Professional Documents
Culture Documents
A Smart Door Security-Based Home Automation System: An Internet of Things
A Smart Door Security-Based Home Automation System: An Internet of Things
Uploaded by
Samir GhoualiOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
A Smart Door Security-Based Home Automation System: An Internet of Things
A Smart Door Security-Based Home Automation System: An Internet of Things
Uploaded by
Samir GhoualiCopyright:
Available Formats
See discussions, stats, and author profiles for this publication at: https://www.researchgate.
net/publication/326991167
A Smart Door Security-Based Home Automation System: An Internet of
Things
Article in Journal of Telecommunication · July 2018
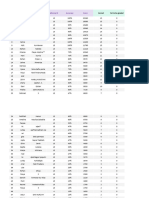
CITATIONS READS
0 97
6 authors, including:
Ajao Lukman Olaniyi Olayemi Mikail
Federal University of Technology Minna Federal University of Technology Minna
32 PUBLICATIONS 45 CITATIONS 73 PUBLICATIONS 202 CITATIONS
SEE PROFILE SEE PROFILE
Jonathan Gana Kolo Emmanuel Adewale Adedokun
Federal University of Technology Minna Ahmadu Bello University
41 PUBLICATIONS 115 CITATIONS 23 PUBLICATIONS 5 CITATIONS
SEE PROFILE SEE PROFILE
Some of the authors of this publication are also working on these related projects:
Knowledge Contribution View project
Pastoralist Optimization Algorithm: A Novel Nature-Inspired Metaheuristic Optimization Algorithm View project
All content following this page was uploaded by Ajao Lukman on 13 August 2018.
The user has requested enhancement of the downloaded file.
SCIFED
Publishers
Ajao LA, SF J Telecommunic, 2018, 2:2
SciFed Journal of Telecommunication
Research Article Open Access
A Smart Door Security-Based Home Automation System: An Internet of
Things
*1
Ajao LA, 2Kolo JG, 3Adedokun EA, 4Olaniyi OM, 5Inalegwu OC, 6Abolade SK
*1,2,4,5
Department of Computer Engineering, School of Electrical Engineering and Technology, Federal University of Technology,
Minna, Nigeria
3
Department of Computer Engineering, Faculty of Engineering, Ahamadu Bello University, Zaria, Nigeria
Abstract
The recent advancement in smart technology design with integration of smart sensors and embedded
components has rapidly improved human lives in so many areas which includes home automation, smart phones, smart
healthcare, smart cars and so on. Therefore, smart home security demand serious attention and is indispensable in this
era of internet of things communication over 6LowPAN model using IPv6 addresses for interconnectivities and end-
to end links. In this paper, the access control, embedded sensors and alarm systems are used for safeguard the device
facilities in the home automation for authentication or authorization and users management over the network. However,
wireless technology (such as GSM, ultrasonic sensor, and Bluetooth low-power enable) was used for controlling
and monitoring home entrance, user authentication, authorization and smart devices management. An android web
application was also developed and integrate with the system for home user control remotely. This developed system
was equipped with a strict access control and password security features for an intruder denial or violation and also
keep the neighbor’s alert of possible human attacks.
Keywords which contains various domestic appliances for the user
Authorization; Human Attack; Smart Technology; enjoyment and comfortability. The smart devices require
Sensors; Security; 6lowpan adequate security for user data controlling, monitoring,
management, and securing every device itself. Home
Introduction automation is define by [3] as home-owner that contains
The advent of intelligence home appliances based many intelligence domestic appliances for users living
embedded sensors and wireless technology has improved comfortability and ease of achieving many system
the home livings with several domestic appliances which operations and control remotely. Home security is the most
includes washing machines, cloth dryers, refrigerators, visible element in home computerization.
electric and gas cooking materials, dishwashers,
sewing machines, television and home theater gadget
*Corresponding author: Ajao LA, Department of Computer Engineering,
[1, 2]. Therefore, security of life and property is a key School of Electrical Engineering and Technology, Federal University of
responsibility of every citizen in a country where these Technology, Minna, Nigeria. E-mail: ajao.wale@futminna.edu.ng
social infrastructures based internet of things appliances
Received May 17, 2018; Accepted July 2, 2018; Published July 13, 2018
are been implemented.
Security is described as countermeasure that Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation
resist or protection against any harmful attacker which System: An Internet of Things. SF J Telecommunic 2:2.
are widely applicable to any vulnerable host or valuable Copyright: © 2018 Ajao LA. This is an open-access article distributed
asset in a network such as smart appliances, user data, and under the terms of the Creative Commons Attribution License, which
permits unrestricted use, distribution, and reproduction in any medium,
many others. One of the fastest emergent technologies provided the original author and source are credited.
in the universal network is home automation system
SF J Telecommunic Volume 2 · Issue 2 · 1000014
ISSN:XXXX-XXXX SFJTC, an open access journal page 1 of 9
Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation System: An Internet of Things. SF J Telecommunic 2:2.
A conventional method of securing home has attack, eavesdropping, interception, hijacking and spoofing
improved significantly compared to the past decades. and many others[13, 14].Also, the proliferation of smart
Today, embedded sensor, digital camera, GPS/GPRS embedded sensors particularly in smart home environment
and many others have been discovered for the efficient has raised some threat of cyber-attacks, hackers, wormhole
implementation of home automation security monitoring, attacks, services availability (such as flooding, spoofing,
intruder detection and managing of smart home technology jamming, and replay attacks), unauthorized routing
facilities [4, 5]. update, unauthorized node access (such as impersonation
The smart embedded wireless sensors devices or eavesdropping attacks). Therefore, the need for a robust
has gain more attention in the era of Internet of Things security is significant to study.
technology for surveillance, tracking, monitoring and The first remote home automation control
remote smart home control and applications [6]. This is as technology was developed with X10 network technology
a result of widely applications in the electronics industries, for signaling, transmission and communication between
automobiles, robotics, military for security, surveillance electronics home devices. Smart home systems have
and so on. The importance of smart embedded sensors tremendously developed over the years, adopting various
claims in the smart technology particularly smart home technologies: ZigBee [2], Bluetooth [15], RFID [9],
environment has raises some threat of cyber-attacks, GPRS/GSM [2, 4, 10, 14], and so on. The 2010 report by
hackers, wormhole attacks, services availability (such the Alarm Industry Research and Educational Foundation
as flooding, spoofing, jamming, and replay attacks), [15] states that burglars spends fewer than 60 seconds to
unauthorized routing update, unauthorized node access break into a home [AIREF]. Deductively, any measure
(such as impersonation or eavesdropping attacks). established that makes a facility more difficult to access,
The first remote home automation control will inherently serve as a deterrent [7]. Some structures
technology was developed with X10 network technology have employed artificial intelligence (AI) control and
for signaling transmission and communication between computational intelligent based robotic systems with
electronics home devices. This smart home technology human interaction [16]. Also, implementations of central
was classified into three generation categories which are gateway or user interfaces such as wall terminals, computer
home automation wireless technology with proxy server system, mobile phone apps or android web apps through
using ZigBee, Bluetooth, Wi-Fi, and so on. These wireless the universal network were presented in [10, 11].
technology approaches are discussed in [2, 3, 7, 8], others The HAS is vulnerable to different threats
are artificial intelligence control and computational or attacks since most of their devices depend on the
intelligence based robotic system or embedded system universal networks. These attacks are physical attack,
with human interaction (Rooma and Rovio robot) [9]. nefarious attack, eavesdropping, interception, hijacking
Also, implementation of central gateway or user interfaces and spoofing and many others [17]. The authors in [18]
such as wall terminals, computer system, mobile phone also demonstrated the possibility of a real-time remote
apps or android web apps through the universal network monitoring via an IoT based doorbell. All of these are
[10, 11] which can be achieved through smart technology evident of the limitless applications for IoT based smart
security. security systems. Since security systems have often been
Smart embedded wireless sensors devices have breached by intelligent thieves, it becomes so necessary
gain more attention in the era of Internet of Things for the deterring measures in place to also advance ahead
technology for surveillance, tracking, monitoring and of the criminals.
remote smart home control and applications [12]. This
is as a result of the wide applications in the electronics 3. Methods and Materials
industries, automobiles, robotics, military tracking and The embedded smart sensor approach integrated
investigation. with other wireless components was employed in the door
security based home automation monitoring. The system
2. Related Works coding and development for an IoT-based smart home
The HAS is vulnerable to different threats or door security involves integration of both hardware and
attacks since most of their devices depend on the universal software system design. The embedded software coding
networks. These attacks are physical attack, nefarious was implemented in Arduino integrated development
SF J Telecommunic Volume 2 · Issue 2 · 1000014
ISSN:XXXX-XXXX SFJTC, an open access journal page 2 of 9
Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation System: An Internet of Things. SF J Telecommunic 2:2.
environment (IDE) using C language. The wireless based 3.1 Hardware Module
home appliances are control remotely with the development 3.1.1 Controller Unit
of an android application using eclipse IDE. The integration of hardware system for home
This system is flexible and friendly to operate. When the automation door security consists of Arduino Uno
system is power ON, it will initialized all the modules integrated with Atmega 328 for system processing and
connected to it which includes servo motor, keypad, LCD servo motor used for control of opening and closing of
display, buzzer, Bluetooth module, and GSM module. The the home automation door. The Arduino Uno external
door security home automation systems allow the user to architecture and its features are illustrated in (Figure 3).
enter password for door opening or closing. The password Figure 3: Arduino Uno (Atmega 328) External Architecture
will be verified for its validity or denial before further action
is taken. If the password is valid, the door will open and
if wrong password is enter after four attempts, the system
is programmed to report unauthorized user which signal
the controller to send alert to buzzer and GSM module for
buzzing and sent message as illustrated in the flowchart of
Figure 1. Figure 2 shows the smart door security based IoT
block diagram. (Figures 1, 2)
Figure 1: Home Automation Door Security System Based Iot
Figure 4A: Internal Architecture of Servo Motor
Figure 4B: External Architecture SM
Figure 2: Home Automation Door Security System Block Diagram
3.1.2 Servo Motor
The drive security door mechanism is servo motor
which helps in control of the door opened and closed,
the mechanism dimensions, mass and friction coefficient
are calculated for load determination. This device can
be described as an actuator or closed loop system that
SF J Telecommunic Volume 2 · Issue 2 · 1000014
ISSN:XXXX-XXXX SFJTC, an open access journal page 3 of 9
Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation System: An Internet of Things. SF J Telecommunic 2:2.
produces a rotary motion or toque, enable the precise T= (TL + Ta ) *S f (5)
M
movement of angular velocity, acceleration and linear
position with suitable embedded sensor integrated with
motor for feedback position. Servo motor consist of both Trms = (Ta + Ta ) 2 * t1 + TL2 * t2 + (Td + TL ) 2 * t3 / t f (6)
input signal (analogue or digital) which signifying the
output shaft position as commanded by the controller. This Where, TM is torque required, TL is load torque, Ta is
servo mechanism consists of three pin connection PWR, acceleration torque and Sf is safety factor.
GND and DATA. It has 4.0kgcm torque, Size (L * W * H):
20.0 * 17.6 * 8.0mm, operation voltage 4.8 ~ 6.0V, Speed 3.1.3 Output Unit
0.12sec/60owithout load and operating current of 100mA The buzzer implemented for blow alarm in case of
[20]. The internal and external architecture are illustrated any intruder detection. The liquid crystal display unit was
in Figure 4a and 4b respectively. (Figures 4a, 4b) used for HA door security message display, it consists of
16 pins connection as illustrated in Figure 4a and 4b. The
Figure 5: Servo Mechanism Rotational of Inertial Moment
pin 1, 2 and 3 are Ground (VSS), 5V power (VDD) and
contrast voltage (VE) respectively. The Pin 4 is the register
select (RS), and when this pin is LOW, data transferred to
the display is treated as commands. When RS is HIGH,
character data can be transferred to and from the module.
Pin 5 is the read/write (R/W) line. This pin is pulled LOW
in order to write commands or character data to the LCD
module. When this pin is HIGH, character data or status
information can be read from the module. Pin 6 is the enable
(E) pin, which is used to initiate the transfer of commands
or data between the module and the microcontroller.
The inertial moment (J) in (oz-in-sec²), rotation of When writing to the display, data is transferred only on
servo motor, speed and load torque as shown in (Figure the HIGH-to-LOW transition of this line. When reading
5), can be calculated as expressed in Equation 1, to 4 from the display, data becomes available after the LOW-
reverentially. to-HIGH transition of the enable pin, and this data remains
valid as long as the enable pin is at logic HIGH. Pins 7
to 14 are the eight data bus lines (D0 to D7). Data can
∫∫∫ ρ (χ
2
J
= + y 2 ) d χ dydz (1)
be transferred between the microcontroller and the LCD
module using either a single 8-bit byte or as two 4-bit
J = mL2 (2) nibbles. In the latter case, only the upper four data lines
D (D4 to D7) are used. The 4-bit mode means that four fewer
S= (3) I/O lines are used to communicate with the LCD. (Figures
T 6a, 6b) illustrate LCD architecture.
D
Sm = (4) Figure 6A: LCD Back-View Architecture
(T − A t )
where, m is mass, L is distance between center
of gravity and rotational center, Sm is servo motor speed
(m/s), T is time (s), and At is acceleration time in (m/s2).
For the safety factor, the torque required can
be calculated by multiplying the sum of load torque
with acceleration torque as given in Equation 5, and the
effective load torque for fast cycle operation pattern can
be calculated where acceleration divided by deceleration
is frequent as expressed in Equation 6.
SF J Telecommunic Volume 2 · Issue 2 · 1000014
ISSN:XXXX-XXXX SFJTC, an open access journal page 4 of 9
Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation System: An Internet of Things. SF J Telecommunic 2:2.
Figure 6B: LCD Front-View Architecture Figure 7: Breadboard of Bluetooth Circuit Implementation
Figure 8: The Flowchart of Bluetooth Communication Process
3.1.4 The Communication Module
The portable GSM/GPRS module (NEO M590)
was employed for remote data communication between
the automation home door security and the user android
web application. The HC-06 Bluetooth module was used
for remote signal control and transmission. This wireless
technology based IoT is a serial port profile support chip that
allows connection and establishment of serial emulation
of microcontroller connection. It enables communication Where, R is resistor value, Vcc is microcontroller
between the devices connected in the universal network power 5v, Vf is LED voltage reference 0.7v Bluetooth
using Bluetooth protocol or universal bus (USB) cable. power 3.3v, and current consumption is 30-40mA.
Bluetooth low power capable of transmitting 5 − 0.7
signal over a range 10 meters maximum and can be R = = 109.25Ω
configure as a master/slave device, it consume about 30-
4 x10−3
40 mA current, 3.3 voltage during pairing of devices and
8mA current during communication [21, 22]. The HC-06 3.3
=
R = 82.5Ω
Ground (GND) pin is connected to ground, power VCC pin 4 x10−3
is connected to 5v, transmission/receiver TX/TXD pin is This shows that 100Ω to 110Ω resistor can be used
connected to Arduino digital pin 4 and receiver RX/RXD for controller and in the case of Bluetooth implementation
pin is connected to Arduino digital pin 2 as illustrated in required 80Ω to 100Ω for the efficient and reliability of
(Figure 7), and the Bluetooth communication flowchart is system performance.
depicted in (Figure 8). Also, the voltage through the Rx/Tx pin of the
Arduino can be calculated as in Equation 8.
Therefore, the voltage and resistance value used in
the system design can be calculated as given in Equation 7.
R1
VRx = Vcc * (8)
R Vcc − Vf / If
= (7) R1 + R2
SF J Telecommunic Volume 2 · Issue 2 · 1000014
ISSN:XXXX-XXXX SFJTC, an open access journal page 5 of 9
Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation System: An Internet of Things. SF J Telecommunic 2:2.
20 K door security for the system modules integrations which
VRx = 5* ≈ 3.3V includes liquid crystal display (LCD), servo motor (SV),
10 K + 20 K 4x4 hexadecimal keypad, ultrasonic sensor and GSM
module in Arduino IDE using C-language.
3.1.5 The Sensing Module
Ultrasonic sensor is integrated into the circuit Hardware modules programming
physical detection or images of any illegal movement #include <Wire.h>
detection around the smart home environment. This sensor #include <LiquidCrystal.h>
is electrical transducers that consist of transmitter and #include <Servo.h>
receiver, which convert ultrasound waves to electrical #include <Keypad.h>
signals. It consist of four (4) connected pins, which are #include <EEPROM.h>
ground (GND), power (VCC), trigger (TRIG) and echo #include <Ultrasonic.h>
(ECHO) pin connection as illustrated in Figure 9. The high Servo myservo;
voltage of 5v from controller is connected to the TRIG LiquidCrystallcd(A0, A1, A2, A3, A4, A5);
pin to generate high frequency waves within a particular Ultrasonic ultrasonic(2,3); // (Trig PIN,Echo PIN)
period of time which helps to determine the distance
between sensor and the object. (Figure 9) const byte ROWS = 4; //four rows
Figure 9: External Architecture of Ultrasonic Sensor const byte COLS = 4; //three columns
char keys[ROWS][COLS] = {
{‘1’,’2’,’3’,’A’},
{‘4’,’5’,’6’,’B’}, //first set of pins are col pins
{‘7’,’8’,’9’,’C’},
{‘*’,’0’,’#’,’D’}
};
byterowPins[ROWS] = {13, 12, 11, 10}; //connect to the
row pinouts of the keypad
bytecolPins[COLS] = {9, 8, 7,6}; //connect to the column
pinouts of the keypad
The distance covered by the ultrasonic sensor can be
calculated through the speed of sound produced, the Keypad keypad = Keypad(makeKeymap(keys), rowPins,
microcontroller takes 11.6ms to received feedback from colPins, ROWS, COLS );
the sensor, as expressed in Equation 9. String phoneNo=”+2348168670476”; //variable to hold
phone number
speed of sound × time taken String pin =”1234”;
D= (9)
String keyInput =””;
2
int buzzer =4;
Where, speed of sound is given as 344m/s
intpinTime=0;
int lock=5;
344 ×11.6 ×10−3 boolean sent =false;
=D = 1.9952m ≈ 2.0m
2
This shows that each side of ultrasonic sensor 3.2 The software development
can covered a distance of approximately 2 meters apart in The android application platform was developed
detecting object or obstacle in real life application. using java native language with SDK development kit,
and it was deployed on the mobile phone for remote door
3.1.6 Hardwired Program Design security based HA control, authorization and monitoring.
The following lines of code demonstrate the The graphic user interface was developed in the eclipse IDE
beginning of hardware configuration system based HA using XML to link the design to the cloud database system
SF J Telecommunic Volume 2 · Issue 2 · 1000014
ISSN:XXXX-XXXX SFJTC, an open access journal page 6 of 9
Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation System: An Internet of Things. SF J Telecommunic 2:2.
as depicted in Figure 10. The login graphic user interface 4. Discussions
required a unique home automation user identities like The smart home automation door security was
user password and name which denied wrong provisions implemented by integrating the smart embedded sensor
of user name or password as first level of authorization/ system with android mobile apps developed as illustrated
authentication security level. (Figure 10) in Figure 11a. The embedded sensor security lines of
Figure 10: Door Security Android GUI code for door security system based home automation
are highlighted. This is strictly design for access control
of opening and closing door remotely through wireless
communication module (Bluetooth) using a password
authentication/authorization techniques. If a valid
password is enter through the 4x4 hex keypad implemented
at the entrance, this will control the door opening (access
granted) and send message to the home user for the security
notification. Also, if an invalid password entered, it will
denied user access to the entrance of the building (denied
access) and send messages for wrong password user trial.
This process will allow user trial for four consecutive
The android application is a mobile operating times before alarm system begin to buzzing for intruder
system that based on the Linux kernel for direct detection. Also, with embedded sensor integration using
manipulation and mobile operations which includes ultrasonic sensor assist impressively in detection of any
swiping, tapping, pinching and so on. This apps was movement around the doors or windows in case of burgle
developed and powered by Google Incorporation primarily and alert the home users with continuous alarm and invader
for touch screen mobile operations on the devices like attentive messages sent to the home users as shown in
smart phones and tablets. Also, the Eclipse is an integrated (Figures 11b, 12).
development java programming environment that support Figure 11b: Door Security Based Smart Home
an android application design for real time purposes and
cloud database for data or image storage and retrieval
using XML link. This is widely used for programming
language like Java, C++, Python, Ruby, and many others.
The flowchart illustrated in Figure 11 shows the design
flows of an android based Apps. (Figure 11a)
Figure 11A: Android Apps Design Phases
Figure 12: Security Message Alerts GUI
SF J Telecommunic Volume 2 · Issue 2 · 1000014
ISSN:XXXX-XXXX SFJTC, an open access journal page 7 of 9
Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation System: An Internet of Things. SF J Telecommunic 2:2.
Door security opening/denial authentication programming communication based IoT and android mobile Apps-based
password authorization for adequate security level against
lcd.clear(); intruders. This home automation door security control
lcd.print(“ ENTER PASSWORD”); provides multifaceted levels of user authentication on
} both hardware system development and android mobile
void loop() Apps for system resourceful, privacy and trustworthy of
{ the home users or administrator. The door security mobile
char key = keypad.getKey(); control system is users friendly and flexible to operate.
Based on the detailed analysis of the system developed, it
if(key){ is concluded that the system is reliable, maintainable and
if(key==’A’ || key==’B’ || key==’C’ || key==’D’) available for individual users’ consumption, commercial
{ and industries. Some improvement can be added to the
if(keyInput.length()>0) system in the future for the efficient functionalities and
keyInput=keyInput.substring(0,keyInput.length()-1); wide areas of application which include motion detection
} sensor integration, camera for surveillance and image
else { capturing, addition of a biometric system for unique
if(checkForAlarm()) security identification together with the keypad and so on.
triggerAlarm();
else{ References
keyInput +=key; 1. Hill J (2015) The smart home: a glossary guide for the
if(keyInput.length()==4){ perplexed.
pinTime++;
if(keyInput==pin) 2. Ajao LA, Ajao FJ, Adegboye MA, et al. (2018) An embedded
fuzzy logic based application for density traffic control system,
openDoor();
Int J Artif Intel Res 2: 6-13.
else
if(pinTime>3) 3. Aliyu S, Yusuf A, Umar A, et al. (2017) Design and
triggerAlarm(); development of a low-cost GSM-bluetooth home automation
else system. IJAIA 8:41-50.
wrongPass();
} 4. Zhao Y, Ye Z (2008) A low cost GSM/GPRS based wireless
} home security system, IEEE Trans. Consum. Electron 54:
} 567-572.
String toPrint=””;
5. Felix C, Jacob Raglend I (2011), Home automation using GSM,
for(inti=0;i!=keyInput.length();i++)
International Conference on Signal Processing, Communication,
toPrint+=’*’; Computing and Networking Technologies 15-19.
lcd.clear();
lcd.print(“ ENTER PASSWORD”); 6. Papadopoulos K, Zahariadis T, Leligou N et.al (2008) Sensor
lcd.setCursor(0,1); Networks Security Issues in Augmented Home Environment
lcd.print(toPrint); Proceedings of the IEEE International Symposium on Consumer
} Electronics, Las Vegas, NV, USA 1-4.
else
if(checkForAlarm()) 7. Abhishek AP, Joglekar A (2015) Implementation of home
triggerAlarm(); security system using GSM module and microcontroller IJCSIT
6: 2950-2953.
}
8. Yan M and Shi H (2013) Smart Living Using Blueooth-Based
5.0 Conclusion android smartphone, International Journal of Wireless Mobile
In this research a smart door security based HAS Networks 5: 65-72.
is developed using smart embedded sensor, wireless
SF J Telecommunic Volume 2 · Issue 2 · 1000014
ISSN:XXXX-XXXX SFJTC, an open access journal page 8 of 9
Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation System: An Internet of Things. SF J Telecommunic 2:2.
9. Li RYM, Li HCY, Mak CK et al. (2016) Sustainable Smart
Home and Home Automation: Big Data Analytics Approach
IJSH 10: 177-198.
10. Ahammed T, Banik PP (2015) Home appliances control
using mobile phone, Proceedings of 3rd International Conference
on Advances in Electrical Engineering 251-254.
11. Mulla A, Baviskar J, Baviskar A (2014) DTMF based
automation system with reduction of noise usinggoertzel DFT
estimation, Fourth International Conference on Communication
Systems and Network Technologies 1124-1129.
12. Yong Q, Hao L, Junhua H (2013) The Design
of Grading Software System Based on Bluetooth in
Android, 8th International Forum on Strategic Technology
(IFOST) 16-19.
13. Huichenand L, Neil WB (2016) IoT privacy and security
challenges for smart home environments MDPI Journal
information, Basel, Switzerland 7: 1-15.
14. Bakoand A, Ali IA (2018) Cyber and physical security
vulnerability assessment for IoT-based smart homes, MDPI
Journal Sensors 18: 1-17.
15. Khan SR, Dristy FS (2015) Android based security and home
automation system. IJASA 3:15-24.
16. Sabeel U, Chandra N (2013) A Smart and Contemporary
Home Security System using802.15.4 Standard. 5th International
Conference on Computational Intelligence and Communication
Networks 374-379.
17. Suh C, Ko Y (2008) Design and implementation of intelligent
home control systems based on active sensor networks, IEEE
Trans Consume Electron 54: 1177-1184.
18. Ping W, Guichu W, Wenbin X, et al. (2010) Remote
Monitoring Intelligent System Based on Fingerprint Door
Lock, International Conference on Intelligent Computation
Technology and Automation.
Citation: Ajao LA (2018) A Smart Door Security-Based Home Automation
System: An Internet of Things. SF J Telecommunic 2:2.
SF J Telecommunic Volume 2 · Issue 2 · 1000014
ISSN:XXXX-XXXX SFJTC, an open access journal page 9 of 9
View publication stats
You might also like
- Home Security SystemDocument30 pagesHome Security SystemNjitnumNo ratings yet
- 2021 Book Artificial Intelligence in OphthalmoDocument280 pages2021 Book Artificial Intelligence in OphthalmoSamir Ghouali100% (1)
- A Review Advancement of Security Alarm System Using Internet of Things (Iot)Document13 pagesA Review Advancement of Security Alarm System Using Internet of Things (Iot)AppyNo ratings yet
- Internet of Things (IoT) of Smart Home Privacy and Security PDFDocument7 pagesInternet of Things (IoT) of Smart Home Privacy and Security PDFNguyễn Tiến Đạo ĐứcNo ratings yet
- Paper 34Document12 pagesPaper 34billa narasimhaNo ratings yet
- A Monitoring and Control Gateway For Iot Edge Devices in Smart HomeDocument7 pagesA Monitoring and Control Gateway For Iot Edge Devices in Smart HomeNguyễn Hồng NhungNo ratings yet
- Design and Construction of A Door Securrity Alarm System Based On Sms Verification and Voice RecognitionDocument15 pagesDesign and Construction of A Door Securrity Alarm System Based On Sms Verification and Voice RecognitionasieluekingsleyNo ratings yet
- A Simple and Reliable Touch Sensitive Security SysDocument18 pagesA Simple and Reliable Touch Sensitive Security SysMK MillyNo ratings yet
- Smart Home Security and Intrusion Detection SystemDocument7 pagesSmart Home Security and Intrusion Detection SystemEditor IJTSRDNo ratings yet
- An IoT Based Smart Home Security and Home Automation SystemDocument3 pagesAn IoT Based Smart Home Security and Home Automation SystemEditor IJTSRDNo ratings yet
- Chapter 2 RRLDocument12 pagesChapter 2 RRLramossophialynn00762No ratings yet
- Systematic Survey On Smart Home Safety and Security Systems Using The Arduino PlatformDocument24 pagesSystematic Survey On Smart Home Safety and Security Systems Using The Arduino PlatformGeri MaeNo ratings yet
- T IFS 06528 2016 - Final VersionDocument13 pagesT IFS 06528 2016 - Final VersionSUDARSANA SAMHITA SNo ratings yet
- GSM Based Intelligent Home Security System For Intrusion DetectionDocument12 pagesGSM Based Intelligent Home Security System For Intrusion DetectionNam HaNo ratings yet
- Assessment of Smart HomeDocument10 pagesAssessment of Smart Homeelon huskNo ratings yet
- Security Issues On Smarthome in Iot EnvironmentDocument2 pagesSecurity Issues On Smarthome in Iot EnvironmentPHùng TrầnNo ratings yet
- Securityin Io TDocument37 pagesSecurityin Io TAbd ANo ratings yet
- Security of Internet of ThingsDocument4 pagesSecurity of Internet of ThingsKannan AlagumuthiahNo ratings yet
- Intelligent Home Automation System For Disabled PeopleDocument7 pagesIntelligent Home Automation System For Disabled Peoplepmm321No ratings yet
- Automated Hybrid Smart Door Control SystemDocument13 pagesAutomated Hybrid Smart Door Control SystemKIU PUBLICATION AND EXTENSIONNo ratings yet
- 2072236869aams Vol 203 January 2020 A12 p445-457 Raj Kumar and Jyoti ChaudharyDocument13 pages2072236869aams Vol 203 January 2020 A12 p445-457 Raj Kumar and Jyoti Chaudharydharanidharan2204No ratings yet
- Internet of Things and Smart Home SecurityDocument13 pagesInternet of Things and Smart Home SecurityfreeretdocsNo ratings yet
- Sensor Based Home Automation and Security SystemDocument6 pagesSensor Based Home Automation and Security Systemshivani mNo ratings yet
- A Review On Smart Home Environment and Consequences of Cyber Security Attacks On Smart HomesDocument8 pagesA Review On Smart Home Environment and Consequences of Cyber Security Attacks On Smart HomesRajesh BathulaNo ratings yet
- Homeshield: A Credential-Less Authentication Framework For Smart Home SystemsDocument15 pagesHomeshield: A Credential-Less Authentication Framework For Smart Home SystemsمحمدNo ratings yet
- A Review On Intruder Alarm SystemDocument7 pagesA Review On Intruder Alarm SystemIJRASETPublicationsNo ratings yet
- Smart Lock Systems Overview - CompressedDocument5 pagesSmart Lock Systems Overview - Compressed4CMOHAMAD AIZAT ASNAWI BIN MOHD HARONNo ratings yet
- Wjaets 2024 0037Document9 pagesWjaets 2024 0037chewanthegreatNo ratings yet
- 5G Applications in Heterogeneous Network Issues and ChallengesDocument10 pages5G Applications in Heterogeneous Network Issues and ChallengesyadoNo ratings yet
- Ethical Hackingon Mobile Devices ConsiderationsandpracticalusesDocument12 pagesEthical Hackingon Mobile Devices Considerationsandpracticalusessolaymanhowlader01No ratings yet
- Prototype For A Personal Safety Gadget Using ArduiDocument7 pagesPrototype For A Personal Safety Gadget Using ArduiFauji GabeNo ratings yet
- GSM SaurajDocument6 pagesGSM SaurajSAURAJ PANDEYNo ratings yet
- A Critical Analysis On The Security Concerns of Internet of Things IotDocument7 pagesA Critical Analysis On The Security Concerns of Internet of Things IotMadamNo ratings yet
- Anty Theft Security SystemDocument27 pagesAnty Theft Security Systemtechbuilderinventor101No ratings yet
- Securityin Io TDocument37 pagesSecurityin Io TManal SaeedNo ratings yet
- Security in IotDocument37 pagesSecurity in Iotsamir YOUSIFNo ratings yet
- Enhanced Security Methods of Door Locking Based FingerprintDocument7 pagesEnhanced Security Methods of Door Locking Based FingerprintMark LeeNo ratings yet
- PublicationDocument7 pagesPublicationForhadi TechNo ratings yet
- IoT Network Anomaly Detection in Smart Homes Using Machine LearningDocument20 pagesIoT Network Anomaly Detection in Smart Homes Using Machine LearningMaicol Soria PabloNo ratings yet
- A Research Paper On Internet of Things Based UponDocument9 pagesA Research Paper On Internet of Things Based UponHiền Trang Lê ThiênNo ratings yet
- Nayyar 2017Document5 pagesNayyar 2017Karina MariaNo ratings yet
- Final VersionDocument11 pagesFinal Versionapo panagNo ratings yet
- A Novel Design and Implementation of Smart Home Security System: Future PerspectiveDocument6 pagesA Novel Design and Implementation of Smart Home Security System: Future Perspectivedharanidharan2204No ratings yet
- Ijrar Issue 20542936IOTDocument6 pagesIjrar Issue 20542936IOTThang TruongNo ratings yet
- 2015 - Survey On Secure Communication Protocols For The Internet of ThingsDocument15 pages2015 - Survey On Secure Communication Protocols For The Internet of ThingsAnkit SoniNo ratings yet
- Iot With SDNDocument17 pagesIot With SDNjatin yadavNo ratings yet
- Lightweight and Privacy-Preserving Remote User Authentication For Smart HomesDocument15 pagesLightweight and Privacy-Preserving Remote User Authentication For Smart HomesTEJAS B NNo ratings yet
- Enhancing Home Security Using SMS-based Intruder Detection SystemDocument9 pagesEnhancing Home Security Using SMS-based Intruder Detection SystemOjobo BlessingNo ratings yet
- Paper 1 IJRARDocument8 pagesPaper 1 IJRARmanjunathNo ratings yet
- IoT Based Home Security and Automation System: A ReviewDocument20 pagesIoT Based Home Security and Automation System: A ReviewInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Design and Implementation of Motion Detection Alarm and Security SystemDocument13 pagesDesign and Implementation of Motion Detection Alarm and Security Systemirteza_faruqiNo ratings yet
- Mobile Computing and Its Security: AbstractDocument5 pagesMobile Computing and Its Security: AbstractRamaNo ratings yet
- Security Protocols IoT SpringerDocument29 pagesSecurity Protocols IoT SpringerCông SơnNo ratings yet
- Network Security For Home Iot Devices Must Involve The User: A Position PaperDocument10 pagesNetwork Security For Home Iot Devices Must Involve The User: A Position PaperdwightNo ratings yet
- 1 s2.0 S2542660519301957 Main PDFDocument19 pages1 s2.0 S2542660519301957 Main PDFArunNo ratings yet
- Burgler Alarm Using IOTDocument6 pagesBurgler Alarm Using IOTIJRASETPublicationsNo ratings yet
- 76 - Security of Smart Home-Smartphones SystemsDocument5 pages76 - Security of Smart Home-Smartphones SystemsLARS Projetos & Soluções em Engenharia ElétricaNo ratings yet
- Smart Homes Steps Components Utilities and ChallenDocument6 pagesSmart Homes Steps Components Utilities and ChallenAlcides TiagoNo ratings yet
- Smart Home Using IoTDocument5 pagesSmart Home Using IoTIJSTENo ratings yet
- Management of Network Service Orchestration and 5G Networks: Hind Fadhil AbbasDocument6 pagesManagement of Network Service Orchestration and 5G Networks: Hind Fadhil AbbasSamir GhoualiNo ratings yet
- Implementation of The Numerical Analysis of Dynamic Loads On The Composite Structure Employing The FE MethodDocument7 pagesImplementation of The Numerical Analysis of Dynamic Loads On The Composite Structure Employing The FE MethodSamir GhoualiNo ratings yet
- Research Article Robust Blood Cell Image Segmentation Method Based On Neural Ordinary Differential EquationsDocument11 pagesResearch Article Robust Blood Cell Image Segmentation Method Based On Neural Ordinary Differential EquationsSamir GhoualiNo ratings yet
- Wear Debris From Total Joint Replacements Evaluation of Automated Categorisation by Scale Invariant Feature TransformsDocument8 pagesWear Debris From Total Joint Replacements Evaluation of Automated Categorisation by Scale Invariant Feature TransformsSamir GhoualiNo ratings yet
- Accepted ManuscriptDocument33 pagesAccepted ManuscriptSamir GhoualiNo ratings yet
- Accepted Manuscript: MethodsDocument33 pagesAccepted Manuscript: MethodsSamir GhoualiNo ratings yet
- Automatic Classification of Heartbeats Using Wavelet Neural NetworkDocument11 pagesAutomatic Classification of Heartbeats Using Wavelet Neural NetworkSamir GhoualiNo ratings yet
- Mobile Health in The Management of Type 1 DiabetesDocument10 pagesMobile Health in The Management of Type 1 DiabetesSamir GhoualiNo ratings yet
- The Liar's Walk Detecting Deception With Gait and GestureDocument11 pagesThe Liar's Walk Detecting Deception With Gait and GestureSamir GhoualiNo ratings yet
- A High Electrical Performance of Dg-Mosfet Transistors in 4H-Sic and 6H-Sic 130 NM Technology by Bsim3V3 ModelDocument8 pagesA High Electrical Performance of Dg-Mosfet Transistors in 4H-Sic and 6H-Sic 130 NM Technology by Bsim3V3 ModelSamir GhoualiNo ratings yet
- Review and Use of The Algerian Renewable Energy For Sustainable DevelopmentDocument9 pagesReview and Use of The Algerian Renewable Energy For Sustainable DevelopmentSamir GhoualiNo ratings yet
- Activity Monitoring of Islamic Prayer Salat PosturDocument6 pagesActivity Monitoring of Islamic Prayer Salat PosturSamir GhoualiNo ratings yet
- Benzerga 2015Document10 pagesBenzerga 2015Samir GhoualiNo ratings yet
- Effective Writing and Publishing Scientific PapersDocument2 pagesEffective Writing and Publishing Scientific PapersSamir GhoualiNo ratings yet
- A Novel Stateful PCE-Cloud Based Control Architecture of Optical Networks For Cloud ServicesDocument11 pagesA Novel Stateful PCE-Cloud Based Control Architecture of Optical Networks For Cloud ServicesSamir GhoualiNo ratings yet
- Engineering Science and Technology, An International JournalDocument7 pagesEngineering Science and Technology, An International JournalSamir GhoualiNo ratings yet
- Engineering Science and Technology, An International JournalDocument12 pagesEngineering Science and Technology, An International JournalSamir GhoualiNo ratings yet
- Estimating Interconnection Cost in Mobile Phone Market in TunisiaDocument12 pagesEstimating Interconnection Cost in Mobile Phone Market in TunisiaSamir GhoualiNo ratings yet
- L&T Program 2021Document8 pagesL&T Program 2021Samir GhoualiNo ratings yet
- Towards Cloud Transport Using IP-multiservices Access Network (MSAN)Document9 pagesTowards Cloud Transport Using IP-multiservices Access Network (MSAN)Samir GhoualiNo ratings yet
- A Green Communication Model For 5G SystemsDocument17 pagesA Green Communication Model For 5G SystemsSamir GhoualiNo ratings yet
- A Sample Path Measure of Causal in Uence: June 2018Document6 pagesA Sample Path Measure of Causal in Uence: June 2018Samir GhoualiNo ratings yet
- A Voice Controlled Multi Functional Smart Home Automation SystemDocument6 pagesA Voice Controlled Multi Functional Smart Home Automation SystemChakradharReddyNo ratings yet
- D'Smart Series CatalogueDocument11 pagesD'Smart Series CatalogueChithravelu TamilkumaranNo ratings yet
- Software Defined Network: DefinitionDocument20 pagesSoftware Defined Network: Definitionmaruthi631No ratings yet
- Revised IOT - SyllabusDocument3 pagesRevised IOT - SyllabusRam DinNo ratings yet
- Atulkumar Bca 5thsem A35404819038 NTCC Amity University JharkhandDocument76 pagesAtulkumar Bca 5thsem A35404819038 NTCC Amity University JharkhandAtul KumarNo ratings yet
- Eee 2-2 Sem Cs & Syllabus Ug r20Document20 pagesEee 2-2 Sem Cs & Syllabus Ug r20Aditya Kumar TikkireddiNo ratings yet
- BrochureDocument46 pagesBrochureDjokin DjokaNo ratings yet
- IoT Unit II Part1Document19 pagesIoT Unit II Part1Ramesh BoseNo ratings yet
- SAA2 - Geeni App For PC Download (Windows 11,10,8,7)Document5 pagesSAA2 - Geeni App For PC Download (Windows 11,10,8,7)Sakshi MishraNo ratings yet
- Coccion ZanussiDocument96 pagesCoccion ZanussiJesús Alberto Velarde CuestaNo ratings yet
- Introduction of Internet of Things (IoT By) Thakur Pawan & Pathania SusheelaDocument23 pagesIntroduction of Internet of Things (IoT By) Thakur Pawan & Pathania SusheelaDrPawan Thakur100% (1)
- Analisis Soalan SPM 2019Document31 pagesAnalisis Soalan SPM 2019MuzakkirMohdNoorIINo ratings yet
- MIRM - ICT Proposal - Smart Senior Living Residence Project - 20191030-1Document15 pagesMIRM - ICT Proposal - Smart Senior Living Residence Project - 20191030-1Mehan Nackeeran100% (1)
- Smart Fault Detection and Home Automation SystemDocument8 pagesSmart Fault Detection and Home Automation SystemAnonymous izrFWiQNo ratings yet
- IoT-Home Automation-Test ProjectDocument15 pagesIoT-Home Automation-Test ProjectAqib LatifNo ratings yet
- Q Inter Cooler DrawingsDocument5 pagesQ Inter Cooler DrawingsHri VitalionNo ratings yet
- HackSpace - October 2021Document116 pagesHackSpace - October 2021MuhammadNabeel100% (1)
- Corporate Strategy - Assessment 03 - SonyDocument21 pagesCorporate Strategy - Assessment 03 - Sonyabhilashasingh8791No ratings yet
- Information Sciences Research Methodology PG (6797) ICT Eng Research Methods (9826) Assignment 2 GuideDocument4 pagesInformation Sciences Research Methodology PG (6797) ICT Eng Research Methods (9826) Assignment 2 GuideUsama NawazNo ratings yet
- Transparansi Skor Kamou-Camp Quiz Challenge???Document6 pagesTransparansi Skor Kamou-Camp Quiz Challenge???daffa puteraNo ratings yet
- Unit 5 - Wireless Network - WWW - Rgpvnotes.inDocument18 pagesUnit 5 - Wireless Network - WWW - Rgpvnotes.inZappY100% (1)
- Advanced View Arduino Projects List - Use Arduino For Projects-3Document57 pagesAdvanced View Arduino Projects List - Use Arduino For Projects-3Bilal AfzalNo ratings yet
- KNX Building AutomationDocument28 pagesKNX Building AutomationMihaela AntonNo ratings yet
- Ej S1DPRIR006 20230829Document373 pagesEj S1DPRIR006 20230829mhdluth5No ratings yet
- Chapter 4 - Internet of Things (IOT)Document48 pagesChapter 4 - Internet of Things (IOT)Lee HailuNo ratings yet
- IoT Project Using ESP32 Blynk Google Assistant WitDocument33 pagesIoT Project Using ESP32 Blynk Google Assistant WitTaofik HidayatNo ratings yet
- Vacuum Cleaner Using Iot Base PaperDocument10 pagesVacuum Cleaner Using Iot Base Paper18351ec051No ratings yet
- Brochure Linea Ego Chorus Tecnica - en - LDocument77 pagesBrochure Linea Ego Chorus Tecnica - en - LStefan IorgaNo ratings yet
- Vivint SmartHubV2 GettingStartedGuide ENU - RevA.2Document32 pagesVivint SmartHubV2 GettingStartedGuide ENU - RevA.2Kumara VelNo ratings yet
- IoT - ACT6Document3 pagesIoT - ACT6Jaydine T. CallejoNo ratings yet