Professional Documents
Culture Documents
Chapter 94
Chapter 94
Uploaded by
cheintOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Chapter 94
Chapter 94
Uploaded by
cheintCopyright:
Available Formats
Quantum Cryptography & its Comparison with Classical
Cryptography: A Review Paper
Aakash Goyal1, Sapna Aggarwal2 and Aanchal Jain3
1
M.Tech. Student (CSE) JIET-Jind, India
2
Assistant Professor, CSE Department, JIET-Jind, India
3
M.Tech. Student (ECE), BMIET-Sonipat, India
E-mail: aakash.goyal99@gmail.com1, sapna.ruby@gmail.com2, aanchal.always@gmail.com3
Abstract cryptographic protocols can invoke up streams of random bits
Cryptography long had been a valuable, essential tool for whose values will remain unknown to third parties. When we
defensive computer security. A technique whether classical or use these bits as key material for Vernam ciphers, we can get
modern must be well-built and also must be practically viable. Shannon’s ideal of perfect secrecy—cheaply and easily.
With the application of quantum mechanics principles to The development of quantum cryptography was inspired
cryptography, a new dimension to secure communication can by the short comings of classical cryptography methods. In
be given; such system so developed can detect eavesdropping classical cryptography communicating parties need to share a
and assure that it should not occur at all. Work presents the secret sequence of random numbers, the key, that is exchanged
brief review of the existing state of quantum cryptography by physical means and thus open to security loopholes. The
science. Core principles of the quantum cryptography are classical cryptography does not detect eavesdropping like
demonstrated by giving the example of BB84 protocol. Work quantum cryptography, also with increase in computing power
principally presents quantum cryptography’s comparison with and new computational techniques are developed, the
classical cryptography. numerical keys will no longer be able to provide satisfactory
levels of secure communications. These flaws led to the
Keywords: BB84 protocol;, Quantum cryptography; Classical development of quantum cryptography, whose security basis
cryptography; Polarization states; is quantum mechanics [2]. This paper presents the comparison
of quantum and classical cryptography on several
backgrounds.
Introduction Historical Timeline
Cryptography is the science in which the use of mathematics In 1917, Gilbert S Vernam, an AT&T employee, created a
occurs to encrypt and decrypt data .Cryptography enables user machine that makes a non-repeating, virtually random
to store sensitive information or transmit it across Insecure sequence of characters called as one-time pad. Using an
networks (like the Internet) so that it cannot be read by anyone encryption key the same length as the message and never
other than the intended receiver. To attain secure transmission, using that key again is the only proven method of securely
an algorithm is used which unite the message with additional communicating. In the 1940s, Claude Shannon provided the
information to produce a cryptogram. The algorithm is called information-theoretic basis for secrecy; the amount of
as cipher and the additional information is known as the key. uncertainty that can be commenced into an encoded message
This technique is termed as encryption. can’t be greater than that of the cryptographic key used to
Whereas cryptanalysis is the science of analyzing and encode it. In the early 1970s, or possibly earlier, numerous
breaking secure communication. Classical cryptanalysis researchers, including Whitfield Diffie, Martin Hellman,
involves an interesting combination of analytical reasoning, Ralph Merkle, Ron Rivest, Adi Shamir, Leonard Adleman,
application of mathematical tools, pattern finding, patience, James Ellis, Clifford Cocks, and Malcolm Williamson,
determination, and luck. Quantum cryptographic devices in invented cryptographic techniques based on computational
general make use of individual photons of light and take complexity. Quantum cryptography was first proposed in 1984
benefit of Heisenberg's uncertainty principle, according to by Brennet and Brassard [1] based on the No-Cloning
which attempt to compute a quantum system disturbs it and theorem. It relies on fact that we should base security on
yields partial information about its state before the known physical laws not on mathematical complexities.
measurement. Eavesdropping on a quantum communications
channel thus causes an unavoidable disturbance, alerting the
legal users. Quantum techniques also support the achievement Classical Cryptography
of cryptographic objectives such as enabling two mutually Classical cryptography makes use of several mathematical
suspicious parties to make combined decisions based on techniques to restrict eavesdroppers from knowing the
private information, while compromising its confidentiality as contents of encrypted messages. The most popular among
little as possible. Physical devices with these specialized them that are adopted globally have been described below.
[Page No. 428]
Quantum Cryptography & its Comparison with Classical Cryptography: A Review Paper
Throughout the paper, the transmitter is referred as ‘Alice’, the ensures perfect secrecy. A one-time pad is sometimes
receiver as ‘Bob’, and an eavesdropper as ‘Eve’. considered as ideal cipher. The system is named after
encryption method in which a large, non repeating set of keys
Data Encryption Standard (DES) is written on sheets of paper, attached together into a pad. For
The data encryption algorithm developed by IBM for NBS the encryption to work, the receiver needs a pad identical to
was based on Lucifer, and it became known as the Data that of the sender. The major disadvantage with one-time pad
Encryption Standard, although its proper name is DEA (Data is even though its security it is very impractical. For every
Encryption Algorithm) in the United States and DEA1 (Data message encoded with the system, the participants have to to
Encryption Algorithm-1) in other countries. In DES [4] the exchange a secret key that has at least the same length. The
encrypting and decrypting algorithms are publicly announced; one-time pad method needs absolute synchronization between
the security of the cryptogram depends entirely on the secrecy sender and receiver and no key should be used twice.
of the key and the key consist of randomly chosen, sufficiently
long string of bits. This algorithm ensures that the output bits
have no apparent relationship to the input bits and spreading Quantum Cryptography
the effect of one plaintext bit to other bits in the cipher text. Quantum channel construction requires a pair of polarizing
Once the key is established between the sender and the filters at both sender and receiver ends. So, that at sender end
receiver, subsequent communication involves sending we can send photos of selected polarization and at receiver
cryptograms over a public channel which is vulnerable to total end to measure the polarization of photons. There are two
passive eavesdropping. However with the purpose of types of polarization filters rectilinear and diagonal; in
establishing the key between two users, who share no secret rectilinear filter we have horizontal and vertical orientation of
information initially, must at a certain stage of communication photons whereas in diagonal we have 45 and 135 degree of
use a reliable and a very secure channel. A random key must orientation of photons. The two directions can be detected by
first be send through a secret channel before the transfer of vertically oriented calcite crystal and two detectors like
actual message. The major drawback of DES is that like other photomultiplier. If the photon is horizontally polarized it will
classical cryptographic mechanism it also cannot guarantee be directed to upper filter and to vertical detector if it is
ultimate security of a communication channel. vertically polarized. If similar apparatus is rotated at 45 it will
record diagonal directions. Thus the rotated apparatus is
Public Key Cryptographic (PKC) Systems useless for rectilinear direction and vertical apparatus for
With a conventional symmetric key system, each pair of users diagonal direction .hence we cant measure both
needs a separate key. As the number of users grows, the simultaneously thus verifying Heisenberg uncertainty
number of keys increases very rapidly. An n-user system principle.BB84 Protocol was developed by Charles H, Bennett
requires n * (n - 1)/2 keys, and each user must track and of the IBM Thomas J. Watson Research Centre and Gilles
remember a key for each other user with which he or she Brassard of the University of Montreal, quantum cryptography
wants to communicate. We can reduce the problem of key is based on the fact that measuring a quantum system such as a
proliferation by using a public key approach. In a public key photon irreversibly changes its state and wipes out information
or asymmetric encryption system, each user has two keys: a about the aspects before measurement [1]. It uses two
public key and a private key. The user may publish the public channels-quantum by which Alice and bob send polarized
key freely because each key does only half of the encryption photons second is classical public channel by which they send
and decryption process [3]. The keys would be inverse ordinary messages such as comparing and conferring the
functions. If ‘Alice’ wants to send a secret message to ‘Bob’, signals sent through quantum channel. In Quantum Key
he would encrypt his message with Bob’s public key and send Distribution sequence of operations are as follow:-
it via an insecure channel. ‘Bob’ receiving the message would First, Alice generates and forwards Bob a sequence of
then decode it using his private key. This methodology photons with polarizations that are chosen randomly (0, 45, 90
ensures that the sender can’t decode his own message once or 135 degrees). Bob receives the photons and chooses
encrypted. These systems make use of the fact that certain randomly whether to measure its rectilinear or diagonal
mathematical operations are simple to do in one direction than polarization for each photon. Next Bob publicizes which kind
the other. For example, multiplication of two large prime of measurement he has made (either rectilinear or diagonal)
numbers is easy but factoring the result would be infeasible if but not the measurement result for each photon. Alice tells
the number is large and computational assets are poor. RSA him openly, whether he has made the correct type of
(Rivest-Shamir-Adleman encryption Algorithm), the first PKC measurement for each photon. Alice and Bob then discard all
cryptosystem [5] obtains its security from the straightforward cases in which Bob has made the incorrect measurement or in
fact that factoring of large numbers is extremely tough. The which his detectors have failed to record a photon.
disadvantage of classical cryptosystem is that it provides no
method for detecting eavesdropping. Also, with the building
of feasible quantum computer Shor’s algorithm could easily
break RSA in polynomial time.
One-time pad (OTP) Cryptosystem
The one-time pad cryptosystem [6] created by Gilbert Vernam
in 1917 is very simple and yet, very effective. The system
[Page No. 429]
5th IEEE International Conference on Advanced Computing & Communication Technologies [ICACCT-2011] ISBN 81-87885-03-3
when there has been no eavesdropping. An added fragile end
is key storage. Once Alice and Bob have recognized the key,
they must store it until it is required. But the longer they keep
the key in, the more they are vulnerable to unauthorized
check. It is possible to build a cryptosystem based on the well-
known Einstein-Podolsky-Rosen (EPR) effect. Employing the
EPR effect, Ekert recently developed a cryptosystem that gave
assurance of security of both key storage and key distribution.
It also cannot be used practically due to the technical
infeasibility of stocking up photons for more than a tiny
portion of a second [8].
Classical V/S Quantum Cryptography
Both quantum cryptography and classical cryptography can be
compared on following dimensions:
Figure 1: Sequence of operations
Fundamental dimension
In theory, any classical private channel can be easily
monitored inertly, without the knowledge to sender or receiver
If none has eavesdropped on the quantum channel, the left
that the eavesdropping has been done. Classical physics is the
over polarizations should be shared as secret information
theory of macroscopic bodies and phenomena such as radio
between Alice and Bob. Alice and Bob next test for
signals that allows a physical property of an object to be
eavesdropping, for example, by openly evaluating and
measured without disturbing other properties. Cryptographic
discarding a randomly selected subset of their polarization
key like information is encoded in computable physical
data. If the evaluation shows proof of eavesdropping, Alice
properties of some object or signal. Thus there is open
and Bob abandon all their data and start again with a fresh lot
possibility of passive eavesdropping in classical cryptography.
of photons. Otherwise they adopt the left over polarizations as
Quantum theory which is basis of quantum cryptography is
shared secret bits, reading 0 or 45-degree photons as binary 0's
believed to direct all objects, but its consequences are mainly
and 90 or 135-degree photons as binary 1's. If she makes the
noticeable in individual atoms or subatomic particles like
incorrect measurement, then she resends Bob a photon reliable
microscopic systems. As far as classical cryptography is
with the result of her measurement, she will have forever
concerned there is frequent requirement of using longer keys
randomized the polarization originally sent by Alice for a
as computational power doubles in every 18 months and cost
particular photon, which causes errors in one fourth of the bits
of computation is reducing rapidly with time [moors law].
in Bob's data that have been subjected to attack since one has
Thus an algorithm using k bit key which is secure may not be
no information of Alice's secret choice, 50% of the time
secure in future, i.e. it needs regular updating. On the other
(probability 1/2) one will estimate exactly and 50% of the time
hand,, security in quantum cryptography is based on the basic
(probability 1/2) one will estimate incorrectly. If one estimates
principles of quantum mechanics, so the possibilities of major
exactly, then Alice's transmitted bit is received with
changes requirements for future are almost negligible.
probability 1. On the other hand, if one estimates wrongly,
then Alice's transmitted bit is received correctly with
Commercial dimensions
probability 1/2[7]. Overall the probability of accurately
Commercial solutions for QC that already exist; they are only
receiving Alice's transmitted bit is
suitable for point-to-point connections. On the other hand,
P=1.1/2+1/2.1/2=3/4
crypto chip made by the siemens and Graz technical university
[11] makes possible the creation of networks with many
The BB84 scheme was customized to produce a working
participants, and cost of €100,000 per unit, the system is very
kit of quantum cryptography at IBM. The modifications were
expensive and requires a lot of work. On other hand classical
done to handle with practical problems like noise in the
cryptography can be implemented in software and its cost for
detectors. In BB84 scheme encoding is done as single
consumer is almost zero. Also, cryptographic system based on
polarized photon for each bit but this kit encodes each bit in a
classical cryptography can be implemented on small hardware
dim flash of light. This initiates a fresh eavesdropping danger
component like smart card , but this is major issue in case of
to the system, if Eve taps into the beam; splitting each flash
quantum cryptography shrinkage to such a level require too
into two flashes of lesser intensity can be done, evaluating one
much development.
for her while letting the other move to Bob. If Eve diverts only
a meek fraction of the beam, Bob may not see the abating
Application dimensions
signal, or may take it as expected losses in the channel. This
The digital signatures reveal the authenticity of the digital data
attack can be successfully let down by reducing data
to the receiver. A digital signature assures recipient that the
transmission rate, by sending very dim flashes of an intensity
message was formed by a known sender, and it was not
less than one photon per flash on average. Another problem is
changed in transit. The three main algorithms are key
that available detectors for a moment produce a reaction even
generation, signing, and key verification. But we know that
when no photon has been arrived which sources errors even
[Page No. 430]
Quantum Cryptography & its Comparison with Classical Cryptography: A Review Paper
algorithms cannot be implemented in QC very easily. Conclusion
Therefore QC lacks many critical features like digital Quantum cryptography is based on mixture of concepts from
signature, certified mail etc. quantum physics and information theory. The security
standard in QC is based on theorems in classical information
Technological dimensions theory and on the Heisenberg’s uncertainty principle.
Chinese scientists accomplished the worlds most long-distance Experiments have demonstrated that keys can be exchanged
of quantum communication transmission (teleportation), or as over distances of a few miles at low bit rate. Its combination
"instant matter transmission technology" technology. From the with classical secret key cryptographic algorithms permits
China University of Technology and researchers at Tsinghua increasing the confidentiality of data transmissions to an
University, Hefei National Laboratory in their free-space extraordinary high level. From comparison, it’s obvious that
quantum communication experiments, and effectively enlarges quantum cryptography (QC) is having more advantage than
the communication distance to 10 miles [9]. But classical Classical Cryptography (CC) though some issues are yet to be
cryptography can be used to communication distance of solved. This is mainly due to the implementation problems but
several million miles. According to the latest research, in future there exist possibilities that most of the problems in
Toshiba achieve new record bit rate for quantum key quantum cryptography will get resolved.
distribution, that is, 1 Mbit/s on average [10]. On the other
hand the bit rate of classical cryptography depends on the
computational power largely. Challenges & Future Direction
In the future, enhancing the performance of practical QKD
Other dimensions systems and further improvements, both in key rate and secure
Communication medium is not an issue in classical transmission distance, are necessary for some applications.
cryptography because its security depends only on the Another vital point is that, in real life, that is, quantum signals
computational complexity. Thus, this removes the need for may share the channel with regular classical signals. The final
excessively secure channels. On the other hand goal is to achieve a client affable QKD system that can be
communication of quantum cryptography require a quantum effortlessly included in the Internet. To achieve a higher QKD
channel like optical fiber or through air (wireless), also, there key rate, one can consider other QKD protocols. Continuous
is constantly a likelihood of modification in polarization of variable QKD is projected to get a higher key rate in the small
photon due to Birefringence effect or rough paths that cause and medium transmission distance. Still, the scalability is a big
change in refractive index due to damage sometimes. Also, an challenge, as no one knows how to build a large scale
n bit classical register can store at any moment exactly one n- quantum computer, which is interesting subject to be worked
bit string. Whereas an n-qubit quantum register can store at out.
any moment a superposition of all 2n n-bit strings.
References
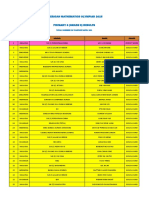
Comparison of Quantum and Classical Cryptography
[1] C. Bennett and G. Brassard, in Proceedings of IEEE,
Features Quantum Classical International Conference on Computers, Systems.
cryptography cryptography [2] Hughes, Richard J., D.M. Alde, P. Dyer, G.G. Luther,
Basis Quantum Mathematical G.L. Morgan, and M. Schauer, Quantum
mechanics computation cryptography, Contemporary Physics, Vol. 36, No. 3
Development Infantile & not Deployed and tested (1995).
tested fully [3] Applied Cryptography, Second Edition: Protocols,
Existing Sophisticated Widely used Algorithms, and Source Code in C (cloth) Author(s):
Infrastructure Bruce Schneier.
Digital Signature Not present Present [4] FIPS. 46-3, ‘“Data Encryption Standard,” Federal
Bit rate 1Mbit/s avg.[10] Depend on Information Processing Standard (FIPS), Publication
Computing power 46-3, National Bureau of Standards, US. Department
Cost Crypto chip Almost zero of Commerce, Washington D.C., October 25, 1999.
€100,000[11] [5] R.L. Rivest, “Dr. Ron Rivest on the Difficulty of
Register storage (n one n-bit string 2n n-bit strings Factoring,” Cipher text: The RSA Newsletter, v. 1, n.
bit) at any moment 1, fall 1993, pp. 6-8.
Communication 10 miles max.[9] Million of miles [6] G. R. Blakley, “One Time Pads Are Key Safeguarding
Range Schemes, Not Cryptosystems Fast Key Safeguarding
Requirements Devoted h/w & S/w and portable Schemes (Threshold Schemes) Exist.” , Proceedings of
communication. the 1980 IEEE Symposium on Security and Privacy,
1980, pp. 108-113.
lines
[7] Charles H. Bennett, Gilles Brassard, and Artur K.
Life No change as based Require changes as
Ekert "Quantum Cryptography", Scientific
expectancy on physics laws computing power
American 267:4, (October 1992).
increases
[8] Einstein, A., B. Podolsky, N. Rosen, Can quantum,
Medium Dependent Independent
[Page No. 431]
5th IEEE International Conference on Advanced Computing & Communication Technologies [ICACCT-2011] ISBN 81-87885-03-3
mechanical description of physical reality be
considered complete?, Phys. Rev. 47, 777 (1935).
[9] Quantum communication transmission experiments
http://www.waybeta.com/news/10441/quotquantum-
communication-transmissionquot-experiments-in-
china-_-the-success-of-huawei-wireless-network-card-
news/
[10] Cambridge Lab of Toshiba
http://www.physorg.com/news191010509.html
[11] Affordable Quantum Cryptography
http://www.siemens.com/innovation/apps/pof_microsit
e/_pof-spring-2009/_html_en/interview-christian-
monyk.html
[Page No. 432]
You might also like
- Internship Report (Ethical Hacking)Document20 pagesInternship Report (Ethical Hacking)Sujee Reddy100% (2)
- Assignment 2 - Part 2 - CryptographyDocument11 pagesAssignment 2 - Part 2 - CryptographyPJ1988No ratings yet
- Quantum CryptographyDocument20 pagesQuantum CryptographyBridget SmithNo ratings yet
- A Survey On Quantum Key Distribution ProtocolsDocument9 pagesA Survey On Quantum Key Distribution ProtocolsAnonymous lVQ83F8mCNo ratings yet
- An Overview of Major Developments, Applications and Challenges in Quantum CryptographyDocument9 pagesAn Overview of Major Developments, Applications and Challenges in Quantum CryptographyInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- An Invention of Quantum Cryptography Over The Classical Cryptography For Enhancing SecurityDocument4 pagesAn Invention of Quantum Cryptography Over The Classical Cryptography For Enhancing SecurityInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- State-of-the-Art Survey of Quantum CryptographyDocument38 pagesState-of-the-Art Survey of Quantum Cryptographyehtesham.k90No ratings yet
- Quantum Cryptography A ReviewDocument5 pagesQuantum Cryptography A ReviewJaime Bala NormaNo ratings yet
- Cryptography Using Quantum Key Distribution in Wireless NetworksDocument5 pagesCryptography Using Quantum Key Distribution in Wireless NetworksThet Hmue Hay ThiNo ratings yet
- Quantum Key DistributionDocument48 pagesQuantum Key DistributionANISH RAGHUVIR SHARMA 22123005No ratings yet
- Quantum Cryptography 1Document14 pagesQuantum Cryptography 1Nayana ParasharNo ratings yet
- Three Party Authenticated Key Distribution Using Quantum CryptographyDocument3 pagesThree Party Authenticated Key Distribution Using Quantum CryptographyIJMERNo ratings yet
- Quantum Cryptography:: Information Protection For The Quantum AgeDocument15 pagesQuantum Cryptography:: Information Protection For The Quantum Ageamitom_pandey4974100% (1)
- ECE - Network - KrantishDocument4 pagesECE - Network - KrantishTJPRC PublicationsNo ratings yet
- Quantum Key Distribution: A Revolutionary Security TechnologyDocument8 pagesQuantum Key Distribution: A Revolutionary Security Technologydrg1No ratings yet
- Quantum Cryptography: Realizing Next Generation Information SecurityDocument4 pagesQuantum Cryptography: Realizing Next Generation Information SecurityInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Advanced Encryption Standards (Aes)Document13 pagesAdvanced Encryption Standards (Aes)pulikondaNo ratings yet
- Quantum Cryptography State-Of-Art, Challenges and Future PerspectivesDocument7 pagesQuantum Cryptography State-Of-Art, Challenges and Future Perspectivesshahriar.iqbal.devNo ratings yet
- Cryptographic Algorithms and Current TrendsDocument13 pagesCryptographic Algorithms and Current TrendsvignanarajNo ratings yet
- (IJCST-V5I3P31) :P. Rajesh Kannan, Dr. MalaDocument5 pages(IJCST-V5I3P31) :P. Rajesh Kannan, Dr. MalaEighthSenseGroupNo ratings yet
- The New Approach of Quantum Cryptography in Network SecurityDocument5 pagesThe New Approach of Quantum Cryptography in Network SecuritySelvaKumarNo ratings yet
- Exploring Polymorphic Algorithmsandtheirusein Cryptography CCWC2024Document8 pagesExploring Polymorphic Algorithmsandtheirusein Cryptography CCWC2024Dương Trần Mỹ LinhNo ratings yet
- Quantum Computing and Blockchain:: The Definitive GuideDocument40 pagesQuantum Computing and Blockchain:: The Definitive GuideAndrés Cárdenas NovoaNo ratings yet
- Quantum Cryptography Research PaperDocument7 pagesQuantum Cryptography Research PaperDương Trần Mỹ LinhNo ratings yet
- Quantum Cryptography Thesis 2013Document9 pagesQuantum Cryptography Thesis 2013aaqvuknbf100% (2)
- Neural Cryptography For Secret Key ExchangeDocument4 pagesNeural Cryptography For Secret Key ExchangeIJMTST-Online JournalNo ratings yet
- Chaos Based Direct Public Verifiable Signcryption Scheme: Richa, Parvinder SinghDocument7 pagesChaos Based Direct Public Verifiable Signcryption Scheme: Richa, Parvinder SinghInternational Organization of Scientific Research (IOSR)No ratings yet
- Quantum Cryptography ThesisDocument7 pagesQuantum Cryptography ThesisDoMyCollegePaperJackson100% (2)
- Chapter 2 & 3Document20 pagesChapter 2 & 3Yakubu AliuNo ratings yet
- Information SecurityDocument11 pagesInformation Securityapi-3798998No ratings yet
- Index: 3.1 Private Key Algorithm 3.2 Public Key Algorithm 3.3 Hash FunctionsDocument11 pagesIndex: 3.1 Private Key Algorithm 3.2 Public Key Algorithm 3.3 Hash FunctionsYogesh YadavNo ratings yet
- Cryptography ReportDocument6 pagesCryptography ReportSakthiSriNo ratings yet
- Cs8792 Notes CnsDocument277 pagesCs8792 Notes CnsMathioli SenthilNo ratings yet
- Submitted By: A.Irfana Cse-First Year Deepthi Cse-First YearDocument14 pagesSubmitted By: A.Irfana Cse-First Year Deepthi Cse-First YearNiranjan ChandarrajNo ratings yet
- Research Paper On Classical CryptographyDocument6 pagesResearch Paper On Classical Cryptographyhjuzvzwgf100% (1)
- AMPC A Lightweight Hybrid Cryptographic Algorithm For Wireless Sensor NetworksDocument5 pagesAMPC A Lightweight Hybrid Cryptographic Algorithm For Wireless Sensor NetworksInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Network Security Using CryptographyDocument11 pagesNetwork Security Using CryptographySheema HazariNo ratings yet
- WIll Quantum Inventions Be The End of Public Keys IB EEDocument19 pagesWIll Quantum Inventions Be The End of Public Keys IB EELareb DrighNo ratings yet
- Cryptography Course WorkDocument27 pagesCryptography Course WorkSovan PalNo ratings yet
- CB3491 NotesDocument192 pagesCB3491 NotesANITHARANI KNo ratings yet
- Cryptographic Hash FunctionsDocument29 pagesCryptographic Hash FunctionsMarcos CorrêaNo ratings yet
- Quantum ComputersDocument13 pagesQuantum ComputersAayush GargNo ratings yet
- 2006 A Cryptosystem Based On Vigenère Cipher With Varying KeyDocument6 pages2006 A Cryptosystem Based On Vigenère Cipher With Varying Keyma za reNo ratings yet
- The Review of The Commercial Quantum Key Distribution SystemDocument6 pagesThe Review of The Commercial Quantum Key Distribution SystemImogen SmithNo ratings yet
- ON Cryptography: BY: Deepak Krishna 08/ ME/08 Mechanical Fiem, KolkataDocument14 pagesON Cryptography: BY: Deepak Krishna 08/ ME/08 Mechanical Fiem, KolkataEmanuel MaričićNo ratings yet
- Combined Strength of Steganography and Cryptography-A Literature SurveyDocument4 pagesCombined Strength of Steganography and Cryptography-A Literature SurveyFalasifaNo ratings yet
- Computer Security Chapter 2-3-4-1Document72 pagesComputer Security Chapter 2-3-4-1guta lamessaNo ratings yet
- Hill DecryptionDocument49 pagesHill DecryptionDhamodaran SrinivasanNo ratings yet
- 1 s2.0 S2590005622000777 MainDocument27 pages1 s2.0 S2590005622000777 MainMila Datul MuharromahNo ratings yet
- Cryptography Prior To The Modern Age Was Effectively Synonymous WithDocument3 pagesCryptography Prior To The Modern Age Was Effectively Synonymous Withanmathew00No ratings yet
- Seminar RepDocument55 pagesSeminar RepArpit SharmaNo ratings yet
- Cryptography and Network Security Lecture NotesDocument171 pagesCryptography and Network Security Lecture NoteskomalNo ratings yet
- Secure Data Communication and Cryptography Based On DNA Based Message EncodingDocument6 pagesSecure Data Communication and Cryptography Based On DNA Based Message EncodingHaroonRashidNo ratings yet
- Encryption and Decryption System Using Rc4Document11 pagesEncryption and Decryption System Using Rc4Atul KhadeNo ratings yet
- The Technical Presentation Is OnDocument2 pagesThe Technical Presentation Is OnSesha Sai VavillaNo ratings yet
- Seminar ReportDocument34 pagesSeminar ReportJayant KumarNo ratings yet
- A Three Party Authentication For Key Distributed Protocol Using Classical and Quantum CryptographyDocument6 pagesA Three Party Authentication For Key Distributed Protocol Using Classical and Quantum Cryptographyleks_2007No ratings yet
- Quantum Cryptography Thesis PDFDocument7 pagesQuantum Cryptography Thesis PDFlorischadedesmoines100% (2)
- Network Security Using A Symmetric Key CryptographyDocument2 pagesNetwork Security Using A Symmetric Key CryptographyInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Cryptography And Computer Science: Design Manual For Algorithms, Codes And CiphersFrom EverandCryptography And Computer Science: Design Manual For Algorithms, Codes And CiphersNo ratings yet
- Lec2 UniversalDocument163 pagesLec2 UniversalcheintNo ratings yet
- Lec1 IntroDocument119 pagesLec1 IntrocheintNo ratings yet
- Lec 6Document154 pagesLec 6cheintNo ratings yet
- Deep Learning 115Document3 pagesDeep Learning 115cheintNo ratings yet
- Lec4 Learning PresentedDocument101 pagesLec4 Learning PresentedcheintNo ratings yet
- Lec 5Document175 pagesLec 5cheintNo ratings yet
- Lec1.Intro 2Document110 pagesLec1.Intro 2cheintNo ratings yet
- Lec3 LearningDocument135 pagesLec3 LearningcheintNo ratings yet
- DL in Computer VisionDocument13 pagesDL in Computer VisioncheintNo ratings yet
- Modified SHA256 For Block ChainDocument5 pagesModified SHA256 For Block ChaincheintNo ratings yet
- Applications of DL For CV 23Document6 pagesApplications of DL For CV 23cheintNo ratings yet
- Cyber Security On Smart GridDocument14 pagesCyber Security On Smart Gridcheint100% (1)
- Smart City Cyber Security ArchitectureDocument38 pagesSmart City Cyber Security ArchitecturecheintNo ratings yet
- Primary 5 (Grade 5) Answers: Singapore International Math Olympiad Challenge 2015Document1 pagePrimary 5 (Grade 5) Answers: Singapore International Math Olympiad Challenge 2015cheintNo ratings yet
- Cyber Security of Critical InfrastructuresDocument4 pagesCyber Security of Critical InfrastructurescheintNo ratings yet
- Cryptarithms Worksheet NewDocument1 pageCryptarithms Worksheet NewcheintNo ratings yet
- Primary 5 (Grade 5) Answers: Singapore International Math Olympiad Challenge 2015Document1 pagePrimary 5 (Grade 5) Answers: Singapore International Math Olympiad Challenge 2015cheintNo ratings yet
- Cryptarithms Worksheet NewDocument1 pageCryptarithms Worksheet Newcheint100% (1)
- Lecture Notes On Mathematical Olympiad Courses: For Junior Section Vol. 2Document12 pagesLecture Notes On Mathematical Olympiad Courses: For Junior Section Vol. 2cheintNo ratings yet
- Teachers' Manual: United States of America Mathematical Olympiad United States of America Junior Mathematical OlympiadDocument28 pagesTeachers' Manual: United States of America Mathematical Olympiad United States of America Junior Mathematical OlympiadcheintNo ratings yet
- American Mathematics Olympiad 2015 Primary 6 (Grade 6) ResultsDocument10 pagesAmerican Mathematics Olympiad 2015 Primary 6 (Grade 6) ResultscheintNo ratings yet
- New Encryption AlgorithmDocument5 pagesNew Encryption AlgorithmcheintNo ratings yet
- Traffic Shield: Rainer SingerDocument30 pagesTraffic Shield: Rainer SingerNew ComersNo ratings yet
- What Is GPG ?Document2 pagesWhat Is GPG ?Rama KrishnanNo ratings yet
- CrossWordPuzzle Chap 9Document3 pagesCrossWordPuzzle Chap 9NurizzzNo ratings yet
- Da 05Document9 pagesDa 05Rajvansh SinghNo ratings yet
- Is CombinedDocument566 pagesIs Combinedlolzcat3454No ratings yet
- SECURING ProjectDocument23 pagesSECURING Projectsaadsidd22No ratings yet
- Cyberoam Unified Threat Management - An IntroDocument20 pagesCyberoam Unified Threat Management - An Introrajesh_cbrmNo ratings yet
- Cryptographic Security in Embedded SystemsDocument14 pagesCryptographic Security in Embedded SystemsJayes JayesNo ratings yet
- Network Security NotesDocument170 pagesNetwork Security NotesJega DeesanNo ratings yet
- Guess-And-Determine Attacks On SNOW-Vi Stream CiphDocument36 pagesGuess-And-Determine Attacks On SNOW-Vi Stream CiphHARSHITHA R Ece-2019-23No ratings yet
- Facebook Log in Test CaseDocument3 pagesFacebook Log in Test CaseTeo FloareaNo ratings yet
- OWASP MASVS Spain Nov 17Document47 pagesOWASP MASVS Spain Nov 17betosecNo ratings yet
- IDirect TRANSEC - Advanced OverviewDocument13 pagesIDirect TRANSEC - Advanced Overviewkira0190% (1)
- Approach To Auditing Network Security: by S. Anantha SayanaDocument3 pagesApproach To Auditing Network Security: by S. Anantha SayanaJohn Rey Bantay RodriguezNo ratings yet
- Fortigate: 52 MCQ Questions & Answers With ExplanationsDocument18 pagesFortigate: 52 MCQ Questions & Answers With ExplanationsAndi LloydNo ratings yet
- # 037-013 Mayer Steel Pipe Corp. 50ingDocument3 pages# 037-013 Mayer Steel Pipe Corp. 50ingChristopher Monserate PiojoNo ratings yet
- 1a.4 MNEXT ProfileDocument6 pages1a.4 MNEXT ProfileSham KumbharNo ratings yet
- Two-Factor AuthenticationDocument2 pagesTwo-Factor Authenticationumair riazNo ratings yet
- DesDocument19 pagesDesAmir HelmiNo ratings yet
- SG 248525Document208 pagesSG 248525onlinenandaNo ratings yet
- Red Hat JBoss Fuse-6.3-Security Guide-en-USDocument136 pagesRed Hat JBoss Fuse-6.3-Security Guide-en-USEDPAEZNo ratings yet
- Top 10 Pci Dss Compliance PitfallsDocument4 pagesTop 10 Pci Dss Compliance PitfallsdurgasainathNo ratings yet
- EncryptionDocument3 pagesEncryptionVinny SashaNo ratings yet
- Omron MR504DV & GreenBow IPsec VPN ConfigurationDocument14 pagesOmron MR504DV & GreenBow IPsec VPN Configurationgreenbow100% (1)
- Compliance BigFixDocument5 pagesCompliance BigFixjwgibson949No ratings yet
- Smart Card Presentation For Trinity9-02Document13 pagesSmart Card Presentation For Trinity9-02rsb1962100% (2)
- CipherDocument9 pagesCipherAnonymous jpeHV73mLzNo ratings yet
- Anyconnect GuideDocument46 pagesAnyconnect GuideomoboyNo ratings yet
- Instructions:: Application For Digital CertificateDocument4 pagesInstructions:: Application For Digital CertificateClaire OrogoNo ratings yet