Dr. Amjad Ali Department of Computer Science COMSATS University Islamabad, Lahore CampusShaheer ArshadNo ratings yet
- Odlyzko1 PsDocument10 pagesOdlyzko1 PsAmador Perez LopezNo ratings yet
- Diffie Hellman PDFDocument6 pagesDiffie Hellman PDFsushmaNo ratings yet
- Diffie HellmanDocument1 pageDiffie HellmanAhmed HeshamNo ratings yet
- Key Concepts: ConfidentialityDocument30 pagesKey Concepts: ConfidentialityManiya KadamNo ratings yet
- Wireless Comm Systems 4Document37 pagesWireless Comm Systems 4abdulsahibNo ratings yet
- Public-Key Cryptosystems, I. Key Exchange, Knapsack, RSADocument58 pagesPublic-Key Cryptosystems, I. Key Exchange, Knapsack, RSATom_Babej_5778No ratings yet
- Diffie Hellman Key Exchange Algorithm For Key GenerationDocument5 pagesDiffie Hellman Key Exchange Algorithm For Key Generationshahrbano 14No ratings yet
- 4.2. Cryptographic Coding (Part 2)Document27 pages4.2. Cryptographic Coding (Part 2)ReachNo ratings yet
- Assignment No 6Document3 pagesAssignment No 6spNo ratings yet
- Lecture 2 C Public Key CryptographyDocument27 pagesLecture 2 C Public Key CryptographyKedir MohammedNo ratings yet
- CHAPTER 5: Public-Key Cryptography I. RSA: Two Different KeysDocument43 pagesCHAPTER 5: Public-Key Cryptography I. RSA: Two Different KeysMin KhantNo ratings yet
- Discrete Mathematics AssignmentDocument12 pagesDiscrete Mathematics AssignmentLalitSisodiaNo ratings yet
- Elliptic Curve CryptographyDocument30 pagesElliptic Curve CryptographyAsha MuruganNo ratings yet
- Deffiehellman AlgoDocument6 pagesDeffiehellman Algoparidhiagarwal129No ratings yet
- GP Report (Key Exchange)Document20 pagesGP Report (Key Exchange)Manish 'MySt' SinghNo ratings yet
- PR5 Diffie Hellman FinalDocument4 pagesPR5 Diffie Hellman FinalprafullaNo ratings yet
- Diffie HellmanDocument8 pagesDiffie Hellmanabdulrahim221298No ratings yet
- Group B-Assignment No. 1 : CNSL Te-ItDocument3 pagesGroup B-Assignment No. 1 : CNSL Te-ItPriyanshu AgrawalNo ratings yet
- Diffie Hellman AlgorithmDocument11 pagesDiffie Hellman Algorithmjoxy johnNo ratings yet
- P4 - The Keystone - Encryption v0Document11 pagesP4 - The Keystone - Encryption v0Thierry IRIENo ratings yet
- Aim: To Implement Diffiehellman Key Exchange Protocol. Theory: Diffiehellman Key Exchange Is A Cryptographic Protocol That Allows TwoDocument3 pagesAim: To Implement Diffiehellman Key Exchange Protocol. Theory: Diffiehellman Key Exchange Is A Cryptographic Protocol That Allows Twocreative_g33kNo ratings yet
- Group Theory in CS: Cryptography, Diffie-Hellman, and Elliptic CurvesDocument5 pagesGroup Theory in CS: Cryptography, Diffie-Hellman, and Elliptic CurvesMihir VahanwalaNo ratings yet
- Cryptography 3Document25 pagesCryptography 3Venera MakhambayevaNo ratings yet
- IS TheoryDocument14 pagesIS Theoryapi-26548538No ratings yet
- Digital ElectronicsDocument16 pagesDigital ElectronicsRobin RohitNo ratings yet
- Diffie Hellman Algorithm RileyDocument16 pagesDiffie Hellman Algorithm RileySRC ExamNo ratings yet
- Diffie Hellman Algorithm RileyDocument16 pagesDiffie Hellman Algorithm RileymarioNo ratings yet
- Diffie Hellman Algorithm RileyDocument16 pagesDiffie Hellman Algorithm RileyShiva Prasad100% (1)
- Exp 05Document4 pagesExp 0548Nara Amit GopalNo ratings yet
- Lec 7 - RSADocument41 pagesLec 7 - RSAMoOez InamNo ratings yet
- Cryptography and Network SecurityDocument30 pagesCryptography and Network SecuritysanjuNo ratings yet
- IT Hash FunctionsDocument47 pagesIT Hash Functionscvdm_vio614No ratings yet
- Cryptographic PrimitivesDocument59 pagesCryptographic Primitivesposer4uNo ratings yet
- Network Security - CryptographyDocument4 pagesNetwork Security - CryptographymississipNo ratings yet
- Public Cryptosystem RDocument12 pagesPublic Cryptosystem RgamerNo ratings yet
- TBS Answer Question No 1Document2 pagesTBS Answer Question No 1deepNo ratings yet
- Boneh-Venkatesan1996 Chapter HardnessOfComputingTheMostSignDocument14 pagesBoneh-Venkatesan1996 Chapter HardnessOfComputingTheMostSignmathmaxfysNo ratings yet
- Encryption TechniquesDocument6 pagesEncryption TechniquesMujahida EhsanNo ratings yet
- Security of C.N.: By: Eng. Ahmed K. DarajDocument8 pagesSecurity of C.N.: By: Eng. Ahmed K. DarajAHMED DARAJNo ratings yet
- Rsa (Cryptosystem) : RsaisaDocument10 pagesRsa (Cryptosystem) : RsaisaXerus AnatasNo ratings yet
- CHAPTER 05 - Public-Key CryptographyDocument29 pagesCHAPTER 05 - Public-Key CryptographyPNo ratings yet
- The Science of Encryption: Prime Numbers and Mod N ArithmeticDocument6 pagesThe Science of Encryption: Prime Numbers and Mod N ArithmeticManuel Aleixo LeiriaNo ratings yet
- Key Management Other Public Key Cryptosystems: - The Golden Bough, Sir James George FrazerDocument29 pagesKey Management Other Public Key Cryptosystems: - The Golden Bough, Sir James George FrazerLavanya_123No ratings yet
- Book 2 CryptographyDocument17 pagesBook 2 CryptographyGajanan GitteNo ratings yet
- Lecture 3 RSADocument7 pagesLecture 3 RSAAHMED DARAJNo ratings yet
- Class+Notes5 Diffie+Hellman+Key+Exchange+AlgorithmDocument2 pagesClass+Notes5 Diffie+Hellman+Key+Exchange+Algorithmk5c6hdvmq7No ratings yet
- Chapter 3 Public Key Cryptography PrinciplesDocument22 pagesChapter 3 Public Key Cryptography PrinciplesZoe KhanNo ratings yet
- Cryptography and Network SecurityDocument25 pagesCryptography and Network SecurityViraj KumarNo ratings yet
- Diffie-Hellman Case Study - 1DS18TE075Document10 pagesDiffie-Hellman Case Study - 1DS18TE075Gaurav AgarwalNo ratings yet
- ShevchukDocument13 pagesShevchukunbanmebeast727No ratings yet
- Montessori Stamp Game MaterialDocument15 pagesMontessori Stamp Game Materialbrunerteach100% (1)
- Data Driven Modeling For Energy Consumption Prediction in Smart Buildings PDFDocument8 pagesData Driven Modeling For Energy Consumption Prediction in Smart Buildings PDFRicardo Chegwin HillembrandNo ratings yet
- Word Sense Disambiguation: by Under The Guidance ofDocument99 pagesWord Sense Disambiguation: by Under The Guidance ofgadidheerajreddy.20.itNo ratings yet
- 3 Connected Bodies: SolutionDocument34 pages3 Connected Bodies: SolutionHerbertNo ratings yet
- Masons RuleDocument2 pagesMasons RulemohamedhegaNo ratings yet
- Python modules-XIDocument9 pagesPython modules-XIDevanshi AwasthiNo ratings yet
- Identification, Prediction and Detection of The Process Fault in A Cement Rotary Kiln by Locally Linear Neuro-Fuzzy TechniqueDocument7 pagesIdentification, Prediction and Detection of The Process Fault in A Cement Rotary Kiln by Locally Linear Neuro-Fuzzy TechniqueAnonymous NxpnI6jCNo ratings yet
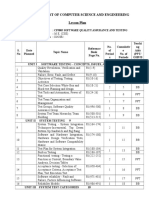
- Cp5005 Sqat LsDocument3 pagesCp5005 Sqat LsKeerthi KaNo ratings yet
- Trigonometry Unit AssignmentDocument3 pagesTrigonometry Unit AssignmentDr. Gopalakrishnan GNo ratings yet
- Theorem Environments: L TEX For Math and ScienceDocument14 pagesTheorem Environments: L TEX For Math and SciencejaxbaiadNo ratings yet
- Final Quiz 2Document4 pagesFinal Quiz 2Erick GarciaNo ratings yet
- Unit 2Document30 pagesUnit 2Bhavesh AjmeraaNo ratings yet
- Class 6 Yearly Plan 2022-23Document22 pagesClass 6 Yearly Plan 2022-23Srivatsan Parthasarathy100% (1)
- Engineering Is The Application of Mathematics, Empirical Evidence and Scientific, EconomicDocument5 pagesEngineering Is The Application of Mathematics, Empirical Evidence and Scientific, EconomicKylle BedisNo ratings yet
- Boiler Heat FluxDocument8 pagesBoiler Heat FluxMubarik Ali100% (1)
- Problem: CommentsDocument2 pagesProblem: CommentsMatheus Henrique Pavani PachecoNo ratings yet
- 5-E Model Lesson PlanDocument3 pages5-E Model Lesson Planapi-418555834No ratings yet
- Math AA HL Version E P1 Worked SolutionsDocument15 pagesMath AA HL Version E P1 Worked Solutionsjoelkota018No ratings yet
- 09 - Chapter 1 PDFDocument35 pages09 - Chapter 1 PDFJhuma DeyNo ratings yet
- SSC CPO SI Detailed Syllabus 2022Document3 pagesSSC CPO SI Detailed Syllabus 2022jitendra mishraNo ratings yet
- Measuring S-Parameters - The First 50 YearsDocument15 pagesMeasuring S-Parameters - The First 50 YearsScribdFgNo ratings yet
- Analysis of Maths by Theosophical ReductionDocument37 pagesAnalysis of Maths by Theosophical ReductionMarkMadMunkiNo ratings yet
- Hobsonajjustthemaths20021296smcetp PDFDocument1,296 pagesHobsonajjustthemaths20021296smcetp PDFAIvan DCam G0% (1)
- Prob StatsDocument80 pagesProb StatsRahul SaxenaNo ratings yet
- String Theory Vs Loop Quantum GravityDocument9 pagesString Theory Vs Loop Quantum Gravityapi-241908559No ratings yet
- Panning in AI PPT SelfDocument17 pagesPanning in AI PPT Selfruff ianNo ratings yet
- Decision Theory and The Normal Distribution: Eaching Uggestions M3-5Document3 pagesDecision Theory and The Normal Distribution: Eaching Uggestions M3-5José Manuel Orduño VillaNo ratings yet
- Design of VCBDocument14 pagesDesign of VCBAniruth100% (1)
- Bessel PDFDocument40 pagesBessel PDFscabero16No ratings yet
- Introduction To Algorithms: Divide and ConquerDocument38 pagesIntroduction To Algorithms: Divide and Conquerchakshu agarwalNo ratings yet
Diffie-Hellman Key Exchange
Diffie-Hellman Key Exchange
Uploaded by
deekshant0 ratings0% found this document useful (0 votes)
295 views7 pagesDiffie–Hellman key exchange is a method for securely exchanging cryptographic keys over a public channel. It allows two parties that have no prior knowledge of each other to jointly establish a shared secret key. Each party generates a public/private key pair and computes a shared secret using both keys, arriving at the same secret value. This key can then be used to encrypt subsequent communications over the insecure public channel.
Original Description:
Original Title
Diffie-hillman
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentDiffie–Hellman key exchange is a method for securely exchanging cryptographic keys over a public channel. It allows two parties that have no prior knowledge of each other to jointly establish a shared secret key. Each party generates a public/private key pair and computes a shared secret using both keys, arriving at the same secret value. This key can then be used to encrypt subsequent communications over the insecure public channel.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
Download as docx, pdf, or txt
0 ratings0% found this document useful (0 votes)
295 views7 pagesDiffie-Hellman Key Exchange
Diffie-Hellman Key Exchange
Uploaded by
deekshantDiffie–Hellman key exchange is a method for securely exchanging cryptographic keys over a public channel. It allows two parties that have no prior knowledge of each other to jointly establish a shared secret key. Each party generates a public/private key pair and computes a shared secret using both keys, arriving at the same secret value. This key can then be used to encrypt subsequent communications over the insecure public channel.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
Download as docx, pdf, or txt
You are on page 1of 7
Diffie–Hellman key exchange
From Wikipedia, the free encyclopedia
Jump to navigation Jump to search
In the Diffie–Hellman key exchange scheme,
each party generates a public/private key pair
and distributes the public key. After obtaining
an authentic copy of each other's public keys,
Alice and Bob can compute a shared secret
offline. The shared secret can be used, for
instance, as the key for a symmetric cipher.
Diffie–Hellman key exchange[nb 1] is a method
of securely exchanging cryptographic keys
over a public channel and was one of the first
public-key protocols as conceived by Ralph
Merkle and named after Whitfield Diffie and
Martin Hellman.[1][2] DH is one of the earliest
practical examples of public key exchange
implemented within the field of cryptography.
Published in 1976 by Diffie and Hellman, this
is the earliest publicly known work that
proposed the idea of a private key and a
corresponding public key.
Traditionally, secure encrypted
communication between two parties required
that they first exchange keys by some secure
physical means, such as paper key lists
transported by a trusted courier. The Diffie–
Hellman key exchange method allows two
parties that have no prior knowledge of each
other to jointly establish a shared secret key
over an insecure channel. This key can then be
used to encrypt subsequent communications
using a symmetric-key cipher.
Diffie–Hellman is used to secure a variety of
Internet services. However, research published
in October 2015 suggests that the parameters
in use for many DH Internet applications at
that time are not strong enough to prevent
compromise by very well-funded attackers,
such as the security services of some
countries.[3]
The scheme was published by Whitfield Diffie
and Martin Hellman in 1976,[2] but in 1997 it
was revealed that James H. Ellis,[4] Clifford
Cocks, and Malcolm J. Williamson of GCHQ,
the British signals intelligence agency, had
previously shown in 1969[5] how public-key
cryptography could be achieved.[6]
Although Diffie–Hellman key agreement itself
is a non-authenticated key-agreement protocol,
it provides the basis for a variety of
authenticated protocols, and is used to provide
forward secrecy in Transport Layer Security's
ephemeral modes (referred to as EDH or DHE
depending on the cipher suite).
The method was followed shortly afterwards
by RSA, an implementation of public-key
cryptography using asymmetric algorithms.
Expired U.S. Patent 4,200,770 from 1977
describes the now public-domain algorithm. It
credits Hellman, Diffie, and Merkle as
inventors.
General overview
Illustration of the concept behind Diffie–
Hellman key exchange
Diffie–Hellman key exchange establishes a
shared secret between two parties that can be
used for secret communication for exchanging
data over a public network. An analogy
illustrates the concept of public key exchange
by using colors instead of very large numbers:
The process begins by having the two parties,
Alice and Bob, publicly agree on an arbitrary
starting color that does not need to be kept
secret (but should be different every time[3]).
In this example, the color is yellow. Each
person also selects a secret color that they
keep to themselves – in this case, red and
blue-green. The crucial part of the process is
that Alice and Bob each mix their own secret
color together with their mutually shared
color, resulting in orange-tan and light-blue
mixtures respectively, and then publicly
exchange the two mixed colors. Finally, each
of them mixes the color they received from the
partner with their own private color. The result
is a final color mixture (yellow-brown in this
case) that is identical to the partner's final
color mixture.
If a third party listened to the exchange, it
would only know the common color (yellow)
and the first mixed colors (orange-tan and
light-blue), but it would be difficult for this
party to determine the final secret color
(yellow-brown). Bringing the analogy back to
a real-life exchange using large numbers
rather than colors, this determination is
computationally expensive. It is impossible to
compute in a practical amount of time even for
modern supercomputers.
Cryptographic explanation
The simplest and the original
implementation[2] of the protocol uses the
multiplicative group of integers modulo p,
where p is prime, and g is a primitive root
modulo p. These two values are chosen in this
way to ensure that the resulting shared secret
can take on any value from 1 to p–1. Here is
an example of the protocol, with non-secret
values in blue, and secret values in red.
1. Alice and Bob publicly agree to use a
modulus p = 23 and base g = 5 (which is a
primitive root modulo 23).
2. Alice chooses a secret integer a = 4,
then sends Bob A = ga mod p
o A = 54 mod 23 = 4
3. Bob chooses a secret integer b = 3,
then sends Alice B = gb mod p
o B = 53 mod 23 = 10
4. Alice computes s = Ba mod p
o s = 104 mod 23 = 18
5. Bob computes s = Ab mod p
o s = 43 mod 23 = 18
6. Alice and Bob now share a secret (the
number 18).
Both Alice and Bob have arrived at the same
values because under mod p,
More specifically,
Only a and b are kept secret. All the other
values – p, g, ga mod p, and gb mod p – are
sent in the clear. The strength of the scheme
comes from the fact that gab mod p = gba mod
p take extremely long times to compute by any
known algorithm just from the knowledge of
p, g, ga mod p, and gb mod p. Once Alice and
Bob compute the shared secret they can use it
as an encryption key, known only to them, for
sending messages across the same open
communications channel.
Of course, much larger values of a, b, and p
would be needed to make this example secure,
since there are only 23 possible results of n
mod 23. However, if p is a prime of at least
600 digits, then even the fastest modern
computers using the fastest known algorithm
cannot find a given only g, p and ga mod p.
Such a problem is called the discrete logarithm
problem.[3] The computation of ga mod p is
known as modular exponentiation and can be
done efficiently even for large numbers. Note
that g need not be large at all, and in practice
is usually a small integer (like 2, 3, ...)
Source - https://en.wikipedia.org/wiki/Diffie
%E2%80%93Hellman_key_exchange
You might also like
- Super Secreto - The Third Epoch of Cryptography: Multiple, exponential, quantum-secure and above all, simple and practical Encryption for EveryoneFrom EverandSuper Secreto - The Third Epoch of Cryptography: Multiple, exponential, quantum-secure and above all, simple and practical Encryption for EveryoneNo ratings yet
- Diffie-Hellman Key Exchange PDFDocument6 pagesDiffie-Hellman Key Exchange PDFZxzxzxz007No ratings yet
- Diffie-Hellman and Its Application in Security Protocols: ISO 9001:2008 CertifiedDocument5 pagesDiffie-Hellman and Its Application in Security Protocols: ISO 9001:2008 CertifiedHarish KumarNo ratings yet
- Foundations of Computer Security: Lecture 52: Diffie-Hellman Key ExchangeDocument6 pagesFoundations of Computer Security: Lecture 52: Diffie-Hellman Key ExchangegingeevimalNo ratings yet
- Prac V1Document4 pagesPrac V1Niket BhaleraoNo ratings yet
- Diffie-Hellman Key ExchangeDocument6 pagesDiffie-Hellman Key ExchangeMilica LukicNo ratings yet
- Diffie-Hellman Key ExchangeDocument5 pagesDiffie-Hellman Key ExchangeNikitaNo ratings yet
- Diffie Hellman WriteupDocument3 pagesDiffie Hellman WriteupSumitThoratNo ratings yet
- The Diffie-Hellman Algorithm: Dr. Amjad Ali Department of Computer Science COMSATS University Islamabad, Lahore CampusDocument14 pagesThe Diffie-Hellman Algorithm: Dr. Amjad Ali Department of Computer Science COMSATS University Islamabad, Lahore CampusShaheer ArshadNo ratings yet
- Odlyzko1 PsDocument10 pagesOdlyzko1 PsAmador Perez LopezNo ratings yet
- Diffie Hellman PDFDocument6 pagesDiffie Hellman PDFsushmaNo ratings yet
- Diffie HellmanDocument1 pageDiffie HellmanAhmed HeshamNo ratings yet
- Key Concepts: ConfidentialityDocument30 pagesKey Concepts: ConfidentialityManiya KadamNo ratings yet
- Wireless Comm Systems 4Document37 pagesWireless Comm Systems 4abdulsahibNo ratings yet
- Public-Key Cryptosystems, I. Key Exchange, Knapsack, RSADocument58 pagesPublic-Key Cryptosystems, I. Key Exchange, Knapsack, RSATom_Babej_5778No ratings yet
- Diffie Hellman Key Exchange Algorithm For Key GenerationDocument5 pagesDiffie Hellman Key Exchange Algorithm For Key Generationshahrbano 14No ratings yet
- 4.2. Cryptographic Coding (Part 2)Document27 pages4.2. Cryptographic Coding (Part 2)ReachNo ratings yet
- Assignment No 6Document3 pagesAssignment No 6spNo ratings yet
- Lecture 2 C Public Key CryptographyDocument27 pagesLecture 2 C Public Key CryptographyKedir MohammedNo ratings yet
- CHAPTER 5: Public-Key Cryptography I. RSA: Two Different KeysDocument43 pagesCHAPTER 5: Public-Key Cryptography I. RSA: Two Different KeysMin KhantNo ratings yet
- Discrete Mathematics AssignmentDocument12 pagesDiscrete Mathematics AssignmentLalitSisodiaNo ratings yet
- Elliptic Curve CryptographyDocument30 pagesElliptic Curve CryptographyAsha MuruganNo ratings yet
- Deffiehellman AlgoDocument6 pagesDeffiehellman Algoparidhiagarwal129No ratings yet
- GP Report (Key Exchange)Document20 pagesGP Report (Key Exchange)Manish 'MySt' SinghNo ratings yet
- PR5 Diffie Hellman FinalDocument4 pagesPR5 Diffie Hellman FinalprafullaNo ratings yet
- Diffie HellmanDocument8 pagesDiffie Hellmanabdulrahim221298No ratings yet
- Group B-Assignment No. 1 : CNSL Te-ItDocument3 pagesGroup B-Assignment No. 1 : CNSL Te-ItPriyanshu AgrawalNo ratings yet
- Diffie Hellman AlgorithmDocument11 pagesDiffie Hellman Algorithmjoxy johnNo ratings yet
- P4 - The Keystone - Encryption v0Document11 pagesP4 - The Keystone - Encryption v0Thierry IRIENo ratings yet
- Aim: To Implement Diffiehellman Key Exchange Protocol. Theory: Diffiehellman Key Exchange Is A Cryptographic Protocol That Allows TwoDocument3 pagesAim: To Implement Diffiehellman Key Exchange Protocol. Theory: Diffiehellman Key Exchange Is A Cryptographic Protocol That Allows Twocreative_g33kNo ratings yet
- Group Theory in CS: Cryptography, Diffie-Hellman, and Elliptic CurvesDocument5 pagesGroup Theory in CS: Cryptography, Diffie-Hellman, and Elliptic CurvesMihir VahanwalaNo ratings yet
- Cryptography 3Document25 pagesCryptography 3Venera MakhambayevaNo ratings yet
- IS TheoryDocument14 pagesIS Theoryapi-26548538No ratings yet
- Digital ElectronicsDocument16 pagesDigital ElectronicsRobin RohitNo ratings yet
- Diffie Hellman Algorithm RileyDocument16 pagesDiffie Hellman Algorithm RileySRC ExamNo ratings yet
- Diffie Hellman Algorithm RileyDocument16 pagesDiffie Hellman Algorithm RileymarioNo ratings yet
- Diffie Hellman Algorithm RileyDocument16 pagesDiffie Hellman Algorithm RileyShiva Prasad100% (1)
- Exp 05Document4 pagesExp 0548Nara Amit GopalNo ratings yet
- Lec 7 - RSADocument41 pagesLec 7 - RSAMoOez InamNo ratings yet
- Cryptography and Network SecurityDocument30 pagesCryptography and Network SecuritysanjuNo ratings yet
- IT Hash FunctionsDocument47 pagesIT Hash Functionscvdm_vio614No ratings yet
- Cryptographic PrimitivesDocument59 pagesCryptographic Primitivesposer4uNo ratings yet
- Network Security - CryptographyDocument4 pagesNetwork Security - CryptographymississipNo ratings yet
- Public Cryptosystem RDocument12 pagesPublic Cryptosystem RgamerNo ratings yet
- TBS Answer Question No 1Document2 pagesTBS Answer Question No 1deepNo ratings yet
- Boneh-Venkatesan1996 Chapter HardnessOfComputingTheMostSignDocument14 pagesBoneh-Venkatesan1996 Chapter HardnessOfComputingTheMostSignmathmaxfysNo ratings yet
- Encryption TechniquesDocument6 pagesEncryption TechniquesMujahida EhsanNo ratings yet
- Security of C.N.: By: Eng. Ahmed K. DarajDocument8 pagesSecurity of C.N.: By: Eng. Ahmed K. DarajAHMED DARAJNo ratings yet
- Rsa (Cryptosystem) : RsaisaDocument10 pagesRsa (Cryptosystem) : RsaisaXerus AnatasNo ratings yet
- CHAPTER 05 - Public-Key CryptographyDocument29 pagesCHAPTER 05 - Public-Key CryptographyPNo ratings yet
- The Science of Encryption: Prime Numbers and Mod N ArithmeticDocument6 pagesThe Science of Encryption: Prime Numbers and Mod N ArithmeticManuel Aleixo LeiriaNo ratings yet
- Key Management Other Public Key Cryptosystems: - The Golden Bough, Sir James George FrazerDocument29 pagesKey Management Other Public Key Cryptosystems: - The Golden Bough, Sir James George FrazerLavanya_123No ratings yet
- Book 2 CryptographyDocument17 pagesBook 2 CryptographyGajanan GitteNo ratings yet
- Lecture 3 RSADocument7 pagesLecture 3 RSAAHMED DARAJNo ratings yet
- Class+Notes5 Diffie+Hellman+Key+Exchange+AlgorithmDocument2 pagesClass+Notes5 Diffie+Hellman+Key+Exchange+Algorithmk5c6hdvmq7No ratings yet
- Chapter 3 Public Key Cryptography PrinciplesDocument22 pagesChapter 3 Public Key Cryptography PrinciplesZoe KhanNo ratings yet
- Cryptography and Network SecurityDocument25 pagesCryptography and Network SecurityViraj KumarNo ratings yet
- Diffie-Hellman Case Study - 1DS18TE075Document10 pagesDiffie-Hellman Case Study - 1DS18TE075Gaurav AgarwalNo ratings yet
- ShevchukDocument13 pagesShevchukunbanmebeast727No ratings yet
- Montessori Stamp Game MaterialDocument15 pagesMontessori Stamp Game Materialbrunerteach100% (1)
- Data Driven Modeling For Energy Consumption Prediction in Smart Buildings PDFDocument8 pagesData Driven Modeling For Energy Consumption Prediction in Smart Buildings PDFRicardo Chegwin HillembrandNo ratings yet
- Word Sense Disambiguation: by Under The Guidance ofDocument99 pagesWord Sense Disambiguation: by Under The Guidance ofgadidheerajreddy.20.itNo ratings yet
- 3 Connected Bodies: SolutionDocument34 pages3 Connected Bodies: SolutionHerbertNo ratings yet
- Masons RuleDocument2 pagesMasons RulemohamedhegaNo ratings yet
- Python modules-XIDocument9 pagesPython modules-XIDevanshi AwasthiNo ratings yet
- Identification, Prediction and Detection of The Process Fault in A Cement Rotary Kiln by Locally Linear Neuro-Fuzzy TechniqueDocument7 pagesIdentification, Prediction and Detection of The Process Fault in A Cement Rotary Kiln by Locally Linear Neuro-Fuzzy TechniqueAnonymous NxpnI6jCNo ratings yet
- Cp5005 Sqat LsDocument3 pagesCp5005 Sqat LsKeerthi KaNo ratings yet
- Trigonometry Unit AssignmentDocument3 pagesTrigonometry Unit AssignmentDr. Gopalakrishnan GNo ratings yet
- Theorem Environments: L TEX For Math and ScienceDocument14 pagesTheorem Environments: L TEX For Math and SciencejaxbaiadNo ratings yet
- Final Quiz 2Document4 pagesFinal Quiz 2Erick GarciaNo ratings yet
- Unit 2Document30 pagesUnit 2Bhavesh AjmeraaNo ratings yet
- Class 6 Yearly Plan 2022-23Document22 pagesClass 6 Yearly Plan 2022-23Srivatsan Parthasarathy100% (1)
- Engineering Is The Application of Mathematics, Empirical Evidence and Scientific, EconomicDocument5 pagesEngineering Is The Application of Mathematics, Empirical Evidence and Scientific, EconomicKylle BedisNo ratings yet
- Boiler Heat FluxDocument8 pagesBoiler Heat FluxMubarik Ali100% (1)
- Problem: CommentsDocument2 pagesProblem: CommentsMatheus Henrique Pavani PachecoNo ratings yet
- 5-E Model Lesson PlanDocument3 pages5-E Model Lesson Planapi-418555834No ratings yet
- Math AA HL Version E P1 Worked SolutionsDocument15 pagesMath AA HL Version E P1 Worked Solutionsjoelkota018No ratings yet
- 09 - Chapter 1 PDFDocument35 pages09 - Chapter 1 PDFJhuma DeyNo ratings yet
- SSC CPO SI Detailed Syllabus 2022Document3 pagesSSC CPO SI Detailed Syllabus 2022jitendra mishraNo ratings yet
- Measuring S-Parameters - The First 50 YearsDocument15 pagesMeasuring S-Parameters - The First 50 YearsScribdFgNo ratings yet
- Analysis of Maths by Theosophical ReductionDocument37 pagesAnalysis of Maths by Theosophical ReductionMarkMadMunkiNo ratings yet
- Hobsonajjustthemaths20021296smcetp PDFDocument1,296 pagesHobsonajjustthemaths20021296smcetp PDFAIvan DCam G0% (1)
- Prob StatsDocument80 pagesProb StatsRahul SaxenaNo ratings yet
- String Theory Vs Loop Quantum GravityDocument9 pagesString Theory Vs Loop Quantum Gravityapi-241908559No ratings yet
- Panning in AI PPT SelfDocument17 pagesPanning in AI PPT Selfruff ianNo ratings yet
- Decision Theory and The Normal Distribution: Eaching Uggestions M3-5Document3 pagesDecision Theory and The Normal Distribution: Eaching Uggestions M3-5José Manuel Orduño VillaNo ratings yet
- Design of VCBDocument14 pagesDesign of VCBAniruth100% (1)
- Bessel PDFDocument40 pagesBessel PDFscabero16No ratings yet
- Introduction To Algorithms: Divide and ConquerDocument38 pagesIntroduction To Algorithms: Divide and Conquerchakshu agarwalNo ratings yet