Professional Documents
Culture Documents
IAA202 - LAB4 - SE140442: A. Healthcare Provider Under HIPPA Compliance Law
IAA202 - LAB4 - SE140442: A. Healthcare Provider Under HIPPA Compliance Law
Uploaded by
Đinh Khánh LinhOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
IAA202 - LAB4 - SE140442: A. Healthcare Provider Under HIPPA Compliance Law
IAA202 - LAB4 - SE140442: A. Healthcare Provider Under HIPPA Compliance Law
Uploaded by
Đinh Khánh LinhCopyright:
Available Formats
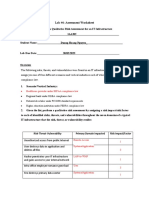
IAA202_LAB4_SE140442
Overview
The following risks, threats, and vulnerabilities were found in an IT infrastructure. Your
Instructor will assign you one of four different scenarios and vertical industries each of
which is under a unique compliance law.
1. Scenario/Vertical Industry:
A. Healthcare provider under HIPPA compliance law
B. Regional bank under GLBA compliance law
C. Nationwide retailer under PCI DSS standard requirements
D. Higher-education institution under FERPA compliance law
2. Given the list, perform a qualitative risk assessment by assigning a
risk impact/risk factor to each of identified risks, threats, and
vulnerabilities throughout the seven domains of a typical IT
infrastructure that the risk, threat, or vulnerability resides.
Risk-Threat- Primary Domain Risk Impact/Factor
Vulnerability Impacted
Unauthorized access from Remote Access Domain 1
public Internet
User destroys data in Systems/Application 3
application and deletes all Domain
files
Hacker penetrates your IT LAN-to-WAN Domain 1
infrastructure and gains
access to your internal
network
Intra-office employee User Domain 3
romance gone bad
Fire destroys primary data Systems/Application 1
center Domain
Risk-Threat- Primary Domain Risk Impact/Factor
Vulnerability Impacted
Service provider SLA is not Service provider SLA is not 3
achieved achieved
Workstation OS has a Workstation Domain 2
known software
vulnerability
Unauthorized access to Workstation Domain 1
organization owned
workstations
Loss of production data Systems/Application 2
Domain
Denial of service attack on LAN-to-WAN Domain 1
organization DMZ e-mail
server
Remote communications Remote Access Domain 2
from home office
LAN server OS has a LAN Domain 2
known software
vulnerability
User downloads and clicks User Domain 1
on an unknown
Workstation browser has a Workstation Domain 3
software vulnerability
Mobile employee needs Remote Access Domain 3
secure browser access to
sales order entry system
Service provider has a WAN Domain 2
major network outage
Weak ingress/egress traffic LAN-to-WAN Domain 3
filtering degrades
performance
User inserts CDs and USB User Domain 2
hard drives with personal
photos, music, and videos
on organization owned
computers
VPN tunneling between LAN-to-WAN Domain 2
remote computer and
ingress/egress router is
needed
WLAN access points are LAN Domain 3
needed for LAN
connectivity within a
warehouse
Need to prevent LAN Domain 1
eavesdropping on WLAN
due to customer privacy
data access
DoS/DDoS attack from the WAN Domain 1
WAN/Internet
3. For each of the identified risks, threats, and vulnerabilities,
prioritize them by listing a “1”, “2”, and “3” next to each risk, threat,
vulnerability found within each of the seven domains of a typical IT
infrastructure. “1” = Critical, “2” = Major, “3” = Minor. Define the
following qualitative risk impact/risk factor metrics:
a. “1” Critical – a risk, threat, or vulnerability that impacts compliance (i.e., privacy law
requirement for securing privacy data and implementing proper security controls,
etc.) and places the organization in a position of increased liability.
b. “2” Major – a risk, threat, or vulnerability that impacts the C-I-A of an organization’s
intellectual property assets and IT infrastructure. c. “3”Minor – a risk, threat, or
vulnerability that can impact user or employee productivity or availability of the IT
infrastructure.
User Domain Risk Impacts: (refer to previous chart)
User downloads and clicks on an unknown e-mail attachment.
User inserts CDs and USB hard drives with personal photos, music, and
videos on organization owned computers.
Intra-office employee romance gone bad
Workstation Domain Risk Impacts: (refer to previous chart)
Unauthorized access to organization owned workstations.
Workstation OS has a known software vulnerability.
Workstation browser has software vulnerability.
LAN Domain Risk Impacts: (refer to previous chart)
Denial of service attack on organization DMZ and e-mail server.
VPN tunneling between remote computer and ingress/egress router is
needed.
Weak ingress/egress traffic filtering degrades performance.
WAN Domain Risk Impacts: (refer to previous chart)
DoS/DDoS attack from the WAN/Internet.
Service provider has a major network outage.
Service provider SLA is not achieved.
Remote Access Domain Risk Impacts: (refer to previous chart)
Unauthorized access from public Internet.
Remote communications from home office.
Mobile employee needs secure browser access to sales order entry system
Systems/Applications Domain Risk Impacts:
(refer to previous chart)
Fire destroys primary data center.
Loss of production data.
User destroys data in application and deletes all files
1. What is the goal or objective of an IT risk assessment?
The goal of the RA is to identify and mitigate risks. it’s used to identify and
evaluate risks based on an analysis of threats and vulnerabilities to assets. Risks
are quantified based on their importance or impact severity. These risks are then
prioritized.
2. Why is it difficult to conduct a qualitative risk assessment for an
IT infrastructure?
It is difficult to conduct a qualitative risk assessment for an IT infrastructure because it is
hard to tell what kind of impact a given attack will have on the infrastructure. This is
based on the probability and impact of a risk. It is not based on dollar values; it instead is
done by gathering opinions of experts. They could all have a different opinion or priority
which could cause an issue.
3. What was your rationale in assigning “1” risk impact/ risk factor
value of “Critical” for an identified risk, threat, or vulnerability? I
assigned critical impact values for threats that severely
compromise patient data or that made the system useless such
as DoS attacks.
“1” was given to a risk, threat or vulnerability that impacts compliance and places the
organization in a position of increased liability
4. When you assembled all of the “1” and “2” and “3” risk
impact/risk factor values to the identified risks, threats, and
vulnerabilities, how did you prioritize the “1”, “2”, and “3” risk
elements?
What would you say to executive management in regards to your final recommended
prioritization? Management should acquire a SLA so that our systems will always be
functioning optimally. I would also recommend that the appropriate countermeasures for
threats are in place. I prioritized them by least destructive to most destructive. I would
always look at risk/threats by how much damage they could potentially cause to the
organization
5. Identify a risk mitigation solution for of the following risk
factors:
A: User downloads and clicks on an unknown e-mail attachment-- Attachments are a
significant security risk associated with emails. Effective email attachment filtering and
restrictions reduce the likelihood of malicious content entering the network.
B: Workstation OS has a known software vulnerability—Define a workstation operating
system vulnerability window policy definition. Start periodic workstation domain
vulnerability tests to find all vulnerabilities.
C: Need to prevent eavesdropping on WLAN due to customer privacy data access—Use
WLAN network keys that require a password for wireless access. Turn of broadcasting
of WAPs, require second level authentication prior to granting WLAN access.
D: Weak ingress/egress traffic filtering degrades performance—Apply WAN optimization
and data compression solutions when accessing remote systems; applications and data.
Enable Access Control lists (ACLs) on outbound router WAN interfaces in keeping with
policy.
E: DoS/DDoS attack from the WAN/Internet—Apply filter on exterior IP stateful firewalls
an IP router WAN interfaces to block TCP SYN and ICMP (ping). Alert your ISP provider
to put the proper filters on its IP router WAN interfaces in accordance with CERT
Advisory CA- 1996-21. F: Remote access from office—Apply first level and second level
security for remote access to sensitive systems, applications and data.
G: Production Server corrupts database—Implement daily data backups and off-site
data storage for monthly data archiving. Define data recovery procedures based on
defined RTOs.
User downloads and clicks on an unknown e-mail attachment – Add restrictions that
would not allow users to download or open attachments.
Workstation OS has a known software vulnerability – Try to patch the vulnerability or
create security measures that prevent that software vulnerability from being exploited.
Need to prevent eavesdropping on WLAN due to customer privacy data access – Make
sure you are using WPA2 because it uses better encryption methods.
Weak ingress/egress traffic filtering degrades performance – Customize firewall settings
DoS/DDoS attack from the WAN/Internet – Acquire more bandwidth
Remote access from home office – Allow access of specified IP addresses only.
Production server corrupts database – Use a RAID setup to mitigate loss of data
You might also like
- IS3110 Lab 1 How To Identify Threats & Vulnerabilities in An IT InfrastructureDocument3 pagesIS3110 Lab 1 How To Identify Threats & Vulnerabilities in An IT InfrastructureAdriennel40100% (7)
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- IAA4Document4 pagesIAA4na100% (1)
- Healthcare Provider Under HIPPA Compliance LawDocument8 pagesHealthcare Provider Under HIPPA Compliance LawDuong Chi Hung (K15 HCM)100% (1)
- Lab1 IAA202Document8 pagesLab1 IAA202Đào Mạnh CôngNo ratings yet
- Lab 1 - IAA202Document4 pagesLab 1 - IAA202Hoàng NguyênNo ratings yet
- Lab #4: Perform A Qualitative Risk Assessment For An It InfrastructureDocument6 pagesLab #4: Perform A Qualitative Risk Assessment For An It InfrastructureHờ Bờ LờNo ratings yet
- Project 3: Crypto - All Things Cryptography CS6035: Prof. Wenke LeeDocument4 pagesProject 3: Crypto - All Things Cryptography CS6035: Prof. Wenke LeeOnehappy FellowNo ratings yet
- Lab #1: Assessment WorksheetDocument5 pagesLab #1: Assessment WorksheetnaNo ratings yet
- Risk - Threat - Vulnerability Primary Domain ImpactedDocument4 pagesRisk - Threat - Vulnerability Primary Domain ImpactedDuong Chi Hung (K15 HCM)No ratings yet
- Iaa202 - Lab 4 - Nguyentuanlinh - Se130002 - 26012021Document9 pagesIaa202 - Lab 4 - Nguyentuanlinh - Se130002 - 26012021Dang Viet My MyNo ratings yet
- Lab #4Document6 pagesLab #4Trần Mỹ LinhNo ratings yet
- IAA Lab4 HuynhMinhHaDocument4 pagesIAA Lab4 HuynhMinhHaHuynh Minh Ha (K16HCM)No ratings yet
- Lab 4: Perform A Qualitative Risk Assessment For An IT InfrastructureDocument4 pagesLab 4: Perform A Qualitative Risk Assessment For An IT InfrastructureBí RẩyNo ratings yet
- LAB 4-Phạm Trần Trung Dũng SE150718Document4 pagesLAB 4-Phạm Trần Trung Dũng SE150718Dũng PhạmNo ratings yet
- Lab4 IAA202Document5 pagesLab4 IAA202Đào Mạnh CôngNo ratings yet
- IAA Lab6 HuynhMinhHaDocument4 pagesIAA Lab6 HuynhMinhHaHuynh Minh Ha (K16HCM)No ratings yet
- Lab 4Document6 pagesLab 4Hoàng NguyênNo ratings yet
- Lab 1: IAADocument3 pagesLab 1: IAANguyen Thanh Trung (K16HL)No ratings yet
- IAA202-LAB - 1-SE151495 - Nguyễn Huỳnh Minh ĐanDocument4 pagesIAA202-LAB - 1-SE151495 - Nguyễn Huỳnh Minh ĐanBí RẩyNo ratings yet
- Lab1 IAA202Document4 pagesLab1 IAA202phonghthe173266No ratings yet
- Lab 2 Assessment Worksheet Align Risk THDocument18 pagesLab 2 Assessment Worksheet Align Risk THChau Minh Khanh (K14 HCM)No ratings yet
- Risk-Threat-Vulnerability Primary Domain Impacted Risk Impact/FactorDocument6 pagesRisk-Threat-Vulnerability Primary Domain Impacted Risk Impact/FactorDang Viet My MyNo ratings yet
- Iaa202 Lab 04 Iam302Document9 pagesIaa202 Lab 04 Iam302Nguyen Tuan Cuong QP3044No ratings yet
- Lab #1: Assessment Worksheet Course Name: IAA202 Student Name: Chế Công Đại Instructor Name: Mai Hoang Dinh Lab Due Date: 7/1/2022Document4 pagesLab #1: Assessment Worksheet Course Name: IAA202 Student Name: Chế Công Đại Instructor Name: Mai Hoang Dinh Lab Due Date: 7/1/2022Mlem MlemNo ratings yet
- Part A - List of Risks, Threats, and Vulnerabilities Commonly Found in An IT InfrastructureDocument4 pagesPart A - List of Risks, Threats, and Vulnerabilities Commonly Found in An IT InfrastructureNguyen Viet Quang Vu (K15 HCM)No ratings yet
- Lab #1Document3 pagesLab #1Trần Mỹ LinhNo ratings yet
- Risk - Threat - Vulnerability Primary Domain ImpactedDocument5 pagesRisk - Threat - Vulnerability Primary Domain ImpactedVinh Huynh K14 HCMNo ratings yet
- Lab6 IAA202Document18 pagesLab6 IAA202Đào Mạnh CôngNo ratings yet
- Lab 6 ReportDocument8 pagesLab 6 ReportNguyen Thi Bang Chau (K16 HCM)No ratings yet
- Lab1 DungTVHE186529 IA1804Document8 pagesLab1 DungTVHE186529 IA1804Tran Viet Dung (K18 HL)No ratings yet
- IAA202 Lab1 SE140723Document4 pagesIAA202 Lab1 SE140723bui lamNo ratings yet
- Lab9 IAP202 IA1503 Se150582 NGUYENVIETQUANGVUDocument3 pagesLab9 IAP202 IA1503 Se150582 NGUYENVIETQUANGVUNguyen Viet Quang Vu (K15 HCM)No ratings yet
- Iaa202 Lab6 Se140442Document17 pagesIaa202 Lab6 Se140442Đinh Khánh LinhNo ratings yet
- Iaa202 Lab6Document17 pagesIaa202 Lab6Dao Manh Cong (K16HL)No ratings yet
- Lab 6 Identify Threats and Vulnerabilities in An IT Infrastructure Object of LAB6Document3 pagesLab 6 Identify Threats and Vulnerabilities in An IT Infrastructure Object of LAB6Henry WiliamNo ratings yet
- Course Name: IAA202 Student Name: Chế Công Đại Instructor Name: Mai Hoang Dinh Lab Due Date: 9/2/2022Document8 pagesCourse Name: IAA202 Student Name: Chế Công Đại Instructor Name: Mai Hoang Dinh Lab Due Date: 9/2/2022Công ĐạiNo ratings yet
- Lab 03Document6 pagesLab 03truongvg2003No ratings yet
- IAA202 - LAB06 - Ngô Hiến Hào - SE161178Document13 pagesIAA202 - LAB06 - Ngô Hiến Hào - SE161178Hào NgôNo ratings yet
- Lab3 SE150956Document4 pagesLab3 SE150956Nhật TrầnNo ratings yet
- Lab3 IAP301Document11 pagesLab3 IAP301thuyptmhe171100No ratings yet
- (IS3110) Week 1 - LabDocument4 pages(IS3110) Week 1 - Labrussell nielsen0% (1)
- Laboratory 1Document11 pagesLaboratory 1Tran Viet Dung (K18 HL)No ratings yet
- IAP301 SE161501 Lab3Document6 pagesIAP301 SE161501 Lab3Le Trung Son (K16HCM)No ratings yet
- Lab 3Document4 pagesLab 3Nguyen Dinh Quan (K15 HCM)No ratings yet
- Lab 1Document6 pagesLab 1Nguyễn Thành Đạt (Nguyễn Thành Đạt)No ratings yet
- Managing Risk in Information Systems: Student Lab ManualDocument9 pagesManaging Risk in Information Systems: Student Lab Manualnguyen hong haNo ratings yet
- Lab 2 IAA202Document4 pagesLab 2 IAA202Anh DucNo ratings yet
- Endpoint SecurityDocument12 pagesEndpoint SecurityCagatay alpNo ratings yet
- Labsheet 10 Basic SecurityDocument4 pagesLabsheet 10 Basic Securitykakran15No ratings yet
- 1.4.1.1 Lab - Researching Network Attacks and Security Audit ToolsDocument4 pages1.4.1.1 Lab - Researching Network Attacks and Security Audit Toolssafwan eshamasulNo ratings yet
- Chapter Six: IS Network and Telecommunications RisksDocument34 pagesChapter Six: IS Network and Telecommunications RisksJay ManNo ratings yet
- IT ThreatsDocument53 pagesIT ThreatsDiana RoșcaNo ratings yet
- Lecture 5 - Cybersecurity Risks ThreatsDocument33 pagesLecture 5 - Cybersecurity Risks ThreatsYahya MakarimNo ratings yet
- Lab #3 - Assessment WorksheetDocument4 pagesLab #3 - Assessment WorksheetLe Quang Vu (K16HCM)No ratings yet
- Forensics Assignment (Main)Document31 pagesForensics Assignment (Main)Mohammad Raf'atiNo ratings yet
- 6 - Security Part I - Auditing Operating Systems and NetworksDocument68 pages6 - Security Part I - Auditing Operating Systems and Networkszara janeNo ratings yet
- Nt2580 Project1Document4 pagesNt2580 Project1RandyGallegosJrNo ratings yet
- LAB 1 ASSESSMENT WORKSHEET Identify ThreDocument5 pagesLAB 1 ASSESSMENT WORKSHEET Identify ThreLâm BạchNo ratings yet
- Iaa 2Document7 pagesIaa 2naNo ratings yet
- FRS301 Lab5 Se140442Document8 pagesFRS301 Lab5 Se140442Đinh Khánh LinhNo ratings yet
- IAA202 - LAB1 - SE140442: RISK, Threats and VulnerabilitiesDocument11 pagesIAA202 - LAB1 - SE140442: RISK, Threats and VulnerabilitiesĐinh Khánh LinhNo ratings yet
- Iaa202 Lab2 Se140442Document6 pagesIaa202 Lab2 Se140442Đinh Khánh LinhNo ratings yet
- Iaa202 Lab6 Se140442Document17 pagesIaa202 Lab6 Se140442Đinh Khánh LinhNo ratings yet
- cRUBhLaxTUOnMJiafsqCjg - CM2025 Past Exam Oct 2023Document8 pagescRUBhLaxTUOnMJiafsqCjg - CM2025 Past Exam Oct 2023chaudhary.ahmadNo ratings yet
- Case Study Hacking ISA ServersDocument9 pagesCase Study Hacking ISA ServersOrlin CoreaNo ratings yet
- Itt320 - Introduction To Computer Security: Lab 3 CryptographyDocument16 pagesItt320 - Introduction To Computer Security: Lab 3 CryptographyftlucasNo ratings yet
- Cryptography and Network Security Unit-5 CP 21669131401618Document31 pagesCryptography and Network Security Unit-5 CP 21669131401618Madhav kasi PNo ratings yet
- Demonstration and Analysis of IP Spoofing Attacks Using Python Scripts and Wireshark Review - 3Document10 pagesDemonstration and Analysis of IP Spoofing Attacks Using Python Scripts and Wireshark Review - 3Anvesh PenkeNo ratings yet
- Vigene're Ciphere 20088 20063 20098Document19 pagesVigene're Ciphere 20088 20063 20098Fajar IqbalNo ratings yet
- Security Technology Prevention Systems, Intrusion Detection, and Other Security ToolsDocument64 pagesSecurity Technology Prevention Systems, Intrusion Detection, and Other Security ToolsAntony0% (1)
- 7 Ways To Prortect Yourself From PhishingDocument1 page7 Ways To Prortect Yourself From PhishingMario1199No ratings yet
- Test Bank For Guide To Firewalls and Vpns 3rd EditionDocument6 pagesTest Bank For Guide To Firewalls and Vpns 3rd EditionErik Vanlandingham100% (42)
- CDS - 2012 03 12.00000Document3 pagesCDS - 2012 03 12.00000veldurthibuntyNo ratings yet
- Cisco SA 500 VPN Security Appliance & GreenBow IPSec VPN Client Software Configuration (English)Document14 pagesCisco SA 500 VPN Security Appliance & GreenBow IPSec VPN Client Software Configuration (English)greenbowNo ratings yet
- Chapter 1: (Network Security) : PreambleDocument21 pagesChapter 1: (Network Security) : PreambleArras DaouNo ratings yet
- MODULE 4 Network SecurityDocument16 pagesMODULE 4 Network SecurityJohn Rold Picardal ArcalaNo ratings yet
- Sec Sec For Vpns W Ipsec 15 MT Book PDFDocument168 pagesSec Sec For Vpns W Ipsec 15 MT Book PDFcrnaupaNo ratings yet
- ICS-CE 6-IOEUA32185A - Open Elective I (Information and Cyber Security)Document4 pagesICS-CE 6-IOEUA32185A - Open Elective I (Information and Cyber Security)Sakshi ChoudharyNo ratings yet
- Public Key Infrastructure (PKIDocument16 pagesPublic Key Infrastructure (PKIhamza iliyas100% (1)
- Cybersecurity: Past, Present and Future: Shahid Alam, PHDDocument123 pagesCybersecurity: Past, Present and Future: Shahid Alam, PHDFabien RobillardNo ratings yet
- 4 KDocument789 pages4 KMariusNo ratings yet
- 2023bske PCVL For Barangay 2612018Document22 pages2023bske PCVL For Barangay 2612018Lee EcaldreNo ratings yet
- EC Council Ehtical Hacking and Contermeasures (CEH) v6Document130 pagesEC Council Ehtical Hacking and Contermeasures (CEH) v6Adam Dhori'unNo ratings yet
- Review QuestionsDocument9 pagesReview QuestionsAbraham GadissaNo ratings yet
- TLS VersionDocument3 pagesTLS VersionsharadNo ratings yet
- DKV Card Specification - V - 1 - 21-2Document10 pagesDKV Card Specification - V - 1 - 21-2piero.albertoNo ratings yet
- Guia de Administracao EjbcaDocument117 pagesGuia de Administracao EjbcaluisbortNo ratings yet
- Events Codes For Fun & ProfitDocument19 pagesEvents Codes For Fun & ProfitMarcia MéndezNo ratings yet
- B.Tech IV Year II Semester (R15) Regular Examinations April 2019Document1 pageB.Tech IV Year II Semester (R15) Regular Examinations April 2019Chitra Madhuri YashodaNo ratings yet
- T. E. Audit Course ReportDocument17 pagesT. E. Audit Course ReportHarshalNo ratings yet
- Domain2: (Chapter 5)Document13 pagesDomain2: (Chapter 5)babyNo ratings yet
- 2021 Yale Access Smart Lock CatalogueDocument33 pages2021 Yale Access Smart Lock CatalogueHuan100% (1)