Professional Documents
Culture Documents
OSG202 Revise3
OSG202 Revise3
Uploaded by
Trần Khang0 ratings0% found this document useful (0 votes)
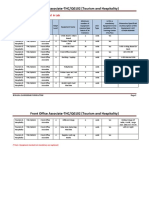
59 views46 pagesThe document contains multiple choice questions about operating systems concepts such as CPU scheduling algorithms, memory management techniques, and virtual memory. Key information that must be saved before transferring control to an interrupt handler includes the program status word (PSW) and processor register contents. Round robin scheduling with a time quantum of 4 would result in a turnaround time of 22 for job D. Demand paging made virtual memory feasible. The working set model is used to determine the minimum number of frames needed for a job to run without excessive paging.
Original Description:
Original Title
OSG202_Revise3
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document contains multiple choice questions about operating systems concepts such as CPU scheduling algorithms, memory management techniques, and virtual memory. Key information that must be saved before transferring control to an interrupt handler includes the program status word (PSW) and processor register contents. Round robin scheduling with a time quantum of 4 would result in a turnaround time of 22 for job D. Demand paging made virtual memory feasible. The working set model is used to determine the minimum number of frames needed for a job to run without excessive paging.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
59 views46 pagesOSG202 Revise3
OSG202 Revise3
Uploaded by
Trần KhangThe document contains multiple choice questions about operating systems concepts such as CPU scheduling algorithms, memory management techniques, and virtual memory. Key information that must be saved before transferring control to an interrupt handler includes the program status word (PSW) and processor register contents. Round robin scheduling with a time quantum of 4 would result in a turnaround time of 22 for job D. Demand paging made virtual memory feasible. The working set model is used to determine the minimum number of frames needed for a job to run without excessive paging.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 46
OSG202 B - QN=5 (6863) Information that must be
saved prior to the processor transferring control
B - QN=1 (6836) A CPU may have multiple to the interrupt handler routine includes:
execution units, so that can carry out multiple a. PSW
instructions in the same time is called: b. PSW and PC
a. Pipeline c. PSW and Contents of processor registers
b. Superscalar d. None of the other choices
c. Multicore ________________________________
d. None of the other choices C - QN=6 (6871) What is not a main function of
________________________________ an operating system?
C - QN=2 (6843) The four main structural a. Provide the users with an extended (virtual)
elements of a computer system are: machine
a. Processor, Registers, I/O Modules, Main b. Manage the I/O devices
Memory c. Provide user interfaces
b. Processor, Registers, Main Memory, System d. Support virtual memory
Bus ________________________________
c. Processor, Main Memory, I/O Modules, C - QN=7 (6883) What is the main
System Bus characteristic of real-time operating system?
d. None of the other choices a. Multiple CPU
________________________________ b. Time-sharing
B - QN=3 (6849) Which of the following c. Time is key parameter
instructions should be allowed in user mode? d. Many I/O devices
a. Disable all interrupts ________________________________
b. Read the time-of-day clock C - QN=8 (6898) What is not correct about
c. Set the time-of-day clock system calls?
d. Change the memory map a. A system call allows a user process to
________________________________ assess and execute operating system functions
C - QN=4 (6858) As one proceeds down the inside the kernel.
memory hierarchy(phân cấp bộ nhớ) (from b. User programs use system calls to invoke
inboard memory to offline storage), which of the operating system services
following conditions is correct? c. In terms of performance, using system calls
a. Increasing cost per bit is better than using procedure calls
b. Decreasing capacity d. Every system call involves overhead due to
c. Increasing access time context switch
d. None of the other choices ________________________________
________________________________ D - QN=9 (6903) Which of the following is a
task of process management of OS?
a. Process creation and deletion. these programs are idle waiting for I/O half the
b. Process suspension and resume time?
c. Provision of mechanisms for process a. 50%
synchronization, Interprocess communication, b. 25%
Prevent or avoid deadlock c. 75%
d. All of the other choices d. None of the other choices
________________________________ ________________________________
D - QN=10 (6909) A simple structuring model C - QN=14 (6956) How many ways is Thread
for monolithic system includes: implemented?
a. A main program that invokes the requested a. 1
service procedure b. 2
b. A set of service procedures that carry out the c. 3
system calls d. None of the other choice
c. A set of utility procedures that help the ________________________________
service procedures A - QN=15 (6963) Critical Region (Section)
d. All of the other choices concept used in interprocess communication is:
________________________________ a. A part of the program where the shared
C - QN=11 (6925) What is the "sequential memory is accessed
processes" concept? b. A part of shared data
a. There are both many CPU and many PC c. A part of shared memory
b. All process is executed in concurrency d. None of the other choices
c. No concurrency inside a process; everything ________________________________
happens sequentially A - QN=16 (6969) Which of the following
d. None of the other choices statements is a hardware solution to the critical
________________________________ region problem?
C - QN=12 (6941) Which of the following a. TSL
process state transitions is correct, when the b. Shared memory
external event for which a process was waiting c. Semaphore
happens? d. None of the other choices
a. Running -> Blocked (waiting) ________________________________
b. Running -> ready D - QN=17 (6978) Which of the following is true
c. Blocked (waiting) -> ready about Atomic action on semaphores?
d. Ready -> running a. Checking the value
________________________________ b. Changing the value
B - QN=13 (6948) How many percent of the c. Possibly going to sleep
CPU time is wasted, when a computer system d. All of the other choices
has enough room to hold two program and ________________________________
A - QN=18 (6987) Which of the following round robin scheduling (quantum=4), the
statements is true about hardware solution to turnaround time for job D is ____.
the critical region problem? Arrival time: 0 1 2 3
a. Disable Interrupts Job: A B C D
b. Monitors CPU cycle: 8 4 9 5
c. Semaphore a. 7
d. None of the other choices b. 20
________________________________ c. 22
A - QN=19 (6991) What is the purpose of CPU d. 24
scheduling algorithms? ________________________________
a. Pick one of the ready processes to run next A - QN=23 (7021) Which of following is true
b. Put to sleep and wake up processes in an about cache in the memory hierarchy?
efficient manner a. Small amount of fast expensive memory
c. Allocate memory to the processes in a fair b. Some medium-speed medium price
and efficient way c. Gigabytes of slow cheap memory
d. None of the other choices d. None of the other choices
________________________________ ________________________________
B - QN=20 (6999) The first-come, first-served C - QN=24 (7029) Which of the following is a
(FCFS) algorithm is fine for most ____ systems method to keep track of memory usages?
a. Interactive a. Memory Management with Bit Maps
b. Batch b. Memory Management with Linked Lists
c. Real time c. Both Memory Management with Bit Maps
d. Multiuser and Memory Management with Linked Lists
________________________________ d. None of the other choices
A - QN=21 (7007) Five batch jobs A through E, ________________________________
arrive at a computer center at almost the same D - QN=26 (7042) One of the most important
time. They have estimated running times of 8, innovations of demand paging was that it made
6, 2, 10, and 4 minutes. Determine the average ____ feasible
waiting time for SJF (Shortest job first) a. Memory demand
scheduling. Ignore process switching overhead. b. Virtual demand
a. 14 minutes c. Virtual paging
b. 8 minutes d. Virtual memory.
c. 6 minutes ________________________________
d. 18.8 minutes A - QN=27 (7048) Which of these statements
________________________________ about the Inverted Page Table are true?
C - QN=22 (7015) Assume jobs A-D arrive in
quick succession in the READY queue. Using
a. An entry contains the pair (process, virtual c. A TLB miss implies a disk operation will
page) mapped into the corresponding page follow
frame d. None of the other choices
b. An entry contains the pair (process, offset) ________________________________
mapped into the corresponding page frame A - QN=31 (7080) Working set model is used
c. An entry contains the pair (segment, virtual for:
page) mapped into the corresponding page a. Finding the minimum number of frames
frame necessary for a job so that jobs can be run
d. An entry contains the pair (segment, offset) without "thrashing"
mapped into the corresponding page frame b. Finding the average number of frames a job
________________________________ will need to run smoothly
D - QN=28 (7057) If there are 64 pages and the c. Determining whether page replacement is
page size is 2048 words, what is the length of needed
logical address? d. All of the other choices
a. 14 bits ________________________________
b. 15 bits C - QN=32 (7086) Which is not true about the
c. 16 bits method of backing store: "Paging to a static
d. 17 bits swap area"?
________________________________ a. The swap area on the disk is as large as the
C - QN=29 (7065) A system with 32 bit virtual process virtual address space
address. If the page size is 4 KB and each table b. Calculating the address in swap area
entry occupies 4 bytes, what is the size of the requires knowing only where the process'
page table? paging area begins
a. 1 MB c. Requires a disk map in memory
b. 2 MB d. A page that is in memory always have
c. 4 MB shadow copy on disk
d. 8 MB ________________________________
________________________________ D - QN=33 (7092) Which of the following
C - QN=30 (7072) Which of the following statements about segmentation is false?
statements is incorrect about Translation Look- a. There are several linear address spaces
aside Buffer (TLB)? b. The total address space can be more than
a. A TLB is sometimes known as an associative the size of physical memory
memory c. Sharing of procedures between different
b. Each entry of a TLB contains the information users can be facilitated
about one page, including the virtual page d. None of the other choices
number and the corresponding page frame ________________________________
C - QN=34 (7406) A ____ is a group of related ________________________________
records that contains information to be used by C - QN=39 (7442) The Linking technique that
specific application programs to generate allows the file to appear in more than one
reports. directory are:
a. Field a. Hard link
b. Record group b. Symbolic link
c. File c. Both hard link and symbolic link
d. Directory d. Soft link
________________________________ ________________________________
D - QN=35 (7413) File Structure can be: A - QN=40 (7449) Which mechanism is
a. Byte sequence implemented by writing to the log file with the
b. Record sequence purpose of file system management and
c. Tree optimization?
d. All of the other choices a. Journaling File Systems
________________________________ b. Log-Structured File Systems
A - QN=36 (7421) ____ is a specialized WRITE c. Virtual File Systems
command for existing data files that allows for d. None of the other choices
adding records to end of the file. ________________________________
a. APPEND B - QN=41 (7454) The File Manager writes the
b. UPDATE volume name and other descriptive information
c. REWRITE on an easy-to-access place on each unit: ____
d. MODIFY of the CD or DVD
________________________________ a. The outermost part
D - QN=37 (7428) Which are allocation b. The innermost part
methods of disk blocks for files? c. Immediately following the master file
a. Contiguous allocation directory
b. Linked allocation d. Stored at the beginning of the volume
c. Indexed allocation ________________________________
d. All of the other choices A - QN=42 (7464) Which is the maximum
________________________________ partition size, if the FAT type is FAT-32 and the
C - QN=38 (7437) Disk can be divided up into block size is 4 KB?
one or more partitions. The first block of every a. 1 TB
partition is called: b. 128 MB
a. Free block c. 256 MB
b. MBR d. 512 MB
c. Boot block ________________________________
d. Super block
D - QN=43 (7475) The main classes of I/O a. Precise interrupt
devices are: b. Imprecise interrupt
a. Stream devices c. Required interrupt
b. Block devices d. Disappointed interrupt
c. Character devices ________________________________
d. Block devices and Character devices C - QN=48 (7507) Which of the following
________________________________ statements is not correct about "device
D - QN=44 (7485) Which of the following independence"?
statements about the task of device controller of a. Files and devices are accessed in the same
I/O devices is correct? way, independent of their physical nature
a. Convert serial bit stream to block of bytes b. A system has to maintain only one set of
b. Perform error correction as necessary system calls for both writing on a file and writing
c. Make available to main memory on the console
d. All of the other choices c. Device independence requires all
________________________________ programmers to deal with different devices
D - QN=45 (7489) Which approach is used in directly
order to CPU communicate with the control d. Device independent interfaces should be
registers of the I/O device? given to programmers
a. Separating I/O and memory space ________________________________
b. Memory-mapped I/O D - QN=49 (7514) Which is the right order
c. Hybrid: separating I/O and memory space between the 4 I/O software layers?
and memory-mapped I/O a. User-level I/O software, Device drivers,
d. All of the other choices Interrupt handlers, Device-independent OS
________________________________ software
C - QN=46 (7495) Which of the following b. User-level I/O software, Interrupt handlers,
statements is not correct about DMA? Device drivers, Device-independent OS
a. DMA controller has access to the system bus software
independent of the CPU c. Device-independent OS software, user-level
b. DMA helps reduce the number of interrupts I/O software, Device drivers, Interrupt handlers
(in comparison with interrupt-driven I/O) d. User-level I/O software, Device-independent
c. DMA controller is usually faster than CPU OS software, Device drivers, Interrupt handlers
d. The operating system can only use DMA if ________________________________
the hardware has a DMA controller C - QN=50 (7523) Each device attached to your
________________________________ computer comes with a special program called
A - QN=47 (7502) An interrupt that leaves the a __________ that facilitates the
machine in well-defined state is called a(n) communication between the device and the OS.
______ a. device configurator
b. translator b. Circular-wait condition
c. device driver c. Hold and wait condition
d. communication utility d. No preemption condition
________________________________ ________________________________
C - QN=51 (7528) In a fixed magnetic disk, B - QN=57 (7593) The permanent blocking of a
each circle is called a ____. set of processes that compete for system
a. sector resources is called
b. block a. Starvation
c. track b. Deadlock
d. platter c. Prioritization
________________________________ d. None of the other choices
A - QN=52 (7541) What is a "stripping" in ________________________________
RAID? B - QN=59 (7619) Which deadlock condition
a. Distributing data over multiple drives does "Request all resources initially" attack?
b. Take away possessions from someone a. Mutual exclusion
c. Get undressed b. Hold and wait
d. All of the other choices c. No preemption
________________________________ d. Circular-wait condition
D - QN=53 (7549) A operation concerning ________________________________
Stable Storage is: D - QN=60 (7624) What is the correct approach
a. Stable writes with the "No preemption condition" to prevent
b. Stable Reads Deadlock?
c. Crash recovery a. Order resources numerically
d. All of the other choices b. Request all resources initially
________________________________ c. Spool everything
D - QN=54 (7576) If a system is deadlocked, no d. Take resources away
processes can ________________________________
a. run C - QN=1 (6840) Which of special register
b. release resources contains the Mode Bit (user or kernel)?
c. be awakened a. Instruction Register (IR)
d. All of the other choices b. Program Counter (PC)
________________________________ c. Program Status Word (PSW)
B - QN=55 (7581) ____ is when each process d. None of the other choices
involved in the impasse is waiting for another to ________________________________
voluntarily release the resource so that at least B - QN=2 (6847) Which of main bus in the IBM
one will be able to continue on. PC computer, that can run at 66 MHz and
a. Mutual-exclusion condition transfer 8 bytes at a time?
a. ISA (Industry Standard Architecture) b. QNX and VxWork
b. PCI (Peripheral Component Interconnect) c. Symbian OS and Palm OS
c. ISA and PCI d. e-COS
d. None of the other choices ________________________________
________________________________ A - QN=8 (6899) A(n) _________ is provided to
D - QN=3 (6855) Booting a general purpose make system calls from some programming
computer involves the following steps except languages
a. Execution of a ROM-based POST sequence a. procedure library
b. Loading one or more bootstrap loaders b. operator
c. Loading the OS c. pointer
d. Loading the command interpreter d. None of the other choices
________________________________ ________________________________
B - QN=4 (6860) Which of the following D - QN=9 (6908) The major operating system
statements about Random Access memory services provide mechanisms for secure and
(RAM) is correct? efficient are:
a. Is typically faster than cache memory a. Communication between processes
b. Is volatile b. File manipulation
c. Can only be read sequentially c. Execution of a program, I/O operations
d. Stores all the files on the computer performed by it, and detecting and reporting
________________________________ errors caused by it
C - QN=5 (6867) Which of the following d. All of the other choices
statements is incorrect about the CMOS? ________________________________
a. Is volatile C - QN=10 (6912) Which of the following is
b. To hold the current time and date correct about the advantages of layered
c. To contain BIOS system?
d. To hold the configuration parameters a. Easier to extend
________________________________ b. Easier to debug from lower to upper layer
D - QN=6 (6873) Which is not an example of a c. Easier to extend and Easier to debug from
resource that is commonly time-multiplexed? lower to upper layer
a. Network interface d. None of the other choices
b. CPU ________________________________
c. Graphics accelerator A - QN=11 (6931) OS Win32 use system
d. Main memory call_____, while OS Unix use system
________________________________ call______ to create a new process
B - QN=7 (6888) A well-known Embedded a. CreateProcess; fork
operating system is: b. fork, CreateProcess
a. TinyOS c. copy, CreateProcess
d. CreateProcess; copy A - QN=16 (6973) In order to implement mutual
________________________________ exclusion on a critical resource for competing
D - QN=12 (6944) Which of the following processes, only one program at a time should
process state transitions is illegal? be allowed:
a. Running -> Blocked (waiting) a. In the critical region of the program
b. Running -> ready b. To perform message passing
c. Blocked (waiting) -> ready c. To exhibit cooperation
d. Ready -> Blocked (waiting) d. None of the other choices
________________________________ ________________________________
C - QN=13 (6951) How many percent is CPU A - QN=17 (6984) Semaphores that are
utilization, when a computer system has initialized to 1 and used for two or more
enough room to hold two program and these processes to ensure only one can enter its
programs are idle waiting for I/O half the time? critical section at the same time are called:
a. 50% a. Binary semaphores
b. 25% b. Integer semaphores
c. 75% c. Counter semaphores
________________________________ d. None of the other choices
A - QN=14 (6959) An arrival message causes ________________________________
the system to create a new thread to handle B - QN=18 (6988) Which cannot be able to
this message. This new thread is call______ solve the race condition?
a. Pop-up a. TSL
b. Upcall b. Shared memory
c. Activator c. Semaphore
d. Distributed d. Monitor
________________________________ ________________________________
A - QN=15 (6966) Which conditions of mutual D - QN=19 (6994) Which is not a goal of a
exclusion does the Lock Variables (Software scheduling algorithm for batch systems?
proposal) violate? a. CPU utilization
a. No two processes simultaneously in critical b. Throughput
region c. Turnaround time
b. No assumptions made about speeds or d. Response time
numbers of CPUs ________________________________
c. No process running outside its critical region C - QN=20 (7002) Some systems increase the
may block another process priority of jobs that have been in the system for
d. No process must wait forever to enter its an unusually long time to expedite their exit,
critical region which is known as ____.?
________________________________ a. Lagging
b. Bumping d. Such thing cannot happen
c. Aging ________________________________
d. Accelerated priority B - QN=24 (7033) Which of these statements
________________________________ about the algorithm "Next fit" is true?
D - QN=21 (7011) Five batch jobs A through E, a. Memory Manager scans along the list of
arrive at a computer center at almost the same segments until it finds a hole that is big enough.
time. They have estimated running times of 8, b. Memory Manager starting searching the list
6, 2, 10, and 4 minutes. Their (externally of segments from the place where it left off last
determined) priorities are 3, 5, 2, 1, and 4, time.
respectively, with 5 being the highest priority. c. Memory Manager searches the entire list of
Determine the average turnaround time for segments from beginning to end and take
priority scheduling. Ignore process switching smallest hole that is adequate.
overhead. d. None of the other choices
a. 6 minutes ________________________________
b. 12.8 minutes B - QN=25 (7041) Assume the Memory
c. 18.8 minutes Manager receives a request for a block of 200.
d. 16.8 minutes When the worst-fit algorithm is used, ____ is
________________________________ the beginning address of the block granted by
C - QN=22 (7017) Assume jobs A-D arrive at the Memory Manager.
almost the same time in the READY queue. Beginning Address Memory Block Size
Determine the average turnaround time for SJF 4075 105
scheduling. Ignore process switching overhead 5225 5
6785 600
Job: A B C D 7560 20
CPU cycle: 5 2 6 4 7600 205
a. 5.5 10250 4050
b. 6.8 a. 7600
c. 9.0 b. 10250
d. 11.1 c. 6785
________________________________ d. 4075
B - QN=23 (7028) With paging, when is the ________________________________
internal fragmentation possible? B - QN=26 (7045) When a virtual memory
a. Page does not fit the frame system manages memory in fixed length units,
b. The last page of the job is less than the which of the following terms correctly
maximum page size represents its unit?
c. The virtual memory assigned to the program a. Frame
is less than the physical memory assigned to it b. Page
c. Block c. thrashing
d. Segment d. Over swapping
________________________________ ________________________________
C - QN=28 (7061) Suppose a virtual address B - QN=32 (7089) In terms of main memory
space of 2^32 words and the page size is 2^12 efficiency the method of "Backing up pages
words. If the virtual address is 12345678 in dynamically" in comparison with the method of
Hexadecimal, what would be the page number "Paging to a static swap area" is
in Hexadecimal? a. Better
a. 123 b. Worse
b. 1234 c. Equal
c. 12345 d. Nearly equal
d. 123456 ________________________________
________________________________ B - QN=33 (7408) Which of the following is
C - QN=29 (7068) A computer with a 32-bit specified to indicate the directory where the file
address uses a two-level page table. Virtual is located?
addresses are split into a 10-bit top-level page a. Extension
table field, an 12-bit second-level page table b. Path name
field, and an offset. How large are the pages? c. Root directory
a. 4-KB page d. Sub-directory
b. 2-KB page ________________________________
c. 1-KB page D - QN=34 (7417) Which of the following file
d. 512B page structure is widely used on large mainframe
________________________________ computers?
C - QN=30 (7077) The ____ policy is based on a. Byte sequence
the theory that the best page to remove is the b. Record sequence
one that has been in memory the longest c. Ring
a. NRU d. Tree
b. LRU ________________________________
c. FIFO C - QN=36 (7430) Which of the following
d. LIFO allocation methods the i-nodes use?
________________________________ a. Contiguous allocation
C - QN=31 (7081) When there is an excessive b. Linked allocation
amount of page swapping between main c. Indexed allocation
memory and secondary storage, the operation d. Linked allocation using FAT
becomes inefficient, which is called ____. ________________________________
a. excessive demand paging D - QN=37 (7438) The disk block in a partition
b. hot swapping that includes a magic number, the number of
blocks in the file system and other key b. Block devices
administrative information is called: c. Character devices
a. Free block d. None of the other choices
b. MBR ________________________________
c. Boot block C - QN=43 (7493) In general, which is the best
d. Superblock technique for I/O Data transfer?
________________________________ a. Programmed I/O
C - QN=38 (7444) Which of the following is b. Interrupt-Driven I/O
correct about symbolic links? c. Direct Memory Access
a. Symbolic links need not space to store the d. None of the other choices
path name ________________________________
b. Symbolic links can only point to files on the D - QN=44 (7498) DMA operations require the
same machines following information from the processor
c. Symbolic links can point to files in the a. Address of I/O device
network b. Starting memory location to read from and
d. None of the other choices write to
________________________________ c. Number of words to be read or written
D - QN=39 (7450) Increasing file system d. All of the other choices
performance is implemented by _____ ________________________________
a. Buffer cache A - QN=45 (7504) What is the table where its
b. Block Read Ahead entry contains the memory address of Interrupt
c. Defragmenting Disks service routine
d. All of the other choices a. Interrupt vector table
________________________________ b. Interrupt table
B - QN=40 (7456) Which of the following is true c. Address table
about the block size in disk space management d. Address lines table
a. The larger the block size is the lower the data ________________________________
rate is A - QN=46 (7510) Imagine that a certain printer
b. The larger the block size is the worse the can print 400 characters per second and that
disk space utilization is the time to write a character to the printer's
c. The larger the block size is lesser the disk output register is so short it can be ignored. If to
space is run this printer using interrupt-driven I/O and
d. None of the other choices each character printed requires an interrupt that
________________________________ takes 50 µsec all-in to service. How many
B - QN=41 (7477) Which class of I/O devices percent of the CPU does the interrupt overhead
that disks and tapes belong to? cost?
a. Stream devices a. 2% of the CPU
b. 98% of the CPU A - QN=51 (7551) How much cylinder skew is
c. 4% of the CPU needed for a 7200- RPM (rotate per minute)
d. 96% of the CPU disk with the track-to-track seek time of 1
________________________________ msec? The disk has 200 sectors of 512 bytes
B - QN=47 (7518) Which of the following I/O on each track.
software do Device drivers do? a. 24 sectors
a. Converting binary integers to ASCII for b. 12 sectors
printing c. 36 sectors
b. Writing commands to the device registers d. 18 sectors
c. Checking to see if the user is permitted to ________________________________
use the device A - QN=52 (7560) A computer uses a
d. None of the other choices programmable clock in square-wave mode. If
________________________________ 500 MHz crystal is used, what should be the
D - Which is not a component of general value of the holding register to achieve a clock
structure of device drivers? resolution of 1 msec (Clock tick)?
a. Checking the input parameters to see if they a. 500,000
are valid b. 50,000
b. Checking if the device is currently in use c. 5,000,000
c. Writing command sequence into controller's d. 50,000,000
device registers ________________________________
d. Checking to see if the user is permitted to B - QN=53 (7578) What is true about
use the device preemptable resources?
________________________________ a. Will cause the process to fail if taken away
A - QN=49 (7531) Of the three components of b. Can be taken away from a process with no ill
access time in a disk, ____ is the longest. effects
a. Seek time c. Can share among processes
b. Search time d. None of the other choices
c. Transfer time ________________________________
d. Delay time D - QN=54 (7583) ____ allows a resource to be
________________________________ held by a process as long as it is needed.
A - QN=50 (7546) Which RAID level duplicates a. Mutual-exclusion condition
all the disks? b. Circular-wait condition
a. 1 c. Hold and wait condition
b. 2 d. No preemption condition
c. 3 ________________________________
d. 4
________________________________
D - QN=55 (7590) Assume the following events a. Hierarchical ordering
and actions take place. The following b. Preemption
statement____ is true. Event Action c. Saving and restoring job state
1 P1 requests and is allocated R1. d. Requesting all resources before job run
2 P2 requests and is allocated R2. ________________________________
3 P3 requests and is allocated R3. B - Movable-head magnetic disks, such as the
4 P1 requests R2. computer hard drive, have ____ read/write
5 P2 requests R3. head(s).
6 P3 requests R1. A) zero
a. There is no deadlock B) one
b. Event 4 caused deadlock C) two
c. Event 5 caused deadlock. D) four
d. Event 6 caused deadlock. ________________________________
________________________________ B - he data-transfer rate for an optical disc is
B - QN=56 (7596) Which of the following measured in ____ per second and refers to the
statements does not apply to manual deadlock speed
management? at which massive amounts of data can be read
a. Deadlock is relatively infrequent for some from the disc.
system resources A) kilobytes
b. OS designers are normally very sensitive to B) megabytes
deadlock when designing resource managers C) gigabytes
c. Recovery may involves rebooting the system D) terabytes
d. None of the other choices ________________________________
________________________________ C - If the transport speed for a magnetic tape is
B - QN=57 (7611) What following resource 200 inches per second and the density is 1600
allocation state is unsafe? bpi, a
total of ____ bytes can be transferred in one
[file:7611.jpg] second.
A) 3,200
a. Fig. B B) 32,000
b. Fig. C C) 320,000
c. Fig. B and Fig. C D) 3,200,000
d. None of the other choices ________________________________
________________________________ A - ____ is a way to optimize search times by
A - QN=59 (7626) The scheme of ____ ordering the requests once the read/write heads
removes the possibility of a circular wait and have
therefore guarantees the removal of deadlocks. been positioned.
A) Rotational ordering A) uniprocessing
B) SSTF B) multiprocessing
C) C-SCAN C) shared processing
D) LOOK and SCAN D) divided processing
________________________________ ________________________________
A - To put data on an optical disc requires a A - ____ proposed a solution to the readers and
high -intensity laser beam, which burns writers problem that did not result in starvation
indentations, for readers or writers.
called pits, and flat areas, called ____. A) Hoare
A) lands B) Courtois
B) valleys C) Heymans
C) hills D) Parnas
D) lakes ________________________________
________________________________ B - Most current operating systems support the
B - Data recorded on fixed- head DASDs may implementation of threads, or ____, which have
or may not be blocked at the discretion of the become part of numerous application
____. packages.
A) end user A) parallel processes
B) application programmer B) lightweight processes
C) operator C) heavyweight processes
D) database administrator D) semaphores
________________________________ ________________________________
B - The need for algorithms to resolve conflicts C - Each active thread in a process shares the
between processors is called process ____. ____ and the resources allocated to its process.
A) communication A) processor registers
B) synchronization B) program counter
C) reduction C) data area
D) transformation D) status
________________________________ ________________________________
B - In a symmetric configuration, processor D - Automatic detection by the compiler of
scheduling is ____. instructions that can be performed in parallel is
A) centralized called
B) decentralized ____.
C) multifaceted A) automatic parallelism
D) balanced B) array parallelism
________________________________ C) explicit parallelism
B - Parallel processing is also called ____. D) implicit parallelism
________________________________ C - ____ is when, in modern printing systems, a
D - Operations on semaphore s enforce the disk accepts output from several users and acts
concept of ____, which is necessary to avoid as a
having temporary storage area for all output until the
two operations attempt to execute at the same printer is ready to accept it.
time. A) Phishing
A) mutual execution B) Lagging
B) mutex execution C) Spooling
C) signal exclusion D) Spoofing
D) mutual exclusion ________________________________
________________________________ C - ____ occurs when two processes do not
C - A ____ of processing must be handled as a release control of resources they are using.
unit. A) No preemption
A) line B) Circular wait
B) segment C) Resource holding
C) critical region D) Mutual exclusion
D) semaphore ________________________________
________________________________ C - For ____ systems, deadlocks quickly
B - In the "dining philosophers" problem, a become critical situations.
philosopher can pick up a fork when____. A) batch
A) there is one available B) interactive
B) there are two available C) real-time
C) no other philosopher is eating D) general purpose
D) it is his turn, going in numerical order from ________________________________
one philosopher to the next B - Failure to lock database records before
________________________________ updating them may result in a ____ between
A - is necessary in any computer system processes.
because some resources such as memory, A) struggle
CPU, and B) race
dedicated devices must be exclusively allocated C) timeout
to one user at a time. D) livelock
A) Mutual exclusion ________________________________
B) Resource holding C - ____ developed the Banker's Algorithm.
C) No preemption A) Havender
D) Circular wait B) Holt
________________________________ C) Dijkstra
D) Lane & Mooney
________________________________ D) 5
B - A network that's congested or has filled a ________________________________
large percentage of its I/O buffer space can B - ____ gives users the appearance that their
become programs are being completely loaded in main
deadlocked if it doesn't have ____ to control the memory during their entire processing time.
flow of messages through the network. A) Segmenting
A) procedures B) Virtual memory
B) protocols C) Shared memory
C) policies D) Multithreading
D) rules ________________________________
________________________________ A - Studies have shown that having any ____,
A - ____ is necessary in any computer system even a small one, can substantially improve the
because some resources such as memory, performance of the computer system.
CPU, and A) cache
dedicated devices must be exclusively allocated B) memory block
to one user at a time. C) page block
A) Mutual exclusion D) block
B) Resource holding ________________________________
C) No preemption B - To access a location in memory when using
D) Circular wait segmented memory management, the address
________________________________ is
C - Interactive systems generally improve the composed of two entries: ____.
use of resources through ____ resource A) the segment number and the line number
sharing, but B) the segment number and the displacement
this resource sharing capability also increases C) the line number and the displacement
the possibility of deadlocks. D) the segment number, the line number, and
A) interspersed the displacement
B) group ________________________________
C) dynamic C - If a particular demand paging configuration
D) static has 9 page interrupts out of 11 page requests,
________________________________ failure rate is ____.
B - When using the clock page replacement A) 18%
policy, a page with a reference bit of ____ is B) 52%
replaced. C) 82%
A) -1 D) 95%
B) 0 ________________________________
C) 1
B - There are ____ entries per page in the A) Case 1
PMT. B) Case 2
A) 0 C) Case 3
B) 1 D) Case 4
C) 2 ________________________________
D) 5 D - One of the most important innovations of
________________________________ demand paging was that it made ____ feasible.
C - The cache hit ratio is ____, if the total A) memory demand
number of requests is 10 and 6 of those are B) virtual demand
found in C) virtual paging
cache memory. D) virtual memory
A) 6% ________________________________
B) 10% A - In a single -user system, jobs are processed
C) 60% ____.
D) 100% A) sequentially
________________________________ B) intermittently
D - Assume that the Page Map Table below is C) randomly
in effect. The number of lines per page is 400. D) in order of longest job to shortest job
The ________________________________
actual memory location for line 433 is ____. A - 3 Put job in waiting queue
Job Page Number Page Frame Number 4 Go fetch next job
08 A) first-fit memory allocation
1 10 B) best-fit memory allocation
25 C) least-fit memory allocation
3 11 D) fixed partition memory allocation
A) 1 ________________________________
B) 33 A - The operating system can tell the ____ of
C) 4000 each group of digits by its location in the line
D) 4033 and the
________________________________ operation code.
D - Consider the following four cases. The LRU A) function
policy,____, will be least likely to swap. B) value
Modified Referenced Meaning C) order
Case 1 0 0 Not modified AND not referenced D) assignment
Case 2 0 1 Not modified BUT was referenced ________________________________
Case 3 1 0 Was modified BUT not referenced C - The ____ of memory, sometimes referred to
Case 4 1 1 Was modified AND was refe renced as garbage collection or defragmentation, is
performed by the operating system to reclaim ________________________________
fragmented sections of the memory space. B - The primary distinguishing characteristic of
A) deallocation modern computers is ____.
B) redirection A) memory capacity
C) compaction B) processor capacity
D) reallocation C) disk space
________________________________ D) physical size
D - By compacting and relocating, the Memory ________________________________
Manager optimizes the use of memory and thus A - A system with ____ divides programs into
improves throughput, but an unfortunate side parts and keep them in secondary storage,
effect is more ____. bringing
A) null entries each part into memory only as it is needed.
B) segmentation A) virtual memory
C) errors B) shared memory
D) overhead C) segmented processing
________________________________ D) passive multiprogramming
A - The fixed partition scheme works well ____. ________________________________
A) when jobs have the same size A - A hybrid system is a combination of the
B) when jobs have different sizes ____ systems.
C) when job sizes are not known in advance A) batch and interactive
D) when all jobs are under 100K B) batch and real -time
________________________________ C) interactive and real -time
C - A supercomputer can perform ____ floating- D) real-time and general-purpose
point operations per second. ________________________________
A) 240 million D - Powerful microcomputers developed for use
B) 2.4 billion by commercial, educational and government
C) 2.4 trillion enterprises are called ____.
________________________________ A) supercomputers
A - In second-generation computers, to reduce B) minicomputers
the discrepancy in speed between the I/O and C) terminals
the D) workstations
CPU, an interface called the ____ was placed ________________________________
between them to act as a buffer. C - Vacuum tube computers were used during
A) control unit the period of ____.
B) scheduler A) 1920s-1930s
C) holder B) 1935-1945
D) buffer manager C) 1940-1955
D) 1945-1960 [C] Instruction set
________________________________ [D] None ofthe other choices
A - ____ introduced the need for control cards, ________________________________
which defined the exact nature of each program A - Linux and are often used as operating
and its requirements. systems on supercomputers, mainframes, and
A) Job scheduling servers.
B) Control scheduling [A] UNIX
C) Job control [B] Windows
D) Structure control [C] None ofthe other choices
________________________________ [D] Mac OS
B - A typical ____ computer houses devices to ________________________________
perform audio, video, and graphic creation and D - Where is the position of the operating
editing. system in computer system:
A) multiprocessor [A] Between the user interface program and the
B) multimedia application Program
C) networked [B] None of the other choices
D) PDA [C] In user space
________________________________ [D] Above the hardware and under the user
D - The name for the nucleus of an operating interface program
system is the ____. ________________________________
A) manager B - Consider a computer system that has cache
B) center memory, main memory (RAM) and disk, and
C) core OS uses
D) kerneld virtual memory. It takes 2 nsec to access a byte
________________________________ from the cache. 20 nsec to access a byte from
C - What is an operating system structure in RAM. and 10 msec to
which the communication between requesting access a block of 1000 bytes from the disk. If a
process b ook has 1000 pages, each with 50 lines of 80
and responding process is message passing? characters each. How long it will take to
[A] Monolithic Systems electronically scan the textfor the case of the
[B] All of the other choices master
[C] MS-DOS copy being in each of the level as
[D] Client-Server Model one proceeds down the memory hierarchy
________________________________ (from inboard memory to offline storage )?
C - The language of the CPU is known as its [A] 1 msec. 10 msec. 10 sec
[A] Register set [B] 4 msec. 40 msec. 20 sec
[B] Control unit set [C] 2 msec. 20 msec. 10 sec
TO] [C] None of the other choices
1 msec. 10 msec. 5 sec [D] 1 %
________________________________ ________________________________
D - The basic idea behind the microkernel C - To specify an address in this segmented
design is: memory, the form is used
[A] All ofthe other choices [A] <physical address, offset>
[B] All other modules run as relatively [B] <process, offset>
powerless o rdinary user processes [C] segment-number, offset>
[C] Only one module runs in kernel mode [D] <virtual address, offset>
[D] To archive high reliability by splitting ________________________________
operating system up into small, well - defined D - QN=3
modules (2537)
________________________________ Page replacement algorithms determine
B - Which of the following conditions that a. when the system should update page table
causes the processes to be terminated, when entries
processes b. how many pages should be added to main
have memory
done their work? c. which pages should be brought into memory
[A] Fatal error (involuntary) because a process is likely to reference them
[B] Normal exit (voluntary) soon
[C] Killed by another process (i nvoluntary) d. which page to remove to provide space for
[D] Error exit (voluntary) an incoming page
________________________________ ________________________________
A - Which of the following is not a CPU A - QN=4
scheduling criterion? (2530)
[A] Burst time The page table for each process maintains:
[B] CPU utilization a. The frame location for each page of the
[C] Throughput process
[D] Response time b. The page location for each frame of the
________________________________ process
D - How many percent of the CPU time is c. The physical memory location of the process
wasted, when a computer system has enough d. None of the above
room to ________________________________
hold two program and these programs are idle A - QN=6
waiting for I/O 10% of the time? (2528)
[A] 90% The second-chance page -replacement
[B] 99% algorithm
a. Moves pages found at the head of a FIFO (2536)
queue with the referenced bit turned on back to In a system employing a paging scheme for
the tail of the queue to avoid replacing them memory management, wasted space is due to:
b. Searches through a circular list of pages and a. External fragmentation
replaces the first page it encounters that has b. Internal fragmentation
the referenced bit turned off c. Pages and frames of different specified sizes
c. Relies on a modified bit to determine which d. None of the above
page to replace ________________________________
d. None of the above C - QN=13
________________________________ (2527)
B - QN=9 The task of subdividing memory between the
(2535) OS and processes is performed automatically
In terms of speed the best method of Dynamic by the
Storage -Allocation is: OS and is called
a. Next fit a. Protection
b. First fit b. Relocation
c. Best fit c. Memory Management
d. Worst fit d. All of the above
________________________________ ________________________________
C - QN=10 A - QN=14
(2538) (2532)
The actual location in main memory is called Which of the following is appropriate to
a(n): determine program size and create page table?
a. Relative address a. Process creation
b. Logical address b. Process execution
c. Absolute address c. Page fault time
d. None of the above d. Process termination time
________________________________ ________________________________
B - QN=11 C - 525)
(2539) What is the method to keep track of memory
LRU replaces the page that has spent the usages?
a. longest time in memory a. Memory Management with Bit Maps
b. longest time in memory without being b. Memory Management with Linked Lists
referenced c. a and b
c. shortest time in memory d. None of the above
________________________________ ________________________________
B - QN=12 D - QN=1
(2548) a. Symbolic links need space to store the name
The special files a and the file pointed to
a. character special b. Hard links do not require extra disk space
b. block special file c. Symbolic links can point to files in the
c. Neither a nor b network
d. Both a and b d. Hard links can point to files on other
________________________________ machines
C - QN=3 ________________________________
(2540) D - QN=2
A file is generally defined to be: (2578)
a. A basic element of data Which of the following I/O software device
b. A collection of related fields layers is done by user-level software?
c. A collection of similar records a. Computing the track, sector, and head for a
d. All of the above disk read
________________________________ b. Writing commands to the device registers
D - QN=4 Which of the following is not a path c. Checking to see if the user is permitted to
name for the file /etc/passwd use the dev ice
(2546) d. Converting binary integers to ASCII for
a. /etc/passwd printing
b. /etc/../etc/passwd ________________________________
c. /etc/../etc/../etc/passwd D - QN=3
d. None of the above (2581)
________________________________ An example of the key differences that can exist
C - QN=7 across (and even in) classes of I/O devices is:
(2544) a. Data rate
What is incorrect about contiguous allocation of b. Data representation
files ? c. Error conditions
a. It is simple to implement d. All of the above
b. It leads to excellent read performance ________________________________
c. It does not cause disk fragmentation B - QN=6
d. It is widely used on CD-ROMs (2580)
________________________________ Which of the following is not correct about the
D - QN=10 reliability of different RAID levels?
(2545) a. There is no reliability support in RAID level 0
Which of the following is not correct about hard b. All RAID levels can survive one disk crash
links and symbolic links? c. In RAID level 2, a single bit error in a word
can be detected AND corrected
d. In RAID levels 3, 4, 5 a single bit error in a c. A hard drive is an example of a character-
word can be detected oriented I/O device
________________________________ d. None of the above
C - QN=7 ________________________________
(2577) A - QN=10
Which of the following statements is not correct (2582)
about "device independence"? The I/O technique where the processor busy
a. Files and devices are accessed in the same waits for an I/O operation to complete is called:
way, ind ependent of their physical nature a. Programmed I/O
b. A system has to maintain only one set of b. Interrupt-driven I/O
system calls for both writing on a file and writing c. Direct Memory Access (DMA)
on the console d. None of the above
c. Device independence requires all ________________________________
programmers to deal with different devices A - QN=1
directly (2590)
d. Device independent interfaces should be The system is said to be in an unsafe state if
given to programmers a. The operating system cannot guarantee that
________________________________ all current processes can complete their work
B - QN=8 b. The system is deadlocked
(2579) c. A process is indefinitely postponed
What kind of I/O devices that disks and tapes d. None of the above
belong to? ________________________________
a. Stream-oriented devices A - QN=2
b. Block-oriented devices (2584)
c. Character-oriented devices If in a resource -allocation graph, each resource
d. None of the above type has exactly one instance, which of the
________________________________ following indicate a deadlock situation?
C - QN=9 a. The graph has at least one cycle.
(2575) b. The graph has no cycle.
Which of the following statements is incorrect? c. The graph is connected.
a. The term data rate refers to the speed with d. The graph is not connected.
which data moves to and from the individual I/O ________________________________
device B - QN=3
b. In the interrupt-driven I/O technique, the (2583)
processor issues an I/O request, continues with All deadlocks involve conflicting needs for
other work and eventually receives notification resources by
that the request was fulfilled a. One or more processes
b. Two or more processes a. mutual-exclusion condition
c. Three or more processes b. circular-wait condition
d. None of the above c. hold and wait condition
________________________________ d. preemption condition
B - QN=4 ________________________________
(2588) D - QN=9
What is the characteristic of deadlocked (2591)
systems Dijkstra's Banker's Algorithm require the system
a. Starvation to maintain the resource information for each
b. Circular wait process, including:
c. Saturation a. A count of the system's total resources
________________________________ b. The maximum resources that can be
B - QN=5 requested by the process
(2586) c. The number of resources currently acquired
A possibility of deadlock can occur: by the process
a. If a system is in safe state d. B and C
b. If a system is in unsafe state ________________________________
c. If a system is in instable state D - N=10
d. None of the above (2585)
________________________________ If a deadlocked system, the processes can
C - QN=6 a. run
(2592) b. release resources
What is the weakness of the Banker's c. be awakened
algorithm? d. do nothing
a. Allowing the population of processes to vary ________________________________
over time D - N=1
b. Enabling processes to hold their resources (2299)
indefinitely Which of the following statements is incorrect
c. Requiring that processes state their about user mode and kernel mode?
maximum needs in advance a. In kernel mode, the OS can execute every
d. Enabling the number of resources to instruction in the instruction set
fluctuate b. In user mode, user program can execute only
________________________________ a subset of instructions
D - QN=8 c. Having two modes of operation helps prevent
(2589) user programs from accessing critical
Which of the following is not a condition instructions
necessary for deadlock to exist? d. None of the above
________________________________ C - In a highly interactive environment there is a
A - First-come, first- served (FCFS) is a very third layer of the Processor Manager called the
simple algorithm to implement because it ____. ____ scheduler.
A) uses a FIFO queue A) Managing
B) uses a LIFO queue B) Subprocess
C) uses a circular queue C) middle- level
D) uses a directed graph D) Program
________________________________ ________________________________
C - The Job Scheduler seeks to ____, when D - 3/ Which of the following is OS component?
scheduling jobs. A/ Space Management
A) run all CPU intensive jobs first B/ Speed Management
B) run all I/O intensive jobs first C/ Time Management
C) balance CPU and I/O intensive jobs D/ Process Management
D) run the quickest jobs first ________________________________
________________________________ B - 4/ MS- DOS is an example of ...
D - Assume jobs A-D arrive in quick succession A/ Layered System
in the READY queue. Using round robin B/ Monolithic system
scheduling, C/ Virtual machine
the turnaround time for job C is ____. D/ Client- server model
Arrival time: 0 1 2 3 ________________________________
Job: A B C D B - 5/ What is interrupt vector?
CPU cycle: 8 4 9 5 A/ A signal an I/O devices sends to CPU
A) 7 B/ Part of memory which contains the
B) 20 addresses of interrupt handlers
C) 22 C/ None of the above
D) 24 ________________________________
________________________________ B - 7/ Which of the following is NOT a correct
D - The Process Scheduler assigns the CPU to explanation of UNIX which is one of the OS?
execute the processes of those jobs placed on A/ Provides network functions that easily
the implement distributed processing.
____ queue by the Job Scheduler. B/ It is a single- user and multi-task OS
A) WAITING C/ Since its specifications have been released
B) NEXT to the public and it has a high portability,
C) PROCESS it has been adopted in a wide range of devices.
D) READY D/ Provides an interactive human interface that
________________________________ uses character- based commands.
________________________________
C - 9/ what is the value of mode bit in User C/ Contention
Mode? D/ Hash
A/ 00 ________________________________
B/ 11 C - 4/ Which of the following preemptive
C/1 scheduling algorithm?
D/ 0 A/ FCFS
________________________________ B/ Shortest Job First
B - 10/ What is the correct statement about the C/ Round Robin
process of booting a computer? D/ None of the above
A/ BIOS loads the operating system ________________________________
immediately into RAM C - 6/ Which of the following state transitions
B/ BIOS detects the boot device, the boot are illegal?
sector determines the active partition, then the A/ ready -> running
boot loader loads the operating system B/ running -> ready
C/ None of the above C/ waiting -> runing
________________________________ D/ running -> terminated
D - 11/ What is the correct about trap ________________________________
instructions and interrupts ? D - 8/ Which of the following cannot be shared
A/ A trap instruction switch the execution mode among different threads of a process?
of a CPU from the user mode to kernel A/ File handless
mode? B/ Process data
B/ A trap instruction is caused by a user C/ Process code
program to invoke functions in the OS kernel D/ Stack
C/ An interrupt is caused by an external event ________________________________
D/ All of the above A - 1/ The maximum segment for Process
________________________________ Pentium if the Limit field of Segment Descriptor
B - 1/ Which of the following is a high-level has Unit of Byte?
synchronization primitive? A/ 1MB
A/ Semaphores B/ 1 GB
B/ Monitors C/ 4GB
C/ TSL D/ None of the above
D/ None of the above ________________________________
________________________________ D - 4/ A page fault means that we referenced a
C - 2/ Which of the following is used in mutual page?
exclusion ( exclusive control)? A/ With an incorrect I/O request
A/ Checkpoint B/ outside the memory boudaries
B/ Semaphore C/ that was not in secondary storage
D/ that was not in main memory ________________________________
________________________________ D - QN=4
D - How many levels of Page Tables the (2292)
Processor Pentium supports: What is the main characteristic of embedded
A/ 3 operating system?
B/ 1 a. Multiple CPU
C/ 4 b. Time-sharing
D/ 2 c. Many I/O devices
________________________________ d. Restriction of memory size, speed of CPU,
B - 6/ What is not the technique of screen size, powers
implemention for Virtual Memory? ________________________________
A/ Demand segmentation D - QN=5
B/ Demand partition (2300)
C/ Demand paging Which is the difference between personal
D/ All of the above computers and mainframe computers?
________________________________ a. Personal computers are always interactive
B - 7/ Which of the following information bits in b. Mainframe computers are mostly batch
the entry of page table is used to indicate Page systems with many users
Fault? c. Protection is much more important on
A/ Status bit mainframe computers
B/ Present/ Absent bit d. All of the above
C/ Referenced bit ________________________________
D/ Modified bit B - QN=8
________________________________ (2293)
C - 8/ How many levels of Protection the A Control/Status register that contains the
Processor Pentium supports; address of the next instruction to be fetched is
A. 8 called
B. 6 the:
C. 4 a. Instruction Register (IR)
D. 2 b. Program Counter (PC)
________________________________ c. Program Status Word (PSW)
C - 10/ The ways to keep track of memory d. All of the above
usages: ________________________________
A/ Memory Management with Bit Maps B - QN=9
B/ Memory Management with Linked Lists (2291)
C/ A vs B The general role of an operating system is to:
D/ None of the above
a. Act as an interface between various B - QN=3
computers (2305)
b. Provide a set of services to system users Which of the following process state transitions
c. Manage files for application programs are legal?
d. None of the above a. waiting -> running
________________________________ b. running -> ready
A - QN=10 c. waiting -> terminated
(2290) d. ready -> terminated
The two basic types of processor registers are: ________________________________
a. General and special registers C - QN=4
b. Control and Status registers (2316)
c. User-visible and user-invisible registers Which of the following is not correct about user-
d. None of the above level threads ?
________________________________ a. User-level threads are more efficient than
D - QN=14 kernel threads, in the sense that they do not
(2298) need
Which of the following statements is incorrect kernel calls to switch among threads
about timesharing and multiprogramming b. User-level threads cannot be preempted by
systems? clock interrupts unless the whole process'
a. In a timesharing system, multiple users can quantum
access the system simultaneously has been used up
b. In a multiprogramming system, one user can c. With user-level threads, customized
run several processes simultaneously scheduling algorithms cannot be implemented
c. All timesharing systems are d. If one user-level thread makes a blocking
multiprogramming systems system call, the system will block the entire
d. All multiprogramming systems are process
timesharing systems (which contains that user-level thread)
________________________________ ________________________________
B - QN=1 D - QN=5
(2309) (2313)
Which of the following statements is correct What is Software proposal in the solution of
about Shortest Job First Mutual exclusion with Busy waiting
a. Avoid Starvation a. Lock Variables
b. Minimize average waiting time b. Strict Alternation
c. Both a and b c. Peterson's Solution
d. None of the above d. All of the above
________________________________ ________________________________
A - QN=10 d. None of the above
(2311) ________________________________
Which is the correct description of transitions D - QN=15
between process states below? (see picture) (2317)
a. 1: Process blocks for input; 2: Scheduler Which of the following synchronization
picks another process; 3: Scheduler picks this mechanisms does not rely on busy -waiting ?
process; 4: Input becomes available a. Lock variables
b. 1: Process blocks for input; 2: Scheduler b. Strict alternation
picks this process; 3: Scheduler picks another c. Peterson's algorithm
process; 4: d. Semaphores
Input becomes available ________________________________
c. 1: Process blocks for input; 2: Input becomes C - is a specialized WRITE command for
available; 3: Scheduler picks another process; existing data files that allows for appending
4: records or for
Scheduler picks this process rewriting selected records in their original place
d. 1: Process blocks for input; 2: Input becomes in the file.
available; 3: Scheduler picks this process; 4: [A] UPDATE
Scheduler picks another process [B] REWRITE
________________________________ [C] MODIFY
C - QN=12 In a single processor system, [D] APPEND
mutual exclusion can be guaranteed by: ________________________________
(2314) C - Many computer users and some operating
a. Overlapping processes systems call subdirectories
b. Interleaving processes [A] Volumes
c. Disabling interrupts [B] Databases
d. All of the above [C] Folders
________________________________ [D] Files
D - QN=14 ________________________________
(2319) D - Which method is used to implement files to
Which is a wrong statement about the quantum keep each file as a linked list of disk blocks?
used in Round Robin algorithm ? [A] Contiguous Allocation
a. If the quantum is very large, RR is essentially [B] i -node
FCFS [C] File Allocation Table
b. If the quantum is very small, the CPU [D] Linked List Allocation
efficiency is reduced ________________________________
c. A reasonable value of quantum is around 20- A - Which of the following allocation methods,
50 ms Operating system MS-DOS is implemented?
[A] Linked allocation using FAT ________________________________
[B] Indexed allocation A - The aspect of disk performance that
[C] Contiguous allocation represents the time it takes to position the head
[D] Linked allocation a the
________________________________ desired track is known as
A - Which of a system call is to allow the [A] Rotational delay
system announce that the file is coming and set [B] Access time
some of [C] Seek time
the attributes? [D] None of the other choices
[A] CREATE ________________________________
[B] RENAME B - A operation concerning Stable Storage is:
[C] OPEN [A] Stable Reads
[D] CLOSE [B] All of the other choices
________________________________ [C] Crash recovery
B - Which of a system call is to allow the file to [D] Stable writes
appear in more than one directory? ________________________________
[A] CREATE D - Rearrange the layers in I/O software starting
[B] INK at the bottom
[C] OPEN 1. User-level I/O software
[D] SEEK 2. Device drivers
________________________________ 3. Interrupt handlers
C - Which of a system call is to allow the 4. Hardware
system free up internal table space? 5. Device-independent OS software
[A] SEEK [A] 12345
[B] OPEN [B] 54321
[C] Close [C] 15234
[D] DELETE [D] 43251
________________________________ ________________________________
A - How much cylinder skew is needed for a C - When an external device becomes ready to
5400- RPM (rotate per minute) disk with the be serviced by the processor, the device sends
track-to-track this
seek time of 1 msec? The disk has 200 sectors signal to the processor. This signal is called:
of 512 bytes on each track. [A] None of the other choices
[A] 18 sectors [B] Halt signal
[B] 12 sectors [C] Interrupt signal
[C] 24 sectors [D] Handler signal
[D] 36 sectors ________________________________
D - Assuming that it takes 10 nsec to copy a [D] DMA is software solution to speed up data
byte, how much time does it take to completely transfer between I/O device and memory
rewrite ________________________________
the C - In a directed graph used to model deadlock,
screen of a 1200 x 800 pixel graphics with 24- resources are re presented using
bit color? [A] Rectangle
[A] 288 msec [B] Circular
[B] 288 micro-sec [C] Squares.
[C] 28.8 micro-sec [D] Ellipse
[D] 28.8 msec ________________________________
________________________________ B - Which deadlock condition does "Ordering
D - What is asynchronous transfer in principles resources numerically" attack?
of I/O software? [A] No preemption
[A] The user process makes system call and [B] Circular-wait condition
goes to sleep until other process it wakes up
[B] None of the other choices [C] Hold and wait
[C] The user program starts system cal l to [D] Mutual exclusion
transfer and automatically suspended until the ________________________________
data are available in the buffer B - Which deadlock condition does "Take
[D] The CPU starts the transfer and goes off to resources away" attack?
do something else until the interrupt arrives [A] Circular-wait condition
________________________________ B
C - Assuming that it takes 10 nsec to copy a No preemption
byte, how much time, does it take to completely C
rewrite the screen of a 200 character Hold and wait
x 20 line text mode memory- mapped screen? [D] Mutual exclusion
[A] 10 micro-sec ________________________________
[B] 30 micro-sec A - Which method is used to prevent the
[C] 0 micro-sec communication deadlock?
[D] 20 micro-sec [A] All of the other choices
________________________________ [B] Timeouts
D - Which of the following statements is [C] Handling alarm
incorrect about I/O using DMA? [D] Acknowledge signa
[A] None of the other choices ________________________________
[B] DMA helps free up the CPU during the I/O D - _________is the act of allowing only one
to do other work process to have access to a dedicated resource
[C] DMA helps reduce the number of interrupts [A] Hold and wait condition
[B] No preemption condition [B] CLOSE
[C] Circular-wait condition [C] SEEK
[D] DELETE
[D] Mutual-exclusion condition ________________________________
________________________________ C - Consider a swapping system in which the
D - What is the correct approach of the driver of memory consists of the following hole sizes:
dedicated devices with requesting device that is 10K, 4K,
busy to solve deadlock using Ostrich algorithm? 20K, 15K, 9K.
[A] The device driver stops the current jobs and Assume best fit algorithm is used. Which holes
releases the devices are taken for successive segment requests of
[B] The device driver kills those requesting 8K,
processes 12K, 10K?
[C] All of the other choices [A] 10K, 15K, 20K
[D] The device driver decides blocking and [B] 10K, 20K, 15K
returning an error code [C] 9K, 15K, 10K
________________________________ [D] 20K, 15K, 10K
C - What is true about non-preemptable ________________________________
resources? (non preemptable) B - Assume the Memory Manager receives a
[A] Can be taken away from a process with no request for a block of 200. When the best-fit
ill effects algorithm
[B] None of the other choices is used, is the beginning address of the hole
[C] Will cause the process to fail if taken away granted by the Memory Manager.
[D] Can share among processes Beginning Address of Hole Hole Size
________________________________ 4075 105
A - Which of the following is not a step in the 5225 5
boot process? 6785 600
[A] The antivirus program checks all files for 7560 20
viruses. 7600 205
[B] Configuration and customization settings are 10250 4050
checked [A] 6785
[C] The operating system is loaded into RAM. [B] 7600
[D] The BIOS is activated by powering on the [C] 10250
CPU. ________________________________
________________________________ B - A ____ is a portion of a process that can run
D - Which of a system call is to allow the independently.
system free up disk space? [A] ubprocess
[A] OPEN [B] thread
[C] program 2 P2 requests and is allocated R2
[D] Mini-process 3 P3 requests and is allocated R3
________________________________ 4 P1 requests R2.
C - The term__________a specialized 5 P2 requests R3.
instruction set. 6 P3 requests R1.
[A] None of the other choices [A] There is no deadlock
[B] I/O device [B] Event 5 caused deadlock.
[C] DMA characterizes a system configuration [C] Event 4 caused deadlock
that includes an I/O module that is a separate [D] Event 6 caused deadlock.
processor with ________________________________
[D] Programmed I/O D - Operating system abstraction supports the
________________________________ ability to have operation even when there is
B - Consider a swapping system in which the only one
memory consists of the following hole sizes: 10 CPU available
K, 4 K, [A] None of the other choices
20 K, 15 K, 9 K. Assume first fit algorithm is [B] parallel
used. Which holes are taken for successive [C] multiple
segment requests [D] pseudoparallelism
of 8 K, 12 K, 10 K? ________________________________
[A] 9 K, 15 K, 10 K C - The page size that is too small wil l
[B] 10 K, 20 K, 15 K generate
[C] 20 K, 15 K, 4 K [A] More difficult to calculate actual position
[D] None of the other choices [B] Excessive internal fragmentation
________________________________ [C] Very long Page tables
A - Which is the fastest bus in the IBM PC [D] Excessive external fragmentation
computer? ________________________________
[A] ISA (Industry Standard Architecture) B - In a directed graph used to model deadlock,
[B] USB (Universal Serial BUS) processes are represented using
[C] IDE (Integrated Drive Electronic) [A] Rectangle
[D] PCI (Peripheral Component Interconnect) [B] Circular
________________________________ [C] Squares
A - Assume the following events and actions [D] Ellipse
take place. The following statement is true. ________________________________
Event B - How many categories can be the I/O
Action devices roughly divided?
1 P1 requests and is allocated R1. P1 requests [A] 3
and is allocated R1 [B] 2
(block devices and character devices) ________________________________
[C] 4 C - QN=5 (6907) Which of the following is not a
[D] 1 task of I/O management of OS?
________________________________ a. Manage main memory for the devices using
D - What is not the technique of implementation caching, buffering, and spooling
for Virtual Memory? b. Maintain and provide a general device-driver
[A] All of the other choices interfaces
[B] Paging c. Mapping files onto secondary storage
[C] Segmentation d. Drivers for specific hardware devices
[D] Partition ________________________________
________________________________ C - QN=7 (6916) ____ is the partitioning of a
B - A CPU may have separate fetch, decode single server, each of which can support a
and execute units, so that can carry out three different operating system.
steps of a. Multiprocessing
the three instructions in the same time is called: b. Multithreading
[A] Multicore c. Virtualization
[B] Pipeline d. Shared processing
[C] None of the other choices ________________________________
[D] Superscalar C - QN=1 (6837) A CPU may have two or more
________________________________ complete processors, so that can carry out
C - Which of a system call is to allow the multiple threads in the same time is called:
system fetch the attributes and list of disk a. Pipeline
addresses into b. Superscalar
main memory for rapid access on later call? c. Multicore
[A] SEEK d. None of the other choices
[B] OPEN ________________________________
[C] RENAME A - QN=8 (6896) The interface between the
[D] CLOSE operating system kernel and the user programs
________________________________ is defined by the set of ________ that the
D - Which of the following statements is not operating system provides
correct about the device controller of I/O a. System calls
devices? b. Functions
[A] Is also called adapter c. Threads
[B] Can handle two, four, or even eight identical d. Processes
devices ________________________________
[C] Is electronic component of device A - QN=17 (6980) What happens when a thread
[D] Is software component of device calls Down (S) when it wants to enter its critical
section, where S is a binary semaphore set to b. translator
1? c. device driver
a. The thread is allowed to enter its critical d. communication utility
section and S is decremented. ________________________________
b. The thread is blocked and added to a queue A - QN=19 (7547) Which concept is described
of waiting threads. as "disk sectors are just numbered
c. The semaphore is set to 2. consecutively starting at 0, without regard to the
d. None of the other choices disk geometry"?
________________________________ a. Logical block addressing
B - QN=8 (7455) The File Manager writes the b. Physical block addressing
volume name and other descriptive information c. Virtual block addressing
on an easy-to-access place on each unit: ____ d. None of the other choices
of the magnetic disk ________________________________
a. The outermost part C - What is the characteristic of the first
b. The innermost part generation of operating system?
c. Immediately following the master file [A] ersonal computers, single user, multitasking
directory [B] ransistors, batch systems
d. Stored at the beginning of the volume [C] acuum tubes, plug boards
________________________________ [D] Cs and multiprogramming
D - QN=11 (7490) Which of the following ________________________________
statement is not true about separating I/O and D - Which is not an example of a resource that
memory space? is commonly time-multiplexed?
a. Device drivers must be written using a. Network interface
assembly language b. CPU
b. Programs must use 2 instructions to test c. Graphics accelerator
whether the device is ready d. Main memory
c. There is special protection mechanism to ________________________________
keep user processes from performing I/O A - Which of the following is an Operating
d. Caching a device control register would be System component?
disastrous [A] rocess Management
________________________________ [B] peed Management
C - QN=50 (7523) Each device attached to your [C] pace Management
computer comes with a specia l program called [D] ime Management
a ________________________________
__________ that facilitates the communication A - Which of the following process state
between the device and the OS. transitions is correct, when the scheduler picks
a. device configurator a process from
the ready queue to run? [A] ADD of two numbers
[A] Ready -> running [B] Read the time-of-day clock
[B] Running -> Blocked (waiting) [C] Disable all interrupts
[C] Blocked (waiting) -> ready [D] AND of two numbers
[D] Running -> ready ________________________________
________________________________ C - The _________is the essential component
A - Which of the following process state ofthe operating system that remains in RAM
transitions is illegal? when your computer is powered on.
[A] Ready -> Blocked (waiting) [A] system file
[B] Running -> Blocked (waiting) [C] kernel
[C] Blocked (waiting) -> ready [D] registry
[D] Running -> ready ________________________________
________________________________ A - Which is not a goal of a sheduling algorithm
B - Critical Region (Section) concept used in for all systems?
interprocess communication is: [A] Balance
[A] A part of shared memory [B] Response time
[B] A part of the program where the shared [C] Policy enforcement
memory is accessed [D] Fairness
[C] None of the other choices ________________________________
[D] A part of shared data D - A entry of the Process table is called:
________________________________ [A] All of the other choices
D - Which ofthe following operating systems is [B] Process check block
an example of monolithic system? [C] Process management block
[A] Windows XP [D] process control block.
[B] Mac OS ________________________________
[C] UNIX B - One of the most important innovations of
[D] MS-DOS demand paging was that it made feasible
________________________________ [A] Virtual paging
B - A well-known Real-Time operating system [B] Virtual memory.
is: [C] Memory demand
[A] MS-DOS [D] Virtual demand
[B] e-COS ________________________________
[C] TinyOS A - When a virtual memory system manages
[D] Personal Operating System memory in fixed length units, which of the
________________________________ following terms
C - Which of the following instructions should correctly represents its unit?
be allowed only in kernel mode? [A] Page
[B] Frame [D] 93% of the CPU
[C] Block ________________________________
[D] Segment D - In a directed graph used to model deadlock,
________________________________ ______represents deadlock.
D - Which is the maximum number of partition [A] Dashed arrow
that most disks can be divided up? [B] Solid arrow
A. 1 [C] Any path
B. 2 [D] Cycle
C. 3 ________________________________
D. 4 B - Which is not a function of device drivers?
________________________________ [A] To manage its power requirements and log
D - Which of the following is not special file? events
[A] None of the other choices [B] To accept abstract read and write request
[B] Block special file from device independent software above it and
[C] Character special file see that they are curried out
[D] Stream special file [C] To receive system call
________________________________ [D] To initialize the device, if needed
A - Device Driver is usually written by: ________________________________
[A] Device's Manufacturer D - An example of preemptable resources is
[B] OS's Manufacturer [A] DVD device
[C] Computer's Manufacturer [B] None of the other choices
[D] All of the other choices [C] CD-ROM device
________________________________ [D] Memory
A - Imagine that a certain modem can read ________________________________
7,000 characters per second and that the time B - In the "dining philosophers" problem, a
to read a philosopher can pick up a fork when____.
character to the modem register is so short it A) there is one available
can be ignored. If to run this modem using B) there are two available
interrupt- C) no other philosopher is eating
driven I/O and each character read requires an D) it is his turn, going in numerical order from
interrupt that takes 10 usee all-in to service. one philosopher to the next
How ________________________________
many percent of the CPU does the interrupt A - Assume the following events and actions
overhead cost? take place. The following statement, ____ is
[A] 4% of the CPU true.
[B] 7% of the CPU Event Action
[C] 96% of the CPU 1 P1 requests and is allocated the printer R1.
2 P1 releases the printer R1. B - Fill in the missing step in the following
3 P2 requests and is allocated the disk drive deadlock situation. Two users from the local
R2. board of education are each running a program
4 P2 releases the disk R2. (P1 and P2), and both programs will eventually
5 P3 requests and is allocated the plotter R3. need two DVD drives to copy files from one disc
6 P3 releases the plotter R3. to another. Only two DVD-R drives are
A) There is no deadlock. available and they're allocated on an "as
B) Event 4 caused deadlock. requested" basis. Soon the following sequence
C) Event 5 caused deadlock. transpires:
D) Event 6 caused deadlock 1. P1 requests drive 1 and gets it.
________________________________ 2. ____
A - Consider the case of a home construction 3. P1 requests drive 2 but is blocked.
company with two application programs, 4. P2 requests drive 1 but is blocked.
purchasing (P1) and sales (P2), which are A) P1 requests drive 2.
active at the same time. They each need to B) P2 requests drive 2 and gets it.
access two files, inventory (F1) and suppliers C) P2 requests drive 1 but is blocked.
(F2), to update daily transactions. The following D) P1 releases drive 1.
series of events will cause a deadlock. Fill in ________________________________
the missing event in the sequence. A - With demand paging, jobs are divided into
equally sized ____ that initially reside in
1. Purchasing (P1) accesses the supplier file secondary storage.
(F2). A) pages
2. Sales (P2) accesses the inventory file (F1). B) blocks
3. Purchasing (P1) doesn't release the supplier C) frames
file (F2) but requests the inventory file (F1), but D) sets
P1 is blocked because F1 is being held by P2. ________________________________
4. Meanwhile, ____ C - If a particular demand paging configuration
has 9 page interrupts out of 11 page requests,
A) sales (P2) doesn't release the inventory file failure rate is ____.
(F1) but requests the supplier file (F2) A) 18%
B) sales (P2) does release the inventory file B) 52%
(F1) and then requests the supplier file (F2) C) 82%
C) purchasing (P1) does release the supplier D) 95%
file (F2) which is then requested by sales (P2) ________________________________
D) purchasing (P1) exits C - The cache hit ratio is ____, if the total
________________________________ number of requests is 10 and 6 of those are
found in cache memory.
A) 6% ________________________________
B) 10% C - Which of the following information bits used
C) 60% by the various page replacement policies
D) 100% indicates if the page has been called lately?
________________________________ a. Locality bit
D - The ____ policy is based on the theory that b. Status bit
the best page to remove is the one that has c. Referenced bit
been in memory the longest. d. Modified bit
A) TRU ________________________________
B) LRU A - The system is said to be in an unsafe state
C) LIFO if
D) FIFO a. The operating system cannot guarantee that
________________________________ all current processes can complete their work
D - What are the allocation methods of disk b. The system is deadlocked
blocks for files: c. A process is indefinitely postponed
a. Contiguous allocation d. None of the above
b. Linked allocation ________________________________
c. Indexed allocation C - QN=42 (7487) In the memory-mapped I/O
d. All of the above system, in order that CPU communicates with
________________________________ the control registers in the devices, the control
D - The following requirement must be met by register is assigned :
any facility or capability that is to provide a. Index
support for mutual exclusion: b. I/O address
a. Only one process at a time can be allowed c. Unique memory address
into a critical code section d. None of the other choices
b. A process remains in its critical region for a ________________________________
finite time only B - QN=60 (7637) A system has four processes
c. No assumption can be made about relative and five allocated resources. The current
process speeds allocation and maximum needs are as follows:
d. All of the above Process Allocated Maximum Available
________________________________ ---------------------------------------------------------------
D - Which of the following is appropriate to ---------------------------------------------------
release page table and pages? A 10211 11212 00x11
a. Process creation B 20110 22210
b. Process execution C 11011 21311
c. Page fault time D 11010 11121
d. Process termination time
a. The interface is exceptionally complex as
What is the smallest value of x for which this is compared with most other resources.
a safe state? b. They are the prevalent form of storing
a. 0 information
b. 1 c. Operating systems often use the file as a
c. 2 primitive for modeling other resource
d. 3 abstractions
________________________________ d. UNIX pipes can be modeled as files
C - 1. The operating system does each of the ________________________________
following except C - 5. A UNIX process contains each of the
a. Allocates the computer's components to following except
different programs a. Text segment
b. Synchronizes individual programs' activities b. Data segment
c. Ensures that programs terminate their c. Thread segment
execution d. Stack segment
d. Provides the general mechanisms that are ________________________________
needed so that the programs execute in perfect D - 6. The process manager deals with the
harmony following except
________________________________ a. Thread management
A - 2. The process is the computational b. Resource management
environment that includes each of the following c. Process management
except d. Window management
a. Operating system ________________________________
b. Data A - 7. The process manager commonly
c. Program interacts with other components except
d. Files a. Device controller
________________________________ b. Device manager
D - 3. Threads can be implemented in each of c. Memory manager
the following ways except d. File manager
a. Run-time libraries ________________________________
b. Operating system D - 8. A trap instruction doesn't cause this CPU
c. Java Virtual Machine hardware step to occur:
d. Parent/child processes a. Switch the CPU to supervisor mode
________________________________ b. Consult the trap table
A - 4. Files are distinguished from other c. Load the PC with an address found in the
resources except that trap table
d. Return control to the user code which d. 8
invoked the trap instruction ________________________________
________________________________ B - 15. The OS implementation of a scheduler
C - 10. On a magnetic disk, which is not a normally does not include
critical timing characteristic? a. Context switcher code
a. Rotational latency b. Procedure call handler code
b. Track seek time c. System call handler code
c. Sector header erasure time d. Interrupt handler code
d. Data transfer latency ________________________________
________________________________ B - 16. In the synchronization context, process
B - 11. Which is not a characteristic of a creation and destruction tend to be quite costly
thread? operations because of the following, except
a. Thread identifier a. Creation/destruction require considerable
b. Thread parent identifier manipulation of process descriptors
c. Thread-specific data b. Parent processes have difficulty tracking
d. Process environment concurrent creation and destruction of child
________________________________ processes
B - 12. Basic process states include the c. Protection mechanism are extensively
following except executed
a. blocked d. Memory management is heavily invoked
b. done ________________________________
c. running C - 17. Which statement about test-and-set is
d. ready incorrect?
________________________________ a. It is the dominant way to accomplish
D - 13. Which is the least common reason that semaphores in modern hardware
a running thread might cease using the CPU? b. Test-and-set involves both a memory
a. Thread completes execution location and a register
b. Thread requests resource, and blocks c. Test-and-set executes as a sequence of
c. Thread voluntarily releases CPU machine instructions
d. Thread involuntarily releases CPU d. Test-and-set can make semaphore
________________________________ implementation simple and efficient
C - 14. How many context switches occur ________________________________
whenever application processes are C - 18. The following statements about AND
multiplexed? synchronization are true except
a. 1 a. Simultaneous semaphore is a programming
b. 2 convenience
c. 4
b. Simultaneous semaphore is an abstraction of c) A program that acts as an intermediary
a basic semaphore between computer software and computer
c. Simultaneous semaphore is slightly more hardware
powerful than basic semaphore d) A program that acts as an intermediary
d. Simultaneous semaphore uses basic between a user of a computer and the
semaphore in a particular pattern computer hardware
________________________________ ________________________________
A - 19. Which statement about monitors is B - What is the main difference function
incorrect? between Operating Systems for Mainframe
a. Monitors can solve just a proper subset of computer and Personal computer?
synchronization problems solvable with a) Multitask
semaphores b) Many I/O devices
b. Monitors provide a simplified paradigm for c) Multi-user
some synchronization problems d) Multiprogramming
c. Monitors can solve synchronization problems ________________________________
too complex for semaphores D - Which of the following is Operating System
d. Monitors are based on abstract data types component?
________________________________ a) Time Management
C - 20. Which statement about IPC is incorrect? b) Space Management
a. The OS explicitly copies information from a c) Speed Management
sending process's address space into a distinct d) File Management
receiving process's space ________________________________
b. Sometimes, the OS can perform the copy by C - Which is the voluntary-condition which
overriding the memory security mechanism terminated process?
c. If the sender and receiver are on different a) Job error
machines, the OS must obtain additional b) Killed by another process
cooperation of the two processes c) Error exit
d. IPC is rarely used between threads in a d) Killed by user
single process ________________________________
________________________________ A - What is the correct approach with the
D - : An Operating System is? Mutual Exclusion condition to prevent
a) A program that acts as an intermediary Deadlock?
between computer processor and computer a) Spool everything
memory b) Request all resources initially
b) A program that acts as an intermediary c) Take resources away
between a user of a computer and a user of d) Order resources numerically
another computer ________________________________
B - : What is the correct approach with the Hold ________________________________
and Wait condition to prevent Deadlock? B - Which command can be used to list all file
a) Spool everything (include hidden files) inside current directory?
b) Request all resources initially a) ls *
c) Take resources away b) ls -a
d) Order resources numerically c) ls -l
________________________________ d) show -a
A - Which of the following actions generates an ________________________________
hardware interrupt? A - Which command would you use to create a
a) An input/output operation is completed. sub-directory in your home directory?
b) A page that does not exist in the main a) mkdir
memory is accessed by the virtual storage b) dir
management. c) cp
c) A system call instruction is executed. d) rm
d) Division by zero occurs. ________________________________
________________________________ B - : Which command will display current day?
D - : Which command is used to change a file's a) day
name? b) date
a) name c) view date
b) move d) calendar
c) chage -n ________________________________
d) mv D - Which command can be used to display the
________________________________ contents of a file on the screen?
B - Which command is used to jump on sub- a) ls
directory? b) grep
a) jump c) dog
b) cd d) cat
c) chage -n ________________________________
d) move C - _____ is the command that writes the
________________________________ bottom 10 lines of a file to the screen.
C - Which command is used to display the a) pr
absolute pathname for the directory that you b) split
are working in? c) tail
a) dir d) head
b) whereami ________________________________
c) pwd D - : _____ is the command that writes the first
d) ls 10 lines of a file to the screen.
a) pr Ignore process switching overhead. Assume
b) split that only one job at a time runs, until it finishes.
c) tail All jobs are completely CPU bound.
d) head a) P-84, F-94, S-70
________________________________ b) P-16, F-18, S-14
C - : The _____ command will list all working c) P-16.8, F-18.8, S-14
processes? ________________________________
a) ls C - The Job Scheduler seeks to ____, when
b) jobs scheduling jobs.
c) ps A) run all CPU intensive jobs first
d) pwd B) run all I/O intensive jobs first
________________________________ C) balance CPU and I/O intensive jobs
D - A system has four processes and five D) run the quickest jobs first
allocated resources. The current allocation and ________________________________
maximum needs are as follows: C - ____ uses the same underlying philosophy
Allocated Maximum Available as shortest job next, where the shortest jobs
Process A 10211 11213 00x11 are processed first and longer jobs are made to
Process B 20110 22210 wait.
Process C 11011 21311 A) LOOK
Process D 11010 11121 B) FCFS
What is the smallest value of x for which this is C) SSTF
a safe state? D) SCAN
a) 0 ________________________________
b) 1 D - The following,____, describes the first
c) 2 memory allocation scheme.
d) 3 A) Each program to be processed was loaded
________________________________ into secondary storage, then swapped into
C - Five batch jobs A through E, arrive at a memory in parts
computer center at almost the same time. They B) Each program to be processed was partially
have estimated running times of 8, 6, 2, 10, and loaded into memory, then granted more
4 minutes. Their (externally determined) memory as needed
priorities are 3, 5, 2, 1, and 4, respectively, with C) Each program to be processed was
5 being the highest priority. For each of the allocated a portion of memory and could
following scheduling algorithms: P-Priority negotiate with other programs to access more
scheduling; F- First-come, first-Server (run in memory
order 8, 6, 2, 10, 4); S-Shortest job first,
determine the mean process turnaround time.
D) Each program to be processed was loaded A) The CPU
in its entirety into memory and allocated as B) I/O Devices
much contiguous space in memory as it needed C) Processors
________________________________ D) Secondary components
C - The ____ contains the value that must be ________________________________
added to each address referenced in the C - The overwhelming demand for ____
program so it will be able to access the correct capability in the mid-1990s sparked the
memory addresses after relocation. proliferation of networking capability.
A) busy list A) e-mail
B) compaction monitor B) processing
C) relocation register C) Internet
D) bounds register D) FTP
________________________________ ________________________________
B - The primary distinguishing characteristic of A - The ____ is unique to each operating
modern computers is ____. system.
A) memory capacity A) User Interface
B) processor capacity B) Process Manager
C) disk space C) Memory Manager
D) physical size D) File Manager
________________________________ ________________________________
B - Second-generation computers were B - The ____ is used to indicate that a program
developed to meet the needs of ____. is permanently held in ROM (read only
A) home users memory), as opposed to being held in
B) businesses secondary storage.
C) secondary education A) hardware
D) online users B) firmware
________________________________ C) software
D - ____ means that several logical records are D) shareware
grouped within one physical record. ________________________________
A) Grouping
B) Fixing
C) Combining
D) Blocking
________________________________
B - ____ include(s) every peripheral unit in the
system such as printers, disk drives, CD/DVD
drives, flash memory, keyboards, and so on.
You might also like
- Solution Manual of Cmputer Organization and ArchitecturDocument29 pagesSolution Manual of Cmputer Organization and ArchitecturHossam Al-atawi44% (27)
- Designing With Xilinx FPGAsDocument257 pagesDesigning With Xilinx FPGAsexfmln89% (9)
- Software Engineering B.Tech IT/II Sem-IIDocument44 pagesSoftware Engineering B.Tech IT/II Sem-IIGaurav SiddharthNo ratings yet
- stm32f7 Reference ManualDocument1,709 pagesstm32f7 Reference ManualЕвгений ИвановNo ratings yet
- Bosch Integrated Circuit Part NumberDocument7 pagesBosch Integrated Circuit Part NumberRadu Soptea100% (2)
- PRO192Document218 pagesPRO192Thành NguyễnNo ratings yet
- Arid Agriculture University, Rawalpindi: Final Exam / Fall 2020 (Paper Duration 24 Hours) To Be Filled by TeacherDocument10 pagesArid Agriculture University, Rawalpindi: Final Exam / Fall 2020 (Paper Duration 24 Hours) To Be Filled by TeacherUmair KhanNo ratings yet
- Cloud Computing LAB ManualDocument13 pagesCloud Computing LAB ManualBhargav RajyagorNo ratings yet
- Experiment-1 Aim: Write A Program For Implementation of Bit StuffingDocument56 pagesExperiment-1 Aim: Write A Program For Implementation of Bit StuffingShaurya KapoorNo ratings yet
- Linux Practical FileDocument41 pagesLinux Practical FilePrashant Kumar100% (1)
- WEB Technologies LAB: Abhishek MPDocument56 pagesWEB Technologies LAB: Abhishek MPAnjan HRNo ratings yet
- Assignment Bca DBMSDocument13 pagesAssignment Bca DBMSbinalamitNo ratings yet
- Assignment 1 Study of DDL and DML Operations On Tables.Document2 pagesAssignment 1 Study of DDL and DML Operations On Tables.Krishna AsharNo ratings yet
- Pipes in PHPDocument15 pagesPipes in PHPRaju PuppalaNo ratings yet
- Multiple Choice Questions (MCQS) On Fundamental of Computers - Set 13 - Loksewa ExamDocument3 pagesMultiple Choice Questions (MCQS) On Fundamental of Computers - Set 13 - Loksewa ExamgdeepthiNo ratings yet
- Figure ListDocument57 pagesFigure ListDien CaoNo ratings yet
- موسوعة امثلة C++ المحلولةDocument34 pagesموسوعة امثلة C++ المحلولةRay AlNo ratings yet
- CoE415R Lab ManualDocument5 pagesCoE415R Lab Manualnak6257No ratings yet
- Hbase Lab Manual3.0-UpdateDocument8 pagesHbase Lab Manual3.0-UpdateDムRK々 BLムDENo ratings yet
- Annauniversity DBMSDocument4 pagesAnnauniversity DBMSlegy86No ratings yet
- C DacDocument117 pagesC DacBhushan Jichkar80% (5)
- CA 2marksDocument41 pagesCA 2marksJaya ShreeNo ratings yet
- Cloud Computing Quiz 1Document2 pagesCloud Computing Quiz 1DiamondNo ratings yet
- 2 2 PPT Managing Oracle InstanceDocument43 pages2 2 PPT Managing Oracle InstancePartho Bora100% (1)
- Solved Question Paper Computer Operator 2011 Samsad SewaDocument13 pagesSolved Question Paper Computer Operator 2011 Samsad SewaksunilbNo ratings yet
- SQL Queries Table Name:-Employee: Empi D Empnam E Departmen T Contactno Emailid Empheadi DDocument4 pagesSQL Queries Table Name:-Employee: Empi D Empnam E Departmen T Contactno Emailid Empheadi DJesin John LMC19MCA003No ratings yet
- CPPDocument303 pagesCPPKatragadda RajeshNo ratings yet
- Devops Assignment 1Document33 pagesDevops Assignment 1selvabharathiNo ratings yet
- ADBMS Parallel and Distributed DatabasesDocument98 pagesADBMS Parallel and Distributed DatabasesTulipNo ratings yet
- PF Lab 4 SummerDocument5 pagesPF Lab 4 SummerTechnical InformationNo ratings yet
- Persistant CompanyDocument13 pagesPersistant Companyanilnaik287No ratings yet
- Lab Manual For RDBMSDocument25 pagesLab Manual For RDBMSMohammad BangeeNo ratings yet
- Oops Lab VaseemDocument41 pagesOops Lab VaseemMohd. VaseemNo ratings yet
- GPL Unix Questions For AMDOCSDocument8 pagesGPL Unix Questions For AMDOCSTabish AlmasNo ratings yet
- 15mis0429 (Javascript)Document35 pages15mis0429 (Javascript)Chandana ChanduNo ratings yet
- Shift Micro-OperationsDocument8 pagesShift Micro-Operationsoureducation.in100% (4)
- Compiler Design Practical FileDocument24 pagesCompiler Design Practical FileSagarNo ratings yet
- Lab 1.5.3: Challenge Router Configuration: Topology DiagramDocument4 pagesLab 1.5.3: Challenge Router Configuration: Topology DiagramAnjasa Keisar EtienNo ratings yet
- Lab 2 - Function and ArrayDocument4 pagesLab 2 - Function and Arrayananyasri.upadhyaNo ratings yet
- Nishant Web TechDocument40 pagesNishant Web TechNishant MishraNo ratings yet
- MySQL Basic SELECT Statement - Exercises, Practice, SolutionDocument45 pagesMySQL Basic SELECT Statement - Exercises, Practice, SolutionDarwin VargasNo ratings yet
- Operating System NotesDocument16 pagesOperating System NotesSreedhar YellamNo ratings yet
- System Programming Lab Report 04Document12 pagesSystem Programming Lab Report 04Abdul RehmanNo ratings yet
- Data Stage FaqsDocument47 pagesData Stage FaqsVamsi Krishna EmanyNo ratings yet
- Operating System MCQsDocument13 pagesOperating System MCQsmanish_singh51No ratings yet
- 3 - Introduction SQL Plus PDFDocument16 pages3 - Introduction SQL Plus PDFArtiakuNo ratings yet
- 15CS45 OOC Solutions - Dec 2017 - Jan 2018Document20 pages15CS45 OOC Solutions - Dec 2017 - Jan 2018Arjun S NNo ratings yet
- 41-58 It MCQSDocument18 pages41-58 It MCQSSameer SharmaNo ratings yet
- Computer Based MCQ (1-100)Document26 pagesComputer Based MCQ (1-100)sam heisenberg100% (1)
- Charusat Android Practical List.Document95 pagesCharusat Android Practical List.programmerNo ratings yet
- PHP Whole PDFDocument284 pagesPHP Whole PDFKshitij NayakNo ratings yet
- DBMS Lab AssgDocument9 pagesDBMS Lab AssgAbhishek Jha100% (1)
- 6 SQL Bangla TutorialsDocument16 pages6 SQL Bangla TutorialsFaruqur RashidNo ratings yet
- Distributed DatabaseDocument49 pagesDistributed DatabaseSatheswaran RajasegaranNo ratings yet
- Chapter 10: Forouzan Data Communications and NetworksDocument3 pagesChapter 10: Forouzan Data Communications and NetworksMaithaNo ratings yet
- I.C.T 2nd Term 2017 Western Province Sinhala Medium Past PaperDocument16 pagesI.C.T 2nd Term 2017 Western Province Sinhala Medium Past PaperDeshaniNo ratings yet
- CH 2 Word Assignment Sheet-2Document2 pagesCH 2 Word Assignment Sheet-2Deedra RossiNo ratings yet
- Exercise 101 For Students Enrolled in Joomla CourseDocument4 pagesExercise 101 For Students Enrolled in Joomla CourseJoel Fagsao100% (1)
- Install and Run Hadoop On WindowsDocument29 pagesInstall and Run Hadoop On WindowssunilswastikNo ratings yet
- Compiler Construction - CS606 Power Point Slides Lecture 01Document20 pagesCompiler Construction - CS606 Power Point Slides Lecture 01Mashavia100% (1)
- ExamDocument7 pagesExamMaynard Angelo C. MarcosNo ratings yet
- Java Lab ManualDocument48 pagesJava Lab Manualkhanimran182No ratings yet
- Test3 (SP22) - Attempt ReviewDocument17 pagesTest3 (SP22) - Attempt ReviewTrần KhangNo ratings yet
- Test3SP22 Attempt ReviewDocument22 pagesTest3SP22 Attempt ReviewTrần KhangNo ratings yet
- SU21-Progress TestDocument45 pagesSU21-Progress TestTrần KhangNo ratings yet
- OSG202 Revise1Document43 pagesOSG202 Revise1Trần KhangNo ratings yet
- Tugas 4 MHSDocument17 pagesTugas 4 MHSMelly Amelia VelinaNo ratings yet
- Operating System ReviwDocument24 pagesOperating System ReviwRafael D. SanchezNo ratings yet
- ArduinoDocument156 pagesArduinoMike Gomez91% (23)
- Computer by Yatendra Sir: MemoryDocument7 pagesComputer by Yatendra Sir: Memoryparassh knowledgeNo ratings yet
- H97M ITXacDocument93 pagesH97M ITXaceujanroNo ratings yet
- Introduction To ICC AVR: Setting Up A New Project: NEX Robotics Fire Bird III - ICCAVR ManualDocument12 pagesIntroduction To ICC AVR: Setting Up A New Project: NEX Robotics Fire Bird III - ICCAVR ManualChester Noel Brenes AguirreNo ratings yet
- Tutorial Letter 201/2/2018 Solutions To Assignment No.1: School of ComputingDocument8 pagesTutorial Letter 201/2/2018 Solutions To Assignment No.1: School of ComputingThanyani SirumulaNo ratings yet
- Product ID: SDOCK2U33REDocument5 pagesProduct ID: SDOCK2U33REayham HamamaNo ratings yet
- SVM 53 I SVM 53 C: Thermal Transfer OverprintersDocument2 pagesSVM 53 I SVM 53 C: Thermal Transfer OverprintersYsabel Cristina Yaguaracuto TorrealbaNo ratings yet
- How To Install Windows-10Document7 pagesHow To Install Windows-10Amin KhanNo ratings yet
- Instruction Set ArchitectureDocument10 pagesInstruction Set ArchitecturejoNo ratings yet
- Poweredge r840 Spec SheetDocument2 pagesPoweredge r840 Spec SheetNoemi VelasquezNo ratings yet
- Q630 (LC630, P630, P631, P635, P636, P638, P640) SpeedupDocument6 pagesQ630 (LC630, P630, P631, P635, P636, P638, P640) SpeedupTek NikoNo ratings yet
- FOA Lab Equioment ListDocument2 pagesFOA Lab Equioment ListSUVIDHA COUNSALTANCYNo ratings yet
- Thinkpad E15: 20Rd001CgeDocument3 pagesThinkpad E15: 20Rd001CgesacralNo ratings yet
- Spot Billing SystemDocument2 pagesSpot Billing Systemvicky_89inNo ratings yet
- CoDeSys V3 Linux - EDocument2 pagesCoDeSys V3 Linux - EVinothNo ratings yet
- Computer Science CVDocument2 pagesComputer Science CVSaid ElhantaouiNo ratings yet
- Intel Processor ChecklistDocument7 pagesIntel Processor ChecklistMilind ShahNo ratings yet
- 5_6066848005196087350Document25 pages5_6066848005196087350Yared TarikuNo ratings yet
- Imac (21.5-Inch and 27-Inch, Mid 2011) - Technical SpecificationsDocument4 pagesImac (21.5-Inch and 27-Inch, Mid 2011) - Technical SpecificationsprincedottyNo ratings yet
- Processor 521x User Manual: Messung Systems NEXGEN - 5000Document54 pagesProcessor 521x User Manual: Messung Systems NEXGEN - 5000arunkumarNo ratings yet
- The Museum of HP CalculatorsDocument3 pagesThe Museum of HP CalculatorsRodrigo Zúñiga GarcíaNo ratings yet
- Bus Cycles (Chap. 7) : 4 System Bus Clock Periods For 8086/8088/80286Document8 pagesBus Cycles (Chap. 7) : 4 System Bus Clock Periods For 8086/8088/80286नील दासNo ratings yet
- H8 539 ExtendedDocument916 pagesH8 539 ExtendedNixon Maldonado100% (1)
- MCUXpresso SDK USB Stack Device Reference ManualDocument239 pagesMCUXpresso SDK USB Stack Device Reference ManualcorazzaedwardNo ratings yet