Professional Documents
Culture Documents
Secure Cloud Network Using Partial Homomorphic Algorithms: International Journal of Advanced Research in Computer Science
Secure Cloud Network Using Partial Homomorphic Algorithms: International Journal of Advanced Research in Computer Science
Uploaded by
Azmi AbdulbaqiOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Secure Cloud Network Using Partial Homomorphic Algorithms: International Journal of Advanced Research in Computer Science
Secure Cloud Network Using Partial Homomorphic Algorithms: International Journal of Advanced Research in Computer Science
Uploaded by
Azmi AbdulbaqiCopyright:
Available Formats
ISSN
No. 0976‐5697
Volume 5, No. 5, May-June 2014
International Journal of Advanced Research in Computer Science
RESEARCH PAPER
Available Online at www.ijarcs.info
Secure Cloud Network using Partial Homomorphic Algorithms
Vineet Kumar Singh Dr. Maitreyee Dutta
M.E. Student Associate Professor
Department of Computer Science NITTTR Department of Computer Science, NITTTR
Chandigarh (U.T.), India Chandigarh (U.T.), India
vineetnitr@gmail.com d_maitreyee@yahoo.co.in
Abstract-- Cloud computing has proved its worth in different technological domains by various means. With its IAAS, PAAS and
SAAS, it has adopted the concept of pay as-per-use which is very trustworthy for all types of service consumers. Cloud computing
is the demand of changing time and everyday more and more service consumers of cloud services are increasing. With the
continuously increasing number of consumers, cloud security is now a much big concern than ever. In spite of many advantages of
the cloud computing, many organizations are still reluctant towards the adoption of this technological advancement, and
unfortunately the reason is genuine. The security concerns of cloud network are even increasing along with today’s growing cloud
network. These security concerns can be addressed if users encrypt the data while transmitting to the cloud with strong security
algorithms. In this paper we have analyzed the performance of such strong semantically secure algorithms, namely Homomorphic
Algorithms, for cloud network. As Homomorphic algorithms are very strong in terms of zero knowledge proof, these algorithms
will be having wide application in near future, especially in the untrusted environment like cloud computing. We have analyzed
the performance of Paillier and Benaloh Partial homomorphic Algorithms for the cloud network. The algorithms are tested on the
single system and on the cloud environment as well.
Index Terms— Cloud computing, cloud security, homomorphic algorithms, Benaloh Homomorphic Algorithm, Paillier
Homomorphic Algorithm.
associated software’s play an important role in cloud
computing, which is usually known as Virtual Machine
I. INTRODUCTION Monitor (VMM) or Hypervisor [7]. Virtualization allows
one single physical server to host many guest virtual
Cloud computing offers a technological shift in which machines (VM), operating systems and applications
consumer need not worry about infrastructure or software, without the increased cost and complexity of running
instead they get all of these requirements readily available multiple machines[8]. According to Amarnath Jasti et
on pay as-per-use basis by the service provider, which in al.[9], virtualization optimizes the application efficiency
turn results in less expense than owning all these in a cost effective fashion, but it may also project some
requirements[2].According to US National Institute of security risks. Security is a major consideration in cloud as
Standards and Technology (NIST) the key characteristics the control of owners data lies in service providers hand
of cloud are on-demand self-service, rapid elasticity and which is already some-what risky than owning the data at
pay as per the usage of business models[1]. NIST has the owners end itself [10]. According to the Cloud
defined four deployment versions for cloud computing: Computing Services Survey, done by IDC IT group in 2009,
public, private, hybrid, and community clouds. Interested over 87% of the people said that security is the number one
readers may refer to the NIST definition of cloud computing issue which prevents the adoption of the cloud computing
for their detailed description [1].Cloud computing has [11].Thus there is a need to understand the cloud specific
proved to be a great technology for the organizations those risks, & various ways to detect & prevent from those risks
who need large computing power, without investing large which are associated towards successful adoption of the
capital in setting up the IT infrastructure. [3]. Among many cloud.
benefits of cloud computing, some most enticing are i)Less
hardware and maintenance cost, ii) Round the world
accessibility , and iii) Flexible and highly automated II. ASSOSIATED RISKS
processes, for example client need not bother about
maintenance or software updates [4,5 ]. As cloud computing is a new enhanced version of the
Cloud Computing is a successive technological technology, it has also created some new challenges, which
approach of the technologies like grid computing, are quite different from traditional security challenges.
distributed computing, parallel computing, virtualization Based on the survey of Cloud Security Alliance (CSA),“The
technology and utility computing [6].Virtualization & its Notorious Nine: Cloud Computing Top Threats in
© 2010-14, IJARCS All Rights Reserved 224
Vineet Kumar Singh et al, International Journal of Advanced Research In Computer Science, 5 (5), May–June, 2014, 224-229
2013”[12], which they performed with the industry experts Daniel J. Abadi concluded [18] that it is a great risk in
on greatest vulnerabilities of cloud computing, there are nine storing transactional data on an un-trusted host.
critical threats to cloud security (ranked in order of Transactional databases contain the complete set of
severity)- operational data needed to power overall business processes.
This data includes detail at the lowest granularity, and often
a. Data Breaches includes important information such as credit card numbers
of the customers. Thus, any increase in potential security
b. Data Loss breaches is typically unacceptable. Facebook user data
breach is a recent example of the questionable user data
c. Account Hijacking safety on cloud systems [20].
After discussing views of several researchers it can be
d. Insure Application Programming Interfaces concluded that there are so many reasons why still client
feel reluctant in accepting this technology. Cloud is a very
e. DOS (Denial of Service) huge information repository and no client would like to take
risk on his/her information. If we consider that cloud end
f. Malicious Insiders security is up to the mark, then also there is question about
unsecure client data while transition to the cloud end. Our
g. Abuse of Cloud Services next section is an attempt to find out some efficient
solutions, which can be helpful in real time environment.
h. Insufficient Due Diligence
i. Shared Technology Issues III. OVERVIEW OF HOMOMORPHIC
ENCRYPTION
These threats are found most vulnerable for cloud
computing in the latest report of CSA [12].Better
understanding of the cloud threats will lead to better
adoption towards cloud technology. Among all these threats Cloud computing involves frequent uploading and
data breaches is most traditional and still most dangerous downloading of data along with nasty computation on
too. Let’s discuss what researchers conclude about data servers which are managed by third party. Since the client
breaches and why it still persists. does not control the cloud environment, always there is a
probability of losing the confidentiality and integrity of data
Data breaches are ranked as number one threat for the either by intentional or unintentional means. These privacy
cloud computing. Since the inception of cloud computing concerns may be addressed by sending the encrypted data to
technology, this threat is still present in the system. Multi- the cloud by the client [21, 22]. Homomorphic encryption
tenancy is one of the most important reasons among several, permits specific computations on cipher text, which
for data breaches. Since data from various organizations lie produces an encrypted result which is also in cipher text and
together in a multi-tenant cloud environment, breaching into this outcome is the result of computations as if it were
the cloud will ultimately attack the data of all the users. performed on the plaintext. [23]
Thus, the cloud of such huge information becomes an
attractive target for attackers [15]. Homomorphic encryption is classified into three
categories. Partially Homomorphic Encryption (PHE),
Data remanence is also one of the reasons of security Somewhat Homomorphic Encryption (SWHE), and Fully
breach, & generally it is unintentional. Data remanence is Homomorphic Encryption (FHE).In Partially Homomorphic
the vestigial of data that have been nominally removed or Encryption, it is possible to perform one operation on
migrated. As several virtual machines running on one encrypted data, such as multiplication or addition but not
physical machine lack of separation between multiple users, both. Somewhat homomorphic encryption techniques can
may lead to the unwilling disclosure of private data in case perform more than one operation but can only support
of data remanence. This may cause higher risk to the cloud limited number of addition and multiplication operations. A
users than with dedicated resources [13, 22]. Homomorphic Cryptosystem which is capable of both
addition and multiplication, and can compute any function is
Trusted third Party services within the cloud, known as a Fully Homomorphic Encryption system. These
establishes the necessary trust level and provides ideal programs never decrypt their inputs, thus they can be run by
solutions to preserve the confidentiality, integrity and un-trusted individuals without the risk of leaking the
authenticity of data and Communications [13, 14]. privacy. Among these methods PHE and SWHE methods
have one advantage over FHE techniques; they have been
Breach notifications are also important as Poor breach found to be more efficient in their processes.
notification may lead to privacy breach [16]. Unfortunately,
the breach notifications could not really protect a customer’s
data. A recent survey shows that service consumers who
received data breach notifications within the past years are
at a higher security risk than the typical service consumers
[17].
© 2010-14, IJARCS All Rights Reserved 225
Vineet Kumar Singh et al, International Journal of Advanced Research In Computer Science, 5 (5), May–June, 2014, 224-229
IV. PARTIAL HOMOMORPHIC ENCRYPTION Speed-Up Ratio is defined as the ratio of Total
SCHEMES Execution Time on a local processor to the Total Execution
Time on the cloud network.
VI. PROPOSED METHODOLOGY &
Both the RSA and ElGamal encryption schemes were EXECUTION ENVIRONMENT
earlier seen to follow homomorphic properties, but only
with respect to one operation. But at that time researchers
could not understand the importance of this aspect, but now
the community has grown to trust the security of these In the proposed methodology, performance analysis of
schemes and, recently, the work of Gentry and others the given algorithms on the basis of the parameters- Total
demonstrate that, when carefully employed, such Execution Time and Speed-Up Ratio and is done on local
homomorphic properties can be quite valuable[24,25]. system as well as on the cloud network.JavaSE-1.7 on
Earliest discovery in this category was the Goldwasser- Eclipse SDK 4.3.0 release is used for the development of
Micali cryptosystem whose security is based on the both the algorithms.
quadratic residuosity problem and which allows
homomorphic evaluation of a bitwise exclusive-or. This Cloud software environment provider supplies the
scheme has already been applied to the problem of securing developers with programming-level-environment with well
biometric information. Other additive homomorphic defined set of API’s. Cloud-enabled applications on Spoon
encryption schemes that provide semantic security are allow software developers to make available their existing
Benaloh, Naccache-Stern, Paillier, Damgard-Jurik, desktop applications in the cloud, without any installations.
Okamoto-Uchiyama and Boneh-Goh-Nissim. Paillier’s Spoon offers many software through their SAAS offerings;
scheme is the most efficient among currently known we used Eclipse 4.3.0, as cloud SAAS for executing my java
additively homomorphic schemes [25].Our current research algorithms in cloud environment so that performance
work is about analyzing the Benaloh & Paillier Partial comparison can be made on the basis of aforesaid
Homomorphic Systems in terms of Total Execution Time parameters.
and Speed-Up Ratio for cloud network. As partial Both algorithms are tested on Intel core i5 third
homomorphic algorithms are less time consuming than of generation processor with MS Windows 7 Home Premium
Fully Homomorphic Algorithms and have shown some 64 bit SP-1.Processor speed is 2.50 GHz and with 2 GB
positive results, our research analyzed both the algorithms to RAM.
find out the performance of these algorithms for the cloud
environment. VII. RESULTS & DISCUSSIONS
The Benaloh Homomorphic Cryptosystem is an
extended version of the Goldwasser-Micali cryptosystem VIII.
developed in 1994 by Josh Benaloh. The chief advantage of
a. Paillier is considerably faster than Benaloh on local
the Benaloh Cryptosystem over GM is that now, longer
system and on cloud network as well.
message blocks can be encrypted at in one go, while in GM
each message bit is encrypted on bit by bit basis; moreover,
b. Both algorithms are found very slow on cloud
the encryption cost is not too high.
network as compared to local system.
The Paillier scheme was first published by Pascal
Paillier in 1999. This probabilistic scheme has proved to be
c. Both algorithms achieved almost equal speed –Up
very interesting due to the homomorphic property, which
Ratio, less than one, almost half, which indicates their
allows this scheme to do normal additions on encrypted
slow processing over cloud network.
values and achieving the encrypted sum. Later, this
encrypted sum can be decrypted without even knowing the
d. Slow execution on cloud network suggests that both
actual values that constitutes the sum. Because of this useful
algorithm needs an extra processing power for its fast
characteristic this scheme is suggested for use in voting
operation from cloud network, it needs better
protocols, watermarking, secret sharing schemes and in
configuration machines (more number of processors,
private information retrieval etc.
fast processors, more RAM and cache memory) to
V. PARAMETERS USED FOR PROBLEM operate efficiently from cloud network.
ANALYSIS
e. As we know that fully homomorphic encryption
process is not efficient to apply on cloud network in
its present form, due to its extremely time consuming
A. Total Execution Time: process, in such situation, partial homomorphic
Total Execution time is the sum of the total time taken algorithms may do well on cloud comparatively, as
during the homomorphic operation including the key time taken by these algorithms is very less than Fully
generation time, encryption time and decryption time. It will homomorphic encryption process.
be evaluated both on local system and on cloud network.
All the results are obtained with due care for achieving
higher accuracy five samples of Total Execution Time were
B. Speed-Up Ratio: taken then an average of five samples were taken for the
measurement and comparative analysis among algorithms
© 2010-14, IJARCS All Rights Reserved 226
Vineet Kumar Singh ett al, Internationaal Journal of Ad
dvanced Research In Computer Science,
S May–June, 2014, 224-229
5 (5), M
and for the grapph plotting as a well. All the respectiive
obseervation readinngs and graph are shown for both of the
t
analyyzed algorithm
ms.
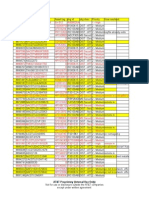
Table:
T 3. Totaal Execution T
Time for Benaloh Cryptosysstem
IX
X. OBSER
RVATION RESULTS
R & GRAPHS
G OF
F on Loccal System
DIF
FFERENT AL
LGORITHMMS M
SAM SAM S
SAM SAM SAM
AVER
A
ALGO
A PLE-- PLE P
PLE- PLE PLE-
A
AGE
1 -2 3 -4 5
Tablle: 1. Total Exxecution Timee for Paillier Cryptosystem
C on BENA
667 556 6600 625 583 6006
Local System LOH
Tablle: 2. Total Exxecution Timee for Paillier Cryptosystem
C on M
SAM SAM S
SAM SAM SAM
AVER
A
Cloud Network ALGO
A PLE-- PLE P
PLE- PLE PLE-
A
AGE
1 -2 3 -4 5
ALG
GO SAM SAM SAM
M SAM SAM AVE
ER PAIL
P
PLE- PLE PLE
E- PLE PLE- AG
GE 344 330 360 356 337 345
LIER
L
1 -2 3 -4 5
PAIIL Table:
T 4. Totaal Execution T
Time for Benaloh Cryptosysstem
708 668 9255 718 681 7400 on Clouud Network
LIE
ER
M
SAM SAM S
SAM SAM SAM
AVER
A
ALGO
A PLE-- PLE P
PLE- PLE PLE-
A
AGE
1 -2 3 -4 5
Speeed-Up Ratio = Total Execuution Time onn local system
m/
BENA
Totaal Execution Time
T on cloud network 1145 1253 1137 1461 1225 12244
LOH
=>>345/740
=>>0.466
Sp
peed-Up Ratio = Total Exxecution Timee on local system /
To
otal Executionn Time on clooud network.
800
0
=>606/1244
=>0.487
700
0
1400
600
0
1200
500
0
400
0 1000
740
300
0
800
200
0
34
45 600 1244
100
0
400
0 606
PAILLIER(sin
ngle system) PAILLIER(cloud network)
200
P
PAILLIER HOMOM
MORPHISM
Fiigure 1: PAILL
LIER: Single System vs. Cloud Networkk 0
\ ALOH(single systeem)
BENA BENALOH(cloud networkk)
Fig 1 illustraates the Total Execution Time
T for Pailllier BENALOH
H HOMOMORPH
HISM
Crypptosystem on single system m as well as onn cloud network.
Grapph clearly indiicates that Paiillier homomoorphic operatiion Figure 2: BEN
NALOH: Singgle System vss. Cloud Netw
work
on siingle system isi significantlyy fast from clooud network.
© 20110-14, IJARCS All
A Rights Reserveed 227
Vineet Kumar Singh et al, International Journal of Advanced Research In Computer Science, 5 (5), May–June, 2014, 224-229
Fig 2 illustrates the Total Execution Time for Benaloh [7]. Manabu Hirano, Takahiro Shinagawa, Hideki Eiraku,
Cryptosystem on single system as well as on cloud network. Shoichi Hasegawa, Kazumasa Omote, Takeshi
Graph clearly indicates that Benaloh homomorphic Okuda, Eiji Kawai, and Suguru Yamaguchi, “A
operation on single system is significantly fast from cloud Two-step Execution Mechanism for Thin Secure
network. Hypervisors”, Third International Conference on
Emerging Security Information, Systems and
Technologies, IEEE, 2009, pp. 129-134
X. CONCLUSION [8]. Udaya Tupakula and Vijay Varadharajan, “TVDSEC:
Trusted Virtual Domain Security”, IEEE, 2011, pp.
Cloud computing is a big technological opportunity for 57-63.
the IT world, there is no doubt about it. Pay-as-per usage [9]. Amarnath jasti, “Security in Multi-tenancy Cloud”,
model of cloud computing has created great opportunities, IEEE, 2010.
that were at some time even beyond the limit, without
paying much more money for the same usage. We strictly [10]. Jen-Sheng Wang, Che-Hung Liu and Grace TR Lin,
feel that there is an instant need to make cloud services more “How to Manage Information Security in Cloud
reliable and safe to use, so that more and more clients can Computing”, IEEE, 2011, pp. 1405-1410
adopt this technology. Our paper is an attempt to make [11]. Ramgovind, S.; Eloff, M.M.; Smith, E., "The
cloud more safe and reliable by means of very secure management of security in Cloud computing,"
Homomorphic Cryptosystem, so we analyzed the Partial Information Security for South Africa, 2010 , vol., no.,
Homomorphic Cryptosystem, which are relatively efficient pp.1-7, 2-4 Aug. 2010.
than other homomorphic cryptosystems, for the cloud usage. [12]. https://cloudsecurityalliance.org/research/top-threats/
Our research work results that Paillier is considerably faster
than Benaloh on local system and on cloud network as well. [13]. Dimitrios Zissis and Dimitrios Lekkas “Addressing
Both algorithms need an extra processing power for its fast cloud computing security issues”, Future Generation
operation from cloud network, need better configuration Computer System, Elsevier 2010, pp. 583–592.
machines (more number of processors, fast processors, more [14]. D. Polemi, Trusted third party services for health care
RAM, more cache memory) to operate on cloud network. in Europe, Future Generation Computer Systems 14
Our current research work is an attempt to analyze the (1998), pp. 51–59.
performance of Partial Homomorphic Algorithms so that its
[15]. Bernard Golden. Defining private clouds,
use in the cloud computations can make it more secure to
2009/http://www.cio.com/article/492695/Defining_Pri
use & organizations may come forward to adopt cloud
computing. vate_Clouds_Part_One.
[16]. Cavoukian A. Information and Privacy Commissioner,
Ontario, Canada. 2009. Nov, [2011-07-
13]. website A Discussion Paper on Privacy
XI. REFERENCES Externalities, Security Breach Notification and the
Role of Independent Oversight
[1]. National Institute of Standards and Technology, NIST http://www.ipc.on.ca/images/Resources/privacy_exter
Definition of Cloud Computing, Sept 2011. nalities.pdf.
[2]. Rohit Bhaduria, Sugata Sanyal, “Survey on Security [17]. Javelin Strategy & Research. 2011. [2011-07-
Issues in Cloud Computing and Associated Mitigation 23]. website Data Breach Notifications: Victims Face
Techniques”, International Journal of computer Four Times Higher Risk of Fraud.
applications, Vol: 47, No: 18, June 2012, pp. 47-66. https://www.javelinstrategy.com/brochure-158.
[3]. Armbrust, M. et. al., (2009), “Above the clouds: A [18]. Daniel J. Abadi, “Data Management in the Cloud:
Berkeley view of Cloud Computing”, UC Berkeley Limitations and Opportunities”, Bulletin of the IEEE
EECS, Feb 2010. Computer Society Technical Committee on Data
[4]. R. Maggiani, Communication Consultant, Solari Engineering/http://sites.computer.org/debull/A09mar/a
Communication, “Cloud computing is changing How badi.pdf.
we Communicate”, IEEE International Professional [19]. Cloud Computing: Benefits, Risks and
Conference, IPCC, pp. 1-4, Waikiki, HI, USA, July Recommendations for Information Security, European
19- 22, 2009. ISBN: 978-1-4244-4357-4. Network and Information Security Agency, ENISA,
[5]. Harold C. Lin, Shivnath Babu, Jeffrey S. Chase, Sujay 2009.
S. Parekh, “Automated Control in Cloud Computing: [20]. https://www.facebook.com/notes/facebook-
Opportunities and Challenges”, Proc. of the 1st security/important-message-from-facebooks-white-
Workshop on Automated control for data centres and hat-program/10151437074840766.
clouds, New York, NY, USA, pp. 13-18, 2009, ISBN:
978-1-60558-585-7. [21]. Park, Daejun, Jeehoon Kang, Kihong Heo, Sungkeun
Cho, Yongho Yoon, and Kwangkeun Yi. "Encrypted
[6]. Murat Kantarcioglu, Alain Bensoussan and SingRu, Execution."
“Impact of Security Risks on Cloud Computing
Adoption”, IEEE, 2011, pp. 670-674. [22]. Naehrig, Michael, Kristin Lauter, and Vinod
Vaikuntanathan. "Can homomorphic encryption be
© 2010-14, IJARCS All Rights Reserved 228
Vineet Kumar Singh et al, International Journal of Advanced Research In Computer Science, 5 (5), May–June, 2014, 224-229
practical?" Proceedings of the 3rd ACM workshop on [24]. C. Gentry. A fully homomorphic encryption scheme.
Cloud computing security workshop, ACM, 2011. PhD thesis, Stanford University, 2009.
[23]. Ogburn, Monique, Claude Turner, and Pushkar Dahal. [25]. Hu, Yin. Improving the Efficiency of Homomorphic
"Homomorphic Encryption" Procedia Computer Encryption Schemes, Diss. Virginia Tech, 2013.
Science 20 (2013), pp. 502-509.
© 2010-14, IJARCS All Rights Reserved 229
You might also like
- Cloud Computing Security Issues & Challenges: A Review: Avijit Mondal & Subrata Paul Radha Tamal Goswami Sayan NathDocument5 pagesCloud Computing Security Issues & Challenges: A Review: Avijit Mondal & Subrata Paul Radha Tamal Goswami Sayan NathMuhammad Atiq ur RehmanNo ratings yet
- Challenges and Mechanisms For Securing Data in Mobile Cloud ComputingDocument3 pagesChallenges and Mechanisms For Securing Data in Mobile Cloud ComputingijcnesNo ratings yet
- Security in Cloud ComputingDocument7 pagesSecurity in Cloud ComputingAlanNo ratings yet
- A Comprehensive Review On Trust Issues, Security and Privacy Issues in Cloud StorageDocument9 pagesA Comprehensive Review On Trust Issues, Security and Privacy Issues in Cloud StorageInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Zhang 2013Document4 pagesZhang 2013Anmol MogalaiNo ratings yet
- Paper 21-Application of Intelligent Data Mining Approach in Securing 2Document1 pagePaper 21-Application of Intelligent Data Mining Approach in Securing 2Shiva prasadNo ratings yet
- Data Security in Cloud Computing JETIRDD06013Document7 pagesData Security in Cloud Computing JETIRDD06013Getachew KefyalewNo ratings yet
- Security Issues in Cloud Computing and Risk Assessment: Darshan R, Smitha G RDocument6 pagesSecurity Issues in Cloud Computing and Risk Assessment: Darshan R, Smitha G RInternational Journal of computational Engineering research (IJCER)No ratings yet
- Reference07 Louk2015Document5 pagesReference07 Louk2015Krishna K. SajjaNo ratings yet
- Security Analysis of CloudDocument5 pagesSecurity Analysis of CloudAaron MangalNo ratings yet
- Data Security and Privacy Protection Issues in Cloud ComputingDocument5 pagesData Security and Privacy Protection Issues in Cloud Computingsabah21No ratings yet
- Emerging Cloud Computing Security Threats: Department of Information Technology City University of New YorkDocument4 pagesEmerging Cloud Computing Security Threats: Department of Information Technology City University of New YorkSumit RanaNo ratings yet
- Various Security Threats and Their Solutions in Cloud ComputingDocument7 pagesVarious Security Threats and Their Solutions in Cloud Computingkalyani anwekarNo ratings yet
- A Project ReportDocument21 pagesA Project Report10-Aniket MatodkarNo ratings yet
- Cyber Security Threats and Vulnerabilities in Cloud Computing and Security MeasurementsDocument42 pagesCyber Security Threats and Vulnerabilities in Cloud Computing and Security MeasurementsKehinde OlusegunNo ratings yet
- A Survey of Cloud Computing Security Challenges, Issues and Their CountermeasuresDocument5 pagesA Survey of Cloud Computing Security Challenges, Issues and Their CountermeasuresA oNo ratings yet
- Risks & Solutions For Data Security in Cloud ComputingDocument7 pagesRisks & Solutions For Data Security in Cloud ComputingInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Cloud Computing Challenges & Related Security Issues: Sabah Naseem Prof. Ashish B. SasankarDocument5 pagesCloud Computing Challenges & Related Security Issues: Sabah Naseem Prof. Ashish B. SasankarPurushothama ReddyNo ratings yet
- A Survey On Data Breach Challenges in Cloud Computing Security: Issues and ThreatsDocument8 pagesA Survey On Data Breach Challenges in Cloud Computing Security: Issues and ThreatsDr StrangeNo ratings yet
- Security Challenges and Issues in Cloud Computing - The Way AheadDocument4 pagesSecurity Challenges and Issues in Cloud Computing - The Way Aheadetylr mailNo ratings yet
- A Detailed Review of Cloud Security Issues, Threats & AttacksDocument7 pagesA Detailed Review of Cloud Security Issues, Threats & AttackssherifabdelmonamalkodousyNo ratings yet
- Ecure Loud Rchitecture: Kashif Munir and Prof Dr. Sellapan PalaniappanDocument14 pagesEcure Loud Rchitecture: Kashif Munir and Prof Dr. Sellapan PalaniappanAnonymous IlrQK9HuNo ratings yet
- Cloud Securityusing Hybrid CryptographyDocument7 pagesCloud Securityusing Hybrid Cryptographyaagat.singhcs.csf20No ratings yet
- Cloud Computing SecurityDocument10 pagesCloud Computing SecurityIJRASETPublicationsNo ratings yet
- SAAS Attack Detection and Prevention WitDocument5 pagesSAAS Attack Detection and Prevention WitImen SaidiNo ratings yet
- Storage ServiceDocument8 pagesStorage Servicemahi mNo ratings yet
- Cloud Security ChallangeDocument5 pagesCloud Security ChallangeAdil RashidNo ratings yet
- An Outline of The Problems and Potential Solutions For Cloud Computing SecurityDocument13 pagesAn Outline of The Problems and Potential Solutions For Cloud Computing SecurityInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Protection and Security of Data in Cloud ComputingDocument5 pagesProtection and Security of Data in Cloud ComputingYutyu YuiyuiNo ratings yet
- Security Challenges in Cloud Computing: A Comprehensive StudyDocument4 pagesSecurity Challenges in Cloud Computing: A Comprehensive Studydesx redjNo ratings yet
- Cloud Computing Security TechniquesDocument8 pagesCloud Computing Security TechniquesVinod NaiduNo ratings yet
- Manakula Vinayagar Istitute of TechnlogyDocument8 pagesManakula Vinayagar Istitute of TechnlogyPrema RajuNo ratings yet
- Data SecurityDocument7 pagesData SecurityRohanNo ratings yet
- (IJCST-V4I2P7) : Jahangeer Qadiree, Mohd Ilyas MaqboolDocument5 pages(IJCST-V4I2P7) : Jahangeer Qadiree, Mohd Ilyas MaqboolEighthSenseGroupNo ratings yet
- 2014 Survey Paper On Various Load Balancing Algorithms in Cloud ComputingDocument6 pages2014 Survey Paper On Various Load Balancing Algorithms in Cloud ComputingPradheeba Smirithi PNo ratings yet
- Data Security and Privacy Protection Issues in Cloud ComputingDocument5 pagesData Security and Privacy Protection Issues in Cloud Computingoptimistic07No ratings yet
- An Analysis of The Cloud Computing Security ProblemDocument6 pagesAn Analysis of The Cloud Computing Security Problemrmsaqib1No ratings yet
- A Systematic Literature Review On Cloud Computing Security Threats and Mitigation StrategiesDocument16 pagesA Systematic Literature Review On Cloud Computing Security Threats and Mitigation StrategiesPranav BNo ratings yet
- Rasheed 2014Document5 pagesRasheed 2014Omosekeji TimilehinNo ratings yet
- Irjet V9i362Document5 pagesIrjet V9i362Rahul ganesha GaneshaNo ratings yet
- Performance Analysis of Data Security Using Cryptographic Policy With Instance Based Encryption in Cloud ComputingDocument6 pagesPerformance Analysis of Data Security Using Cryptographic Policy With Instance Based Encryption in Cloud ComputingEditor IJTSRDNo ratings yet
- A Survey On Security Issues and The Existing Solutions in Cloud ComputingDocument4 pagesA Survey On Security Issues and The Existing Solutions in Cloud ComputingRaed JaradatNo ratings yet
- Confimizer A Novel Algorithm To Optimize Cloud ResDocument14 pagesConfimizer A Novel Algorithm To Optimize Cloud ResRABINA BAGGANo ratings yet
- Ijeta V7i4p7Document6 pagesIjeta V7i4p7editor1ijcstNo ratings yet
- A Survey On Gaps, Threat Remediation Challenges and Some Thoughts For ProactiveDocument19 pagesA Survey On Gaps, Threat Remediation Challenges and Some Thoughts For ProactiveVINOD DADASO SALUNKHE 20PHD0400No ratings yet
- Cts Tutorial HamdiDocument8 pagesCts Tutorial HamdiMaysoon YaghiNo ratings yet
- Security and Privacy Protection Issues in Cloud Computing Nikhil BhutaDocument8 pagesSecurity and Privacy Protection Issues in Cloud Computing Nikhil BhutaNikhil Bhuta DhariyawadNo ratings yet
- Cloud Computing SecurityDocument10 pagesCloud Computing SecurityAYISHA NISARNo ratings yet
- Iciasdfc Ind 0134+Document19 pagesIciasdfc Ind 0134+Willem VincentNo ratings yet
- Security Issue in The Cloud Computing Nagendra Sen & Durgesh PandeyDocument5 pagesSecurity Issue in The Cloud Computing Nagendra Sen & Durgesh PandeyDeepak KesharwaniNo ratings yet
- A Semantic Study On Emerging Risk and Security Management in Cloud ComputingDocument11 pagesA Semantic Study On Emerging Risk and Security Management in Cloud ComputingIJRASETPublicationsNo ratings yet
- Yildiz2009 PDFDocument5 pagesYildiz2009 PDFbeloow beloowNo ratings yet
- Network SecurityDocument5 pagesNetwork Securitykarthiga RNo ratings yet
- Ijacst01462015 PDFDocument4 pagesIjacst01462015 PDFWARSE JournalsNo ratings yet
- Dishant Synopsis 1Document9 pagesDishant Synopsis 1Rina MoonNo ratings yet
- 1.B Intro of Cloud Comparative - Analysis - of - Security - Algorithms - Used - in - Cloud - ComputingDocument6 pages1.B Intro of Cloud Comparative - Analysis - of - Security - Algorithms - Used - in - Cloud - ComputingPatel rajNo ratings yet
- Cloud Computing Security Using EncryptionDocument5 pagesCloud Computing Security Using EncryptionWarren Smith QC (Quantum Cryptanalyst)No ratings yet
- A Survey On Security and Privacy in Cloud Computing: Mir Toornaw IslamDocument9 pagesA Survey On Security and Privacy in Cloud Computing: Mir Toornaw IslamtamernadeemNo ratings yet
- Cloud computing: Moving IT out of the officeFrom EverandCloud computing: Moving IT out of the officeBCS, The Chartered Institute for ITNo ratings yet
- Edddas 11223344Document11 pagesEdddas 11223344Azmi AbdulbaqiNo ratings yet
- Edddas 11223344Document8 pagesEdddas 11223344Azmi AbdulbaqiNo ratings yet
- Edddas 11223344Document3 pagesEdddas 11223344Azmi AbdulbaqiNo ratings yet
- Edddas 11223344Document7 pagesEdddas 11223344Azmi AbdulbaqiNo ratings yet
- 2-Circle Drawing AlgorithmsDocument4 pages2-Circle Drawing AlgorithmsAzmi AbdulbaqiNo ratings yet
- Homogeneous (Or Balanced) .: Example 1: Scale RectangleDocument3 pagesHomogeneous (Or Balanced) .: Example 1: Scale RectangleAzmi AbdulbaqiNo ratings yet
- Enhanced Image No-Reference Quality Assessment Based On Colour Space DistributionDocument11 pagesEnhanced Image No-Reference Quality Assessment Based On Colour Space DistributionAzmi AbdulbaqiNo ratings yet
- Amina 1Document23 pagesAmina 1Azmi AbdulbaqiNo ratings yet
- Computer Graphics - LectureDocument5 pagesComputer Graphics - LectureAzmi AbdulbaqiNo ratings yet
- Neurocomputing: Sergio Decherchi, Paolo Gastaldo, Rodolfo Zunino, Erik Cambria, Judith RediDocument12 pagesNeurocomputing: Sergio Decherchi, Paolo Gastaldo, Rodolfo Zunino, Erik Cambria, Judith RediAzmi AbdulbaqiNo ratings yet
- J. Vis. Commun. Image R.: Saeed Mahmoudpour, Peter SchelkensDocument13 pagesJ. Vis. Commun. Image R.: Saeed Mahmoudpour, Peter SchelkensAzmi AbdulbaqiNo ratings yet
- Computer Graphics: Line and Circle 1-Line Drawing AlgorithmsDocument4 pagesComputer Graphics: Line and Circle 1-Line Drawing AlgorithmsAzmi AbdulbaqiNo ratings yet
- Quality Assessment Tool For Performance Measurement of Image Contrast Enhancement MethodsDocument10 pagesQuality Assessment Tool For Performance Measurement of Image Contrast Enhancement MethodsAzmi AbdulbaqiNo ratings yet
- Neurocomputing: Lin Ma, Xu Wang, Qiong Liu, King Ngi NganDocument11 pagesNeurocomputing: Lin Ma, Xu Wang, Qiong Liu, King Ngi NganAzmi AbdulbaqiNo ratings yet
- Chen2012 Chapter ReducedReferenceImageQualityAsDocument8 pagesChen2012 Chapter ReducedReferenceImageQualityAsAzmi AbdulbaqiNo ratings yet
- Building A Reduced Reference Video Quality Metric With Very Low Overhead Using Multivariate Data AnalysisDocument6 pagesBuilding A Reduced Reference Video Quality Metric With Very Low Overhead Using Multivariate Data AnalysisAzmi AbdulbaqiNo ratings yet
- Signal Processing: Image Communication: Lin Ma, Songnan Li, King Ngi NganDocument19 pagesSignal Processing: Image Communication: Lin Ma, Songnan Li, King Ngi NganAzmi AbdulbaqiNo ratings yet
- Neurocomputing: Xu Wang, Qiong Liu, Ran Wang, Zhuo ChenDocument9 pagesNeurocomputing: Xu Wang, Qiong Liu, Ran Wang, Zhuo ChenAzmi AbdulbaqiNo ratings yet
- IOT Based Wireless Monitoring Stroke Patient With Partial Paralysis AssistanceDocument7 pagesIOT Based Wireless Monitoring Stroke Patient With Partial Paralysis AssistanceAzmi AbdulbaqiNo ratings yet
- Information Sciences: Jinjian Wu, Weisi Lin, Guangming Shi, Leida Li, Yuming FangDocument12 pagesInformation Sciences: Jinjian Wu, Weisi Lin, Guangming Shi, Leida Li, Yuming FangAzmi AbdulbaqiNo ratings yet
- Amina 1Document8 pagesAmina 1Azmi AbdulbaqiNo ratings yet
- Signal Processing: Image Communication: Lin Ma, Songnan Li, King Ngi NganDocument19 pagesSignal Processing: Image Communication: Lin Ma, Songnan Li, King Ngi NganAzmi AbdulbaqiNo ratings yet
- Amina 1Document10 pagesAmina 1Azmi AbdulbaqiNo ratings yet
- A Dependable Sharing Approach With Creation of Encrypted DatabaseDocument3 pagesA Dependable Sharing Approach With Creation of Encrypted DatabaseAzmi AbdulbaqiNo ratings yet
- An Efficient and Secure Searching Model For Outsourced Cloud DataDocument7 pagesAn Efficient and Secure Searching Model For Outsourced Cloud DataAzmi AbdulbaqiNo ratings yet
- Privacy Preserving PHR System in Cloud Using Attribute-Based EncryptionDocument4 pagesPrivacy Preserving PHR System in Cloud Using Attribute-Based EncryptionAzmi AbdulbaqiNo ratings yet
- Towards Secure and Efficient Mobile Cloud Computing For Medical Data Sharing Using Attribute Based EncryptionDocument4 pagesTowards Secure and Efficient Mobile Cloud Computing For Medical Data Sharing Using Attribute Based EncryptionAzmi AbdulbaqiNo ratings yet
- VB6 Support StatementDocument8 pagesVB6 Support StatementtrueradNo ratings yet
- Tutorial 3 2 2022-2023 AnswerDocument5 pagesTutorial 3 2 2022-2023 AnswerZam SkemaNo ratings yet
- Mobile Device Hardware OverviewDocument6 pagesMobile Device Hardware Overviewserba hijabNo ratings yet
- Log TCapDocument28 pagesLog TCapAbir FahadNo ratings yet
- HG1 Intelligent HART Gateway 1Document5 pagesHG1 Intelligent HART Gateway 1Миљан ГацоNo ratings yet
- Ph-Metro Sobremesa Orion Serie Star A211Document2 pagesPh-Metro Sobremesa Orion Serie Star A211Silvana Elena Montecino San MartínNo ratings yet
- GSM Single Site VerificationDocument26 pagesGSM Single Site Verificationgagan_555100% (8)
- Sabic Safco Case Study OwlctiDocument7 pagesSabic Safco Case Study OwlctiTofel EmedNo ratings yet
- NPTEL CC Assignment7Document5 pagesNPTEL CC Assignment7Paul StarkNo ratings yet
- Heuristic in Ai: BY-Chiranjeev Sharma A2324717001 Suraj Kumar Ojha A2324717007 7cse3 MbaDocument14 pagesHeuristic in Ai: BY-Chiranjeev Sharma A2324717001 Suraj Kumar Ojha A2324717007 7cse3 Mbachiranjeev sharmaNo ratings yet
- Session Initiation Protocol: By, Vivek NemarugommulaDocument41 pagesSession Initiation Protocol: By, Vivek Nemarugommulaمحمد التابعي خزازنهNo ratings yet
- Lesson 03 Introduction To Java & Basic Programming ConceptsDocument35 pagesLesson 03 Introduction To Java & Basic Programming ConceptsLawk othmanNo ratings yet
- What Is Software Architecture - Lecture NoteDocument45 pagesWhat Is Software Architecture - Lecture NoteIfeoluwa Olagunju100% (1)
- Online Movie Ticket Reservation APP FYP DOC New SidraDocument62 pagesOnline Movie Ticket Reservation APP FYP DOC New SidrasidrahNo ratings yet
- Installation Requirements UsDocument20 pagesInstallation Requirements Usbrayam11No ratings yet
- NS0-403 Update 25.10.2022Document25 pagesNS0-403 Update 25.10.2022nixdorfNo ratings yet
- Serial Digital Data Networks AN3438Document3 pagesSerial Digital Data Networks AN3438Keijo SalonenNo ratings yet
- Complexity Analysis Time-Space Trade-OffDocument51 pagesComplexity Analysis Time-Space Trade-OffJatin SinghNo ratings yet
- ISC2021 Computer Science Practical PaperDocument5 pagesISC2021 Computer Science Practical PaperAnubhab Dutta GuptaNo ratings yet
- Flyer - Access Controller DS K2810 SeriesDocument2 pagesFlyer - Access Controller DS K2810 SeriesArzo ArizonaNo ratings yet
- Quiz 2Document3 pagesQuiz 2S CHOWDHURYNo ratings yet
- Cybersecurity Roadmap For PPT DownloadDocument7 pagesCybersecurity Roadmap For PPT DownloadDawood life100% (1)
- Embedded EWM - Inbound POSC (Multi-Step Movements) - SAP BlogsDocument15 pagesEmbedded EWM - Inbound POSC (Multi-Step Movements) - SAP BlogsPranith RonaldNo ratings yet
- Nist 767863Document4 pagesNist 767863Vipul TehlanNo ratings yet
- Lab Assignment 8Document3 pagesLab Assignment 8Vaishnavi G 18CA248No ratings yet
- Assignment - Big Data ManagementDocument2 pagesAssignment - Big Data ManagementShwetank PandeyNo ratings yet
- Frequently Asked QuestionsDocument3 pagesFrequently Asked Questionskevin klynNo ratings yet
- Comparison Python, R, SASDocument6 pagesComparison Python, R, SASjohn doeNo ratings yet
- 10th July 2013Document102 pages10th July 2013Adam Richardson100% (1)
- FB BasicDocument39 pagesFB BasiccarlosNo ratings yet