Professional Documents
Culture Documents
E Com 4
E Com 4
Uploaded by
Ankur SinghOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
E Com 4
E Com 4
Uploaded by
Ankur SinghCopyright:
Available Formats
Home work 4
CAP312
1. Explain symmetric and asymmetric cryptography with the help of
example
Ans 1
In a symmetric cipher, both parties must use the same key for encryption and decryption.
This means that the encryption key must be shared between the two parties before any
messages can be decrypted. Symmetric systems are also known as shared secret systems or
private key systems.
Symmetric ciphers are significantly faster than asymmetric ciphers, but the requirements for
key exchange make them difficult to use.
In an asymmetric cipher, the encryption key and the decryption keys are separate. In an
asymmetric system, each person has two keys. One key, the public key, is shared publicly.
The second key, the private key, should never be shared with anyone.
When you send a message using asymmetric cryptography, you encrypt the message using
the recipients public key. The recipient then decrypts the message using his private key. That
is why the system is called asymmetric.
Because asymmetric ciphers tend to be significantly more computationally intensive, they are
usually used in combination with symmetric ciphers to implement effect public key
cryptography. The asymmetric cipher is used to encrypt a session key and the encrypted
session key is then used to encrypt the actual message. This gives the key-exchange benefits
of asymmetric ciphers with the speed of symmetric ciphers.
2. Draw a diagram to represt the internet banking
Ans 2
3. Enlist some of the events provided by the gateways
Ans 3
provides marketing and sales opportunities to reach your audience. Exhibit with Ecommerce
Gateway Pakikstan, we’ll help you move your technology to market.
Reach prequalified buyers
Establish alliances with vendors
Learn about your industry’s future
Build product and brand awareness
Differentiate your offerings
Test market new products
Stay ahead of your competition
4. Explain role of RBI to promote internet banking
Ans 4
Monetary Authority:
• Formulates, implements and monitors the monetary policy.
• Objective: maintaining price stability and ensuring adequate flow of credit to
productive sectors.
Regulator and supervisor of the financial system:
• Prescribes broad parameters of banking operations within which the country''s
banking and financial system functions.
• Objective: maintain public confidence in the system, protect depositors'' interest and
provide cost-effective banking services to the public.
• Regulator and supervisor of the payment systems
o Authorises setting up of payment systems
o Lays down standards for operation of the payment system
o Issues direction, calls for returns/information from payment system operators.
Manager of Foreign Exchange
• Manages the Foreign Exchange Management Act, 1999.
• Objective: to facilitate external trade and payment and promote orderly development
and maintenance of foreign exchange market in India.
Issuer of currency:
• Issues and exchanges or destroys currency and coins not fit for circulation.
• Objective: to give the public adequate quantity of supplies of currency notes and coins
and in good quality.
Developmental role
• Performs a wide range of promotional functions to support national objectives.
Related Functions
• Banker to the Government: performs merchant banking function for the central and
the state governments; also acts as their banker.
• Banker to banks: maintains banking accounts of all scheduled banks.
5. Draw a flow chart to represent necessity of digital signature in
business
Ans 5
You might also like
- Business PlanDocument11 pagesBusiness Plan陈文源100% (2)
- Apexum - Forex Broker Business Plan 2Document43 pagesApexum - Forex Broker Business Plan 2Khaleel Musleh67% (3)
- Course ID 51803 RiO Application Operation CompetencyDocument9 pagesCourse ID 51803 RiO Application Operation CompetencyAnkur Singh100% (2)
- TOSCA AutomationDocument3 pagesTOSCA AutomationAnkur Singh0% (1)
- G and T Awareness PDFDocument5 pagesG and T Awareness PDFAnkur Singh100% (1)
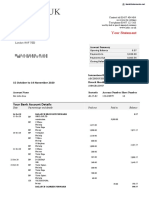
- Your Statement: Your Bank Account DetailsDocument5 pagesYour Statement: Your Bank Account DetailsIvan Krutko75% (4)
- Microsoft Teams Developer Final AssesmentDocument2 pagesMicrosoft Teams Developer Final AssesmentAnkur Singh100% (1)
- ABBYY FlexiCaptureDocument7 pagesABBYY FlexiCaptureAnkur SinghNo ratings yet
- Azure DevOpsDocument2 pagesAzure DevOpsAnkur Singh100% (1)
- SAP FinanceDocument94 pagesSAP FinanceAnkur SinghNo ratings yet
- Currency Convertor: 1.abstractDocument6 pagesCurrency Convertor: 1.abstractUSHASI BANERJEE100% (1)
- Information System For Brokerage HouseDocument17 pagesInformation System For Brokerage HouseVivek KushwahaNo ratings yet
- Cloud FoundryDocument30 pagesCloud FoundryAnkur Singh0% (1)
- StraMa Worksheet 9 Competitive Profile MatrixDocument5 pagesStraMa Worksheet 9 Competitive Profile MatrixRenée Kristen CortezNo ratings yet
- Use Case StudyDocument4 pagesUse Case StudyDustin ShepherdNo ratings yet
- Ecommerce Payment 10012022 054233pmDocument32 pagesEcommerce Payment 10012022 054233pmJawad BhuttaNo ratings yet
- Python TrainingDocument22 pagesPython TrainingHimanshu RajNo ratings yet
- Assignment 1 IISDocument4 pagesAssignment 1 IISZulqarnain KambohNo ratings yet
- Topic 4 Highlights - Wallet and Key ManagementDocument5 pagesTopic 4 Highlights - Wallet and Key ManagementOlivia RadaNo ratings yet
- A Study OnDocument64 pagesA Study OnforwasteNo ratings yet
- CryptoME BUSINESS PLAN 2022Document11 pagesCryptoME BUSINESS PLAN 2022Ceñidoza Ian AlbertNo ratings yet
- Ch4 Symmetric EncryptionDocument21 pagesCh4 Symmetric EncryptionNajma baasheNo ratings yet
- CryptoME BUSINESS PLAN 2022 Techno (Beñegas, Cruz, Ceñidoza, Nariz, Torres)Document10 pagesCryptoME BUSINESS PLAN 2022 Techno (Beñegas, Cruz, Ceñidoza, Nariz, Torres)Ceñidoza Ian AlbertNo ratings yet
- Complete SRS!!!Document5 pagesComplete SRS!!!Farhan SirkhotNo ratings yet
- Title - Crypto-Currency TrackerDocument15 pagesTitle - Crypto-Currency TrackerRishabh MishraNo ratings yet
- Online TrainingDocument57 pagesOnline Trainingvinayagrawal86No ratings yet
- Algorithm Trading Strategies- Crypto and Forex - The Advanced Guide For Practical Trading StrategiesFrom EverandAlgorithm Trading Strategies- Crypto and Forex - The Advanced Guide For Practical Trading StrategiesRating: 5 out of 5 stars5/5 (1)
- Prolitus - Proposal - Crypto Exchange Ade AndrianDocument14 pagesProlitus - Proposal - Crypto Exchange Ade AndrianMay EsterinaNo ratings yet
- Security: Certificates, SSL Banking, MonitoringDocument25 pagesSecurity: Certificates, SSL Banking, MonitoringeviroyerNo ratings yet
- Protected Banking Verification by Figure Pixel Comparison and Bit Coin Transaction Using Block Chain and Image ProcessingDocument18 pagesProtected Banking Verification by Figure Pixel Comparison and Bit Coin Transaction Using Block Chain and Image ProcessingBalamurugan SMNo ratings yet
- Three Kinds of E-Wallets For A Netpay Micro-Payment SystemDocument12 pagesThree Kinds of E-Wallets For A Netpay Micro-Payment Systemsnkelkar16531No ratings yet
- Quikr SrsDocument23 pagesQuikr Srsvijaysai nuniNo ratings yet
- FAH - Crypto CurrencyDocument10 pagesFAH - Crypto CurrencyFaisal A. HussainNo ratings yet
- Whitepaper Ama Token InglesDocument22 pagesWhitepaper Ama Token InglesbelmanNo ratings yet
- Prolitus - Proposal - Crypto Exchange V.1.1Document14 pagesProlitus - Proposal - Crypto Exchange V.1.1May EsterinaNo ratings yet
- Digicash CybercashDocument20 pagesDigicash CybercashAnshul GargNo ratings yet
- WINSEM2022-23 CSE1006 TH VL2022230503155 2023-03-20 Reference-Material-IDocument32 pagesWINSEM2022-23 CSE1006 TH VL2022230503155 2023-03-20 Reference-Material-Ipadm kesavNo ratings yet
- Quikr Software Requirement Specification SrsDocument18 pagesQuikr Software Requirement Specification Srsyuvrajsinghsalariarajput113No ratings yet
- ReportDocument12 pagesReportkirti_guptaNo ratings yet
- Credit Card Fraud Detection Using Neural NetworksDocument30 pagesCredit Card Fraud Detection Using Neural Networkspavithra thatikondaNo ratings yet
- Credit Card Fraud Detection MethodsDocument36 pagesCredit Card Fraud Detection MethodsS Veera Reddy0% (1)
- Class: Financial Management Topic: Process of Online Trading in India Semester: I Date:17-Oct-2020Document16 pagesClass: Financial Management Topic: Process of Online Trading in India Semester: I Date:17-Oct-2020Rudraksh PareyNo ratings yet
- How To Trade CryptoDocument8 pagesHow To Trade CryptoDawo InvestorNo ratings yet
- Cryptocurrency V4Document19 pagesCryptocurrency V4cavishkar57No ratings yet
- AMMC WPDocument17 pagesAMMC WPLiam Selim OmarNo ratings yet
- Swot and ProductDocument5 pagesSwot and ProductavinishNo ratings yet
- Crypto Basic InfoDocument7 pagesCrypto Basic InfoHina ShehzadiNo ratings yet
- Unit 2Document152 pagesUnit 2Rohit KoliNo ratings yet
- Foreign Trading SystemDocument37 pagesForeign Trading Systemabarnatl03No ratings yet
- Cryptocurrency TrackerDocument5 pagesCryptocurrency Tracker19bcs1718No ratings yet
- Whitepaper V 1.941 EngDocument98 pagesWhitepaper V 1.941 EngSinggih SeptiyanNo ratings yet
- Mastering Cryptocurrency Arbitrage: A Comprehensive Guide to Profitable Trading Strategies: way to wealth, #22From EverandMastering Cryptocurrency Arbitrage: A Comprehensive Guide to Profitable Trading Strategies: way to wealth, #22No ratings yet
- MoonX - Technical WPDocument15 pagesMoonX - Technical WPInternova LiveRiverNo ratings yet
- Keerthana 1cd18mca67Document49 pagesKeerthana 1cd18mca67SireeshaNo ratings yet
- Sher KhanDocument14 pagesSher KhanRaja SinghNo ratings yet
- Usama Bin Nasir (2029) BinanceDocument4 pagesUsama Bin Nasir (2029) Binanceuzair nomanNo ratings yet
- ATM Banking SystemDocument3 pagesATM Banking SystemmohitNo ratings yet
- Formal MethodDocument5 pagesFormal MethodAmsa AzeemNo ratings yet
- What Is BitcoinDocument27 pagesWhat Is BitcoinDammi LauNo ratings yet
- Client Server (Maybank)Document24 pagesClient Server (Maybank)ikanbutsuNo ratings yet
- Introduction ATMDocument71 pagesIntroduction ATMaarasu00757% (7)
- Credit Card Fraud DetectionDocument38 pagesCredit Card Fraud Detectionshaa51021No ratings yet
- Cryptocurrency Trading & Investment Guide for Bulls: 2 in 1 Blockchain & Bitcoin Revolution. How to DeFi and Make Money in Decentralized Finance. Learn Bitcoin and Ethereum and Altcoins.From EverandCryptocurrency Trading & Investment Guide for Bulls: 2 in 1 Blockchain & Bitcoin Revolution. How to DeFi and Make Money in Decentralized Finance. Learn Bitcoin and Ethereum and Altcoins.No ratings yet
- Aim: Finger Print Based ATM System Problem Statement: He Wants To TransferDocument3 pagesAim: Finger Print Based ATM System Problem Statement: He Wants To TransferHarry PotterNo ratings yet
- Sàad Sàlahûddin - Assignment On Bin SultanDocument4 pagesSàad Sàlahûddin - Assignment On Bin Sultanuzair nomanNo ratings yet
- Cryptocurrency: Last 2 Slides Very Very ImportantDocument18 pagesCryptocurrency: Last 2 Slides Very Very ImportantRushabNo ratings yet
- Dr.P.G.Arul Dept. of International Business Pondicherry University Pondicherry - 605014Document17 pagesDr.P.G.Arul Dept. of International Business Pondicherry University Pondicherry - 605014vel.well1996No ratings yet
- Online Bidding SystemDocument75 pagesOnline Bidding Systempavithra100% (1)
- Crypto CrunchDocument13 pagesCrypto CrunchMUKADAM ISMAILNo ratings yet
- Foreign Trading System ReportDocument45 pagesForeign Trading System Reportabinsha78% (9)
- Crypto Craft: Cryptocurrency Market Dynamics: Analyzing Trends for Optimal Trading OutcomesFrom EverandCrypto Craft: Cryptocurrency Market Dynamics: Analyzing Trends for Optimal Trading OutcomesNo ratings yet
- Implementing Design ThinkingDocument9 pagesImplementing Design ThinkingAnkur Singh100% (1)
- Mobile App Security QuizDocument2 pagesMobile App Security QuizAnkur SinghNo ratings yet
- Hybrid Apps IntroductionDocument21 pagesHybrid Apps IntroductionAnkur SinghNo ratings yet
- Java InnardsDocument3 pagesJava InnardsAnkur SinghNo ratings yet
- Ansible Automation CoralDocument2 pagesAnsible Automation CoralAnkur SinghNo ratings yet
- Fresco Play 4Document22 pagesFresco Play 4Ankur SinghNo ratings yet
- Association Rule MiningDocument1 pageAssociation Rule MiningAnkur SinghNo ratings yet
- WorkFusion RPA ExpressDocument10 pagesWorkFusion RPA ExpressAnkur SinghNo ratings yet
- Mobile App Security PDFDocument3 pagesMobile App Security PDFAnkur SinghNo ratings yet
- Web Services Security 1Document1 pageWeb Services Security 1Ankur SinghNo ratings yet
- Fresco Play Training 2Document12 pagesFresco Play Training 2Ankur SinghNo ratings yet
- User Research Methods Q ADocument3 pagesUser Research Methods Q AAnkur SinghNo ratings yet
- Cloud ComputingDocument36 pagesCloud ComputingAnkur SinghNo ratings yet
- Stats With PythonDocument4 pagesStats With PythonAnkur SinghNo ratings yet
- Regression Analysis Q ADocument2 pagesRegression Analysis Q AAnkur SinghNo ratings yet
- Automatix Art of RPADocument25 pagesAutomatix Art of RPAAnkur Singh50% (2)
- Google Cloud EssentialDocument19 pagesGoogle Cloud EssentialAnkur Singh100% (1)
- Digital Malware AnalysisDocument2 pagesDigital Malware AnalysisAnkur SinghNo ratings yet
- Data Mining NostosDocument39 pagesData Mining NostosAnkur Singh100% (1)
- Amazon Storage S3Document4 pagesAmazon Storage S3Ankur SinghNo ratings yet
- An Enlightenment To Machine LearningDocument16 pagesAn Enlightenment To Machine LearningAnkur Singh100% (1)
- EMC SAN IntroDocument40 pagesEMC SAN Introsreenathonweb100% (1)
- Configuration FICODocument253 pagesConfiguration FICOjiljil1980No ratings yet
- JANKIDocument47 pagesJANKIJankiNo ratings yet
- Capital Markets Act Cap 485ADocument73 pagesCapital Markets Act Cap 485AMsema Kweli JumanneNo ratings yet
- Industry Trends - Evidor & Gomez HDocument41 pagesIndustry Trends - Evidor & Gomez HErika EvidorNo ratings yet
- Austria - Domestic Interchange FeesDocument5 pagesAustria - Domestic Interchange FeesFlorent TardivelNo ratings yet
- Farrukh Mushtaq Resume FinalDocument3 pagesFarrukh Mushtaq Resume FinalLeah PalmerNo ratings yet
- Syllabus of Banking & Insurance LawDocument4 pagesSyllabus of Banking & Insurance LawAkshay DhawanNo ratings yet
- Chaebols and KeiretsusDocument11 pagesChaebols and Keiretsusamya_sinha11No ratings yet
- Sources of Finance (Business Ib)Document3 pagesSources of Finance (Business Ib)Georgie ZafetNo ratings yet
- Commercial Lendings by BanksDocument65 pagesCommercial Lendings by Banksvivek satviNo ratings yet
- Board Resolution: Appointment of Authorised PersonsDocument5 pagesBoard Resolution: Appointment of Authorised Personsnawala_sa_asyaNo ratings yet
- CIBIL - Know Your Cibil Score - Get Your Cibil Score Deal4loansDocument2 pagesCIBIL - Know Your Cibil Score - Get Your Cibil Score Deal4loansVenkatrao GarigipatiNo ratings yet
- Financial Networth Statement WhereasDocument4 pagesFinancial Networth Statement Whereasjames agboNo ratings yet
- Tunis Stock ExchangeDocument54 pagesTunis Stock ExchangeAnonymous AoDxR5Rp4JNo ratings yet
- Prepaid CardsDocument4 pagesPrepaid CardsVikramjeet SinghNo ratings yet
- BreakdownDocument103 pagesBreakdownhandiNo ratings yet
- CHAPTERIZATIONDocument45 pagesCHAPTERIZATIONRozlyn Rosa100% (3)
- Rene GautreauxDocument19 pagesRene GautreauxAnonymous vRG3cFNjANo ratings yet
- Class Action Suit Filed Against Bank of America For Abuse in TexasDocument51 pagesClass Action Suit Filed Against Bank of America For Abuse in TexasDinSFLANo ratings yet
- Risk Management in BankingDocument45 pagesRisk Management in Bankingpanaskar.umesh100% (3)
- Ia1 NotesDocument23 pagesIa1 NotesAssej C AustriaNo ratings yet
- LAMPIRANDocument49 pagesLAMPIRANInri Gloria TampiNo ratings yet
- Mohd Azhar Abdul Ghafar 2012984401 - OPM 530 TUTORIAL 1Document2 pagesMohd Azhar Abdul Ghafar 2012984401 - OPM 530 TUTORIAL 1Farapple24No ratings yet
- Chap 23Document12 pagesChap 23Sakshi GuptaNo ratings yet
- Account Statement 230919 221019Document7 pagesAccount Statement 230919 221019Latest UpdatesNo ratings yet
- 1 Citibank Vs SabenianoDocument2 pages1 Citibank Vs SabenianoJudielle BrianNo ratings yet
- Make Wire Transfers Through Online Banking From AnywhereDocument2 pagesMake Wire Transfers Through Online Banking From AnywhereDani PermanaNo ratings yet