Professional Documents
Culture Documents
CO1508 Computer Systems & Security - Week 07 Cryptography - Hash Functions & Digital Signatures
CO1508 Computer Systems & Security - Week 07 Cryptography - Hash Functions & Digital Signatures
Uploaded by
Edward LeeOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
CO1508 Computer Systems & Security - Week 07 Cryptography - Hash Functions & Digital Signatures
CO1508 Computer Systems & Security - Week 07 Cryptography - Hash Functions & Digital Signatures
Uploaded by
Edward LeeCopyright:
Available Formats
Page 1 of 7
CO1508 Computer Systems & Security – Week 07
Cryptography – Hash Functions & Digital Signatures
Summary
You are going to learn a new hash algorithm called Hash Message Authentication Code
(HMAC) and practice some examples of other hash functions such as MD5 and SHA-1 using
Cryptool 1. You’ll also learn about digital signatures, RSA signature and mount attacks
against the hash value of a digital signature.
Activities
1. HMAC Hash Algorithm
Keyed Hash Message Authentication Code (HMAC) ensures integrity and authentication of a
message. It requires a common key for both sender and recipient. It follows similar principle
of other hash algorithms but adds a secret key to the process.
Open Cryptool 1 and select Indiv. Procedures > Hash > Generation of HMACs. Read the
description carefully before proceeding.
CO1508 Computer Systems and Security, UCLAN – 2019-2020
Page 2 of 7
Select SHA-1 as a hash function and double hashing as HMAC variants.
Enter your key “cowabunga”. The HMAC code generated from the message and the key is
72 28 A5 7D 50 11 86 09 2E C2 C4 76 2C 98 9A 49 AA C9 E5 6A
Now, select from Indiv. Procedures > Hash > Hash Demonstration.
Select a hash function from Selection of hash function (any hash function you want).
Add a space after ‘CrypTool’ in the plaintext. You will see at least 47% to 53% bits differ. A
good hash function reacts highly sensitively to even the smallest change in the plaintext:
Avalanche effect (small change, big impact).
Now, for the following exercises you can select either SHA-1, HMAC, or MD5.
Exercise 1
Use an example to show that Hash function can help to protect the integrity of your
message. You can encrypt your plaintext message, tamper the ciphertext and use hash
function to check whether the decrypted messaged is changed.
Exercise 2
Use an example to show that if you tamper both ciphertext and hash value properly, you
can escape from the integrity check of the hash function.
CO1508 Computer Systems and Security, UCLAN – 2019-2020
Page 3 of 7
Show your tutor your solutions before moving on to the next stage.
2. Digital Signature Visualisation
Select from Digital Signatures/PKI > Signature Demonstration (Signature Generation)
Click on “Select hash function”. Choose SHA-1 and click OK
Click “Generate Key” and “Generate prime numbers” in the dialogue then enter 2^200 as
the lower limit and 2^201 as upper limit and click Generate prime numbers and apply
primes.
Click Store key button.
Click Provide certificate then enter your details:
Name: Your last name
First name: Your first name
Key identifier: Your key
PIN: cryptool
PIN verification: cryptool
Then click “Create Certificate and PSE”. Click on Certificate and have a look at the
generated one with your name.
CO1508 Computer Systems and Security, UCLAN – 2019-2020
Page 4 of 7
Click Compute hash value then Encrypt hash value.
Now, click Generate signature then Store signature.
Click OK and you’ll see the digital signature generated using RSA and SHA-1 (as hash
algorithm) for the document startingexample-en.txt
Close the signature window before moving on to the next stage.
3. RSA Digital Signature
Select Digital Signatures/PKI > PKI > Generate/Import Keys.
Enter your details as you did before, keep everything to default and click on Generate new
key pair button.
After receiving the confirmation message, click OK then click Show key pair…
Choose your new generated key and click on Show certificate
Now, close all the windows and make sure the startingexample-en.txt is open. We’ll sign
this document as follows:
CO1508 Computer Systems and Security, UCLAN – 2019-2020
Page 5 of 7
Select Digital Signatures/PKI > Sign Message and enter the following details:
Choose hash function: SHA-1
Choose signature algorithm: RSA
Choose a key/PSE to be used when signing: Your key
PIN code: cryptool
And click on Sign button.
Now, examine the signature. You’ll notice the signature is at the beginning of the document
to be signed.
To get a clearer idea, choose Digital Signature/PKI > Extract Signature to see clearly the
signature value and document that is signed.
Click on Verify to verify the signature and choose the right originator from the list. If it’s
correct, you’ll receive a message saying, “Correct signature!”
Try to modify the text by adding/deleting something and try Digital Signature/PKI > Verify
Signature again. You should receive a negative result this time “Invalid signature!”
This is how digital signatures can guarantee the integrity of the message to make sure it’s
not altered or tampered with.
CO1508 Computer Systems and Security, UCLAN – 2019-2020
Page 6 of 7
4. Exploiting Hash Collision to Attack Digital Signatures
Before we start, remember that hash collision occurs when two different messages produce
the same hash value. We’ll try to exploit this vulnerability to break the digital signature.
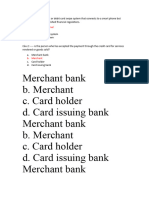
Select Analysis > Hash > Attack on the Hash Value of the Digital Signature. Click Options
and select MD5 under Hash function and 40 for Significant bit length and click Apply.
After that, click Start search and wait ☺ You should then receive a message saying the
attack was successful. Click OK to move on. You should see something like this:
Close this window and have a look at the two messages: harmless message and dangerous
message. It’s two different messages with the same hash value, which means you can get
CO1508 Computer Systems and Security, UCLAN – 2019-2020
Page 7 of 7
the original message (ordering a typewriter), modify it (to order Porsche!), sign it again
(using the receiver’s public key) and it’ll be undetected!!!
You can try larger numbers than 40 for the Significant bit length. However, beware that the
larger you go the longer it’ll take to find a successful attack (it might take days if you put 128
bits). Don’t try this now ☺ unless you want to sleep here for the next few days waiting!
Exercise 3
Generate a new key pair and a digital signature for a file you choose. Then, export the public
key and the signature to two different files.
Verify the digital signature by importing the public key and the signature that is alleged to
be the signature of the specified data file (you’ve chosen) and to verify the authenticity of
the signature.
Exercise 4
List the frequencies for the top 4 characters found in the following ciphertext then break it:
MKLAJZHAIUQWKHJABZNXBVHAGKFASDFGALQPIWRYIOQYWIERMASVZMNBZXCKJASDFGLK
JFHWQERYIOQWTYIOASUDYFLASKJDHFZMZVBCXMVQLWERYIQRASDFQIWUERYIHKMFMAK
HLSDFYUIOQWYREIORYIWQEUFHAKDFHLKASHFKVBBBNASMDFSADFWQEUYRUUEYRUUUQ
KASJHFKJDSHFSNBNBNBNBABABAAASKJFHLKJSADHFIDUASFOYDASIYFQWERBQWBRKLJLKAS
SADFDFDASDA.
Exercise 5
Break this ciphertext. What is the plaintext? What is the key?
OTWEWNGWCBPQABIZVQAPMLJGZWTTQVOBQUMAPMIDGZCAB
EQVBMZLZIXMLAXZQVOQVLMMXAVWEIVLLIZSNZWAB
JQZLWNLMTQOPBVIUMLGWCBPAEQNBTGTMNBBPMVMAB
ITIAKWCTLVBBQUMQBEPQTMQBEIAQVUGBZCAB
CO1508 Computer Systems and Security, UCLAN – 2019-2020
You might also like
- Honeypot Token GuideDocument23 pagesHoneypot Token GuideHaanz Dirtyfinger0% (1)
- ChapterReviewAnswers For Security+ Guide To Network SecurityDocument28 pagesChapterReviewAnswers For Security+ Guide To Network SecurityDerrick S Gabbard60% (10)
- How to Hack Like a Legend: Hacking the Planet, #7From EverandHow to Hack Like a Legend: Hacking the Planet, #7Rating: 4.5 out of 5 stars4.5/5 (5)
- Assignment Network and SecurityDocument4 pagesAssignment Network and SecurityTryson SikanyikaNo ratings yet
- Cyber Ark NISTDocument14 pagesCyber Ark NISTvqbhanu50% (2)
- Actualtests: Topping Certification Exam Prep, Test Dumps Materials - ActualtestsitDocument8 pagesActualtests: Topping Certification Exam Prep, Test Dumps Materials - ActualtestsitFaim HasanNo ratings yet
- Cs 6Document10 pagesCs 6Danish ShaikhNo ratings yet
- LAB2 ElecCertificate&SignatureDocument11 pagesLAB2 ElecCertificate&Signaturerayhane.gouissemNo ratings yet
- CryptoBench User's GuideDocument6 pagesCryptoBench User's GuideEmilianoNo ratings yet
- Pet ExplainedDocument11 pagesPet ExplainedTommy CookseyNo ratings yet
- Cryptography Demo ScriptDocument9 pagesCryptography Demo ScriptAndreEa Corbu-OpreaNo ratings yet
- Question 1: SHA AlgorithmDocument10 pagesQuestion 1: SHA AlgorithmAruni MishraNo ratings yet
- How Encryption Works: in The Key Of..Document5 pagesHow Encryption Works: in The Key Of..tksctr1No ratings yet
- SSL Torn ApartDocument20 pagesSSL Torn Apartapi-3696720No ratings yet
- SSL Certificates HOWTODocument4 pagesSSL Certificates HOWTOArjun MuruganNo ratings yet
- DCN Unit4Document36 pagesDCN Unit4sandipgawali.mca23No ratings yet
- Lab 8Document14 pagesLab 8Avinash AvuthuNo ratings yet
- Cryptographic Hash FunctionsDocument16 pagesCryptographic Hash FunctionsUrvil SitapareNo ratings yet
- UCA 2021 Information Security ExamDocument18 pagesUCA 2021 Information Security ExamGullayazNo ratings yet
- PS-IV Practical 1 - MergedDocument29 pagesPS-IV Practical 1 - Mergedadityarangari09No ratings yet
- Practical - 11360603 - Web and Network Security.Document26 pagesPractical - 11360603 - Web and Network Security.harshil15082004No ratings yet
- Unit3 Cryptography and Cyber SecurityDocument4 pagesUnit3 Cryptography and Cyber SecuritypraveenaNo ratings yet
- Exam Information: Digital Exam in IN2120 "Informasjonssikkerhet" (Autumn 2019)Document28 pagesExam Information: Digital Exam in IN2120 "Informasjonssikkerhet" (Autumn 2019)dasdNo ratings yet
- Unit V CryptoDocument8 pagesUnit V CryptoPriya SNo ratings yet
- Message DigestDocument27 pagesMessage DigestArjunSahooNo ratings yet
- Introduction To Cain and Abel Cracking ToolDocument6 pagesIntroduction To Cain and Abel Cracking ToolallongongNo ratings yet
- 7 CryptographyDocument131 pages7 CryptographyYoraismeNo ratings yet
- Muhammad Iqbal - Combination of MD5 and ElGamal in Verifying File Authenticity and Improving Data SecurityDocument6 pagesMuhammad Iqbal - Combination of MD5 and ElGamal in Verifying File Authenticity and Improving Data SecurityMaya BoutebNo ratings yet
- Computer Sienece 1Document3 pagesComputer Sienece 1poiuret isthisgoodNo ratings yet
- BlockChain UNIT 2Document19 pagesBlockChain UNIT 2manoj tilakchandNo ratings yet
- Need To Know For IT Manager About:: What Is Secured Web Application?Document3 pagesNeed To Know For IT Manager About:: What Is Secured Web Application?SagarChhedaNo ratings yet
- Is CH6Document9 pagesIs CH6Dhruv SojitraNo ratings yet
- Unit 3 Message AuthenticationDocument14 pagesUnit 3 Message AuthenticationSagar ThakurNo ratings yet
- CISA EXAM-Testing Concept-Digital SignatureFrom EverandCISA EXAM-Testing Concept-Digital SignatureRating: 3.5 out of 5 stars3.5/5 (5)
- What Is BlockchainDocument6 pagesWhat Is BlockchainmenakarameshNo ratings yet
- Blockchain & Cryptocurrency Technologies: Digital AssingmentDocument11 pagesBlockchain & Cryptocurrency Technologies: Digital Assingmentlinux tarunNo ratings yet
- Experiment 06: WWW - Oxid.it/cain - HTMLDocument8 pagesExperiment 06: WWW - Oxid.it/cain - HTMLpatilNo ratings yet
- Crypto 2Document8 pagesCrypto 2sangeetha manjulaNo ratings yet
- What Is Cryptography?: Decryption Secret KeyDocument7 pagesWhat Is Cryptography?: Decryption Secret KeyalvincardonaNo ratings yet
- information2Document17 pagesinformation2rohit972012No ratings yet
- Net Security Chap 4Document6 pagesNet Security Chap 4Asif KoujaganurNo ratings yet
- Digital SignatureDocument5 pagesDigital SignatureHarpreet SinghNo ratings yet
- Block Chain NotesDocument15 pagesBlock Chain Notesnaveen pareekNo ratings yet
- Digital Signatures: Hasibur Rahman ASH1711009MDocument13 pagesDigital Signatures: Hasibur Rahman ASH1711009MFarida SiddiqiNo ratings yet
- 1 InsDocument27 pages1 Insaniketshinde16052003No ratings yet
- How Secure Are Your Channels?: by Morag HughsonDocument8 pagesHow Secure Are Your Channels?: by Morag HughsonkarthickmsitNo ratings yet
- What Is Code SigningDocument4 pagesWhat Is Code Signingdarezzo.guidoNo ratings yet
- Literature Survey: 2.1 Cryptographic Hash FunctionDocument11 pagesLiterature Survey: 2.1 Cryptographic Hash Functionm1a2l3a4rNo ratings yet
- Certificates and Digital Signature TutorDocument12 pagesCertificates and Digital Signature TutorMax KleinerNo ratings yet
- Phases 4-6Document12 pagesPhases 4-6Tarik AmezianeNo ratings yet
- U Digital SignaturesDocument11 pagesU Digital SignaturestysoncandyNo ratings yet
- CS Practical 8Document5 pagesCS Practical 8atulraut3773No ratings yet
- Module 3 Module 5Document32 pagesModule 3 Module 5TEJASWINI PNo ratings yet
- Message Authentication CodeDocument6 pagesMessage Authentication CodeAyush KastNo ratings yet
- Unit 3Document22 pagesUnit 3hajirasabuhiNo ratings yet
- Maxbox Collaboration and Code SharingDocument9 pagesMaxbox Collaboration and Code SharingMax KleinerNo ratings yet
- 2.bitcoin ScriptsDocument23 pages2.bitcoin ScriptsManoj ManuNo ratings yet
- CSS UT2 QB AnsDocument13 pagesCSS UT2 QB AnsVinyasNo ratings yet
- SSL / TLS Overview Or:: How I Learned To Stop Worrying and Love The CADocument8 pagesSSL / TLS Overview Or:: How I Learned To Stop Worrying and Love The CAtteggelitNo ratings yet
- DFGHDocument17 pagesDFGHG.m. MeghrajNo ratings yet
- Exam en-GBDocument14 pagesExam en-GBColin DusartNo ratings yet
- Internet SecurityDocument6 pagesInternet SecuritynitNo ratings yet
- CYBERSECURITY FOR BEGINNERS: Essential Skills and Best Practices to Safeguard Your Digital World (2024 Guide)From EverandCYBERSECURITY FOR BEGINNERS: Essential Skills and Best Practices to Safeguard Your Digital World (2024 Guide)No ratings yet
- CO1508 - Week 05Document28 pagesCO1508 - Week 05Edward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 10: Building Your Harmless Virus in C++ - Part 1 Windows RegistryDocument8 pagesCO1508 Computer Systems & Security - Week 10: Building Your Harmless Virus in C++ - Part 1 Windows RegistryEdward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 19 - Incident Response PlanningDocument5 pagesCO1508 Computer Systems & Security - Week 19 - Incident Response PlanningEdward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 09 - Fork Bomb, Windows Pranks and Keyloggers!Document9 pagesCO1508 Computer Systems & Security - Week 09 - Fork Bomb, Windows Pranks and Keyloggers!Edward LeeNo ratings yet
- 2019-20 Assignment 1 Part 1: TasksDocument3 pages2019-20 Assignment 1 Part 1: TasksEdward LeeNo ratings yet
- 2019-20 Assignment 1 Part 2: Blackwell BuildersDocument3 pages2019-20 Assignment 1 Part 2: Blackwell BuildersEdward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 03 Cryptography Exercises - Cryptool 1Document7 pagesCO1508 Computer Systems & Security - Week 03 Cryptography Exercises - Cryptool 1Edward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 03 Cryptography Exercises - Cryptool 1 - AnswersDocument2 pagesCO1508 Computer Systems & Security - Week 03 Cryptography Exercises - Cryptool 1 - AnswersEdward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 14 - Linux Tour, Basic Commands and Text EditingDocument10 pagesCO1508 Computer Systems & Security - Week 14 - Linux Tour, Basic Commands and Text EditingEdward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 02 - Passwords, Patches and Mandatory Access Control (MAC)Document8 pagesCO1508 Computer Systems & Security - Week 02 - Passwords, Patches and Mandatory Access Control (MAC)Edward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 10: Building Your Harmless Virus in C++ - Part 1 Windows RegistryDocument8 pagesCO1508 Computer Systems & Security - Week 10: Building Your Harmless Virus in C++ - Part 1 Windows RegistryEdward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 20 Cryptography Pro Stuff and Reassessment Support!Document3 pagesCO1508 Computer Systems & Security - Week 20 Cryptography Pro Stuff and Reassessment Support!Edward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 13 Windows CMD, Batch Scripting and Some Tricks!Document10 pagesCO1508 Computer Systems & Security - Week 13 Windows CMD, Batch Scripting and Some Tricks!Edward LeeNo ratings yet
- Reminder: Setting Up A C++ Project in Visual Studio: CO1401 - Programming Workshop Sheet 1Document5 pagesReminder: Setting Up A C++ Project in Visual Studio: CO1401 - Programming Workshop Sheet 1Edward LeeNo ratings yet
- CO1508 Computer Systems & Security - Week 11 C++ Pointers and More For Your Virus/Anti-virus - Part 2Document12 pagesCO1508 Computer Systems & Security - Week 11 C++ Pointers and More For Your Virus/Anti-virus - Part 2Edward LeeNo ratings yet
- CO1508 Practical 10 Instructor NotesDocument2 pagesCO1508 Practical 10 Instructor NotesEdward LeeNo ratings yet
- CO1401 Week 3 LectureDocument32 pagesCO1401 Week 3 LectureEdward LeeNo ratings yet
- CO1508 Practical 15Document11 pagesCO1508 Practical 15Edward LeeNo ratings yet
- 1password Emergency KitDocument1 page1password Emergency KitEdward LeeNo ratings yet
- CO1401 - 1457 Week 4 LectureDocument42 pagesCO1401 - 1457 Week 4 LectureEdward LeeNo ratings yet
- CO1401 - 1457 Week 2 LectureDocument44 pagesCO1401 - 1457 Week 2 LectureEdward LeeNo ratings yet
- Compliance BigFixDocument5 pagesCompliance BigFixjwgibson949No ratings yet
- 54 APS Lab3 PDFDocument2 pages54 APS Lab3 PDFAbdias Vazquez MartinezNo ratings yet
- Bluetooth HackingDocument20 pagesBluetooth HackingasherNo ratings yet
- Cryptography ModelDocument142 pagesCryptography ModelHamzah AminNo ratings yet
- Lab 6-IAP202-IA1503-se150582-NGUYENVIETQUANGVUDocument6 pagesLab 6-IAP202-IA1503-se150582-NGUYENVIETQUANGVUNguyen Viet Quang Vu (K15 HCM)No ratings yet
- Secure Electronic TransactionDocument6 pagesSecure Electronic TransactionKirupakaran HarikrishnanNo ratings yet
- Assignment CipherDocument8 pagesAssignment CipherPalak JainNo ratings yet
- Types of Classical CiphersDocument2 pagesTypes of Classical CiphersAsmahani RashidNo ratings yet
- 2.5.2.5 Lab - Authentication Authorization AccountingDocument13 pages2.5.2.5 Lab - Authentication Authorization AccountingAndrew NNo ratings yet
- TD Security 2016 QADocument10 pagesTD Security 2016 QASamira El MargaeNo ratings yet
- BCA E Commerce Assignment ADocument5 pagesBCA E Commerce Assignment ANaveen NagalingamNo ratings yet
- Auditing-Oracle-Database Joa Eng 1114Document7 pagesAuditing-Oracle-Database Joa Eng 1114roychabNo ratings yet
- Mid TermDocument9 pagesMid Termhyd.hus54646No ratings yet
- Bitcoin Wallet Backup SheetDocument1 pageBitcoin Wallet Backup SheetstephanehaddadNo ratings yet
- Beginners Guide To Tls SSL Certificates Whitepaper en 2019Document7 pagesBeginners Guide To Tls SSL Certificates Whitepaper en 2019viswatejaNo ratings yet
- Bifid CipherDocument10 pagesBifid CipherABM ShengalyNo ratings yet
- Perform Cryptanalysis Using Various Cryptanalysis Tools-1Document23 pagesPerform Cryptanalysis Using Various Cryptanalysis Tools-1jsolaresrNo ratings yet
- Bolleting 636Document2 pagesBolleting 636Juan Carlos De Leon CoradoNo ratings yet
- नामांकन म / Enrollment No: 146Document2 pagesनामांकन म / Enrollment No: 146Mukesh MistriNo ratings yet
- 17.2.7 Lab - Certificate Authority StoresDocument7 pages17.2.7 Lab - Certificate Authority StoresntutaNo ratings yet
- CNSSI-4009 National Information Assurance PDFDocument103 pagesCNSSI-4009 National Information Assurance PDFDennisNo ratings yet
- Solution Brief Managed Detection and Response MDR PDFDocument2 pagesSolution Brief Managed Detection and Response MDR PDFnicolepetrescuNo ratings yet
- InfoSec AwarenessDocument51 pagesInfoSec AwarenessGonçalo Almeida TeixeiraNo ratings yet
- Ultimate Guide To CVS Server Administration in Fedora 6Document47 pagesUltimate Guide To CVS Server Administration in Fedora 6ATOzTOA100% (3)
- Enigma MachineDocument32 pagesEnigma Machineguitar_theoryNo ratings yet
- Step by Step To Get Your DepEd Email Account PDFDocument3 pagesStep by Step To Get Your DepEd Email Account PDFimelda sibayanNo ratings yet
- Ramrao Adik Institute of Technology, NerulDocument2 pagesRamrao Adik Institute of Technology, NerulAditya ShahNo ratings yet