Professional Documents
Culture Documents
Viva Shedule
Viva Shedule
Uploaded by
GEO MERIN0 ratings0% found this document useful (0 votes)
30 views4 pagesThe document contains details of student projects presented in different batches, including the program, batch number, student names and registration numbers, project titles, and time slots for presentations. Each batch is assigned a letter (A-B) and contains multiple student presentations on various technical topics related to computer science and engineering, such as IoT, machine learning, computer security, and networking. In total, there are 18 batches (A1-A18, B1-B7) consisting of over 100 student presentations on innovative projects.
Original Description:
Original Title
Viva Shedule (1)
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document contains details of student projects presented in different batches, including the program, batch number, student names and registration numbers, project titles, and time slots for presentations. Each batch is assigned a letter (A-B) and contains multiple student presentations on various technical topics related to computer science and engineering, such as IoT, machine learning, computer security, and networking. In total, there are 18 batches (A1-A18, B1-B7) consisting of over 100 student presentations on innovative projects.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
30 views4 pagesViva Shedule
Viva Shedule
Uploaded by
GEO MERINThe document contains details of student projects presented in different batches, including the program, batch number, student names and registration numbers, project titles, and time slots for presentations. Each batch is assigned a letter (A-B) and contains multiple student presentations on various technical topics related to computer science and engineering, such as IoT, machine learning, computer security, and networking. In total, there are 18 batches (A1-A18, B1-B7) consisting of over 100 student presentations on innovative projects.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 4
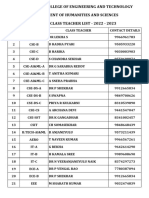
NAME OF
THE BATCH NUMBER
REGISTRATION NO. OF
S NO PROGRAMM WITH (Date : NAME OF THE STUDENT TITLE OF THE PROJECT WORK
THE STUDENT
E AND 22/09/2020) TIME
BRANCH
962216104001 AANCY DINOTHI J J
Selective Authentication Based Geographic
1 B.E. CSE A1 962216104008 AKSHAYA RAJAN
Opportunistic Routing Against DOSATTACK
9.30 AM - 9.45 AM 962216104009 ALAN JOHN RITA A
962216104056 JOSIFHA ASHMI J
2 B.E. CSE A2 962216104032 DEVIKA S S IOT Based Patient Monitoring System
9.30 AM - 9.45 AM 962216104031 DEEPIKA D
962216104003 ABINESH M
Characteristic and predicting early reviews for
3 B.E. CSE A3 962216104051 JEYA RAM M
effective product marketing on e-com websites
9.30 AM - 9.45 AM 962216104703 AJIN V
962216104005 AGNAS GREESMA L
4 B.E. CSE A4 962216104022 ASHLIN A Access Control in webpage retrival based on age
9.45 AM - 10.00 AM 962216104027 BHEL ABINAYA ARTHY T
A5 962216104006 AGNES TINA B
Trust Evaluation in sensor network using self-
5 B.E. CSE 10.00 AM - 10.15 962216104016 ANNIE RINISHA V
scrutiny and self-attestation.
AM 962216104043 HARISHMA S
A6 962216104007 AHIN VINITH C
Data Integrity Auditing without Private key for
6 B.E. CSE 10.15 AM - 10.30 962216104047 JENISH M
Secure Cloud Computing
AM 962216104301 ABINESH V
A7 962216104011 ANEESH M
Collaborative Image Privacy Protection in Online
7 B.E. CSE 10.30 AM - 10.45 962216104024 ASWIN RIJO J
Social Networks
AM 962216104025 BENIL S.S
A8 962216104012 ANGELA BONSE S
An effective method for Improving the visual
8 B.E. CSE 10.45 AM - 11.00 962216104018 ANUSHA B
quality of Grey scale Image
AM 962216104049 JENISHA
ANISH M R.S
A9 962216104013 RAGHAVENDRA
9 B.E. CSE 11.00 AM - 11.15 962216104033 DEXLIN D S A Social Media Analyzer using Machine Learning
AM 962216104050 JENISH RICHARD R
A10 962216104014 ANLET SOWMIYA J
Minutiae based personal identification using
10 B.E. CSE 11.15 AM - 11.30
retinal scan
AM
A10
Minutiae based personal identification using
10 B.E. CSE 11.15 AM - 11.30 962216104021 ARUNESHA B S
retinal scan
AM 962216104026 BHAKYA LEKSHMI R
A11 962216104015 ANLIN SHIA R
Securing crowd-sourced data using an untrusted
11 B.E. CSE 11.30 AM - 11.45 962216104023 ASIFA H
server
AM 962216104055 JOHNCY R
A12 962216104017 ANTO P
12 B.E. CSE 11.45 AM - 11.00 962216104053 JIJIN JOSE DBD Assistant
Noon 962216104054 JITHIN GEORGE
A13 962216104019 ANU VINISHA V
Detection of false data injection attacks in smart
13 B.E. CSE 12.00 Noon - 12.15 962216104048 JENISHA J
grid communication systems
PM 962216104034 DHARSHINI R K
A14 962216104020 ANZIL NINU A
Finger print recognition based digital locker
14 B.E. CSE 12.15 AM - 12.30 962216104037 GAYATHRI S
security system
AM 962216104045 JAINEY MOL
CHRISTY S
SAHAYA
A15 962216104028 BRINTHA
Secured data collection with hardware based
15 B.E. CSE 12.30 PM - 12.45 962216104029 DAFINI J
ciphers for IoT based health care
PM 962216104036 FEMINA JASPHIN G
A16 Productivity Enhancement In Database
16 B.E. CSE 12.45 PM - 1.00 962216104004 ABI SHARON M M Infrastructure Monitoring Application By Integrity
PM With A Customized Chat Application
962216104035 FAREEHA JAILANI
W-Smart A web service framework for smart city
17 B.E. CSE A17 962216104041 HARI JANANI M
application
1.00 PM - 1.15 PM 962216104052 JHAFRIN AP
962216104039 GNANA SELVA A
18 B.E. CSE A18 962216104042 HARI KRISHNAN G Enfermedad- A Tool for disease prediction
1.15 PM - 1.30 PM 962216104044 INDIRA JITH V.V
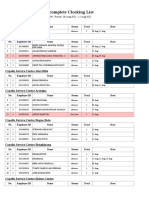
B1 962216104058 KLINSMANN R Smart Travel Android
19 B.E. CSE
9.00 AM - 9.15 AM 962216104073 NIKESH C Application
962216104059 KOHILAM V
Secure and Verifiable Road Condition Monitoring
20 B.E. CSE B2 962216104095 SHAJENA AL SHIFA J
System in VANETS
9.15 AM - 9.30 AM 962216104104 SRUTHI S
B3
A WiFi based prevalent automated billing
21 B.E. CSE 9.30 AM - 9.45 962216104060 KOWSALYA A
systems in shopping malls using Android
AM
962216104061 KRISHNA PRIYA V An Efficient approach
22 B.E. CSE B4 962216104080 RAMYA S. I for Finger Vein
9.45 AM - 10.00 AM 962216104702 ABISHA K A Recognition using support Vector Machine
B5 962216104062 LAJAN Y
MRI Brain Tumor Segmentation using Adaptive
23 B.E. CSE 10.00 AM - 10.15 962216104108 VIGNESH S
Thresholding and SVM Classifier
AM 962216104109 VIJAYCHRISTOPHER
LIFNI K C
B6 962216104063 S
Improved Defogging Methods for Maritime
24 B.E. CSE 10.15 AM - 10.30 962216104070 MUMSHA JOY M
Surveillance
AM 962216104077 PRABISHA V.V
B7 962216104064 MANCY MYSTICA C Integrated Cellular chip Communication for
25 B.E. CSE
10.30 AM - 10.45 962216104076 PON SELVI B Disaster Discovery
B8 962216104066 MEGHA F Hierarchical classification based secure Data
26 B.E. CSE
10.45 AM - 11.00 962216104068 MUJEEBA RAHUMA M sharing scheme in Cloud Computing
B9 962216104069 MUKTHI DEV R S
Two Tier Secure Architecture for Intelligent
27 B.E. CSE 11.00 AM - 11.15 962216104701 SACHIN R Transportation Systems
AM 962216104302 JOHNI KUTTY V
B10 962216104072 NAUSHAD AHAMED S
Service spot - A web based Application for local
28 B.E. CSE 11.15 AM- 11.30 962216104086 RITHIK SAMUEL N
services
AM 962216104101 SHIJU ANTANY S
B11 962216104074 NISCHEVITAA S
An hybrid approach for detecting Automated
29 B.E. CSE 11.30 AM - 11.45 962216104094 SHAHANA BANU S
Spammers in Twitter
AM 962216104103 SOUMYA DEVI C
B12 962216104075 OVIYA A
30 B.E. CSE 11.45 AM - 12.00 962216104082 RASHMI R Human Detection and Tracking during Night Time
Noon 962216104097 SHEBEILA V
B13 962216104079 RAMYA G
Encrypted Negative password using Secure
31 B.E. CSE 12.00 Noon - 12.15 962216104085 RESHMA S
Hashing
PM 962216104088 SANJINI DEV R
B14 962216104081 RAMYA S U
Security and Privacy of Electronic Medical
32 B.E. CSE 12.15 PM - 12.30 962216104102 SHYNISHA M R
Records in Medical training and services
PM 962216104065 MARY JESLIN J
B15 962216104083 RENNY G
Automatic Licence Plate Recognition from Fast
33 B.E. CSE 12.30 PM - 12.45 962216104098 SHEIK P.S
Moving Vehicles
PM 962216104099 SHENITH X
962216104084 RESHMA M
Detecting Malicious URLs Using Machine
34 B.E. CSE B16 962216104087 RIZMAN SAFEERA A
Learning
12.45 PM - 1.00 PM 962216104096 SHANYOMOL S
962216104089 SANTHIYA K
Brain Image Segmentation using Fuzzy Clustering
35 B.E. CSE B17 962216104092 SEETHA KUMARI V
and Roughset
1.00 PM - 1.15 PM 962216104100 SHIFA M
962216104090 SARATH P V
36 B.E. CSE B18 962216104093 SEPHIN REJI SETTLES – Web Based Service Application
1.15 PM - 1.30 PM 962216104106 SUPRADEEP A
B19 962216104105 SUJITHA A Stock Trend Market Prediction Using Machine
37 B.E. CSE
1.30 PM - 1.45 PM 962216104110 VINISHA S S Learning Techniques
You might also like
- Mca Project ListDocument39 pagesMca Project ListBala SudhakarNo ratings yet
- Project Expo 23Document1 pageProject Expo 23yb9894447173No ratings yet
- Project Panel Submission Format For Colleges 15-09-2020Document6 pagesProject Panel Submission Format For Colleges 15-09-2020addssdfaNo ratings yet
- An Autonomous Institution Affiliated To Anna University ChennaiDocument6 pagesAn Autonomous Institution Affiliated To Anna University Chennaishenbagaraman cseNo ratings yet
- Academic Projects-EEE-2016: L.no Project Title Students Name Guide NameDocument45 pagesAcademic Projects-EEE-2016: L.no Project Title Students Name Guide NameImma TzNo ratings yet
- Jadwal PTMT Gasal 2021-2022Document6 pagesJadwal PTMT Gasal 2021-2022ARIZKINo ratings yet
- Bca List 2020-2021Document6 pagesBca List 2020-2021Murtaza AhmarNo ratings yet
- Project Expo 22Document6 pagesProject Expo 22tvenishkumarNo ratings yet
- Masurari Electrice Si Electronice: NR - Crt. Nume Initiala Prenume Grupa Sgr. N - LBDocument6 pagesMasurari Electrice Si Electronice: NR - Crt. Nume Initiala Prenume Grupa Sgr. N - LBmihaela0chiorescuNo ratings yet
- Simple 2Document1 pageSimple 2Jai PandiaNo ratings yet
- IntSch 257 EOAO EPFO EnglDocument24 pagesIntSch 257 EOAO EPFO EnglHamdardvir Singh BoparaiNo ratings yet
- East Point College of Engineering and Technology Bangalore Collegecode - Ep Date - 2021-03-08 Session - 14:00:00 Count - 57Document5 pagesEast Point College of Engineering and Technology Bangalore Collegecode - Ep Date - 2021-03-08 Session - 14:00:00 Count - 57Vasavi VaasuNo ratings yet
- M.E 2009 Phase2Document2 pagesM.E 2009 Phase2Ganesh BabuNo ratings yet
- List of ProjectsDocument1 pageList of Projectsnoble aNo ratings yet
- Result Analysis VIII Sem Format 1 - After RevaluationDocument4 pagesResult Analysis VIII Sem Format 1 - After Revaluationmanoj3e9329No ratings yet
- Midterm Examination Schedule Spring 2021: 507 Total Number of StudentsDocument13 pagesMidterm Examination Schedule Spring 2021: 507 Total Number of StudentsWajiha NadeemNo ratings yet
- BDS NJ 3rd PhaseDocument8 pagesBDS NJ 3rd PhaseABHERAMNo ratings yet
- Random Experiment Numbers: Internal Examiner External ExaminerDocument2 pagesRandom Experiment Numbers: Internal Examiner External ExaminerChithambaramaniRamalingamNo ratings yet
- Project Batch III YearDocument5 pagesProject Batch III YearKeerthy B.No ratings yet
- IV Year Project Details MODELDocument8 pagesIV Year Project Details MODELsridharchandrasekarNo ratings yet
- PL - 400-Hdyrnt LT 7 - LT 8Document2 pagesPL - 400-Hdyrnt LT 7 - LT 8Muh SanadNo ratings yet
- TN Rank List 2019 - With AIQ R1 Allotment Details PDFDocument173 pagesTN Rank List 2019 - With AIQ R1 Allotment Details PDFNavin Chandar50% (10)
- Inv#18 PDFDocument1 pageInv#18 PDFDhanush Shiva DollaiahNo ratings yet
- B.E CseDocument13 pagesB.E CsePulihora Kat RajaNo ratings yet
- 103 Civil PDFDocument3 pages103 Civil PDFci_balaNo ratings yet
- Auto PDFDocument14 pagesAuto PDFAnonymous CyJpkXENo ratings yet
- 2022-23 Btech I-II Sem Class TeachersDocument1 page2022-23 Btech I-II Sem Class Teachersm bilalNo ratings yet
- 21.07.2020 UG Exam Data Time Updated 1Document55 pages21.07.2020 UG Exam Data Time Updated 1Nikkil VNo ratings yet
- Due Date Telephone Number Amount Payable: Summary of Charges Usage History (6 Months)Document5 pagesDue Date Telephone Number Amount Payable: Summary of Charges Usage History (6 Months)GEO MERINNo ratings yet
- 9622 - St. Xavier's Catholic College of Engineering Sl. No. Register No. NameDocument8 pages9622 - St. Xavier's Catholic College of Engineering Sl. No. Register No. NameGEO MERINNo ratings yet
- 5 6138936303955215003Document28 pages5 6138936303955215003GEO MERINNo ratings yet
- Due Date Telephone Number Amount Payable: GstinDocument5 pagesDue Date Telephone Number Amount Payable: GstinGEO MERINNo ratings yet
- Research On Global Positioning System in Mobile Communication Equipment Based On Android PlatformDocument3 pagesResearch On Global Positioning System in Mobile Communication Equipment Based On Android PlatformGEO MERINNo ratings yet
- ١٩-ﺪﻴﻓﻮﻛ ﺎﻧورﻮﻛ سوﺮﻴﻓ ﺪﺿ ﻢﻴﻌﻄﺗ ةدﺎﻬﺷ COVID-19 Vaccination CertificateDocument1 page١٩-ﺪﻴﻓﻮﻛ ﺎﻧورﻮﻛ سوﺮﻴﻓ ﺪﺿ ﻢﻴﻌﻄﺗ ةدﺎﻬﺷ COVID-19 Vaccination CertificateGEO MERINNo ratings yet
- Wellness Manual MM F 179245Document2 pagesWellness Manual MM F 179245GEO MERINNo ratings yet
- Scanned by CamscannerDocument29 pagesScanned by CamscannerGEO MERINNo ratings yet
- MAP UNIT 4 MCQDocument6 pagesMAP UNIT 4 MCQGEO MERIN50% (2)
- TAM9559732640156815Document3 pagesTAM9559732640156815GEO MERINNo ratings yet
- Unit 3 MCQDocument4 pagesUnit 3 MCQGEO MERINNo ratings yet
- MOHAMMEDDocument4 pagesMOHAMMEDGEO MERINNo ratings yet
- Sars-Cov2 (Covid-19) Real Time RT PCR TestDocument2 pagesSars-Cov2 (Covid-19) Real Time RT PCR TestGEO MERINNo ratings yet
- Core Network NFV Proposal For TelcelDocument8 pagesCore Network NFV Proposal For TelcelTELCELINNo ratings yet
- Process Realization Plan: Recruitment and Terminal Benefits ProcessDocument24 pagesProcess Realization Plan: Recruitment and Terminal Benefits ProcessAliIrfanNo ratings yet
- Barredo-Fuentes VS AlbarracinDocument15 pagesBarredo-Fuentes VS AlbarracinViolet BlueNo ratings yet
- STS Syllabus+by+Zarate+JohnDocument17 pagesSTS Syllabus+by+Zarate+JohnJayson DayaoNo ratings yet
- Dolan Et Al. v. Altice USA Inc. Et Al. - Verified ComplaintDocument347 pagesDolan Et Al. v. Altice USA Inc. Et Al. - Verified ComplaintAnonymous g2k2l9b100% (1)
- Marketing Management AssignmentDocument11 pagesMarketing Management AssignmentAnirudh MariaNo ratings yet
- Organization and ManagementDocument11 pagesOrganization and ManagementJaslor LavinaNo ratings yet
- Wykład V.L.SmithDocument20 pagesWykład V.L.SmithprnoxxxNo ratings yet
- McGill-Toolen ResponseDocument18 pagesMcGill-Toolen ResponseJosh BeanNo ratings yet
- 48 Weeks To Fitting The Armor WorkbookDocument115 pages48 Weeks To Fitting The Armor WorkbookAMADO JR BANAWA0% (1)
- 8th Edition Iron Hands Supplement UpdateDocument9 pages8th Edition Iron Hands Supplement UpdateSUPER DJNo ratings yet
- Letter Holy QuranDocument2 pagesLetter Holy QuranAtta RasoolNo ratings yet
- 153 - EPTISA-GM P-2020 - Proposal of Mr. Suhail Khandal For Position of Material EngineerDocument3 pages153 - EPTISA-GM P-2020 - Proposal of Mr. Suhail Khandal For Position of Material EngineerMohd UmarNo ratings yet
- Medieval Joke PoetryDocument67 pagesMedieval Joke PoetryMAVORTIUSNo ratings yet
- If You're Not in Bed by Ten, Come Home - Martin BengtssonDocument17 pagesIf You're Not in Bed by Ten, Come Home - Martin BengtssonMaverick House PublishersNo ratings yet
- Vipassana Weeds in The Wheat Field by Errol FernandesDocument9 pagesVipassana Weeds in The Wheat Field by Errol FernandesFrancis LoboNo ratings yet
- Certificate of IncorporationDocument1 pageCertificate of IncorporationSolanki AshokNo ratings yet
- Listening Practice (Week 9)Document1 pageListening Practice (Week 9)Cici AgussariNo ratings yet
- Dagsaw JRMP2 FPICDocument2 pagesDagsaw JRMP2 FPICPhil ZiggyNo ratings yet
- SociologyDocument146 pagesSociologyVil JeffNo ratings yet
- The True Meaning of LentDocument8 pagesThe True Meaning of LentAndrew WamaeNo ratings yet
- FairnessDocument4 pagesFairnessJanjan Dumaual100% (1)
- Historical Documents Concerning the Ancient Britons - Ιστορικά έγγραφα σχετικά με τους αρχαίους ΒρετανούςDocument534 pagesHistorical Documents Concerning the Ancient Britons - Ιστορικά έγγραφα σχετικά με τους αρχαίους ΒρετανούςmaroudaspNo ratings yet
- Penjelasan Absen 08 - 15 Agt So SPPDocument25 pagesPenjelasan Absen 08 - 15 Agt So SPPnampatisembiringNo ratings yet
- German RevolutionDocument11 pagesGerman RevolutionMeruthulaNo ratings yet
- Foundation of The Christian Faith: The Revelation of GodDocument9 pagesFoundation of The Christian Faith: The Revelation of GodsimpliciusNo ratings yet
- AVBS1003-2020-Lecture 4-Role of ZoosDocument32 pagesAVBS1003-2020-Lecture 4-Role of ZoosOttilia LaiNo ratings yet
- Music of The Lowlands of Luzon 2: Secular Music With Spanish InfluenceDocument20 pagesMusic of The Lowlands of Luzon 2: Secular Music With Spanish InfluenceRiza Indelible SibullasNo ratings yet
- EntrepDocument10 pagesEntrepAlmira AbeNo ratings yet
- Bamu Essay PandemicDocument2 pagesBamu Essay Pandemicbamlak teshomeNo ratings yet